73ebdb64c3
Update privilege_escalation_persistence_phantom_dll.toml ( #2443 )
2023-01-04 07:46:59 +00:00
7cf14dd515
[Rule Tuning] Parent Process PID Spoofing ( #2432 )
...
* Update defense_evasion_parent_process_pid_spoofing.toml
* Update defense_evasion_parent_process_pid_spoofing.toml
* Update defense_evasion_parent_process_pid_spoofing.toml
* Update defense_evasion_parent_process_pid_spoofing.toml
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-12-22 14:23:13 +00:00
ae4f671bae
[New Rule] First Time Seen Driver Loaded ( #2434 )
...
* Create persistence_driver_newterm_imphash.toml
* Update persistence_driver_newterm_imphash.toml
* Update persistence_driver_newterm_imphash.toml
* Update persistence_driver_newterm_imphash.toml
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
2022-12-22 14:10:33 +00:00
9c1bd50a63
[Rule Tuning] Adjust Index Pattern on Windows rules to support WEF ( #2438 )
...
* [Rule Tuning] Adjust Index Pattern on Windows rules to support WEF
* s/host.id/winlog.computer_name
2022-12-21 11:30:04 -03:00
2516a4013a
[Rule Tuning] PrivEsc via Print Spool Service ( #2431 )
...
* Update privilege_escalation_printspooler_service_suspicious_file.toml
* Update privilege_escalation_printspooler_suspicious_spl_file.toml
Co-authored-by: shashank-elastic <91139415+shashank-elastic@users.noreply.github.com >
2022-12-21 11:51:26 +00:00
80548b97f4
[Rule Tuning] Access to a Sensitive LDAP Attribute ( #2430 )
...
* Update credential_access_ldap_attributes.toml
* Update credential_access_ldap_attributes.toml
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-12-18 20:36:17 +00:00
ae4e59ec7d
[FR] Update ATT&CK Package to v12.1 ( #2422 )
...
* initial update to v12.1 attack package
* added additional click echo output
* addressed flake errors
* updated rules with refreshed att&ck data
* Update detection_rules/devtools.py
Co-authored-by: Mika Ayenson <Mikaayenson@users.noreply.github.com >
Co-authored-by: Mika Ayenson <Mikaayenson@users.noreply.github.com >
2022-12-16 12:04:20 -05:00
b0085f4304
[Rule Tuning] Temporarily Scheduled Task Creation ( #2411 )
2022-11-28 09:50:08 -03:00
ac01718bb6
[Rule Tuning] Add tags to flag Sysmon-only rules & Modify Investigation Guide-related tag ( #2352 )
...
* [Rule Tuning] Add tags to flag Sysmon-only rules
* Modify tags
* Revert "Modify tags"
This reverts commit 3d9267d171a41f727bb499501d71d5c4db4f0434.
* Modify tags
* Update test_all_rules.py
* Update test_all_rules.py
* Update test_all_rules.py
* Update test_all_rules.py
* Update test_all_rules.py
2022-11-18 12:32:27 -03:00
6055d0db60
[Security Content] Introduce Osquery Markdown Plugin Queries in Investigation Guides ( #2387 )
...
* [Security Content] Introduce Osquery Markdown Plugin Queries in Investigation Guides
* Remove min_stack and add Note
* Fix Typo and preffix
* Update command_and_control_certutil_network_connection.toml
* Add unit test to check Note about Osquery Markdown plugin and Version limitations
* Update test_all_rules.py
* Update test_all_rules.py
* Change Note Verbiage
2022-11-17 18:38:34 -03:00
6555bba965
[New Rule] Persistence via PowerShell profile ( #2357 )
...
* [New Rule] Persistence via PowerShell profile
* Apply suggestions from code review
Co-authored-by: Samirbous <64742097+Samirbous@users.noreply.github.com >
* Update persistence_powersshell_profiles.toml
Co-authored-by: Samirbous <64742097+Samirbous@users.noreply.github.com >
2022-11-16 08:42:49 -03:00
5a762eaf85
[Rule Tuning] NullSessionPipe Registry Modification ( #2350 )
...
* [Rule Tuning] NullSessionPipe Registry Modification
* Trying length
Co-authored-by: Samirbous <64742097+Samirbous@users.noreply.github.com >
2022-11-16 10:15:18 +00:00
b1ddfb11d4
[New Rule] Windows Services - winlog ( #2280 )
...
* [New Rule] Windows Services - winlog
https://github.com/elastic/detection-rules/issues/2164 (T1543.003 - Windows Service)
- remote windows service (4624,4697)
- suspicious windows service imagepath (7045, 4697) : cmd, powershell etc.
* added winlog.logon.type (keyword)
* Update non-ecs-schema.json
* Update persistence_service_windows_service_winlog.toml
* Update non-ecs-schema.json
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
2022-11-16 10:08:02 +00:00
cbbac02b56
[Rule Tuning] Potential Shadow Credentials added to AD Object ( #2359 )
...
limit the query to suspicious KEYCREDENTIALLINK_BLOB value length to 828 `DN-Binary data: B:<char count>:<binary value>:<object DN>` which matches on the add of a keycredential structure using public offensive tooling and avoid FPs (Azure, CredGuard and others).
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
2022-11-15 20:01:22 +00:00
b0156181e7
[New Rules] T1134 Access Token Manipulation ( #2373 )
...
* New Rules] T1134 Access Token Manipulation
3 rules (2 compatible only with Elastic endpoint) and 1 generic one using winlogs.
* Update privilege_escalation_tokenmanip_sedebugpriv_enabled.toml
* fix ruleid
* Update privilege_escalation_via_token_theft.toml
* timestamp_override = "event.ingested"
* Update non-ecs-schema.json
* linted
* Update privilege_escalation_tokenmanip_sedebugpriv_enabled.toml
* Update non-ecs-schema.json
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-11-15 19:50:47 +00:00
6233c01c34
Update privilege_escalation_suspicious_dnshostname_update.toml ( #2394 )
2022-11-15 19:26:41 +00:00
0bf7dd15a5
[New Rules] CredAccess via LDAP Attributes ( #2391 )
...
* Create credential_access_ldap_attributes.toml
* Create privilege_escalation_credroaming_ldap.toml
* Update non-ecs-schema.json
* Update privilege_escalation_credroaming_ldap.toml
just deleted the extra 'to'
Co-authored-by: Isai <59296946+imays11@users.noreply.github.com >
2022-11-15 15:55:01 +00:00
4997f95300
[Rule Tuning] Link Elastic Security Labs content to compatible rules ( #2388 )
...
* added elastic security labs URL references
* Update rules/macos/credential_access_keychain_pwd_retrieval_security_cmd.toml
Is not compatible with Windows blog.
* Update rules/macos/credential_access_keychain_pwd_retrieval_security_cmd.toml
Is not compatible with Windows blog. Reverting updated date.
* Update rules/macos/credential_access_access_to_browser_credentials_procargs.toml
Is not compatible with Windows blog. Reverting updated date.
* Update rules/macos/credential_access_access_to_browser_credentials_procargs.toml
Is not compatible with Windows blog.
* Update rules/ml/execution_ml_windows_anomalous_script.toml
Is not compatible with Windows blog. Reverting updated date.
* Update rules/linux/credential_access_collection_sensitive_files.toml
Not compatible with Windows blog. Reverting updated date.
* Update rules/linux/credential_access_collection_sensitive_files.toml
Not compatible with Windows blog.
* added credential access URL for mimikatz rules
* updated version ml windows anomalous script rule
* removed change to macOS rule since no blog correlation
2022-11-07 15:17:49 -05:00
25458123dd
Update lateral_movement_mount_hidden_or_webdav_share_net.toml ( #2385 )
...
rule tune: update by adding MITRE tactic/technique/subtechnique : Initial Access>Valid Accounts>Local Accounts. Added new tag for new tactic : Initial Access
2022-11-07 12:14:06 -05:00
85e8c0abad
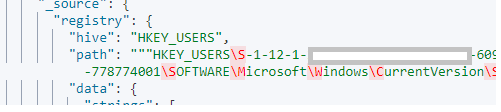
[Rule Tuning] Update User.ID or Registry.Path to include Azure Users SID ( #2378 )
...
Azure AD SIDs start with S-1-12-1-* and we have 8 rules that uses user.id or registry.path to limit activity to AD/local users which starts with S-1-5-21-*.
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-11-01 17:45:39 +00:00
e89bc230ab
[Tuning] Diverse Windows Rules Tuning ( #2383 )
...
* [Rules Tuning] TPrep
* more
* Update credential_access_wireless_creds_dumping.toml
* Update persistence_user_account_creation_event_logs.toml
* Update discovery_files_dir_systeminfo_via_cmd.toml
* fix errors
* Update command_and_control_common_webservices.toml
* fix errors
* Update persistence_user_account_creation_event_logs.toml
* Update rules/windows/credential_access_wireless_creds_dumping.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
* Update rules/windows/defense_evasion_persistence_account_tokenfilterpolicy.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
* Update rules/windows/discovery_files_dir_systeminfo_via_cmd.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
* switched back to kql
* Update persistence_user_account_creation_event_logs.toml
* Update rules/windows/credential_access_wireless_creds_dumping.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
* Update rules/windows/defense_evasion_persistence_account_tokenfilterpolicy.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
* added T1555
* Update persistence_user_account_creation_event_logs.toml
* Update defense_evasion_persistence_account_tokenfilterpolicy.toml
* Update defense_evasion_persistence_account_tokenfilterpolicy.toml
Co-authored-by: Jonhnathan <26856693+w0rk3r@users.noreply.github.com >
2022-11-01 16:48:25 +00:00
183b1ffdd3
[Rule Tuning] Add endgame support for Windows Rules ( #2285 )
...
* [Rule Tuning] Add endgame support for Windows Rules
* Update collection_email_powershell_exchange_mailbox.toml
* Supported Rules - First Half
* bum updated_date
* Add tag
* Revert compat
* missing tags
2022-10-19 08:27:44 -07:00
e761beb0a0
Rule Tuning on Potential Application Shimming via Sdbinst ( #2355 )
2022-10-14 13:25:02 +05:30
9861958833
[Security Content] Add missing "has_guide" tag ( #2349 )
...
* Add missing "has_guide" tag
* bump updated_date
2022-10-11 06:30:19 -07:00
518d146cb0
[Rule Tuning] Exclude Elastic Agent from "Potential Process Herpaderping Attempt" ( #2342 )
...
* adjusted query to filter out Elastic or Trend Micro EXE activity
* added wildcard to drive letter and fixed unit test failure
2022-10-05 13:45:36 -04:00
f5c992b6de
[Security Content] Add Investigation Guides - 2 - 8.5 ( #2314 )
...
* [Security Content] Add Investigation Guides - 2 - 8.5
* Update rules/windows/lateral_movement_execution_via_file_shares_sequence.toml
* Merge branch 'main' into investigation_guides_8.5_2
* Revert "Merge branch 'main' into investigation_guides_8.5_2"
This reverts commit fb3c3f0245301d49229534d8776478c32f6c190e.
* Apply suggested changes from review
* Update discovery_security_software_grep.toml
* Apply suggestions from review
* Apply suggestions from review
2022-09-26 12:59:39 -03:00
4366702b34
[Rule Tuning] Removed potential typo within rule "persistence_gpo_schtask_service_creation" ( #2301 )
...
* Changed potential typo
* Revert "Changed potential typo"
This reverts commit 28e6b7206e7626121c4a2699d1fa12ba2b59408f.
* Changed potential typo
* Change the "updated_date"
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
Co-authored-by: Jonhnathan <jonhnathancesar@gmail.com >
2022-09-26 10:23:54 -03:00
f02ffbbe13
[Security Content] Add Investigation Guides - 8.5 ( #2305 )
...
* [Security Content] Add Investigation Guides - 8.5
* Update persistence_run_key_and_startup_broad.toml
* Apply suggestions from security-docs review review
* Update execution_suspicious_jar_child_process.toml
* Apply suggestions from review
2022-09-23 18:44:24 -03:00
ec04a39413
[Security Content] Tag rules with robust Investigation Guides ( #2297 )
2022-09-23 14:20:32 -03:00
09565d97b7
[New Rule] PowerShell Script with Token Impersonation Capabilities ( #2246 )
...
* [New Rule] PowerShell Script with Token Impersonation Capabilities
* Update privilege_escalation_posh_token_impersonation.toml
* Update privilege_escalation_posh_token_impersonation.toml
* Update privilege_escalation_posh_token_impersonation.toml
Co-authored-by: Mika Ayenson <Mikaayenson@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-09-19 15:43:38 -03:00
a955e34b43
[New Rule] PowerShell Share Enumeration Script ( #2243 )
...
* [New Rule] PowerShell Share Enumeration Script
* Move the rule to the correct folder
* Update discovery_posh_invoke_sharefinder.toml
* Update discovery_posh_invoke_sharefinder.toml
Co-authored-by: Mika Ayenson <Mikaayenson@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-09-19 15:38:23 -03:00
d52c0d2257
[Rule Tuning] Remove "process_started" from Windows Rules ( #2238 )
...
* [Rule Tuning] Remove "process_started" from Windows Rules
* Additional, pending ones
* Update defense_evasion_code_injection_conhost.toml
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-09-19 13:06:30 -05:00
acdfe5ddab
[New Rule] Process Creation via Secondary Logon ( #2282 )
...
* [New Rule] Process Creation via Secondary Logon
https://github.com/elastic/detection-rules/issues/2164
Create process using alternate creds (i.g. runas) :
* Update privilege_escalation_create_process_as_different_user.toml
* Update privilege_escalation_create_process_as_different_user.toml
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-09-19 13:04:08 -05:00
99dcfe2055
[New Rule] Multiple Vault Web credentials were read ( #2281 )
...
* [New Rule] Multiple Vault Web credentials were read
https://github.com/elastic/detection-rules/issues/2164
* Update credential_access_saved_creds_vault_winlog.toml
* Update non-ecs-schema.json
* Update rules/windows/credential_access_saved_creds_vault_winlog.toml
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
2022-09-19 19:07:05 +02:00
4609a5e8fe
[New Rule] Scheduled Task Creation using winlog ( #2277 )
...
* [New Rule] Scheduled Task Creation using winlog
https://github.com/elastic/detection-rules/issues/2164 (T1053.005 - Scheduled Task)
- A scheduled task was created
- A scheduled task was updated
- Temp scheduled task (creation followed by deletion, rare and can be sign of proxy execution via schedule service)
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* toml-lint
* remote task
* Update non-ecs-schema.json
* waaaaaaaaaaaaaa
* Update persistence_scheduled_task_updated.toml
* Update persistence_scheduled_task_creation_winlog.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update lateral_movement_remote_task_creation_winlog.toml
* event.ingested
* Update lateral_movement_remote_task_creation_winlog.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update defense_evasion_persistence_temp_scheduled_task.toml
* Update rules/windows/lateral_movement_remote_task_creation_winlog.toml
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
2022-09-19 18:50:45 +02:00
fc8ec668b1
[New Rule] Brute Force Detection - Windows ( #2275 )
...
* [New Rule] Brute Force Detection - Windows
https://github.com/elastic/detection-rules/issues/2164 (T1110 - Brute Force)
- multiple logon failure from same source address in 10s maxspan
- 5 logon failure followed by success from same source address in 5s maxspan
* non ecs
* Update credential_access_bruteforce_multiple_logon_failure_followed_by_success.toml
* fix error
* added bruteforce admin account and linted tomls
* Update credential_access_bruteforce_admin_account.toml
* Update rules/windows/credential_access_bruteforce_admin_account.toml
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
* related_rules
* 4625_errorcode_notes
Co-authored-by: Justin Ibarra <brokensound77@users.noreply.github.com >
2022-09-19 18:43:28 +02:00
ca2b3c2b7f
[New Rule] Full User-Mode Dumps Enabled System-Wide ( #2276 )
...
* [New Rule] Full User-Mode Dumps Enabled System-Wide
* Apply suggestions from review
* Update credential_access_generic_localdumps.toml
2022-09-15 16:57:00 -03:00
3ba777c1b1
[Rule Tuning] Disable Windows Firewall Rules via Netsh ( #2231 )
...
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
Co-authored-by: Jonhnathan <jonhnathancesar@gmail.com >
2022-08-26 13:10:08 -04:00
97e42d01d8
[Rule Tuning] SUNBURST Command and Control Activity ( #2232 )
...
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
Co-authored-by: Jonhnathan <jonhnathancesar@gmail.com >
2022-08-26 13:11:22 -03:00
46d5e37b76
min_stack all rules to 8.3 ( #2259 )
...
* min_stack all rules to 8.3
* bump date
Co-authored-by: Mika Ayenson <mika.ayenson@elastic.co >
2022-08-24 10:38:49 -06:00
023fbc7bbd
[Rule Tuning] Clearing Windows Event Logs ( #2233 )
...
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-08-23 21:41:30 -03:00
6e2d20362a
[Rule Tuning] Standardizing Risk Score according to Severity ( #2242 )
2022-08-21 22:29:39 -03:00
d3420e3386
[Deprecate Rule] Suspicious Process from Conhost ( #2222 )
...
only FPs with no way to tune other than opening the rule for easy evasion by excluding by process.executable/args).
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-08-16 16:32:24 +02:00
8e0ae64a04
[Rule Tuning] Whoami Process Activity ( #2224 )
...
* added Whoami Process Activity
* Update discovery_whoami_command_activity.toml
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-08-16 16:26:10 +02:00
0f7b29918c
[Rule Tuning] Suspicious Execution via Scheduled Task ( #2235 )
...
Excluding`?:\\ProgramData` and few other noisy FP pattern by process.args + name to reduce users alert fatigue.
2022-08-15 21:50:23 +02:00
b89d6185b2
[Rule Tuning] Reduce FPs ( #2223 )
...
9 rules tuned to exclude common noisy FP patterns.
Co-authored-by: Colson Wilhoit <48036388+DefSecSentinel@users.noreply.github.com >
2022-08-15 09:15:48 -05:00
fc7a384d19
[Security Content] 8.4 - Add Investigation Guides - Windows - 2 ( #2144 )
...
* [Security Content] 8.4 - Add Investigation Guides - Windows - 2
* update date
* Apply suggestions from review
* Apply suggestions from code review
Co-authored-by: Joe Peeples <joe.peeples@elastic.co >
Co-authored-by: Joe Peeples <joe.peeples@elastic.co >
Co-authored-by: Mika Ayenson <Mikaayenson@users.noreply.github.com >
2022-08-08 21:34:05 -03:00
b043695833
Remove ambiguity from impact_modification_of_boot_config.toml ( #2199 )
...
Co-authored-by: Samirbous <64742097+Samirbous@users.noreply.github.com >
Co-authored-by: Terrance DeJesus <99630311+terrancedejesus@users.noreply.github.com >
Co-authored-by: Jonhnathan <jonhnathancesar@gmail.com >
2022-08-05 10:38:41 -03:00
50bb821708
[Rules Tuning] Add support for Sysmon ImageLoad Events ( #2215 )
...
* [Rules Tuning] Add support for Sysmon ImageLoad Events
added correct event.category and event.action to rules using library events to support sysmon eventid 7.
`event.category == "library"` --> `(event.category == "process" and event.action : "Image loaded*")`
`dll.name` --> `file.name`
* added Suspicious RDP ActiveX Client Loaded
* Delete workspace.xml
2022-08-02 18:40:26 +02:00
b15f0de9a4
[Rules Tuning] Diverse Windows Rules - FPs reduction ( #2213 )
...
* [Rules Tuning] 7 diverse Windows rules
Excluding FP patterns while avoiding breaking compat with winlogbeat and 4688 events lack of codesign metadata.
* Update initial_access_suspicious_ms_exchange_process.toml
* Update privilege_escalation_persistence_phantom_dll.toml
* Update execution_psexec_lateral_movement_command.toml
* Update persistence_remote_password_reset.toml
* Update non-ecs-schema.json
* Update persistence_remote_password_reset.toml
* Update non-ecs-schema.json
* Update discovery_privileged_localgroup_membership.toml
2022-08-02 18:37:07 +02:00